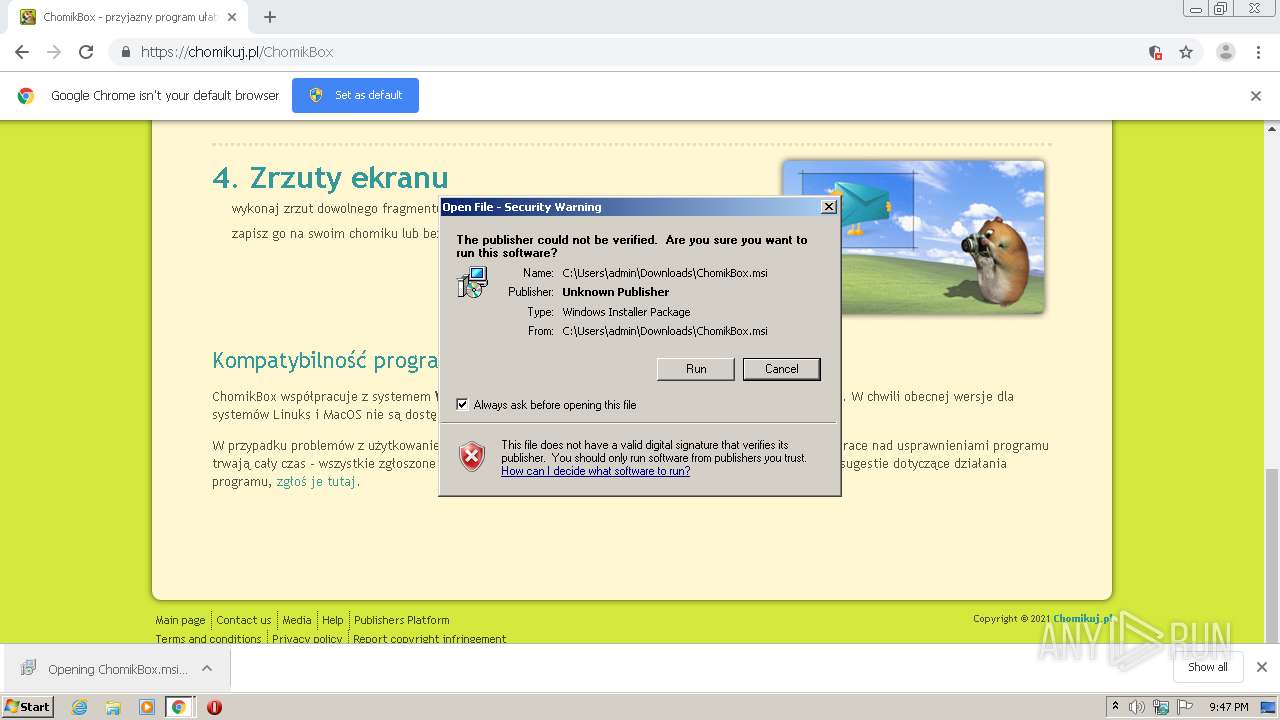
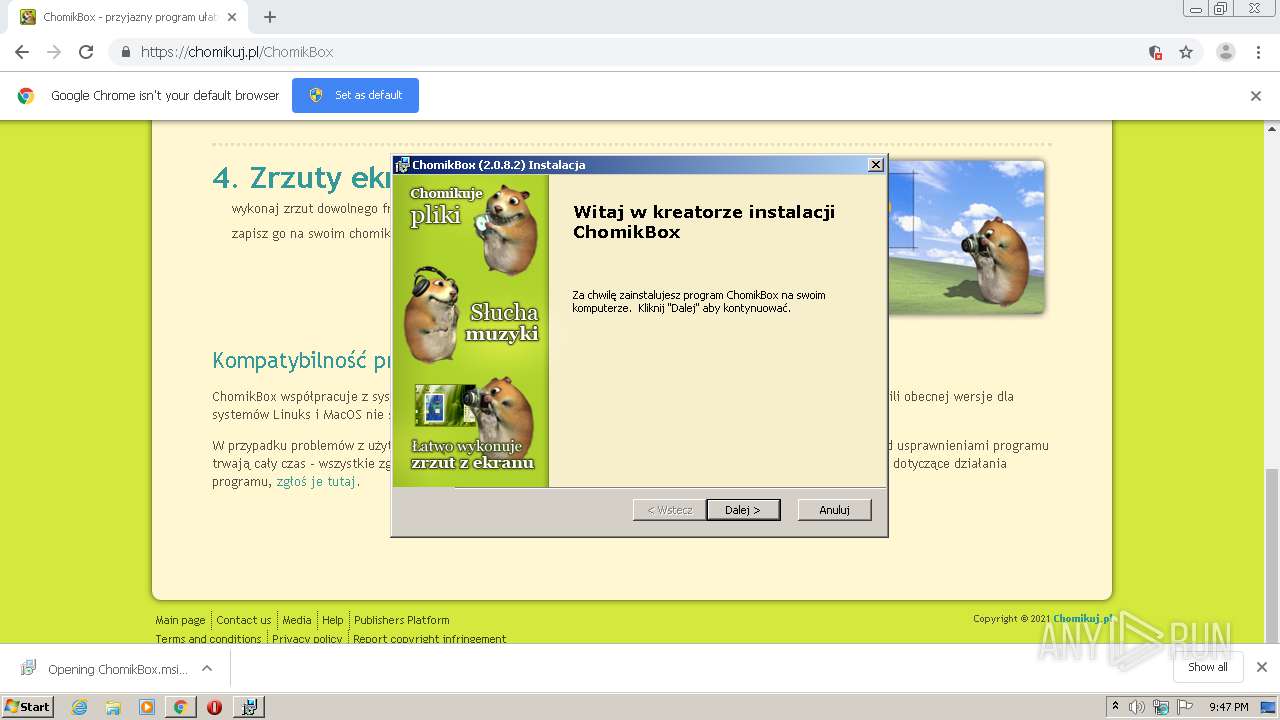
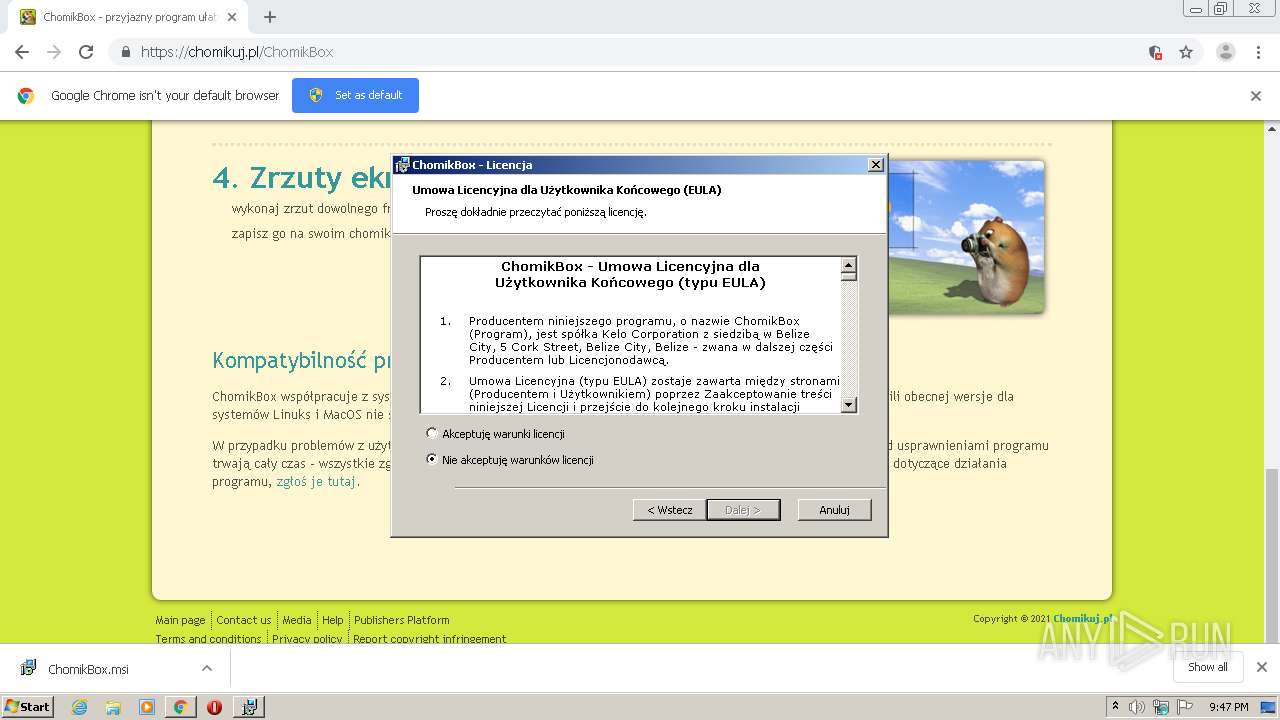
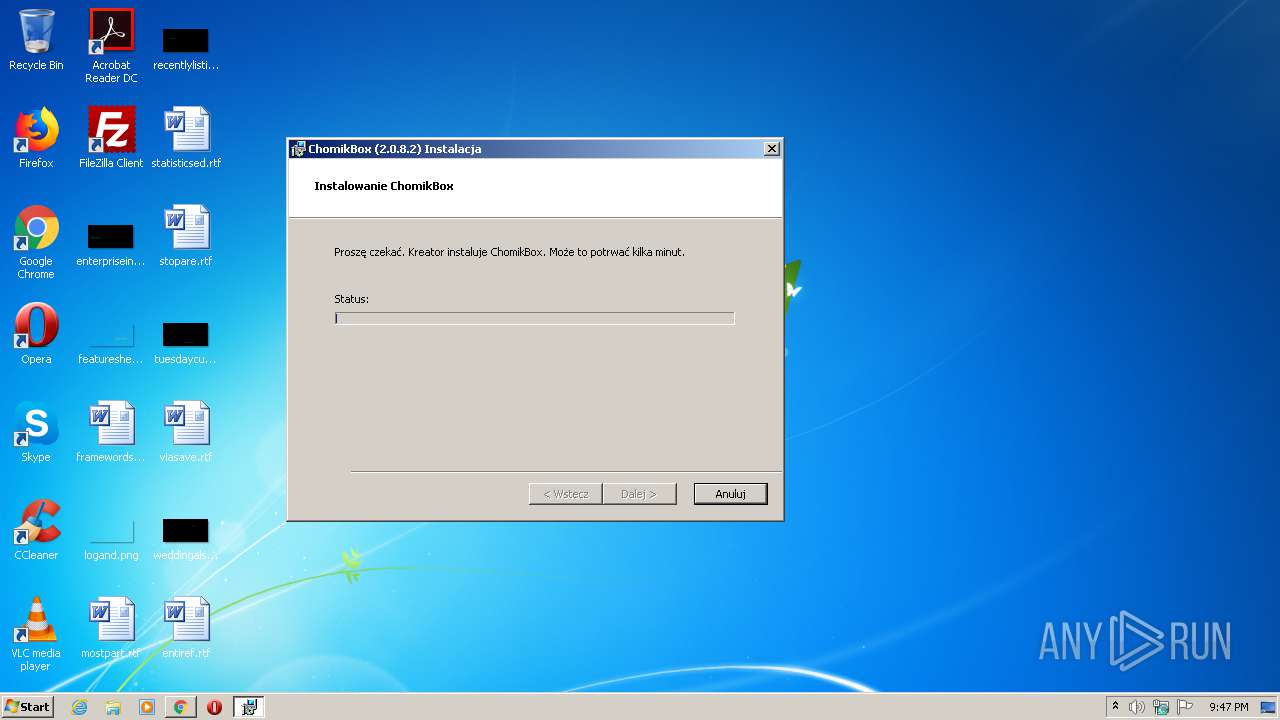
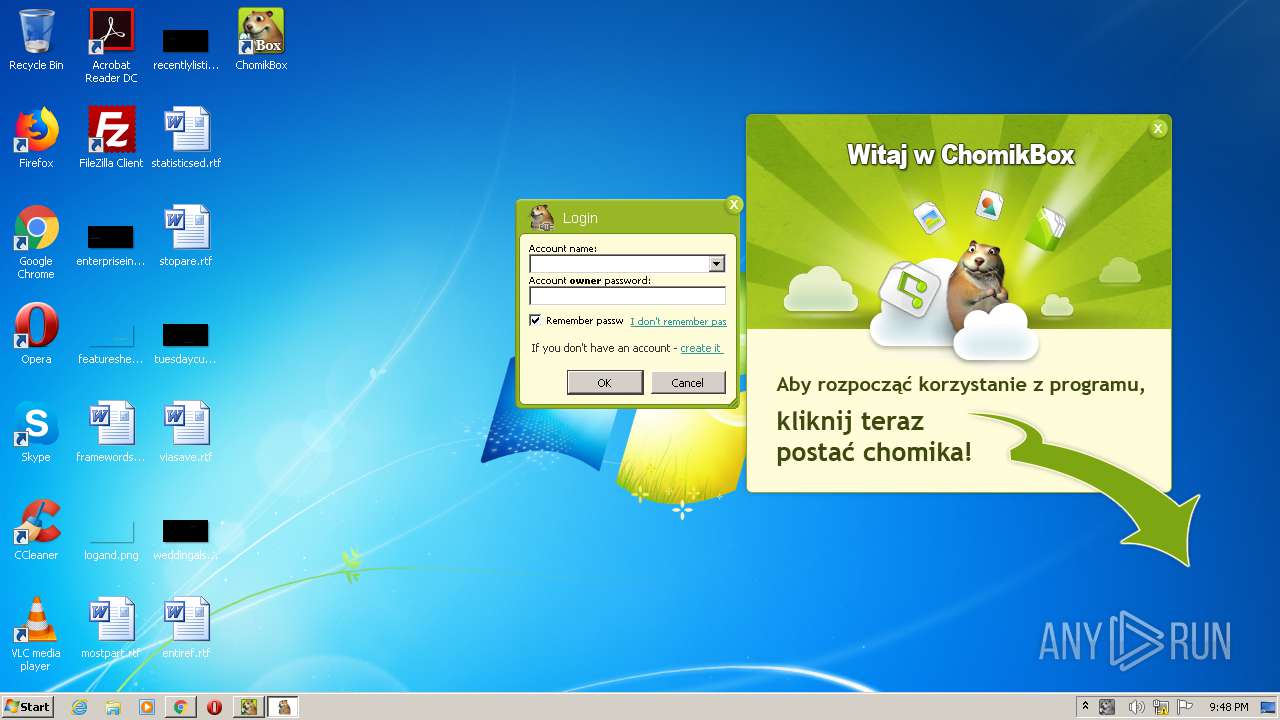
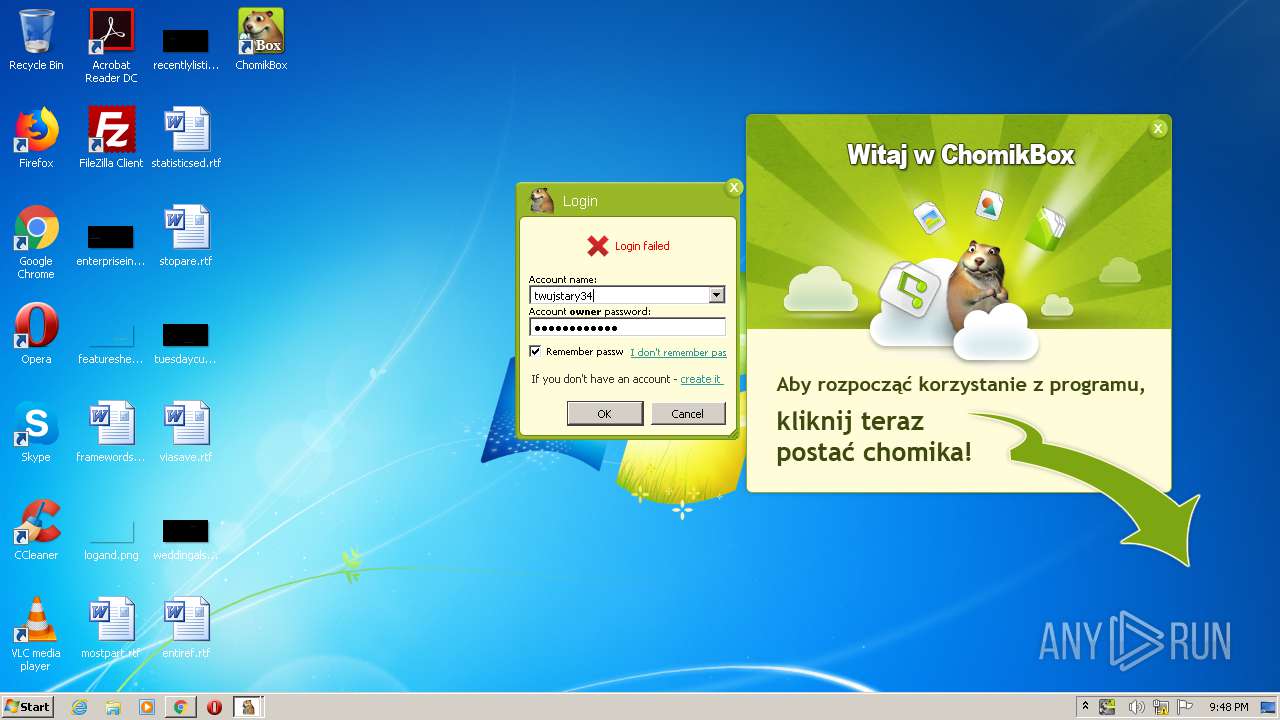
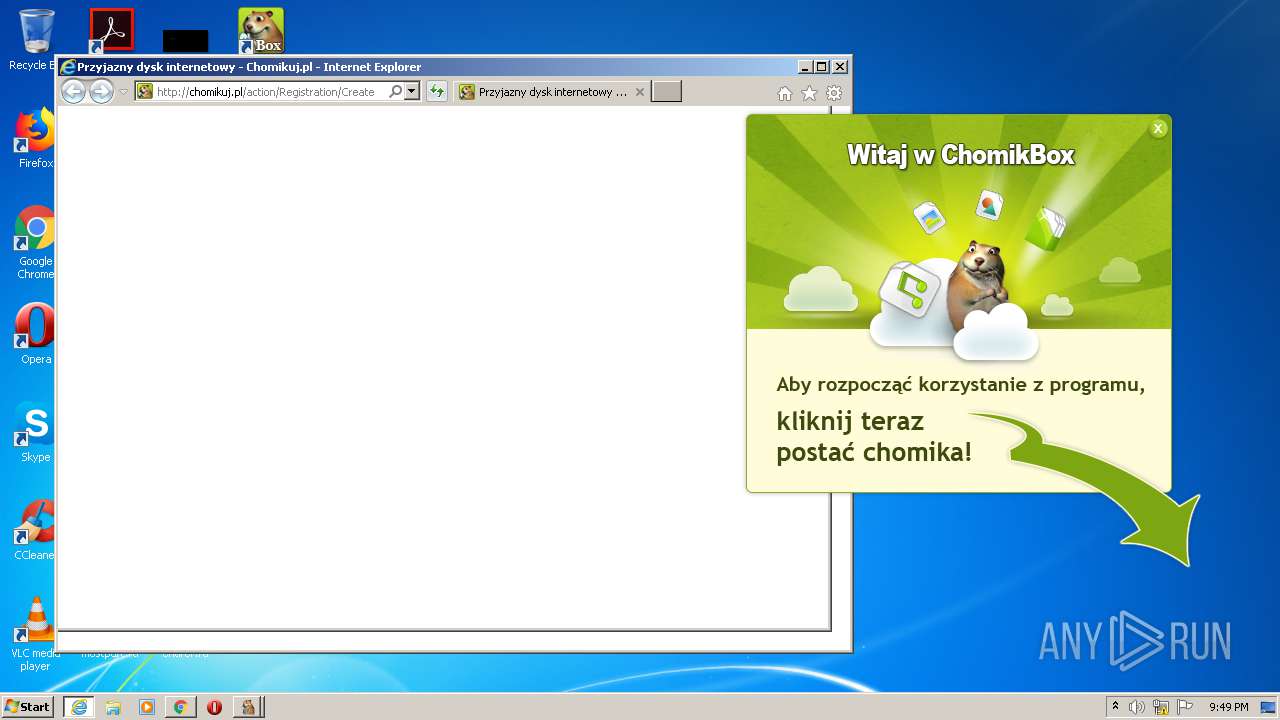
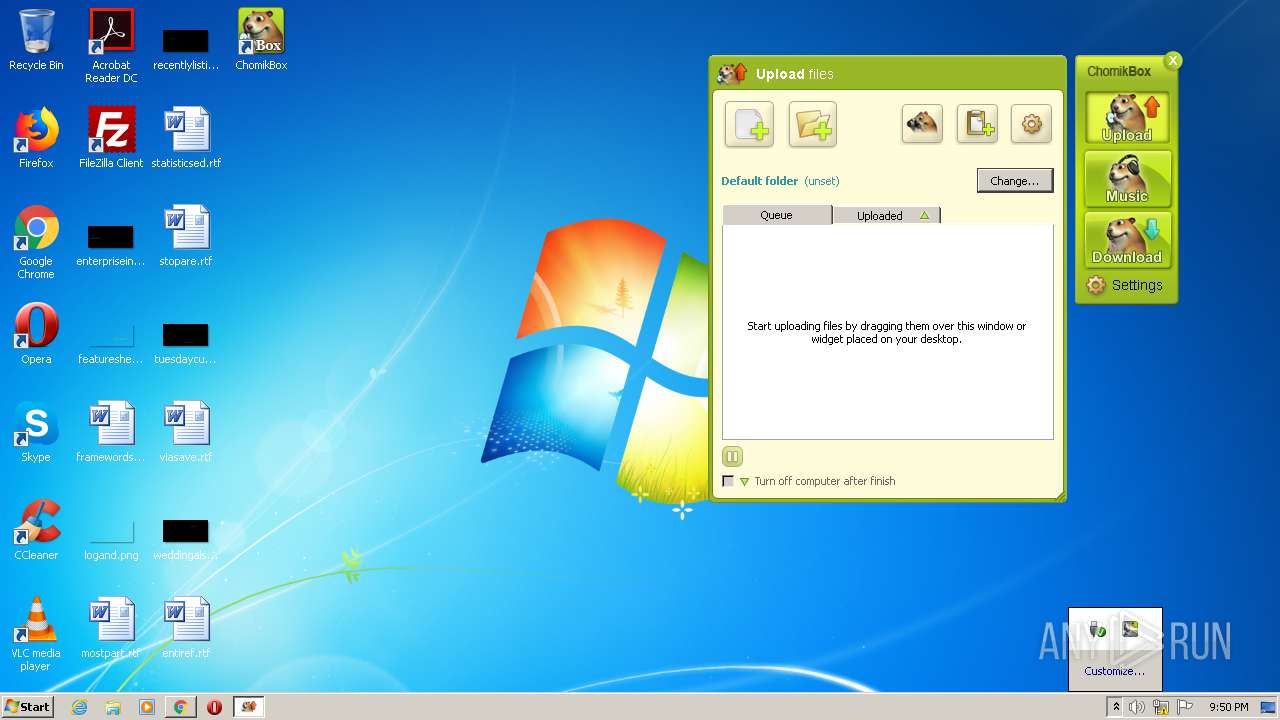
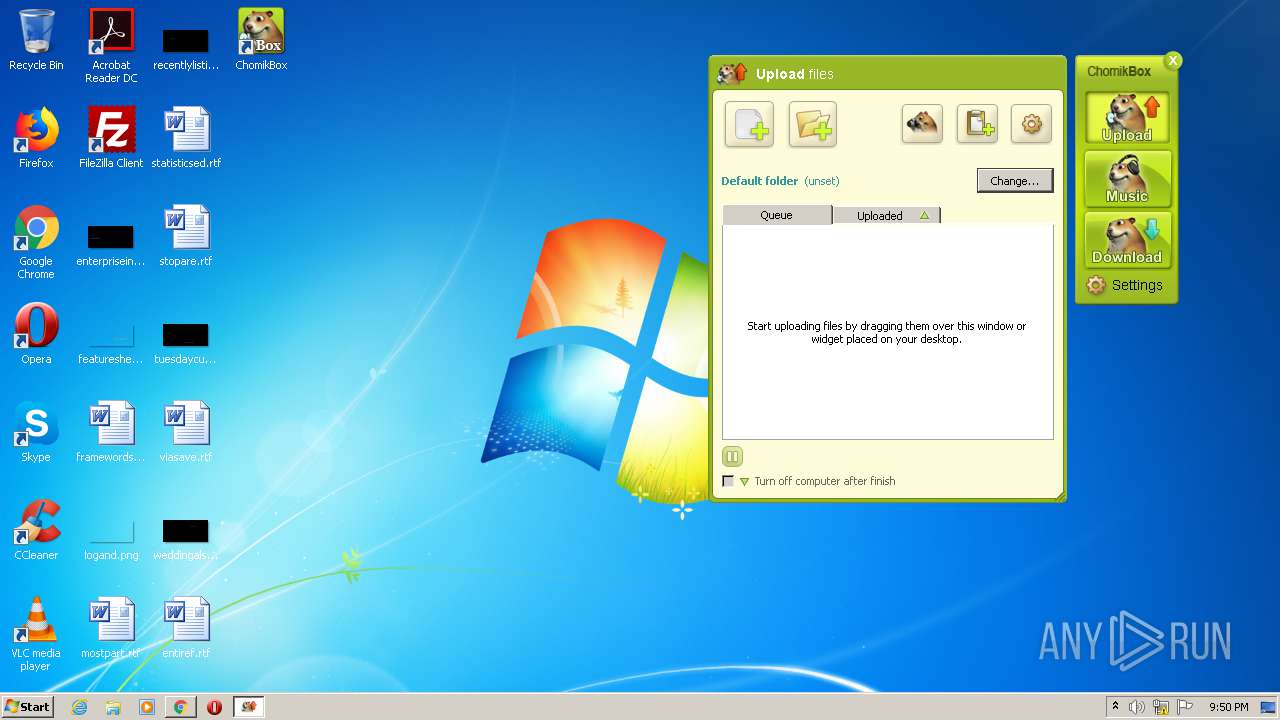
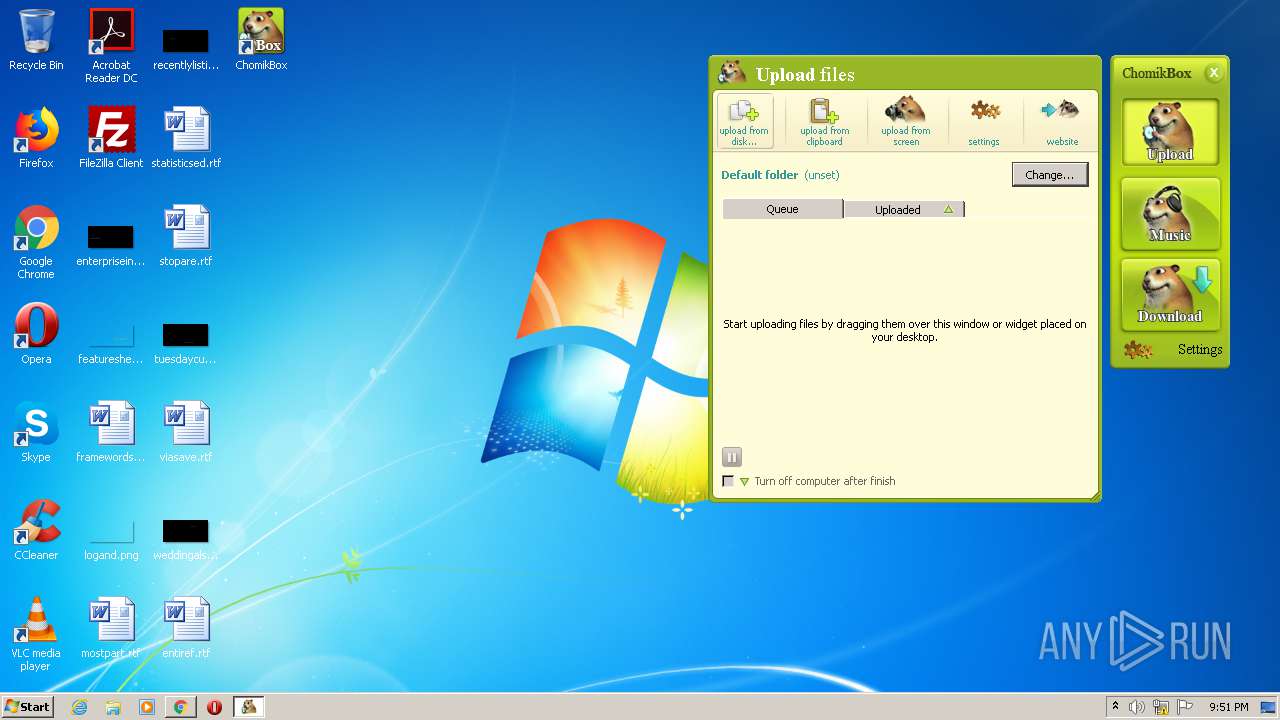
| URL: | https://chomikuj.pl/ChomikBox |
| Full analysis: | https://app.any.run/tasks/ba14fd7b-7c6c-44e9-8c63-ba780352130c |
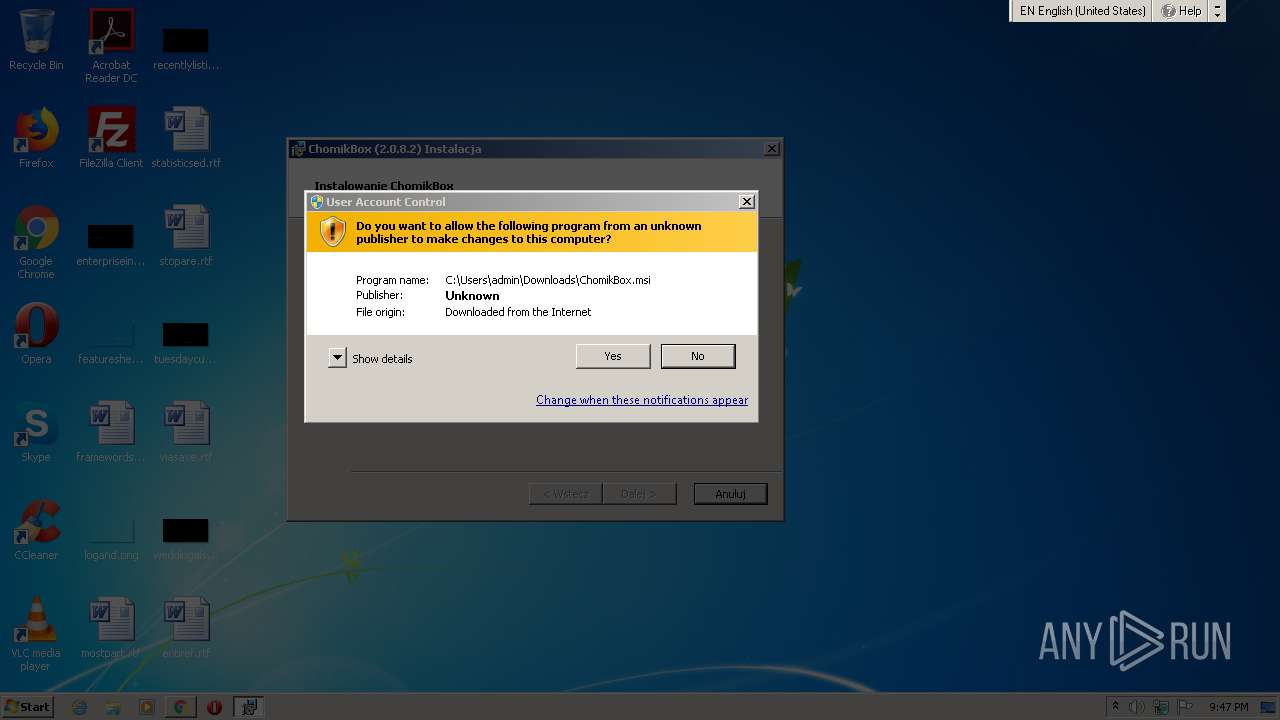
| Verdict: | Malicious activity |
| Analysis date: | May 29, 2021, 20:46:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | CAB60CD60748EC0E58F01B487F9C5C9B |
| SHA1: | 7B6AC67D162776D3524FF4B671FE262CB74223E8 |
| SHA256: | D6E0F052E64D3EE45D3D15E62A2669C96BDD565E1CE87A8E36C2627746EECF7B |
| SSDEEP: | 3:N8QEzVJKeMIKd:2QEX7M3d |
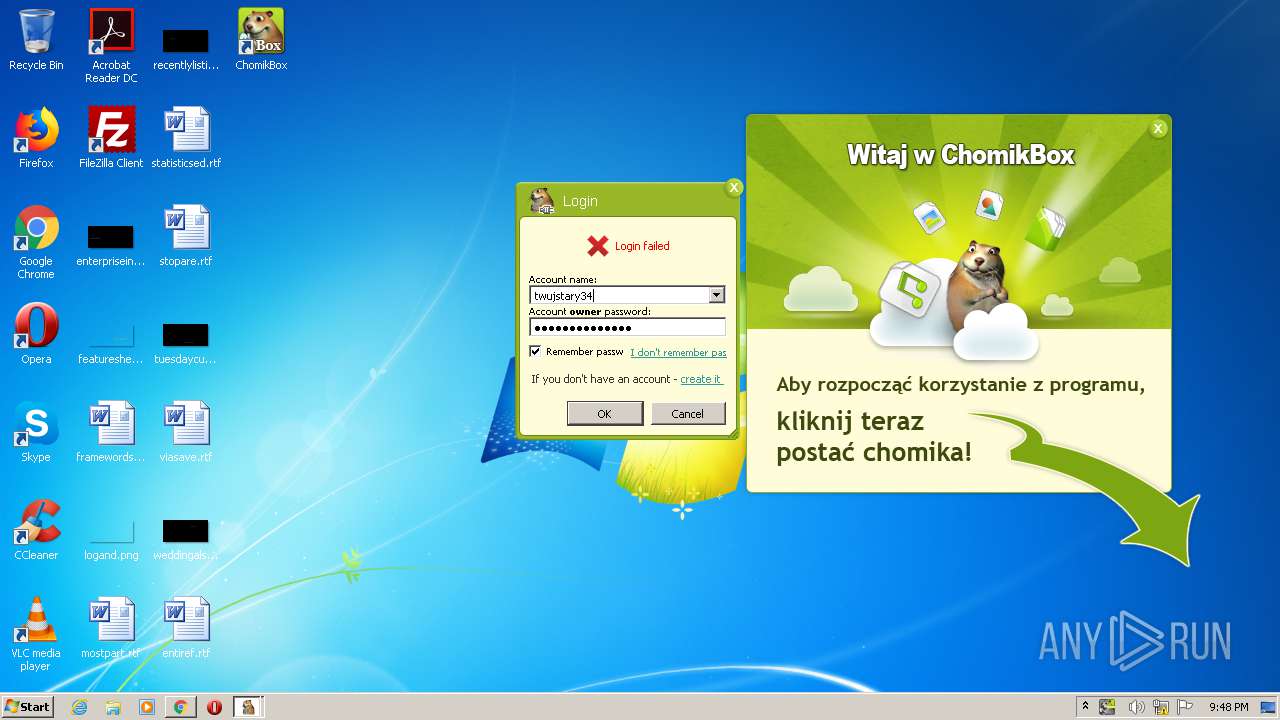
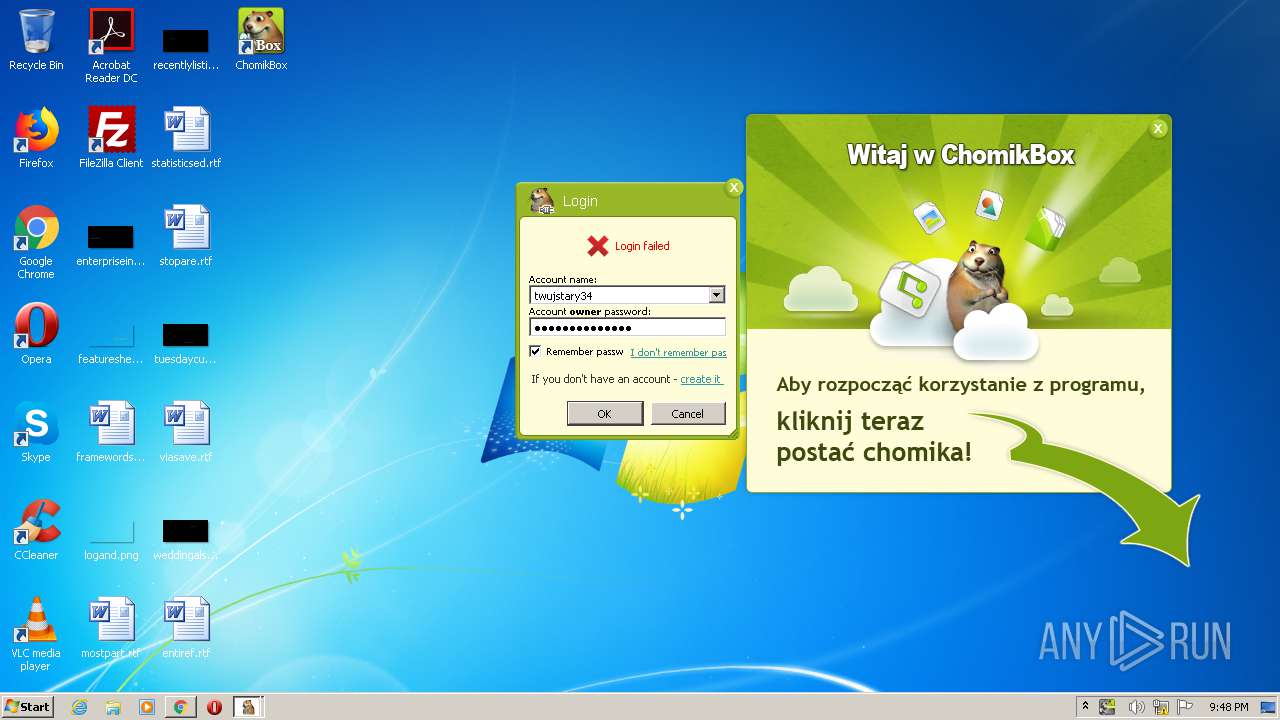
MALICIOUS
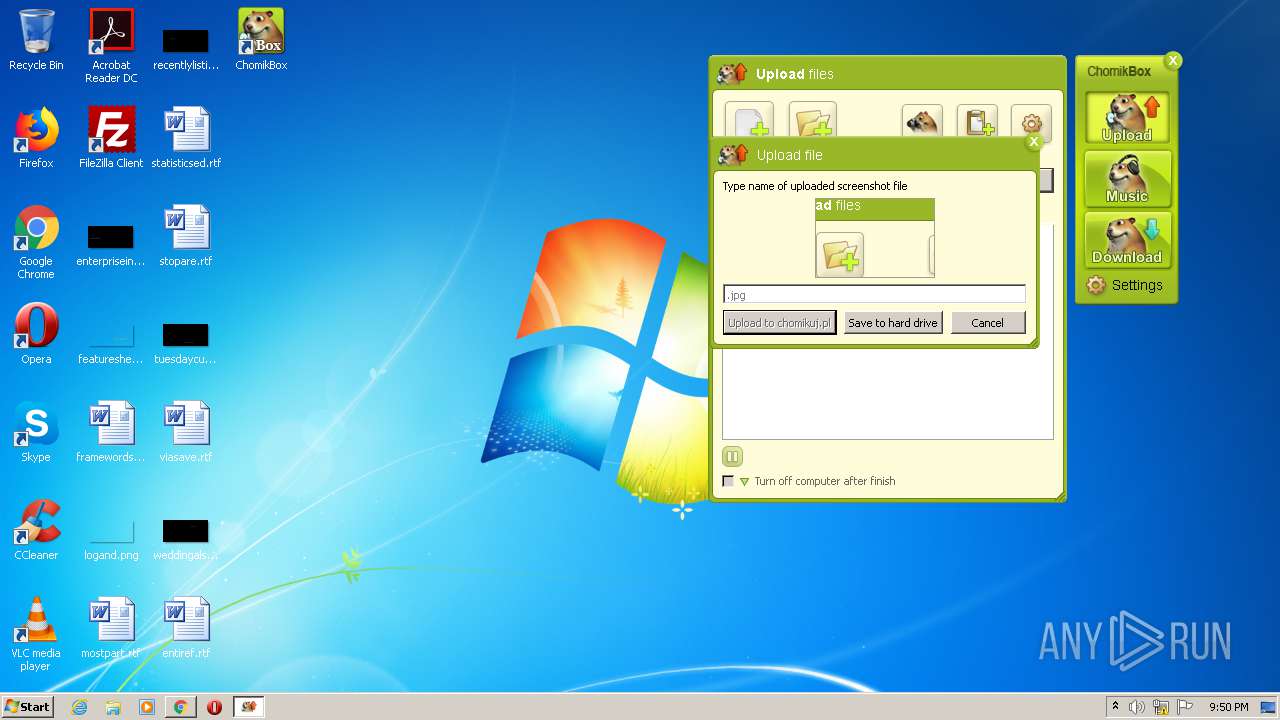
Application was dropped or rewritten from another process
- ChomikBox.exe (PID: 4024)
- chomikbox1conf.exe (PID: 2740)
- ChomikBox.exe (PID: 3928)
Changes the autorun value in the registry
- ChomikBox.exe (PID: 4024)
Loads dropped or rewritten executable
- ChomikBox.exe (PID: 4024)
- wmiprvse.exe (PID: 1768)
- chomikbox1conf.exe (PID: 2740)
- ChomikBox.exe (PID: 3928)
Application was injected by another process
- csrss.exe (PID: 348)
- smss.exe (PID: 264)
- winlogon.exe (PID: 432)
- services.exe (PID: 476)
- wininit.exe (PID: 384)
- lsm.exe (PID: 500)
- csrss.exe (PID: 392)
- svchost.exe (PID: 604)
- svchost.exe (PID: 772)
- lsass.exe (PID: 492)
- svchost.exe (PID: 684)
- svchost.exe (PID: 816)
- svchost.exe (PID: 844)
- spoolsv.exe (PID: 1208)
- svchost.exe (PID: 1064)
- svchost.exe (PID: 880)
- IMEDICTUPDATE.EXE (PID: 1376)
- svchost.exe (PID: 1792)
- srvpost.exe (PID: 1452)
- dwm.exe (PID: 120)
- explorer.exe (PID: 292)
- ctfmon.exe (PID: 668)
- taskeng.exe (PID: 1996)
- SearchIndexer.exe (PID: 1348)
- SearchProtocolHost.exe (PID: 3608)
- SearchProtocolHost.exe (PID: 2024)
- svchost.exe (PID: 2476)
- TrustedInstaller.exe (PID: 3152)
- svchost.exe (PID: 1236)
- host.exe (PID: 3824)
Runs injected code in another process
- wmiprvse.exe (PID: 1768)
SUSPICIOUS
Creates files in the user directory
- lsass.exe (PID: 492)
- msiexec.exe (PID: 2768)
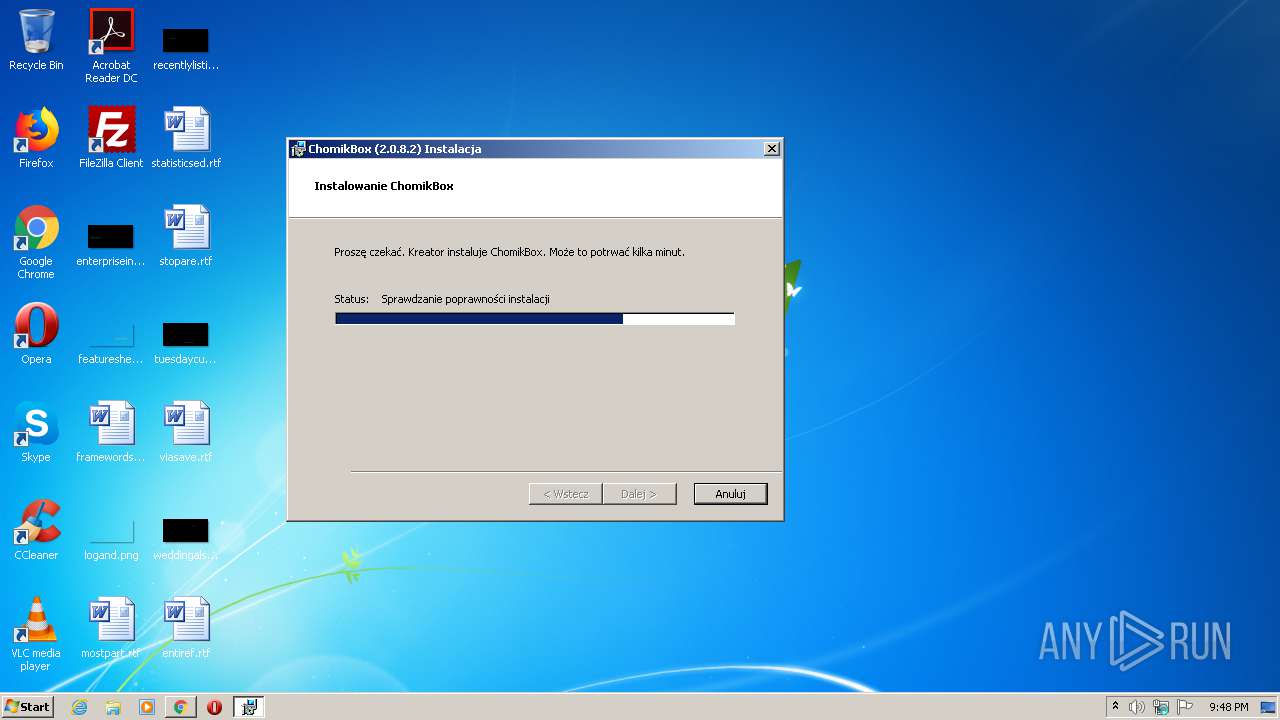
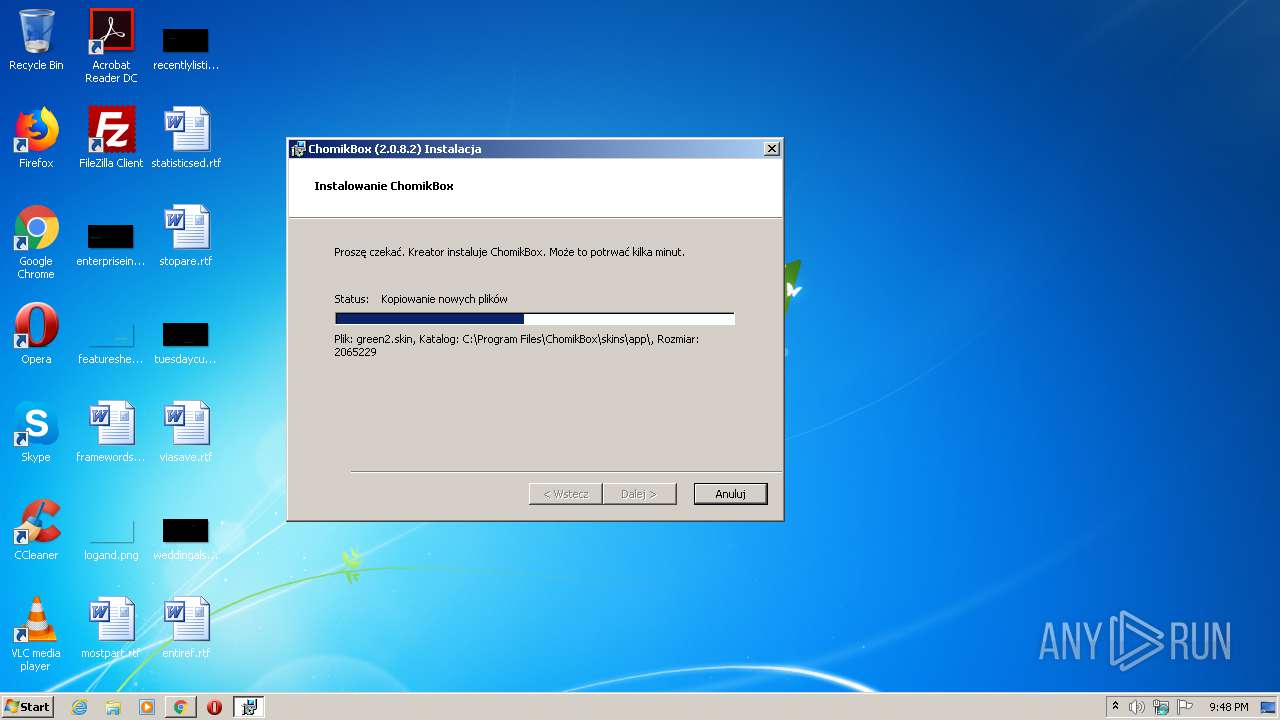
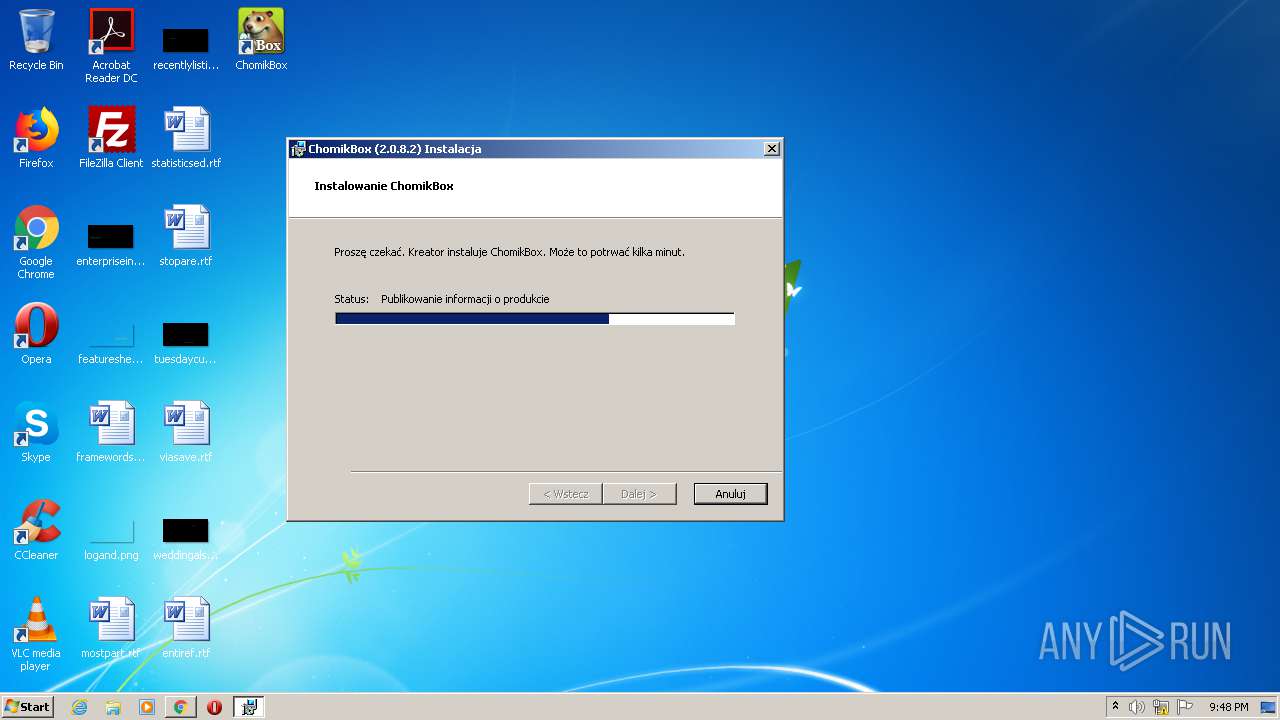
Starts Microsoft Installer
- chrome.exe (PID: 3980)
Executed as Windows Service
- vssvc.exe (PID: 4044)
Drops a file with a compile date too recent
- chrome.exe (PID: 3980)
Creates files in the Windows directory
- msiexec.exe (PID: 2768)
- TrustedInstaller.exe (PID: 3152)
Creates files in the program directory
- SearchIndexer.exe (PID: 1348)
Creates a directory in Program Files
- msiexec.exe (PID: 2768)
Drops a file that was compiled in debug mode
- msiexec.exe (PID: 2768)
Changes default file association
- msiexec.exe (PID: 2768)
Removes files from Windows directory
- msiexec.exe (PID: 2768)
- TrustedInstaller.exe (PID: 3152)
Loads DLL from Mozilla Firefox
- csrss.exe (PID: 392)
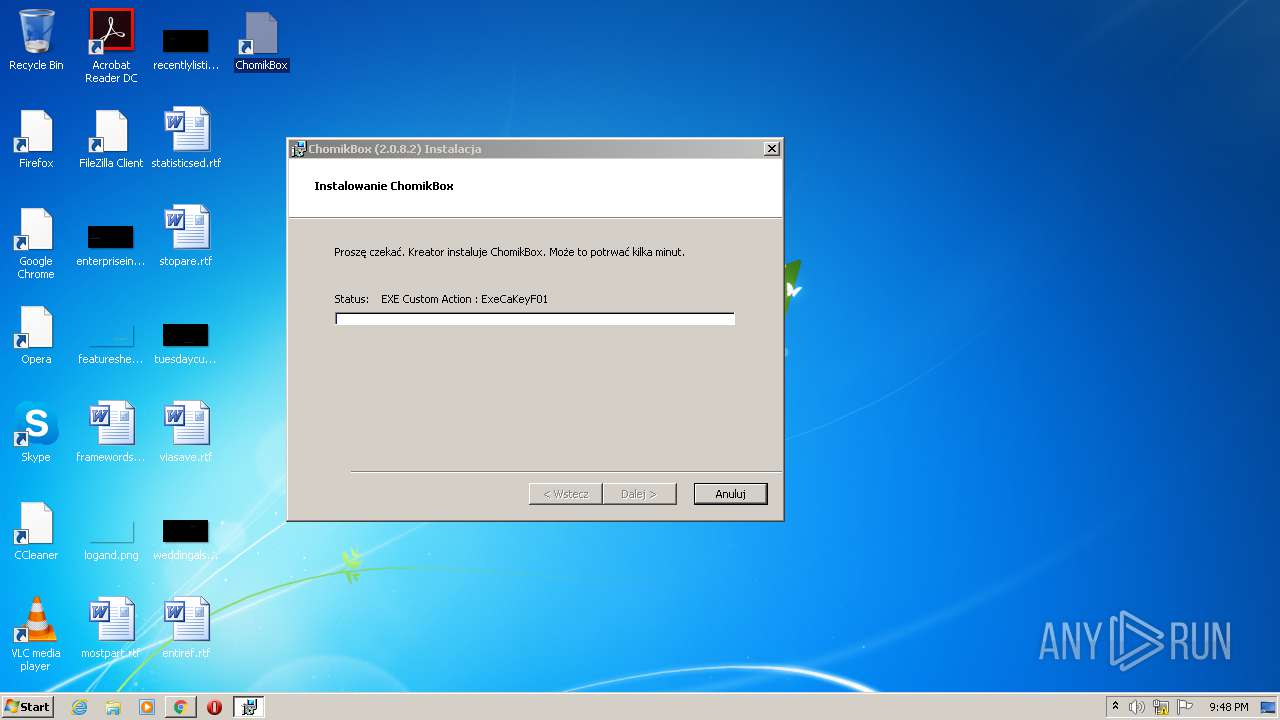
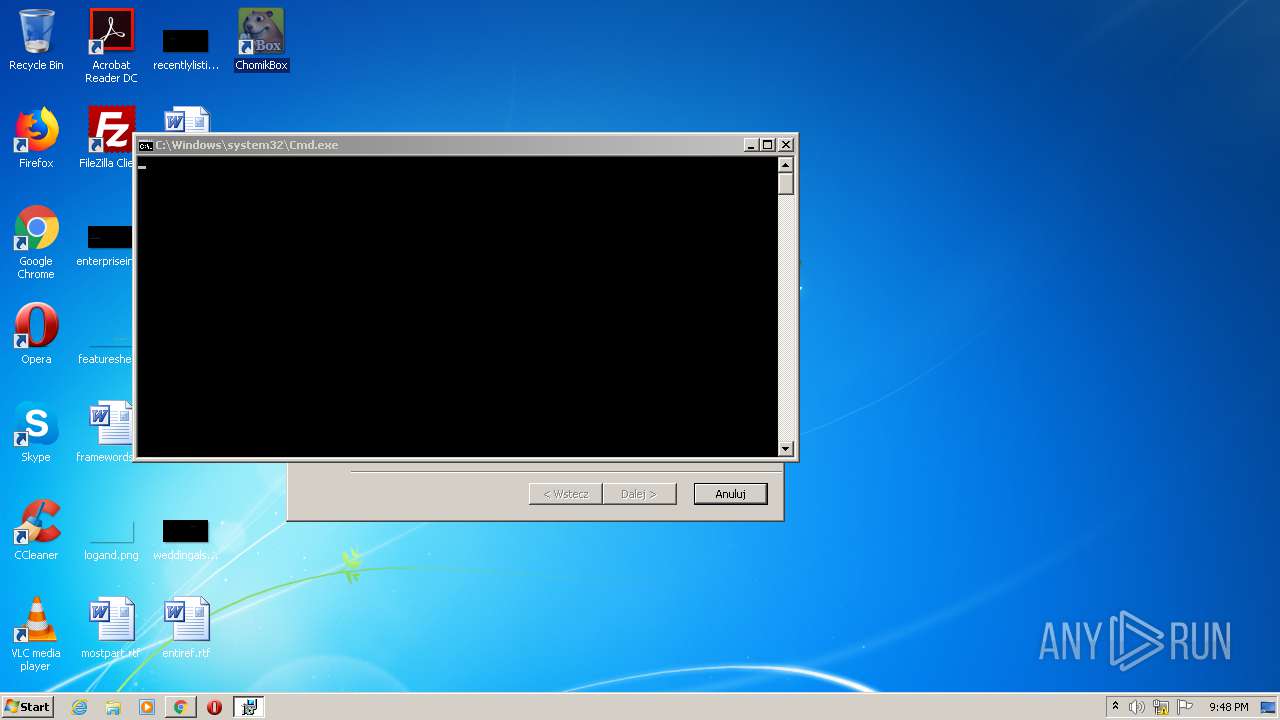
Starts CMD.EXE for commands execution
- msiexec.exe (PID: 2768)
Executable content was dropped or overwritten
- ChomikBox.exe (PID: 4024)
- msiexec.exe (PID: 2768)
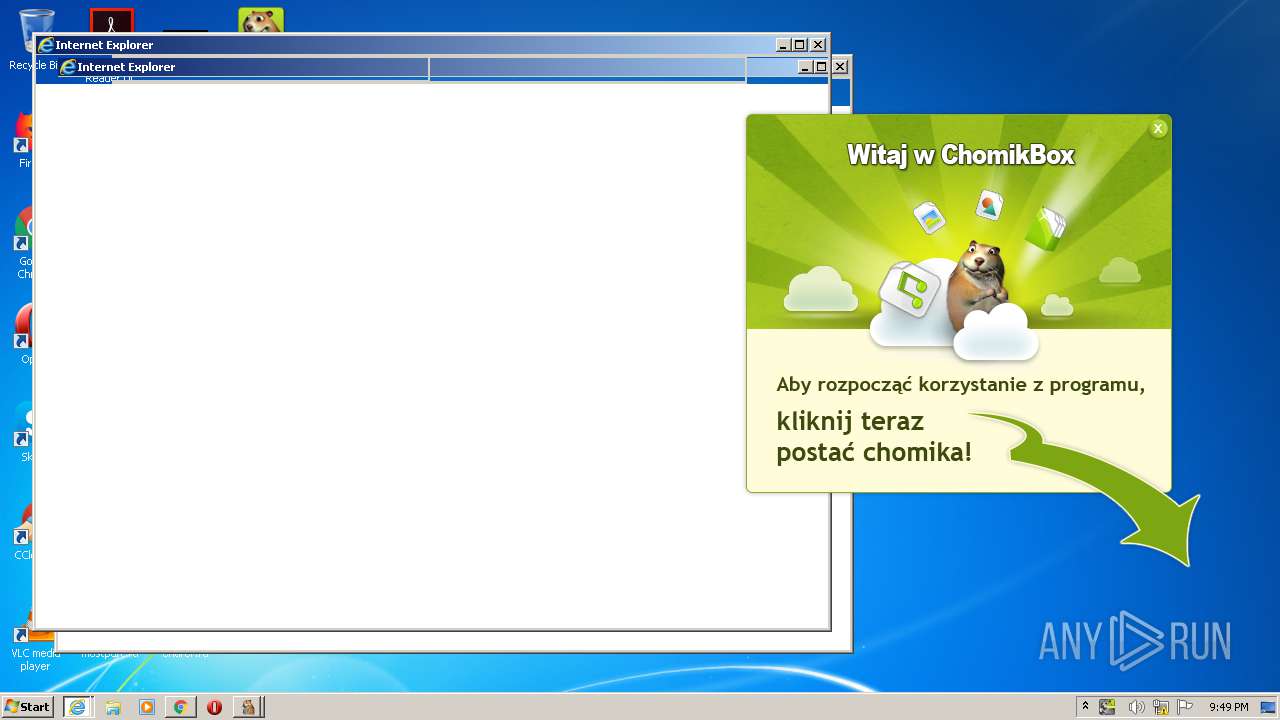
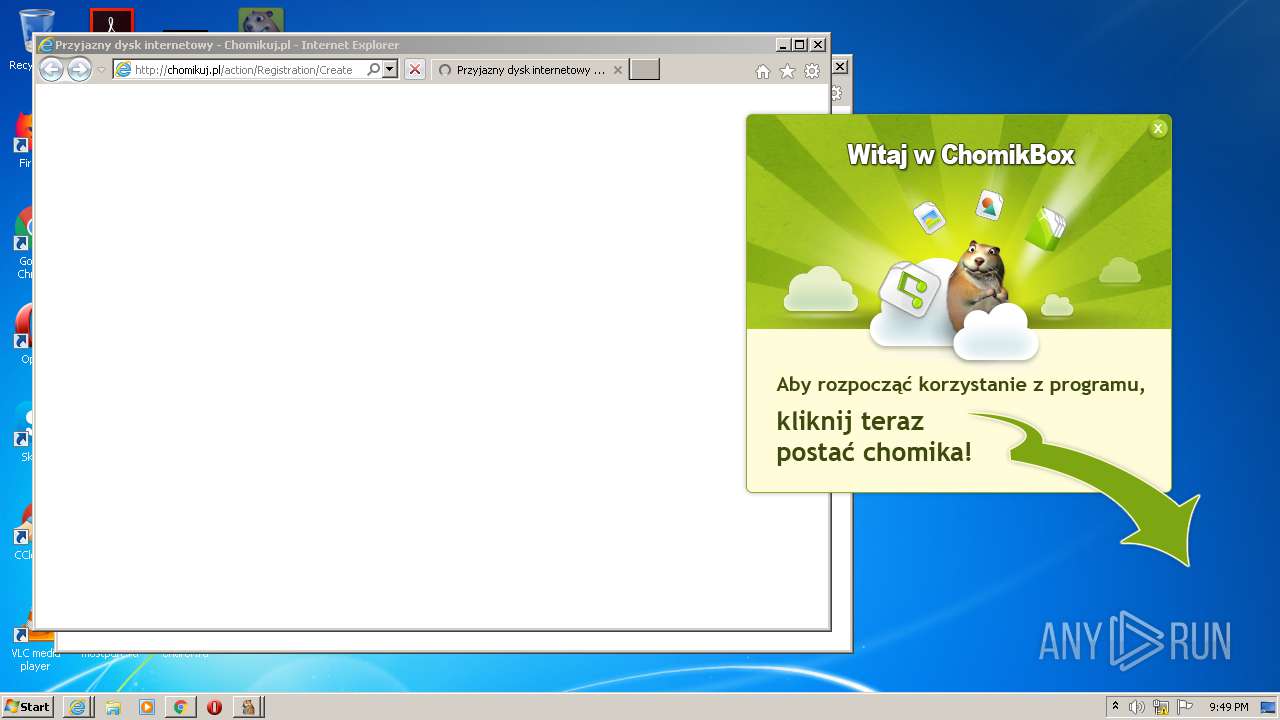
Starts Internet Explorer
- ChomikBox.exe (PID: 4024)
Executed via COM
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3052)
INFO
Application launched itself
- chrome.exe (PID: 3980)
- iexplore.exe (PID: 2744)
- iexplore.exe (PID: 2992)
Reads the hosts file
- chrome.exe (PID: 3980)
- chrome.exe (PID: 2896)
Searches for installed software
- msiexec.exe (PID: 2768)
Low-level read access rights to disk partition
- vssvc.exe (PID: 4044)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2768)
Creates a software uninstall entry
- msiexec.exe (PID: 2768)
Loads dropped or rewritten executable
- msiexec.exe (PID: 2768)
Changes internet zones settings
- iexplore.exe (PID: 2744)
- iexplore.exe (PID: 2992)
Creates files in the program directory
- msiexec.exe (PID: 2768)
Creates files in the user directory
- iexplore.exe (PID: 3932)
- iexplore.exe (PID: 2744)
- iexplore.exe (PID: 2204)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3052)
- iexplore.exe (PID: 2992)
Reads internet explorer settings
- iexplore.exe (PID: 2204)
- iexplore.exe (PID: 3932)
Reads settings of System Certificates
- iexplore.exe (PID: 2204)
- iexplore.exe (PID: 3932)
- iexplore.exe (PID: 2992)
- iexplore.exe (PID: 2744)
Changes settings of System certificates
- iexplore.exe (PID: 2744)
- iexplore.exe (PID: 2992)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2744)
- iexplore.exe (PID: 2992)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
56
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | "C:\Windows\system32\Dwm.exe" | C:\Windows\System32\dwm.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Desktop Window Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 264 | \SystemRoot\System32\smss.exe | C:\Windows\System32\smss.exe | System | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Session Manager Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 292 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 348 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 384 | wininit.exe | C:\Windows\System32\wininit.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Start-Up Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 392 | %SystemRoot%\system32\csrss.exe ObjectDirectory=\Windows SharedSection=1024,12288,512 Windows=On SubSystemType=Windows ServerDll=basesrv,1 ServerDll=winsrv:UserServerDllInitialization,3 ServerDll=winsrv:ConServerDllInitialization,2 ServerDll=sxssrv,4 ProfileControl=Off MaxRequestThreads=16 | C:\Windows\System32\csrss.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Client Server Runtime Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 432 | winlogon.exe | C:\Windows\System32\winlogon.exe | — | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Logon Application Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 476 | C:\Windows\system32\services.exe | C:\Windows\System32\services.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Services and Controller app Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 492 | C:\Windows\system32\lsass.exe | C:\Windows\System32\lsass.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Security Authority Process Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 500 | C:\Windows\system32\lsm.exe | C:\Windows\System32\lsm.exe | wininit.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Local Session Manager Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8 414
Read events
7 363
Write events
1 021
Delete events
30
Modification events
| (PID) Process: | (292) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Action Center\Checks\{C8E6F269-B90A-4053-A3BE-499AFCEC98C4}.check.0 |
| Operation: | write | Name: | CheckSetting |
Value: 01000000D08C9DDF0115D1118C7A00C04FC297EB010000008E25677CBCD31C499F56375CD369015C000000000200000000001066000000010000200000003EE74C5510336D8B3947AF7E36150C8B74F57A2CEA3EDB3336BE630604AB9513000000000E8000000002000020000000D2AD55D6F501188519744846A482405DCC23417CE7172EB92A130CA21A836D313000000035228D61263516855AE1242CE2C1F683869F72609318150790FBA7408C7A7259DE577BBDA1D2154E91030197D23219F140000000627A97E63FDC175CCF8C41FD6DA07E7247BC70A461C9F4F9BA43B139AB2FF089E2B6885C58B4CE514B3CF689787C44F7D48B371883DBE9F408CE2BD47E9C27DB | |||
| (PID) Process: | (3980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3980) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (3980) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
114
Suspicious files
151
Text files
154
Unknown types
55
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60B2A84D-F8C.pma | — | |
MD5:— | SHA256:— | |||
| 3980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\2a855d69-d360-4067-bcc4-b0730153a07d.tmp | — | |
MD5:— | SHA256:— | |||
| 3980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 844 | svchost.exe | C:\Windows\ServiceProfiles\LocalService\AppData\Local\~FontCache-S-1-5-21-1302019708-1500728564-335382590-1000.dat | — | |
MD5:— | SHA256:— | |||
| 492 | lsass.exe | C:\Users\admin\AppData\Roaming\Microsoft\Protect\S-1-5-21-1302019708-1500728564-335382590-1000\7c67258e-d3bc-491c-9f56-375cd369015c | binary | |
MD5:9585F9A7520B4C69C19BFC8B867EADC3 | SHA256:5A005288489C207B0D90A634F3DFF9FDCA39B62FF8FC74595D658E58B1B72DBB | |||
| 3980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF183524.TMP | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 3980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 3980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF183534.TMP | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 3980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:D4322EEBAC92D1B8F7A6F5E39F6264B7 | SHA256:A3EEDF21B850DCC7CE5AE04395ECDD2D29DA4EA549C8A185DD9E8B552A87B8C2 | |||
| 3980 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF183582.TMP | text | |
MD5:67F45CAA18C889645F50CD6216C81E65 | SHA256:33ED82CDDDFFD55A5059C147C6CD20F66C6712314F890A39576D3C10914D0029 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
118
TCP/UDP connections
120
DNS requests
55
Threats
16
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4024 | ChomikBox.exe | GET | 200 | 95.211.227.131:80 | http://download.box.chomikuj.pl/updates/2.0.8.2/win32/packages.xml | NL | xml | 10.1 Kb | suspicious |
4024 | ChomikBox.exe | GET | 200 | 95.211.227.131:80 | http://download.box.chomikuj.pl/updates/2.0.8.2/win32/chomikbox.exe.gz | NL | compressed | 1.47 Mb | suspicious |
4024 | ChomikBox.exe | GET | 301 | 95.211.227.131:80 | http://download.box.chomikuj.pl/updates/win32/packages.xml | NL | html | 189 b | suspicious |
4024 | ChomikBox.exe | GET | 200 | 95.211.227.131:80 | http://download.box.chomikuj.pl/updates/2.0.8.2/win32/configurator.exe.gz | NL | compressed | 102 Kb | suspicious |
4024 | ChomikBox.exe | GET | 200 | 95.211.227.131:80 | http://download.box.chomikuj.pl/updates/2.0.8.2/win32/installer.exe.gz | NL | compressed | 55.4 Kb | suspicious |
4024 | ChomikBox.exe | GET | 200 | 95.211.227.131:80 | http://download.box.chomikuj.pl/updates/2.0.8.2/win32/chomikbox1conf.exe.gz | NL | compressed | 153 Kb | suspicious |
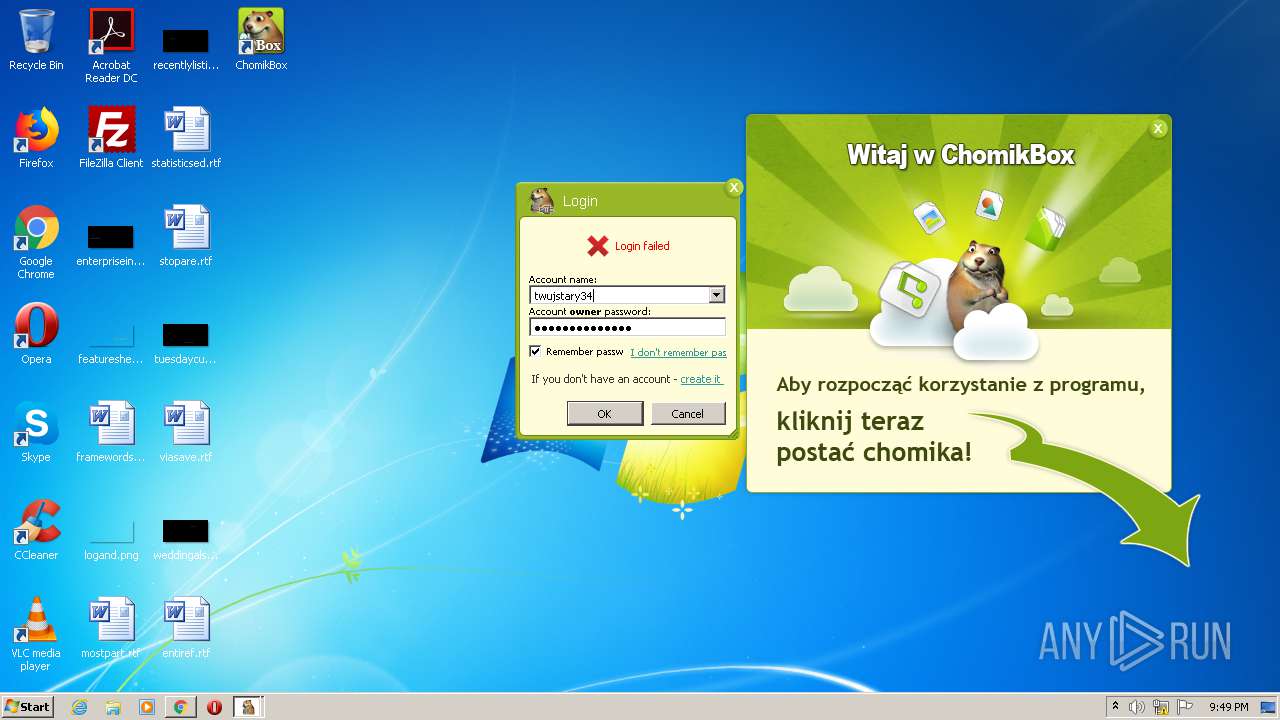
4024 | ChomikBox.exe | POST | 200 | 104.22.25.70:80 | http://box.chomikuj.pl/services/ChomikBoxService.svc | US | text | 249 b | suspicious |
4024 | ChomikBox.exe | POST | 200 | 104.22.25.70:80 | http://box.chomikuj.pl/services/ChomikBoxService.svc | US | text | 249 b | suspicious |
4024 | ChomikBox.exe | GET | 200 | 95.211.227.131:80 | http://download.box.chomikuj.pl/updates/2.0.8.2/win32/installeru.exe.gz | NL | compressed | 55.4 Kb | suspicious |
4024 | ChomikBox.exe | POST | 200 | 104.22.25.70:80 | http://box.chomikuj.pl/services/ChomikBoxService.svc | US | text | 249 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2896 | chrome.exe | 172.67.42.83:443 | chomikuj.pl | — | US | suspicious |
2896 | chrome.exe | 172.67.160.221:443 | x4.static-chomikuj.pl | — | US | unknown |
2896 | chrome.exe | 142.250.184.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
2896 | chrome.exe | 216.58.212.132:443 | www.google.com | Google Inc. | US | whitelisted |
2896 | chrome.exe | 142.250.185.174:443 | apis.google.com | Google Inc. | US | whitelisted |
2896 | chrome.exe | 64.233.167.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2896 | chrome.exe | 142.250.186.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2896 | chrome.exe | 142.250.185.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
2896 | chrome.exe | 217.74.71.132:443 | js.iplsc.com | INTERIA.PL Sp z.o.o. | PL | suspicious |
2896 | chrome.exe | 142.250.184.238:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
chomikuj.pl |
| whitelisted |
accounts.google.com |
| shared |
x4.static-chomikuj.pl |
| malicious |
www.google.com |
| malicious |
apis.google.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
www.gstatic.com |
| whitelisted |
x2.static-chomikuj.pl |
| malicious |
x1.static-chomikuj.pl |
| malicious |
x3.static-chomikuj.pl |
| malicious |
Threats
16 ETPRO signatures available at the full report