| URL: | https://video-weaver.sea01.hls.ttvnw.net/v1/playlist/Cu0EHTF_W3CVkosJjJ5qDf1L0C8a_ZPfhNQzJyAiHXA1vxiDH03JDd0g2FIxEjzhzsbZB1ssSdzuGwhwvwyiFU4IeoQdEKd3c7CuPdX5cooAPYmZOBfpegDiCvpR2i5NgYmw7cOITRx9zbyDhLJBBdQSQGzE-bKg974MgOenoGq-IkfquQCnQsAZ1Nx-QEamjadcYZajaCdQHBSZcSdQKx93uBaBr_VoDKp_UqD5jUhBMejuIedX0ezESBLpWxMS8TN-AUjOVbVPQ-iwsuDGuckEsIIR_81Ld0w65-rQDktCwq3x73dwsDLPQBm18EAgoU9exvSl1j6yJgDhaiV7p3CDJq9ptGMvVO2UR50EbHt2YtiY-7CJOyfXcBk4lFLTO_yLsuV_s4SfsrjuZKk-6iv1cv3bEhgQ30WX0hKeUly-xu-iuLs_56O--ErGowedQxQvjfBHeWQbV78_riWSI5PohBAU2dpQJCZgd7mi0KvxIv2_qU55WrU1orYFEwRbTbqNsI881TnBYVsqMzEcQWjDw3T2qZe-UwQU-LP6oUMO9b0vkEGMqpLkpcxKC8Go-nf8ewB-yPjs_uPpeFE1uIqzmhkbR3E5I47vwG1Ak56pU07voQFPnStGXZXC6s9rXGS9-M-xZ1RlQOJfbZbZAlVNyEqoZkzJ93W-fTi6a3KDn8A9Idmoq17pOA6SDoQo1RSQdWu5jMURzUANKWORgKyYcBaxmfRCW4T39faxQ8PM3oorUcAYcPaQ_RtqkOyutotO_hSri_E-4rU2V-HNZP_3oK1vBfmH_vJlJouVLyde_ObgQfcfxt7i56K1QHYUEhCPH23eEKYcwPZeCtBAJ5b2GgxmFHytyQ87_9Namzo.m3u8;https://video-weaver.sea01.hls.ttvnw.net/v1/playlist/Cu0EHTF_W3CVkosJjJ5qDf1L0C8a_ZPfhNQzJyAiHXA1vxiDH03JDd0g2FIxEjzhzsbZB1ssSdzuGwhwvwyiFU4IeoQdEKd3c7CuPdX5cooAPYmZOBfpegDiCvpR2i5NgYmw7cOITRx9zbyDhLJBBdQSQGzE-bKg974MgOenoGq-IkfquQCnQsAZ1Nx-QEamjadcYZajaCdQHBSZcSdQKx93uBaBr_VoDKp_UqD5jUhBMejuIedX0ezESBLpWxMS8TN-AUjOVbVPQ-iwsuDGuckEsIIR_81Ld0w65-rQDktCwq3x73dwsDLPQBm18EAgoU9exvSl1j6yJgDhaiV7p3CDJq9ptGMvVO2UR50EbHt2YtiY-7CJOyfXcBk4lFLTO_yLsuV_s4SfsrjuZKk-6iv1cv3bEhgQ30WX0hKeUly-xu-iuLs_56O--ErGowedQxQvjfBHeWQbV78_riWSI5PohBAU2dpQJCZgd7mi0KvxIv2_qU55WrU1orYFEwRbTbqNsI881TnBYVsqMzEcQWjDw3T2qZe-UwQU-LP6oUMO9b0vkEGMqpLkpcxKC8Go-nf8ewB-yPjs_uPpeFE1uIqzmhkbR3E5I47vwG1Ak56pU07voQFPnStGXZXC6s9rXGS9-M-xZ1RlQOJfbZbZAlVNyEqoZkzJ93W-fTi6a3KDn8A9Idmoq17pOA6SDoQo1RSQdWu5jMURzUANKWORgKyYcBaxmfRCW4T39faxQ8PM3oorUcAYcPaQ_RtqkOyutotO_hSri_E-4rU2V-HNZP_3oK1vBfmH_vJlJouVLyde_ObgQfcfxt7i56K1QHYUEhCPH23eEKYcwPZeCtBAJ5b2GgxmFHytyQ87_9Namzo.m3u8 |
| Full analysis: | https://app.any.run/tasks/dd4cc4c1-dd52-45d7-994e-c6aa0304c5d0 |
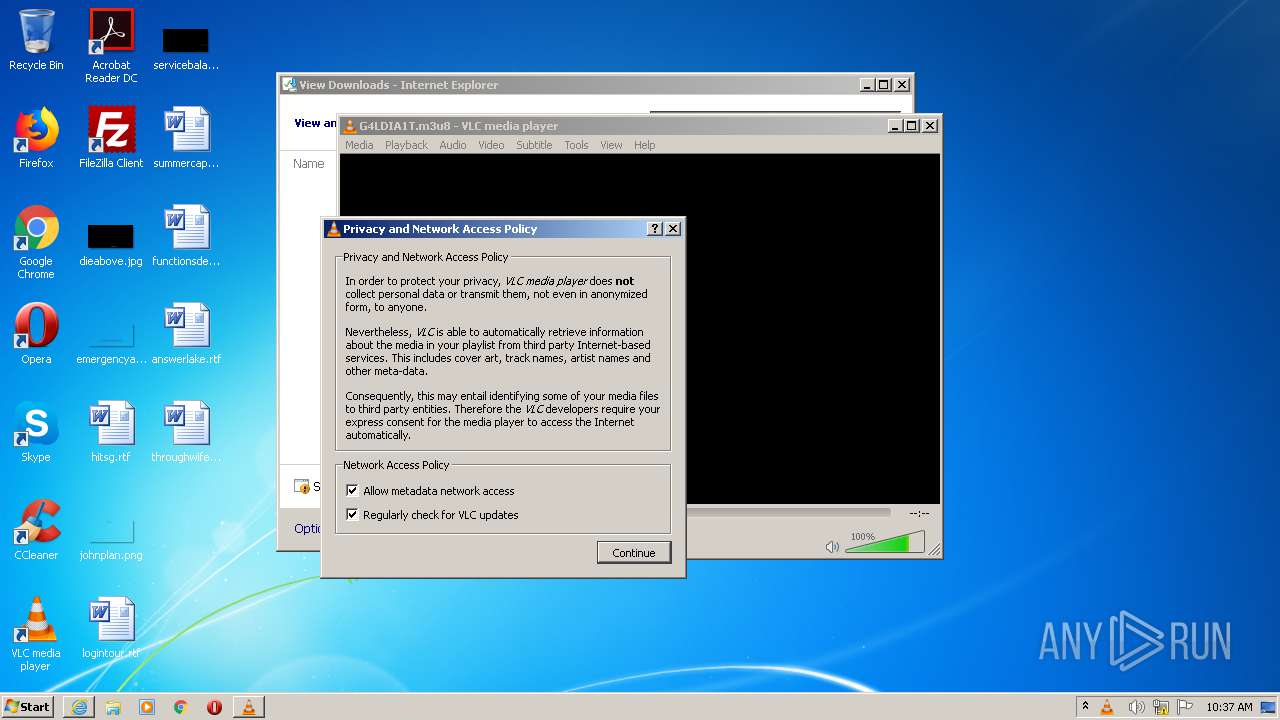
| Verdict: | No threats detected |
| Analysis date: | September 02, 2020, 09:36:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | E9F05EC82E927946264B9F40F45227E4 |
| SHA1: | 38356094D55307C3AFC19EC4DD9CA10E4B7D2525 |
| SHA256: | D715A841C086C9D1B2522F6F4A98E8D2C95F43DCCC6C84264BA3BCA29AE77305 |
| SSDEEP: | 48:euL2dq8IGiLqVxW1TjuL2dq8IGiLqVxW1TR:KdeGhVxYZdeGhVxYR |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- vlc.exe (PID: 2468)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2964)
Reads Internet Cache Settings
- iexplore.exe (PID: 2964)
- iexplore.exe (PID: 2904)
Application launched itself
- iexplore.exe (PID: 2964)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2964)
Reads internet explorer settings
- iexplore.exe (PID: 2904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
39
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2468 | "C:\Program Files\VideoLAN\VLC\vlc.exe" --started-from-file "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\G4LDIA1T.m3u8" | C:\Program Files\VideoLAN\VLC\vlc.exe | iexplore.exe | ||||||||||||
User: admin Company: VideoLAN Integrity Level: MEDIUM Description: VLC media player Exit code: 0 Version: 2.2.6 Modules
| |||||||||||||||
| 2904 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2964 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2964 | "C:\Program Files\Internet Explorer\iexplore.exe" https://video-weaver.sea01.hls.ttvnw.net/v1/playlist/Cu0EHTF_W3CVkosJjJ5qDf1L0C8a_ZPfhNQzJyAiHXA1vxiDH03JDd0g2FIxEjzhzsbZB1ssSdzuGwhwvwyiFU4IeoQdEKd3c7CuPdX5cooAPYmZOBfpegDiCvpR2i5NgYmw7cOITRx9zbyDhLJBBdQSQGzE-bKg974MgOenoGq-IkfquQCnQsAZ1Nx-QEamjadcYZajaCdQHBSZcSdQKx93uBaBr_VoDKp_UqD5jUhBMejuIedX0ezESBLpWxMS8TN-AUjOVbVPQ-iwsuDGuckEsIIR_81Ld0w65-rQDktCwq3x73dwsDLPQBm18EAgoU9exvSl1j6yJgDhaiV7p3CDJq9ptGMvVO2UR50EbHt2YtiY-7CJOyfXcBk4lFLTO_yLsuV_s4SfsrjuZKk-6iv1cv3bEhgQ30WX0hKeUly-xu-iuLs_56O--ErGowedQxQvjfBHeWQbV78_riWSI5PohBAU2dpQJCZgd7mi0KvxIv2_qU55WrU1orYFEwRbTbqNsI881TnBYVsqMzEcQWjDw3T2qZe-UwQU-LP6oUMO9b0vkEGMqpLkpcxKC8Go-nf8ewB-yPjs_uPpeFE1uIqzmhkbR3E5I47vwG1Ak56pU07voQFPnStGXZXC6s9rXGS9-M-xZ1RlQOJfbZbZAlVNyEqoZkzJ93W-fTi6a3KDn8A9Idmoq17pOA6SDoQo1RSQdWu5jMURzUANKWORgKyYcBaxmfRCW4T39faxQ8PM3oorUcAYcPaQ_RtqkOyutotO_hSri_E-4rU2V-HNZP_3oK1vBfmH_vJlJouVLyde_ObgQfcfxt7i56K1QHYUEhCPH23eEKYcwPZeCtBAJ5b2GgxmFHytyQ87_9Namzo.m3u8;https://video-weaver.sea01.hls.ttvnw.net/v1/playlist/Cu0EHTF_W3CVkosJjJ5qDf1L0C8a_ZPfhNQzJyAiHXA1vxiDH03JDd0g2FIxEjzhzsbZB1ssSdzuGwhwvwyiFU4IeoQdEKd3c7CuPdX5cooAPYmZOBfpegDiCvpR2i5NgYmw7cOITRx9zbyDhLJBBdQSQGzE-bKg974MgOenoGq-IkfquQCnQsAZ1Nx-QEamjadcYZajaCdQHBSZcSdQKx93uBaBr_VoDKp_UqD5jUhBMejuIedX0ezESBLpWxMS8TN-AUjOVbVPQ-iwsuDGuckEsIIR_81Ld0w65-rQDktCwq3x73dwsDLPQBm18EAgoU9exvSl1j6yJgDhaiV7p3CDJq9ptGMvVO2UR50EbHt2YtiY-7CJOyfXcBk4lFLTO_yLsuV_s4SfsrjuZKk-6iv1cv3bEhgQ30WX0hKeUly-xu-iuLs_56O--ErGowedQxQvjfBHeWQbV78_riWSI5PohBAU2dpQJCZgd7mi0KvxIv2_qU55WrU1orYFEwRbTbqNsI881TnBYVsqMzEcQWjDw3T2qZe-UwQU-LP6oUMO9b0vkEGMqpLkpcxKC8Go-nf8ewB-yPjs_uPpeFE1uIqzmhkbR3E5I47vwG1Ak56pU07voQFPnStGXZXC6s9rXGS9-M-xZ1RlQOJfbZbZAlVNyEqoZkzJ93W-fTi6a3KDn8A9Idmoq17pOA6SDoQo1RSQdWu5jMURzUANKWORgKyYcBaxmfRCW4T39faxQ8PM3oorUcAYcPaQ_RtqkOyutotO_hSri_E-4rU2V-HNZP_3oK1vBfmH_vJlJouVLyde_ObgQfcfxt7i56K1QHYUEhCPH23eEKYcwPZeCtBAJ5b2GgxmFHytyQ87_9Namzo.m3u8 | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 133
Read events
1 073
Write events
60
Delete events
0
Modification events
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 2608949774 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30834956 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A3000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2964) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
5
Text files
8
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2904 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab8822.tmp | — | |
MD5:— | SHA256:— | |||
| 2904 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar8823.tmp | — | |
MD5:— | SHA256:— | |||
| 2964 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2964 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD56565CAE63EAB9F.TMP | — | |
MD5:— | SHA256:— | |||
| 2904 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5B9763FB83E74617D0DB58992800F69B | — | |
MD5:— | SHA256:— | |||
| 2964 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB02121486FDE6963.TMP | — | |
MD5:— | SHA256:— | |||
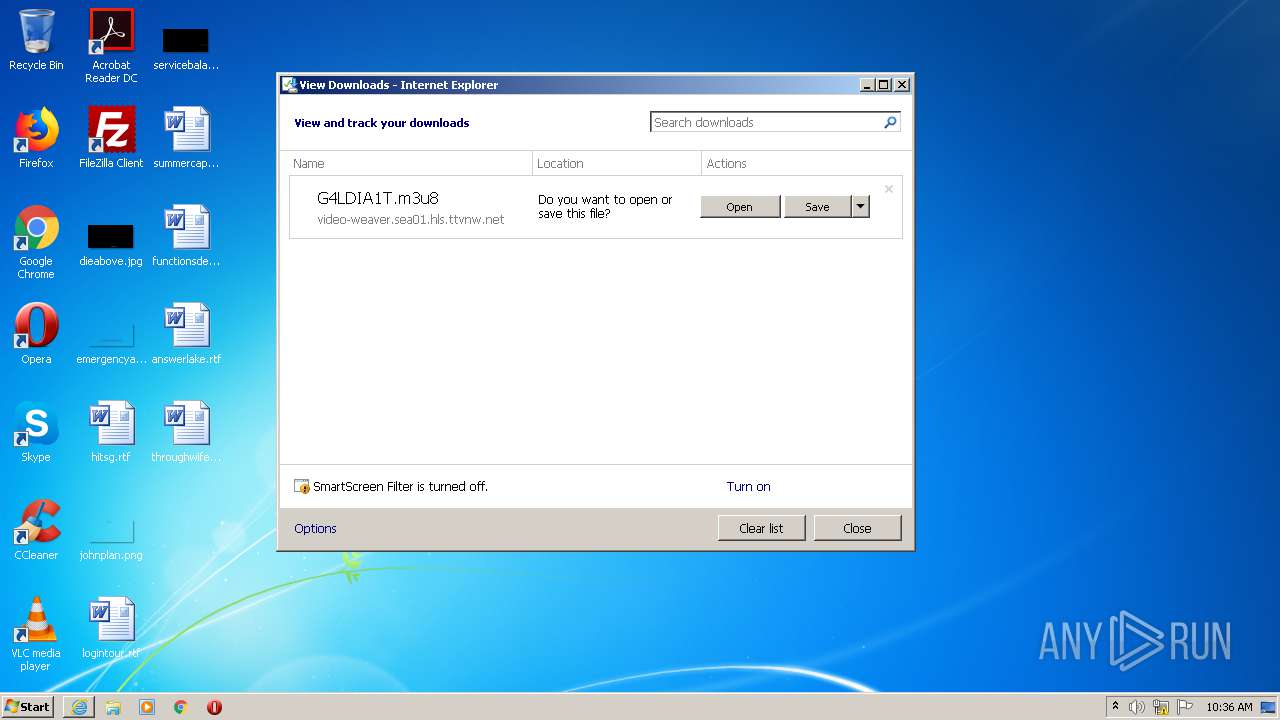
| 2964 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\G4LDIA1T.m3u8.hprtki7.partial:Zone.Identifier | — | |
MD5:— | SHA256:— | |||
| 2468 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCCDF5.tmp | — | |
MD5:— | SHA256:— | |||
| 2468 | vlc.exe | C:\Users\admin\AppData\Roaming\vlc\vlcrc.2468 | — | |
MD5:— | SHA256:— | |||
| 2468 | vlc.exe | C:\Users\admin\AppData\Local\Temp\VLCF554.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
15
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2904 | iexplore.exe | GET | — | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAhLFq%2Bx5LMU0RxrG1GDCeM%3D | US | — | — | whitelisted |
2904 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/ssca-sha2-g6.crl | US | binary | 12.9 Mb | whitelisted |
2904 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAH9o%2BtuynXIiEOLckvPvJE%3D | US | der | 471 b | whitelisted |
2964 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
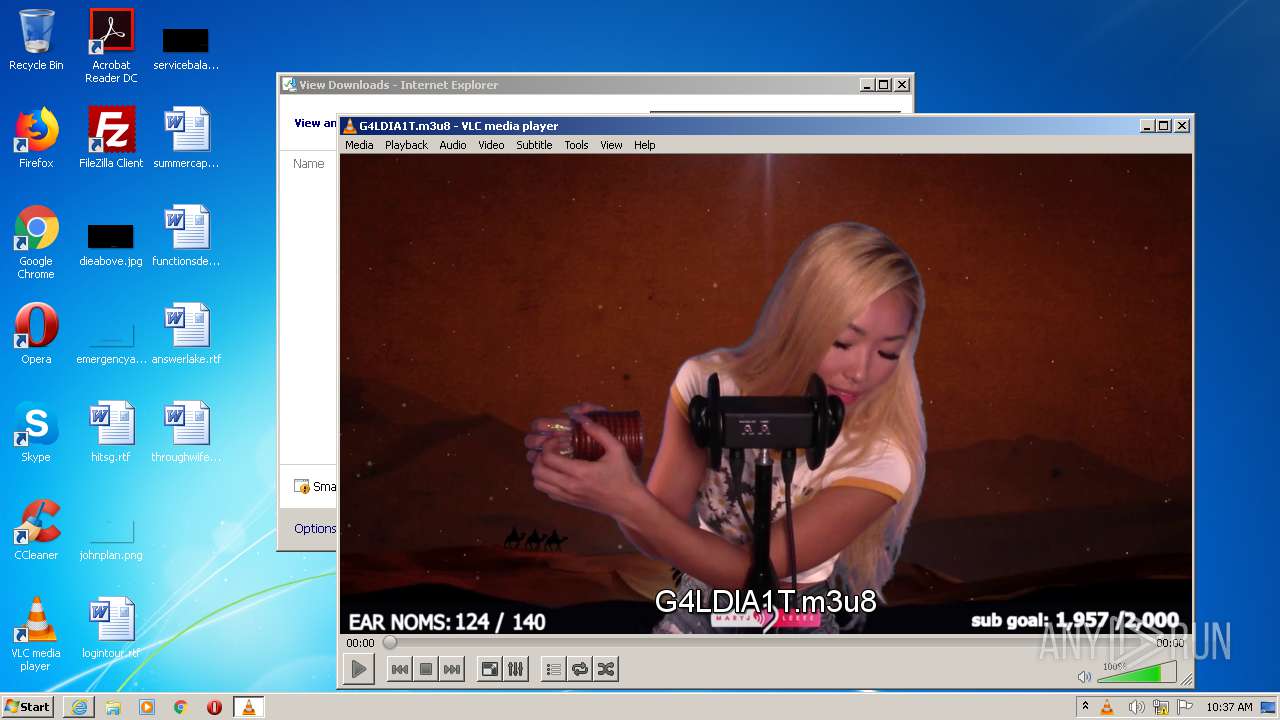
2904 | iexplore.exe | 52.223.241.1:443 | video-weaver.sea01.hls.ttvnw.net | Twitch Interactive Inc. | US | unknown |
2904 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2964 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2468 | vlc.exe | 52.223.228.107:443 | video-edge-7dbd48.sea01.abs.hls.ttvnw.net | Twitch Interactive Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
video-weaver.sea01.hls.ttvnw.net |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
video-edge-7dbd48.sea01.abs.hls.ttvnw.net |
| unknown |
Threats
Process | Message |
|---|---|
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|
vlc.exe | httplive stream: HTTP Live Streaming (/C:/Users/admin/AppData/Local/Microsoft/Windows/Temporary%20Internet%20Files/Content.IE5/PO2HN1X2/G4LDIA1T.m3u8)
|
vlc.exe | core tls session error: TLS client session handshake timeout
|
vlc.exe | http access error: cannot establish HTTP/TLS session
|
vlc.exe | core tls session error: TLS client session handshake error
|
vlc.exe | httplive stream error: downloading segment 21804 from stream 0 failed
|
vlc.exe | core stream error: no suitable access module for `https://video-edge-7dbd48.sea01.abs.hls.ttvnw.net/v1/segment/CoMF-vaXvVy0KAHy_HVhWGAo3vY8TAhMJqNtzze2ur69wS4peybldDJ7tNXskg8socaj5ADePeNx1fNbFethxbfKv2BAYs4tzkG2fETSD_7Q2IpZcAu8cV1G9EdS55J66NQBLDl_ab0BnB35ZfSb2dKJQAbcoBuikbAwsSFWT9RsFqaejdi976reSneyzChE4A9LMWGnpXafiNw_mCxe1NYz1wcR9b9qBmrCBTB1xCTmGDpg0NOE1kdTCneP2E-7lJK-kvprdxmgBeLwlMkyCtSRIMXsaeHE23E3USYOQ6RNA-IblCVrn_nLDmH9Pp81jCheZ9Dg36oFcvvpuKq36eKHXzyaH-lqpRsyI2sUm5kkIcy9qA4-BaewunpJUX7tSkjBCCijZebtT9CyIUPlelS7yFSXQm3BaJltJYhVc5AVobd1H0daTUVjoJJQ2DAO50OSqb7gqgmRc4gCtbrnyjqgcOMyyXIFFUK5CHz9wq9f_IJ7hhJF5eCDXi1ztPIrCgEM2pGCKgt6IKo5KGX0UCPL-8lwaDvbpYZF7sR1Wvt3t4ATovPbREkwJ7srQfV3_a-toaGHwFP4ifwB8OdGLMqhWI6JBuaR0cIqxYfBvyazF-bK24FDesU5iYC0DHVQPMVFFR5D1Q2IM3EWCh5SCyE7XijVYvy_npdiHVMKsC-H7KG4atNrawvLL3aYO1N8iwbuudid2mFvEn1DpUneHmuLvUxYON9f_JQ_peeE7UCn18mGx7ZfWJZEbM0ljfYfbHZ646mdWOcerVYOiTW9bioA3J0HWfcGUtPyJsGj0i2t6cRtpQj1gp3ifTMa4kWvz1cisV00E39hSBNFkeeP318O-w8SORIQijUAXFxra4TmfnU-Q7fkERoMCg3Vo4kvxiYvlTx4.ts'
|
vlc.exe | httplive stream error: fetching first segment failed.
|
vlc.exe | httplive stream error: segment 5 should have been available (stream 0)
|