| File name: | DiagnosticoItau.exe |
| Full analysis: | https://app.any.run/tasks/6d669c08-69bb-4c4b-ab06-a0162fc30cb6 |
| Verdict: | Malicious activity |
| Analysis date: | December 07, 2018, 15:55:08 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B9B2AC722054343DB3D1797E6B846D2A |
| SHA1: | A4C97CFD08D0FE137782BC9611E63B14D9B6D793 |
| SHA256: | D6EAE3C40936E093DC0E81AB72C9053B4393DC5E6DB2863FC1FB0D37533D6F92 |
| SSDEEP: | 98304:qgFCuulh5WTiB0piaZZk8ymjcvnvXUU7uSmnhRdov:bCuupWeipiaZulnvXtDOhRCv |
MALICIOUS
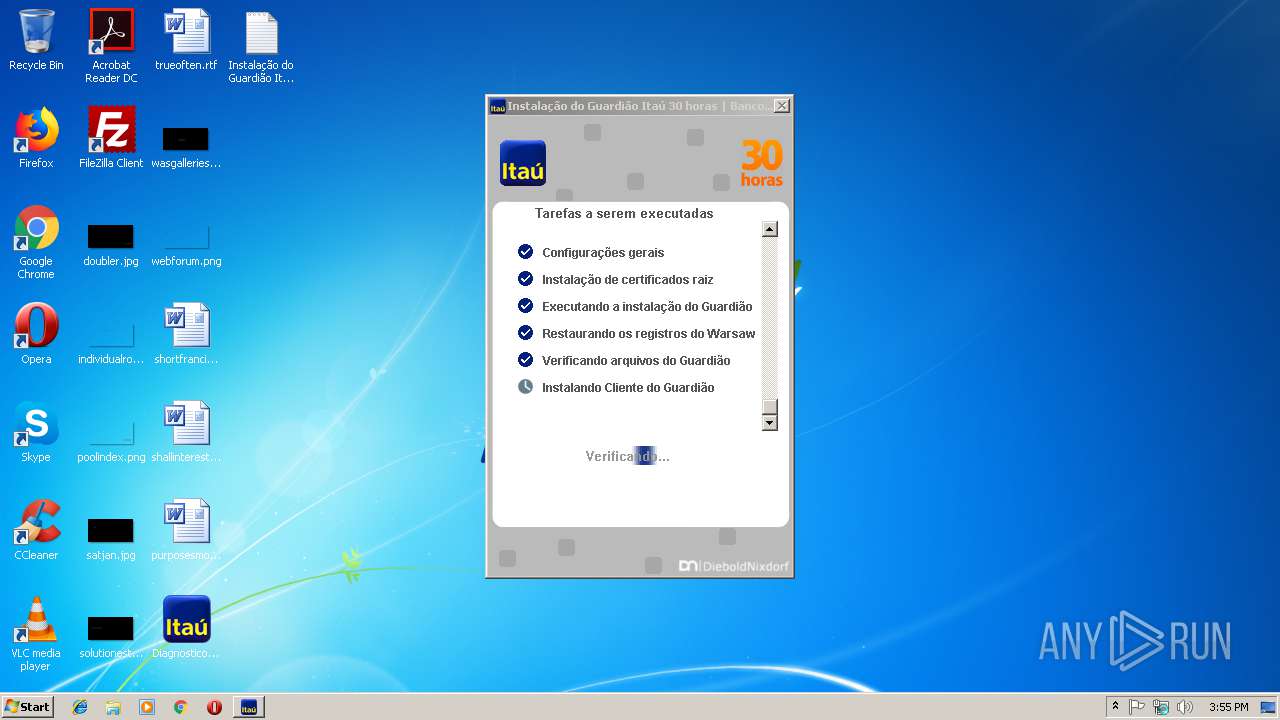
Application was dropped or rewritten from another process
- warsaw_setup_32.exe (PID: 2664)
- warsaw_setup_32.tmp (PID: 3680)
- impersonate.exe (PID: 2988)
- core.exe (PID: 4024)
- core.exe (PID: 3244)
- core.exe (PID: 2696)
- corefixer.exe (PID: 2308)
- wsffcmgr.exe (PID: 2892)
- wsffcmgr.exe (PID: 2628)
- wsffcmgr.exe (PID: 3312)
- ffcu.dat (PID: 2296)
- get_version.exe (PID: 2636)
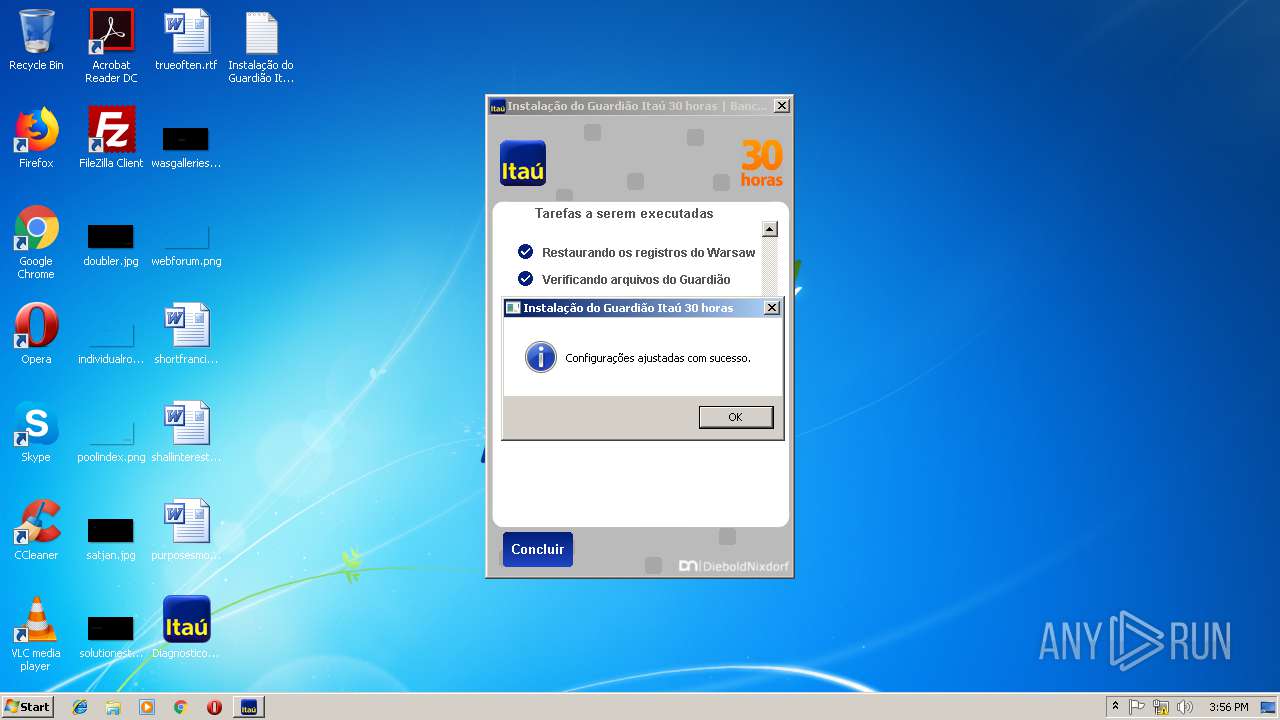
Changes settings of System certificates
- DiagnosticoItau.exe (PID: 1464)
- core.exe (PID: 4024)
Loads dropped or rewritten executable
- rundll32.exe (PID: 3076)
- rundll32.exe (PID: 3516)
- core.exe (PID: 4024)
- core.exe (PID: 3244)
- rundll32.exe (PID: 2576)
- core.exe (PID: 2696)
- iexplore.exe (PID: 3176)
- iexplore.exe (PID: 3784)
- DiagnosticoItau.exe (PID: 3860)
Loads the Task Scheduler COM API
- corefixer.exe (PID: 2308)
SUSPICIOUS
Application launched itself
- DiagnosticoItau.exe (PID: 3860)
- core.exe (PID: 4024)
Creates files in the user directory
- DiagnosticoItau.exe (PID: 3860)
- wsffcmgr.exe (PID: 2892)
- wsffcmgr.exe (PID: 2628)
- wsffcmgr.exe (PID: 3312)
- ffcu.dat (PID: 2296)
Creates files in the program directory
- DiagnosticoItau.exe (PID: 3860)
- DiagnosticoItau.exe (PID: 1464)
- warsaw_setup_32.tmp (PID: 3680)
- core.exe (PID: 4024)
Executable content was dropped or overwritten
- DiagnosticoItau.exe (PID: 3860)
- warsaw_setup_32.exe (PID: 2664)
- warsaw_setup_32.tmp (PID: 3680)
- core.exe (PID: 4024)
- DrvInst.exe (PID: 2388)
- DiagnosticoItau.exe (PID: 1464)
Reads the Windows organization settings
- warsaw_setup_32.tmp (PID: 3680)
Creates files in the Windows directory
- warsaw_setup_32.exe (PID: 2664)
- get_version.exe (PID: 2636)
- warsaw_setup_32.tmp (PID: 3680)
- cmd.exe (PID: 3980)
- core.exe (PID: 4024)
- DrvInst.exe (PID: 2388)
Starts SC.EXE for service management
- warsaw_setup_32.tmp (PID: 3680)
Creates files in the driver directory
- warsaw_setup_32.tmp (PID: 3680)
- DrvInst.exe (PID: 2388)
- core.exe (PID: 4024)
Reads Windows owner or organization settings
- warsaw_setup_32.tmp (PID: 3680)
Removes files from Windows directory
- warsaw_setup_32.tmp (PID: 3680)
- warsaw_setup_32.exe (PID: 2664)
- DrvInst.exe (PID: 2388)
- core.exe (PID: 4024)
Uses RUNDLL32.EXE to load library
- warsaw_setup_32.tmp (PID: 3680)
- impersonate.exe (PID: 2988)
Creates or modifies windows services
- core.exe (PID: 4024)
Creates a software uninstall entry
- warsaw_setup_32.tmp (PID: 3680)
Reads Internet Cache Settings
- core.exe (PID: 2696)
Reads the BIOS version
- core.exe (PID: 4024)
- DiagnosticoItau.exe (PID: 3860)
Starts CMD.EXE for commands execution
- warsaw_setup_32.tmp (PID: 3680)
- cmd.exe (PID: 3980)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 2888)
- cmd.exe (PID: 3980)
Low-level read access rights to disk partition
- core.exe (PID: 4024)
Searches for installed software
- DrvInst.exe (PID: 2388)
Loads DLL from Mozilla Firefox
- wsffcmgr.exe (PID: 2892)
- wsffcmgr.exe (PID: 2628)
- wsffcmgr.exe (PID: 3312)
- ffcu.dat (PID: 2296)
Creates COM task schedule object
- core.exe (PID: 4024)
Starts application with an unusual extension
- DiagnosticoItau.exe (PID: 1464)
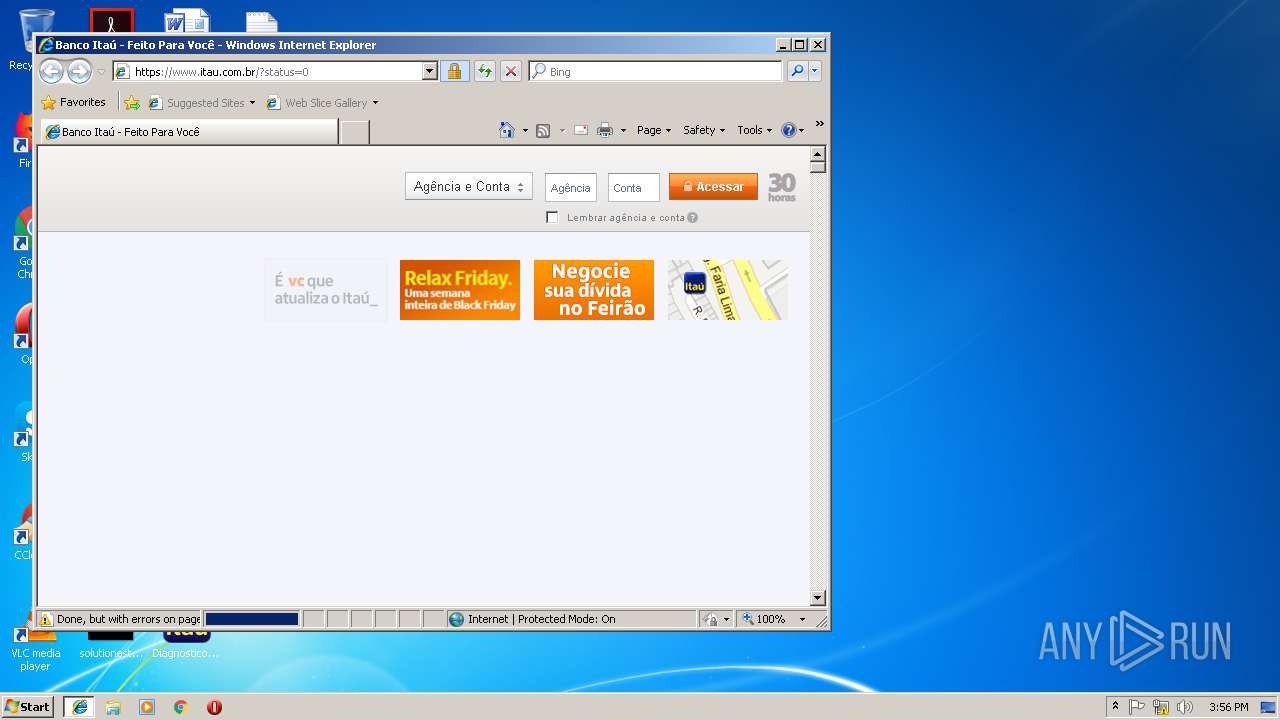
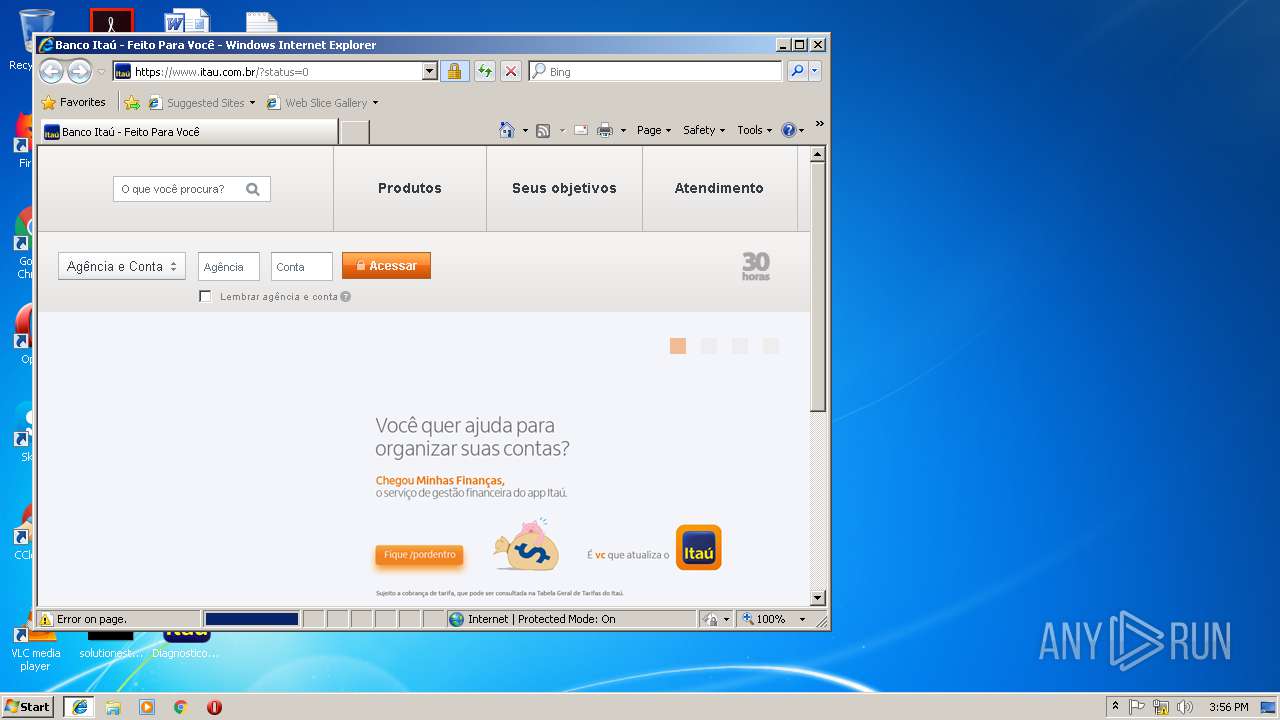
Starts Internet Explorer
- DiagnosticoItau.exe (PID: 3860)
INFO
Reads settings of System Certificates
- DiagnosticoItau.exe (PID: 1464)
- core.exe (PID: 4024)
- iexplore.exe (PID: 3176)
Changes settings of System certificates
- DrvInst.exe (PID: 2388)
- DrvInst.exe (PID: 2072)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3636)
Reads Internet Cache Settings
- iexplore.exe (PID: 3784)
- iexplore.exe (PID: 3176)
Application launched itself
- iexplore.exe (PID: 3176)
Creates files in the user directory
- iexplore.exe (PID: 3784)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 1328)
Changes internet zones settings
- iexplore.exe (PID: 3176)
Reads internet explorer settings
- iexplore.exe (PID: 3784)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 3784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:18 16:10:35+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 2404864 |
| InitializedDataSize: | 3417088 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1c780e |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.1.1.8 |
| ProductVersionNumber: | 2.1.1.8 |
| FileFlagsMask: | 0x001f |
| FileFlags: | Private build |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | Unknown (0016) |
| CharacterSet: | Unicode |
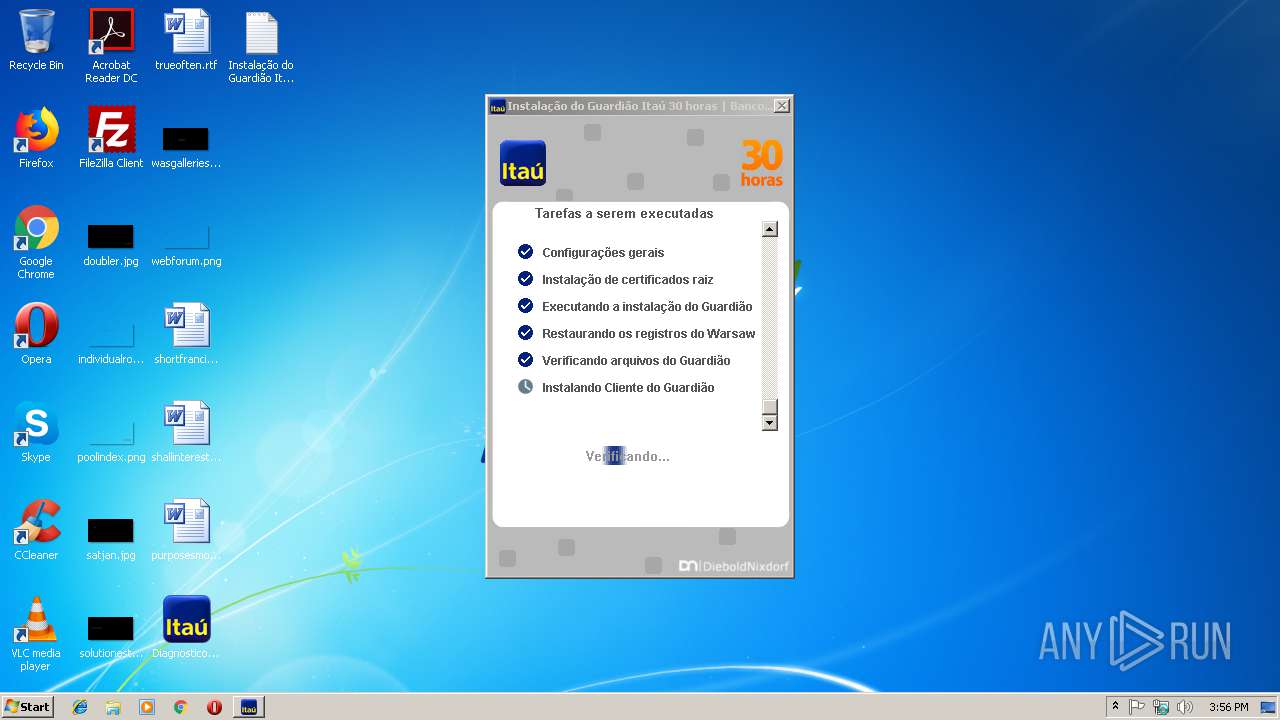
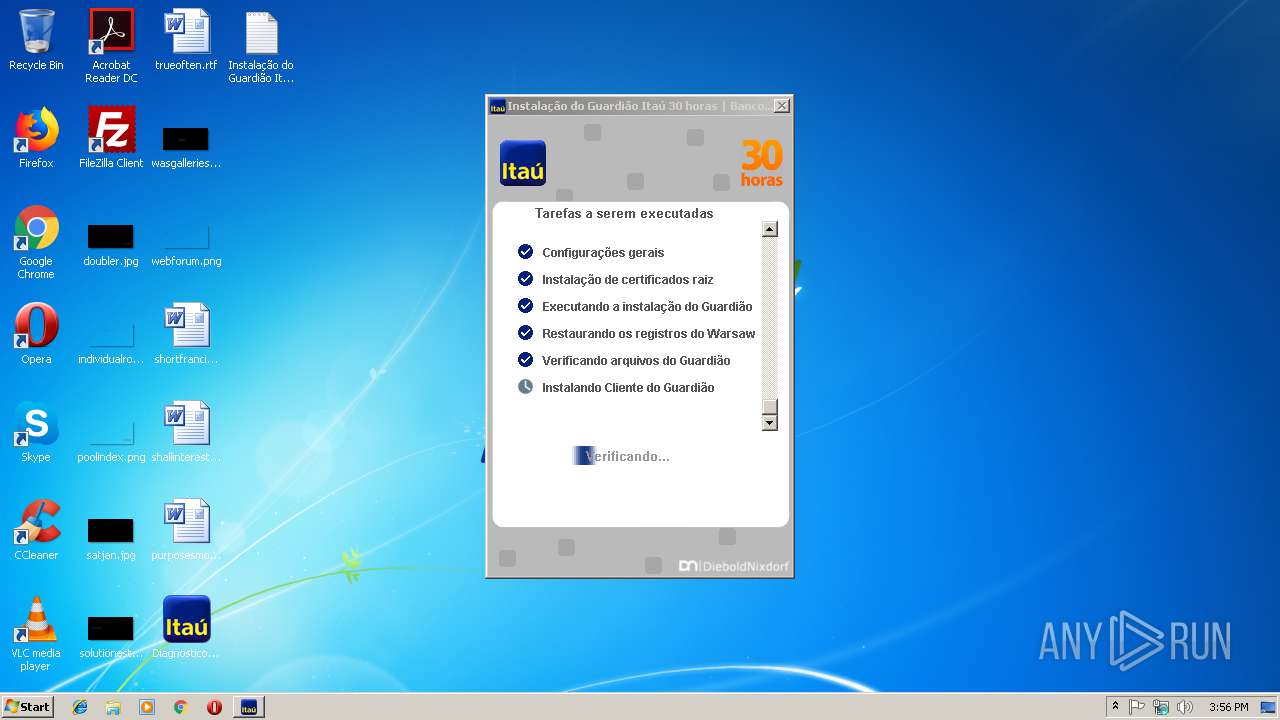
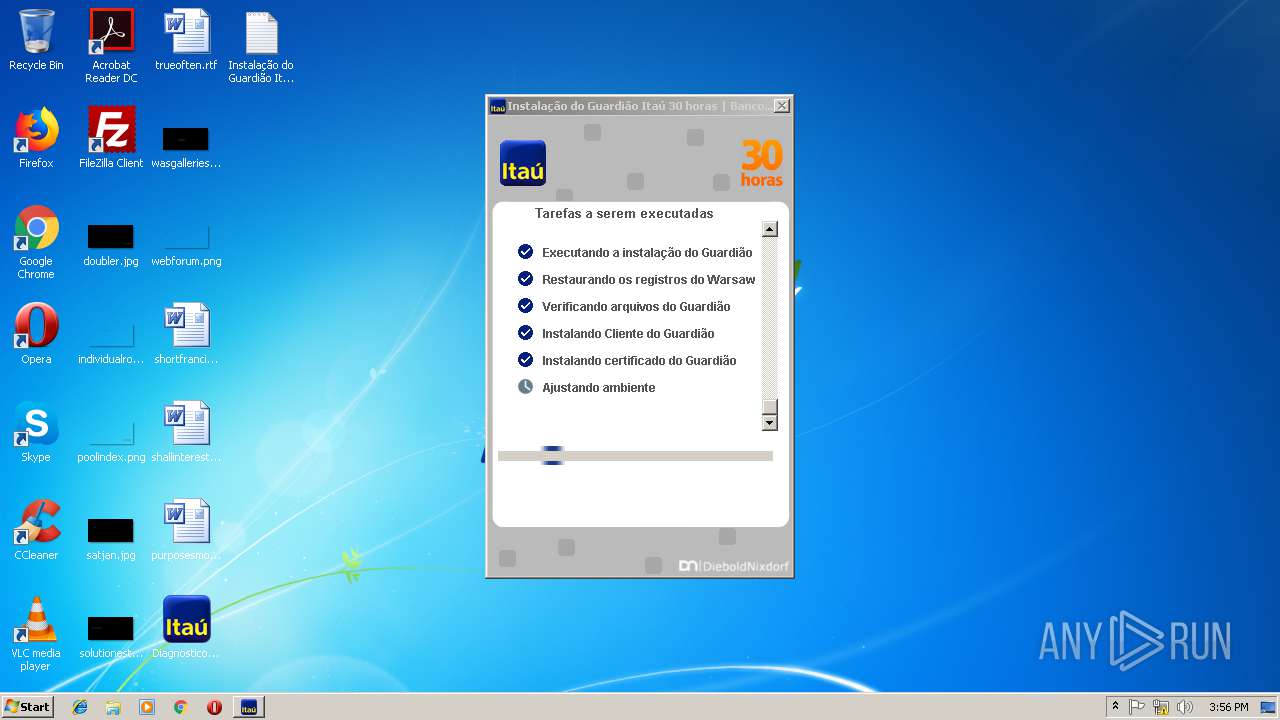
| CompanyName: | Banco Itaú |
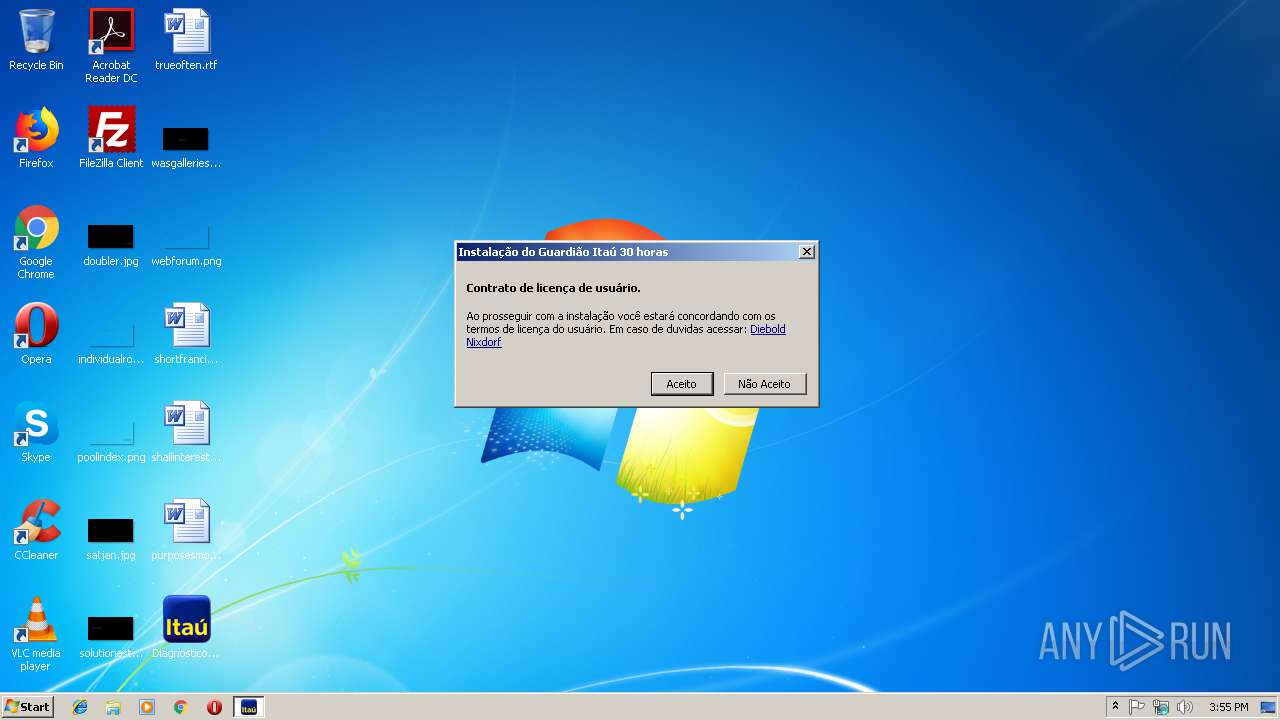
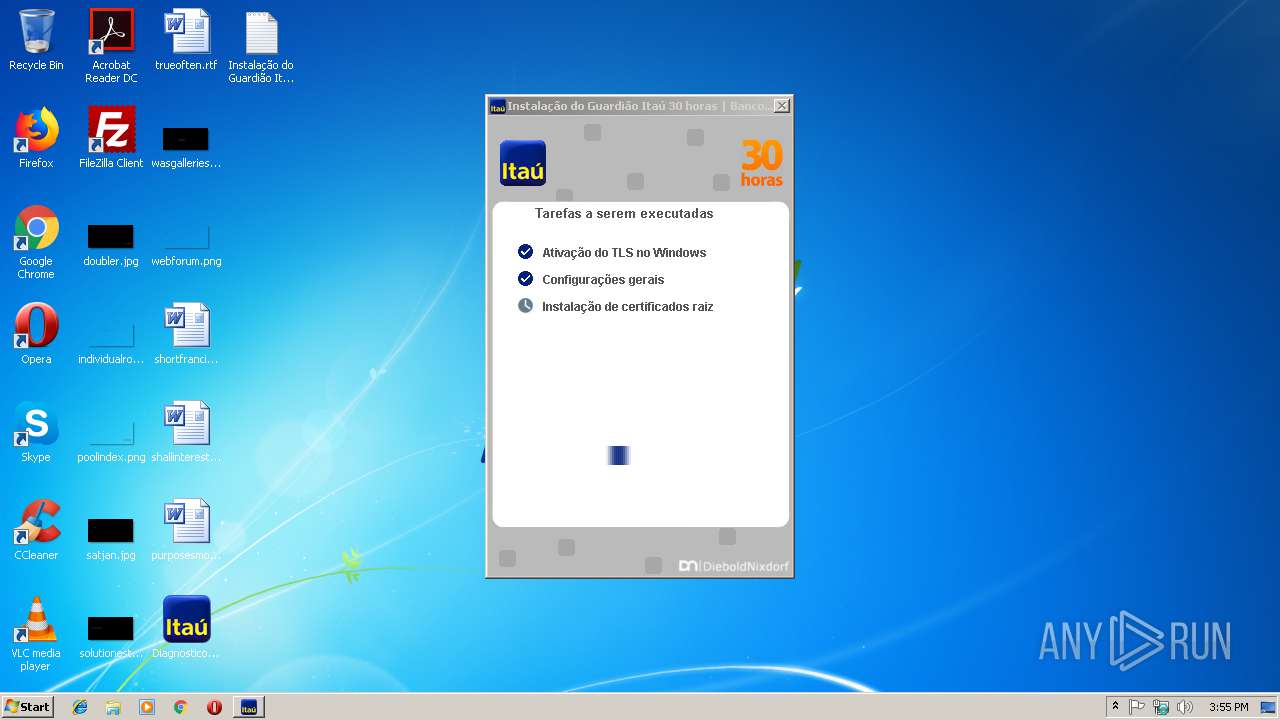
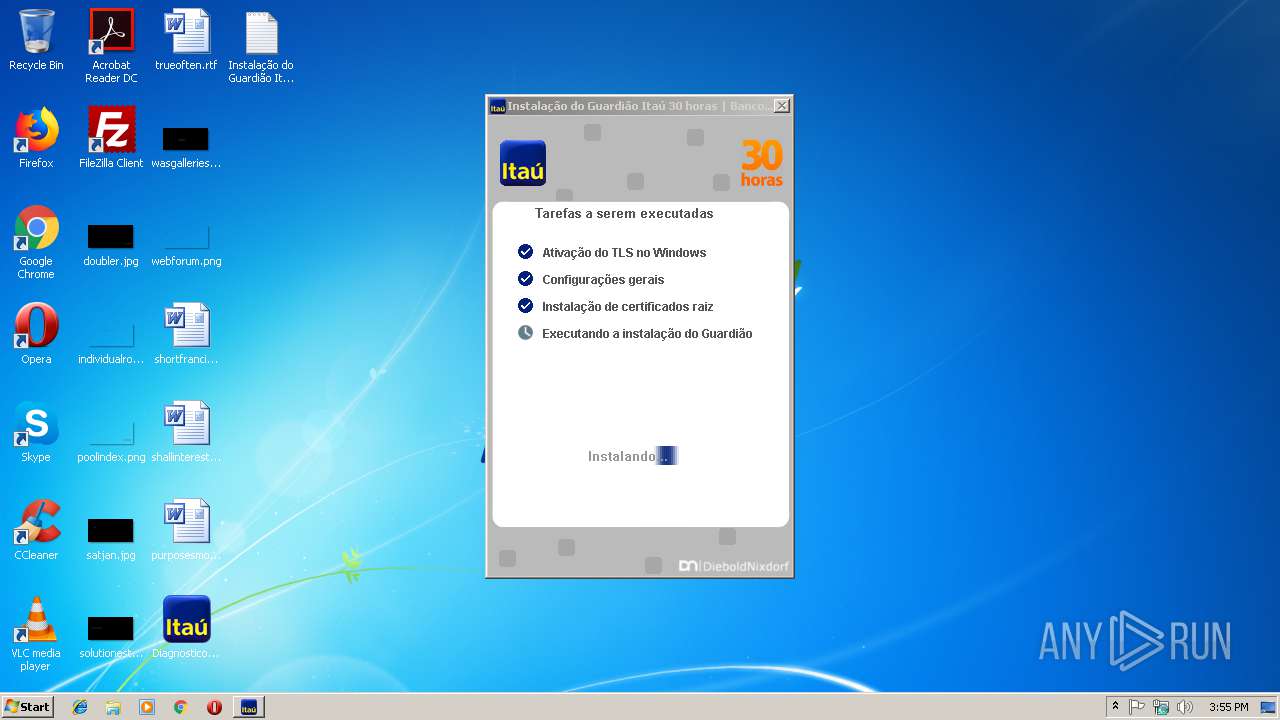
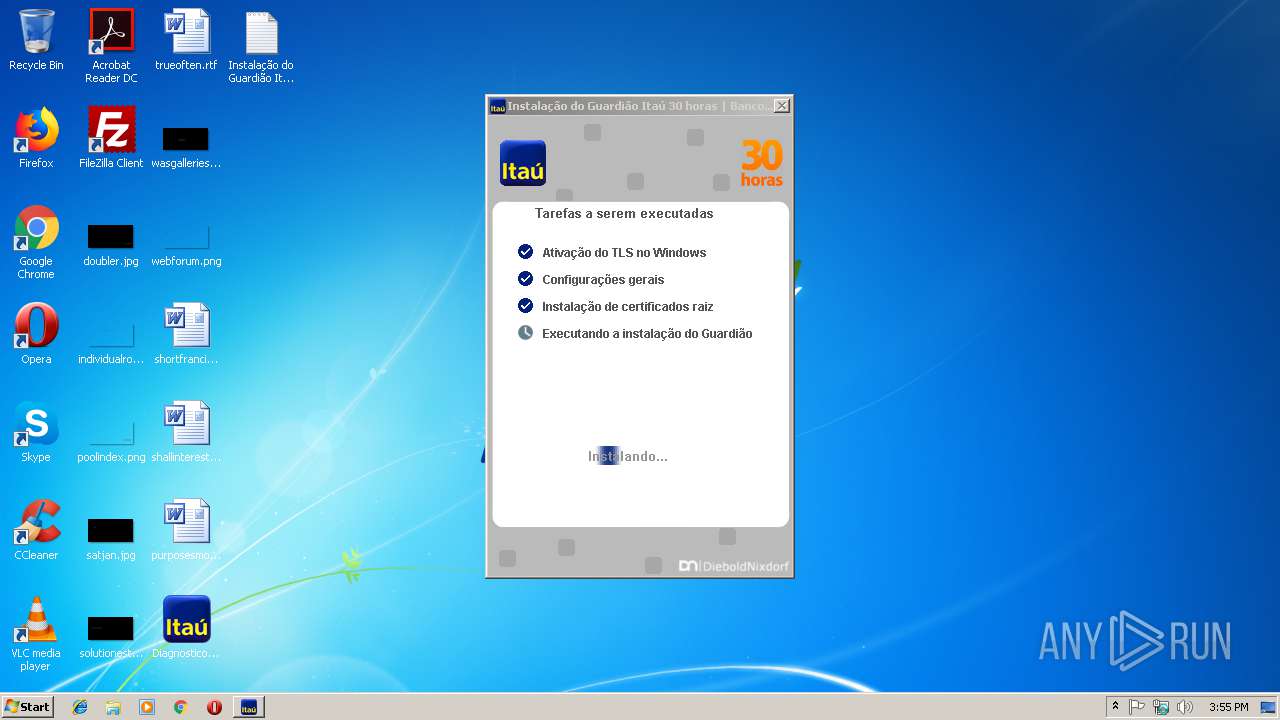
| FileDescription: | Instalação do Guardião Itaú 30 horas |
| FileVersion: | 2,1,1,8 |
| InternalName: | HDA |
| LegalCopyright: | Copyright © 2018, Banco Itaú |
| OriginalFileName: | DiagnosticoItau_PROD |
| PrivateBuild: | 2,1,1,8 |
| ProductName: | Instalação do Guardião Itaú 30 horas |
| ProductVersion: | 2,1,1,8 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Jun-2018 14:10:35 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| Debug artifacts: |
|
| CompanyName: | Banco Itaú |
| FileDescription: | Instalação do Guardião Itaú 30 horas |
| FileVersion: | 2,1,1,8 |
| InternalName: | HDA |
| LegalCopyright: | Copyright © 2018, Banco Itaú |
| OriginalFilename: | DiagnosticoItau_PROD |
| PrivateBuild: | 2,1,1,8 |
| ProductName: | Instalação do Guardião Itaú 30 horas |
| ProductVersion: | 2,1,1,8 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 18-Jun-2018 14:10:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0022A25A | 0x0022A400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66773 |
CODE | 0x0022C000 | 0x00020DA0 | 0x00020E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57387 |
.rdata | 0x0024D000 | 0x00048F7A | 0x00049000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.46234 |
.data | 0x00296000 | 0x00010368 | 0x00009600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.17063 |
DATA | 0x002A7000 | 0x000014E0 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.98761 |
BSS | 0x002A9000 | 0x00000761 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.tls | 0x002AA000 | 0x00000002 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x002AB000 | 0x002C26A0 | 0x002C2800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.67911 |
.reloc | 0x0056E000 | 0x0002B474 | 0x0002B600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.11846 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.8253 | 872 | Latin 1 / Western European | Portuguese - Brazil | RT_MANIFEST |
2 | 6.32263 | 4264 | Latin 1 / Western European | Portuguese - Brazil | RT_ICON |
3 | 6.40717 | 1128 | Latin 1 / Western European | Portuguese - Brazil | RT_ICON |
101 | 7.55101 | 1270 | Latin 1 / Western European | Portuguese - Brazil | FILE |
104 | 7.88025 | 14083 | Latin 1 / Western European | Portuguese - Brazil | IMG |
105 | 6.62894 | 148 | Latin 1 / Western European | Portuguese - Brazil | IMG |
106 | 7.36799 | 454 | Latin 1 / Western European | Portuguese - Brazil | IMG |
107 | 7.62796 | 563 | Latin 1 / Western European | Portuguese - Brazil | IMG |
108 | 7.30965 | 465 | Latin 1 / Western European | Portuguese - Brazil | IMG |
112 | 7.85361 | 3085 | Latin 1 / Western European | Portuguese - Brazil | FILE |
Imports
ADVAPI32.dll |
COMCTL32.dll |
CRYPT32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MSIMG32.dll |
NETAPI32.dll |
OLEAUT32.dll |
PSAPI.DLL |
Total processes
78
Monitored processes
32
Malicious processes
11
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | "C:\Users\admin\Desktop\DiagnosticoItau.exe" admin_service | C:\Users\admin\Desktop\DiagnosticoItau.exe | DiagnosticoItau.exe | ||||||||||||
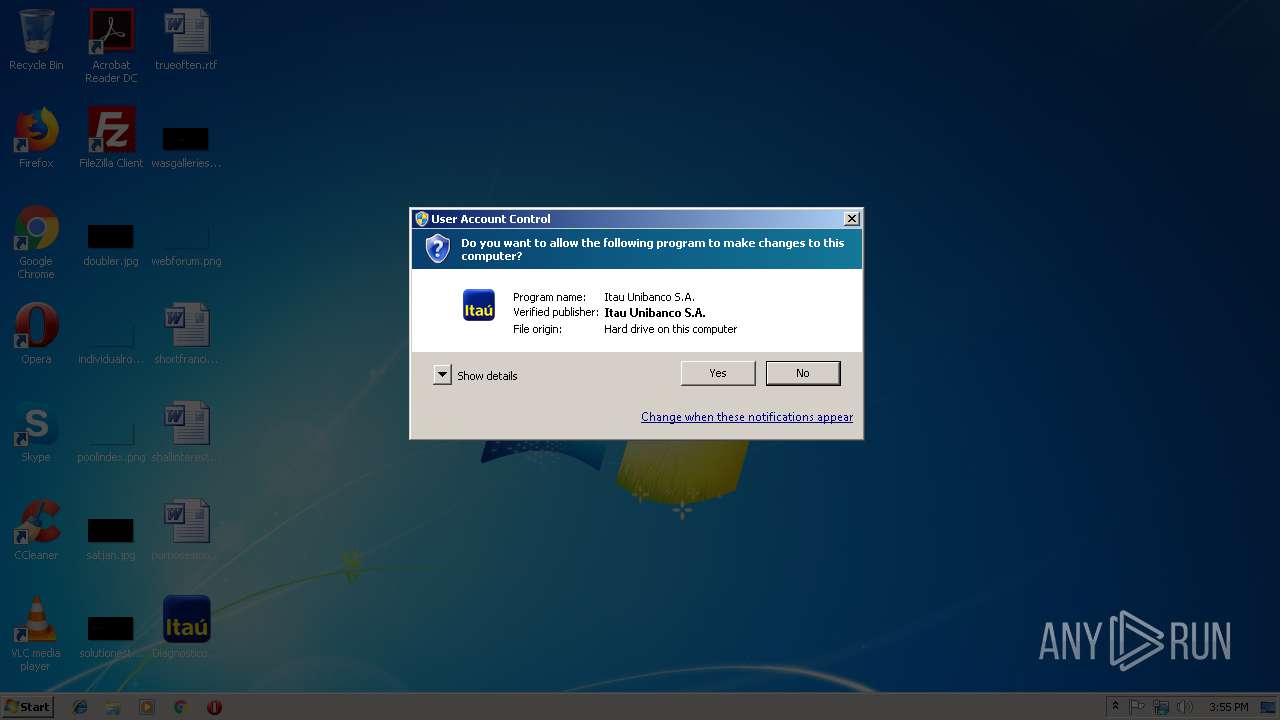
User: admin Company: Banco Itaú Integrity Level: HIGH Description: Instalação do Guardião Itaú 30 horas Exit code: 0 Version: 2,1,1,8 Modules
| |||||||||||||||
| 920 | "sc" stop wsddfac | C:\Windows\system32\sc.exe | — | warsaw_setup_32.tmp | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1328 | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_26_0_0_131_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 26.0 r0 Exit code: 0 Version: 26,0,0,131 Modules
| |||||||||||||||
| 1464 | "C:\Users\admin\Desktop\DiagnosticoItau.exe" service_service | C:\Users\admin\Desktop\DiagnosticoItau.exe | services.exe | ||||||||||||
User: SYSTEM Company: Banco Itaú Integrity Level: SYSTEM Description: Instalação do Guardião Itaú 30 horas Exit code: 0 Version: 2,1,1,8 Modules
| |||||||||||||||
| 2072 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000005EC" "000005E8" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2188 | tasklist /FI "imagename eq core.exe" | C:\Windows\system32\tasklist.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2296 | C:\ProgramData\Temp\ffcu.dat | C:\ProgramData\Temp\ffcu.dat | — | DiagnosticoItau.exe | |||||||||||
User: SYSTEM Company: GAS Tecnologia LTDA Integrity Level: SYSTEM Description: GAS Tecnologia - Protection Module Exit code: 0 Version: 1.2.1.220114 Modules
| |||||||||||||||
| 2308 | "C:\Windows\TEMP\is-27AOK.tmp\corefixer.exe" /nocert | C:\Windows\TEMP\is-27AOK.tmp\corefixer.exe | — | warsaw_setup_32.tmp | |||||||||||
User: SYSTEM Company: GAS Tecnologia LTDA Integrity Level: SYSTEM Description: GAS Tecnologia - Warsaw Fixer Exit code: 0 Version: 1.7.2.127 Modules
| |||||||||||||||
| 2388 | DrvInst.exe "4" "8" "C:\Windows\TEMP\{22957857-6f40-2c19-7b3b-8e671b3e5340}\wsddntf.inf" "0" "6a6586d23" "00000334" "Service-0x0-3e7$\Default" "00000060" "208" "C:\Windows\system32\drivers" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2576 | "C:\Windows\system32\rundll32.exe" "C:\Program Files\Diebold\Warsaw\wslbmid.dll", Function6 | C:\Windows\system32\rundll32.exe | — | warsaw_setup_32.tmp | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 713
Read events
947
Write events
758
Delete events
8
Modification events
| (PID) Process: | (3860) DiagnosticoItau.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3860) DiagnosticoItau.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1464) DiagnosticoItau.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 512 | |||
| (PID) Process: | (1464) DiagnosticoItau.exe | Key: | HKEY_USERS\S-1-5-19\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 512 | |||
| (PID) Process: | (1464) DiagnosticoItau.exe | Key: | HKEY_USERS\S-1-5-20\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 512 | |||
| (PID) Process: | (1464) DiagnosticoItau.exe | Key: | HKEY_USERS\S-1-5-21-1302019708-1500728564-335382590-1000\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 672 | |||
| (PID) Process: | (1464) DiagnosticoItau.exe | Key: | HKEY_USERS\NTUSER.DAT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 512 | |||
| (PID) Process: | (1464) DiagnosticoItau.exe | Key: | HKEY_USERS\NTUSER.DAT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 672 | |||
| (PID) Process: | (1464) DiagnosticoItau.exe | Key: | HKEY_USERS\.DEFAULT\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 2560 | |||
| (PID) Process: | (1464) DiagnosticoItau.exe | Key: | HKEY_USERS\S-1-5-19\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | SecureProtocols |
Value: 2560 | |||
Executable files
63
Suspicious files
63
Text files
457
Unknown types
72
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1464 | DiagnosticoItau.exe | C:\ProgramData\Temp\cert_temp\cert0.crt | — | |
MD5:— | SHA256:— | |||
| 1464 | DiagnosticoItau.exe | C:\ProgramData\Temp\cert_temp\cert1.crt | — | |
MD5:— | SHA256:— | |||
| 3860 | DiagnosticoItau.exe | C:\Users\admin\Desktop\Instalação do Guardião Itaú 30 horas.log | text | |
MD5:— | SHA256:— | |||
| 1464 | DiagnosticoItau.exe | C:\Windows\system32\config\systemprofile\NTUSER.DAT | hiv | |
MD5:— | SHA256:— | |||
| 1464 | DiagnosticoItau.exe | C:\Windows\system32\config\systemprofile\NTUSER.DAT.LOG1 | log | |
MD5:— | SHA256:— | |||
| 1464 | DiagnosticoItau.exe | C:\Users\Administrator\NTUSER.DAT | hiv | |
MD5:— | SHA256:— | |||
| 3860 | DiagnosticoItau.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@digicert[1].txt | text | |
MD5:— | SHA256:— | |||
| 3860 | DiagnosticoItau.exe | C:\ProgramData\Temp\cert2.zip | compressed | |
MD5:— | SHA256:— | |||
| 1464 | DiagnosticoItau.exe | C:\Users\Administrator\NTUSER.DAT.LOG1 | log | |
MD5:— | SHA256:— | |||
| 1464 | DiagnosticoItau.exe | C:\ProgramData\Temp\cert_temp\VeriSign Root Certificates\.DS_Store | ds_store | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
110
DNS requests
32
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3860 | DiagnosticoItau.exe | GET | 200 | 150.162.159.4:80 | http://acraiz.icpbrasil.gov.br/ICP-Brasilv5.crt | BR | text | 2.30 Kb | unknown |
3176 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3784 | iexplore.exe | 2.18.232.23:443 | assets.adobedtm.com | Akamai International B.V. | — | whitelisted |
3860 | DiagnosticoItau.exe | 45.60.123.229:443 | www.digicert.com | — | US | suspicious |
3860 | DiagnosticoItau.exe | 104.111.231.226:443 | www.symantec.com | Akamai International B.V. | NL | whitelisted |
3860 | DiagnosticoItau.exe | 150.162.159.4:80 | acraiz.icpbrasil.gov.br | Universidade Federal de Santa Catarina | BR | unknown |
3860 | DiagnosticoItau.exe | 2.18.234.32:443 | guardiao.itau.com.br | Akamai International B.V. | — | whitelisted |
3176 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3860 | DiagnosticoItau.exe | 54.230.202.199:443 | log.gastecnologia.com.br | Amazon.com, Inc. | US | unknown |
3784 | iexplore.exe | 104.109.87.116:443 | cdn.tt.omtrdc.net | Akamai International B.V. | NL | whitelisted |
3784 | iexplore.exe | 173.194.76.155:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
3784 | iexplore.exe | 151.101.2.49:443 | sync-tm.everesttech.net | Fastly | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.digicert.com |
| whitelisted |
www.symantec.com |
| whitelisted |
acraiz.icpbrasil.gov.br |
| unknown |
guardiao.itau.com.br |
| suspicious |
log.gastecnologia.com.br |
| malicious |
www.bing.com |
| whitelisted |
www.itau.com.br |
| whitelisted |
maps-api-ssl.google.com |
| whitelisted |
assets.adobedtm.com |
| whitelisted |
www.googleadservices.com |
| whitelisted |