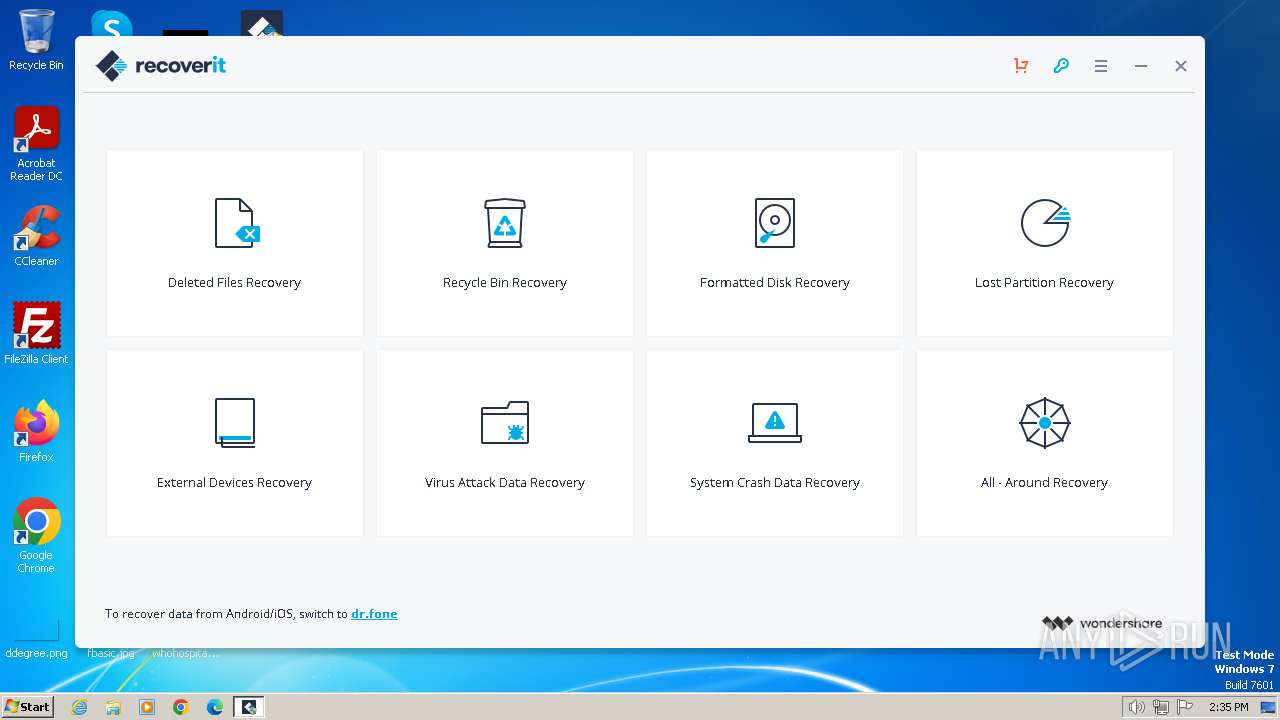
| File name: | recoverit_setup_full4174.exe |
| Full analysis: | https://app.any.run/tasks/e987347b-711c-4863-9f4d-a8f65a198e43 |
| Verdict: | Malicious activity |
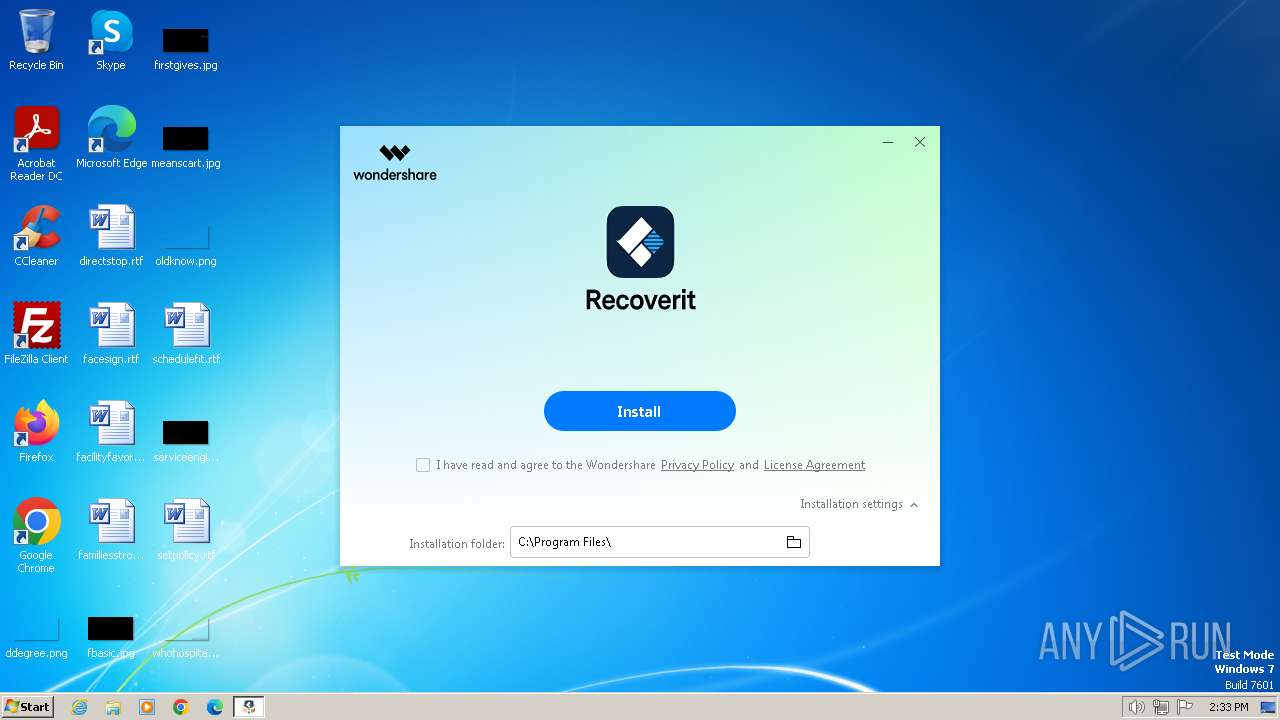
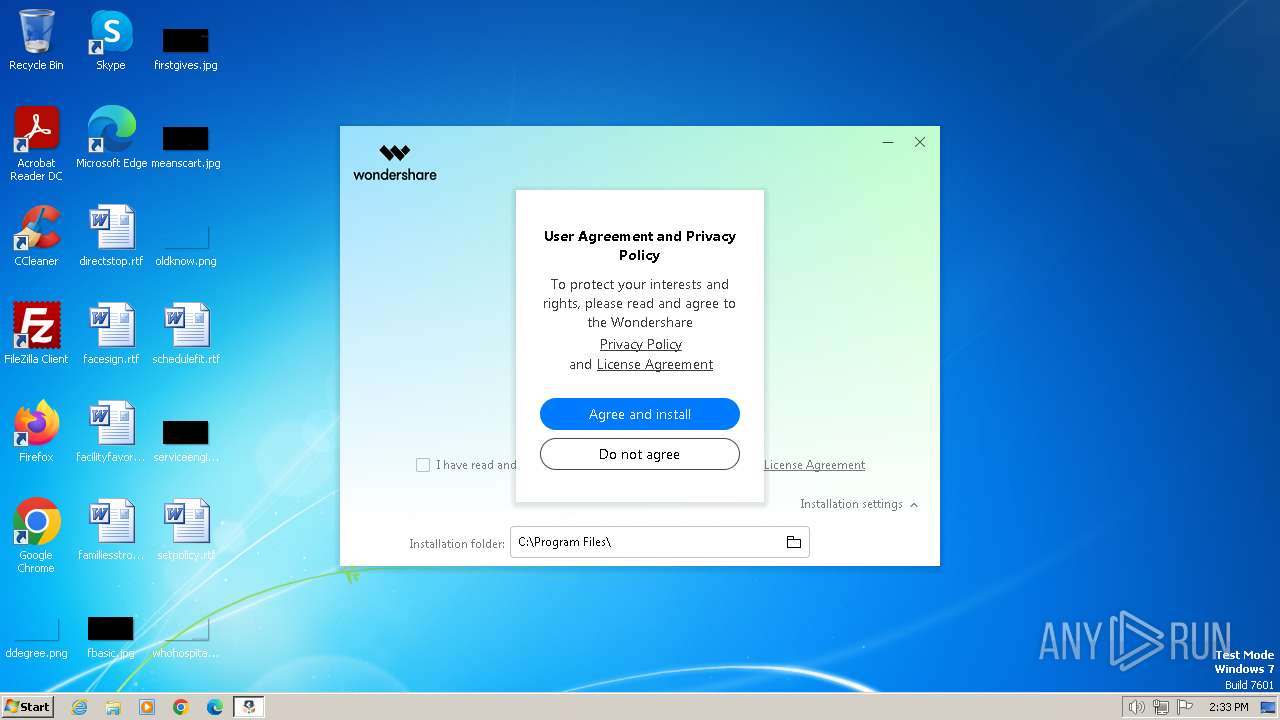
| Analysis date: | February 13, 2024, 14:33:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A12A6AB201F3FCF5A224B83AE36F0107 |
| SHA1: | 25DDB238BC8F4514C0004BADBFB7723816D6D269 |
| SHA256: | D6EEFB70FF36E758677FDF5B6F6C7873754421C430CA2206F307CBAA3326D832 |
| SSDEEP: | 98304:cJFfX3z+2Pwwgpzp5suNP4Uv5+/wDMXC0IPWgB:h |
MALICIOUS
Drops the executable file immediately after the start
- recoverit_setup_full4174.exe (PID: 2036)
- recoverit_full4174.exe (PID: 3912)
- WAFSetup.exe (PID: 1368)
- WAFSetup.tmp (PID: 1308)
- recoverit_full4174.tmp (PID: 3308)
- WsAppService.exe (PID: 920)
Actions looks like stealing of personal data
- WAFSetup.tmp (PID: 1308)
Creates a writable file in the system directory
- WAFSetup.tmp (PID: 1308)
SUSPICIOUS
Reads Microsoft Outlook installation path
- recoverit_setup_full4174.exe (PID: 2036)
Reads the Internet Settings
- recoverit_setup_full4174.exe (PID: 2036)
- RegAsm.exe (PID: 1336)
- RegAsm.exe (PID: 2968)
- RegAsm.exe (PID: 3680)
- RegAsm.exe (PID: 2384)
- RegAsm.exe (PID: 1784)
- RegAsm.exe (PID: 552)
- recoverit_full4174.tmp (PID: 3308)
- diskfeedback.exe (PID: 3484)
- checkwaf.exe (PID: 4092)
- WsAppClient.exe (PID: 324)
- WsAppClient.exe (PID: 3516)
- recoverit.exe (PID: 3760)
Reads security settings of Internet Explorer
- recoverit_setup_full4174.exe (PID: 2036)
- RegAsm.exe (PID: 1336)
- RegAsm.exe (PID: 2968)
- RegAsm.exe (PID: 3680)
- RegAsm.exe (PID: 2384)
- RegAsm.exe (PID: 1784)
- RegAsm.exe (PID: 552)
- recoverit.exe (PID: 3760)
- recoverit_full4174.tmp (PID: 3308)
Reads Internet Explorer settings
- recoverit_setup_full4174.exe (PID: 2036)
Likely accesses (executes) a file from the Public directory
- NFWCHK.exe (PID: 2124)
- recoverit_full4174.exe (PID: 3912)
- recoverit_full4174.tmp (PID: 3308)
Executable content was dropped or overwritten
- recoverit_setup_full4174.exe (PID: 2036)
- recoverit_full4174.tmp (PID: 3308)
- WAFSetup.exe (PID: 1368)
- WAFSetup.tmp (PID: 1308)
- recoverit_full4174.exe (PID: 3912)
- WsAppService.exe (PID: 920)
Checks Windows Trust Settings
- recoverit_setup_full4174.exe (PID: 2036)
Connects to unusual port
- recoverit_setup_full4174.exe (PID: 2036)
Reads settings of System Certificates
- recoverit_setup_full4174.exe (PID: 2036)
- recoverit_full4174.tmp (PID: 3308)
Process requests binary or script from the Internet
- recoverit_setup_full4174.exe (PID: 2036)
Process drops legitimate windows executable
- recoverit_full4174.tmp (PID: 3308)
- WAFSetup.tmp (PID: 1308)
Reads the Windows owner or organization settings
- recoverit_full4174.tmp (PID: 3308)
- WAFSetup.tmp (PID: 1308)
The process drops C-runtime libraries
- recoverit_full4174.tmp (PID: 3308)
Searches for installed software
- RegAsm.exe (PID: 1784)
- WsAppService.exe (PID: 920)
Creates/Modifies COM task schedule object
- RegAsm.exe (PID: 552)
- RegAsm.exe (PID: 1784)
Executes as Windows Service
- WsAppService.exe (PID: 920)
Creates or modifies Windows services
- WAFSetup.tmp (PID: 1308)
INFO
Checks supported languages
- recoverit_setup_full4174.exe (PID: 2036)
- NFWCHK.exe (PID: 2124)
- recoverit_full4174.exe (PID: 3912)
- recoverit_full4174.tmp (PID: 3308)
- WAFSetup.exe (PID: 1368)
- WAFSetup.tmp (PID: 1308)
- RegAsm.exe (PID: 2968)
- RegAsm.exe (PID: 3680)
- RegAsm.exe (PID: 2384)
- RegAsm.exe (PID: 1784)
- RegAsm.exe (PID: 552)
- WsAppService.exe (PID: 920)
- RegAsm.exe (PID: 1336)
- diskfeedback.exe (PID: 3484)
- checkwaf.exe (PID: 4092)
- recoverit.exe (PID: 3760)
- WsAppClient.exe (PID: 324)
- WsAppClient.exe (PID: 3516)
- wget.exe (PID: 2300)
- DiskAnalyzer.exe (PID: 3776)
Reads the computer name
- recoverit_setup_full4174.exe (PID: 2036)
- NFWCHK.exe (PID: 2124)
- recoverit_full4174.tmp (PID: 3308)
- WAFSetup.tmp (PID: 1308)
- RegAsm.exe (PID: 1336)
- RegAsm.exe (PID: 2968)
- RegAsm.exe (PID: 3680)
- RegAsm.exe (PID: 2384)
- RegAsm.exe (PID: 1784)
- RegAsm.exe (PID: 552)
- WsAppService.exe (PID: 920)
- recoverit.exe (PID: 3760)
- checkwaf.exe (PID: 4092)
- diskfeedback.exe (PID: 3484)
- WsAppClient.exe (PID: 324)
- WsAppClient.exe (PID: 3516)
- DiskAnalyzer.exe (PID: 3776)
- wget.exe (PID: 2300)
Checks proxy server information
- recoverit_setup_full4174.exe (PID: 2036)
- RegAsm.exe (PID: 1784)
- WsAppService.exe (PID: 920)
Reads the software policy settings
- recoverit_setup_full4174.exe (PID: 2036)
- recoverit_full4174.tmp (PID: 3308)
Reads the machine GUID from the registry
- NFWCHK.exe (PID: 2124)
- recoverit_setup_full4174.exe (PID: 2036)
- RegAsm.exe (PID: 1336)
- RegAsm.exe (PID: 2968)
- RegAsm.exe (PID: 3680)
- RegAsm.exe (PID: 2384)
- RegAsm.exe (PID: 1784)
- RegAsm.exe (PID: 552)
- recoverit_full4174.tmp (PID: 3308)
- WsAppService.exe (PID: 920)
- diskfeedback.exe (PID: 3484)
- checkwaf.exe (PID: 4092)
- WsAppClient.exe (PID: 324)
- recoverit.exe (PID: 3760)
- DiskAnalyzer.exe (PID: 3776)
- WsAppClient.exe (PID: 3516)
Create files in a temporary directory
- recoverit_full4174.exe (PID: 3912)
- recoverit_full4174.tmp (PID: 3308)
- WAFSetup.exe (PID: 1368)
- recoverit_setup_full4174.exe (PID: 2036)
- WAFSetup.tmp (PID: 1308)
Creates files or folders in the user directory
- recoverit_full4174.tmp (PID: 3308)
- recoverit_setup_full4174.exe (PID: 2036)
Creates files in the program directory
- recoverit_setup_full4174.exe (PID: 2036)
- WAFSetup.tmp (PID: 1308)
- recoverit_full4174.tmp (PID: 3308)
- RegAsm.exe (PID: 2384)
- RegAsm.exe (PID: 1784)
- RegAsm.exe (PID: 552)
- WsAppService.exe (PID: 920)
- recoverit.exe (PID: 3760)
- WsAppClient.exe (PID: 324)
- WsAppClient.exe (PID: 3516)
- DiskAnalyzer.exe (PID: 3776)
- wget.exe (PID: 2300)
- chrome.exe (PID: 2828)
- checkwaf.exe (PID: 4092)
Creates a software uninstall entry
- recoverit_full4174.tmp (PID: 3308)
Reads Environment values
- RegAsm.exe (PID: 1784)
- WsAppService.exe (PID: 920)
- diskfeedback.exe (PID: 3484)
- checkwaf.exe (PID: 4092)
- WsAppClient.exe (PID: 324)
- recoverit.exe (PID: 3760)
- WsAppClient.exe (PID: 3516)
Application launched itself
- chrome.exe (PID: 2828)
The process uses the downloaded file
- chrome.exe (PID: 1748)
- chrome.exe (PID: 2052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (16.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (14.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.4) |
| .exe | | | Win32 Executable (generic) (2.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2024:01:13 08:19:46+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 1278976 |
| InitializedDataSize: | 718336 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1069f0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.4.18 |
| ProductVersionNumber: | 4.0.4.18 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | recoverit---data-recovery-(cpc)_setup_full4174.exe |
| FileVersion: | 4.0.4.18 |
| LegalCopyright: | Copyright©2023 Wondershare. All rights reserved. |
| ProductName: | Recoverit - Data Recovery (CPC) |
| ProductVersion: | 12.0.19 |
Total processes
89
Monitored processes
36
Malicious processes
8
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Program Files\Wondershare\WAF\2.4.3.242\WsAppClient.exe" -Embedding | C:\Program Files\Wondershare\WAF\2.4.3.242\WsAppClient.exe | svchost.exe | ||||||||||||
User: admin Company: Wondershare Integrity Level: HIGH Description: Wondershare Passport Exit code: 0 Version: 2.4.3.242 Modules
| |||||||||||||||
| 552 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" "C:\Program Files\Wondershare\WAF\2.4.3.242\WsAppClient.exe" /codebase /tlb:"C:\Program Files\Wondershare\WAF\WsAppClient.tlb" /nologo | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | WAFSetup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 920 | "C:\Program Files\Wondershare\WAF\2.4.3.242\WsAppService.exe" | C:\Program Files\Wondershare\WAF\2.4.3.242\WsAppService.exe | services.exe | ||||||||||||
User: SYSTEM Company: Wondershare Integrity Level: SYSTEM Description: Wondershare Passport Exit code: 0 Version: 2.4.3.242 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3600 --field-trial-handle=1016,i,6840728537681938771,12719501043712096598,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1308 | "C:\Users\admin\AppData\Local\Temp\is-IDKQ4.tmp\WAFSetup.tmp" /SL5="$15018E,7542491,140288,C:\Users\admin\AppData\Local\Temp\is-MAGMT.tmp\WAFSetup.exe" /verysilent /NORESTART | C:\Users\admin\AppData\Local\Temp\is-IDKQ4.tmp\WAFSetup.tmp | WAFSetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1336 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe" "C:\Program Files\Wondershare\WAF\2.4.3.242\WsAppCommon.dll" /u /nologo | C:\Windows\Microsoft.NET\Framework\v4.0.30319\RegAsm.exe | — | WAFSetup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.3761.0 built by: NET48REL1 Modules
| |||||||||||||||
| 1368 | "C:\Users\admin\AppData\Local\Temp\is-MAGMT.tmp\WAFSetup.exe" /verysilent /NORESTART | C:\Users\admin\AppData\Local\Temp\is-MAGMT.tmp\WAFSetup.exe | recoverit_full4174.tmp | ||||||||||||
User: admin Company: Wondershare Integrity Level: HIGH Description: Wondershare Passport Exit code: 0 Version: 2.4.3.242 Modules
| |||||||||||||||
| 1404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=3340 --field-trial-handle=1016,i,6840728537681938771,12719501043712096598,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1504 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=109.0.5414.120 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x64f68b38,0x64f68b48,0x64f68b54 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3392 --field-trial-handle=1016,i,6840728537681938771,12719501043712096598,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: HIGH Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
35 769
Read events
34 915
Write events
790
Delete events
64
Modification events
| (PID) Process: | (2036) recoverit_setup_full4174.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WafCX |
| Operation: | write | Name: | 4174 |
Value: sku-ppc | |||
| (PID) Process: | (2036) recoverit_setup_full4174.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wondershare\Wondershare Helper Compact |
| Operation: | write | Name: | ClientSign |
Value: {3b63fee4-23fe-49cb-87dc-bae0284ddd22G} | |||
| (PID) Process: | (2036) recoverit_setup_full4174.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wondershare\WAF |
| Operation: | write | Name: | ClientSign |
Value: {3b63fee4-23fe-49cb-87dc-bae0284ddd22G} | |||
| (PID) Process: | (2036) recoverit_setup_full4174.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2036) recoverit_setup_full4174.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2036) recoverit_setup_full4174.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2036) recoverit_setup_full4174.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2036) recoverit_setup_full4174.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2036) recoverit_setup_full4174.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2036) recoverit_setup_full4174.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
191
Suspicious files
47
Text files
301
Unknown types
49
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2036 | recoverit_setup_full4174.exe | C:\Users\Public\Documents\Wondershare\recoverit_full4174.exe.~P2S | — | |
MD5:— | SHA256:— | |||
| 2036 | recoverit_setup_full4174.exe | C:\Users\admin\AppData\Local\Temp\wsduilib.log | text | |
MD5:36247BC9BBA7C6893D8A766873E3423C | SHA256:42927A44997732E726F23D08FD431C516DD34D7610C35A0D34EC967C8DB88B44 | |||
| 2036 | recoverit_setup_full4174.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_23FFFDCAABB8E63694AD1202ED02BF57 | binary | |
MD5:8224535768B14E8758C04DBDFE396867 | SHA256:AC74806E2F19E3B85E6BAE7A24C2DEFFBB5699178B6D6486F2EC5083DDAEFF46 | |||
| 2036 | recoverit_setup_full4174.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | der | |
MD5:AC89A852C2AAA3D389B2D2DD312AD367 | SHA256:0B720E19270C672F9B6E0EC40B468AC49376807DE08A814573FE038779534F45 | |||
| 2036 | recoverit_setup_full4174.exe | C:\Users\Public\Documents\Wondershare\NFWCHK.exe.config | xml | |
MD5:5BABF2A106C883A8E216F768DB99AD51 | SHA256:9E676A617EB0D0535AC05A67C0AE0C0E12D4E998AB55AC786A031BFC25E28300 | |||
| 2036 | recoverit_setup_full4174.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_23FFFDCAABB8E63694AD1202ED02BF57 | binary | |
MD5:E15485214094540074C79D067FF262CF | SHA256:BD0E4A3AA60C666B82FF5268E4EAB76E81A97D0341869AD7DA43B66069FED127 | |||
| 2036 | recoverit_setup_full4174.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | binary | |
MD5:86D8E8C56D10E717C13B4F41CC4D89ED | SHA256:CB7FCBE7772F61185FAD46BB438C406AAC127F451AD717A6EB92FD05536A81B1 | |||
| 2036 | recoverit_setup_full4174.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\javascript_call_native[1].js | text | |
MD5:B9DA127236EFDB755F568304B5EF3044 | SHA256:01C839C0A9C47DC571175312EBC208EAE6FF28CED3A3EFA13C1EE81CD9764F71 | |||
| 2036 | recoverit_setup_full4174.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\24BD96D5497F70B3F510A6B53CD43F3E_3A89246FB90C5EE6620004F1AE0EB0EA | der | |
MD5:9E7689E2C9C677A9AD9E78E3035D6A16 | SHA256:5EFE43A176D2D5C8A7A45CBEDF933B8B0E0D87C7C8762B6CC8AF7CBD291EB507 | |||
| 2036 | recoverit_setup_full4174.exe | C:\Users\Public\Documents\Wondershare\recoverit_full4174.exe | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
60
TCP/UDP connections
91
DNS requests
60
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2036 | recoverit_setup_full4174.exe | GET | — | 8.209.73.211:80 | http://platform.wondershare.cc/rest/v2/downloader/runtime/?client_sign={3b63fee4-23fe-49cb-87dc-bae0284ddd22G}&product_id=4174&wae=4.0.4&platform=win_x86 | unknown | — | — | unknown |
2036 | recoverit_setup_full4174.exe | HEAD | 200 | 23.15.179.57:80 | http://download.wondershare.net/cbs_down/recoverit_full4174.exe | unknown | — | — | unknown |
2036 | recoverit_setup_full4174.exe | HEAD | 200 | 23.15.179.66:80 | http://download.wondershare.net/cbs_down/recoverit_full4174.exe | unknown | — | — | unknown |
2036 | recoverit_setup_full4174.exe | HEAD | 200 | 23.15.179.66:80 | http://download.wondershare.net/cbs_down/recoverit_full4174.exe | unknown | — | — | unknown |
2036 | recoverit_setup_full4174.exe | GET | — | 23.15.179.57:80 | http://download.wondershare.net/cbs_down/recoverit_full4174.exe | unknown | — | — | unknown |
2036 | recoverit_setup_full4174.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?24ddb4487e7e8edc | unknown | — | — | unknown |
2036 | recoverit_setup_full4174.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAoFmyX1Sz2HlMxmMUd1OKM%3D | unknown | binary | 471 b | unknown |
2036 | recoverit_setup_full4174.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQlOydjtpho0%2Bholo77zGjGxETUEQQU8JyF%2FaKffY%2FJaLvV1IlNHb7TkP8CEA3EQd5SLWy5mr7JXcu5TKw%3D | unknown | binary | 727 b | unknown |
2036 | recoverit_setup_full4174.exe | GET | 206 | 23.15.179.66:80 | http://download.wondershare.net/cbs_down/recoverit_full4174.exe | unknown | text | 2 b | unknown |
2036 | recoverit_setup_full4174.exe | GET | 200 | 142.250.185.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2036 | recoverit_setup_full4174.exe | 8.209.72.213:443 | pc-api.wondershare.cc | Alibaba US Technology Co., Ltd. | DE | unknown |
2036 | recoverit_setup_full4174.exe | 8.209.73.211:80 | platform.wondershare.cc | Alibaba US Technology Co., Ltd. | DE | unknown |
2036 | recoverit_setup_full4174.exe | 47.91.89.51:443 | prod-web.wondershare.cc | Alibaba US Technology Co., Ltd. | DE | unknown |
2036 | recoverit_setup_full4174.exe | 23.15.179.66:80 | download.wondershare.net | Akamai International B.V. | FR | unknown |
2036 | recoverit_setup_full4174.exe | 47.91.90.244:8106 | analytics.wondershare.cc | Alibaba US Technology Co., Ltd. | DE | unknown |
2036 | recoverit_setup_full4174.exe | 47.91.74.43:8106 | analytics.300624.com | Alibaba US Technology Co., Ltd. | DE | unknown |
2036 | recoverit_setup_full4174.exe | 163.181.92.235:443 | wae.wondershare.cc | Zhejiang Taobao Network Co.,Ltd | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pc-api.wondershare.cc |
| malicious |
platform.wondershare.cc |
| unknown |
prod-web.wondershare.cc |
| unknown |
download.wondershare.net |
| whitelisted |
analytics.wondershare.cc |
| unknown |
analytics.300624.com |
| unknown |
wae.wondershare.cc |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2036 | recoverit_setup_full4174.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2036 | recoverit_setup_full4174.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1080 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
4 ETPRO signatures available at the full report
Process | Message |
|---|---|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|
RegAsm.exe | Cannot delete a subkey tree because the subkey does not exist.
|