| File name: | AGLoader.dll |
| Full analysis: | https://app.any.run/tasks/63832745-18ae-473d-a694-634dbcf119bf |
| Verdict: | Malicious activity |
| Analysis date: | August 10, 2023, 19:52:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (DLL) (GUI) Intel 80386, for MS Windows |
| MD5: | 1D296865107F94D309610FB92C5035AC |
| SHA1: | 5FDE937DBB83CF60B3004ED9ACA74A63908555F5 |
| SHA256: | D703AC3C8116503DB1273F6C30C5AA35315697F9DA065B107FA793B98A3F6D95 |
| SSDEEP: | 49152:XfN14TDCo9B4E3UymOJJSUTeRAg+yWG6jeLiJLHbRfOjI5FGHXyAKC5xCp9LI:vN14Px9JUpRApvjCiJHRfOjICHXbay |
MALICIOUS
Loads dropped or rewritten executable
- rundll32.exe (PID: 1116)
- WerFault.exe (PID: 2504)
SUSPICIOUS
No suspicious indicators.INFO
[YARA] Network interface manipulation strings were found
- rundll32.exe (PID: 1116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| ProductVersion: | 1.9.6.4 |
|---|---|
| ProductName: | Anonymizer Gadget |
| OriginalFileName: | AGLoader.dll |
| LegalCopyright: | Copyright (C) 2016 |
| InternalName: | Anonymizer Gadget |
| FileVersion: | 1.9.6.4 |
| FileDescription: | Anonymizer Gadget |
| CompanyName: | Jetico ltd |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.9.6.4 |
| FileVersionNumber: | 1.9.6.4 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x394ff4 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 479232 |
| CodeSize: | 3751424 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit, DLL |
| TimeStamp: | 2023:08:03 18:17:51+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Aug-2023 18:17:51 |
| Detected languages: |
|
| CompanyName: | Jetico ltd |
| FileDescription: | Anonymizer Gadget |
| FileVersion: | 1.9.6.4 |
| InternalName: | Anonymizer Gadget |
| LegalCopyright: | Copyright (C) 2016 |
| OriginalFilename: | AGLoader.dll |
| ProductName: | Anonymizer Gadget |
| ProductVersion: | 1.9.6.4 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 03-Aug-2023 18:17:51 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0038FB4C | 0x0038FC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.47865 |
.itext | 0x00391000 | 0x0000400C | 0x00004200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.03048 |
.data | 0x00396000 | 0x00010274 | 0x00010400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.80004 |
.bss | 0x003A7000 | 0x00007E74 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x003AF000 | 0x00003D50 | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.27861 |
.didata | 0x003B3000 | 0x00000D12 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.22557 |
.edata | 0x003B4000 | 0x000000B1 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.17502 |
.rdata | 0x003B5000 | 0x00000045 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.1924 |
.reloc | 0x003B6000 | 0x0004E734 | 0x0004E800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.71385 |
.rsrc | 0x00405000 | 0x00011400 | 0x00011400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.14987 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.41904 | 732 | UNKNOWN | UNKNOWN | RT_VERSION |
2 | 2.80231 | 308 | UNKNOWN | English - United States | RT_CURSOR |
3 | 3.00046 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4 | 2.56318 | 308 | UNKNOWN | English - United States | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | English - United States | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | English - United States | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | English - United States | RT_CURSOR |
4055 | 3.25826 | 508 | UNKNOWN | UNKNOWN | RT_STRING |
4056 | 3.30189 | 784 | UNKNOWN | UNKNOWN | RT_STRING |
4057 | 3.36302 | 1132 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
msvcrt.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x003AA648 |
__dbk_fcall_wrapper | 2 | 0x00012120 |
__Get__JsonConfigImpl__Instance__ | 3 | 0x003832D4 |
RunLoader | 4 | 0x003832D4 |
Total processes
35
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\AGLoader.dll.exe", dbkFCallWrapperAddr | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
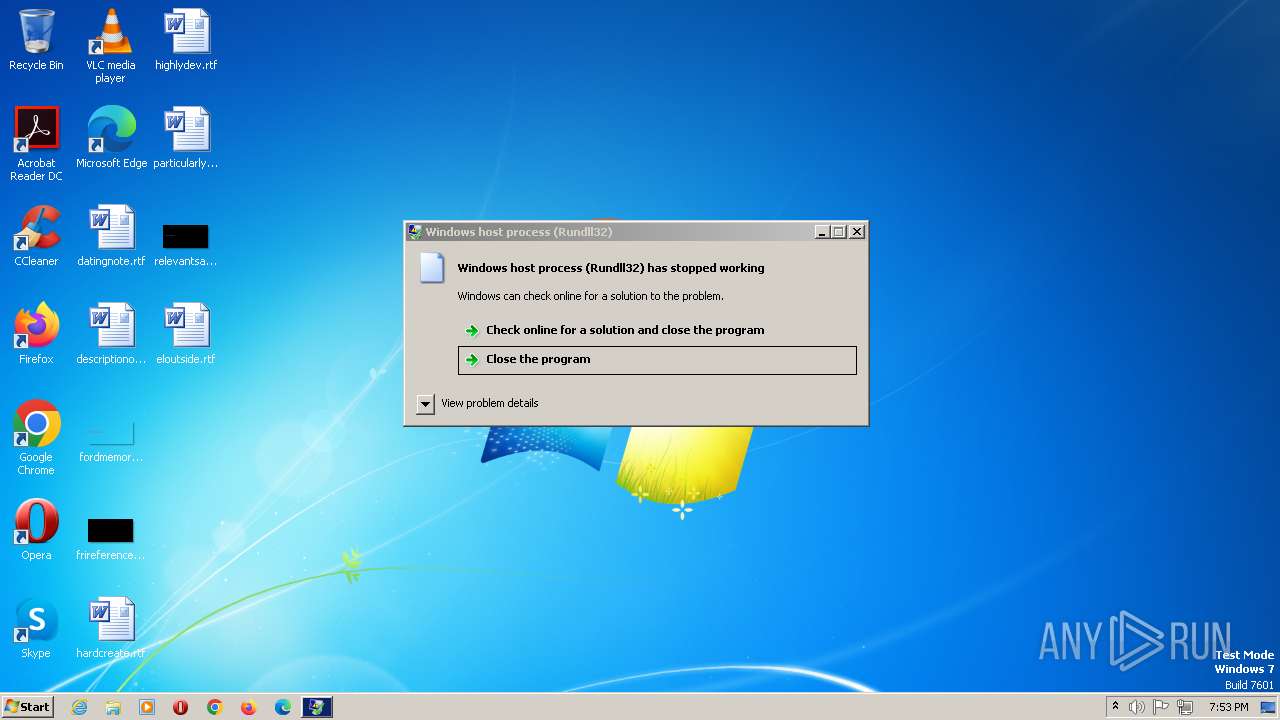
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1116 | "C:\Windows\System32\rundll32.exe" "C:\Users\admin\AppData\Local\Temp\AGLoader.dll.exe", dbkFCallWrapperAddr | C:\Windows\SysWOW64\rundll32.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2504 | C:\Windows\SysWOW64\WerFault.exe -u -p 1116 -s 440 | C:\Windows\SysWOW64\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
214
Read events
214
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
332 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |