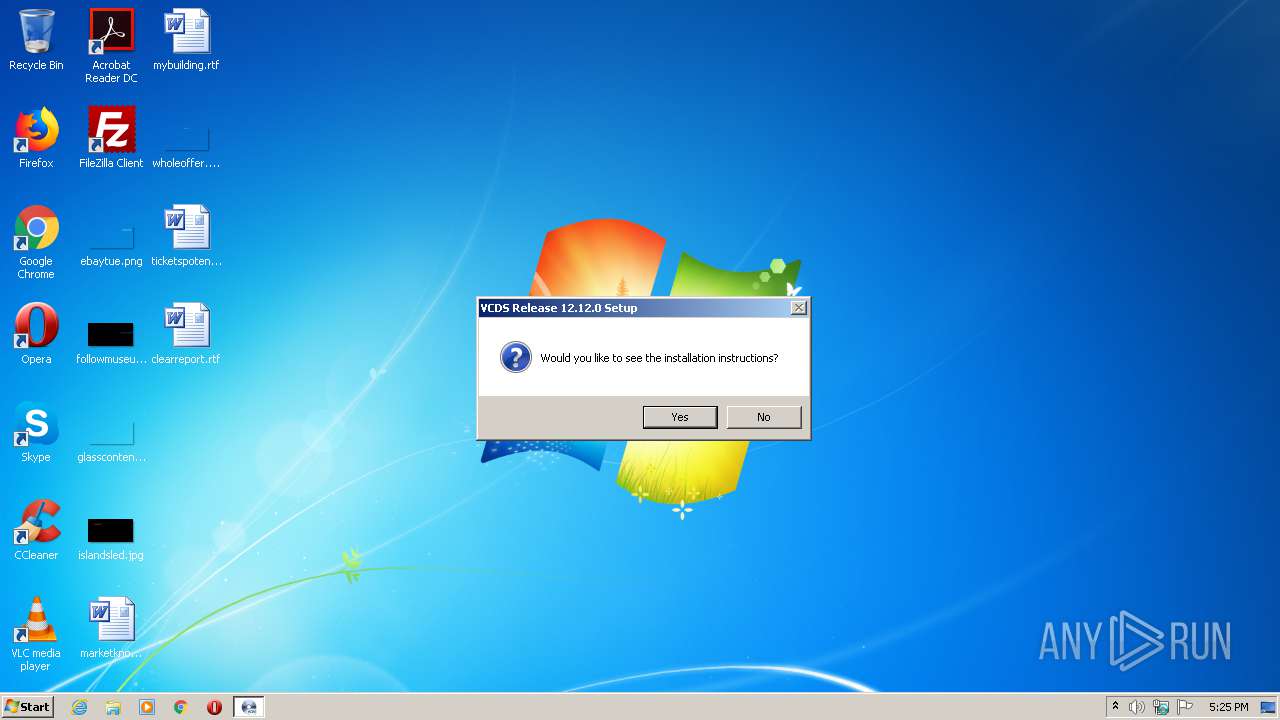
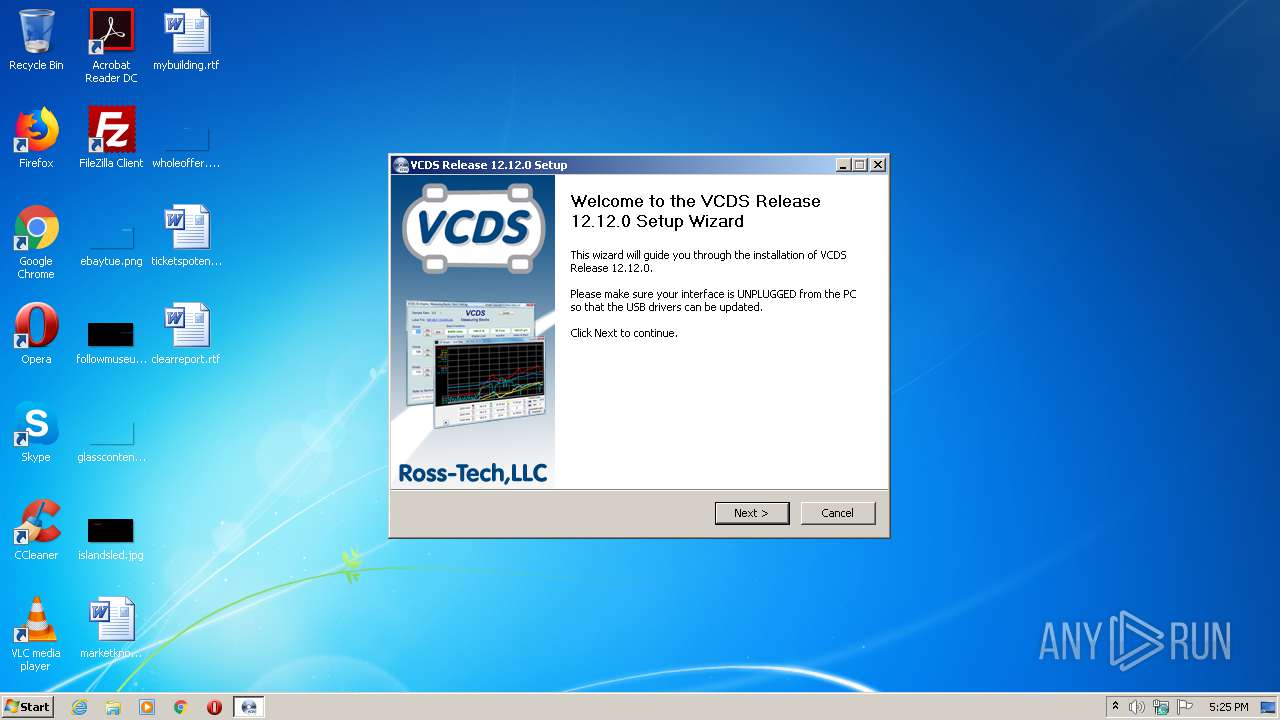
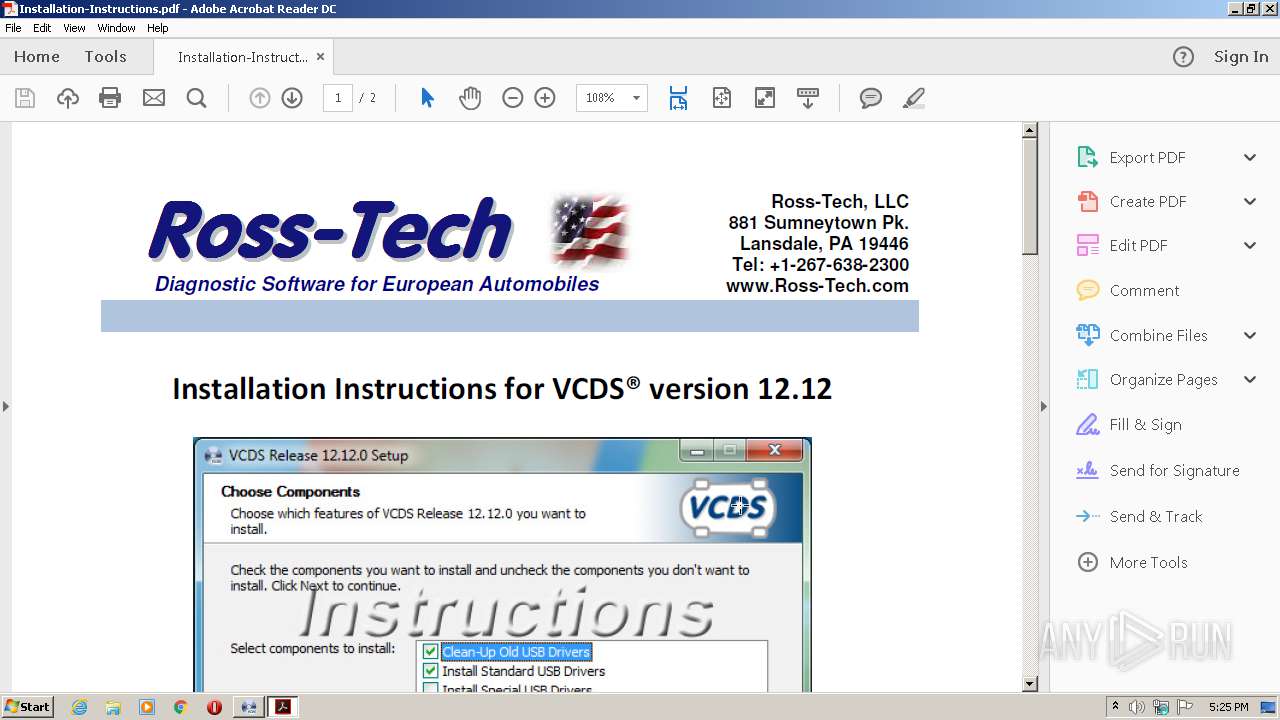
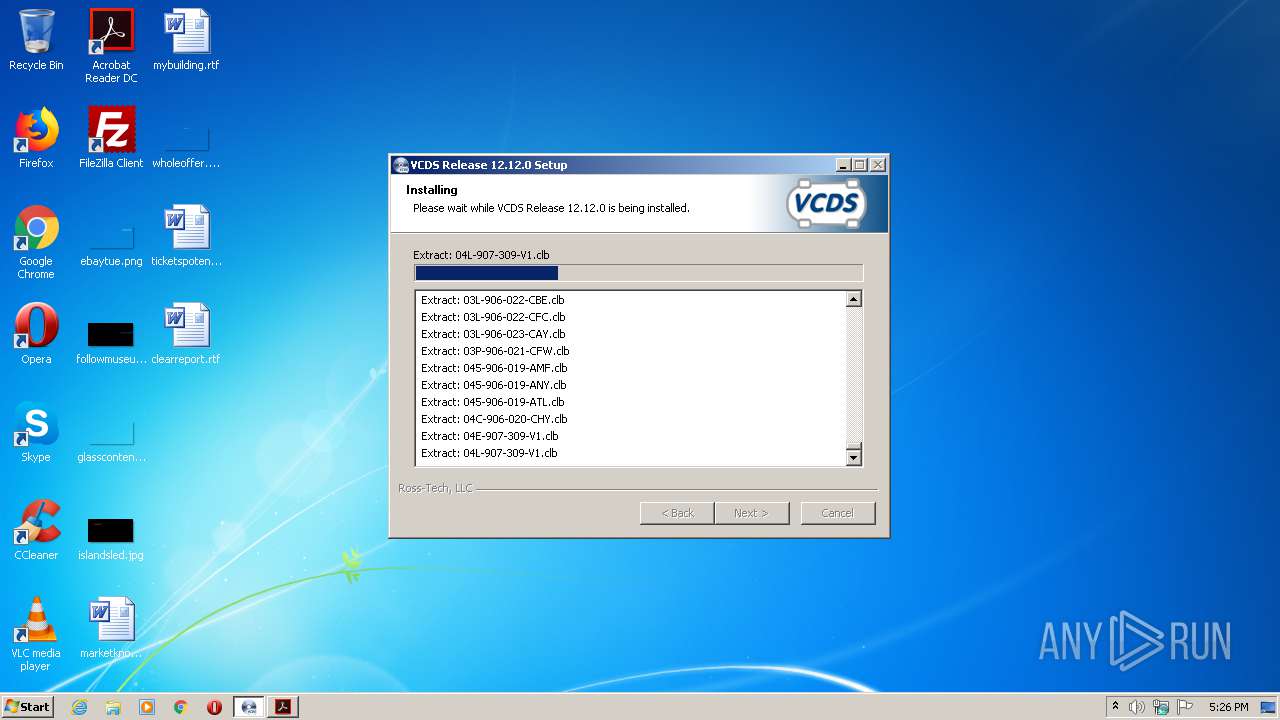
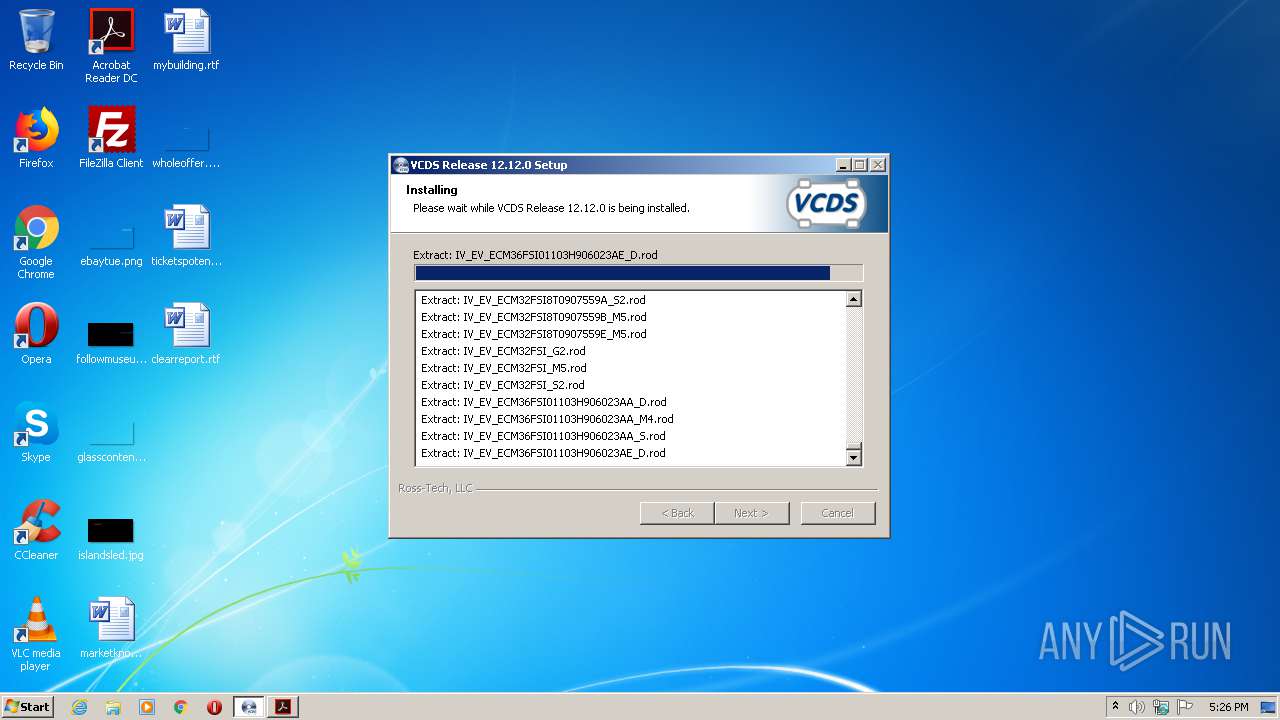
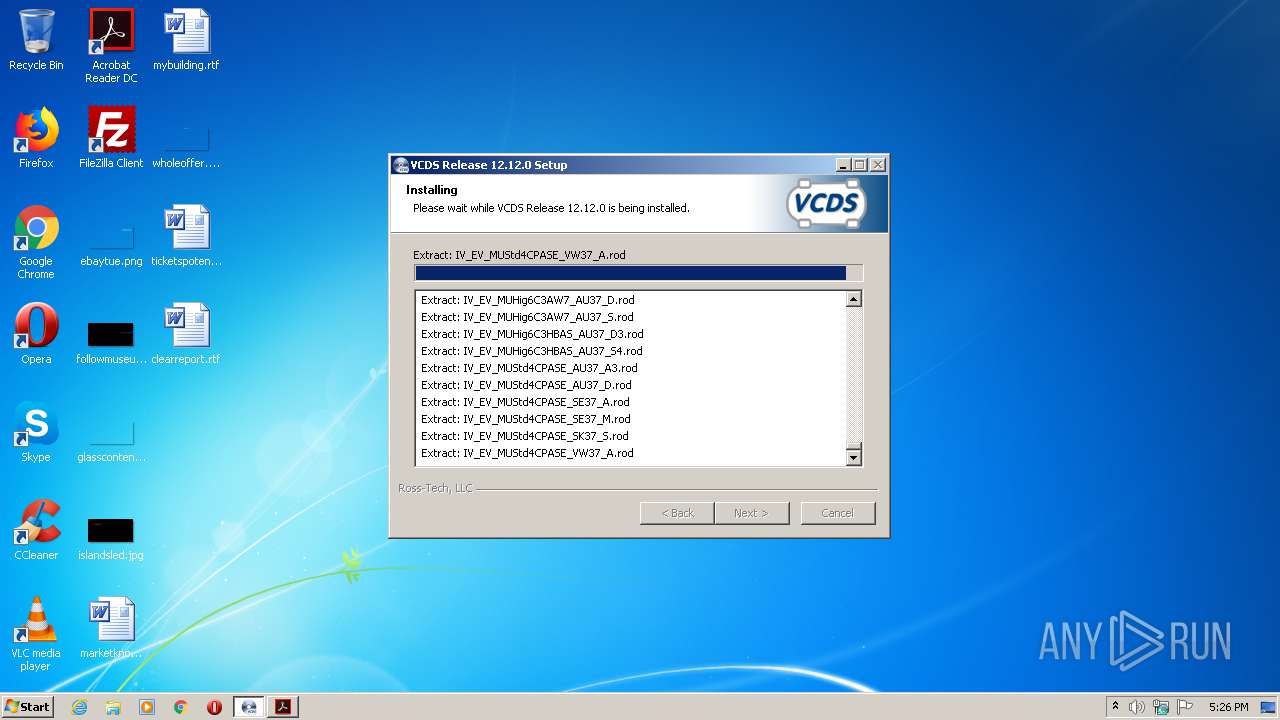
| File name: | vcds-release-12.12.0-installer.exe |
| Full analysis: | https://app.any.run/tasks/fb85ade9-0b03-45d4-87e0-d737444db28a |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2021, 16:25:05 |
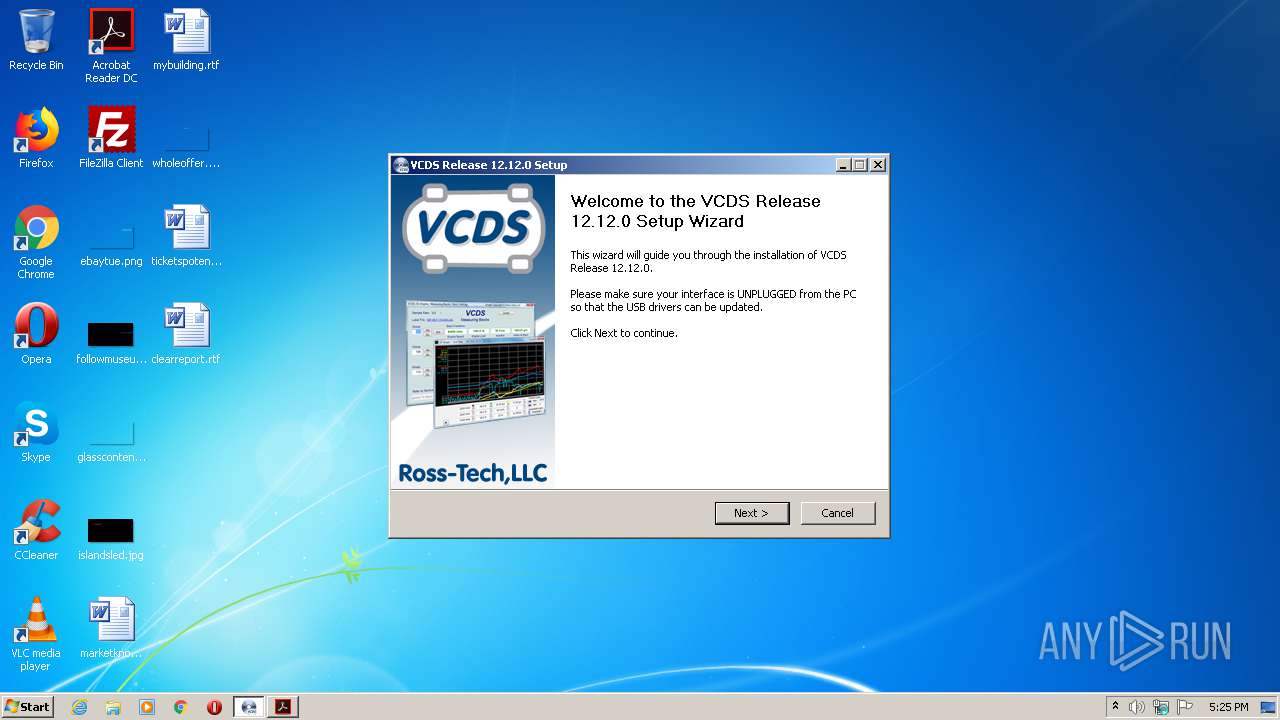
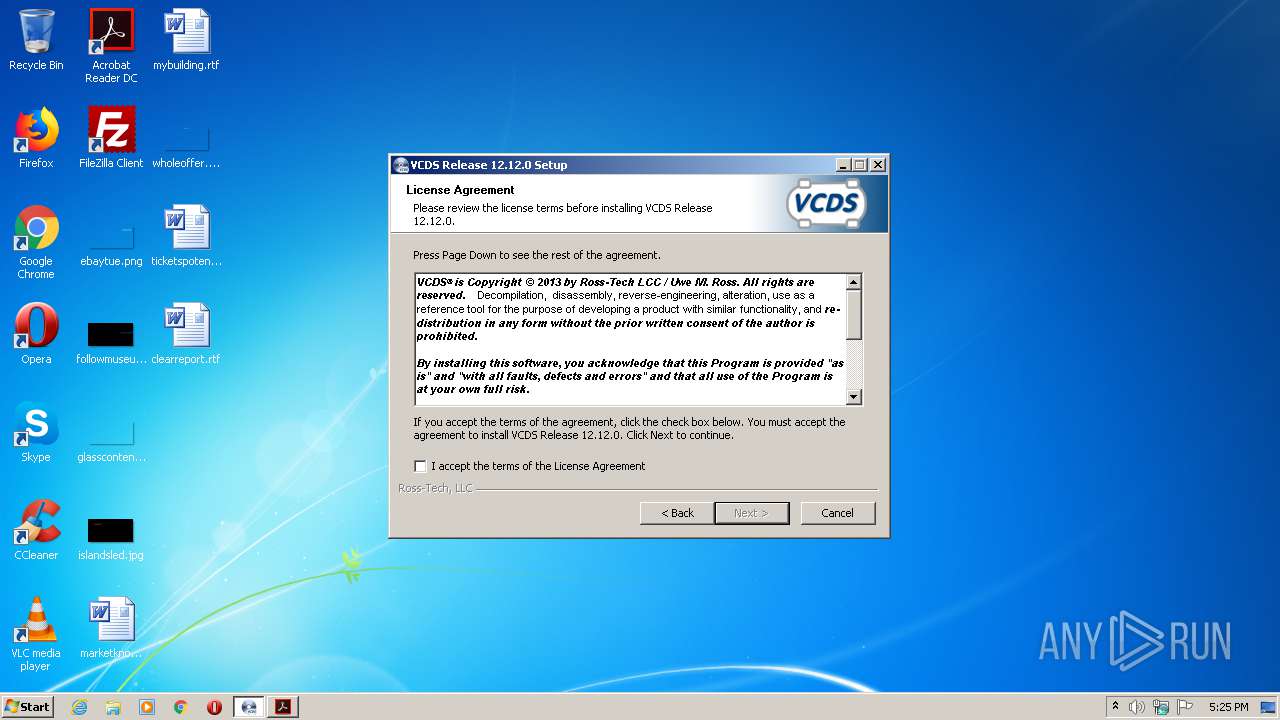
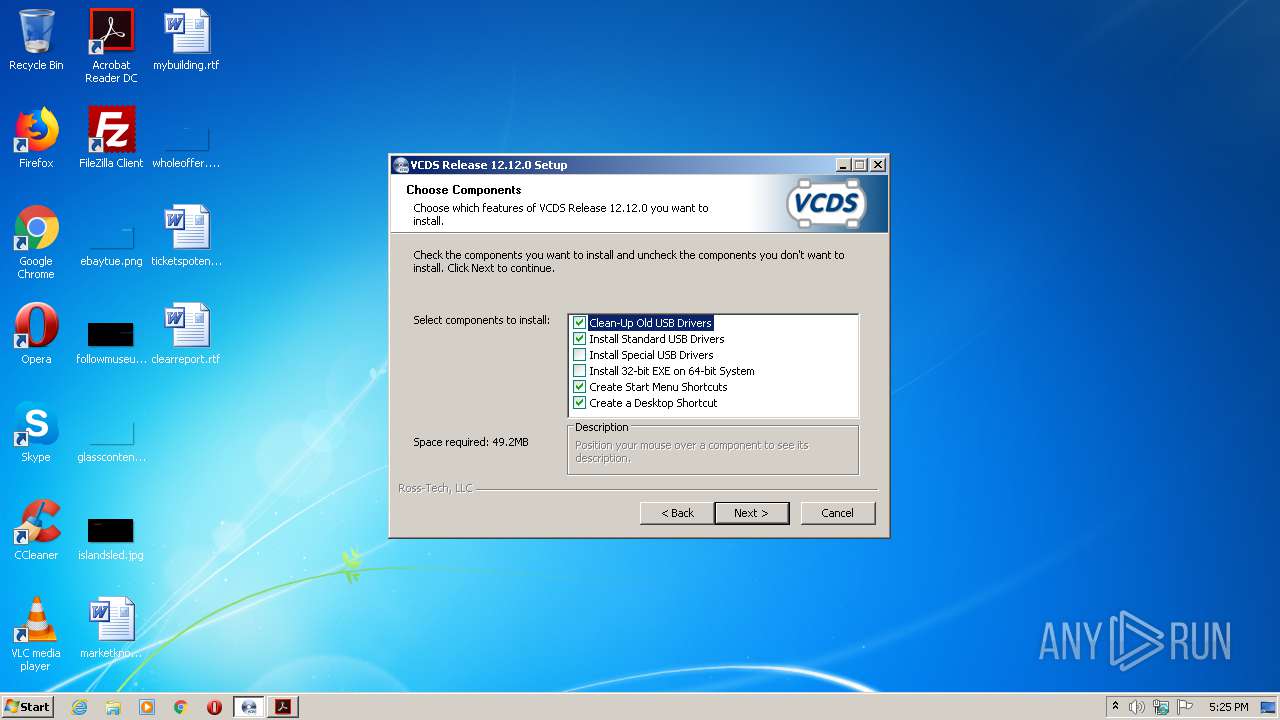
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A76BB8AD97EFF11E949158E00DE49C2F |
| SHA1: | F34366AE57AD7D6865852E3AA75BE528282C40D7 |
| SHA256: | D726EDC5A30E483702C4E094891557CD84062BFA4C50CEDAF906FB23D023ED90 |
| SSDEEP: | 393216:RV+0v2adZ2To0i8VGhPPty6nC0RYs8RoVb3CItsZqTl:n/uS8TunbNeoNS3q |
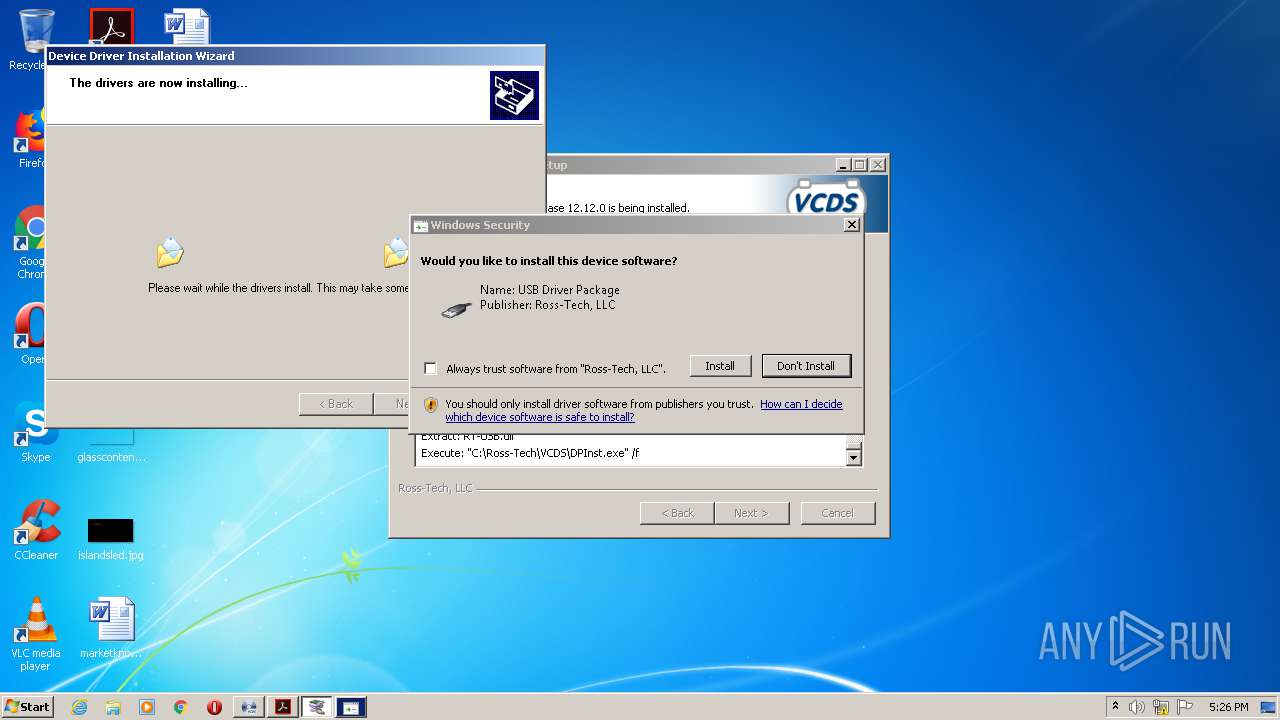
MALICIOUS
Loads dropped or rewritten executable
- vcds-release-12.12.0-installer.exe (PID: 2076)
Changes settings of System certificates
- AcroRd32.exe (PID: 3832)
- AdobeARM.exe (PID: 3524)
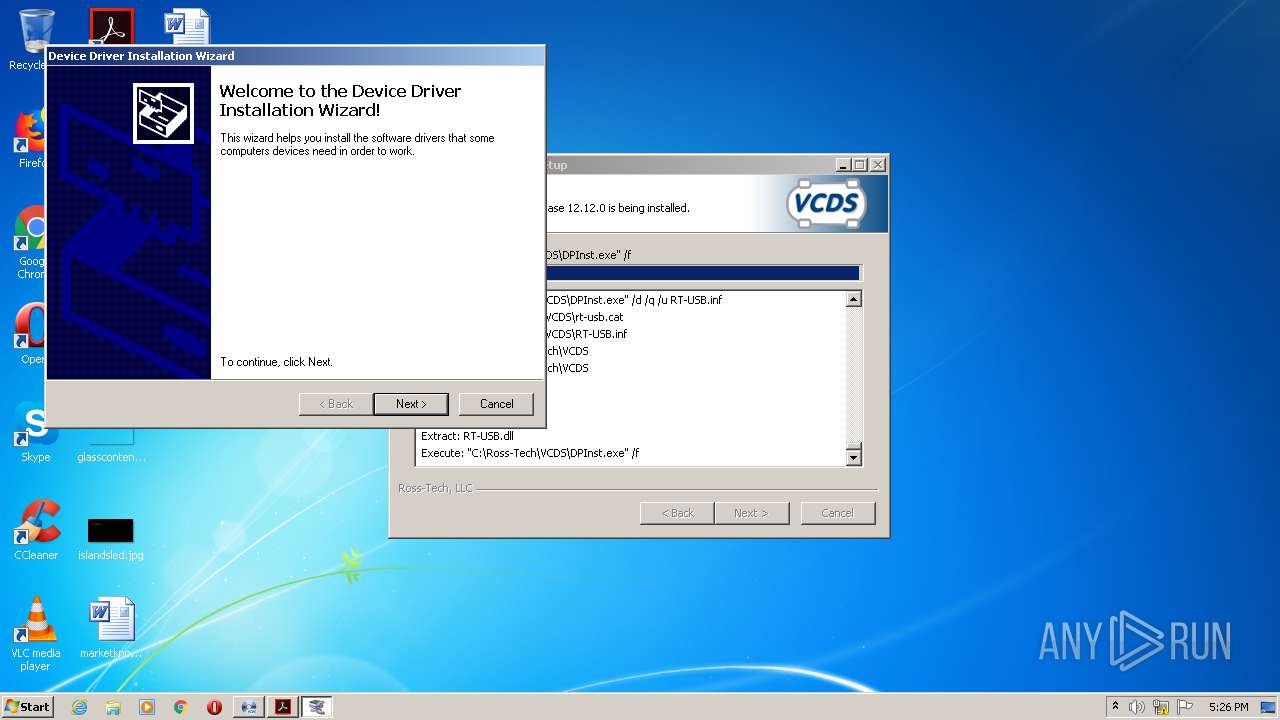
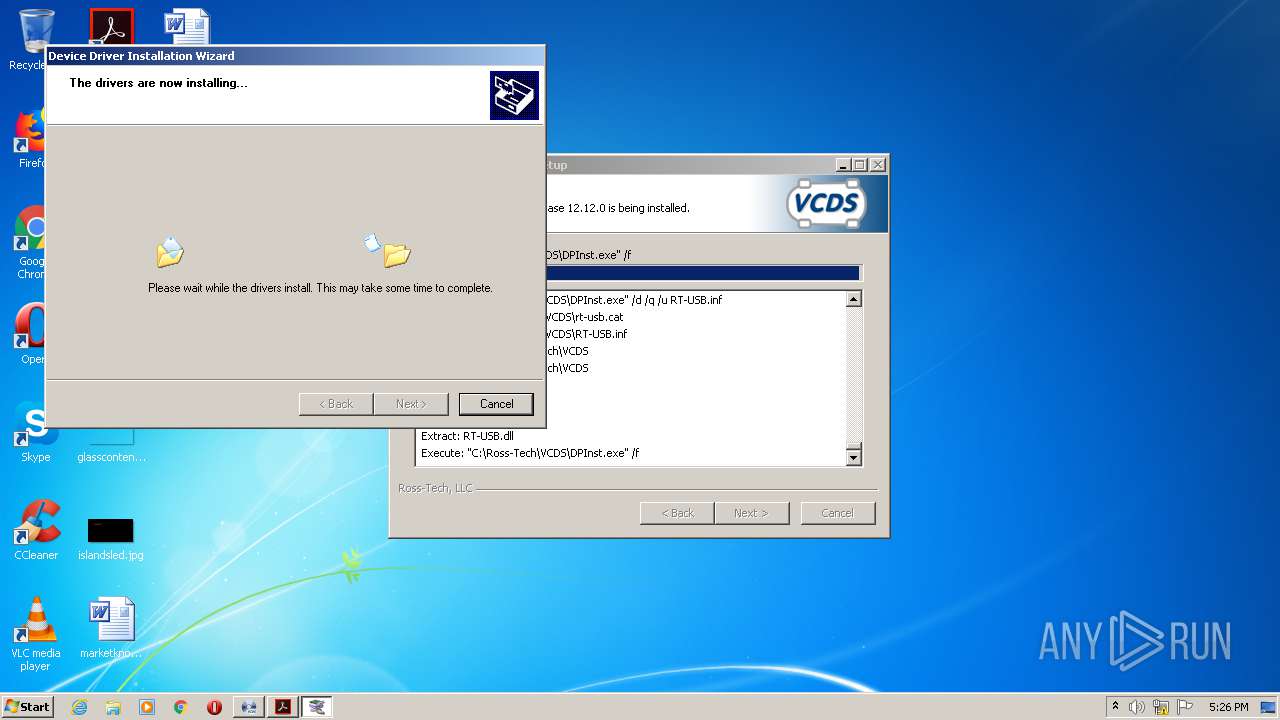
Application was dropped or rewritten from another process
- DPInst.exe (PID: 3896)
- DPInst.exe (PID: 544)
- DPInst.exe (PID: 1692)
- DPInst.exe (PID: 3148)
- DPInst.exe (PID: 2640)
- DPInst.exe (PID: 3048)
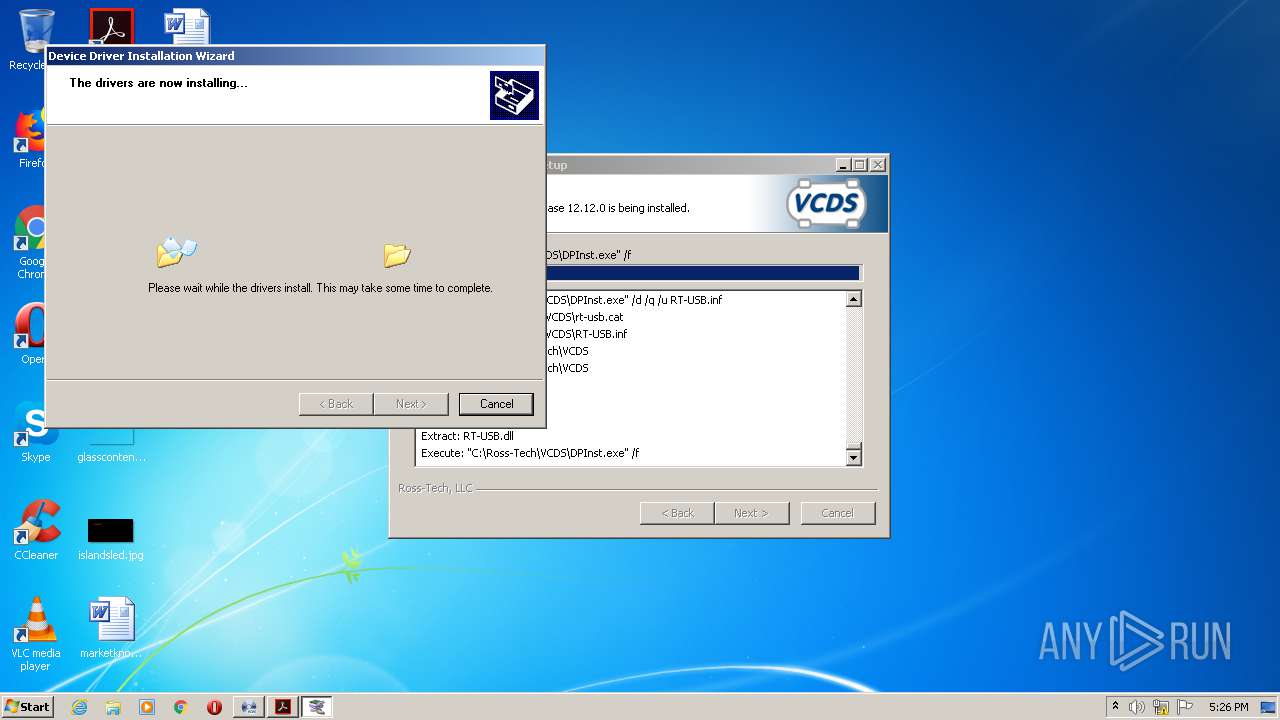
Drops executable file immediately after starts
- DrvInst.exe (PID: 3752)
SUSPICIOUS
Executable content was dropped or overwritten
- vcds-release-12.12.0-installer.exe (PID: 2076)
- DPInst.exe (PID: 3048)
- DrvInst.exe (PID: 3752)
Drops a file that was compiled in debug mode
- vcds-release-12.12.0-installer.exe (PID: 2076)
- DPInst.exe (PID: 3048)
- DrvInst.exe (PID: 3752)
Creates files in the Windows directory
- DPInst.exe (PID: 3896)
- DrvInst.exe (PID: 3752)
Adds / modifies Windows certificates
- AcroRd32.exe (PID: 3832)
- AdobeARM.exe (PID: 3524)
Drops a file with too old compile date
- vcds-release-12.12.0-installer.exe (PID: 2076)
Executed via COM
- DrvInst.exe (PID: 3752)
Removes files from Windows directory
- DrvInst.exe (PID: 3752)
Creates files in the driver directory
- DrvInst.exe (PID: 3752)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 3752)
Creates files in the program directory
- AdobeARM.exe (PID: 3524)
INFO
Reads the hosts file
- RdrCEF.exe (PID: 1672)
Changes IE settings (feature browser emulation)
- AcroRd32.exe (PID: 3832)
Application launched itself
- AcroRd32.exe (PID: 3832)
- RdrCEF.exe (PID: 1672)
Reads settings of System Certificates
- AcroRd32.exe (PID: 3832)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 3752)
Searches for installed software
- DrvInst.exe (PID: 3752)
Changes settings of System certificates
- DrvInst.exe (PID: 3752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
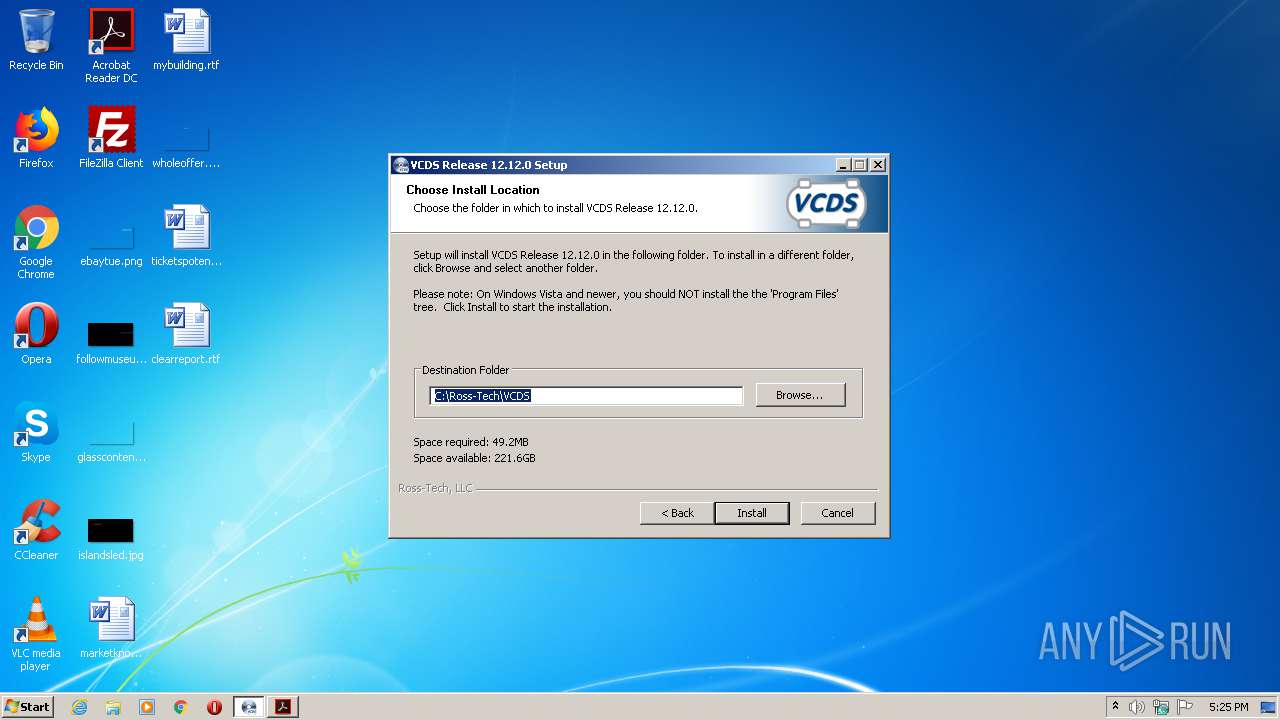
| ProductName: | VCDS |
|---|---|
| LegalCopyright: | Copyright (C) 2011 Ross-Tech, LLC |
| InstallerVersion: | v2.46 |
| FileVersion: | Release 12.12.0 |
| FileDescription: | VCDS Installer |
| CompanyName: | Ross-Tech, LLC |
| Comments: | Used to install VCDS Release 12.12.0 |
| CharacterSet: | ASCII |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x323c |
| UninitializedDataSize: | 1024 |
| InitializedDataSize: | 119808 |
| CodeSize: | 23552 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:46 |
| Detected languages: |
|
| Comments: | Used to install VCDS Release 12.12.0 |
| CompanyName: | Ross-Tech, LLC |
| FileDescription: | VCDS Installer |
| FileVersion: | Release 12.12.0 |
| InstallerVersion: | v2.46 |
| LegalCopyright: | Copyright (C) 2011 Ross-Tech, LLC |
| ProductName: | VCDS |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005A5A | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4177 |
.rdata | 0x00007000 | 0x00001190 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18163 |
.data | 0x00009000 | 0x0001AF98 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.70903 |
.ndata | 0x00024000 | 0x0000B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0002F000 | 0x000092E8 | 0x00009400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.83672 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10394 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.10768 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.92278 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 6.09046 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.41973 | 62 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.67866 | 344 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.68372 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
109 | 2.70146 | 212 | UNKNOWN | English - United States | RT_DIALOG |
110 | 2.82633 | 1638 | UNKNOWN | English - United States | RT_BITMAP |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
55
Monitored processes
17
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 544 | "C:\Ross-Tech\VCDS\DPInst.exe" /d /q /u RT-USB.inf | C:\Ross-Tech\VCDS\DPInst.exe | — | vcds-release-12.12.0-installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Exit code: 2147483648 Version: 2.1 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="1672.1.1916598720\1033987729" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: HIGH Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 1692 | "C:\Ross-Tech\VCDS\DPInst.exe" /d /q /u RT-USB.inf | C:\Ross-Tech\VCDS\DPInst.exe | — | vcds-release-12.12.0-installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Exit code: 2147483648 Version: 2.1 Modules
| |||||||||||||||
| 2076 | "C:\Users\admin\AppData\Local\Temp\vcds-release-12.12.0-installer.exe" | C:\Users\admin\AppData\Local\Temp\vcds-release-12.12.0-installer.exe | explorer.exe | ||||||||||||
User: admin Company: Ross-Tech, LLC Integrity Level: HIGH Description: VCDS Installer Exit code: 0 Version: Release 12.12.0 Modules
| |||||||||||||||
| 2376 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{6c9514b6-5073-3176-c7a0-ce036339ab5e} Global\{0c19b7f6-7d77-560b-866d-de5f3de57a10} C:\Windows\System32\DriverStore\Temp\{5b8a2559-8342-760e-b371-502bead09a73}\rt-usb.inf C:\Windows\System32\DriverStore\Temp\{5b8a2559-8342-760e-b371-502bead09a73}\RT-USB.CAT | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2640 | "C:\Ross-Tech\VCDS\DPInst.exe" /d /q /u RT-USB.inf | C:\Ross-Tech\VCDS\DPInst.exe | — | vcds-release-12.12.0-installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Exit code: 2147483648 Version: 2.1 Modules
| |||||||||||||||
| 3048 | "C:\Ross-Tech\VCDS\DPInst.exe" /f | C:\Ross-Tech\VCDS\DPInst.exe | vcds-release-12.12.0-installer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Exit code: 0 Version: 2.1 Modules
| |||||||||||||||
| 3148 | "C:\Ross-Tech\VCDS\DPInst.exe" /d /q /u RT-USB.inf | C:\Ross-Tech\VCDS\DPInst.exe | — | vcds-release-12.12.0-installer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Driver Package Installer Exit code: 2147483648 Version: 2.1 Modules
| |||||||||||||||
| 3436 | "C:\Users\admin\AppData\Local\Temp\vcds-release-12.12.0-installer.exe" | C:\Users\admin\AppData\Local\Temp\vcds-release-12.12.0-installer.exe | — | explorer.exe | |||||||||||
User: admin Company: Ross-Tech, LLC Integrity Level: MEDIUM Description: VCDS Installer Exit code: 3221226540 Version: Release 12.12.0 Modules
| |||||||||||||||
Total events
809
Read events
674
Write events
134
Delete events
1
Modification events
| (PID) Process: | (3836) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\ExitSection |
| Operation: | write | Name: | bLastExitNormal |
Value: 0 | |||
| (PID) Process: | (3832) AcroRd32.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Acrobatbrokerserverdispatchercpp789 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (3836) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Acrobat Reader\DC\AVGeneral |
| Operation: | write | Name: | bExpandRHPInViewer |
Value: 1 | |||
| (PID) Process: | (3832) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main\FeatureControl\FEATURE_BROWSER_EMULATION |
| Operation: | write | Name: | AcroRd32.exe |
Value: 10001 | |||
| (PID) Process: | (3832) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3832) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3832) AcroRd32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3832) AcroRd32.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\A8985D3A65E5E5C4B2D7D66D40C6DD2FB19C5436 |
| Operation: | write | Name: | Blob |
Value: 04000000010000001000000079E4A9840D7D3A96D7C04FE2434C892E0F0000000100000014000000B34DDD372ED92E8F2ABFBB9E20A9D31F204F194B030000000100000014000000A8985D3A65E5E5C4B2D7D66D40C6DD2FB19C54361D000000010000001000000059779E39E21A2E3DFCED6857ED5C5FD90B000000010000001200000044006900670069004300650072007400000014000000010000001400000003DE503556D14CBB66F0A3E21B1BC397B23DD1556200000001000000200000004348A0E9444C78CB265E058D5E8944B4D84F9662BD26DB257F8934A443C701615300000001000000230000003021301F06096086480186FD6C020130123010060A2B0601040182373C0101030200C0090000000100000034000000303206082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030306082B060105050703081900000001000000100000000F3A0527D242DE2DC98E5CFCB1E991EE2000000001000000B3030000308203AF30820297A0030201020210083BE056904246B1A1756AC95991C74A300D06092A864886F70D01010505003061310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D3120301E06035504031317446967694365727420476C6F62616C20526F6F74204341301E170D3036313131303030303030305A170D3331313131303030303030305A3061310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D3120301E06035504031317446967694365727420476C6F62616C20526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100E23BE11172DEA8A4D3A357AA50A28F0B7790C9A2A5EE12CE965B010920CC0193A74E30B753F743C46900579DE28D22DD870640008109CECE1B83BFDFCD3B7146E2D666C705B37627168F7B9E1E957DEEB748A308DAD6AF7A0C3906657F4A5D1FBC17F8ABBEEE28D7747F7A78995985686E5C23324BBF4EC0E85A6DE370BF7710BFFC01F685D9A844105832A97518D5D1A2BE47E2276AF49A33F84908608BD45FB43A84BFA1AA4A4C7D3ECF4F5F6C765EA04B37919EDC22E66DCE141A8E6ACBFECDB3146417C75B299E32BFF2EEFAD30B42D4ABB74132DA0CD4EFF881D5BB8D583FB51BE84928A270DA3104DDF7B216F24C0A4E07A8ED4A3D5EB57FA390C3AF270203010001A3633061300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E0416041403DE503556D14CBB66F0A3E21B1BC397B23DD155301F0603551D2304183016801403DE503556D14CBB66F0A3E21B1BC397B23DD155300D06092A864886F70D01010505000382010100CB9C37AA4813120AFADD449C4F52B0F4DFAE04F5797908A32418FC4B2B84C02DB9D5C7FEF4C11F58CBB86D9C7A74E79829AB11B5E370A0A1CD4C8899938C9170E2AB0F1CBE93A9FF63D5E40760D3A3BF9D5B09F1D58EE353F48E63FA3FA7DBB466DF6266D6D16E418DF22DB5EA774A9F9D58E22B59C04023ED2D2882453E7954922698E08048A837EFF0D6796016DEACE80ECD6EAC4417382F49DAE1453E2AB93653CF3A5006F72EE8C457496C612118D504AD783C2C3A806BA7EBAF1514E9D889C1B9386CE2916C8AFF64B977255730C01B24A3E1DCE9DF477CB5B424080530EC2DBD0BBF45BF50B9A9F3EB980112ADC888C698345F8D0A3CC6E9D595956DDE | |||
| (PID) Process: | (3836) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Adobe Acrobat\DC\DiskCabs |
| Operation: | write | Name: | bForms_AdhocWorkflowBackup |
Value: 0 | |||
| (PID) Process: | (3836) AcroRd32.exe | Key: | HKEY_CURRENT_USER\Software\Adobe\Adobe Acrobat\DC\DiskCabs |
| Operation: | write | Name: | bJSCache_GlobData |
Value: 1 | |||
Executable files
14
Suspicious files
423
Text files
4 198
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3836 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 3836 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\Cache\AdobeFnt16.lst.3836 | — | |
MD5:— | SHA256:— | |||
| 3836 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\AdobeFnt16.lst.3836 | — | |
MD5:— | SHA256:— | |||
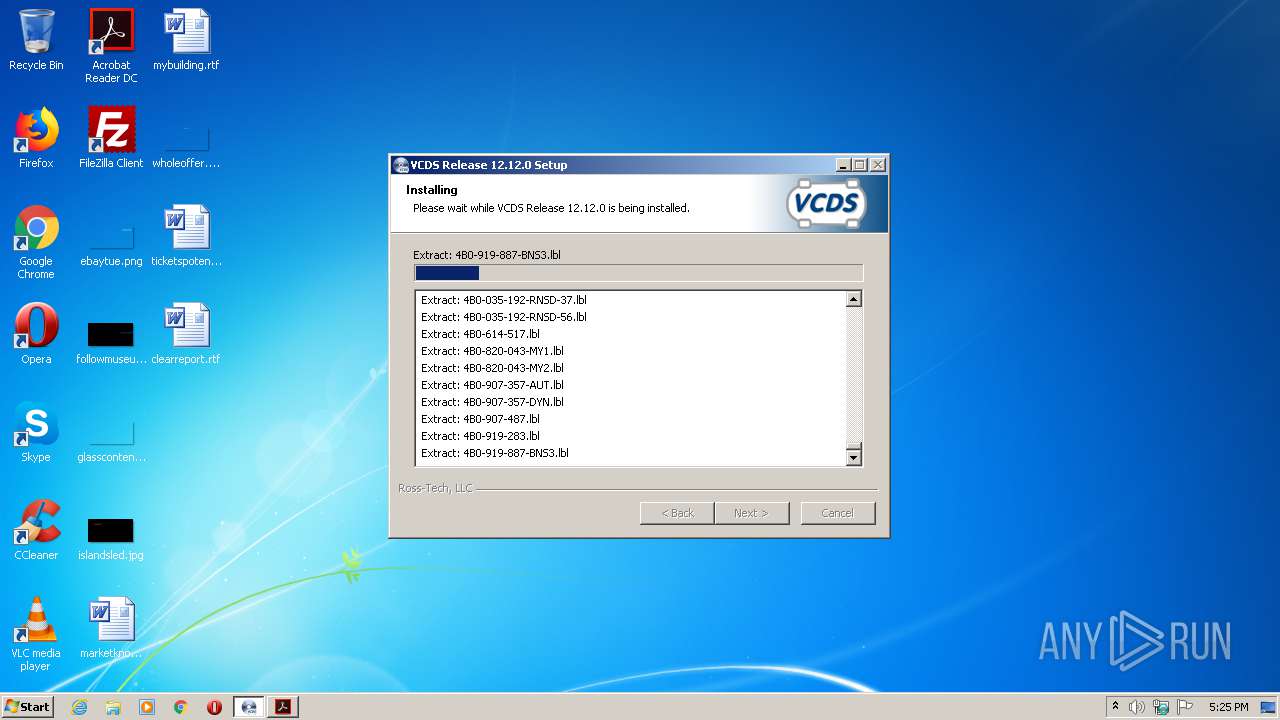
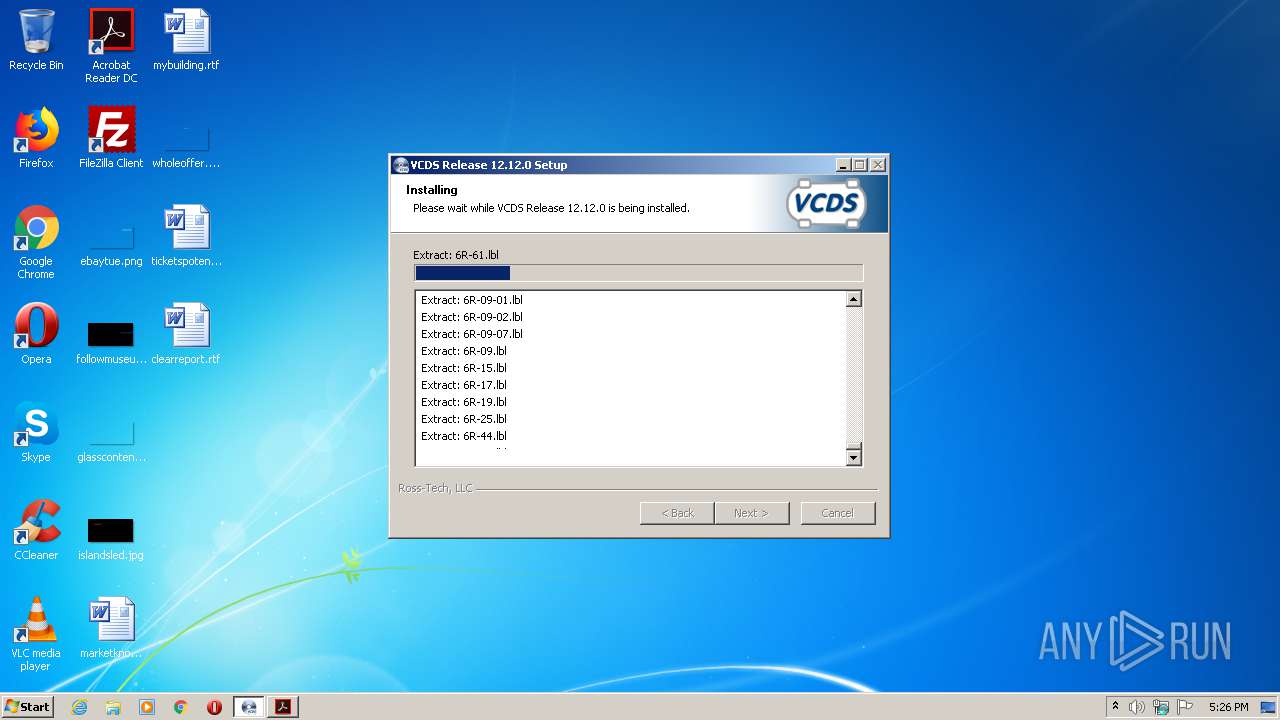
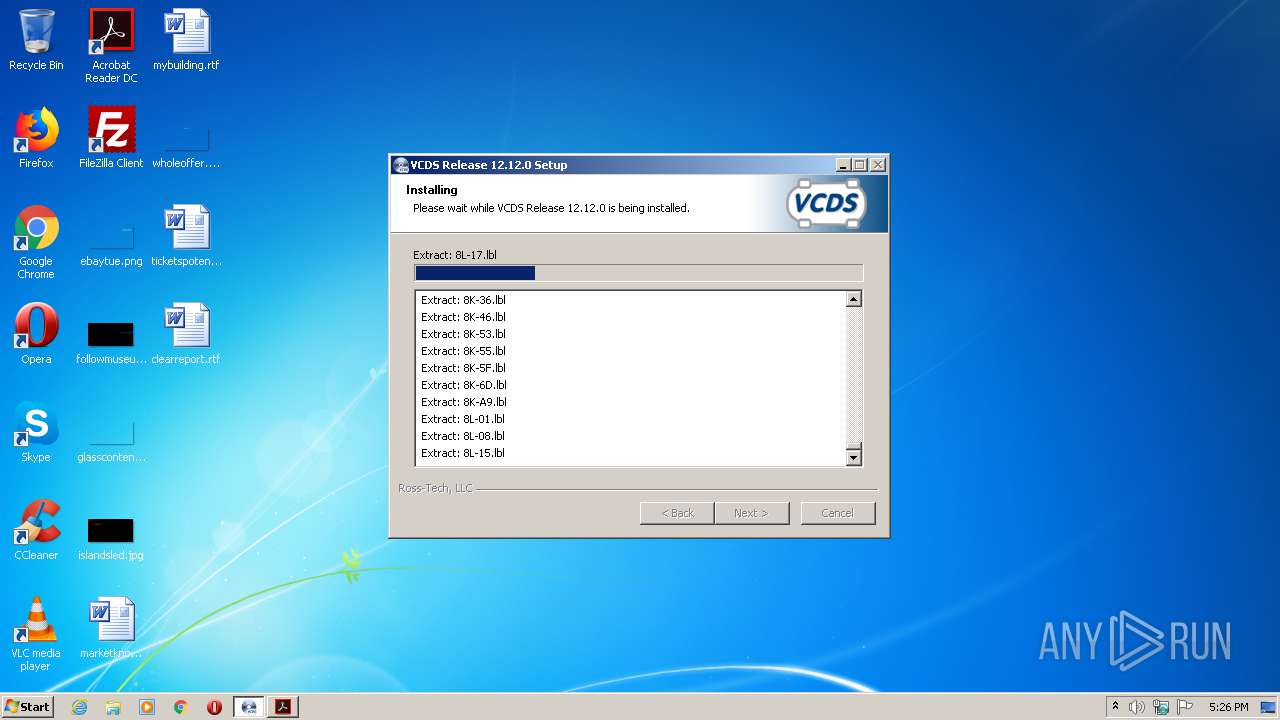
| 2076 | vcds-release-12.12.0-installer.exe | C:\Ross-Tech\VCDS\HN116.bin | binary | |
MD5:— | SHA256:— | |||
| 2076 | vcds-release-12.12.0-installer.exe | C:\Ross-Tech\VCDS\LCode.ini | text | |
MD5:— | SHA256:— | |||
| 2076 | vcds-release-12.12.0-installer.exe | C:\Ross-Tech\VCDS\HCC192.bin | binary | |
MD5:— | SHA256:— | |||
| 2076 | vcds-release-12.12.0-installer.exe | C:\Ross-Tech\VCDS\VCDS-32.exe | — | |
MD5:— | SHA256:— | |||
| 2076 | vcds-release-12.12.0-installer.exe | C:\Ross-Tech\VCDS\LCode.exe | executable | |
MD5:— | SHA256:— | |||
| 3832 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\AdobeSysFnt15.lst | ps | |
MD5:— | SHA256:— | |||
| 2076 | vcds-release-12.12.0-installer.exe | C:\Ross-Tech\VCDS\HP192.bin | bs | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
6
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3832 | AcroRd32.exe | GET | 304 | 2.16.107.49:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
3832 | AcroRd32.exe | GET | 304 | 2.16.107.49:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
3832 | AcroRd32.exe | GET | 304 | 2.16.107.49:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
3832 | AcroRd32.exe | GET | 304 | 2.16.107.49:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/278_15_23_20070.zip | unknown | — | — | whitelisted |
3832 | AcroRd32.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
3832 | AcroRd32.exe | GET | 200 | 2.16.107.49:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | compressed | 9.54 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.16.107.49:80 | acroipm2.adobe.com | Akamai International B.V. | — | suspicious |
3832 | AcroRd32.exe | 2.16.107.49:80 | acroipm2.adobe.com | Akamai International B.V. | — | suspicious |
3832 | AcroRd32.exe | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
— | — | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
3832 | AcroRd32.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |