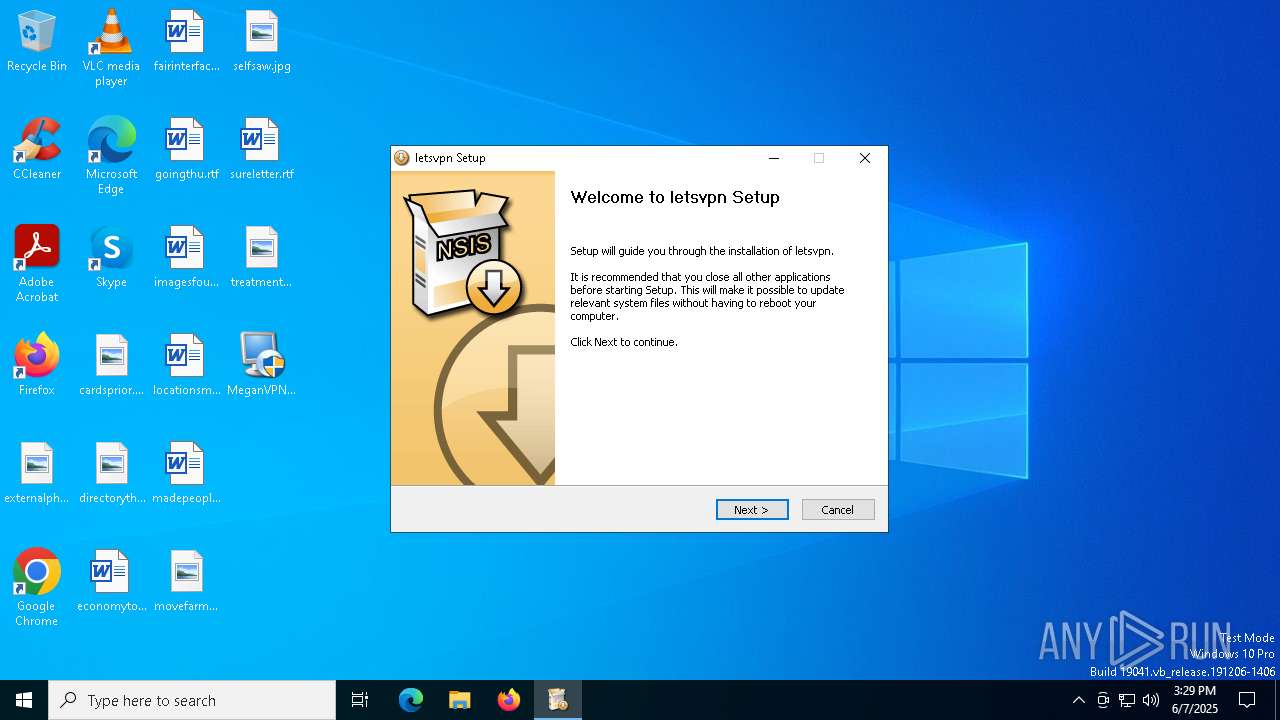
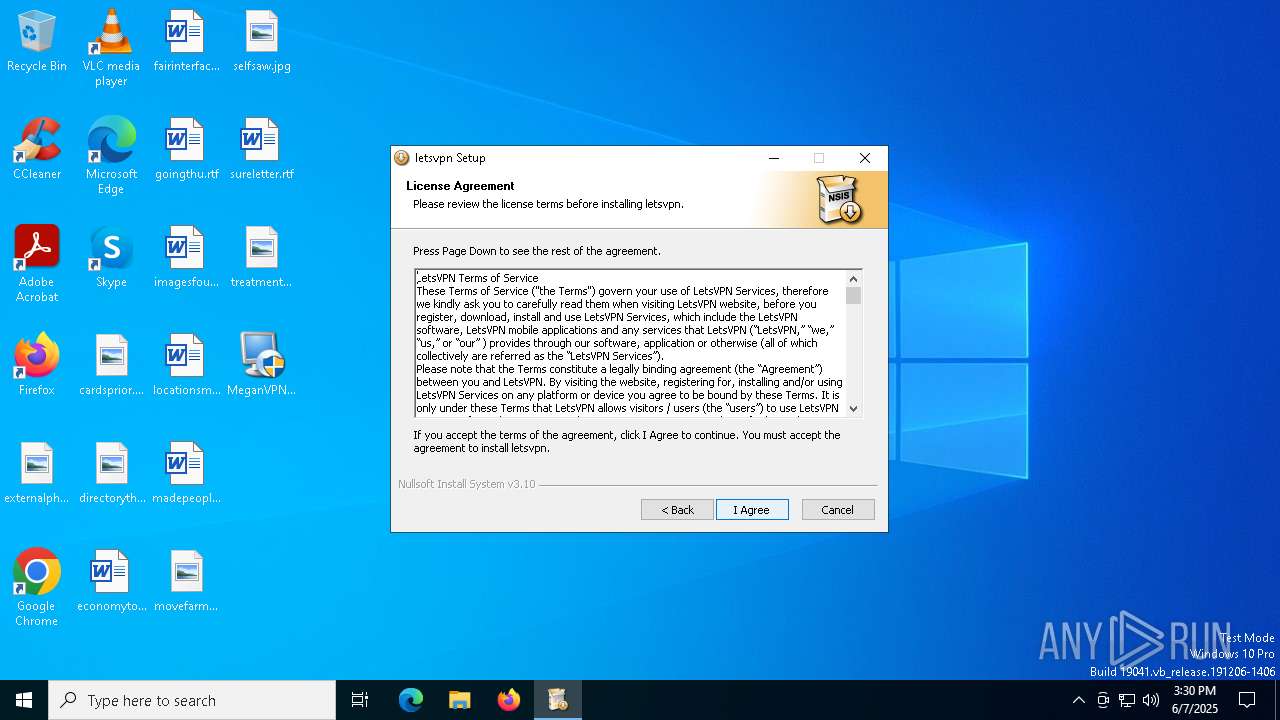
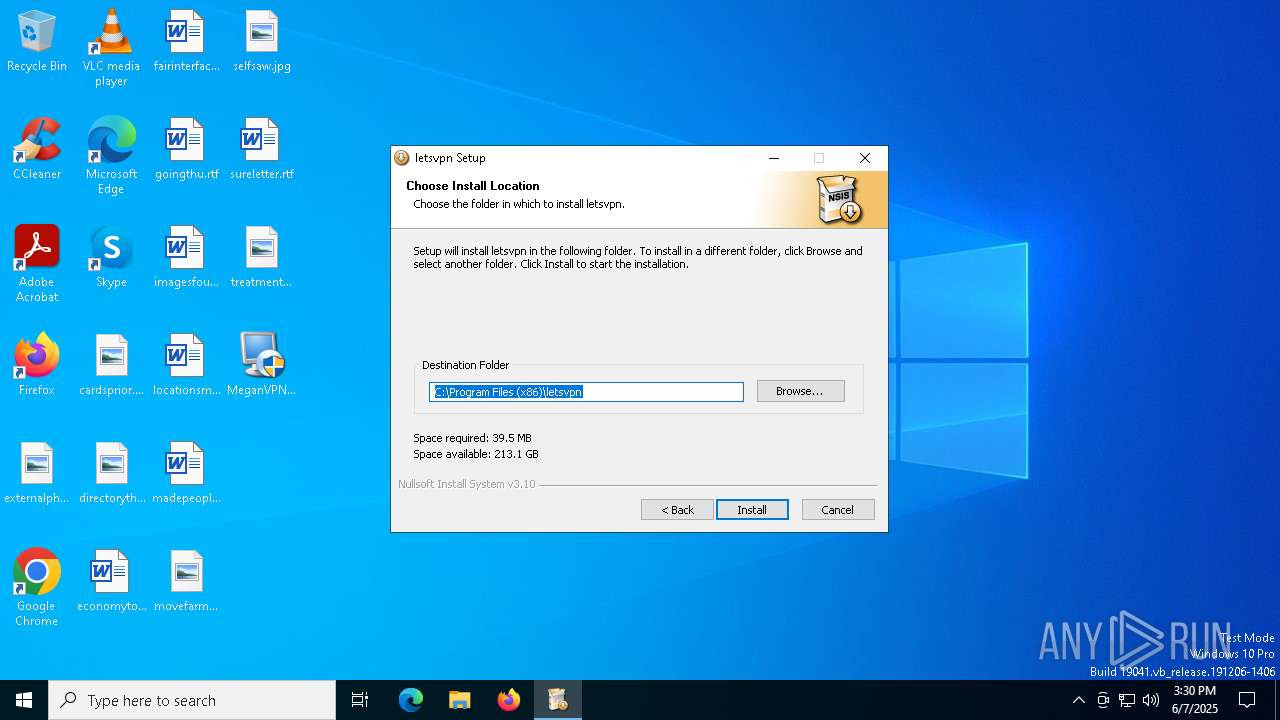
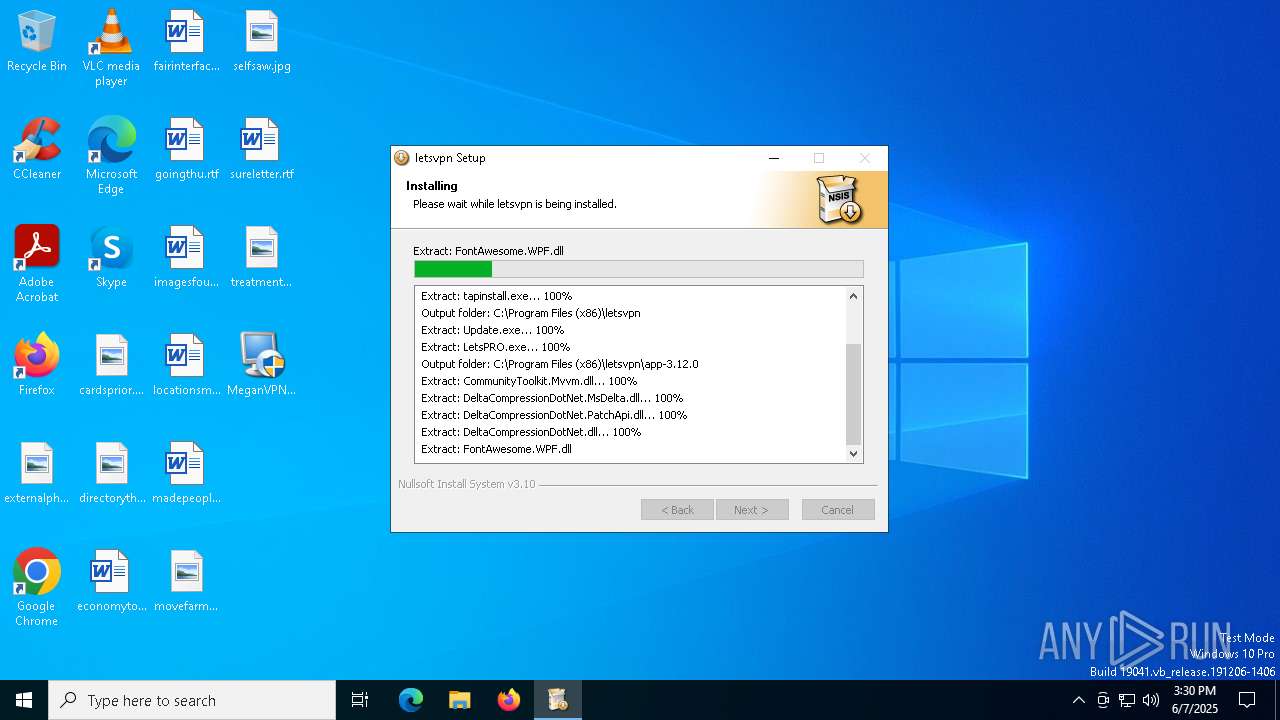
| File name: | MeganVPN-letes1.5.5.37.exe |
| Full analysis: | https://app.any.run/tasks/f49366a8-5f8a-41fd-bb2b-c4a888f74e88 |
| Verdict: | Malicious activity |
| Analysis date: | June 07, 2025, 15:29:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | B163E8B231030163E6844E0AFDDF38FB |
| SHA1: | A6B7CDE3FBA37B52148815AC3292CB3375D9DAF9 |
| SHA256: | D6D7565CCE033557ADA43E865AD9A186C1C770854304510FA8FACC1ED2527BA2 |
| SSDEEP: | 196608:jv4RfVmKbOkOisgbxI1VfVOuWIzU1K2zZaww2W0:j8ftbOkOPgb6dOXSUFZDr |
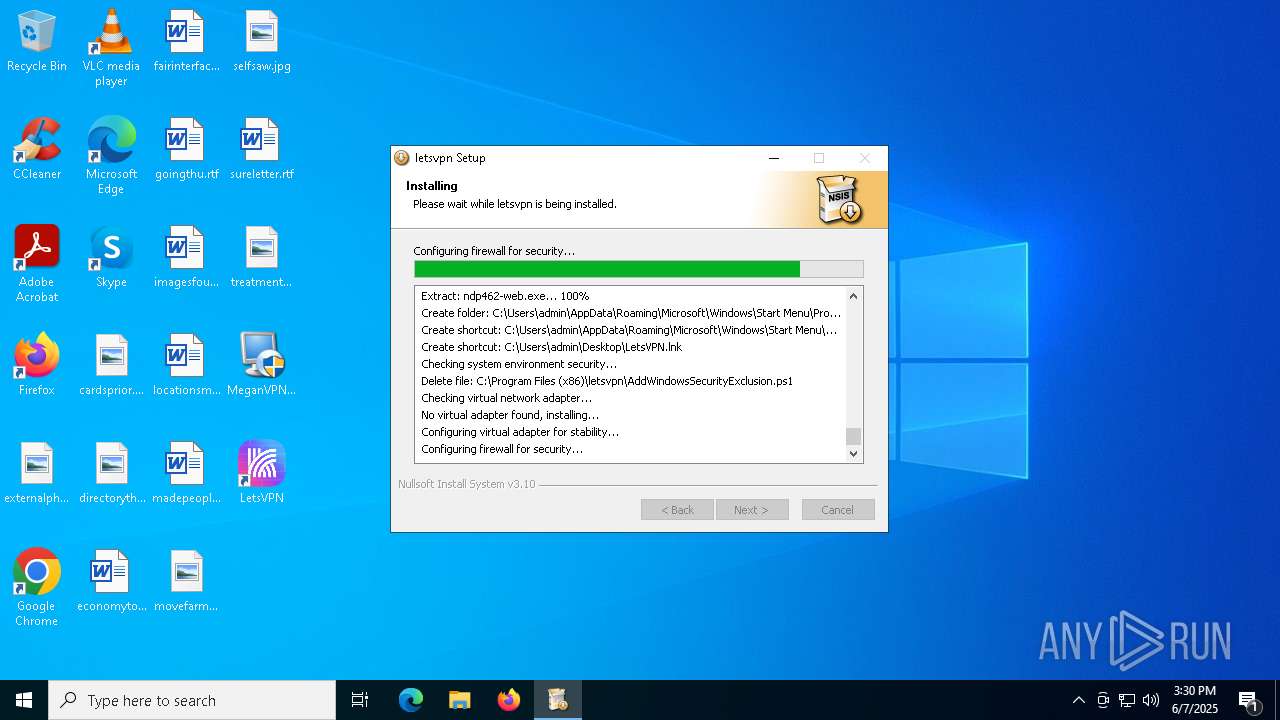
MALICIOUS
Executing a file with an untrusted certificate
- MeganVPN-letes1.5.5.37.exe (PID: 4700)
- MeganVPN-letes1.5.5.37.exe (PID: 5956)
Antivirus name has been found in the command line (generic signature)
- powershell.exe (PID: 4448)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 4528)
- cmd.exe (PID: 208)
Changes the autorun value in the registry
- iusb3mon.exe (PID: 5968)
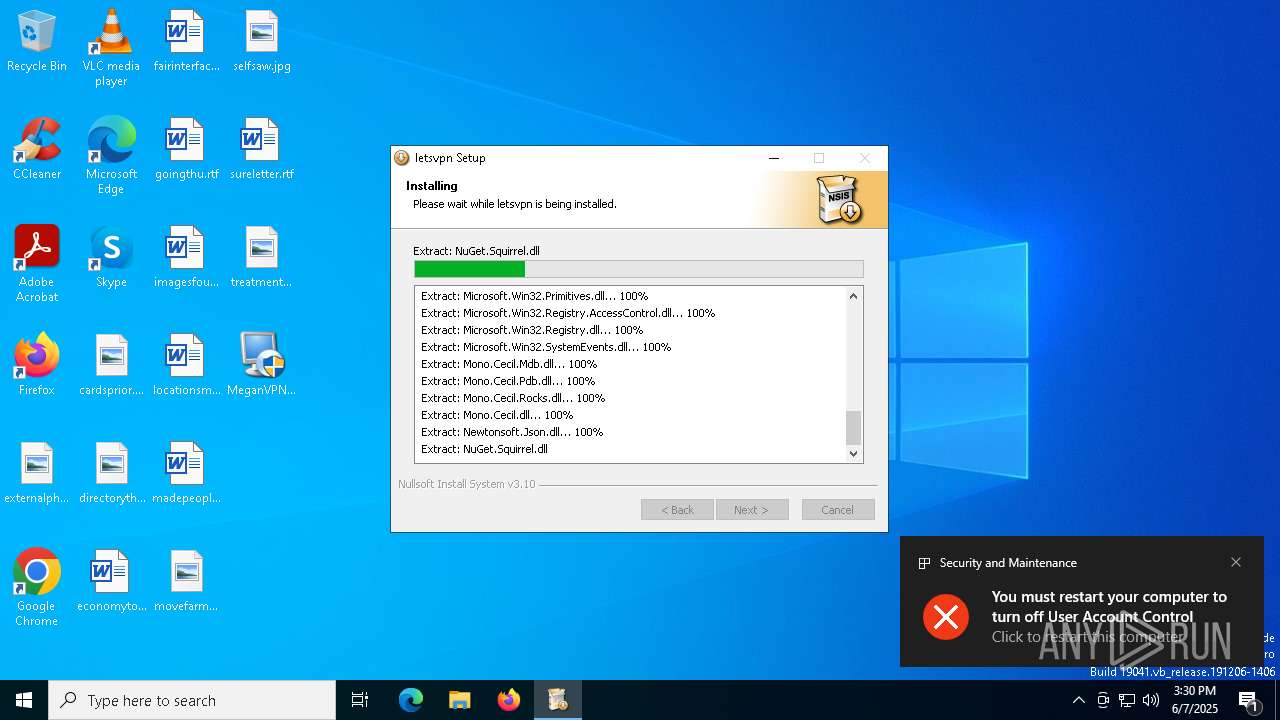
UAC/LUA settings modification
- iusb3mon.exe (PID: 5968)
Bypass execution policy to execute commands
- powershell.exe (PID: 7840)
Changes powershell execution policy (Bypass)
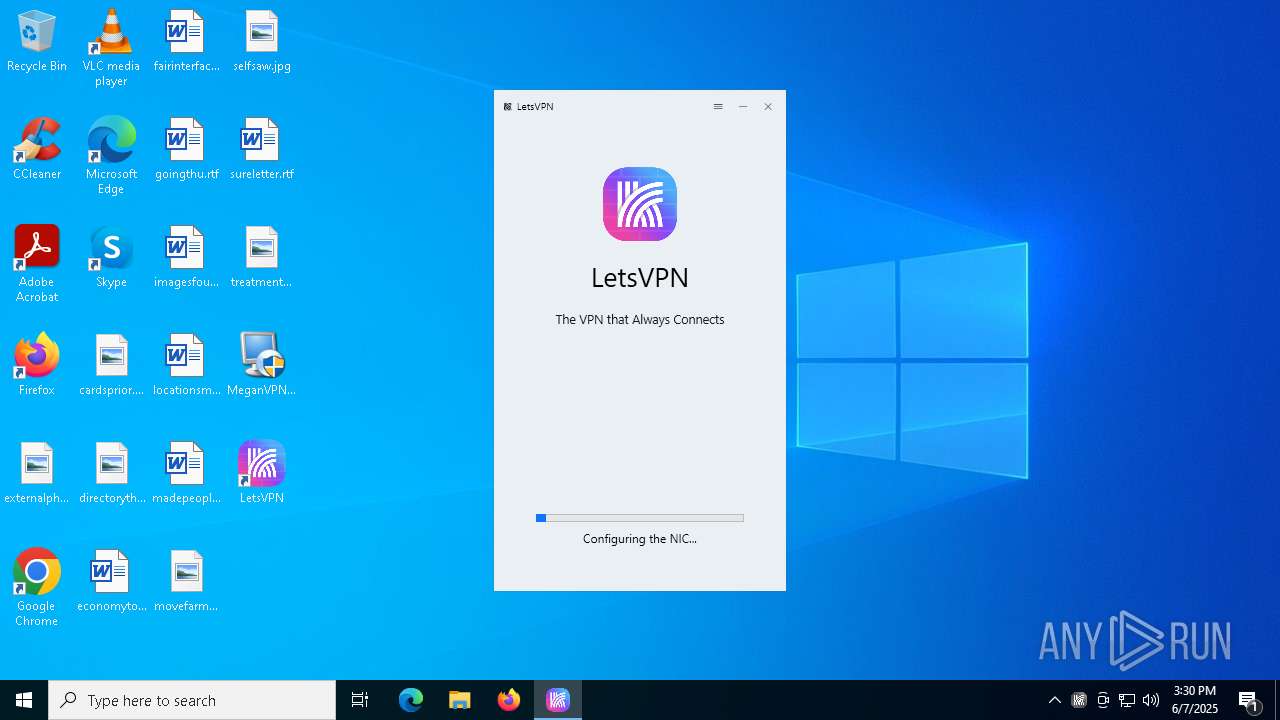
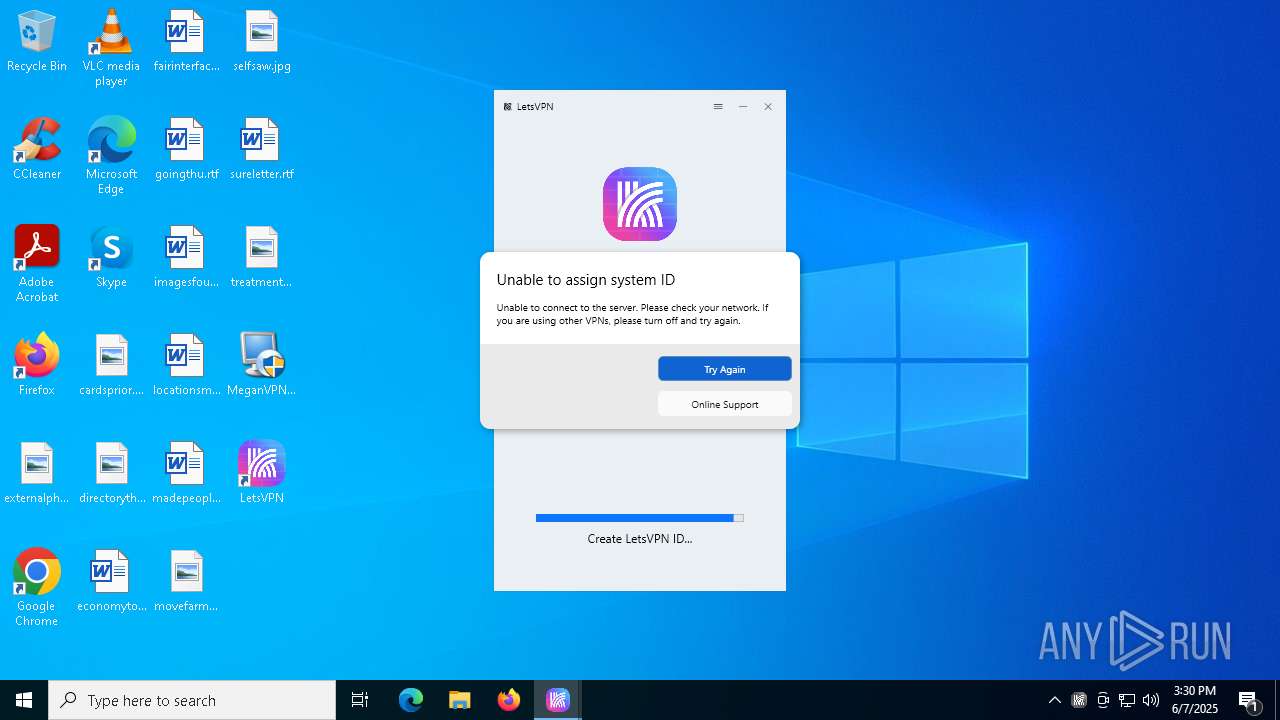
- LetsVPN.exe (PID: 6668)
SUSPICIOUS
Executable content was dropped or overwritten
- MeganVPN-letes1.5.5.37.exe (PID: 5956)
- irsetup.exe (PID: 6040)
- 7z.exe (PID: 32)
- LetsVPN.exe (PID: 6668)
- tapinstall.exe (PID: 772)
- drvinst.exe (PID: 1672)
- drvinst.exe (PID: 6072)
Reads security settings of Internet Explorer
- MeganVPN-letes1.5.5.37.exe (PID: 5956)
- irsetup.exe (PID: 6040)
- ShellExperienceHost.exe (PID: 8076)
- tapinstall.exe (PID: 772)
Reads the date of Windows installation
- MeganVPN-letes1.5.5.37.exe (PID: 5956)
- irsetup.exe (PID: 6040)
Reads the Windows owner or organization settings
- irsetup.exe (PID: 6040)
Get information on the list of running processes
- irsetup.exe (PID: 6040)
Starts POWERSHELL.EXE for commands execution
- irsetup.exe (PID: 6040)
- iusb3mon.exe (PID: 5968)
- LetsVPN.exe (PID: 6668)
The process drops C-runtime libraries
- irsetup.exe (PID: 6040)
Process drops legitimate windows executable
- irsetup.exe (PID: 6040)
- LetsVPN.exe (PID: 6668)
Drops 7-zip archiver for unpacking
- irsetup.exe (PID: 6040)
The process bypasses the loading of PowerShell profile settings
- iusb3mon.exe (PID: 5968)
The process creates files with name similar to system file names
- LetsVPN.exe (PID: 6668)
Malware-specific behavior (creating "System.dll" in Temp)
- LetsVPN.exe (PID: 6668)
Manipulates environment variables
- powershell.exe (PID: 6252)
Removes files via Powershell
- powershell.exe (PID: 6252)
PowerShell delay command usage (probably sleep evasion)
- powershell.exe (PID: 6252)
Base64-obfuscated command line is found
- iusb3mon.exe (PID: 5968)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 6252)
Starts CMD.EXE for commands execution
- iusb3mon.exe (PID: 5968)
- LetsVPN.exe (PID: 6668)
- LetsPRO.exe (PID: 6156)
Probably obfuscated PowerShell command line is found
- iusb3mon.exe (PID: 5968)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 6252)
There is functionality for VM detection Parallels (YARA)
- iusb3mon.exe (PID: 5968)
There is functionality for VM detection VirtualBox (YARA)
- iusb3mon.exe (PID: 5968)
There is functionality for VM detection VMWare (YARA)
- iusb3mon.exe (PID: 5968)
There is functionality for taking screenshot (YARA)
- iusb3mon.exe (PID: 5968)
- LetsVPN.exe (PID: 6668)
Drops a system driver (possible attempt to evade defenses)
- LetsVPN.exe (PID: 6668)
- tapinstall.exe (PID: 772)
- drvinst.exe (PID: 1672)
- drvinst.exe (PID: 6072)
Connects to unusual port
- iusb3mon.exe (PID: 5968)
The process executes Powershell scripts
- LetsVPN.exe (PID: 6668)
Creates files in the driver directory
- drvinst.exe (PID: 1672)
- drvinst.exe (PID: 6072)
Creates or modifies Windows services
- drvinst.exe (PID: 6072)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 6564)
- cmd.exe (PID: 3868)
- cmd.exe (PID: 2432)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 7520)
Process uses IPCONFIG to discover network configuration
- cmd.exe (PID: 5980)
Suspicious use of NETSH.EXE
- LetsPRO.exe (PID: 6156)
Executes as Windows Service
- WmiApSrv.exe (PID: 8068)
Process uses ARP to discover network configuration
- cmd.exe (PID: 7396)
Uses ROUTE.EXE to obtain the routing table information
- cmd.exe (PID: 6464)
INFO
Checks supported languages
- MeganVPN-letes1.5.5.37.exe (PID: 5956)
- irsetup.exe (PID: 6040)
- 7z.exe (PID: 32)
- LetsVPN.exe (PID: 6668)
- iusb3mon.exe (PID: 5968)
- ShellExperienceHost.exe (PID: 8076)
- iusb3mon.exe (PID: 8144)
- tapinstall.exe (PID: 2596)
- tapinstall.exe (PID: 772)
- drvinst.exe (PID: 1672)
- drvinst.exe (PID: 6072)
- tapinstall.exe (PID: 2124)
The sample compiled with english language support
- MeganVPN-letes1.5.5.37.exe (PID: 5956)
- irsetup.exe (PID: 6040)
- LetsVPN.exe (PID: 6668)
- drvinst.exe (PID: 1672)
- drvinst.exe (PID: 6072)
- tapinstall.exe (PID: 772)
Create files in a temporary directory
- MeganVPN-letes1.5.5.37.exe (PID: 5956)
- irsetup.exe (PID: 6040)
- LetsVPN.exe (PID: 6668)
- SecEdit.exe (PID: 6724)
- iusb3mon.exe (PID: 5968)
- tapinstall.exe (PID: 772)
Process checks computer location settings
- MeganVPN-letes1.5.5.37.exe (PID: 5956)
- irsetup.exe (PID: 6040)
Reads the computer name
- MeganVPN-letes1.5.5.37.exe (PID: 5956)
- irsetup.exe (PID: 6040)
- 7z.exe (PID: 32)
- LetsVPN.exe (PID: 6668)
- ShellExperienceHost.exe (PID: 8076)
- iusb3mon.exe (PID: 5968)
- tapinstall.exe (PID: 772)
- drvinst.exe (PID: 6072)
- drvinst.exe (PID: 1672)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 3304)
- powershell.exe (PID: 7516)
- powershell.exe (PID: 3332)
- powershell.exe (PID: 7456)
- powershell.exe (PID: 7832)
- powershell.exe (PID: 4448)
- powershell.exe (PID: 7840)
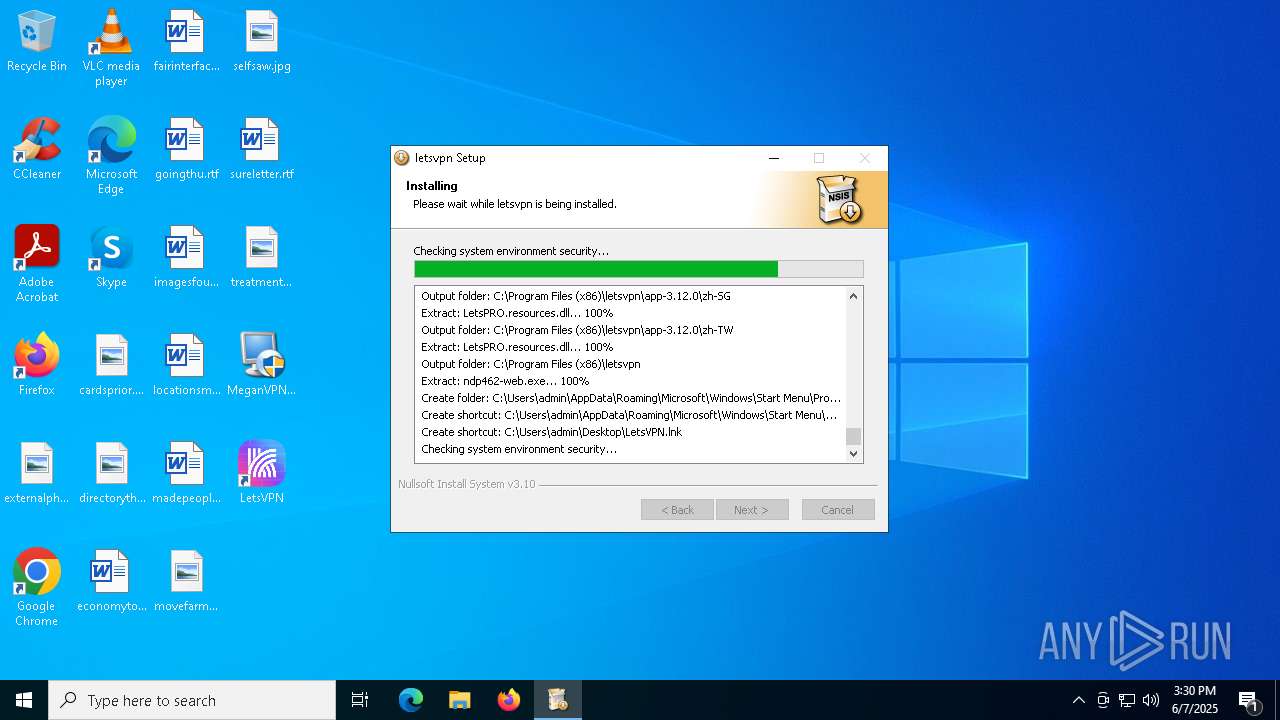
Creates files or folders in the user directory
- irsetup.exe (PID: 6040)
- 7z.exe (PID: 32)
- LetsVPN.exe (PID: 6668)
The sample compiled with chinese language support
- irsetup.exe (PID: 6040)
Creates files in the program directory
- irsetup.exe (PID: 6040)
- LetsVPN.exe (PID: 6668)
UPX packer has been detected
- iusb3mon.exe (PID: 5968)
Launching a file from a Registry key
- iusb3mon.exe (PID: 5968)
Process checks whether UAC notifications are on
- iusb3mon.exe (PID: 5968)
Manual execution by a user
- iusb3mon.exe (PID: 8144)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 7840)
Reads the software policy settings
- tapinstall.exe (PID: 772)
- drvinst.exe (PID: 1672)
Reads the machine GUID from the registry
- tapinstall.exe (PID: 772)
- drvinst.exe (PID: 1672)
Prints a route via ROUTE.EXE
- ROUTE.EXE (PID: 8092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2012:06:14 16:16:12+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 10 |
| CodeSize: | 25088 |
| InitializedDataSize: | 49152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2d1c |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
214
Monitored processes
76
Malicious processes
7
Suspicious processes
3
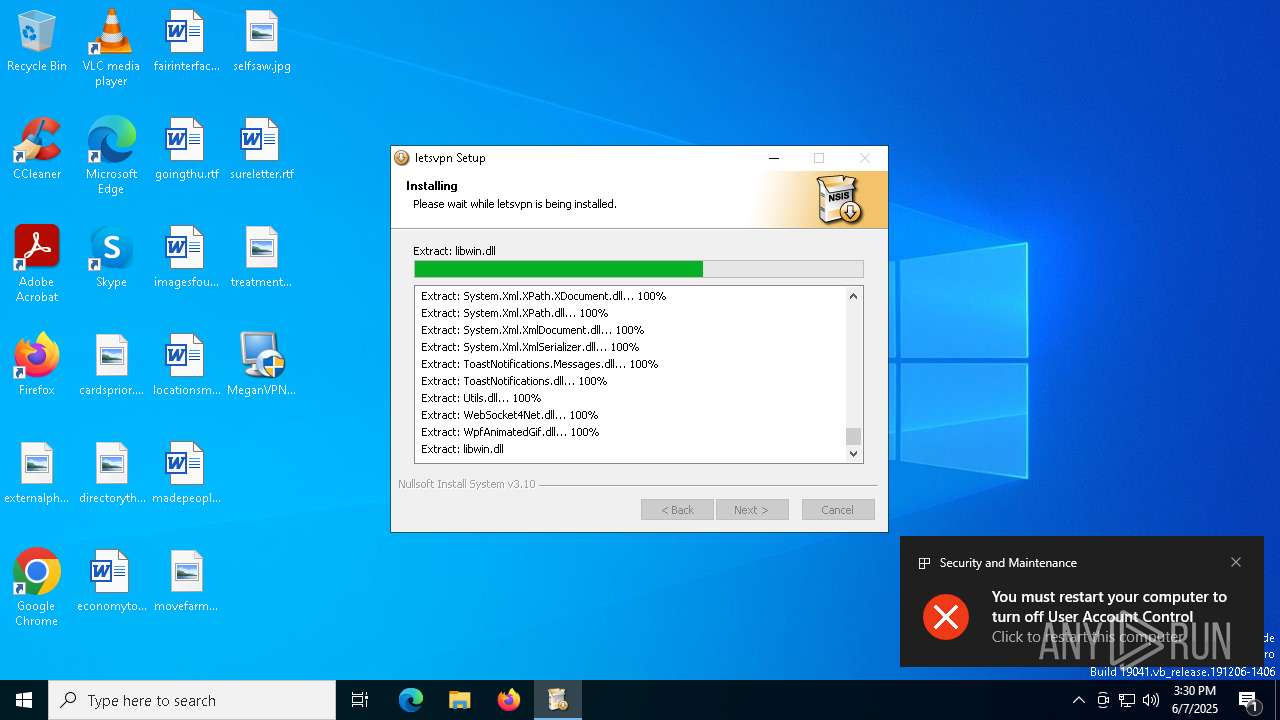
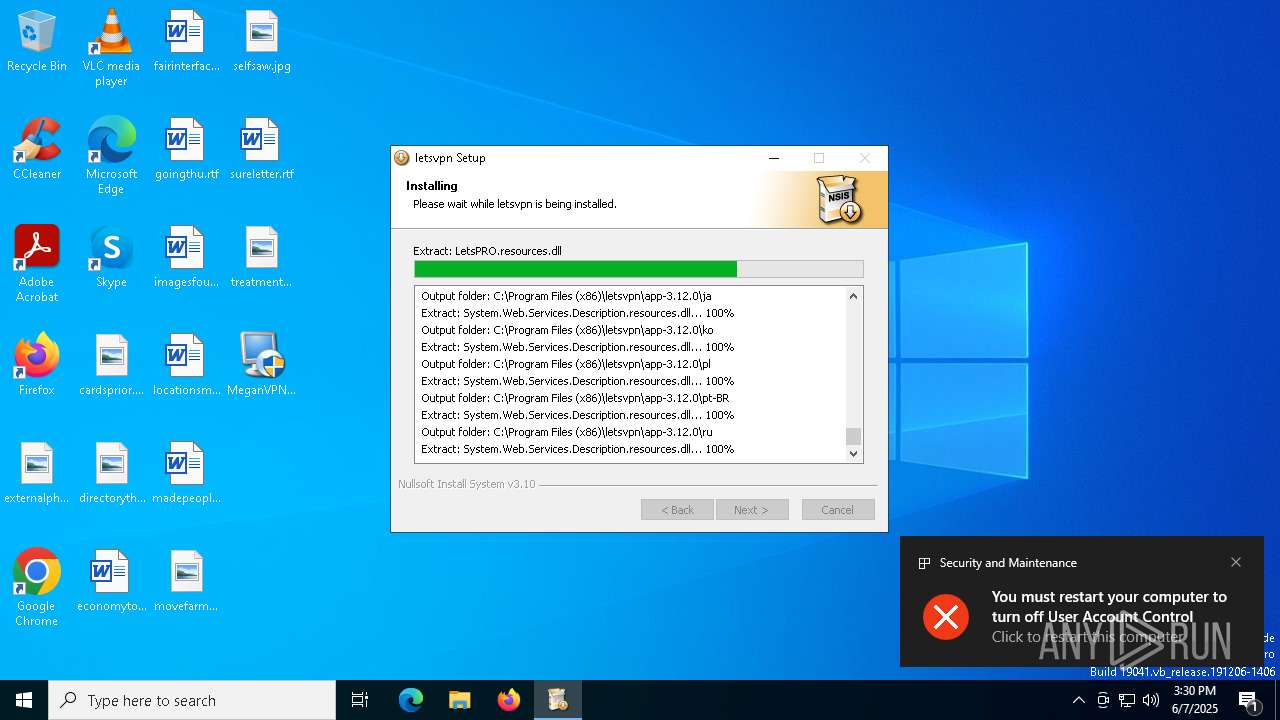
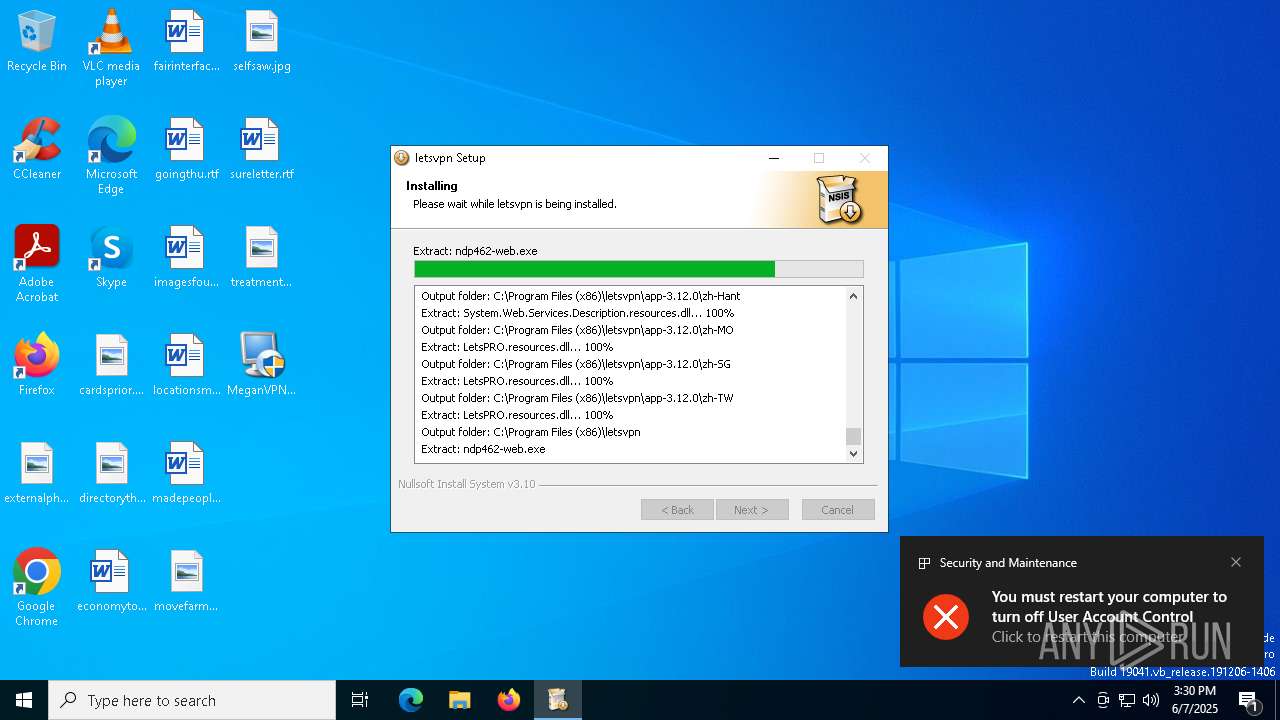
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\Users\admin\AppData\Roaming\..\Local\7z.exe" x -pmiyao123 -o"C:\Users\admin\AppData\Roaming\..\Local\AppData" "C:\Users\admin\AppData\Roaming\..\Local\7z.7z" "EduWebContainer.dll" -y | C:\Users\admin\AppData\Local\7z.exe | irsetup.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Console Exit code: 0 Version: 24.09 Modules
| |||||||||||||||
| 132 | netsh advfirewall firewall Delete rule name=lets | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 208 | cmd.exe /c schtasks.exe /create /tn "Intel USB 3.0 eXtensible Host Controller" /xml "C:\Users\admin\AppData\Local\Temp\1209187_t.xml" | C:\Windows\SysWOW64\cmd.exe | — | iusb3mon.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 404 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7z.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 444 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 704 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 716 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | tapinstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 772 | "C:\Program Files (x86)\letsvpn\driver\tapinstall.exe" install "C:\Program Files (x86)\letsvpn\driver\OemVista.inf" tap0901 | C:\Program Files (x86)\letsvpn\driver\tapinstall.exe | LetsVPN.exe | ||||||||||||
User: admin Company: Windows (R) Win 7 DDK provider Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 6.1.7600.16385 built by: WinDDK Modules
| |||||||||||||||
| 856 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
83 767
Read events
83 598
Write events
149
Delete events
20
Modification events
| (PID) Process: | (6724) SecEdit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows NT\CurrentVersion\SecEdit |
| Operation: | delete value | Name: | LastWinlogonConfig |
Value: | |||
| (PID) Process: | (5968) iusb3mon.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftUSBMonitor |
Value: C:\Users\admin\AppData\Local\AppData\iusb3mon.exe | |||
| (PID) Process: | (5968) iusb3mon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftUSBMonitor |
Value: C:\Users\admin\AppData\Local\AppData\iusb3mon.exe | |||
| (PID) Process: | (6668) LetsVPN.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\lets |
| Operation: | write | Name: | InstallTimeStamp |
Value: 20250607153011.226 | |||
| (PID) Process: | (6668) LetsVPN.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\lets |
| Operation: | write | Name: | InstallNewVersion |
Value: 3.12.0 | |||
| (PID) Process: | (5968) iusb3mon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | ConsentPromptBehaviorAdmin |
Value: 0 | |||
| (PID) Process: | (5968) iusb3mon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | EnableLUA |
Value: 0 | |||
| (PID) Process: | (5968) iusb3mon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | PromptOnSecureDesktop |
Value: 0 | |||
| (PID) Process: | (8076) ShellExperienceHost.exe | Key: | \REGISTRY\A\{3732e94a-cb34-7c04-b760-b8cf8de35c03}\LocalState |
| Operation: | write | Name: | PeekBadges |
Value: 5B005D0000003342510FC1D7DB01 | |||
| (PID) Process: | (5968) iusb3mon.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | DisableLockWorkstation |
Value: 0 | |||
Executable files
236
Suspicious files
44
Text files
39
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5956 | MeganVPN-letes1.5.5.37.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\lua5.1.dll | executable | |
MD5:958103E55C74427E5C66D7E18F3BF237 | SHA256:3EA4A4C3C6DEA44D8917B342E93D653F59D93E1F552ACE16E97E43BB04E951D8 | |||
| 5956 | MeganVPN-letes1.5.5.37.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | executable | |
MD5:2A7D5F8D3FB4AB753B226FD88D31453B | SHA256:879109AE311E9B88F930CE1C659F29EC0E338687004318661E604D0D3727E3CF | |||
| 6040 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\IRIMG1.JPG | image | |
MD5:3220A6AEFB4FC719CC8849F060859169 | SHA256:988CF422CBF400D41C48FBE491B425A827A1B70691F483679C1DF02FB9352765 | |||
| 2432 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sh3n5tly.vz0.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3304 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_lxpg5aqq.hhd.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3304 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_jxzpwy3n.yii.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7832 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_4n4qrlkc.scp.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 2432 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_wdkh34wx.pu3.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7456 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_be2lgysh.guv.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_nryx3ycp.xk1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
133
DNS requests
29
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.160.66:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
— | — | POST | 200 | 40.126.32.72:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
— | — | POST | 200 | 40.126.32.72:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
— | — | POST | 200 | 40.126.31.0:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
— | — | POST | 200 | 40.126.31.0:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | whitelisted |
— | — | GET | 304 | 4.175.87.197:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
— | — | GET | 200 | 4.175.87.197:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | compressed | 23.9 Kb | whitelisted |
5352 | SIHClient.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5352 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5408 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5604 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5352 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
huazai168.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
— | — | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
— | — | Misc activity | ET INFO Go-http-client User-Agent Observed Outbound |
— | — | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
— | — | Misc activity | ET INFO Go-http-client User-Agent Observed Outbound |
— | — | Misc activity | ET INFO Go-http-client User-Agent Observed Outbound |
6156 | LetsPRO.exe | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |
— | — | Misc activity | ET USER_AGENTS Go HTTP Client User-Agent |
— | — | Misc activity | ET INFO Go-http-client User-Agent Observed Outbound |