| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/ba97a1b0-79db-4258-a68b-a4aa17f53d06 |
| Verdict: | Malicious activity |
| Analysis date: | November 24, 2024, 06:11:41 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 5 sections |
| MD5: | 13199A06F646DD1E82D9A6E2DFDE62E3 |
| SHA1: | 3847F7BE74BE45066C493B7B71C52D50649F8FA0 |
| SHA256: | D6F6FD3FE8EBA8CCEE31A270BA3FC6B6A7A1DE58F4C9B45F40A9F322A84F8B1F |
| SSDEEP: | 98304:EeBEtlyiGMi2kx1z/x1VgcSC7p7yo/lFwm+regNUR+gWqgET7laeRTgXoyTYLhwT:yZnpGY |
MALICIOUS
Scans artifacts that could help determine the target
- setup.exe (PID: 4796)
SUSPICIOUS
Starts a Microsoft application from unusual location
- setup.exe (PID: 2648)
- setup.exe (PID: 3752)
- setup.exe (PID: 4796)
Creates file in the systems drive root
- setup.exe (PID: 2648)
Process drops legitimate windows executable
- setup.exe (PID: 2648)
Application launched itself
- setup.exe (PID: 2648)
- setup.exe (PID: 3752)
Reads security settings of Internet Explorer
- setup.exe (PID: 3752)
- setup.exe (PID: 4796)
Reads the Internet Settings
- setup.exe (PID: 3752)
- setup.exe (PID: 4796)
Reads settings of System Certificates
- setup.exe (PID: 3752)
- setup.exe (PID: 4796)
Checks Windows Trust Settings
- setup.exe (PID: 4796)
INFO
Checks supported languages
- setup.exe (PID: 2648)
- setup.exe (PID: 3752)
- setup.exe (PID: 4796)
Reads the computer name
- setup.exe (PID: 3752)
- setup.exe (PID: 4796)
Checks proxy server information
- setup.exe (PID: 3752)
- setup.exe (PID: 4796)
Reads the machine GUID from the registry
- setup.exe (PID: 3752)
- setup.exe (PID: 4796)
The process uses the downloaded file
- setup.exe (PID: 3752)
Process checks whether UAC notifications are on
- setup.exe (PID: 3752)
Reads the software policy settings
- setup.exe (PID: 3752)
- setup.exe (PID: 4796)
Reads Microsoft Office registry keys
- setup.exe (PID: 3752)
- setup.exe (PID: 4796)
Creates files or folders in the user directory
- setup.exe (PID: 4796)
Reads Environment values
- setup.exe (PID: 4796)
Create files in a temporary directory
- setup.exe (PID: 4796)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:10:07 01:44:58+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, Removable run from swap, Net run from swap |
| PEType: | PE32 |
| LinkerVersion: | 14.38 |
| CodeSize: | 4538880 |
| InitializedDataSize: | 2995712 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3dbb85 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 16.0.18129.20030 |
| ProductVersionNumber: | 16.0.18129.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft 365 and Office |
| FileVersion: | 16.0.18129.20030 |
| InternalName: | Bootstrapper.exe |
| LegalTrademarks1: | Microsoft® is a registered trademark of Microsoft Corporation. |
| LegalTrademarks2: | Windows® is a registered trademark of Microsoft Corporation. |
| OriginalFileName: | Bootstrapper.exe |
| ProductName: | Microsoft Office |
| ProductVersion: | 16.0.18129.20030 |
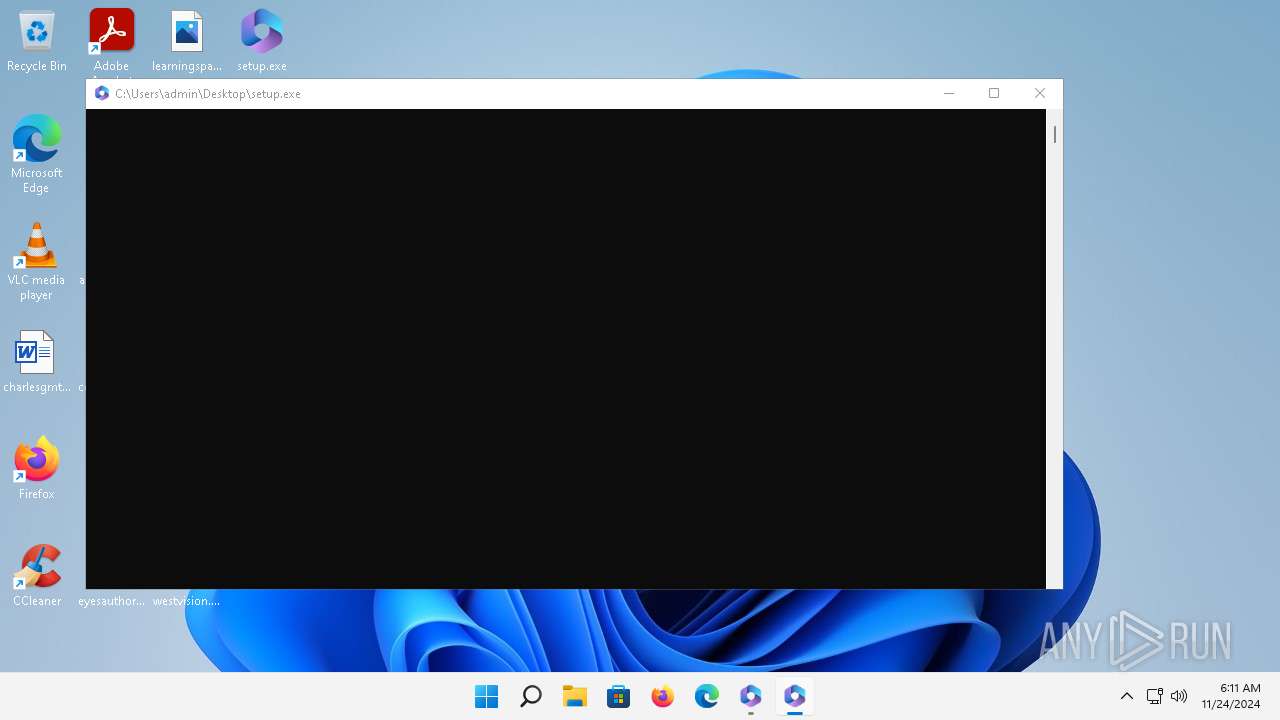
Total processes
124
Monitored processes
6
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2648 | "C:\Users\admin\Desktop\setup.exe" | C:\Users\admin\Desktop\setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft 365 and Office Exit code: 0 Version: 16.0.18129.20030 Modules
| |||||||||||||||
| 3508 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3752 | setup.exe RELAUNCHED | C:\Users\admin\Desktop\setup.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft 365 and Office Exit code: 0 Version: 16.0.18129.20030 Modules
| |||||||||||||||
| 3880 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4796 | "C:\Users\admin\Desktop\setup.exe" ELEVATED sid=S-1-5-21-166304369-59083888-3082702900-1001 RELAUNCHED | C:\Users\admin\Desktop\setup.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft 365 and Office Exit code: 0 Version: 16.0.18129.20030 Modules
| |||||||||||||||
| 5360 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 612
Read events
8 470
Write events
138
Delete events
4
Modification events
| (PID) Process: | (3752) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (3752) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (3752) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (3752) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (3752) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (3752) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (3752) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (3752) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
| (PID) Process: | (3752) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ru-ru |
Value: 2 | |||
| (PID) Process: | (3752) setup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | tr-tr |
Value: 2 | |||
Executable files
0
Suspicious files
7
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4796 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\B219E9BD-05CF-4740-B912-AB653C39907A | xml | |
MD5:B77B40347BAE32E78D28F2A04F30BAA7 | SHA256:9391D82BBE4341715059A46DA8188C72EC7971B4B6915C398F168791284159A1 | |||
| 3752 | setup.exe | C:\Users\admin\AppData\Local\Temp\DESKTOP-BFTPUHP-20241124-0611a.log | text | |
MD5:42716A956905ECE99BE58593D2FDF172 | SHA256:28B15685E3CB9CFBD4A682BDDE488817E5349B04F886208A93BBFB7A982E9F0F | |||
| 4796 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\setup.exe.db-journal | binary | |
MD5:F7B614C72F3F6A642C28BF04B2CF0F3F | SHA256:F531BC8706D045ACA2B2DB481278282545A61CCFFAA08F5800868788C85129A9 | |||
| 4796 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\setup.exe.db-shm | binary | |
MD5:8FEA8E227CA209669E6EE05F55A5C336 | SHA256:E57D5886853AE8128170BBD555D615FE27AEF57EBE119F2DC591072617D7B18B | |||
| 4796 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\setup.exe.db-wal | binary | |
MD5:DD1F9483F18E4AB1565F67B38CE3A8B7 | SHA256:DA94C3AADDF41738E2E6F9186ECAF9C44BFC0E7134F669DE39D2C59C0B19CB35 | |||
| 4796 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\setup.exe.db | binary | |
MD5:34ED672C6E690044FCC370709EE1E0AB | SHA256:10A17C4E5B5AFCCE8AE5A13F879E270AE8DB598BDE3C483A2B3BE867F4FA5418 | |||
| 4796 | setup.exe | C:\Users\admin\AppData\Local\Temp\DESKTOP-BFTPUHP-20241124-0611.log | text | |
MD5:9D10D293610C5D000C43F34F11B5479B | SHA256:B28A4B593528D1FF67A9FCB7A93E486C9D1AC9D24E16D27948267160DD9CCFCD | |||
| 3752 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\setup.exe.db-wal | binary | |
MD5:61495DA61B2CE09EF08A978DB264D87F | SHA256:32FF84820002415F9F736EC5AC93260C3D53CEBB73A90984A12CF311D129BFC8 | |||
| 3752 | setup.exe | C:\Users\admin\AppData\Local\Microsoft\Office\OTele\setup.exe.db-shm | binary | |
MD5:DFCCD307AA9C1B21C5D195DFCFBE35E8 | SHA256:7D8957EF86660594E020914C64D7B9329241D35CF2B36D3580242BE6C59F292B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
33
TCP/UDP connections
42
DNS requests
34
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2316 | MoUsoCoreWorker.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?5fde02a172d3ca44 | GB | — | — | whitelisted |
— | — | GET | 200 | 23.55.161.164:80 | http://www.msftconnecttest.com/connecttest.txt | DE | text | 22 b | whitelisted |
5488 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | US | binary | 471 b | whitelisted |
5488 | firefox.exe | POST | 200 | 2.16.241.8:80 | http://r10.o.lencr.org/ | DE | binary | 504 b | whitelisted |
5488 | firefox.exe | POST | 200 | 2.16.241.15:80 | http://r10.o.lencr.org/ | DE | binary | 504 b | whitelisted |
5488 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | US | binary | 471 b | whitelisted |
— | — | HEAD | 200 | 23.53.114.19:443 | https://fs.microsoft.com/fs/windows/config.json | US | — | — | unknown |
5488 | firefox.exe | POST | 200 | 2.16.241.8:80 | http://r10.o.lencr.org/ | DE | binary | 504 b | whitelisted |
— | — | GET | 200 | 52.113.194.132:443 | https://ecs.office.com/config/v2/Office/officeclicktorun/16.0.18129.20030/Production/CC?&EcsCanary=1&Clientid=%7b72FA513C-1434-461C-BFDF-DCC1864A73F3%7d&Application=officeclicktorun&Platform=win32&Version=16.0.18129.20030&MsoVersion=16.0.18129.20030&SDX=fa000000069.1.0.2211.2001&SDXfa000000069=1.0.2211.2001&SDX=fa000000070.1.0.2211.4002&SDXfa000000070=1.0.2211.4002&OfficeFirstRunSDXVersion=1.0.2211.2001&ProcessName=C2R.exe&Audience=Production&Build=ship&Architecture=x86&PerpetualLicense=2021&LicenseCategory=13&LicenseSKU=HomeBusiness2021Retail&OsVersion=10.0&OsBuild=22000&Channel=CC&InstallType=C2R&ProviderId=9fcc1350af7dd254&SessionId=%7b86A67698-1241-4982-BC4C-E54E9DDDEB89%7d&LabMachine=false | US | binary | 91.1 Kb | whitelisted |
— | — | GET | 200 | 52.113.194.132:443 | https://ecs.office.com/config/v2/Office/officeclicktorun/16.0.18129.20030/Production/CC?&EcsCanary=1&Clientid=%7b72FA513C-1434-461C-BFDF-DCC1864A73F3%7d&Application=officeclicktorun&Platform=win32&Version=16.0.18129.20030&MsoVersion=16.0.18129.20030&SDX=fa000000069.1.0.2211.2001&SDXfa000000069=1.0.2211.2001&SDX=fa000000070.1.0.2211.4002&SDXfa000000070=1.0.2211.4002&OfficeFirstRunSDXVersion=1.0.2211.2001&ProcessName=C2R.exe&Audience=Production&Build=ship&Architecture=x86&PerpetualLicense=2021&LicenseCategory=13&LicenseSKU=HomeBusiness2021Retail&OsVersion=10.0&OsBuild=22000&Channel=CC&InstallType=C2R&ProviderId=9fcc1350af7dd254&SessionId=%7bEB061012-6A36-4F8B-AC7E-256E26636EC7%7d&LabMachine=false | US | binary | 91.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3484 | rundll32.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6848 | OfficeC2RClient.exe | 52.109.32.97:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
5488 | firefox.exe | 34.120.208.123:443 | incoming.telemetry.mozilla.org | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
5488 | firefox.exe | 34.149.100.209:443 | firefox.settings.services.mozilla.com | GOOGLE | US | whitelisted |
5552 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 23.55.161.164:80 | — | Akamai International B.V. | DE | unknown |
2316 | MoUsoCoreWorker.exe | 52.167.17.97:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2316 | MoUsoCoreWorker.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3752 | setup.exe | 52.113.194.132:443 | ecs.office.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
incoming.telemetry.mozilla.org |
| whitelisted |
telemetry-incoming.r53-2.services.mozilla.com |
| whitelisted |
prod.remote-settings.prod.webservices.mozgcp.net |
| whitelisted |
google.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ecs.office.com |
| whitelisted |
r10.o.lencr.org |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Microsoft Connection Test |