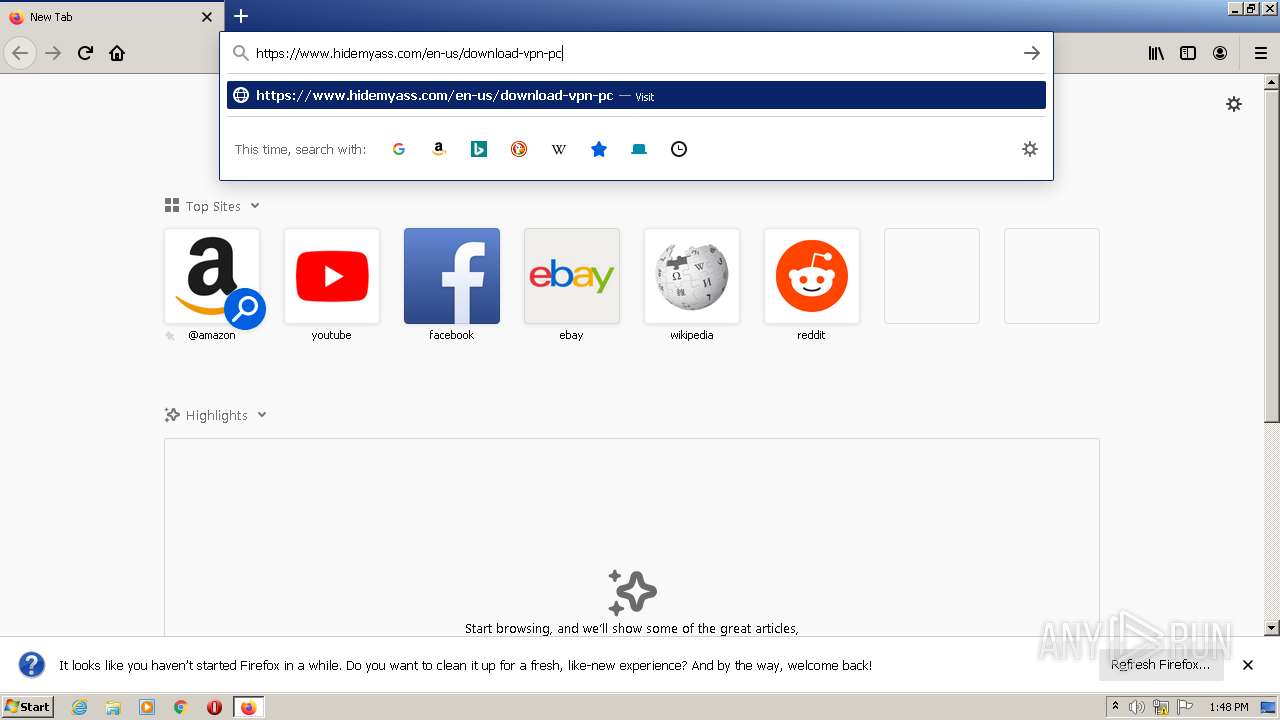
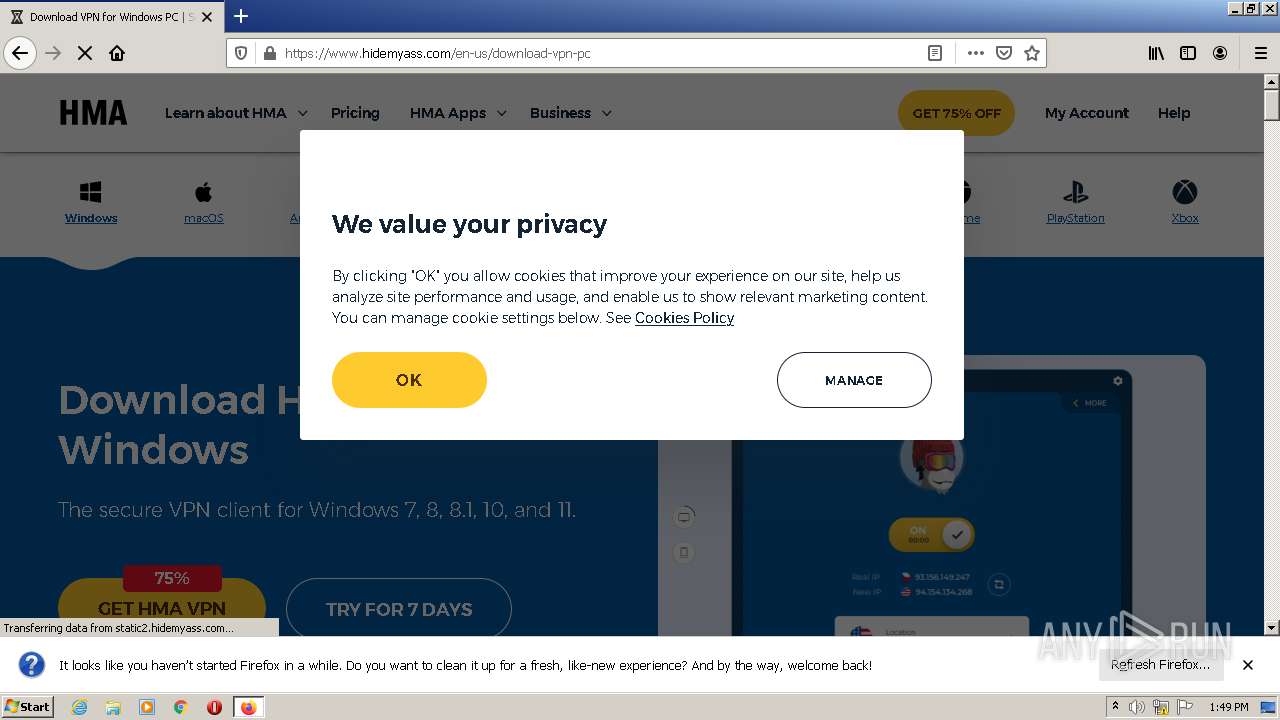
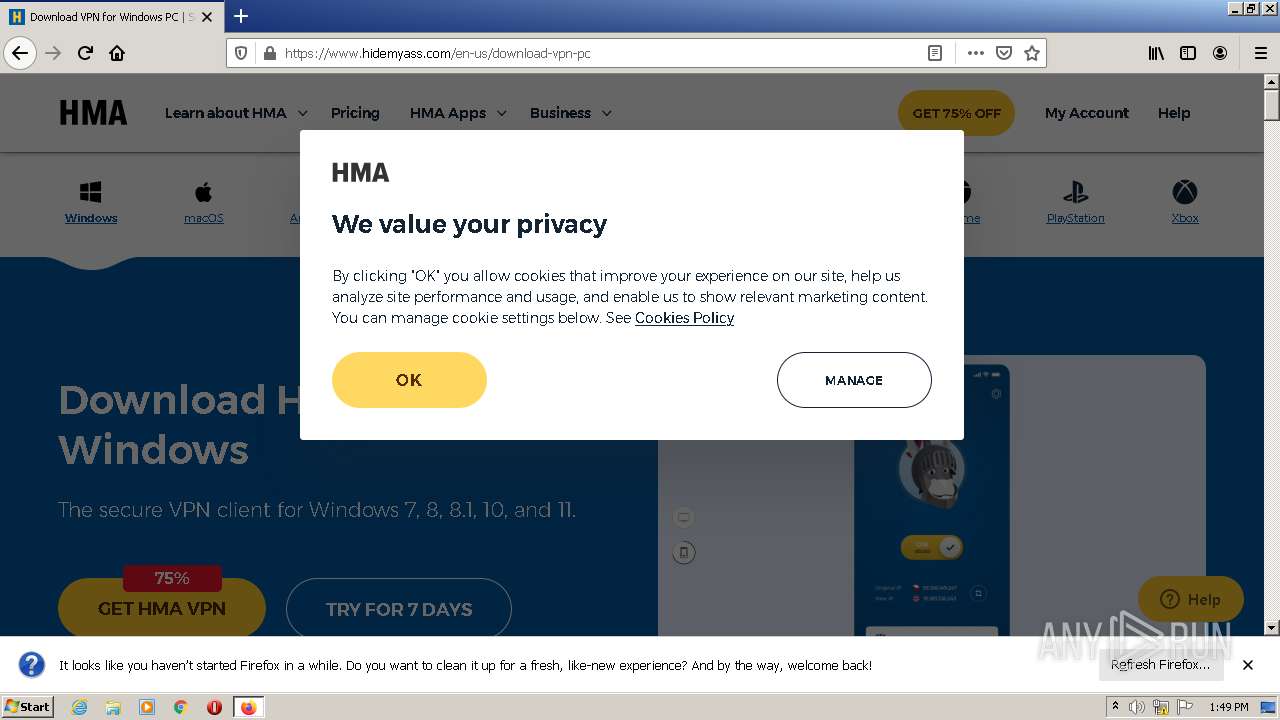
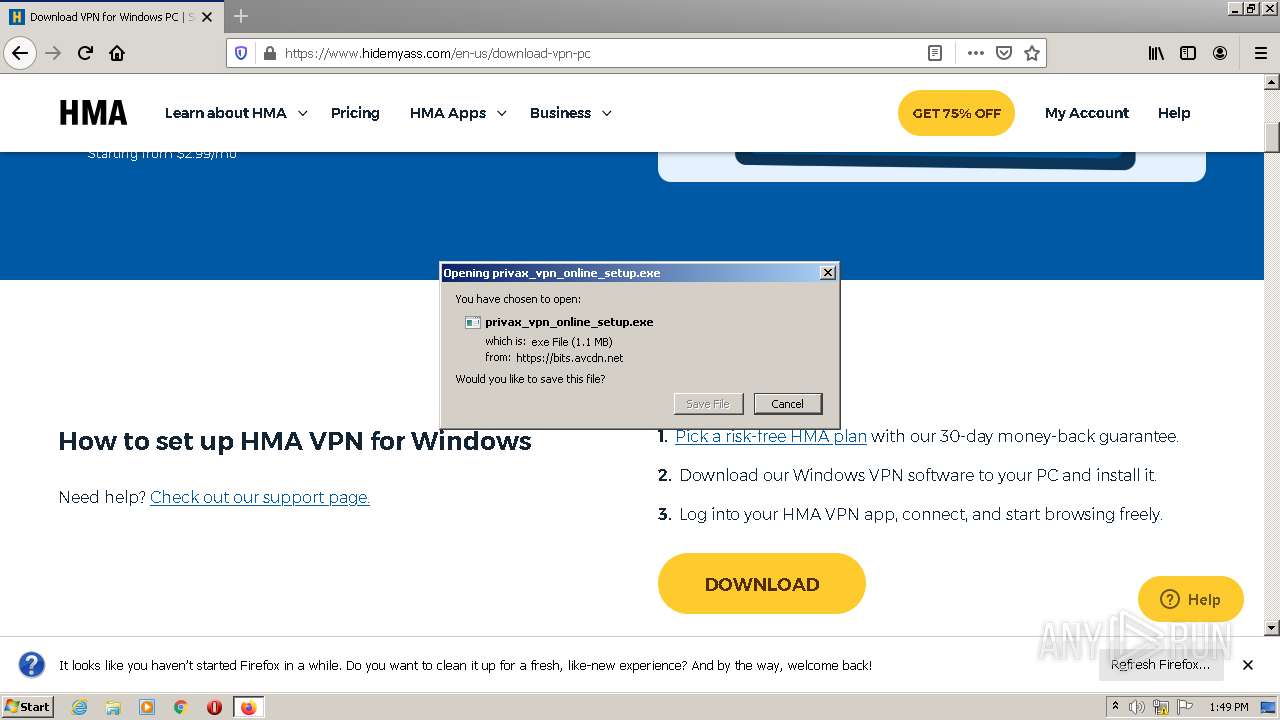
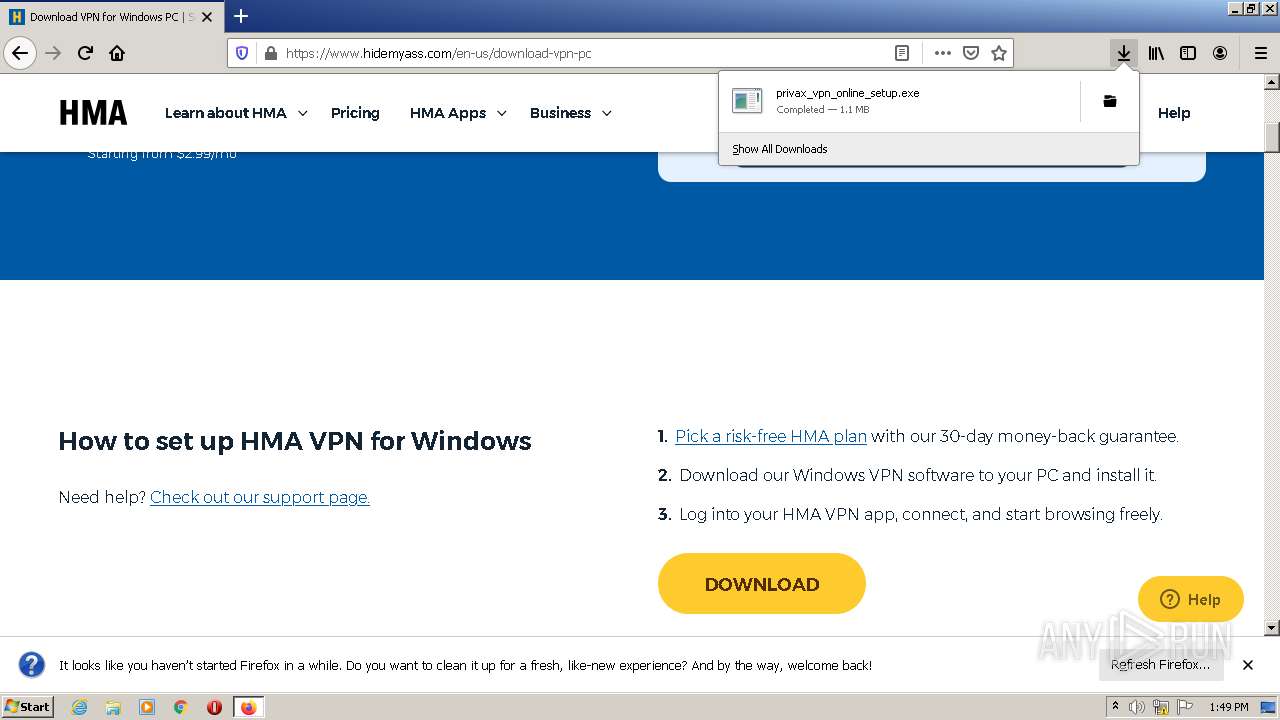
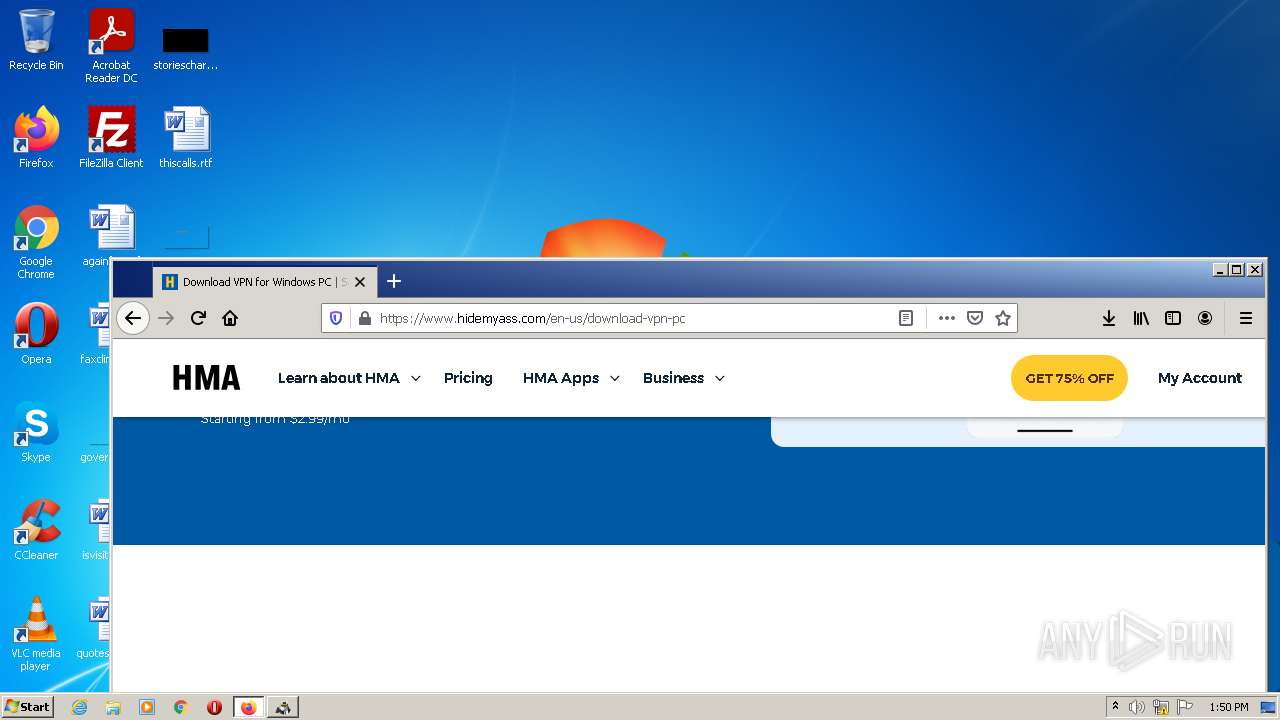
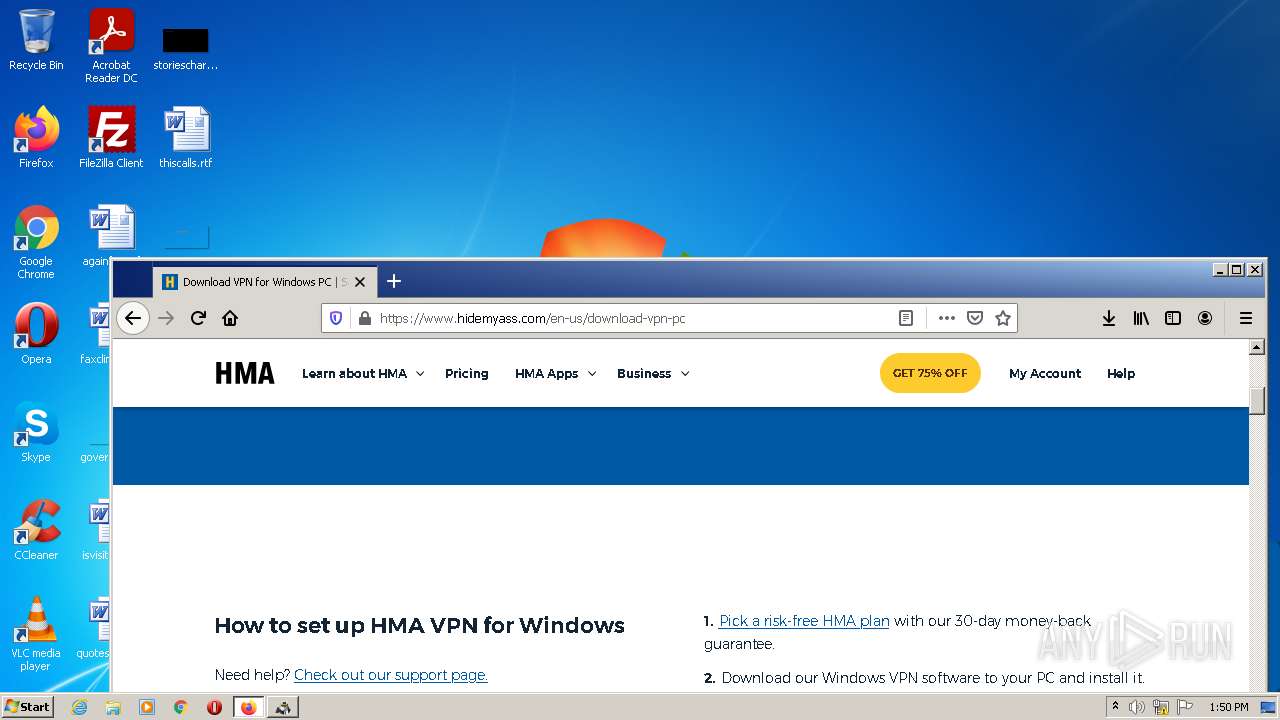
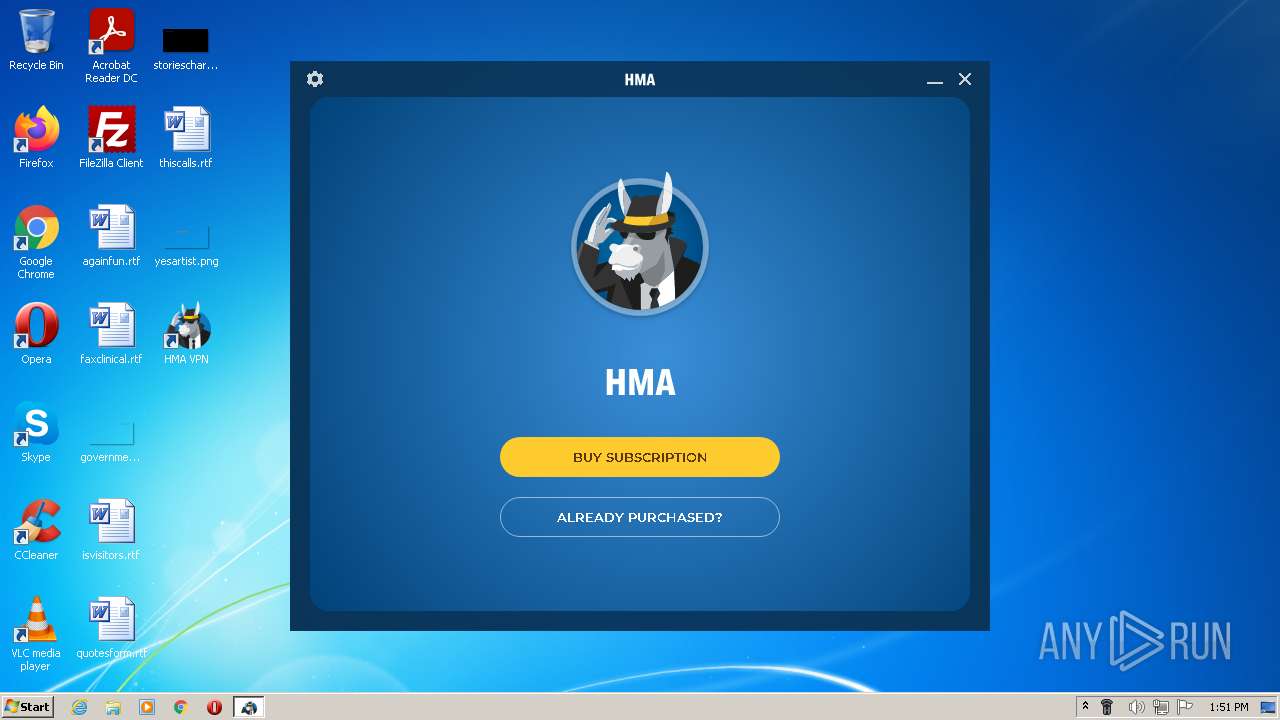
| URL: | https://www.hidemyass.com/en-us/download-vpn-pc |
| Full analysis: | https://app.any.run/tasks/d664c24c-4b16-42b2-8ea3-7a197b002492 |
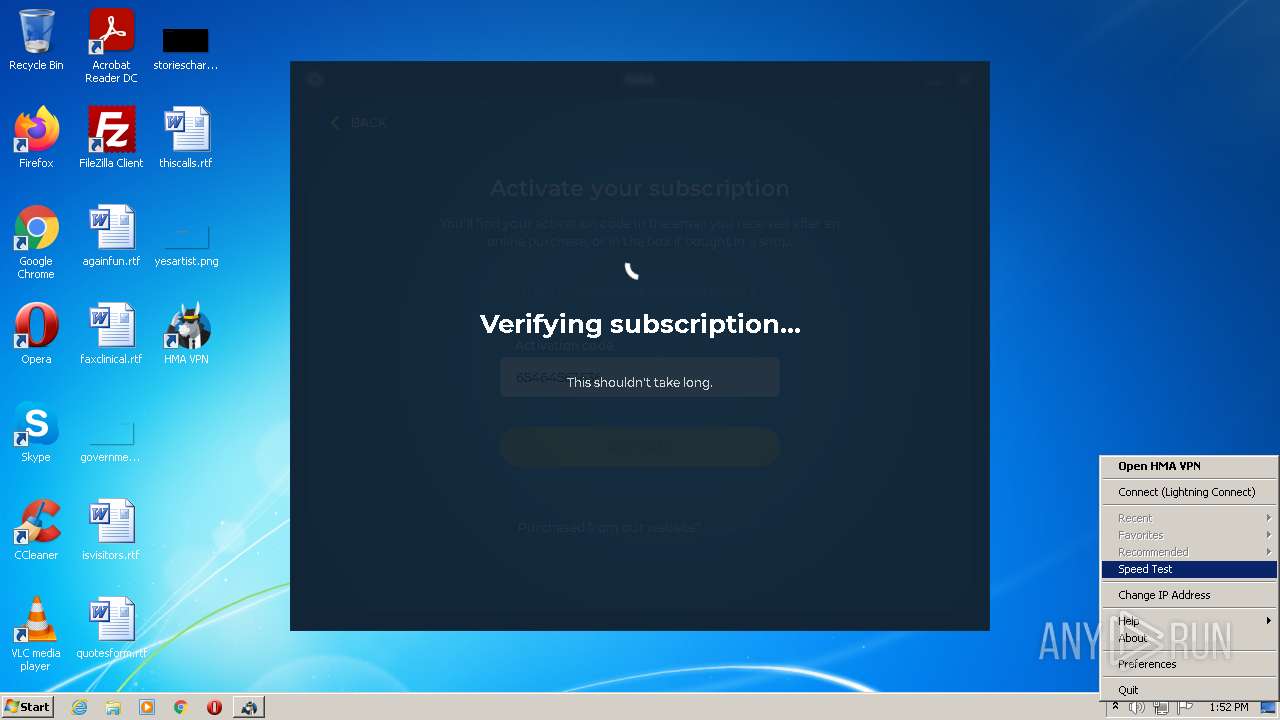
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2022, 13:48:35 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | B66C4ECBCB021CFF88AA1156D495176A |
| SHA1: | 71A21E68B635B794EC5B82BB8E68AE41199816BD |
| SHA256: | D6FADAFDDBB4A9245F963378D3B0B3578E7B15AB72B9B0EEC7BF655086999344 |
| SSDEEP: | 3:N8DSLfIcrb8d4kThb:2OLg2b8d/ |
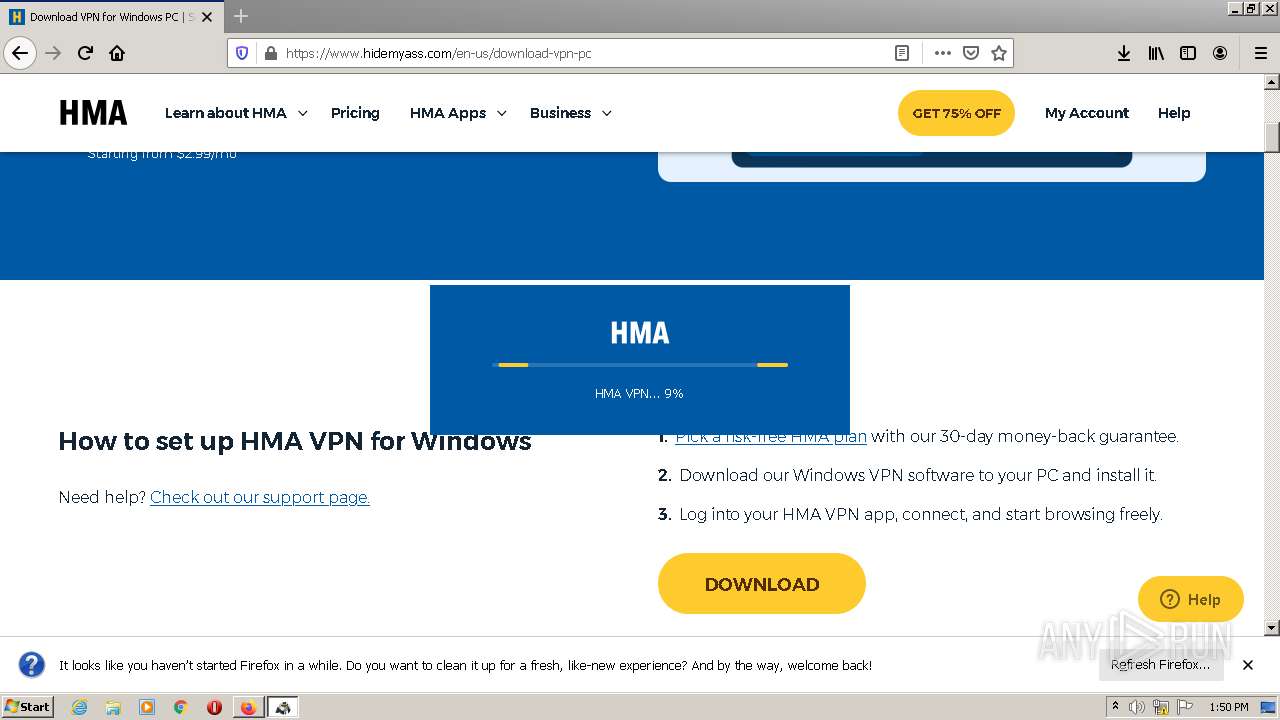
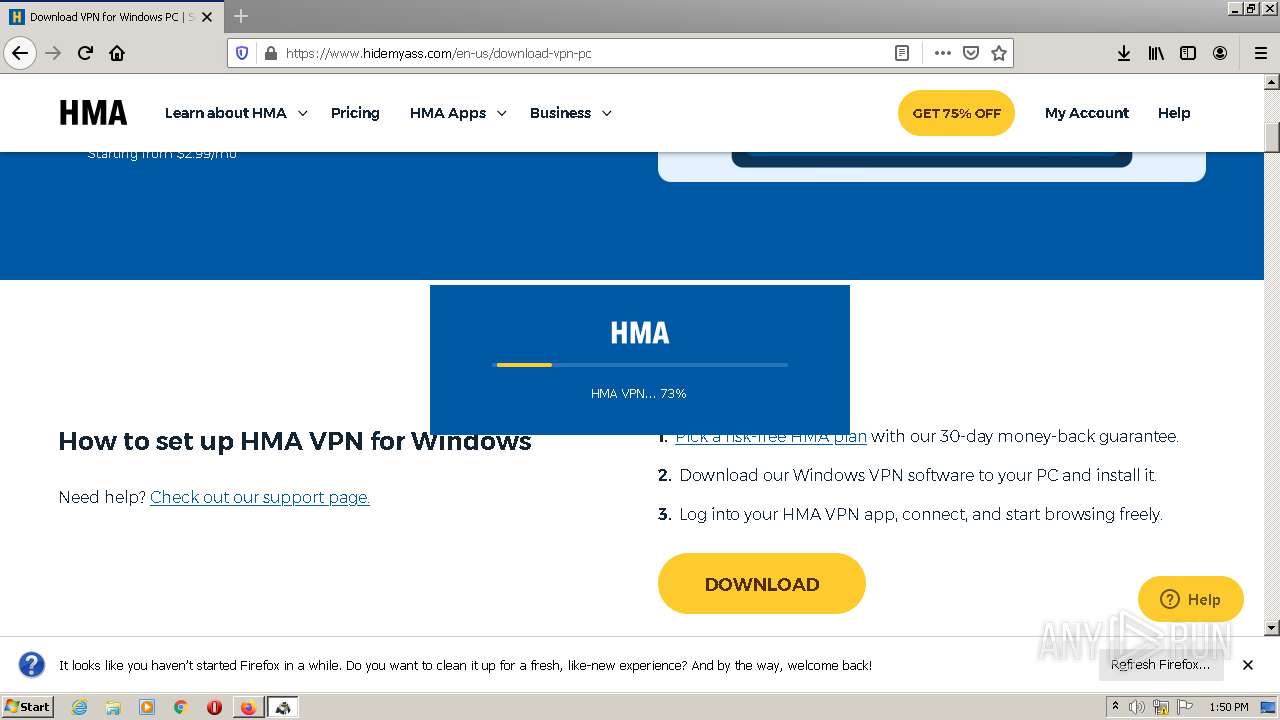
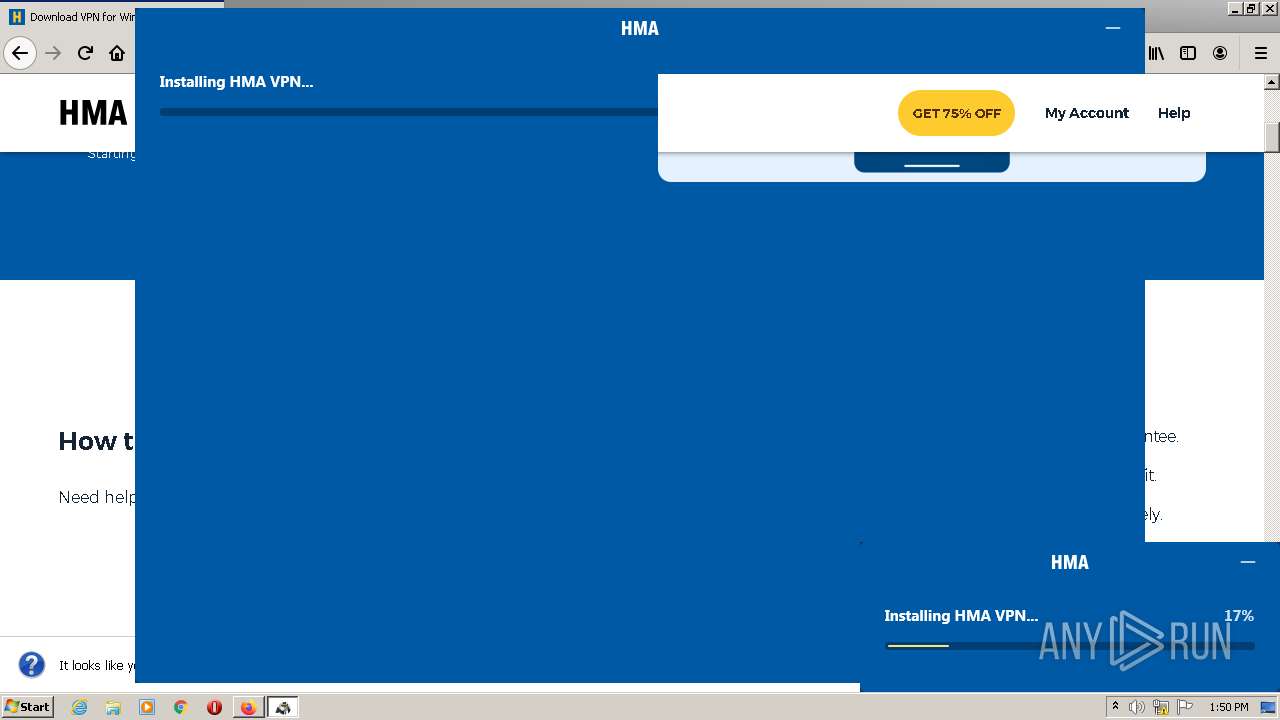
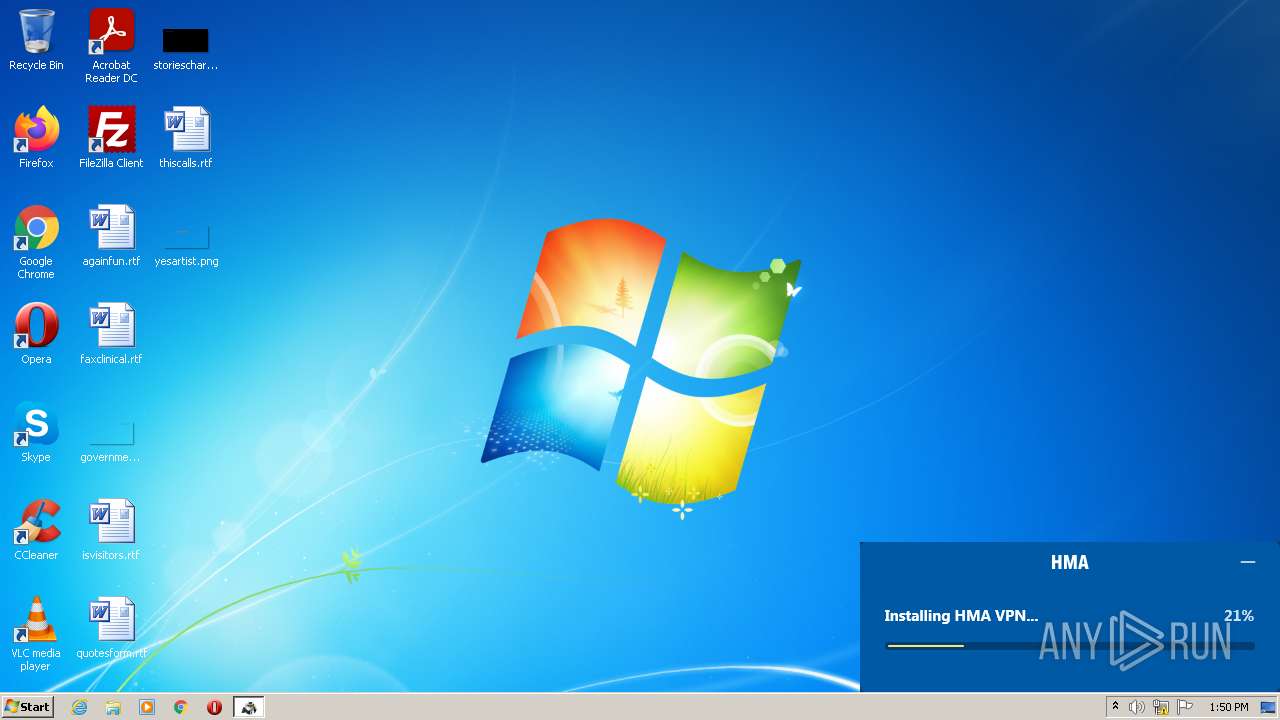
MALICIOUS
Application was dropped or rewritten from another process
- privax_vpn_online_setup.exe (PID: 3808)
- icarus.exe (PID: 3544)
- privax_vpn_online_setup.exe (PID: 3084)
- icarus_ui.exe (PID: 3068)
- icarus.exe (PID: 2972)
- VpnSvc.exe (PID: 3936)
- tapinstall.exe (PID: 2396)
- VpnUpdate.exe (PID: 3408)
- tapinstall.exe (PID: 3276)
- VpnUpdate.exe (PID: 3356)
- Vpn.exe (PID: 3404)
- Vpn.exe (PID: 856)
- icarus.exe (PID: 1136)
- Vpn.exe (PID: 1008)
- Vpn.exe (PID: 3208)
- Vpn.exe (PID: 2916)
Loads the Task Scheduler COM API
- icarus.exe (PID: 3544)
- icarus.exe (PID: 2972)
- VpnSvc.exe (PID: 3936)
- VpnUpdate.exe (PID: 3408)
- VpnUpdate.exe (PID: 3356)
Loads dropped or rewritten executable
- icarus.exe (PID: 2972)
- VpnSvc.exe (PID: 3936)
- Vpn.exe (PID: 3404)
- Vpn.exe (PID: 1008)
- Vpn.exe (PID: 3208)
- Vpn.exe (PID: 2916)
- Vpn.exe (PID: 856)
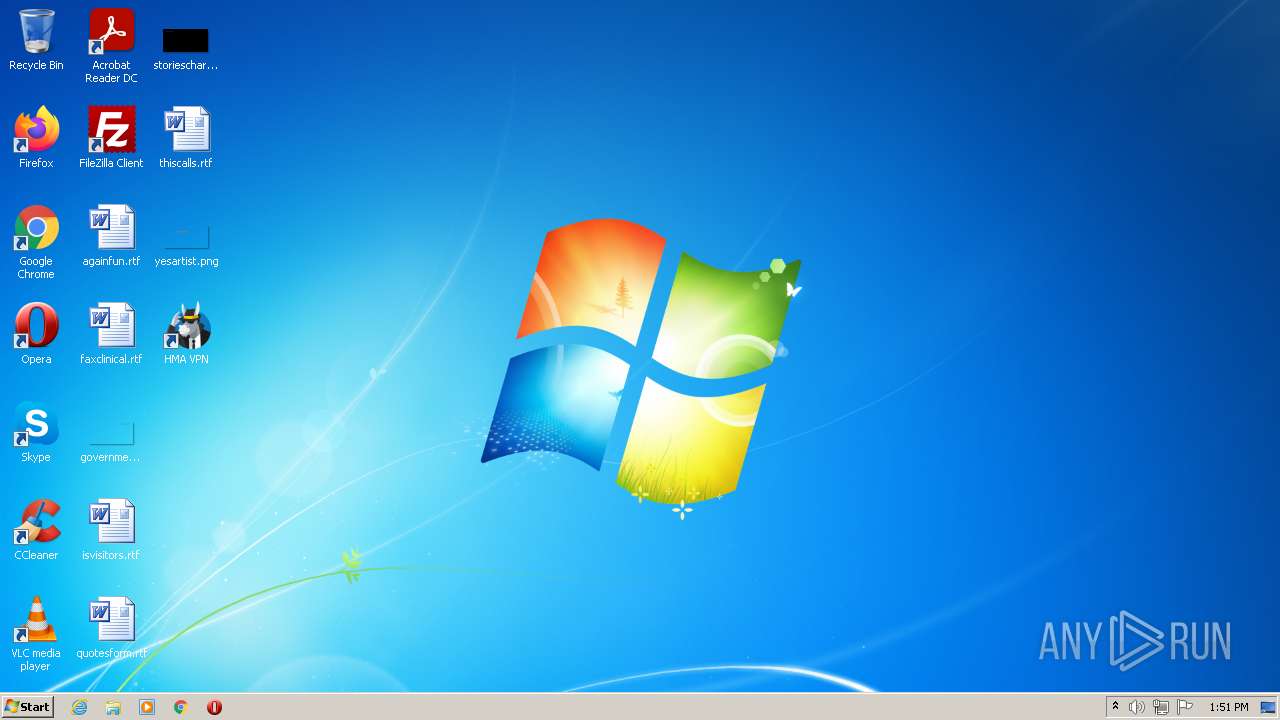
Writes to a start menu file
- VpnSvc.exe (PID: 3936)
SUSPICIOUS
Executable content was dropped or overwritten
- firefox.exe (PID: 3504)
- privax_vpn_online_setup.exe (PID: 3084)
- icarus.exe (PID: 3544)
- icarus.exe (PID: 2972)
Drops a file that was compiled in debug mode
- firefox.exe (PID: 3504)
- privax_vpn_online_setup.exe (PID: 3084)
- icarus.exe (PID: 3544)
- icarus.exe (PID: 2972)
Checks supported languages
- privax_vpn_online_setup.exe (PID: 3084)
- icarus.exe (PID: 3544)
- icarus_ui.exe (PID: 3068)
- icarus.exe (PID: 2972)
- VpnSvc.exe (PID: 3936)
- VpnUpdate.exe (PID: 3408)
- tapinstall.exe (PID: 3276)
- VpnUpdate.exe (PID: 3356)
- Vpn.exe (PID: 3404)
- tapinstall.exe (PID: 2396)
- Vpn.exe (PID: 856)
- icarus.exe (PID: 1136)
- Vpn.exe (PID: 1008)
- Vpn.exe (PID: 3208)
- Vpn.exe (PID: 2916)
Reads the computer name
- privax_vpn_online_setup.exe (PID: 3084)
- icarus.exe (PID: 3544)
- icarus_ui.exe (PID: 3068)
- icarus.exe (PID: 2972)
- VpnSvc.exe (PID: 3936)
- VpnUpdate.exe (PID: 3408)
- tapinstall.exe (PID: 2396)
- tapinstall.exe (PID: 3276)
- VpnUpdate.exe (PID: 3356)
- Vpn.exe (PID: 3404)
- icarus.exe (PID: 1136)
- Vpn.exe (PID: 856)
- Vpn.exe (PID: 3208)
- Vpn.exe (PID: 1008)
- Vpn.exe (PID: 2916)
Creates files in the program directory
- privax_vpn_online_setup.exe (PID: 3084)
- icarus.exe (PID: 3544)
- icarus_ui.exe (PID: 3068)
- VpnSvc.exe (PID: 3936)
- icarus.exe (PID: 2972)
- Vpn.exe (PID: 3404)
- Vpn.exe (PID: 2916)
Creates files in the Windows directory
- privax_vpn_online_setup.exe (PID: 3084)
- icarus.exe (PID: 3544)
- icarus.exe (PID: 2972)
Reads CPU info
- icarus.exe (PID: 3544)
- icarus_ui.exe (PID: 3068)
- icarus.exe (PID: 2972)
- VpnSvc.exe (PID: 3936)
- VpnUpdate.exe (PID: 3408)
- VpnUpdate.exe (PID: 3356)
- Vpn.exe (PID: 3404)
- Vpn.exe (PID: 856)
- Vpn.exe (PID: 1008)
- Vpn.exe (PID: 3208)
- icarus.exe (PID: 1136)
- Vpn.exe (PID: 2916)
Creates or modifies windows services
- icarus.exe (PID: 3544)
Starts itself from another location
- icarus.exe (PID: 3544)
Creates a directory in Program Files
- icarus.exe (PID: 2972)
Drops a file with too old compile date
- icarus.exe (PID: 2972)
Creates a software uninstall entry
- icarus.exe (PID: 2972)
Reads Environment values
- VpnSvc.exe (PID: 3936)
- Vpn.exe (PID: 3404)
- Vpn.exe (PID: 1008)
- Vpn.exe (PID: 3208)
- Vpn.exe (PID: 2916)
- Vpn.exe (PID: 856)
Executed as Windows Service
- VpnSvc.exe (PID: 3936)
Drops a file with a compile date too recent
- icarus.exe (PID: 2972)
Removes files from Windows directory
- icarus.exe (PID: 3544)
- privax_vpn_online_setup.exe (PID: 3084)
Application launched itself
- Vpn.exe (PID: 3404)
INFO
Reads the computer name
- chrome.exe (PID: 2204)
- chrome.exe (PID: 2076)
- chrome.exe (PID: 1088)
- chrome.exe (PID: 1676)
- firefox.exe (PID: 2176)
- firefox.exe (PID: 3504)
- firefox.exe (PID: 1336)
- firefox.exe (PID: 3740)
- firefox.exe (PID: 2316)
- firefox.exe (PID: 2936)
- firefox.exe (PID: 124)
Reads the hosts file
- chrome.exe (PID: 2204)
- chrome.exe (PID: 2076)
- icarus.exe (PID: 3544)
- icarus.exe (PID: 2972)
- Vpn.exe (PID: 3404)
- Vpn.exe (PID: 2916)
- icarus.exe (PID: 1136)
Checks supported languages
- chrome.exe (PID: 2204)
- chrome.exe (PID: 2076)
- chrome.exe (PID: 2988)
- chrome.exe (PID: 2100)
- chrome.exe (PID: 2004)
- firefox.exe (PID: 3928)
- firefox.exe (PID: 3504)
- chrome.exe (PID: 1088)
- chrome.exe (PID: 424)
- chrome.exe (PID: 1676)
- firefox.exe (PID: 2176)
- firefox.exe (PID: 3740)
- firefox.exe (PID: 1336)
- firefox.exe (PID: 2316)
- firefox.exe (PID: 2936)
- firefox.exe (PID: 124)
Manual execution by user
- firefox.exe (PID: 3928)
- Vpn.exe (PID: 3404)
Application launched itself
- chrome.exe (PID: 2204)
- firefox.exe (PID: 3928)
- firefox.exe (PID: 3504)
Reads settings of System Certificates
- chrome.exe (PID: 2076)
- firefox.exe (PID: 3504)
- privax_vpn_online_setup.exe (PID: 3084)
- icarus.exe (PID: 2972)
- VpnSvc.exe (PID: 3936)
Reads CPU info
- firefox.exe (PID: 3504)
Reads the date of Windows installation
- firefox.exe (PID: 3504)
Creates files in the user directory
- firefox.exe (PID: 3504)
Checks Windows Trust Settings
- firefox.exe (PID: 3504)
Creates files in the program directory
- firefox.exe (PID: 3504)
Dropped object may contain Bitcoin addresses
- icarus.exe (PID: 2972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
77
Monitored processes
32
Malicious processes
12
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3504.34.1241966255\2084063706" -childID 5 -isForBrowser -prefsHandle 4004 -prefMapHandle 4012 -prefsLen 7777 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3504 "\\.\pipe\gecko-crash-server-pipe.3504" 4024 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1076,8420905723023492817,1863921715114014642,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1452 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Privax\HMA VPN\Vpn.exe" --type=gpu-process --field-trial-handle=1920,13152109290714526654,1190030729585629779,131072 --disable-features=CookiesWithoutSameSiteMustBeSecure,ForcedColors,SameSiteByDefaultCookies,SameSiteDefaultChecksMethodRigorously --no-sandbox --disable-gpu-driver-bug-workarounds --log-file="C:\ProgramData\Privax\HMA VPN\log\cef_log.txt" --log-severity=error --user-agent="Chrome/37.0.2062.124 Avastium (17.0)" --lang=en-US --proxy-auto-detect --disable-webaudio --force-wave-audio --disable-software-rasterizer --no-sandbox --blacklist-accelerated-compositing --disable-accelerated-2d-canvas --disable-accelerated-compositing --disable-accelerated-layers --disable-accelerated-video-decode --blacklist-webgl --disable-bundled-ppapi-flash --disable-flash-3d --enable-aggressive-domstorage-flushing --enable-media-stream --allow-file-access-from-files=1 --pack_loading_disabled=1 --gpu-preferences=SAAAAAAAAADgAABwAAAAAAAAAAAAAAAAAABgAAAAAAAoAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAB4AAAAAAAAAHgAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAAIAAAAAAAAAAgAAAAAAAAA --use-gl=swiftshader-webgl --log-file="C:\ProgramData\Privax\HMA VPN\log\cef_log.txt" --mojo-platform-channel-handle=1960 /prefetch:2 | C:\Program Files\Privax\HMA VPN\Vpn.exe | Vpn.exe | ||||||||||||
User: admin Company: Privax Limited Integrity Level: MEDIUM Description: Privax HMA VPN Exit code: 0 Version: 5.4.5999.0 Modules
| |||||||||||||||
| 1008 | "C:\Program Files\Privax\HMA VPN\Vpn.exe" --type=renderer --no-sandbox --autoplay-policy=no-user-gesture-required --log-file="C:\ProgramData\Privax\HMA VPN\log\cef_log.txt" --field-trial-handle=1920,13152109290714526654,1190030729585629779,131072 --disable-features=CookiesWithoutSameSiteMustBeSecure,ForcedColors,SameSiteByDefaultCookies,SameSiteDefaultChecksMethodRigorously --disable-gpu-compositing --lang=en-US --log-file="C:\ProgramData\Privax\HMA VPN\log\cef_log.txt" --log-severity=error --user-agent="Chrome/37.0.2062.124 Avastium (17.0)" --proxy-auto-detect --disable-webaudio --force-wave-audio --disable-software-rasterizer --no-sandbox --blacklist-accelerated-compositing --disable-accelerated-2d-canvas --disable-accelerated-compositing --disable-accelerated-layers --disable-accelerated-video-decode --blacklist-webgl --disable-bundled-ppapi-flash --disable-flash-3d --enable-aggressive-domstorage-flushing --enable-media-stream --allow-file-access-from-files=1 --pack_loading_disabled=1 --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=3 --mojo-platform-channel-handle=3644 /prefetch:1 | C:\Program Files\Privax\HMA VPN\Vpn.exe | — | Vpn.exe | |||||||||||
User: admin Company: Privax Limited Integrity Level: MEDIUM Description: Privax HMA VPN Exit code: 0 Version: 5.4.5999.0 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1076,8420905723023492817,1863921715114014642,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1060 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1136 | "C:\Program Files\Common Files\Privax\Icarus\privax-vpn\icarus.exe" /checkforupdates:privax-vpn /silent | C:\Program Files\Common Files\Privax\Icarus\privax-vpn\icarus.exe | VpnSvc.exe | ||||||||||||
User: SYSTEM Company: Privax Limited Integrity Level: SYSTEM Description: Privax Installer Exit code: 0 Version: 21.21.4143.0 Modules
| |||||||||||||||
| 1336 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3504.6.999926418\1957375604" -childID 1 -isForBrowser -prefsHandle 3000 -prefMapHandle 2996 -prefsLen 181 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3504 "\\.\pipe\gecko-crash-server-pipe.3504" 3012 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1076,8420905723023492817,1863921715114014642,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1056 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1076,8420905723023492817,1863921715114014642,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1852 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1076,8420905723023492817,1863921715114014642,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1244 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
33 396
Read events
33 206
Write events
190
Delete events
0
Modification events
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
205
Suspicious files
221
Text files
213
Unknown types
474
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-6239D3B7-89C.pma | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Extension Settings\pkedcjkdefgpdelpbcmbmeomcjbeemfm\LOG.old | text | |
MD5:5202CA4D6AF0C37DAEC0D528CC7F2986 | SHA256:8F5B8FF94B14C36EA0CBE8FA0A4D165A632B45F834BBB7239E1A6CF6685F256C | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2988 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\634b4299-00e1-4a2a-8b9d-3645a6d29dbc.tmp | text | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d277bcf2-3247-4e18-a955-353ab5bb91ef.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RFed9e1.TMP | text | |
MD5:D097F8EB2230B3F32C41C5D75790508C | SHA256:ADDF87D20CD455CFB4AACB6B76719629C0277A4CF70B496343047BB73ABBAEF5 | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
161
DNS requests
256
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3504 | firefox.exe | POST | 200 | 100.24.223.135:80 | http://ocsps.ssl.com/ | US | der | 727 b | whitelisted |
3504 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3504 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3504 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3504 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
3504 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
3504 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3504 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3504 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3504 | firefox.exe | POST | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2076 | chrome.exe | 104.90.160.112:443 | www.hidemyass.com | Akamai Technologies, Inc. | NL | unknown |
2076 | chrome.exe | 142.250.186.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
2076 | chrome.exe | 142.250.184.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3504 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
3504 | firefox.exe | 142.250.184.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3504 | firefox.exe | 35.160.112.165:443 | location.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3504 | firefox.exe | 142.250.184.195:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3504 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3504 | firefox.exe | 143.204.98.64:443 | firefox-settings-attachments.cdn.mozilla.net | — | US | shared |
3504 | firefox.exe | 104.90.160.112:443 | www.hidemyass.com | Akamai Technologies, Inc. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
www.hidemyass.com |
| suspicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3504 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3504 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3504 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3504 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3936 | VpnSvc.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
— | — | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
Process | Message |
|---|---|
VpnSvc.exe | [2022-03-22 13:51:49.458] [error ] [vpn ] [ 3936: 3664] [B8C9E4: 184] asw::vpn::PrivateEventRouting::CheckForBrowserExtension
Exception: Unable to open process 1480!
Code: 0x00000057 (87)
|
Vpn.exe | [0322/135149.747:ERROR:gpu_init.cc(440)] Passthrough is not supported, GL is swiftshader
|