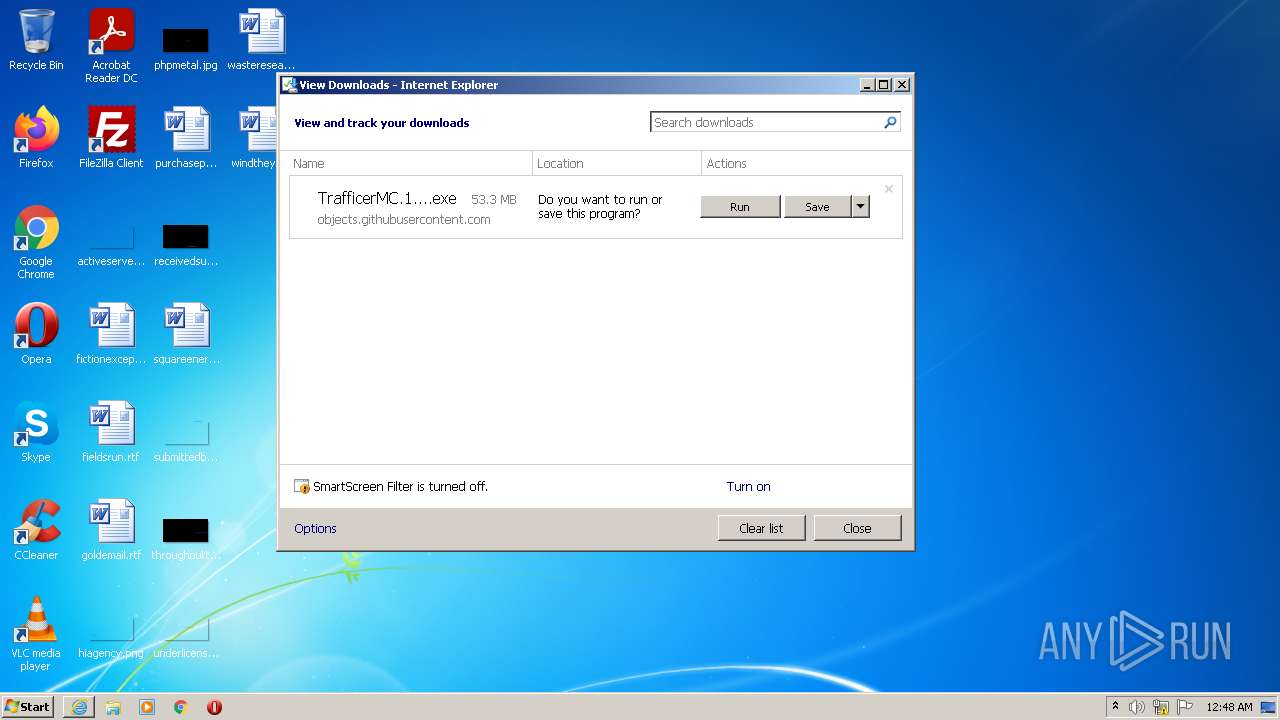
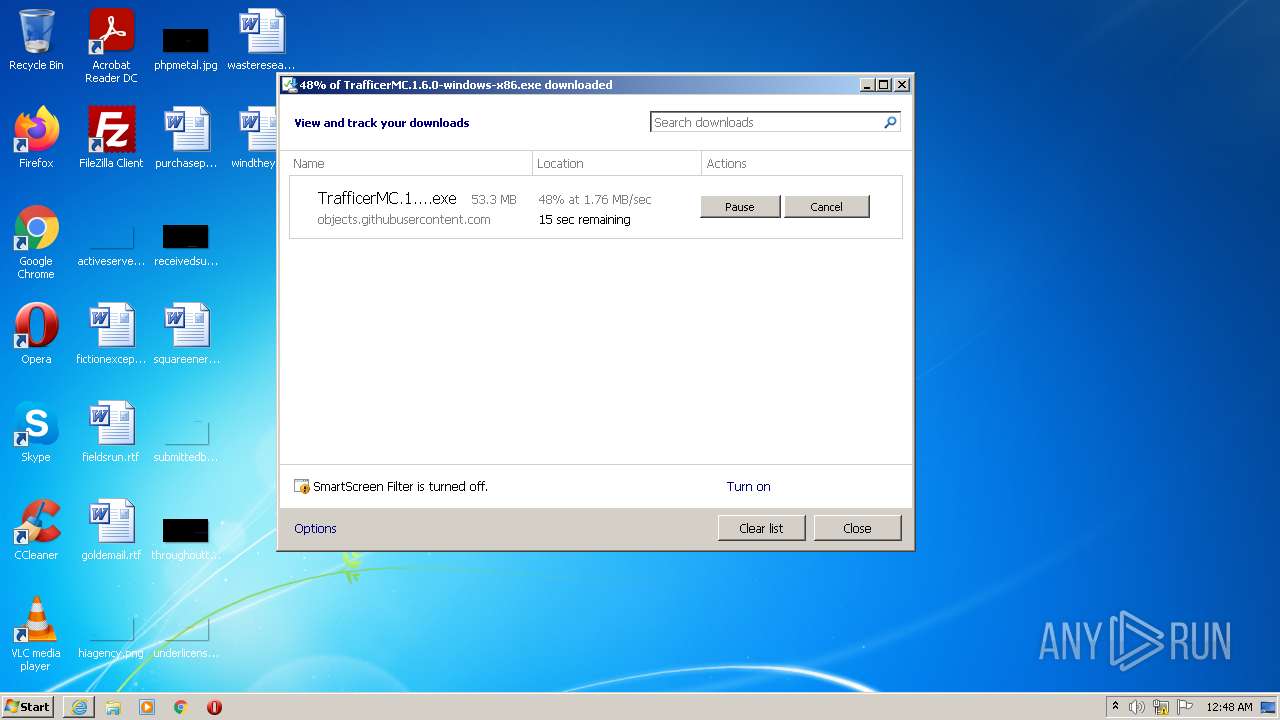
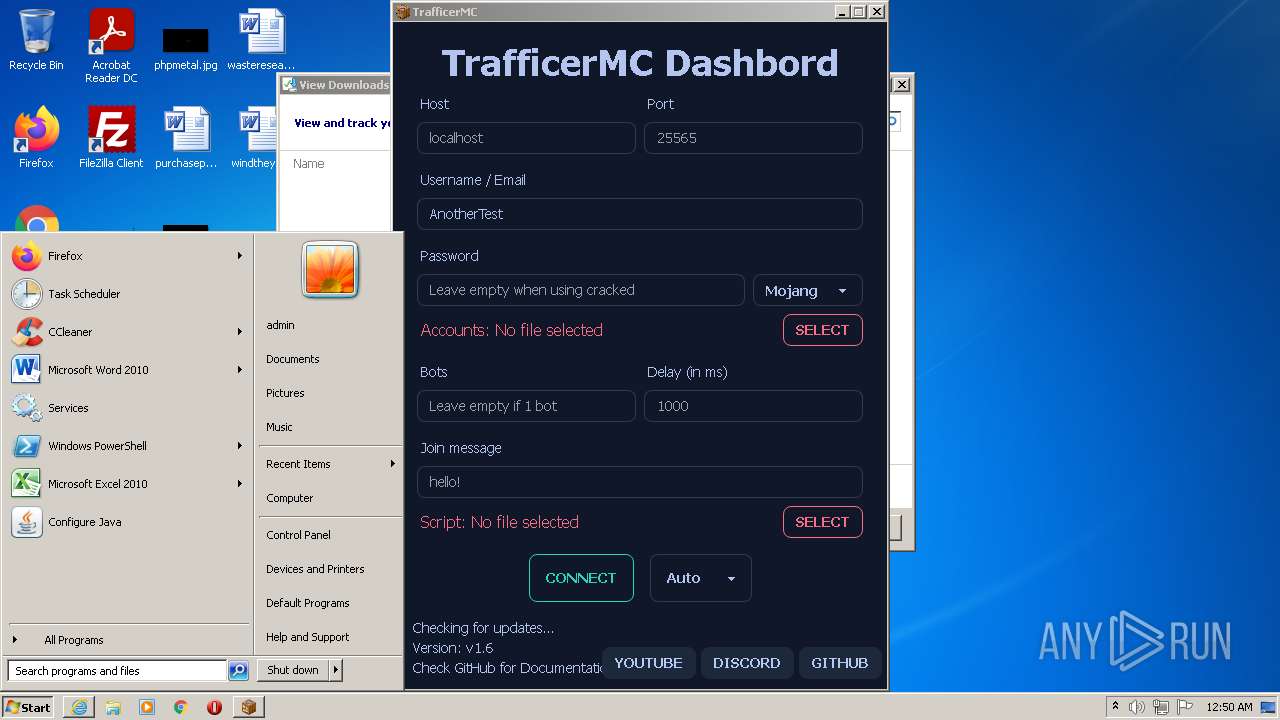
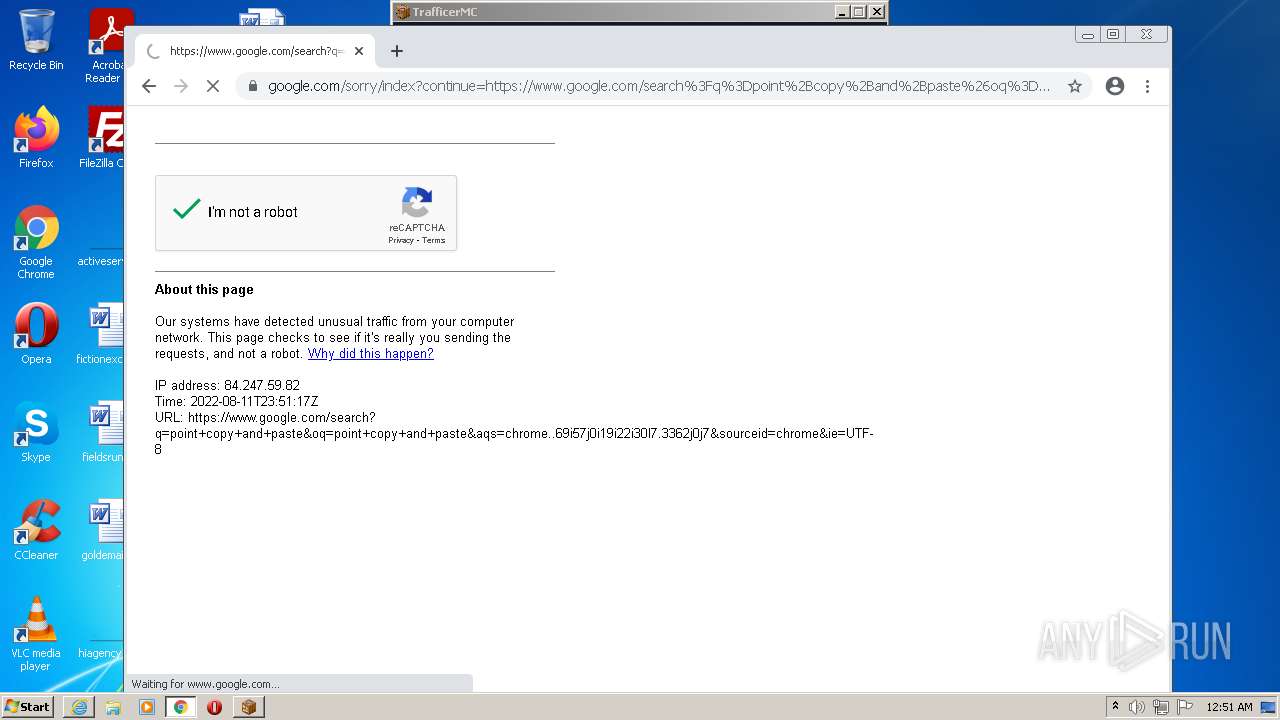
| URL: | https://github.com/RattlesHyper/TrafficerMC/releases/download/v1.6/TrafficerMC.1.6.0-windows-x86.exe |
| Full analysis: | https://app.any.run/tasks/4121bffc-9193-4a2f-b3e5-31a4775e45b7 |
| Verdict: | Malicious activity |
| Analysis date: | August 11, 2022, 23:47:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1AC8605C840589DDC9DC710934F1DE96 |
| SHA1: | F217B6421CEC2F42B9756312A17957A4EFD9B7F3 |
| SHA256: | D6EF71EEB9CA33DB7CB797D40608098E806A9921F4E2257914DBBBD570C8B48A |
| SSDEEP: | 3:N8tEdkRR4xIMHNJArkCmmXqDMHqTevnAdA:2uiRR4xI2MsmXqDJSn4A |
MALICIOUS
Drops executable file immediately after starts
- iexplore.exe (PID: 584)
- TrafficerMC.1.6.0-windows-x86.exe (PID: 2412)
Application was dropped or rewritten from another process
- TrafficerMC.1.6.0-windows-x86.exe (PID: 2412)
Loads dropped or rewritten executable
- TrafficerMC.1.6.0-windows-x86.exe (PID: 2412)
- TrafficerMC.exe (PID: 2104)
- TrafficerMC.exe (PID: 3400)
- TrafficerMC.exe (PID: 1036)
- TrafficerMC.exe (PID: 544)
- TrafficerMC.exe (PID: 532)
- TrafficerMC.exe (PID: 3776)
- TrafficerMC.exe (PID: 2480)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 584)
- TrafficerMC.1.6.0-windows-x86.exe (PID: 2412)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 584)
Drops a file with a compile date too recent
- iexplore.exe (PID: 584)
- TrafficerMC.1.6.0-windows-x86.exe (PID: 2412)
Checks supported languages
- TrafficerMC.1.6.0-windows-x86.exe (PID: 2412)
- TrafficerMC.exe (PID: 3400)
- TrafficerMC.exe (PID: 544)
- TrafficerMC.exe (PID: 1036)
- TrafficerMC.exe (PID: 532)
- TrafficerMC.exe (PID: 2104)
- TrafficerMC.exe (PID: 2480)
- TrafficerMC.exe (PID: 3776)
Reads Environment values
- TrafficerMC.exe (PID: 3400)
- TrafficerMC.exe (PID: 544)
- TrafficerMC.exe (PID: 2480)
- TrafficerMC.exe (PID: 3776)
Reads the computer name
- TrafficerMC.1.6.0-windows-x86.exe (PID: 2412)
- TrafficerMC.exe (PID: 2104)
- TrafficerMC.exe (PID: 1036)
- TrafficerMC.exe (PID: 532)
- TrafficerMC.exe (PID: 3400)
- TrafficerMC.exe (PID: 3776)
- TrafficerMC.exe (PID: 2480)
Application launched itself
- TrafficerMC.exe (PID: 3400)
Modifies files in Chrome extension folder
- chrome.exe (PID: 368)
INFO
Reads the computer name
- iexplore.exe (PID: 2364)
- iexplore.exe (PID: 584)
- chrome.exe (PID: 368)
- chrome.exe (PID: 872)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 616)
- chrome.exe (PID: 1152)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 4048)
Application launched itself
- iexplore.exe (PID: 2364)
- chrome.exe (PID: 368)
Checks supported languages
- iexplore.exe (PID: 2364)
- iexplore.exe (PID: 584)
- chrome.exe (PID: 368)
- chrome.exe (PID: 4052)
- chrome.exe (PID: 1712)
- chrome.exe (PID: 872)
- chrome.exe (PID: 500)
- chrome.exe (PID: 3128)
- chrome.exe (PID: 1484)
- chrome.exe (PID: 2208)
- chrome.exe (PID: 4000)
- chrome.exe (PID: 1040)
- chrome.exe (PID: 4056)
- chrome.exe (PID: 3548)
- chrome.exe (PID: 1412)
- chrome.exe (PID: 3440)
- chrome.exe (PID: 1160)
- chrome.exe (PID: 2224)
- chrome.exe (PID: 2204)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 1104)
- chrome.exe (PID: 3440)
- chrome.exe (PID: 1900)
- chrome.exe (PID: 1152)
- chrome.exe (PID: 2200)
- chrome.exe (PID: 616)
- chrome.exe (PID: 2584)
- chrome.exe (PID: 2116)
Changes internet zones settings
- iexplore.exe (PID: 2364)
Checks Windows Trust Settings
- iexplore.exe (PID: 584)
- iexplore.exe (PID: 2364)
Reads settings of System Certificates
- iexplore.exe (PID: 584)
- iexplore.exe (PID: 2364)
- TrafficerMC.exe (PID: 3400)
- chrome.exe (PID: 872)
Reads internet explorer settings
- iexplore.exe (PID: 584)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2364)
Modifies the phishing filter of IE
- iexplore.exe (PID: 2364)
Changes settings of System certificates
- iexplore.exe (PID: 2364)
Reads the date of Windows installation
- iexplore.exe (PID: 2364)
- chrome.exe (PID: 1152)
Manual execution by user
- chrome.exe (PID: 368)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
75
Monitored processes
36
Malicious processes
4
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1028,9470014867814396005,786162567303862875,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1944 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 532 | "C:\Users\admin\AppData\Local\Temp\2BdmL2kTzYZ43JE819YeV9x5k49\TrafficerMC.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\trafficermc" --mojo-platform-channel-handle=1276 --field-trial-handle=1044,i,16012447423040348761,11834861076781479229,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Users\admin\AppData\Local\Temp\2BdmL2kTzYZ43JE819YeV9x5k49\TrafficerMC.exe | TrafficerMC.exe | ||||||||||||
User: admin Company: RattlesHyper Integrity Level: MEDIUM Description: TrafficerMC Exit code: 0 Version: 1.6.0 Modules
| |||||||||||||||
| 544 | "C:\Users\admin\AppData\Local\Temp\2BdmL2kTzYZ43JE819YeV9x5k49\TrafficerMC.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\trafficermc" --app-path="C:\Users\admin\AppData\Local\Temp\2BdmL2kTzYZ43JE819YeV9x5k49\resources\app.asar" --no-sandbox --no-zygote --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --mojo-platform-channel-handle=1524 --field-trial-handle=1044,i,16012447423040348761,11834861076781479229,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:1 | C:\Users\admin\AppData\Local\Temp\2BdmL2kTzYZ43JE819YeV9x5k49\TrafficerMC.exe | — | TrafficerMC.exe | |||||||||||
User: admin Company: RattlesHyper Integrity Level: MEDIUM Description: TrafficerMC Exit code: 0 Version: 1.6.0 Modules
| |||||||||||||||
| 584 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2364 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1028,9470014867814396005,786162567303862875,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=2020 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1028,9470014867814396005,786162567303862875,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1404 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1036 | "C:\Users\admin\AppData\Local\Temp\2BdmL2kTzYZ43JE819YeV9x5k49\TrafficerMC.exe" --type=gpu-process --user-data-dir="C:\Users\admin\AppData\Roaming\trafficermc" --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=996 --field-trial-handle=1044,i,16012447423040348761,11834861076781479229,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:2 | C:\Users\admin\AppData\Local\Temp\2BdmL2kTzYZ43JE819YeV9x5k49\TrafficerMC.exe | — | TrafficerMC.exe | |||||||||||
User: admin Company: RattlesHyper Integrity Level: LOW Description: TrafficerMC Exit code: 0 Version: 1.6.0 Modules
| |||||||||||||||
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1028,9470014867814396005,786162567303862875,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3272 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1028,9470014867814396005,786162567303862875,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3732 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
30 054
Read events
29 804
Write events
246
Delete events
4
Modification events
| (PID) Process: | (2364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30977500 | |||
| (PID) Process: | (2364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30977500 | |||
| (PID) Process: | (2364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2364) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
23
Suspicious files
217
Text files
170
Unknown types
146
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | der | |
MD5:— | SHA256:— | |||
| 2364 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{0763D12C-19D0-11ED-9A81-1203334A04AF}.dat | binary | |
MD5:— | SHA256:— | |||
| 2364 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF3E0B07EF0513ADAA.TMP | gmc | |
MD5:— | SHA256:— | |||
| 584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_A4CF52CCA82D7458083F7280801A3A04 | binary | |
MD5:— | SHA256:— | |||
| 584 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\TrafficerMC.1.6.0-windows-x86[1].exe | executable | |
MD5:— | SHA256:— | |||
| 584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | der | |
MD5:— | SHA256:— | |||
| 584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\50CD3D75D026C82E2E718570BD6F44D0_60E83F2095C16CA099C94596E7B8AA5D | der | |
MD5:— | SHA256:— | |||
| 584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:— | SHA256:— | |||
| 584 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\50CD3D75D026C82E2E718570BD6F44D0_60E83F2095C16CA099C94596E7B8AA5D | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
58
DNS requests
42
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
856 | svchost.exe | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
2364 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2364 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
584 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAfy81yHqHeveu%2FpR5k1Jb0%3D | US | der | 471 b | whitelisted |
584 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.70 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.69 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 43.4 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.69 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
584 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2364 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
584 | iexplore.exe | 185.199.108.133:443 | objects.githubusercontent.com | GitHub, Inc. | NL | malicious |
2364 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2364 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2364 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
584 | iexplore.exe | 185.199.109.133:443 | objects.githubusercontent.com | GitHub, Inc. | NL | malicious |
2364 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
2364 | iexplore.exe | 96.16.143.41:443 | go.microsoft.com | Akamai International B.V. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.microsoft.com |
| whitelisted |
github.com |
| malicious |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
objects.githubusercontent.com |
| shared |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |