| File name: | PWLSWS.ps1 |
| Full analysis: | https://app.any.run/tasks/9907418c-3c15-4e0f-880c-6de5c309d6ea |
| Verdict: | Malicious activity |
| Analysis date: | March 03, 2025, 15:24:31 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | F930A30C59F0A35D82BB47233B9C489E |
| SHA1: | BE565F031C28F485921F31B5A23D8B19BD35C909 |
| SHA256: | D6C6BF9502BF37F11180B51D3D8FE3029123DE00E108F327D6EC7DE5887F5B25 |
| SSDEEP: | 3:qGQTH3x8JCRVfMRC+FEvtFwJAFHBuxHSSleWVgM9NYfxHSSlFIWQuSfxHYsxHMr7:q3Lh8JSRMRC+FE0ldhh9cdhfIWQusdYn |
MALICIOUS
Bypass execution policy to execute commands
- powershell.exe (PID: 2908)
Executing a file with an untrusted certificate
- AUpdate.exe (PID: 8064)
- AUpdate.exe (PID: 8076)
- AUpdate.exe (PID: 8136)
- AUpdate.exe (PID: 8088)
SUSPICIOUS
Gets file extension (POWERSHELL)
- powershell.exe (PID: 2908)
Executable content was dropped or overwritten
- powershell.exe (PID: 2908)
- AUpdate.exe (PID: 8136)
Connects to unusual port
- MSBuild.exe (PID: 5720)
Starts CMD.EXE for commands execution
- AUpdate.exe (PID: 8136)
INFO
The executable file from the user directory is run by the Powershell process
- AUpdate.exe (PID: 8076)
- AUpdate.exe (PID: 8064)
- AUpdate.exe (PID: 8136)
- AUpdate.exe (PID: 8088)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 2908)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 2908)
Creates files or folders in the user directory
- AUpdate.exe (PID: 8136)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
146
Monitored processes
11
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2908 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\AppData\Local\Temp\PWLSWS.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5720 | C:\WINDOWS\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | C:\Windows\Microsoft.NET\Framework\v4.0.30319\MSBuild.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: MSBuild.exe Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 5740 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7356 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7388 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8064 | "C:\Users\admin\AppData\Local\Temp\MaxiAir\AUpdate.exe" | C:\Users\admin\AppData\Local\Temp\MaxiAir\AUpdate.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 8076 | "C:\Users\admin\AppData\Local\Temp\MaxiAir\AUpdate.exe" "C:\Users\admin\AppData\Local\Temp\MaxiAir\AUpdate.exe" | C:\Users\admin\AppData\Local\Temp\MaxiAir\AUpdate.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 8088 | "C:\Users\admin\AppData\Local\Temp\MaxiAir\AUpdate.exe" | C:\Users\admin\AppData\Local\Temp\MaxiAir\AUpdate.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 8136 | "C:\Users\admin\AppData\Local\Temp\MaxiAir\AUpdate.exe" | C:\Users\admin\AppData\Local\Temp\MaxiAir\AUpdate.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 8176 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | AUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 323
Read events
8 323
Write events
0
Delete events
0
Modification events
Executable files
7
Suspicious files
10
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8176 | cmd.exe | C:\Users\admin\AppData\Local\Temp\txweyiwxdgkj | — | |
MD5:— | SHA256:— | |||
| 2908 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5SO4ZEHO8AO8JMFUHW4X.temp | binary | |
MD5:F945A076DCD2810096DD2A2B5943256F | SHA256:9AC523F2734000C8C16BB9B72032151DC79357A80F64327C0645E2706911A7CD | |||
| 8136 | AUpdate.exe | C:\Users\admin\AppData\Local\DemostreamPI\DirectGUI.dll | executable | |
MD5:6D8293DB1634077D6F76CD93DA8F92BF | SHA256:F4C8385BB0168DEBF28E146AD5E1D78585BDFBCBFC258D65EC3F2BCBD843F52D | |||
| 2908 | powershell.exe | C:\Users\admin\AppData\Local\Temp\MaxiAir\DirectGUI.dll | executable | |
MD5:6D8293DB1634077D6F76CD93DA8F92BF | SHA256:F4C8385BB0168DEBF28E146AD5E1D78585BDFBCBFC258D65EC3F2BCBD843F52D | |||
| 2908 | powershell.exe | C:\Users\admin\AppData\Local\Temp\MaxiAir\dx0.dll | executable | |
MD5:693DFBB9B324E80B70660927CA1DEA69 | SHA256:7C28D90E3484B566EE00ADAB4679A3D1C51F86F01560035D86C8F7788AC05234 | |||
| 8136 | AUpdate.exe | C:\Users\admin\AppData\Local\DemostreamPI\pasquinade.dat | binary | |
MD5:4FAB9312EC36A231F105EAA18B8F6A4F | SHA256:CF12599CDCA9BEF8DBF8C6E7A1A954B5B4DB39EDF8D09C2EF1319F51DE739BFE | |||
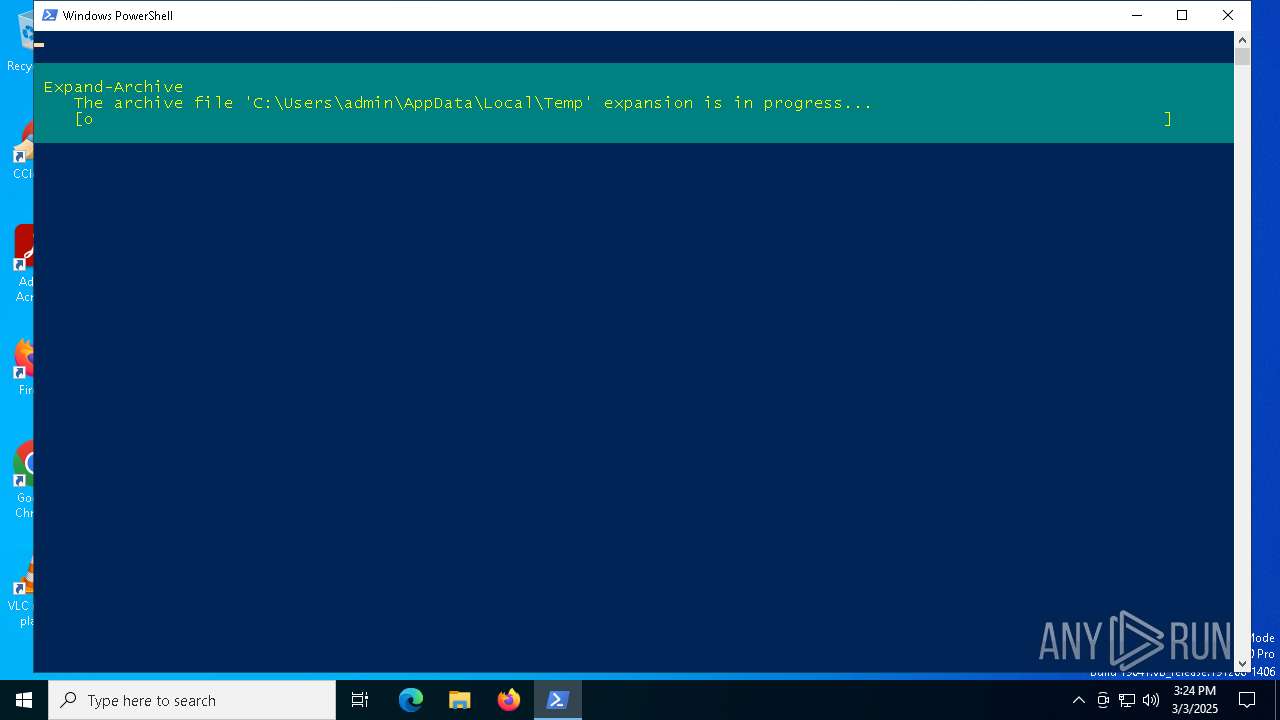
| 2908 | powershell.exe | C:\Users\admin\AppData\Local\Temp\Tower.zip | compressed | |
MD5:8FF08339991868D16683A8EE9D5D7992 | SHA256:0FB6B5BEDFBCC41C57E31C6A02456CD8766792C6F3A9A213DE6E3C8678130AF7 | |||
| 2908 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:CBA2C4994F85EFD8E4E24A7CC91A5513 | SHA256:D06A26AF6BE19EA8111A1B1B4886FB0F4ED7DB31908465BCA574FCB52B296BA8 | |||
| 8136 | AUpdate.exe | C:\Users\admin\AppData\Local\DemostreamPI\IconX.dll | executable | |
MD5:01E48A2665F9F5285873B44FAA1DA62D | SHA256:59D564454A343D59F4559AB289ACF864FF63BFEDBCFAE3E2F0DB7C37AD77AE0F | |||
| 2908 | powershell.exe | C:\Users\admin\AppData\Local\Temp\MaxiAir\IconX.dll | executable | |
MD5:01E48A2665F9F5285873B44FAA1DA62D | SHA256:59D564454A343D59F4559AB289ACF864FF63BFEDBCFAE3E2F0DB7C37AD77AE0F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
22
DNS requests
14
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1764 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1764 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
2908 | powershell.exe | 104.26.8.129:443 | shorturl.at | CLOUDFLARENET | US | whitelisted |
3216 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2908 | powershell.exe | 172.67.153.135:443 | ssl-reload-connect.help | CLOUDFLARENET | US | unknown |
4024 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7256 | backgroundTaskHost.exe | 20.31.169.57:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
shorturl.at |
| whitelisted |
www.shorturl.at |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ssl-reload-connect.help |
| unknown |
login.live.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Misc activity | INFO [ANY.RUN] Possible short link service (shorturl .at) |
2196 | svchost.exe | Misc activity | ET INFO URL Shortening Service Domain in DNS Lookup (shorturl .at) |
2908 | powershell.exe | Misc activity | ET INFO Observed URL Shortening Service Domain (shorturl .at) in TLS SNI |
2196 | svchost.exe | Misc activity | INFO [ANY.RUN] Possible short link service (shorturl .at) |