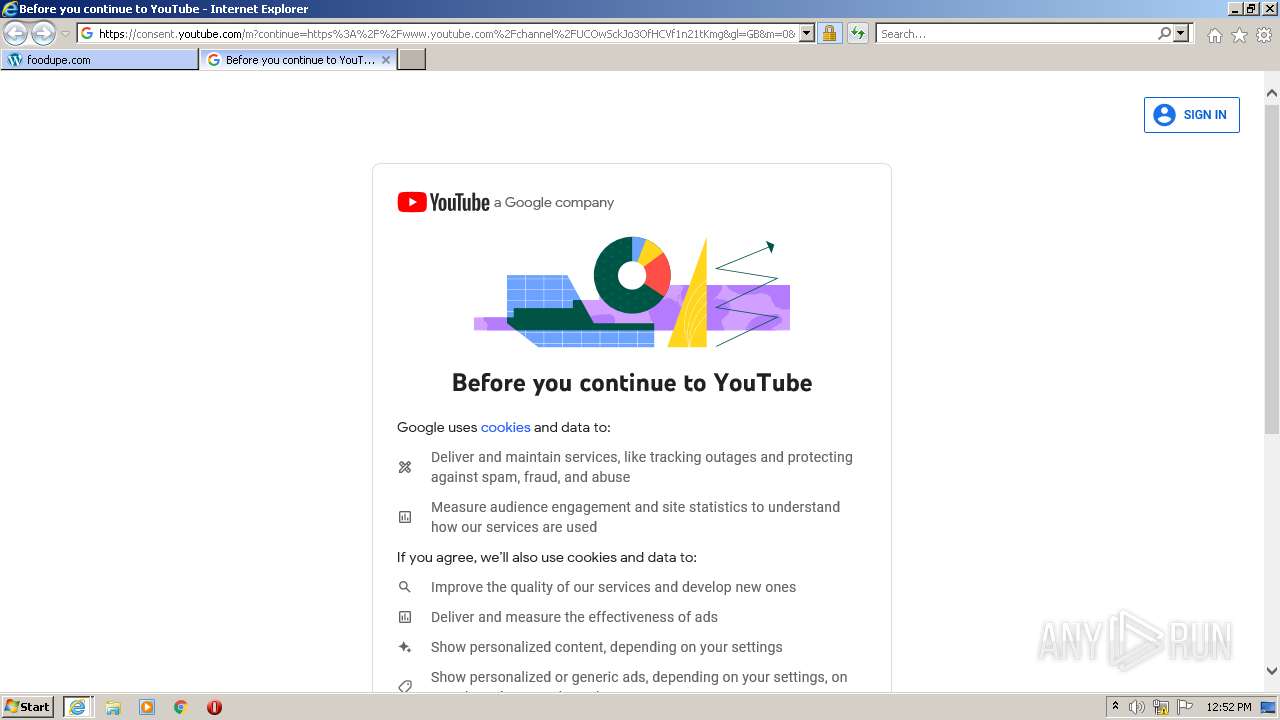
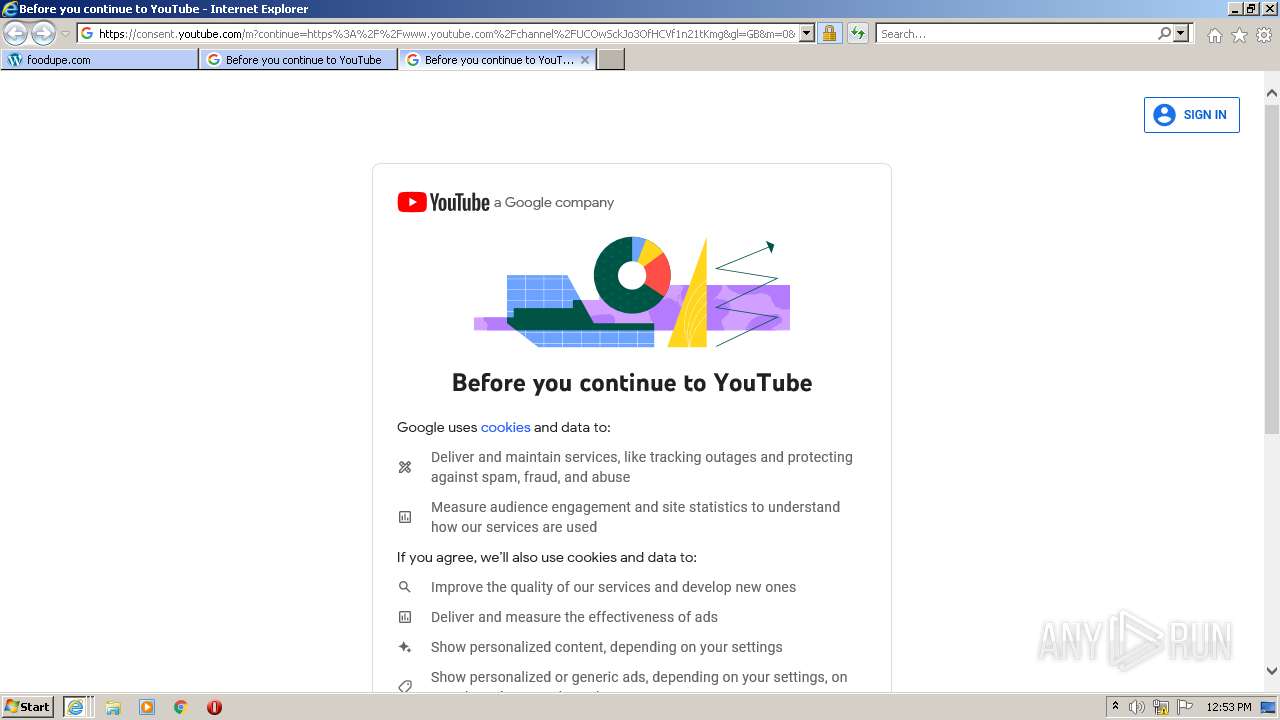
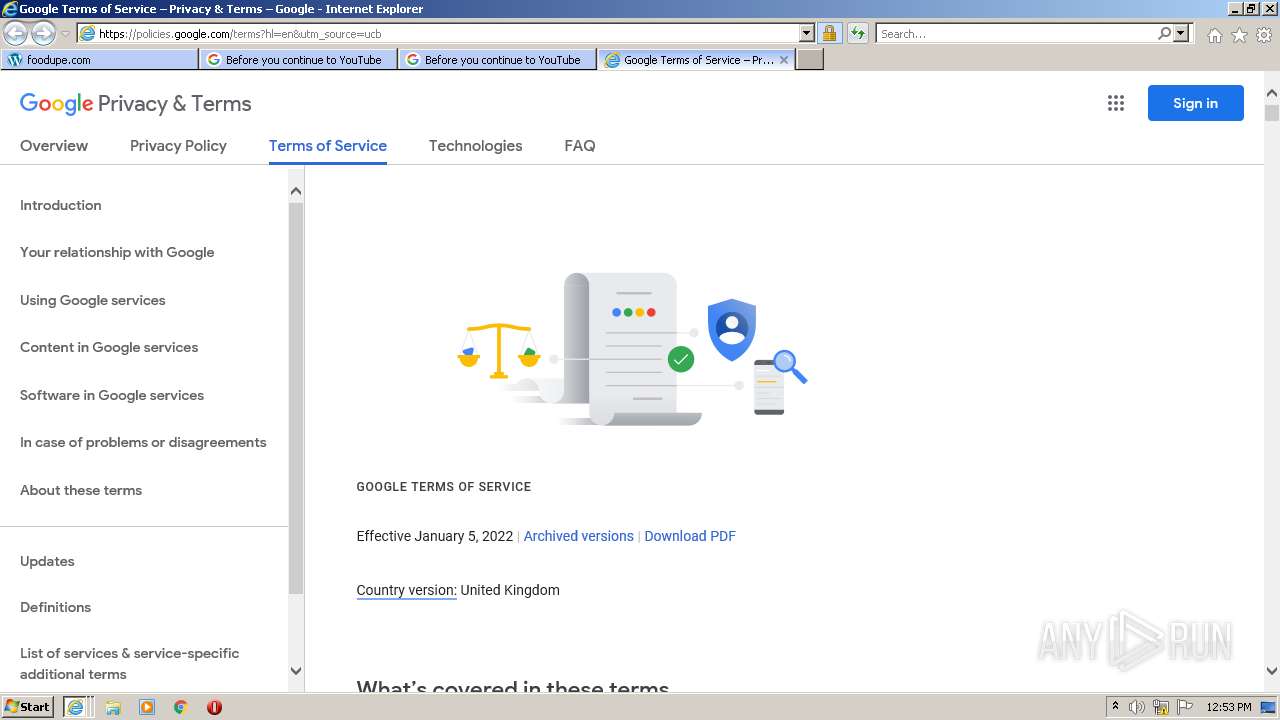
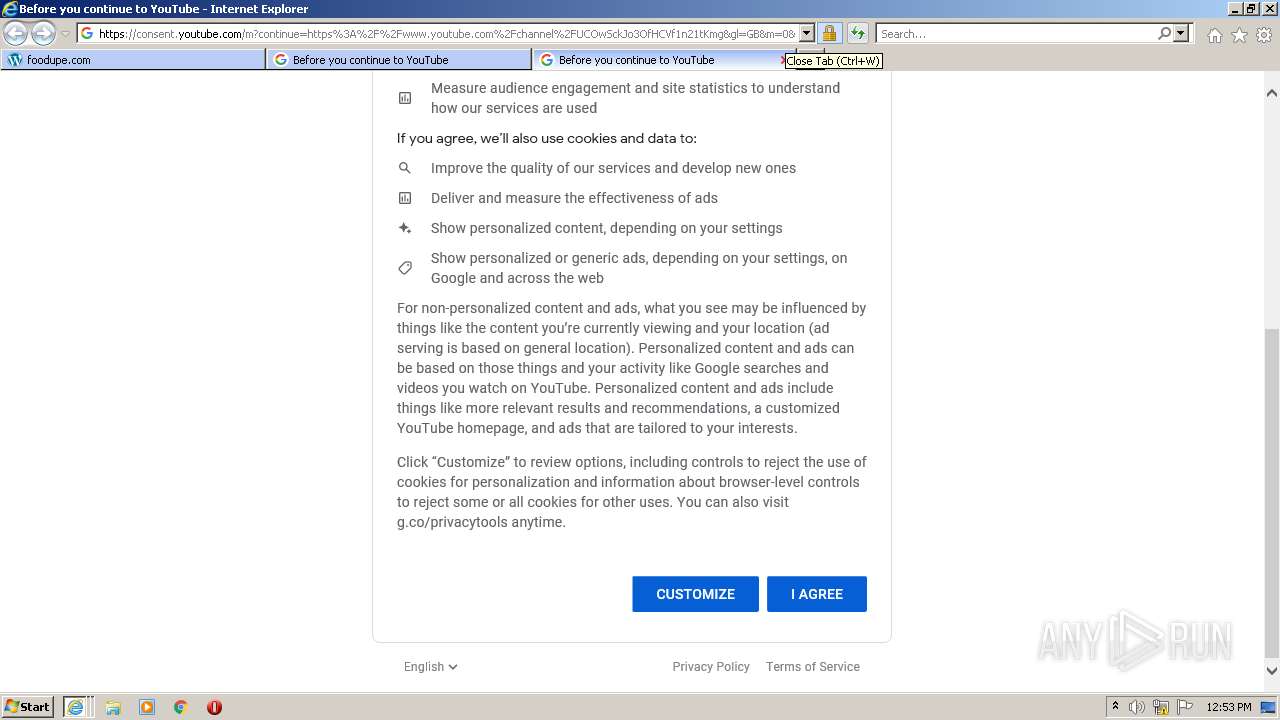
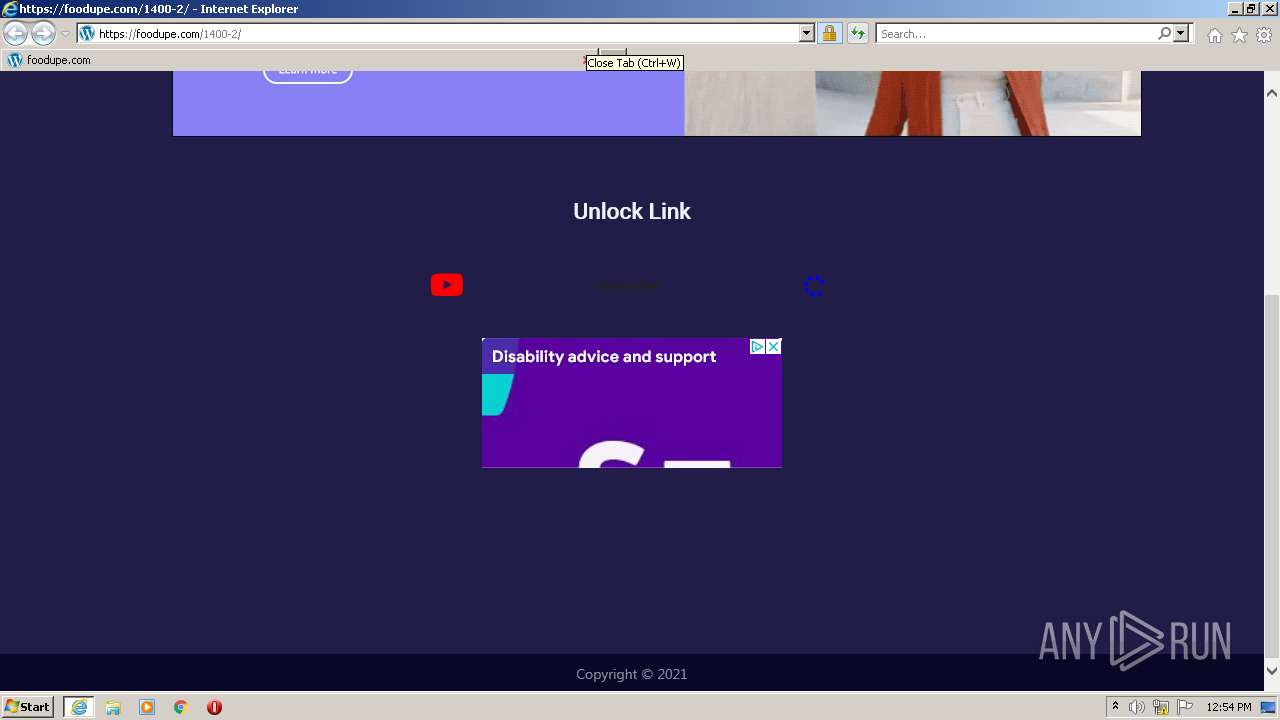
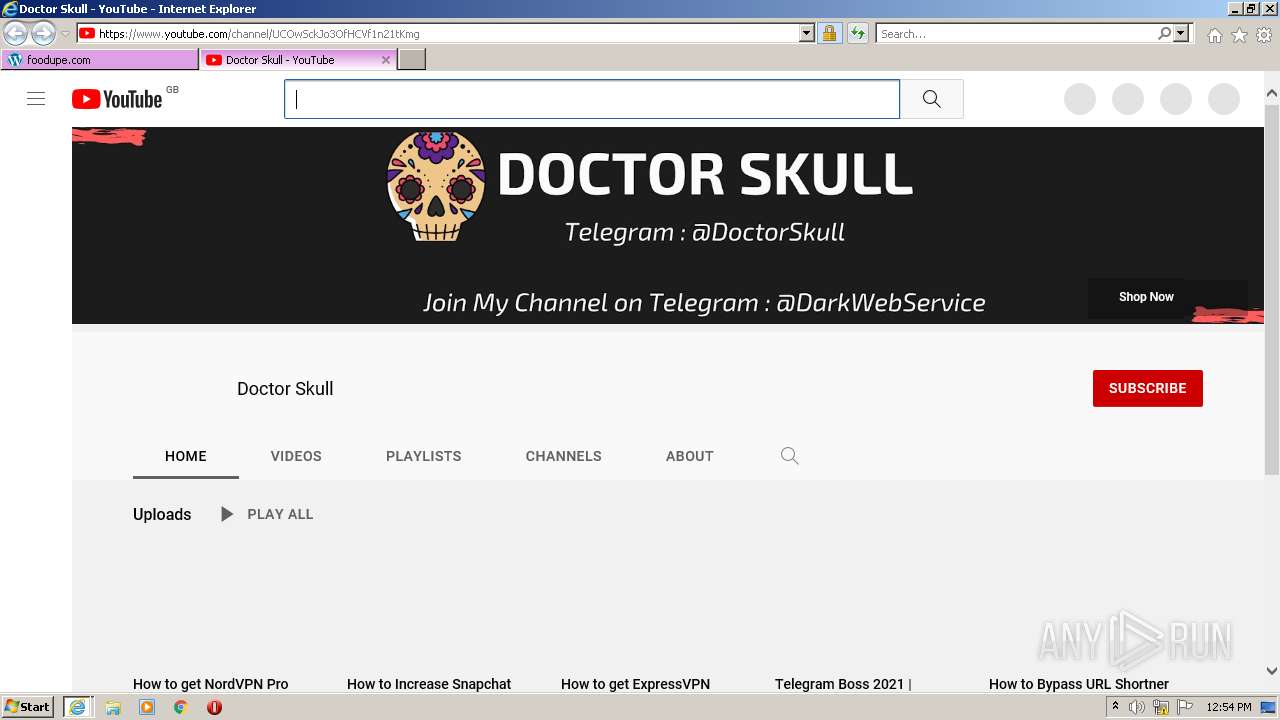
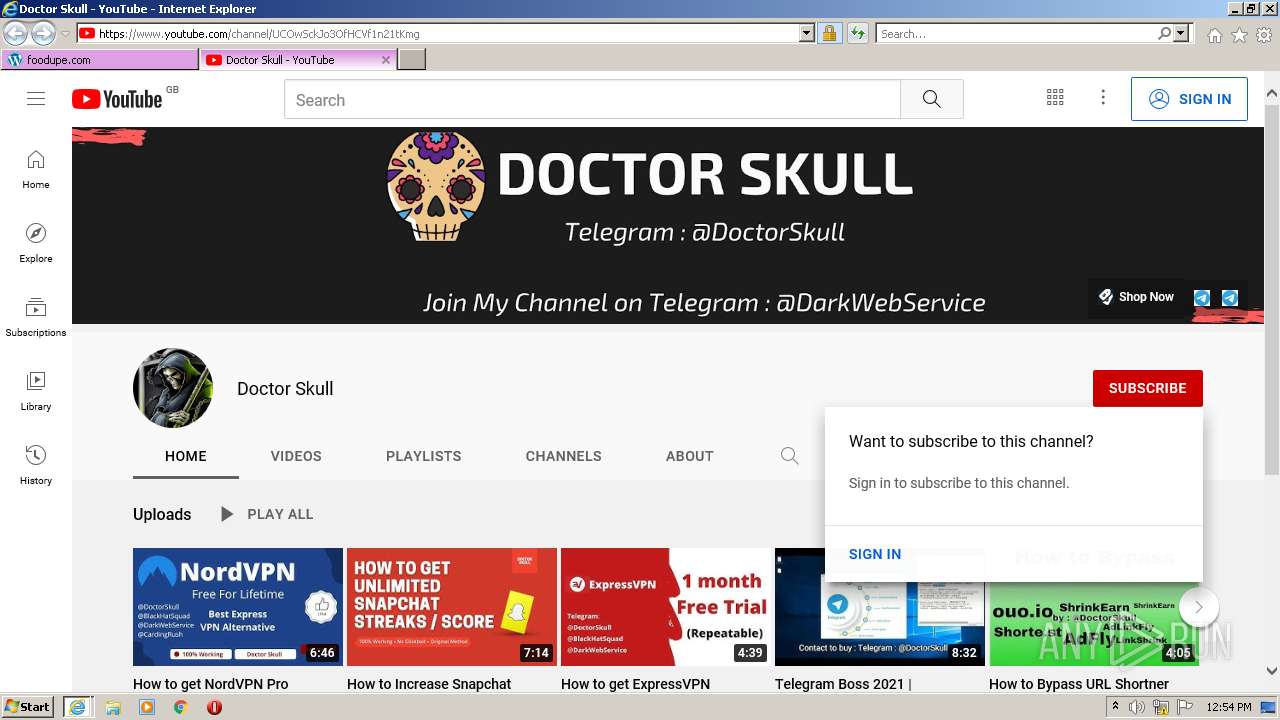
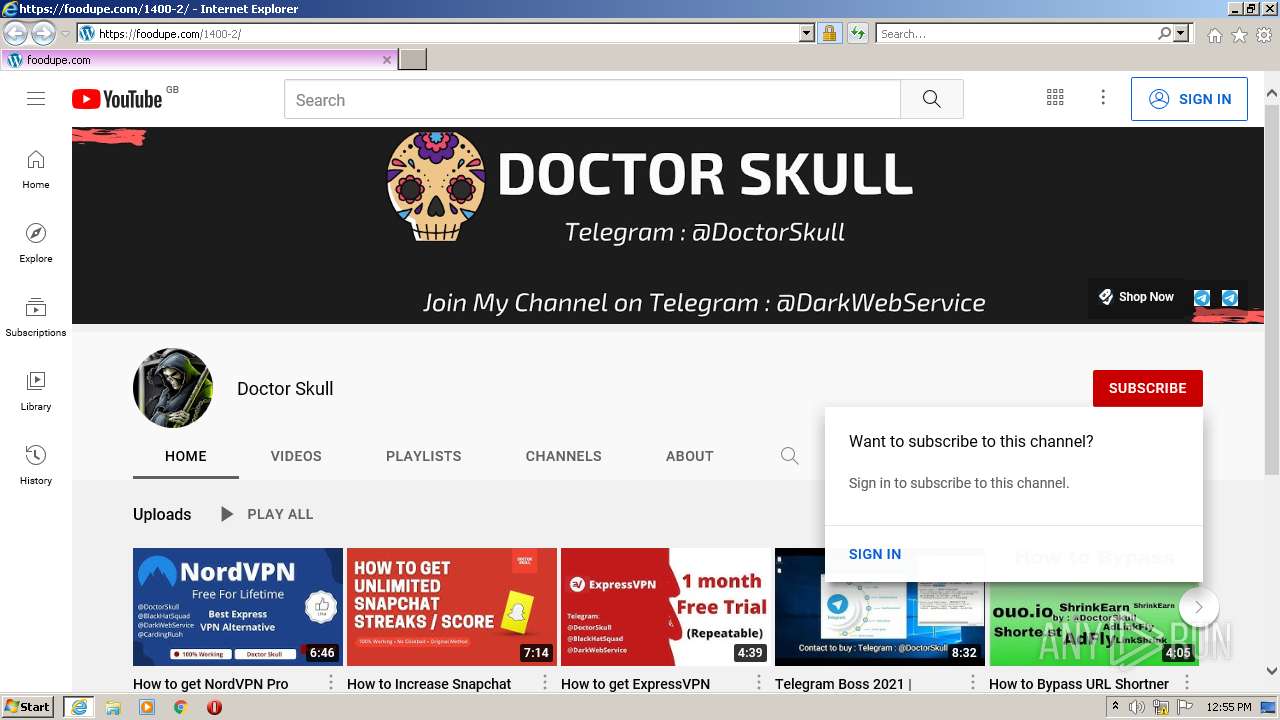
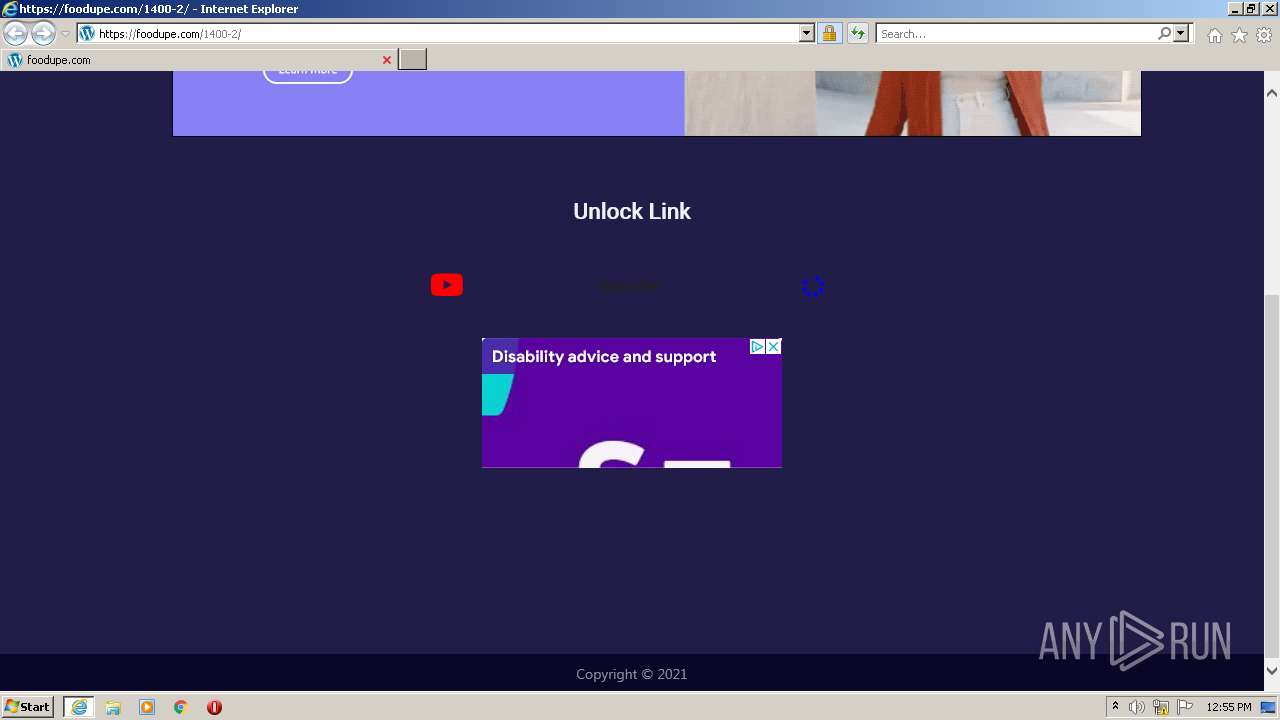
| URL: | https://sub2unlock.me/LXzw1 |
| Full analysis: | https://app.any.run/tasks/4f2a4cb7-b935-48fd-b9b6-5745e34eb2ea |
| Verdict: | Malicious activity |
| Analysis date: | February 05, 2022, 12:52:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A27E375B4C8E84E6490E0123F87C000D |
| SHA1: | AF30722CAD9586BD22CE35773CC3245FFF384541 |
| SHA256: | D6E269B375D1712999610525722C513137C220FE237F70D565AD98FD927A8245 |
| SSDEEP: | 3:N8dMphn:2iphn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 1132)
- iexplore.exe (PID: 3396)
- iexplore.exe (PID: 3628)
INFO
Checks supported languages
- iexplore.exe (PID: 3448)
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 1132)
- iexplore.exe (PID: 3396)
- iexplore.exe (PID: 3628)
Reads the computer name
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 3448)
- iexplore.exe (PID: 1132)
- iexplore.exe (PID: 3396)
- iexplore.exe (PID: 3628)
Reads settings of System Certificates
- iexplore.exe (PID: 3448)
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 1132)
- iexplore.exe (PID: 3628)
- iexplore.exe (PID: 3396)
Changes internet zones settings
- iexplore.exe (PID: 3448)
Reads internet explorer settings
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 1132)
- iexplore.exe (PID: 3628)
- iexplore.exe (PID: 3396)
Application launched itself
- iexplore.exe (PID: 3448)
Checks Windows Trust Settings
- iexplore.exe (PID: 3448)
- iexplore.exe (PID: 1132)
- iexplore.exe (PID: 3396)
- iexplore.exe (PID: 3628)
- iexplore.exe (PID: 3348)
Creates files in the user directory
- iexplore.exe (PID: 3348)
- iexplore.exe (PID: 1132)
- iexplore.exe (PID: 3448)
- iexplore.exe (PID: 3628)
- iexplore.exe (PID: 3396)
Changes settings of System certificates
- iexplore.exe (PID: 3448)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
42
Monitored processes
5
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1132 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3448 CREDAT:3347727 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3348 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3448 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3396 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3448 CREDAT:3675408 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3448 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://sub2unlock.me/LXzw1" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3628 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3448 CREDAT:1971480 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
73 721
Read events
73 152
Write events
565
Delete events
4
Modification events
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 879024864 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30939791 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30939791 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3448) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
70
Text files
276
Unknown types
83
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:F636ECEB7A5AD83C0726F99BB17B5370 | SHA256:D774FBF79BB62E575B9A575EFD2AA263266FED426178579EEB5FF8955B146865 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:DD4AFCF4F206940F54850110E702DCE8 | SHA256:4A1C41B1C937D985B5D78A6664FC598791E64C7DC20E0FBEA0E5E7ECDEE7E5D4 | |||
| 3448 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:F742C983BFB271422CC314818647A531 | SHA256:A89DDB6D65479220E630154A298DFF5F2F2174365DBD8E78BB08DC2AE6E9D988 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\invisible[1].js | text | |
MD5:80BED80BE09FA71CFBD41C1EDB04B225 | SHA256:B314E1B1C60DB0DEA1A28963E3CCBC1248161AAC1436C82348BB98ACA9013B3B | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | der | |
MD5:71485D6DAD10CEEF12040FD711DF872A | SHA256:3E07FBECBBDEBE402542141B968EC6DD2FE96C4A48C47563B759AD24C3516F30 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_A7725538C46DE2D0088EE44974E2CEBA | binary | |
MD5:22188AEE94FA02B96C4BCD11AFEBB8C5 | SHA256:316B042D705D71118B5403395F0C2B2DF03E556EF6F7AB9B70FA86DE0E02DEBC | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\LXzw1[1].htm | html | |
MD5:236012692ECCEDE035CA5C89811F12D8 | SHA256:815FED9B0D9AD035B3F8D87721DC8B583F16F438FEEF5A97C7039FF2BC12433B | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\F07644E38ED7C9F37D11EEC6D4335E02_936D4E173FC7A4376FA9E9E815E854A4 | der | |
MD5:3E47A960DFC81C6C85D9BEE9CCC29BD6 | SHA256:F7AE12AE13B8B47612A1B946BA5AB01CAD55FBA905B2C4C0433B245BB111D6B1 | |||
| 3348 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A16C6C16D94F76E0808C087DFC657D99_AFA5C73FEB3FB7EE0CF0FEA076EB9A67 | der | |
MD5:FAE9D46DC63E4E2EB52FCE5EDC913084 | SHA256:2CA6180600775191BB0559297FB8DCE4DBAC4B42AD77E4FB50DEF09737EBD29E | |||
| 3448 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:073385420B446EF974A68A1F00D0FA6F | SHA256:F241C56E103DA10CAB4A21A119A21649EBD184CFA5201B41D82D0173D774CB8B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
58
TCP/UDP connections
325
DNS requests
96
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3348 | iexplore.exe | GET | 200 | 23.32.238.201:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?15a5742b95a409ac | US | compressed | 4.70 Kb | whitelisted |
3348 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://crl.pki.goog/gsr1/gsr1.crl | US | der | 1.61 Kb | whitelisted |
3448 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3348 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDfzJPL1j6yvwoAAAABLgJc | US | der | 472 b | whitelisted |
3348 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | US | der | 724 b | whitelisted |
3348 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCLHtDCfO2bBwoAAAABLgJa | US | der | 472 b | whitelisted |
3348 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDIRy5Lqyj5dAoAAAABLgV%2F | US | der | 472 b | whitelisted |
3348 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCv%2F46iPAj3HwoAAAABLgd6 | US | der | 472 b | whitelisted |
3348 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDKa002niAMOQoAAAABLgV0 | US | der | 472 b | whitelisted |
3348 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAonX%2BcE1u7LI9XNW0saTgQ%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3348 | iexplore.exe | 142.250.186.174:443 | fundingchoicesmessages.google.com | Google Inc. | US | whitelisted |
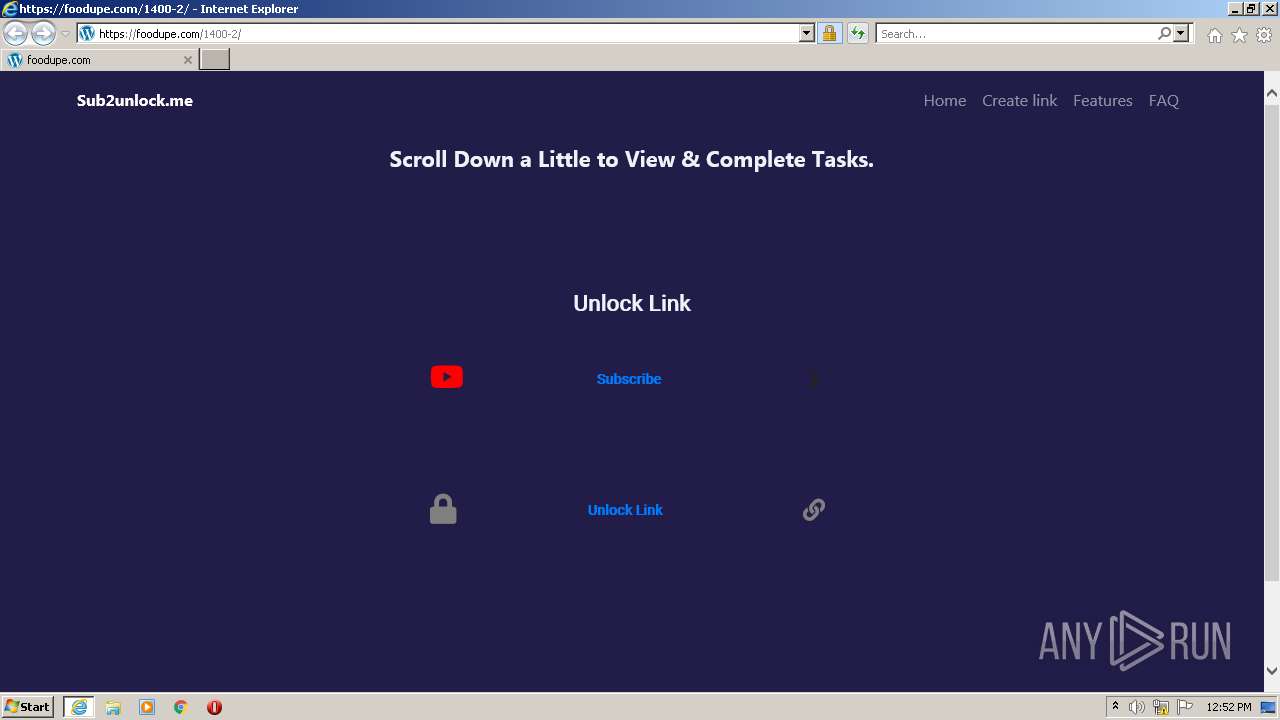
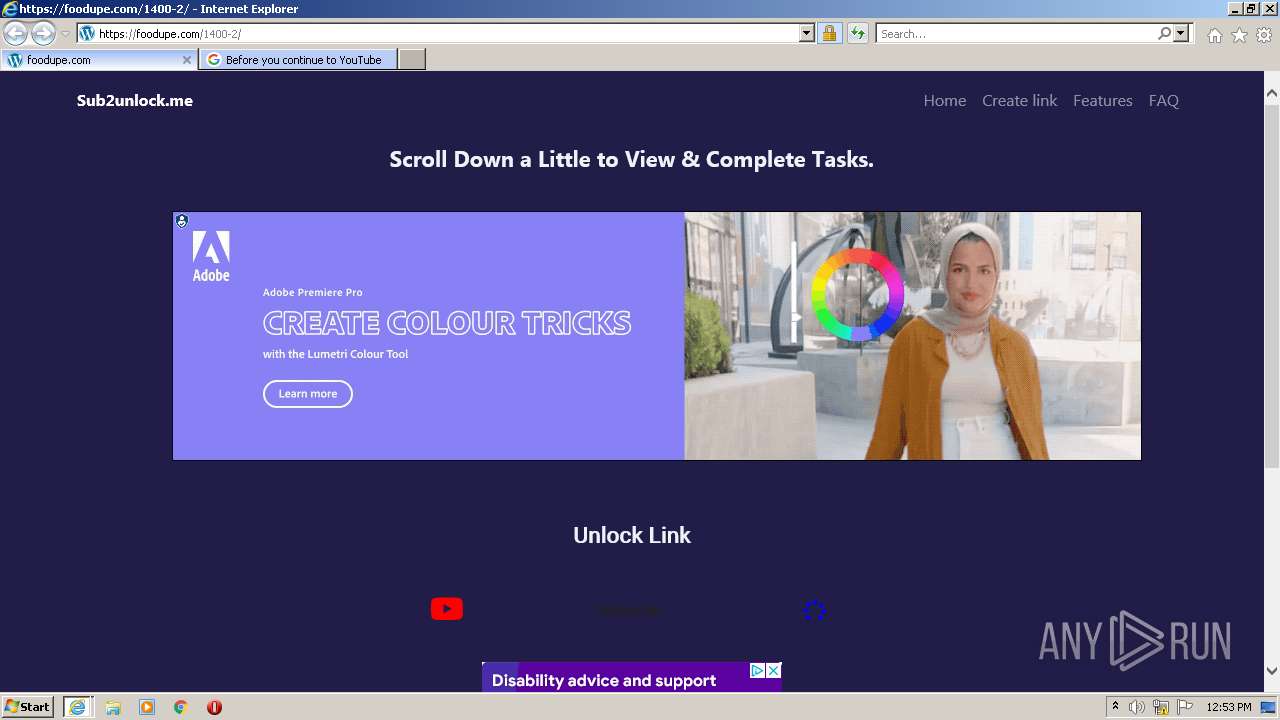
3348 | iexplore.exe | 172.67.167.9:443 | sub2unlock.me | — | US | suspicious |
3348 | iexplore.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
3348 | iexplore.exe | 23.32.238.201:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
3348 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3348 | iexplore.exe | 142.250.186.72:443 | www.googletagmanager.com | Google Inc. | US | suspicious |
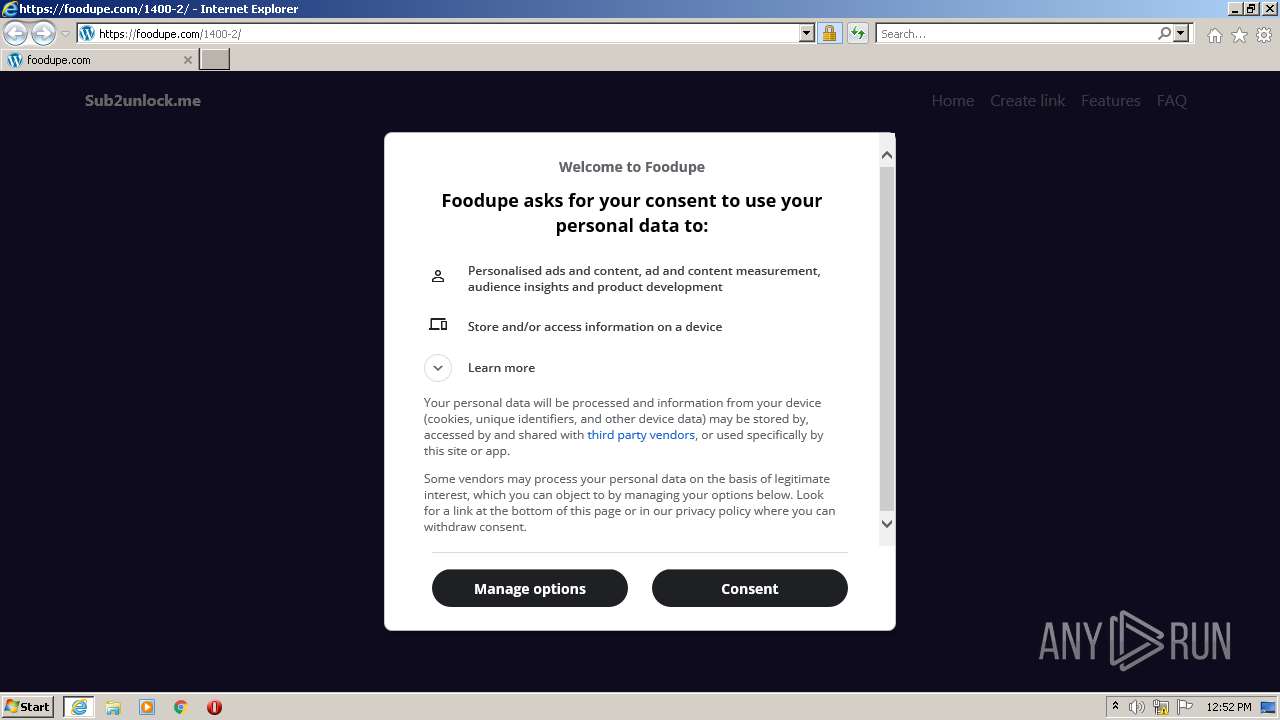
3348 | iexplore.exe | 172.67.140.182:443 | foodupe.com | — | US | unknown |
3348 | iexplore.exe | 142.250.186.131:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3348 | iexplore.exe | 142.250.185.100:443 | www.google.com | Google Inc. | US | whitelisted |
3448 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sub2unlock.me |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
foodupe.com |
| unknown |
ocsp.pki.goog |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.google.com |
| malicious |
crl.pki.goog |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
3348 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3348 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3348 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3348 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3348 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3348 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3348 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3348 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3348 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |