| File name: | Luczystrap.exe |
| Full analysis: | https://app.any.run/tasks/31a35a9f-c70a-42bf-a180-2a2733f15f77 |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2025, 21:57:57 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 10 sections |
| MD5: | 3C9C66D70BD0E4F260BAA74EC9108EEA |
| SHA1: | C4EA77FD838EA882716515AAE5548999CB2252FA |
| SHA256: | D71C31057677BC392F680C6303DCFDA9FA8F366240284DAC6D5A14F7CC352424 |
| SSDEEP: | 393216:3U4FNAGOicBQlKd7L9NvtiNFoL0Fn1jioDTfVL8pAU9TZyaerkBrsuLAZBWF2:3vNAti0nNvtfqjLDTmTEdQBrJkQ2 |
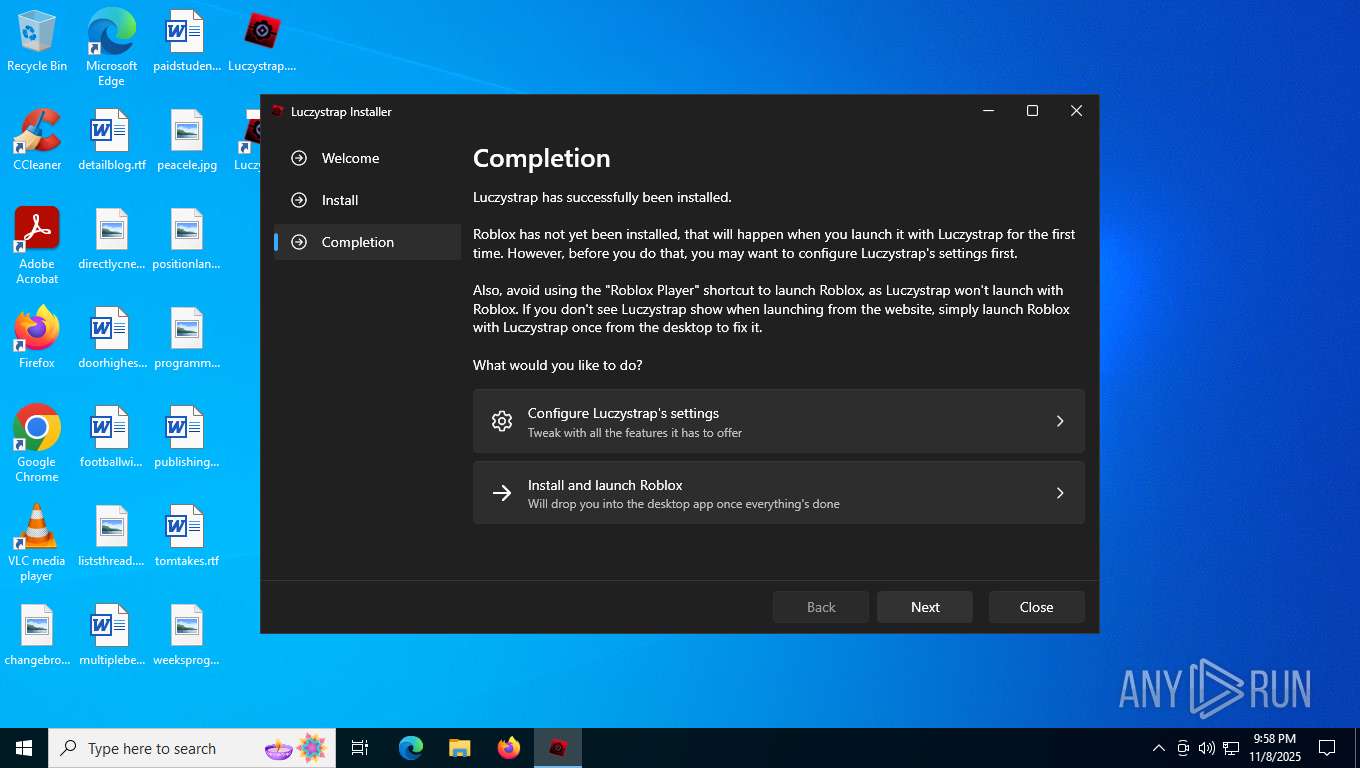
MALICIOUS
GENERIC has been found (auto)
- Luczystrap.exe (PID: 7888)
SUSPICIOUS
The process creates files with name similar to system file names
- Luczystrap.exe (PID: 7888)
Process drops legitimate windows executable
- Luczystrap.exe (PID: 7888)
Executable content was dropped or overwritten
- Luczystrap.exe (PID: 7888)
The process drops C-runtime libraries
- Luczystrap.exe (PID: 7888)
Reads security settings of Internet Explorer
- Luczystrap.exe (PID: 7888)
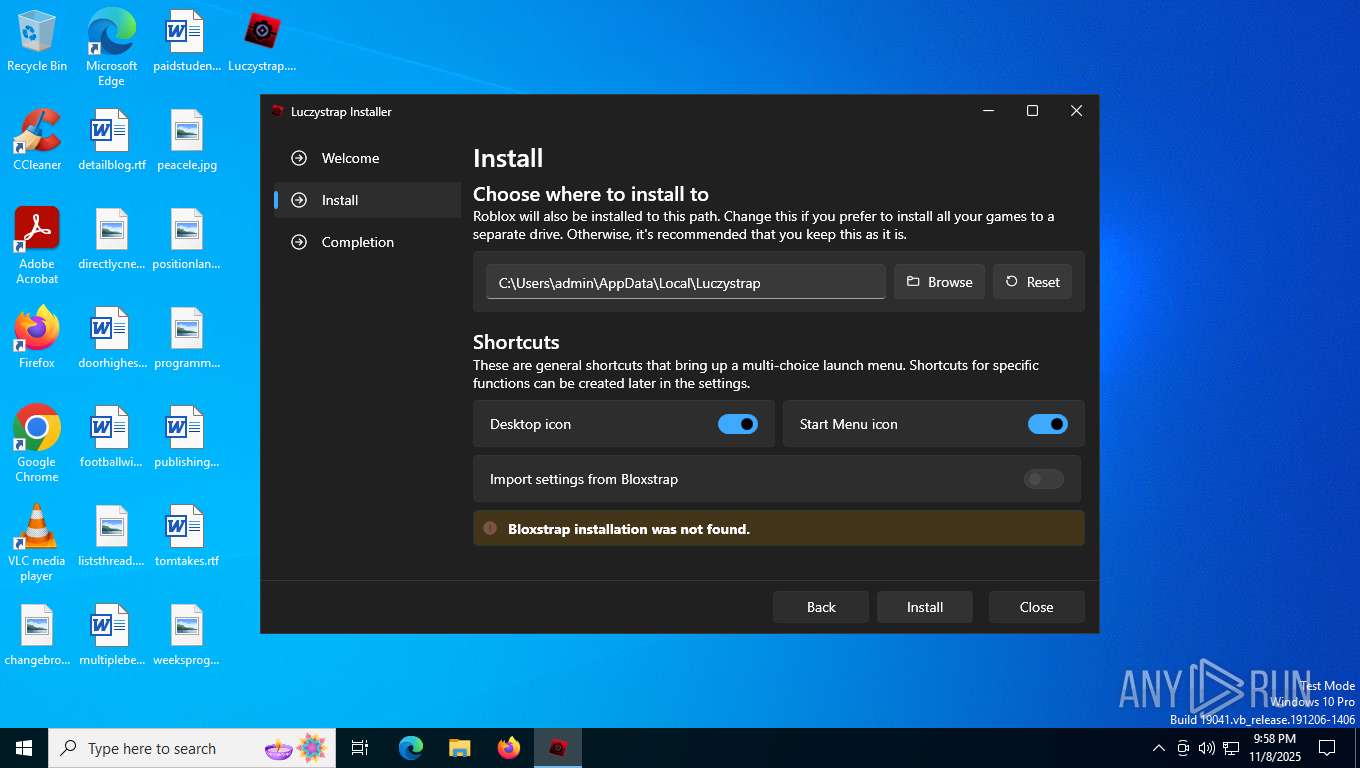
Searches for installed software
- Luczystrap.exe (PID: 7888)
Possible usage of Discord/Telegram API has been detected (YARA)
- Luczystrap.exe (PID: 7888)
INFO
Create files in a temporary directory
- Luczystrap.exe (PID: 7888)
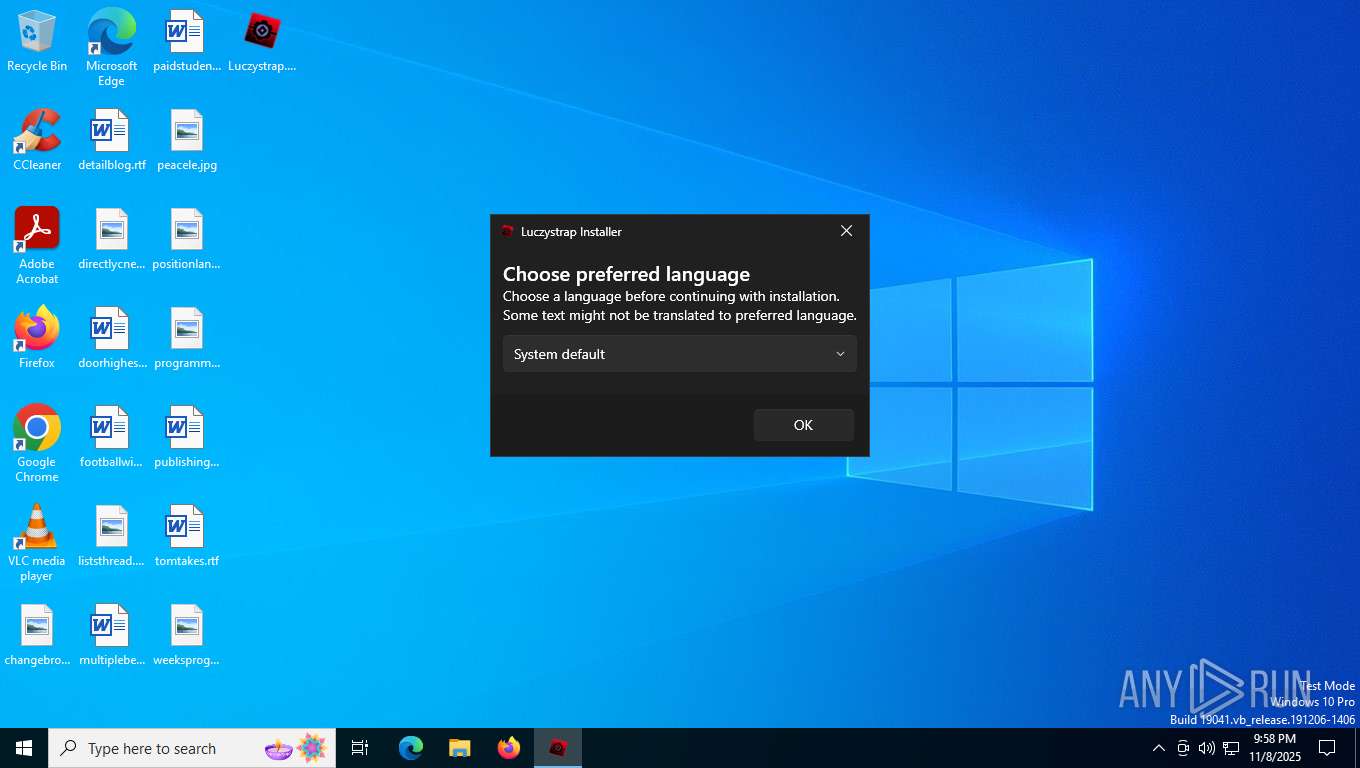
Checks supported languages
- Luczystrap.exe (PID: 7888)
The sample compiled with english language support
- Luczystrap.exe (PID: 7888)
Creates files in the program directory
- Luczystrap.exe (PID: 7888)
Process checks computer location settings
- Luczystrap.exe (PID: 7888)
Reads the computer name
- Luczystrap.exe (PID: 7888)
Creates files or folders in the user directory
- Luczystrap.exe (PID: 7888)
Creates a software uninstall entry
- Luczystrap.exe (PID: 7888)
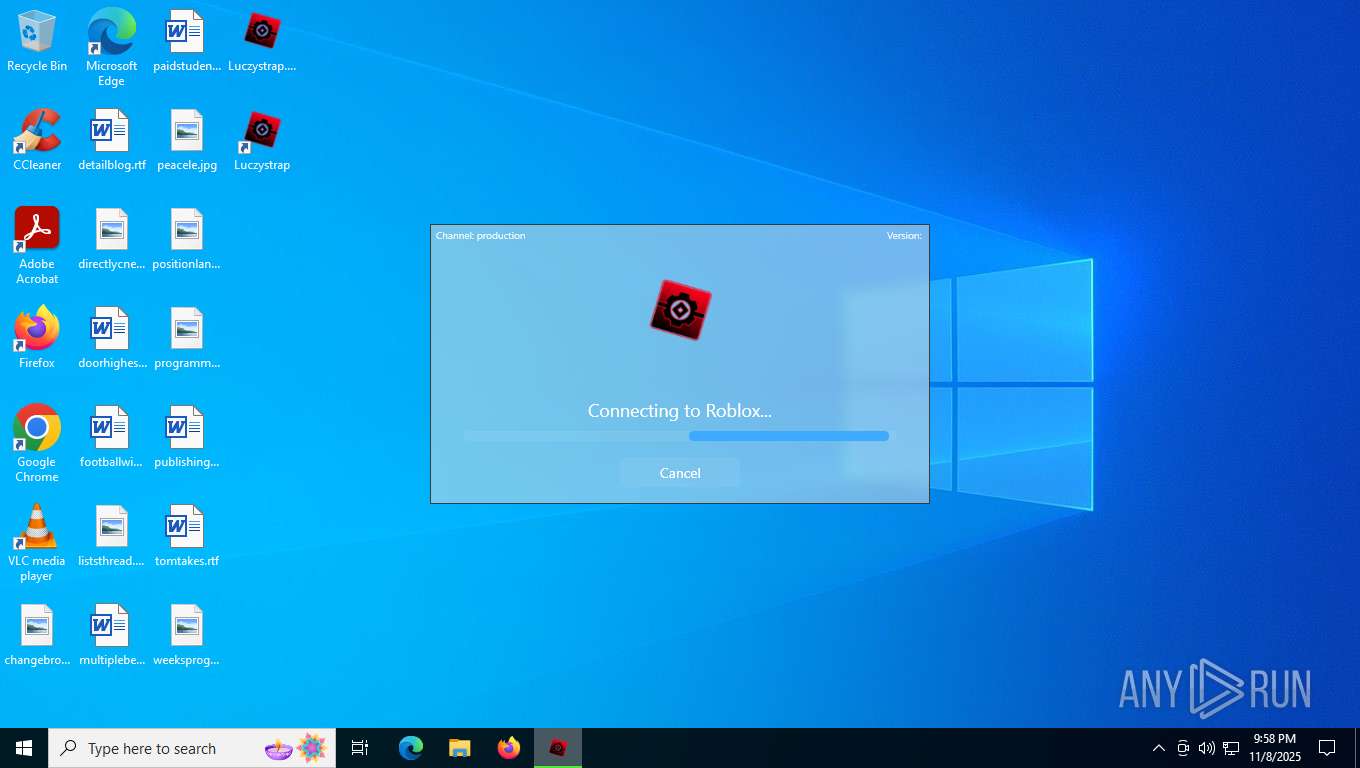
ROBLOX mutex has been found
- Luczystrap.exe (PID: 7888)
Reads the software policy settings
- Luczystrap.exe (PID: 7888)
- slui.exe (PID: 6992)
Checks proxy server information
- Luczystrap.exe (PID: 7888)
- slui.exe (PID: 6992)
Reads the machine GUID from the registry
- Luczystrap.exe (PID: 7888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(7888) Luczystrap.exe
Discord-Webhook-Tokens (1)1435648454318887056/q5OwTDzKE-uqT6iP0KzzJr0Y4kiyXvB0KpjJljbNYLVfMoXkYQv7wr_gFNyriq4yh7A5
Discord-Info-Links
1435648454318887056/q5OwTDzKE-uqT6iP0KzzJr0Y4kiyXvB0KpjJljbNYLVfMoXkYQv7wr_gFNyriq4yh7A5
Get Webhook Infohttps://discord.com/api/webhooks/1435648454318887056/q5OwTDzKE-uqT6iP0KzzJr0Y4kiyXvB0KpjJljbNYLVfMoXkYQv7wr_gFNyriq4yh7A5
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:09:25 19:23:21+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.44 |
| CodeSize: | 6348288 |
| InitializedDataSize: | 3501568 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5c30d0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.4.9.0 |
| ProductVersionNumber: | 1.4.9.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
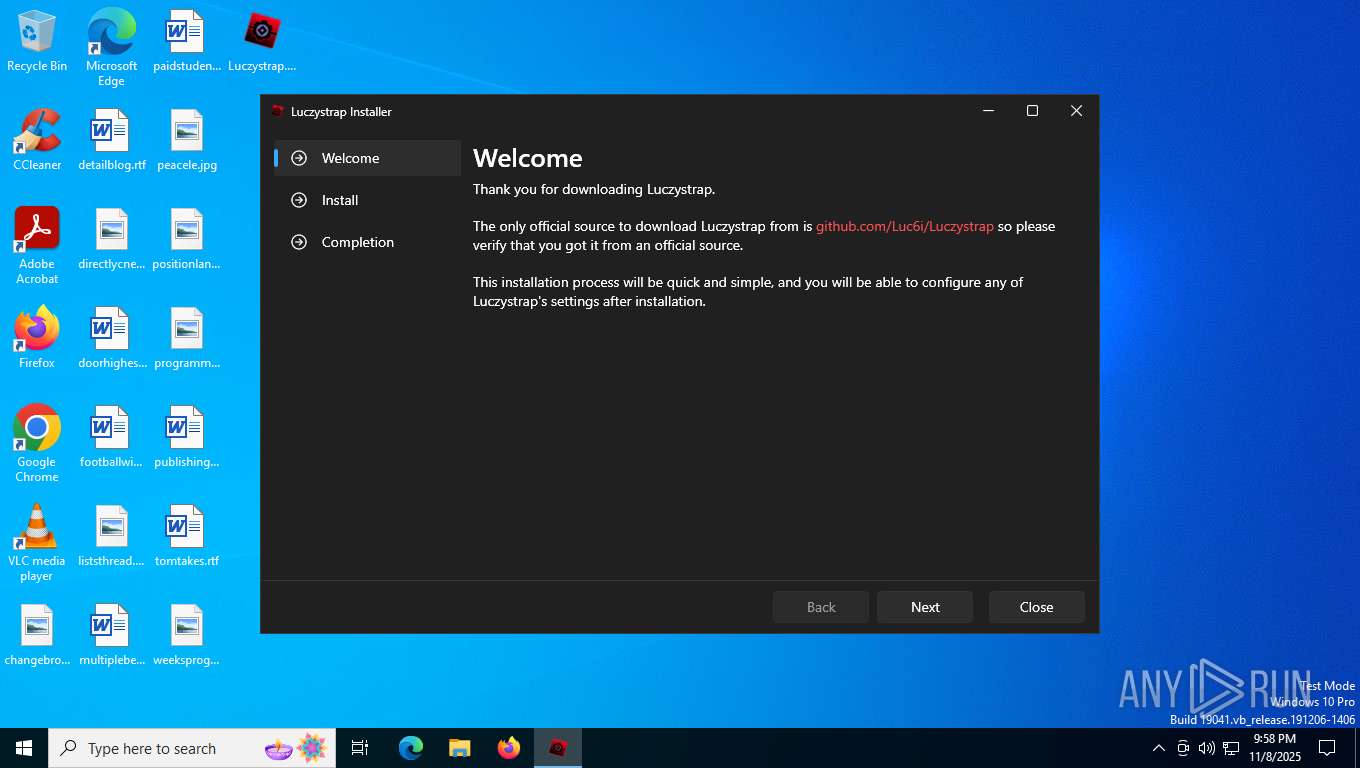
| CompanyName: | Luczystrap |
| FileDescription: | Luczystrap |
| FileVersion: | 1.4.9 |
| InternalName: | Luczystrap.dll |
| LegalCopyright: | |
| OriginalFileName: | Luczystrap.dll |
| ProductName: | Luczystrap |
| ProductVersion: | 1.4.9 |
| AssemblyVersion: | 1.4.9.0 |
Total processes
134
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6992 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7888 | "C:\Users\admin\Desktop\Luczystrap.exe" | C:\Users\admin\Desktop\Luczystrap.exe | explorer.exe | ||||||||||||
User: admin Company: Luczystrap Integrity Level: MEDIUM Description: Luczystrap Version: 1.4.9 Modules
ims-api(PID) Process(7888) Luczystrap.exe Discord-Webhook-Tokens (1)1435648454318887056/q5OwTDzKE-uqT6iP0KzzJr0Y4kiyXvB0KpjJljbNYLVfMoXkYQv7wr_gFNyriq4yh7A5 Discord-Info-Links 1435648454318887056/q5OwTDzKE-uqT6iP0KzzJr0Y4kiyXvB0KpjJljbNYLVfMoXkYQv7wr_gFNyriq4yh7A5 Get Webhook Infohttps://discord.com/api/webhooks/1435648454318887056/q5OwTDzKE-uqT6iP0KzzJr0Y4kiyXvB0KpjJljbNYLVfMoXkYQv7wr_gFNyriq4yh7A5 | |||||||||||||||
Total events
7 468
Read events
7 449
Write events
19
Delete events
0
Modification events
| (PID) Process: | (7888) Luczystrap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Luczystrap |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\Luczystrap\Luczystrap.exe,0 | |||
| (PID) Process: | (7888) Luczystrap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Luczystrap |
| Operation: | write | Name: | DisplayName |
Value: Luczystrap | |||
| (PID) Process: | (7888) Luczystrap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Luczystrap |
| Operation: | write | Name: | DisplayVersion |
Value: 1.4.9.0 | |||
| (PID) Process: | (7888) Luczystrap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Luczystrap |
| Operation: | write | Name: | InstallDate |
Value: 20251108 | |||
| (PID) Process: | (7888) Luczystrap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Luczystrap |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Luczystrap | |||
| (PID) Process: | (7888) Luczystrap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Luczystrap |
| Operation: | write | Name: | ModifyPath |
Value: "C:\Users\admin\AppData\Local\Luczystrap\Luczystrap.exe" -menu | |||
| (PID) Process: | (7888) Luczystrap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Luczystrap |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Users\admin\AppData\Local\Luczystrap\Luczystrap.exe" -uninstall -quiet | |||
| (PID) Process: | (7888) Luczystrap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Luczystrap |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Local\Luczystrap\Luczystrap.exe" -uninstall | |||
| (PID) Process: | (7888) Luczystrap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Luczystrap |
| Operation: | write | Name: | NoModify |
Value: 0 | |||
| (PID) Process: | (7888) Luczystrap.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Luczystrap |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
Executable files
278
Suspicious files
9
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7888 | Luczystrap.exe | C:\Users\admin\AppData\Local\Temp\.net\Luczystrap\1ed0\de\Luczystrap.resources.dll | executable | |
MD5:6B0088F1586457F9E418C08997814243 | SHA256:7CDF49405673FA0295991E29CEC684173AF261C9B294C6F3908E47B1855E8B2F | |||
| 7888 | Luczystrap.exe | C:\Users\admin\AppData\Local\Temp\.net\Luczystrap\1ed0\License - Fluent System Icons.txt | text | |
MD5:F225F140316A29CBE720CBC0CD7C258D | SHA256:9BE360C19BF5502C7927A6CA365A7504B620B408CDF6E3E2413FA63A325BD381 | |||
| 7888 | Luczystrap.exe | C:\Users\admin\AppData\Local\Temp\.net\Luczystrap\1ed0\License - Segoe Fluent Icons.txt | text | |
MD5:9ED1459E7AB3A73649F91CAFC7179B07 | SHA256:9E90BA20D2288CE1625E6126A9BCA3E1FC26B38F85620D1F92201A165001813F | |||
| 7888 | Luczystrap.exe | C:\Users\admin\AppData\Local\Temp\.net\Luczystrap\1ed0\es-ES\Luczystrap.resources.dll | executable | |
MD5:7691BCBC9A474F61AB6E895A632F2FDC | SHA256:24E8C2522D4F405CBC5AF5F865B4239E24F3F3A8F007AC60CC98DDD5674FAB24 | |||
| 7888 | Luczystrap.exe | C:\Users\admin\AppData\Local\Temp\.net\Luczystrap\1ed0\bg\Luczystrap.resources.dll | executable | |
MD5:DAAEF2E7EC64B6559EEFA199DB57B863 | SHA256:C20450FAF22FD56EF7E6B470A2F9FFE9E663469A27BEEBF6A3B275ECEBCE649A | |||
| 7888 | Luczystrap.exe | C:\Users\admin\AppData\Local\Temp\.net\Luczystrap\1ed0\License - VirtualizingWrapPanel.txt | text | |
MD5:635E513603C28BB55AC3010B68C77808 | SHA256:3EB591915F953D90D661B6CF89F347F1DD295FAB85E8E3FF4C761B727DBEA799 | |||
| 7888 | Luczystrap.exe | C:\Users\admin\AppData\Local\Temp\.net\Luczystrap\1ed0\Luczystrap.runtimeconfig.json | binary | |
MD5:394D97D8E1185DB1D1E5672511ED5774 | SHA256:EAEFCEC287B085437AD735F2A7715E2097676BE3333A480DB6C77B2866B836F2 | |||
| 7888 | Luczystrap.exe | C:\Users\admin\AppData\Local\Temp\.net\Luczystrap\1ed0\bs\Luczystrap.resources.dll | executable | |
MD5:8305AD967F85F4720FB9E30C6F5A57D6 | SHA256:52ACC4263DB7979D50904A501EF8DC0320A9CFE58B8721E1FFB84A3D87FF53B6 | |||
| 7888 | Luczystrap.exe | C:\Users\admin\AppData\Local\Temp\.net\Luczystrap\1ed0\cs\Luczystrap.resources.dll | executable | |
MD5:A6AC596E9B113195CA091FDD3FBF7613 | SHA256:E8450BFDE8EAC7DFC2AA67566FE23E0F797C93D68B4516AEA646AB5FB03FBC87 | |||
| 7888 | Luczystrap.exe | C:\Users\admin\AppData\Local\Temp\.net\Luczystrap\1ed0\fil\Luczystrap.resources.dll | executable | |
MD5:B4402AA476B3FAFF1FCF2BE8CF4A229B | SHA256:6F10691ED949C1B0A801BA34FF7E187728522B135CE6228B533F6AD0678F4E84 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
25
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6416 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5596 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.201.250.50:443 | https://clientsettingscdn.roblox.com/v2/client-version/WindowsPlayer | unknown | binary | 119 b | unknown |
— | — | GET | 200 | 140.82.121.5:443 | https://api.github.com/repos/Luc6i/Luczystrap/releases/latest | unknown | binary | 10.1 Kb | unknown |
— | — | GET | 200 | 18.66.192.61:443 | https://setup.rbxcdn.com/version-f6dd34ecac7b4642-rbxPkgManifest.txt | unknown | — | — | unknown |
— | — | POST | 204 | 2.16.204.153:443 | https://www.bing.com/web/xlsc.aspx?t=5&dl=1&wsbc=1 | unknown | — | — | unknown |
— | — | GET | — | 18.66.192.123:443 | https://setup.rbxcdn.com/version-f6dd34ecac7b4642-RobloxApp.zip | unknown | — | — | unknown |
— | — | POST | — | 4.154.185.43:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | — | — | unknown |
— | — | GET | 200 | 18.66.192.61:443 | https://setup.rbxcdn.com/version | unknown | text | 24 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7088 | SearchApp.exe | 2.16.204.142:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
6416 | svchost.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5596 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
— | — | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
7888 | Luczystrap.exe | 54.192.35.27:443 | setup.rbxcdn.com | AMAZON-02 | US | whitelisted |
7888 | Luczystrap.exe | 140.82.121.6:443 | api.github.com | GITHUB | US | whitelisted |
7888 | Luczystrap.exe | 23.201.250.50:443 | clientsettingscdn.roblox.com | AKAMAI-AS | CH | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
setup.rbxcdn.com |
| whitelisted |
api.github.com |
| whitelisted |
clientsettingscdn.roblox.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |