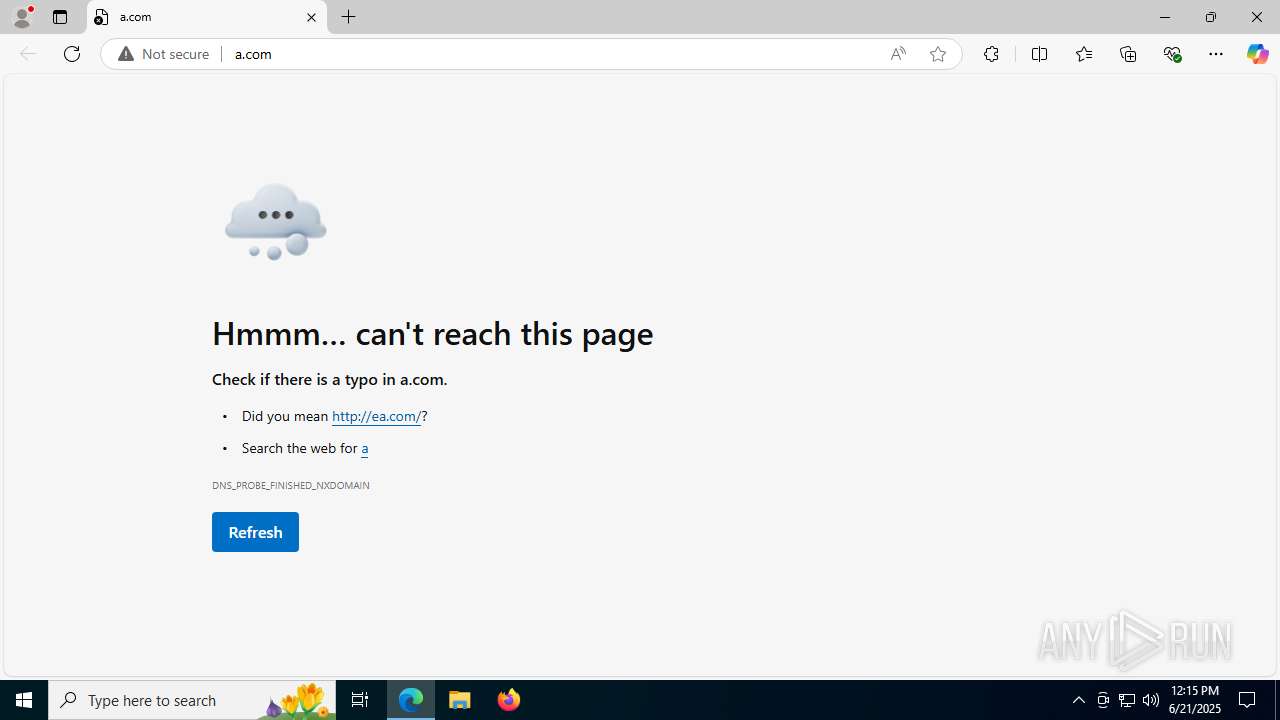
| URL: | a.com |
| Full analysis: | https://app.any.run/tasks/1715b08a-eb37-42ce-a092-755c084f01a3 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 12:15:14 |
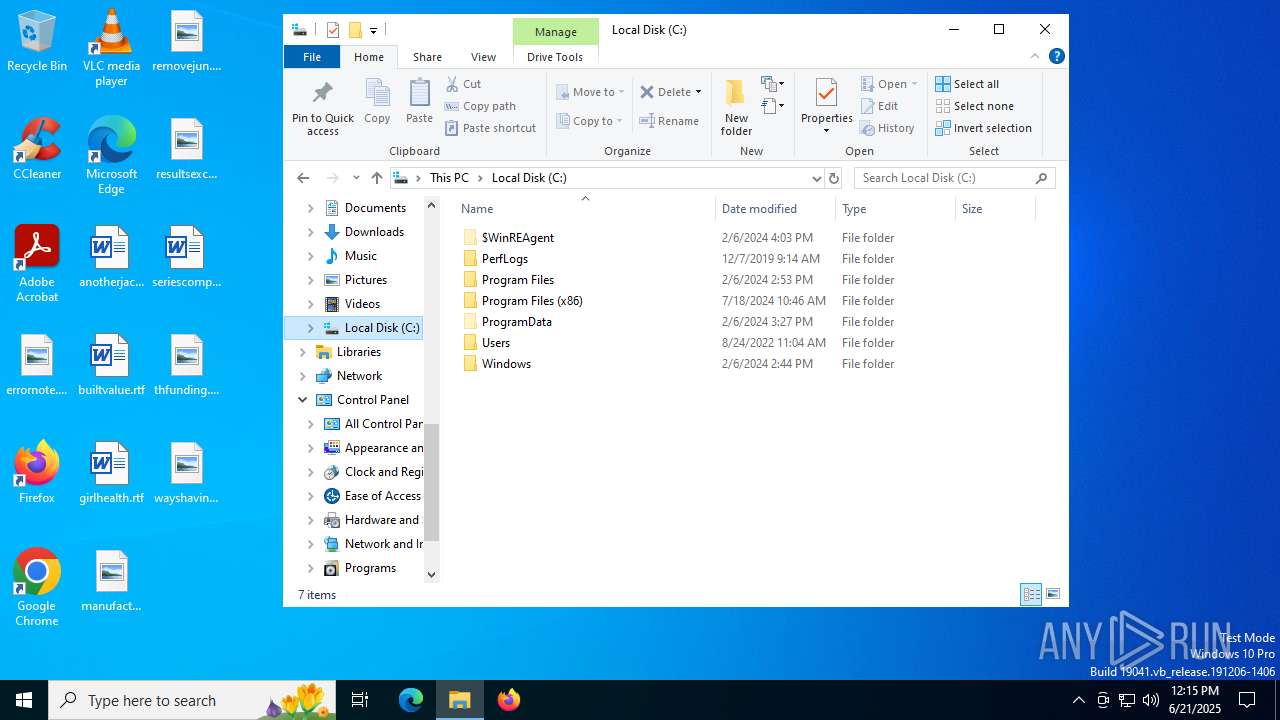
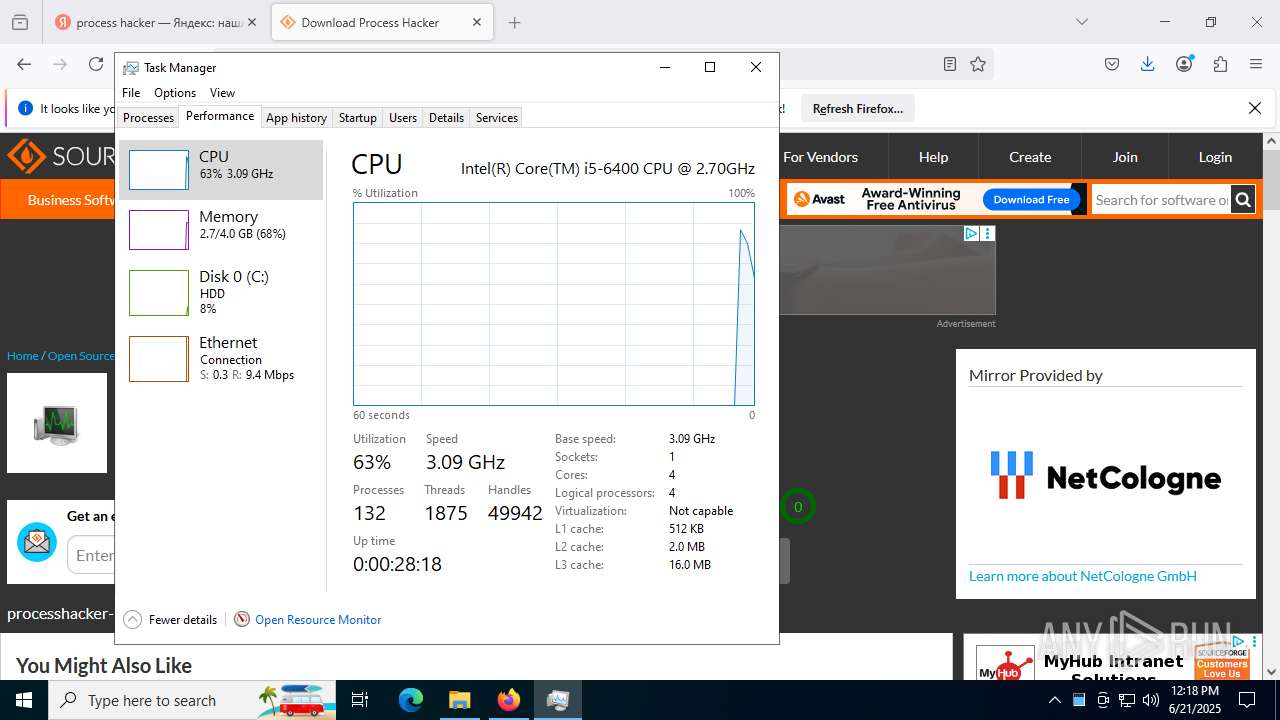
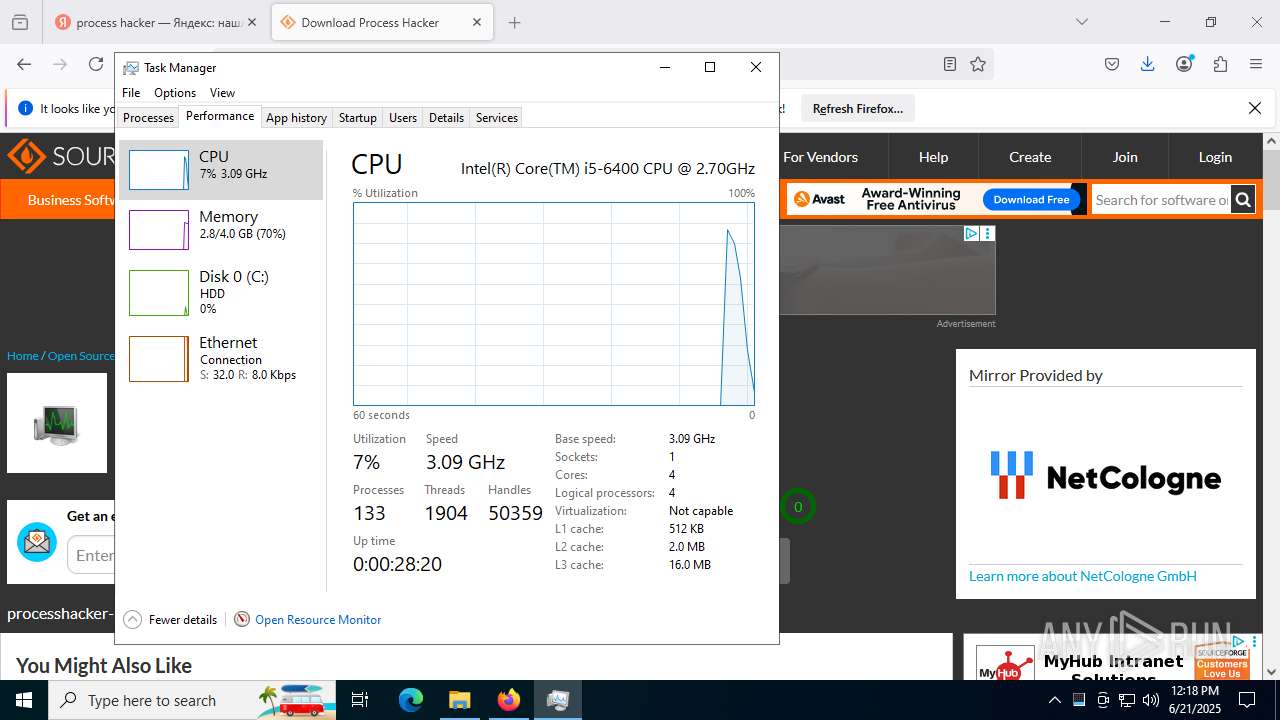
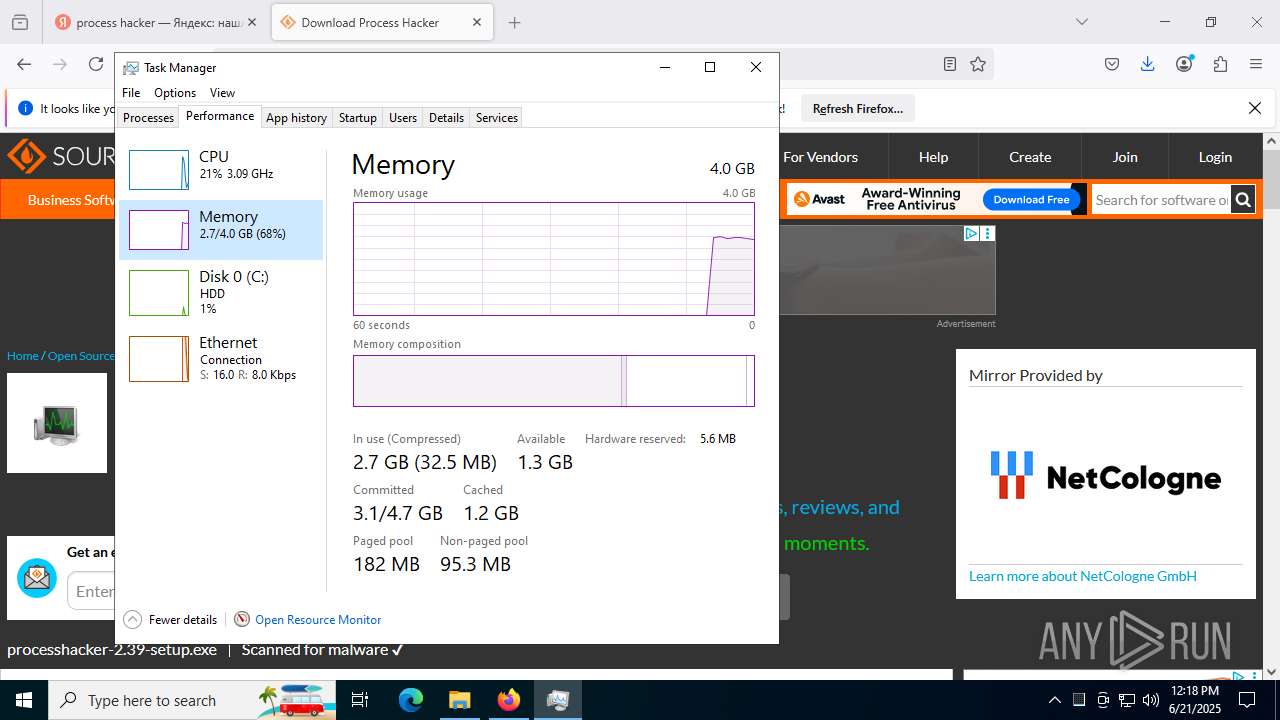
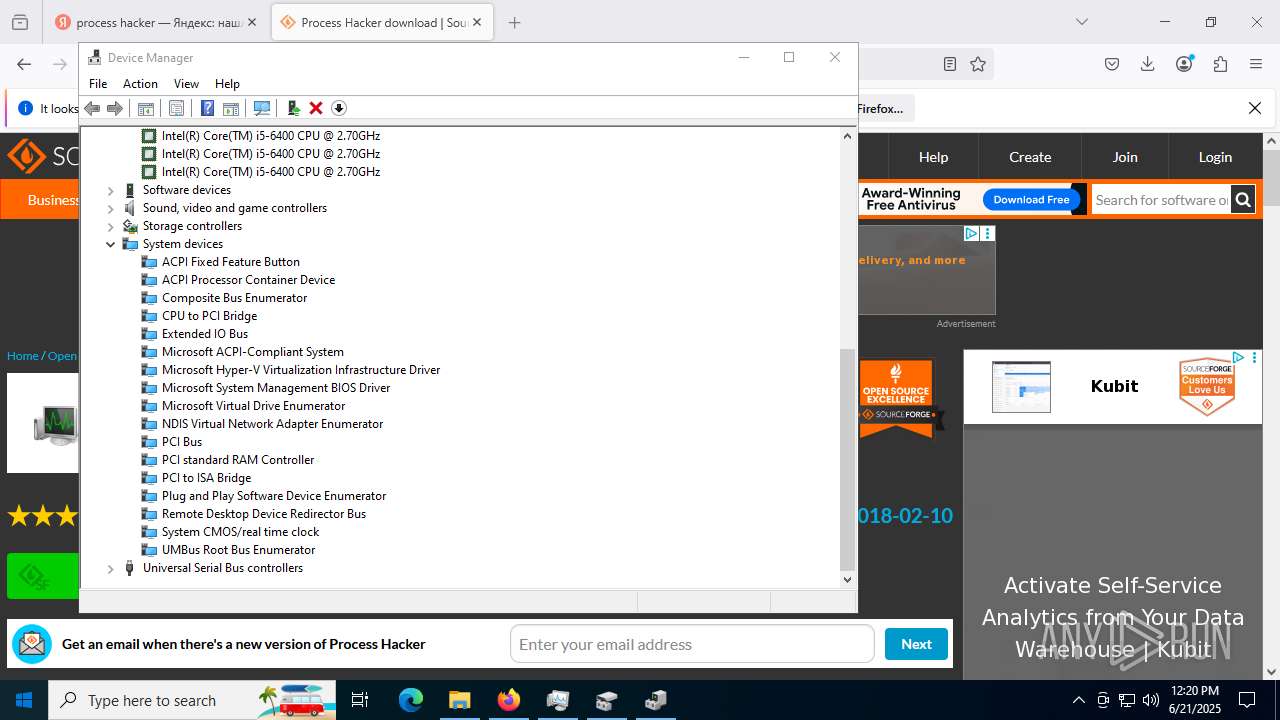
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B3655BD7AAD56513FCDACBD4254ED6B7 |
| SHA1: | 87EC0EC315EEC4E730A55B110AF0D7FA64549479 |
| SHA256: | D6C1754DBBF0BC91D7D6845C7CEC32A165389CC62CD95A24471F7FD6527F112D |
| SSDEEP: | 3:iKn:iK |
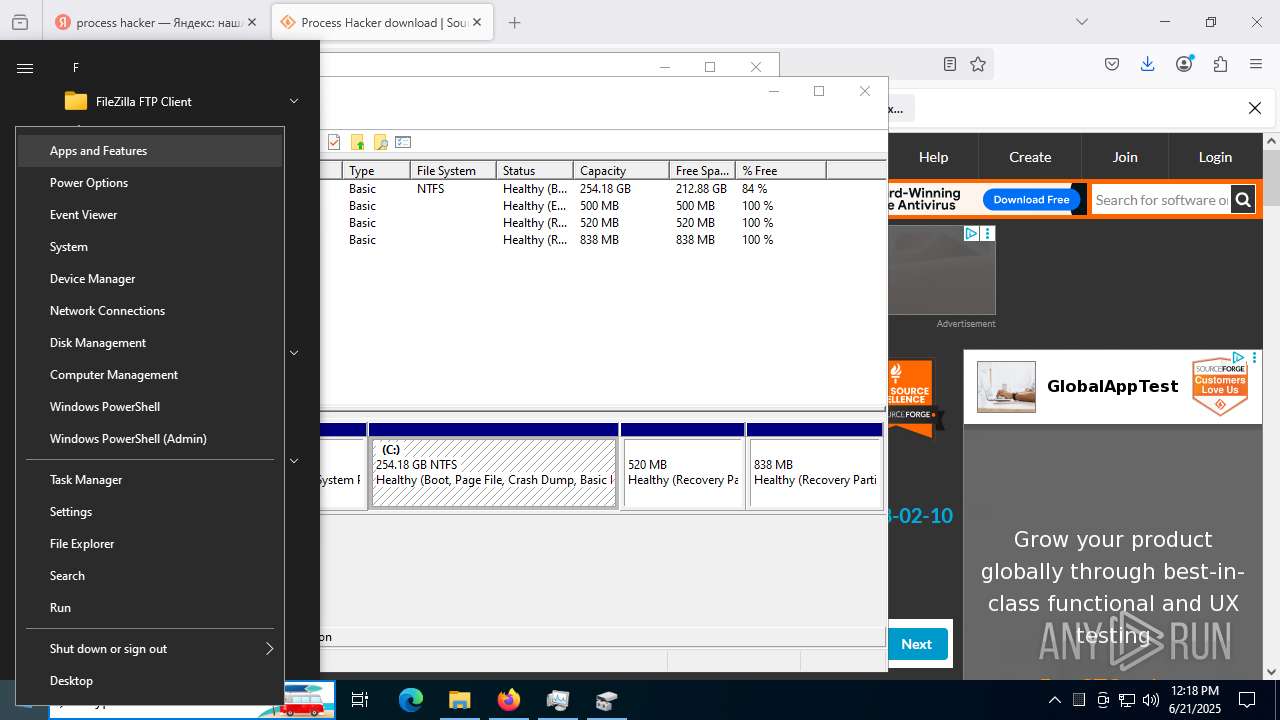
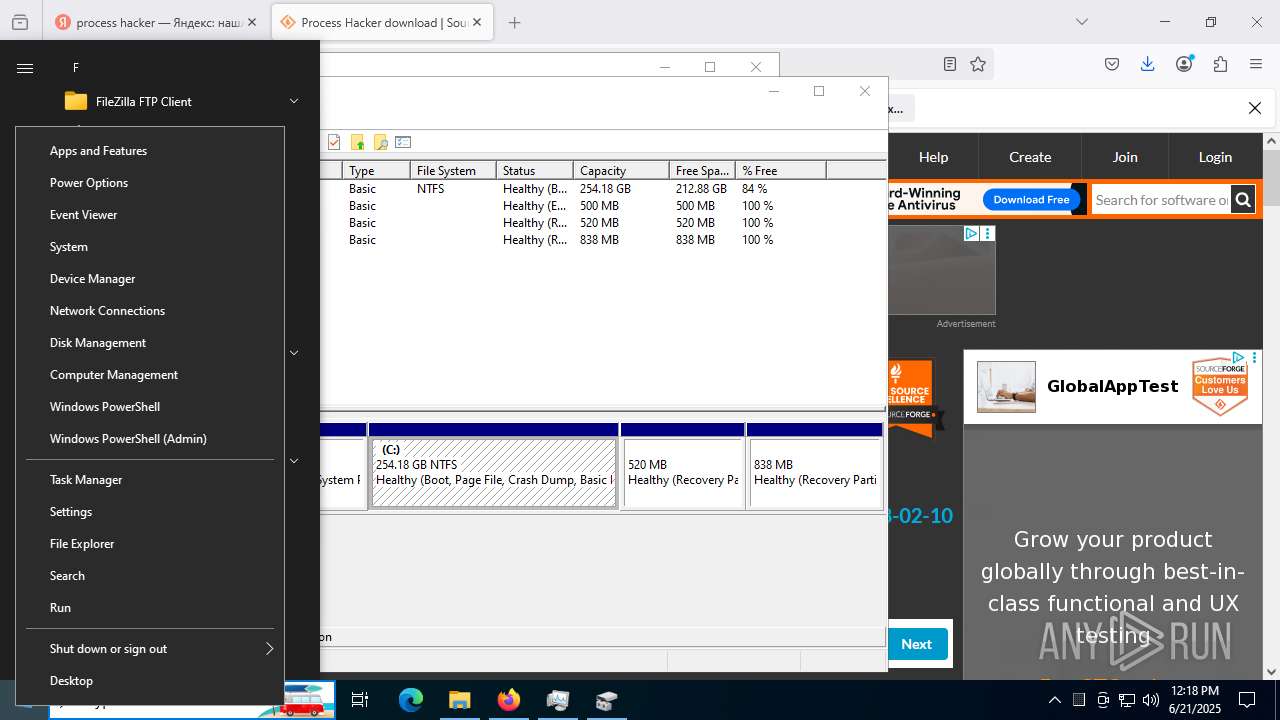
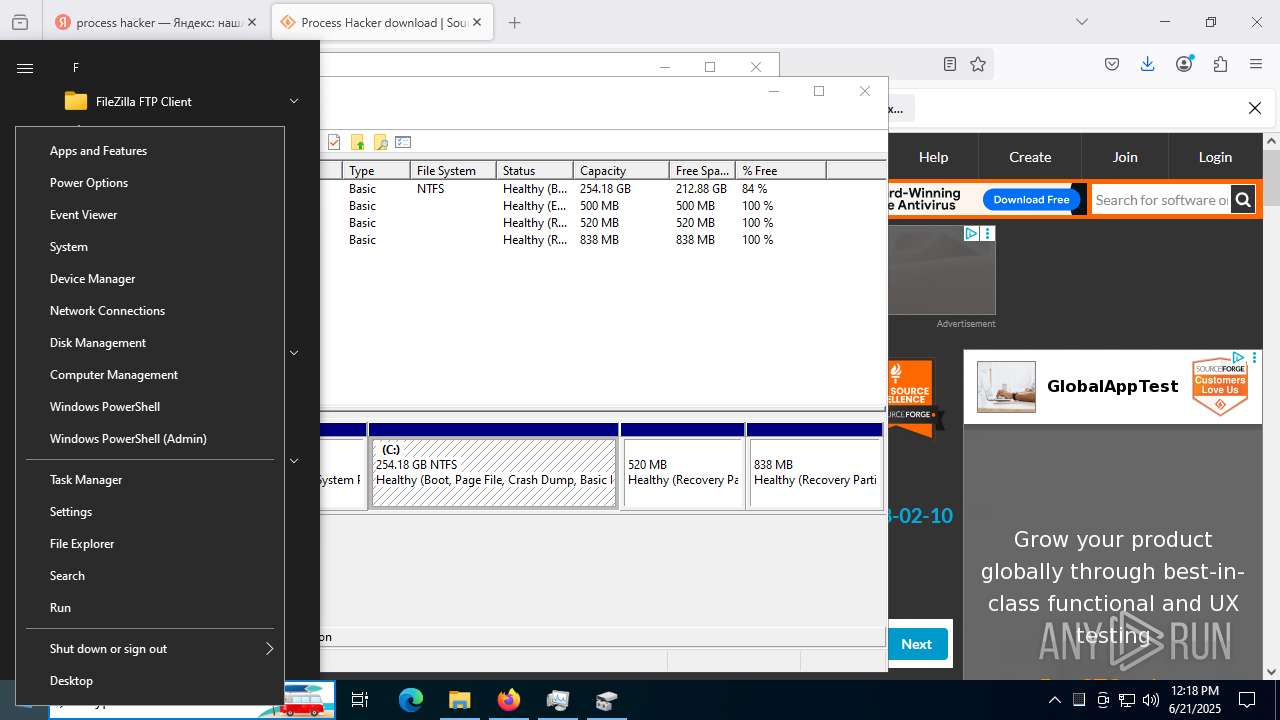
MALICIOUS
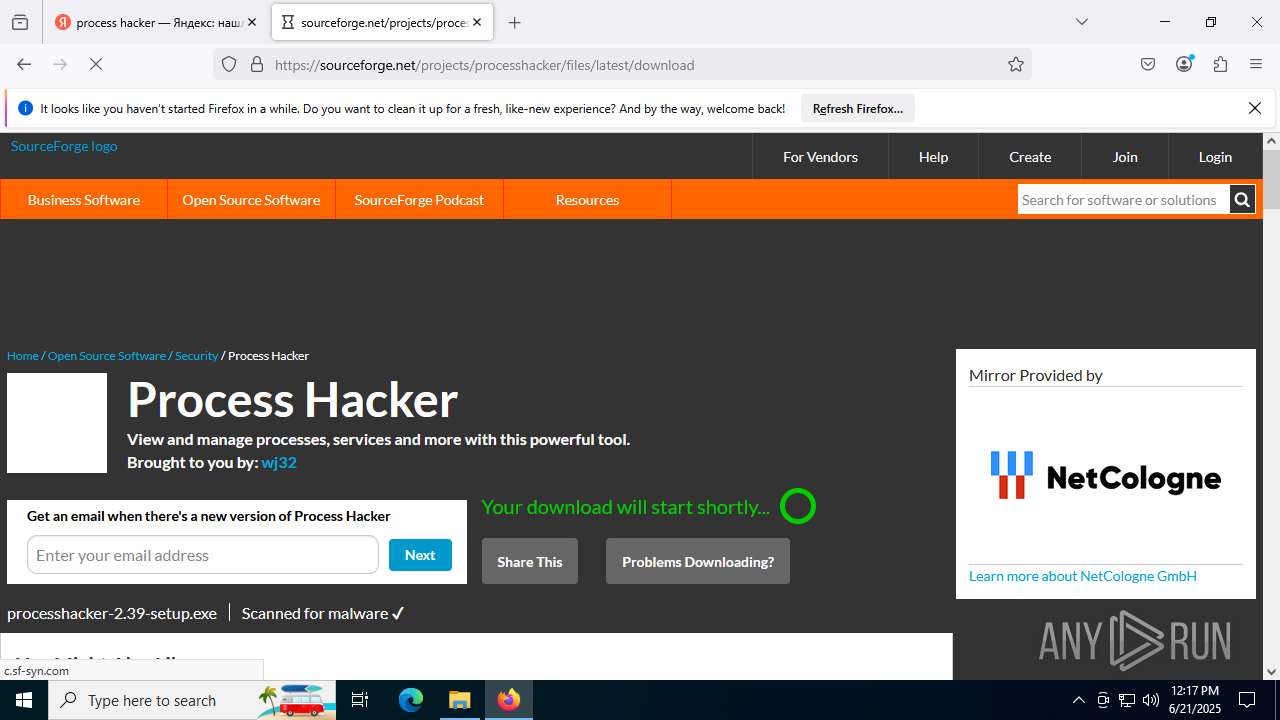
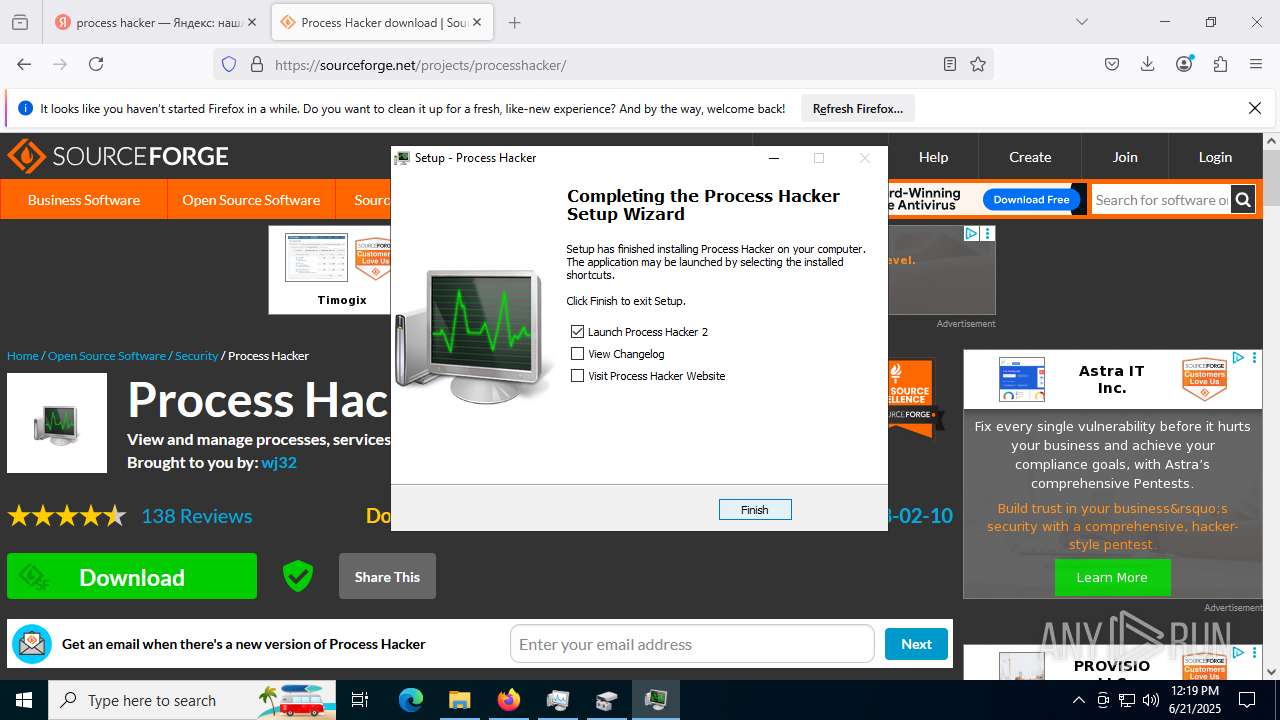
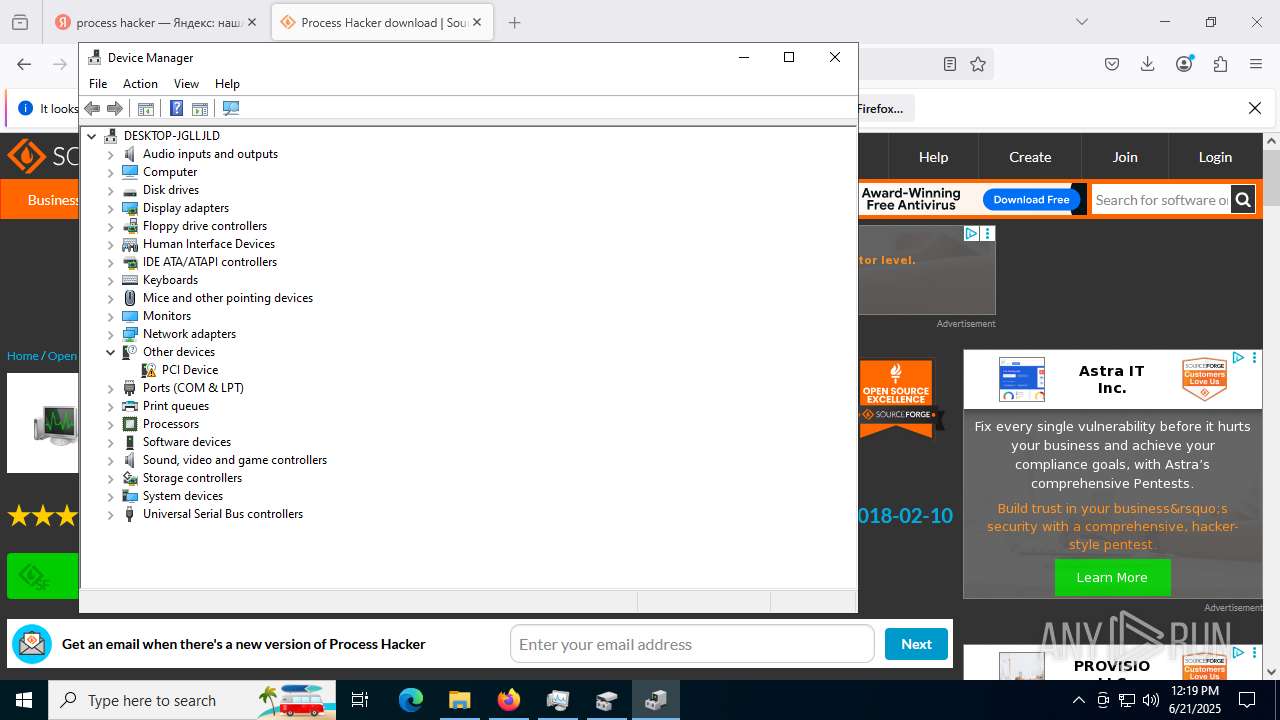
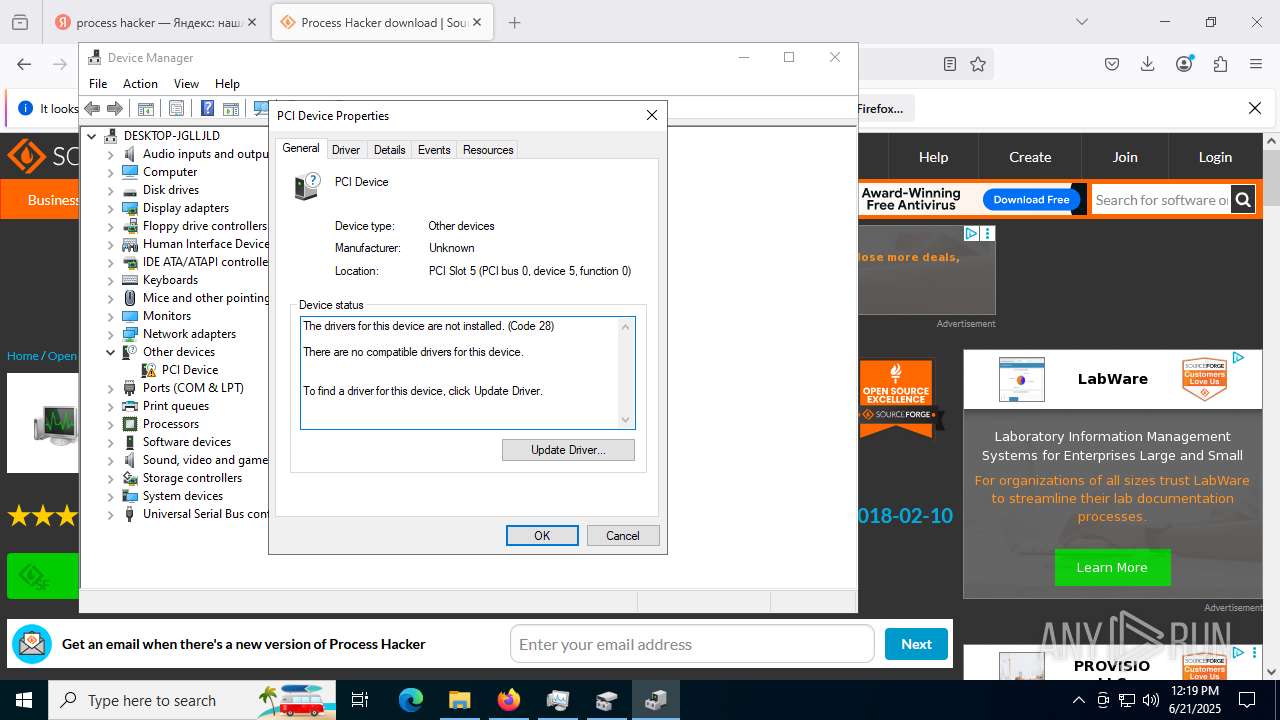
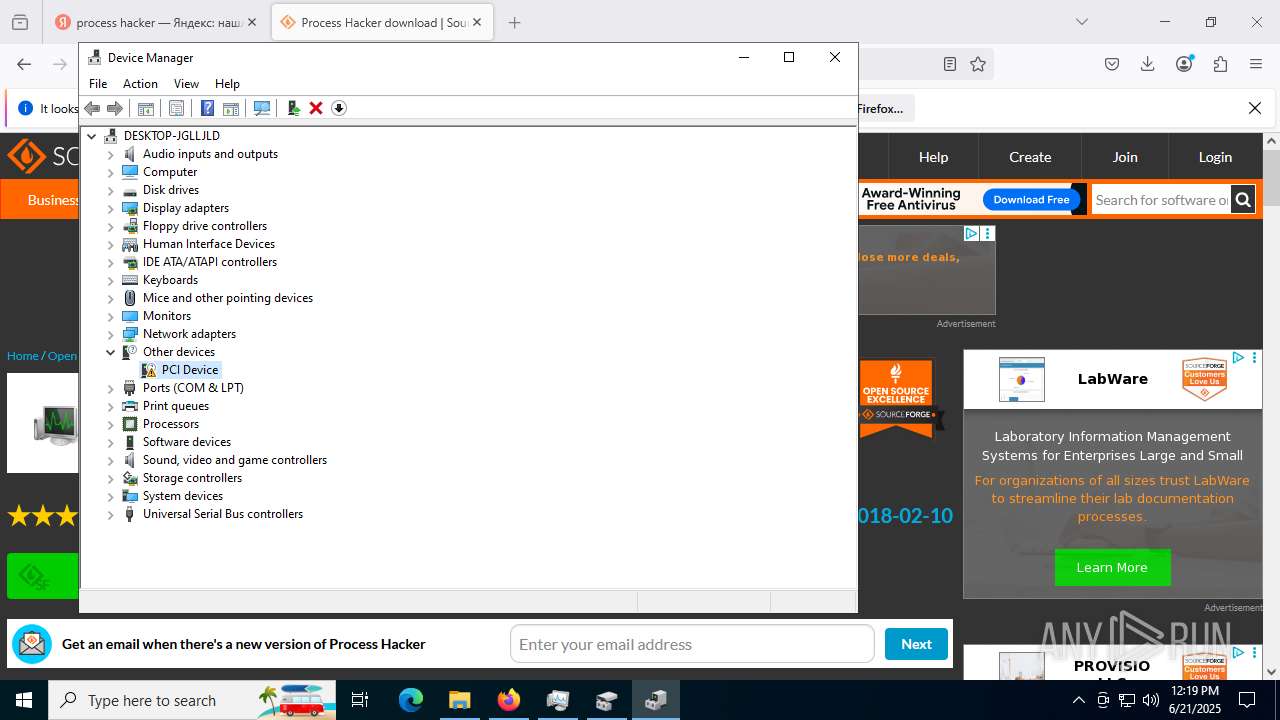
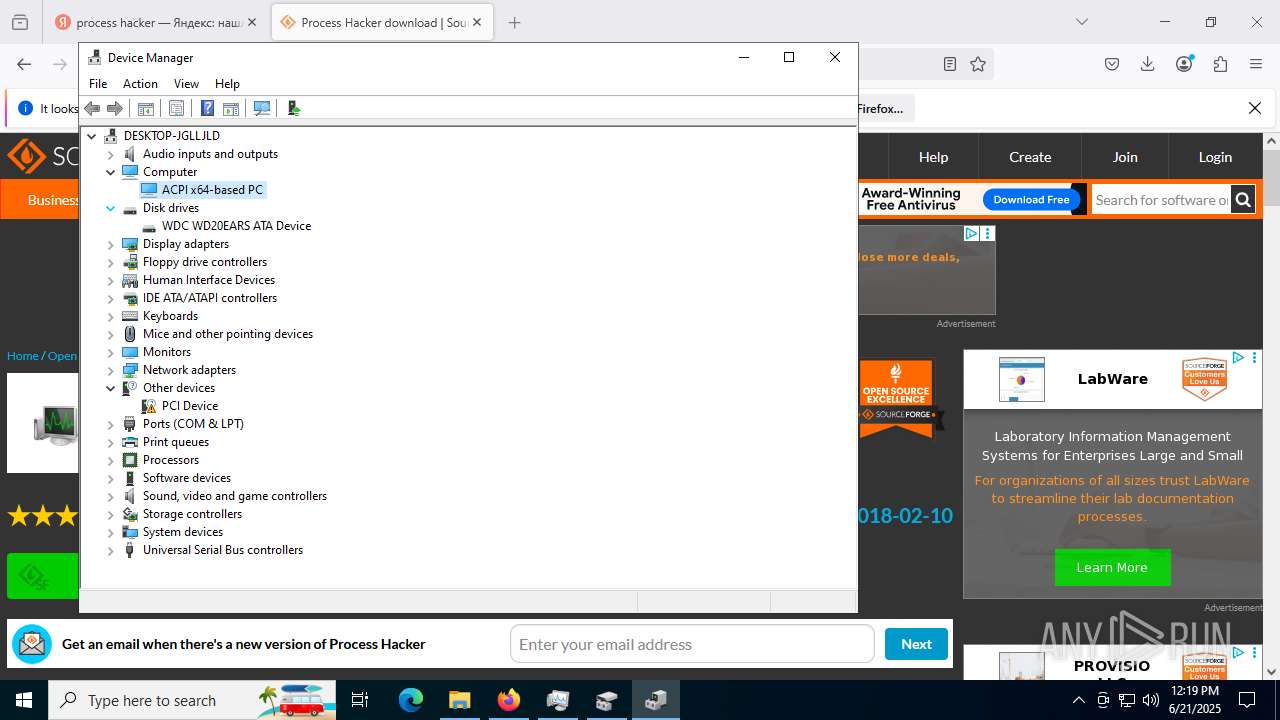
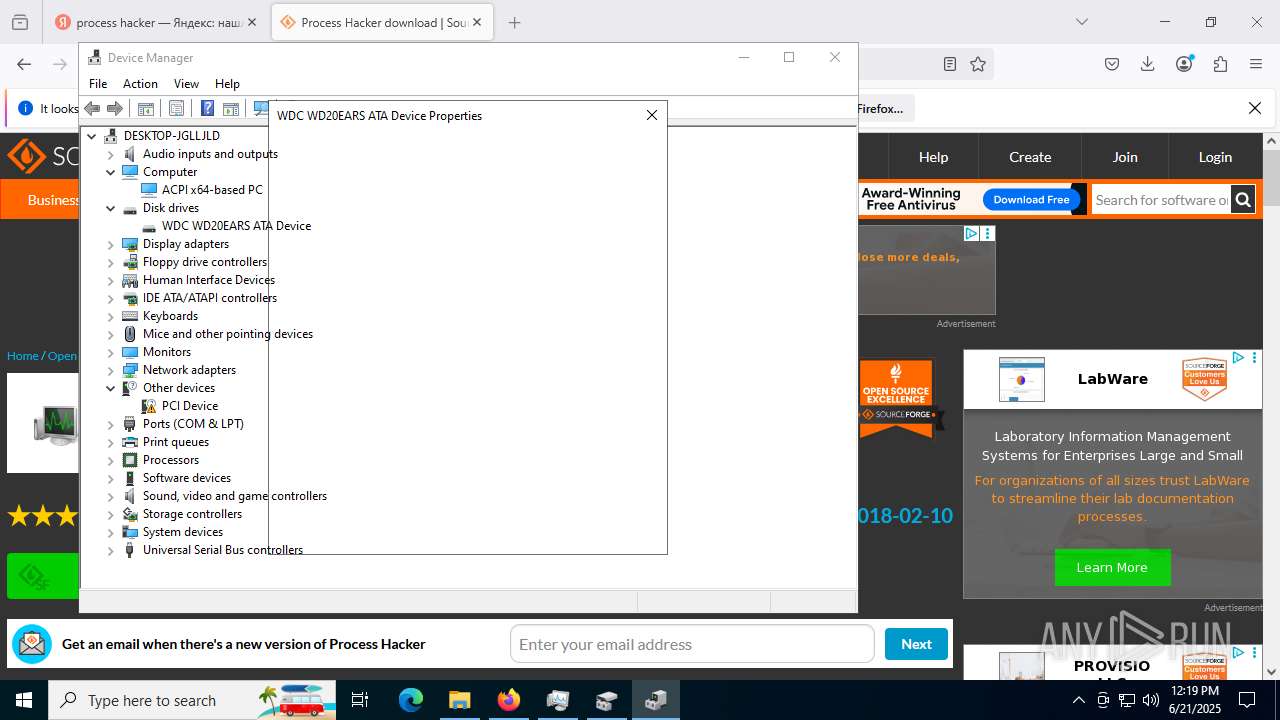
Vulnerable driver has been detected
- processhacker-2.39-setup.tmp (PID: 8460)
SUSPICIOUS
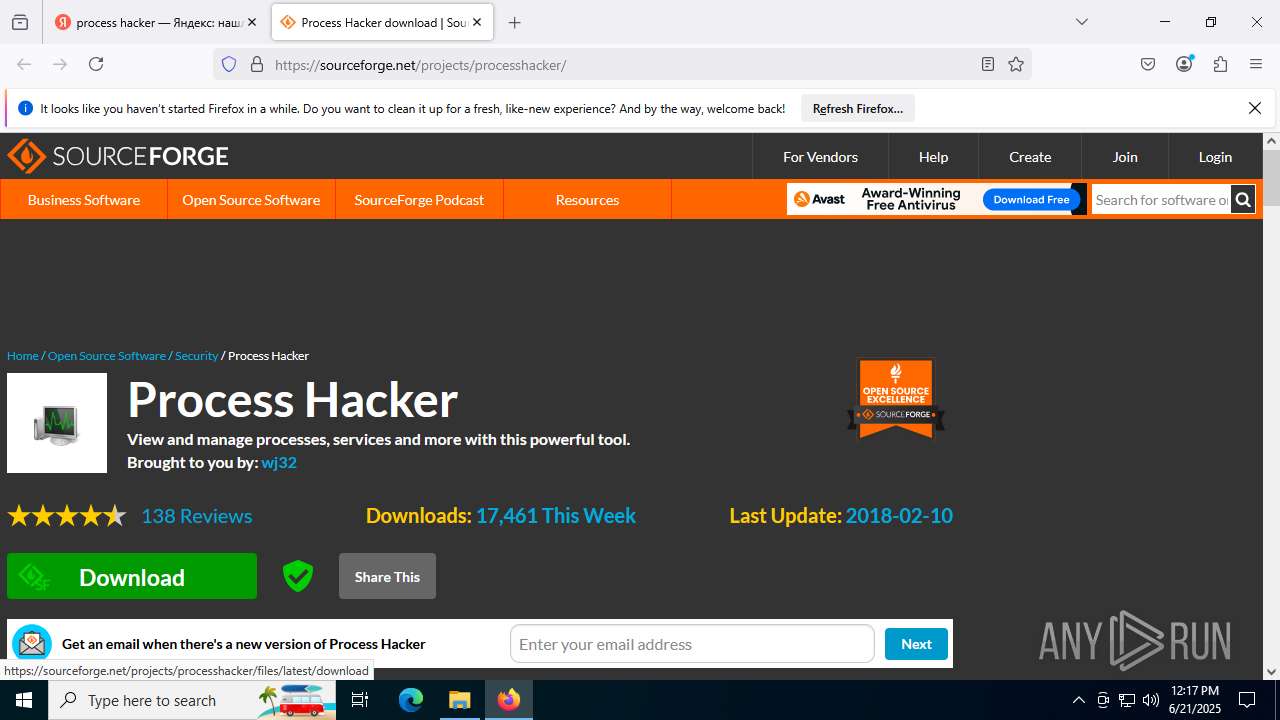
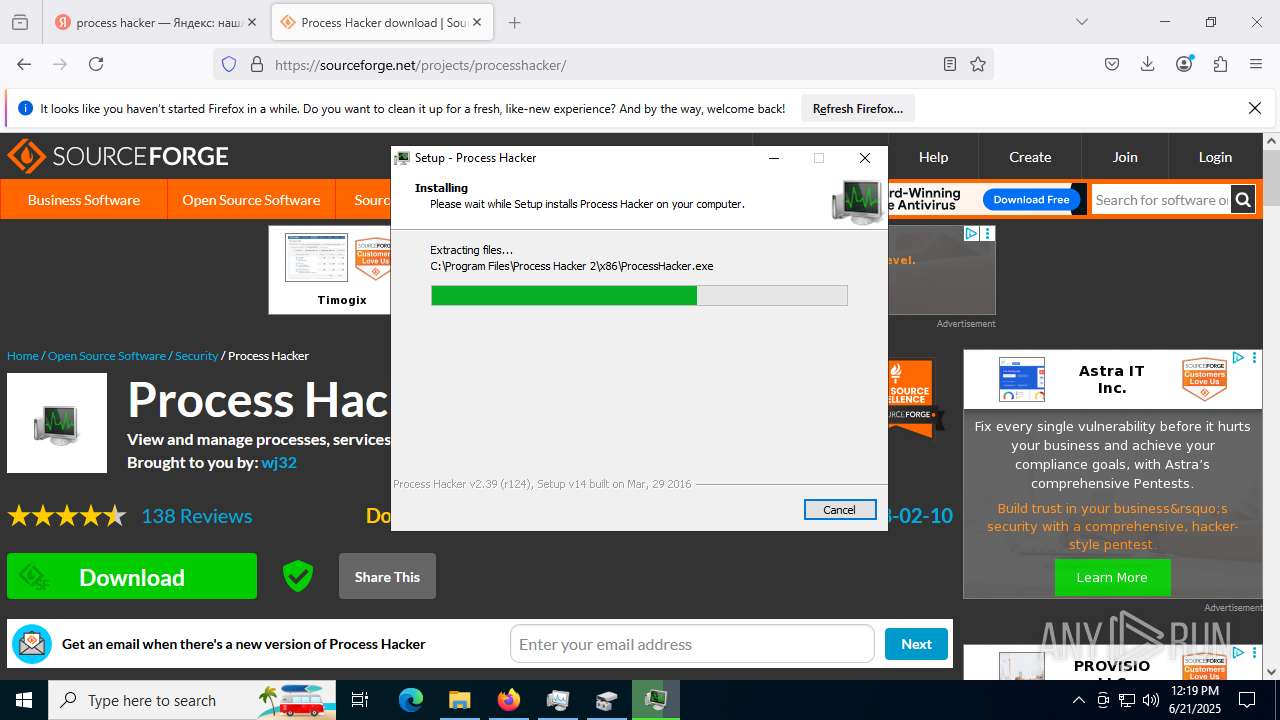
Executable content was dropped or overwritten
- processhacker-2.39-setup.exe (PID: 4916)
- processhacker-2.39-setup.exe (PID: 2396)
- processhacker-2.39-setup.tmp (PID: 8460)
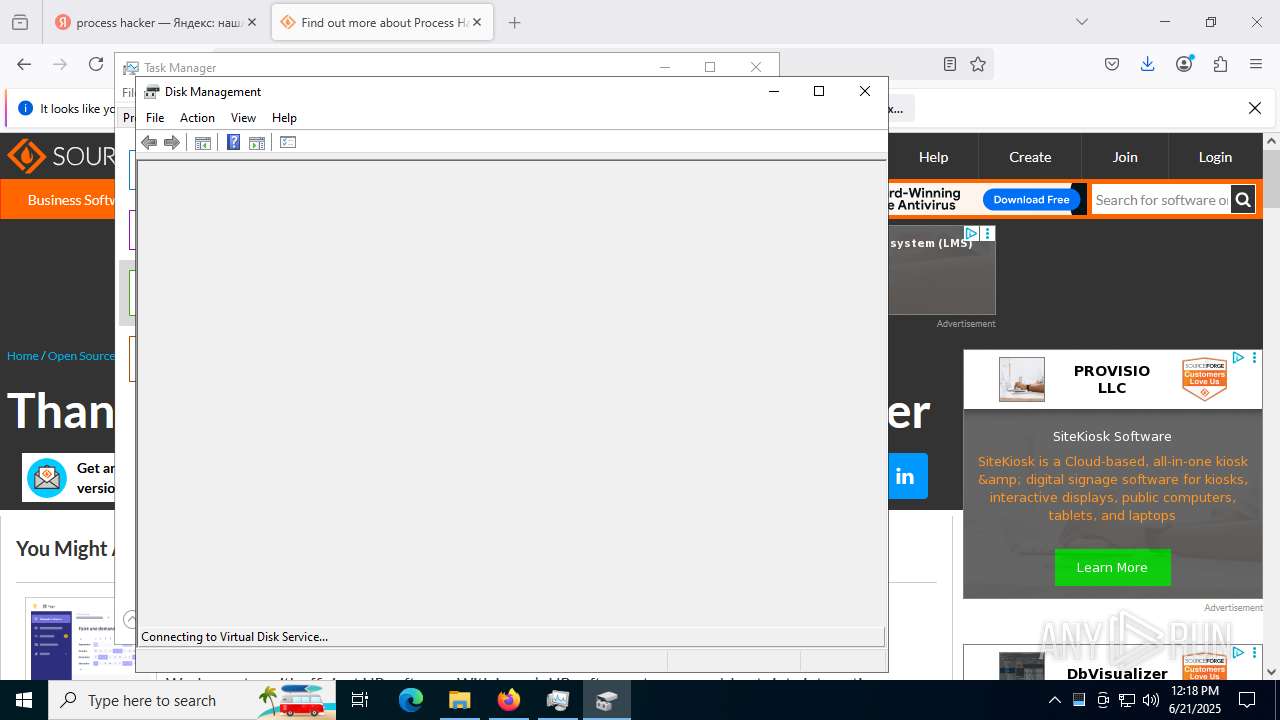
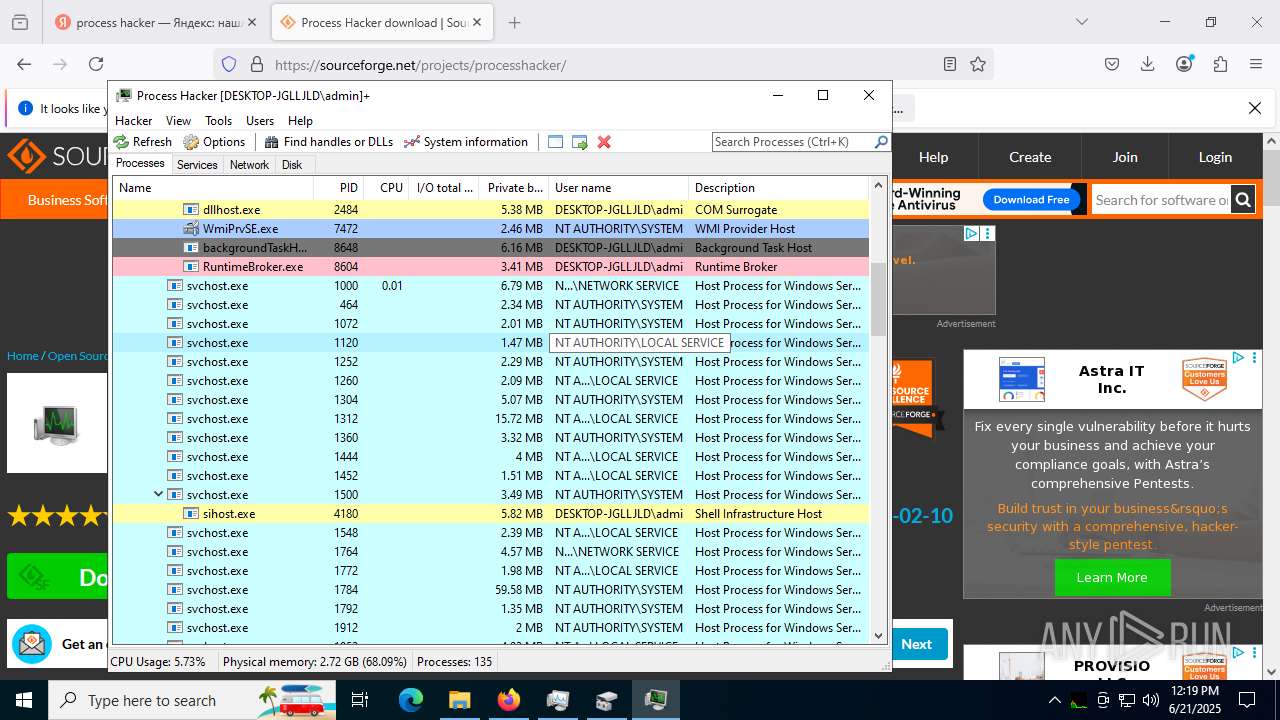
The process executes via Task Scheduler
- mmc.exe (PID: 6896)
- mmc.exe (PID: 2716)
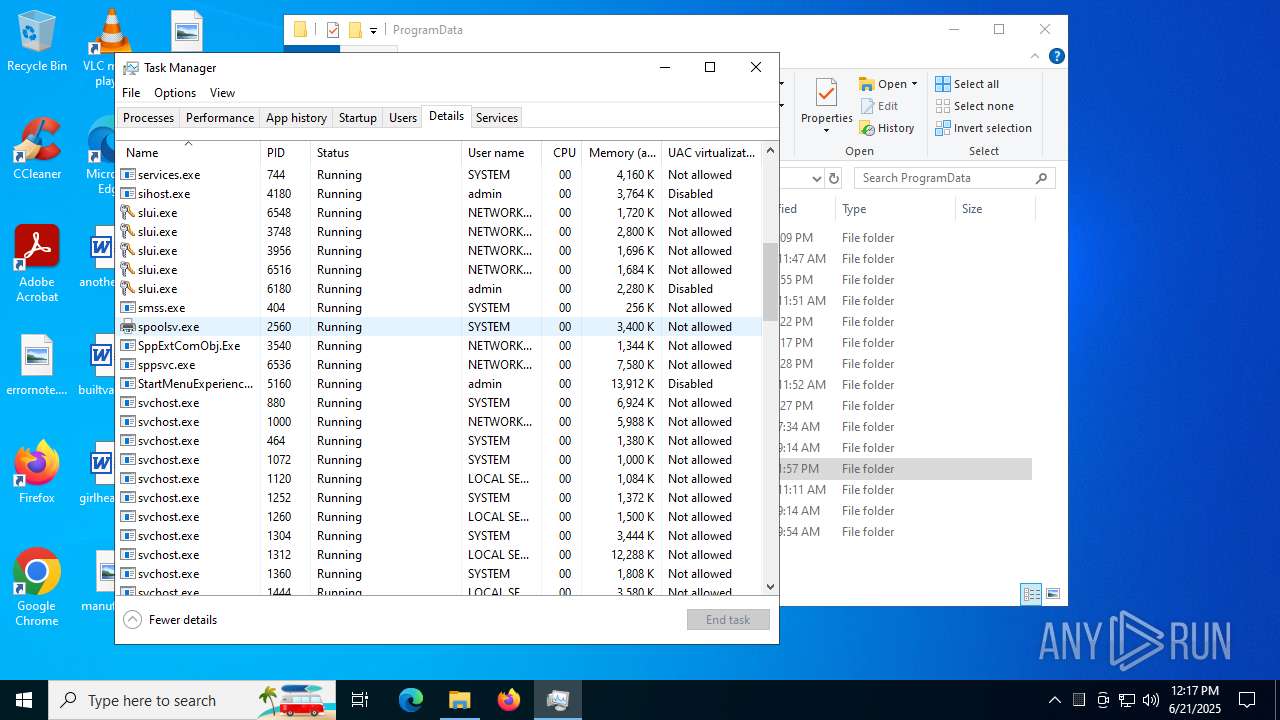
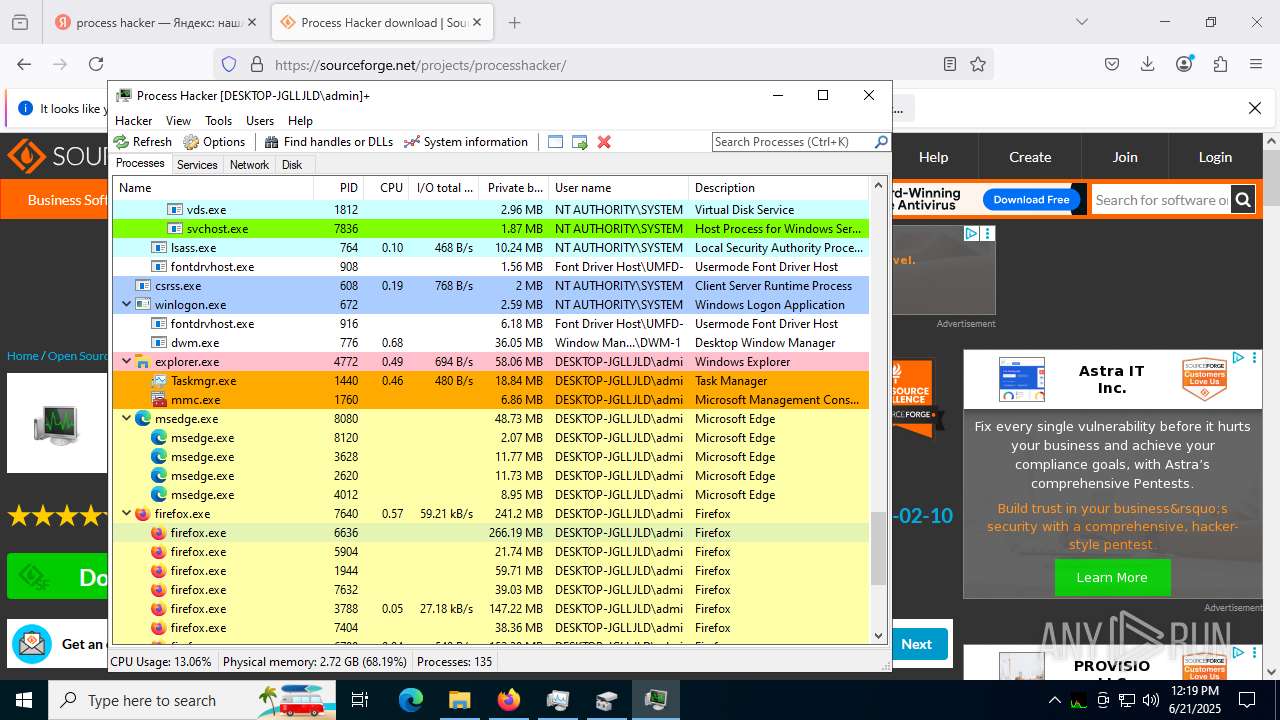
Executes as Windows Service
- vds.exe (PID: 1812)
Reads security settings of Internet Explorer
- processhacker-2.39-setup.tmp (PID: 6572)
- ProcessHacker.exe (PID: 7464)
Drops a system driver (possible attempt to evade defenses)
- processhacker-2.39-setup.tmp (PID: 8460)
Reads the Windows owner or organization settings
- processhacker-2.39-setup.tmp (PID: 8460)
INFO
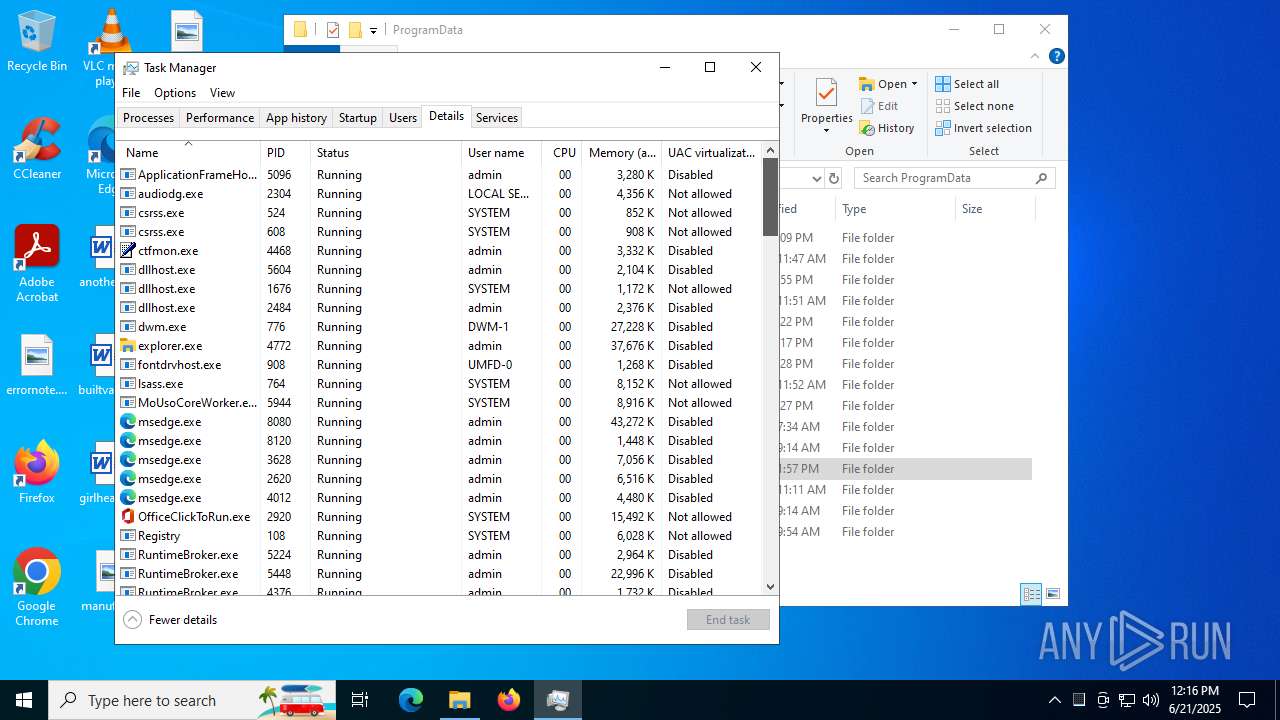
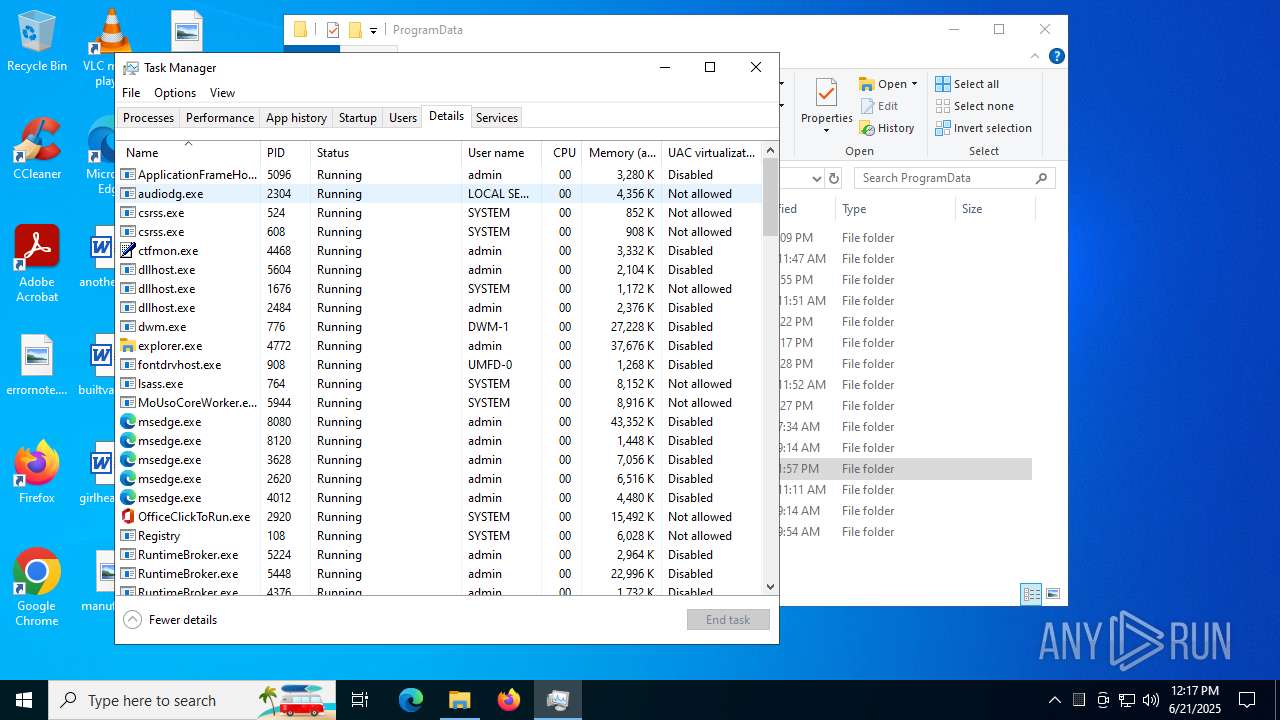
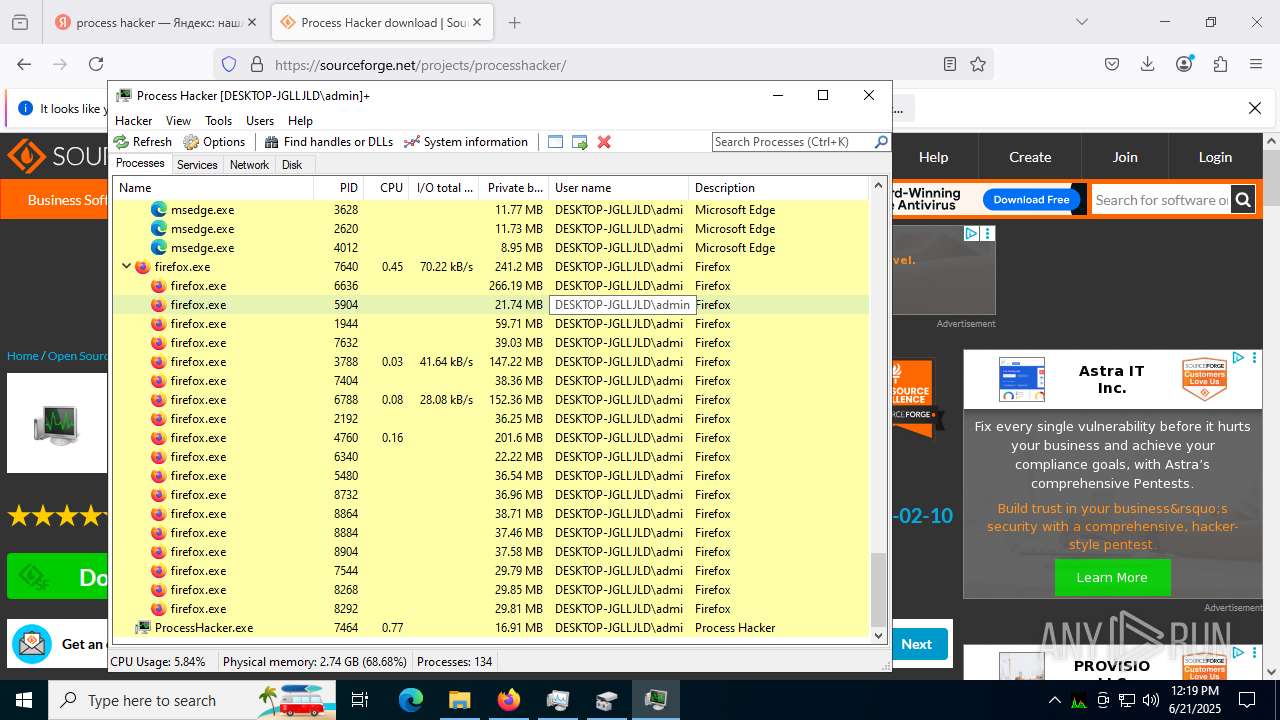
Application launched itself
- msedge.exe (PID: 6016)
- msedge.exe (PID: 8080)
- firefox.exe (PID: 7640)
- firefox.exe (PID: 436)
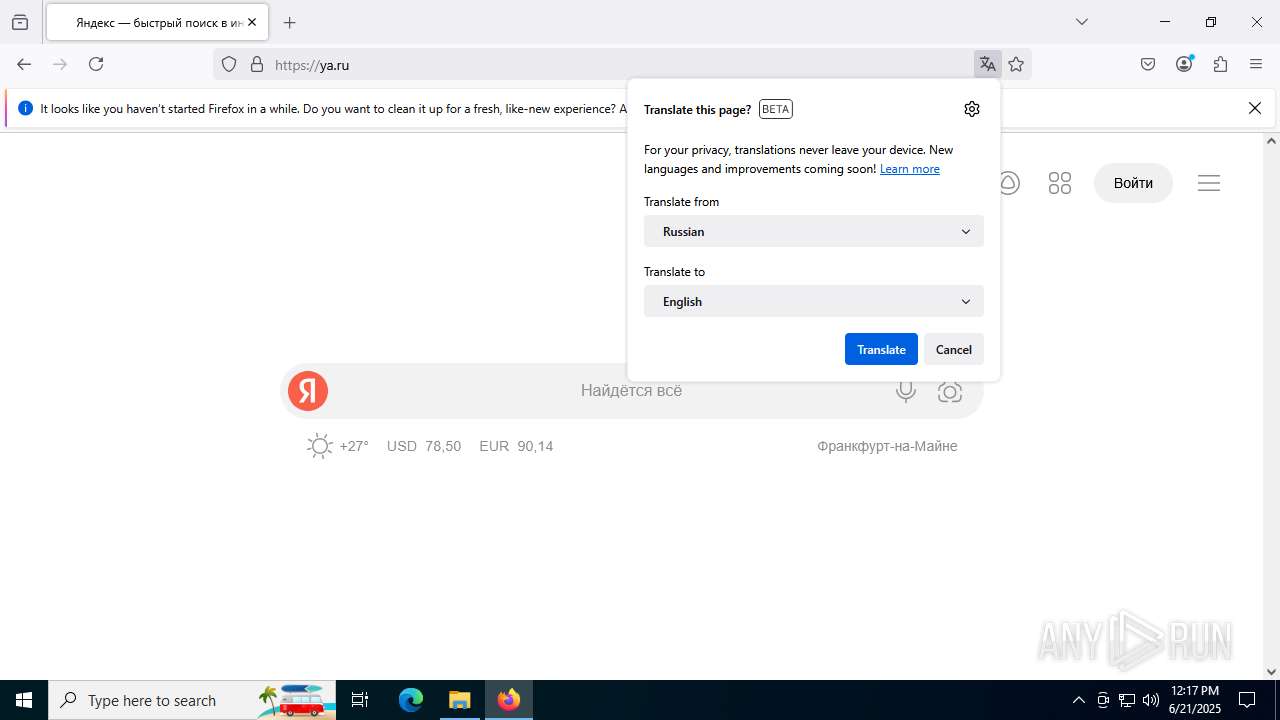
Checks supported languages
- identity_helper.exe (PID: 7608)
- identity_helper.exe (PID: 7000)
- processhacker-2.39-setup.tmp (PID: 6572)
- processhacker-2.39-setup.exe (PID: 4916)
- processhacker-2.39-setup.exe (PID: 2396)
- processhacker-2.39-setup.tmp (PID: 8460)
- ProcessHacker.exe (PID: 7464)
- ProcessHacker.exe (PID: 7468)
Reads the computer name
- identity_helper.exe (PID: 7608)
- identity_helper.exe (PID: 7000)
- processhacker-2.39-setup.tmp (PID: 6572)
- processhacker-2.39-setup.tmp (PID: 8460)
- ProcessHacker.exe (PID: 7464)
- ProcessHacker.exe (PID: 7468)
Reads Environment values
- identity_helper.exe (PID: 7608)
- identity_helper.exe (PID: 7000)
- ProcessHacker.exe (PID: 7464)
Reads security settings of Internet Explorer
- mmc.exe (PID: 6896)
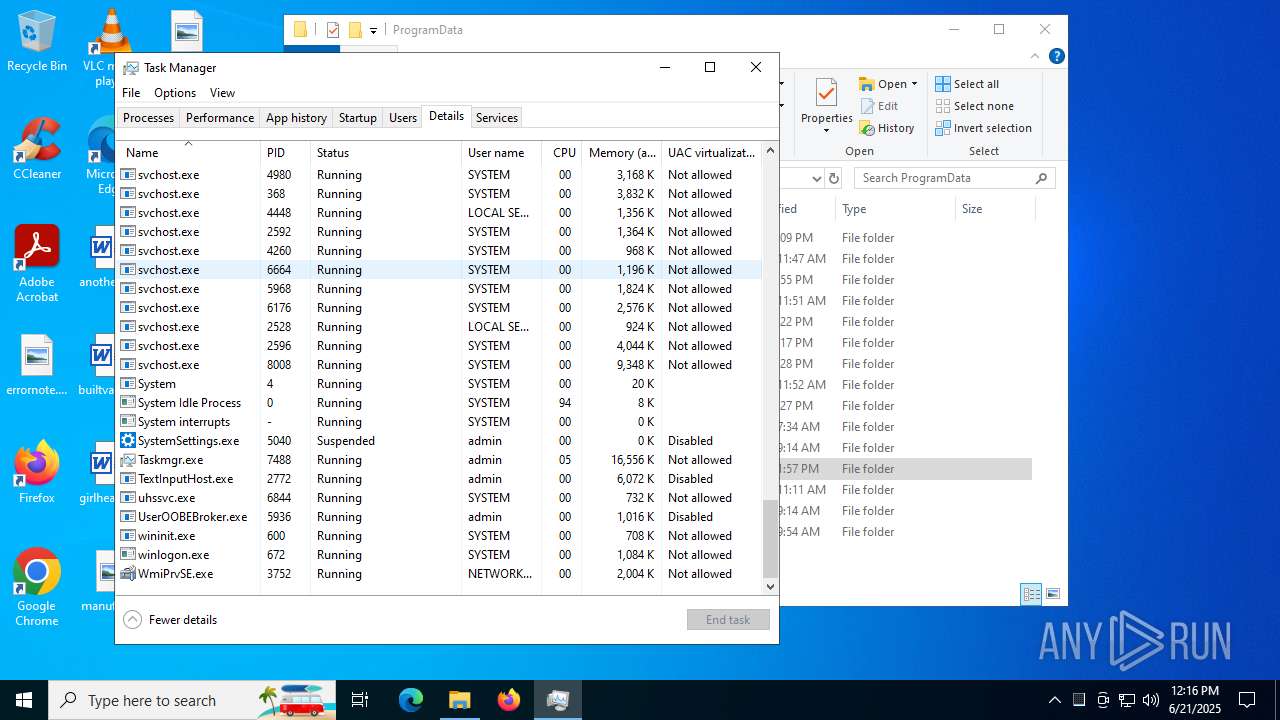
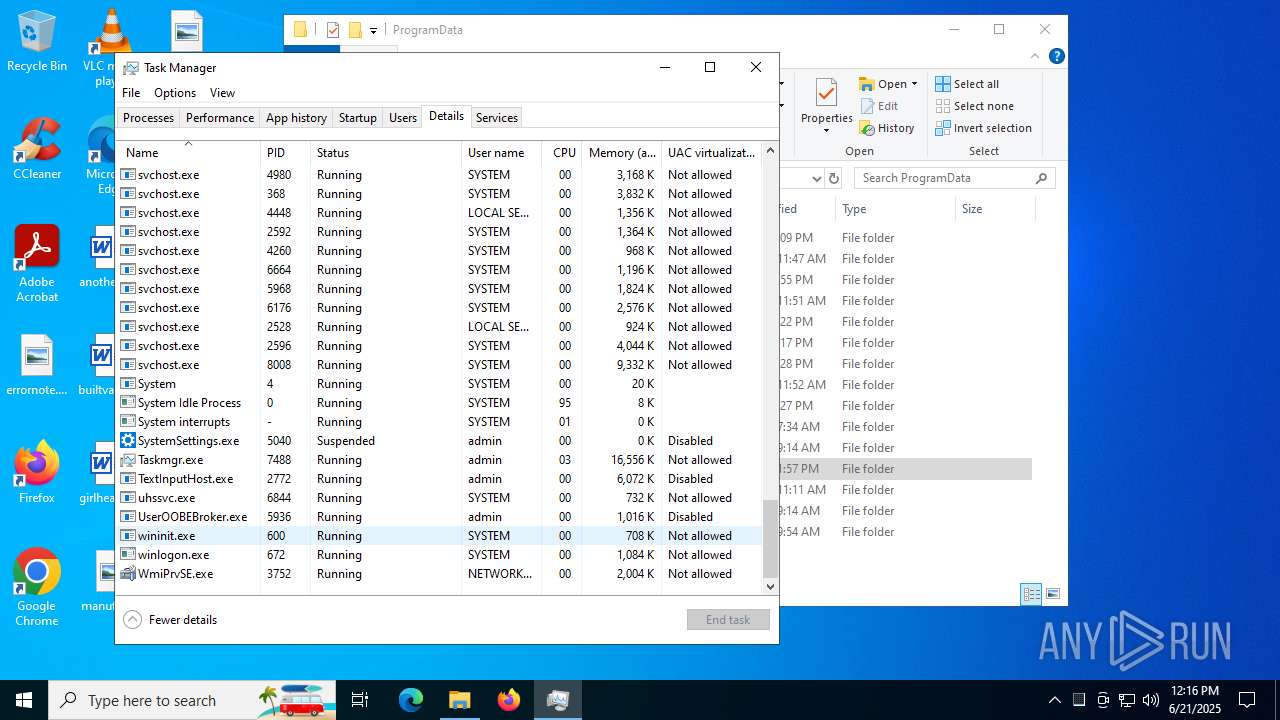
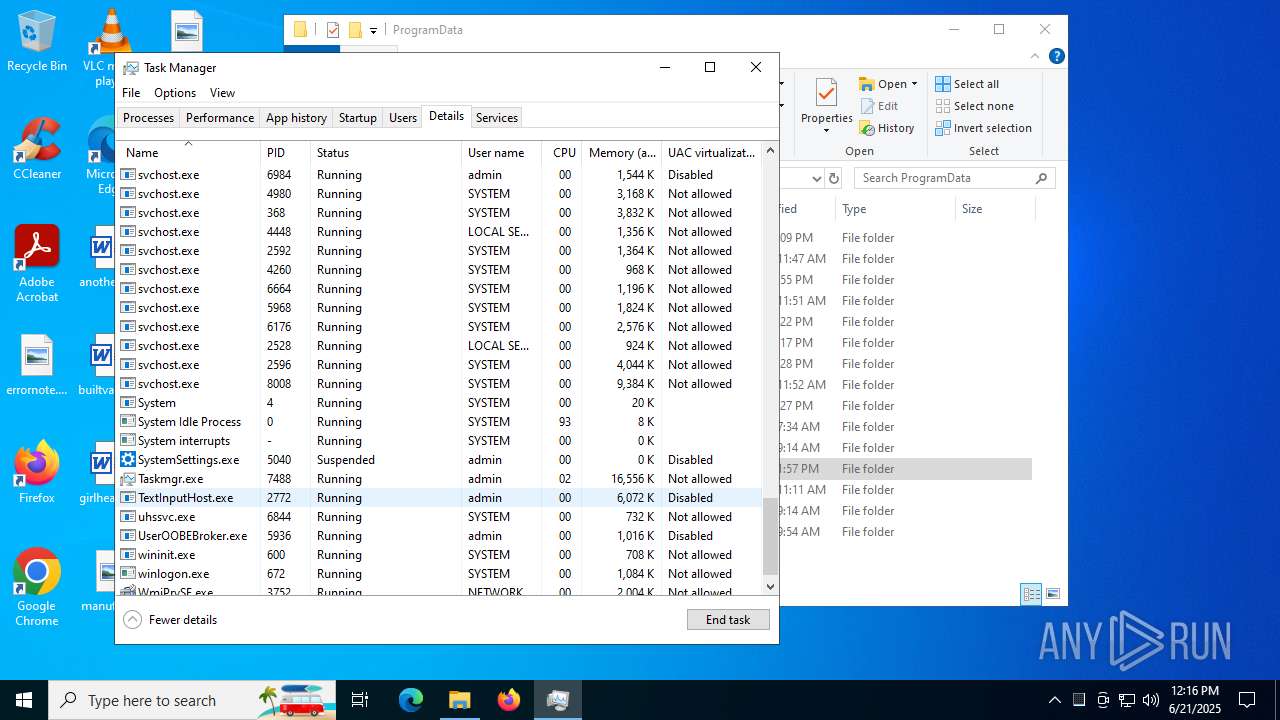
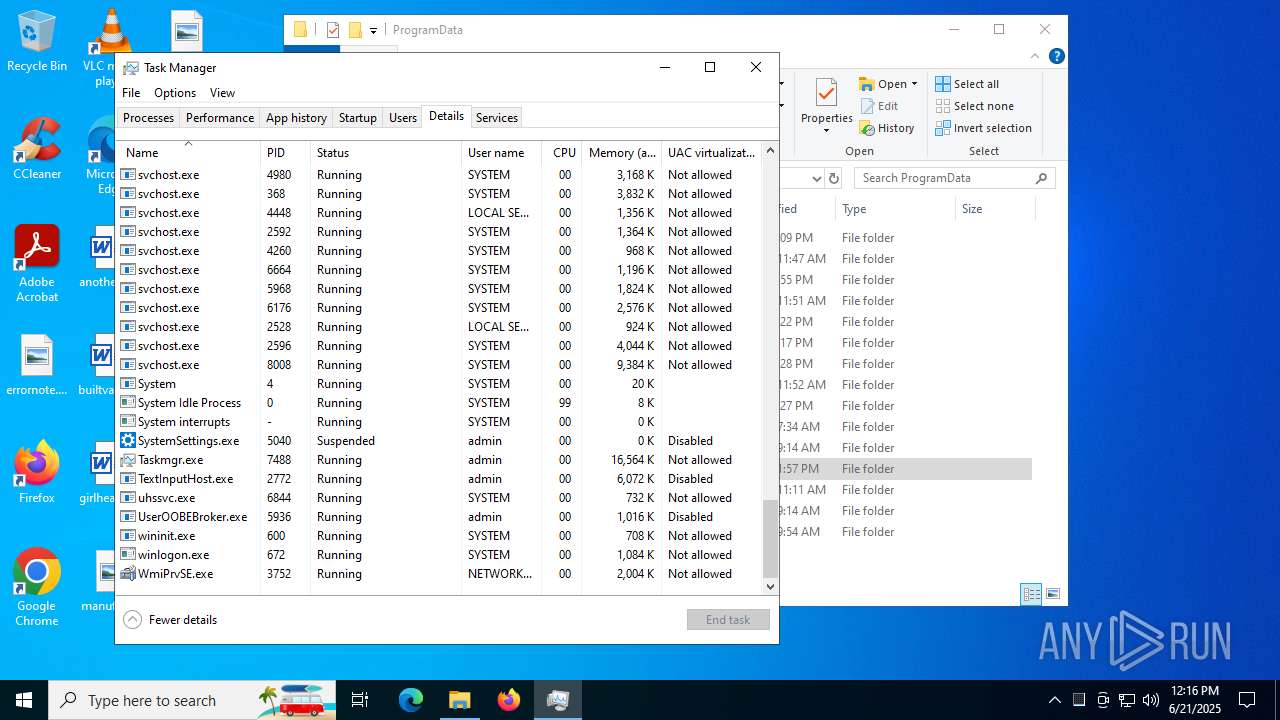
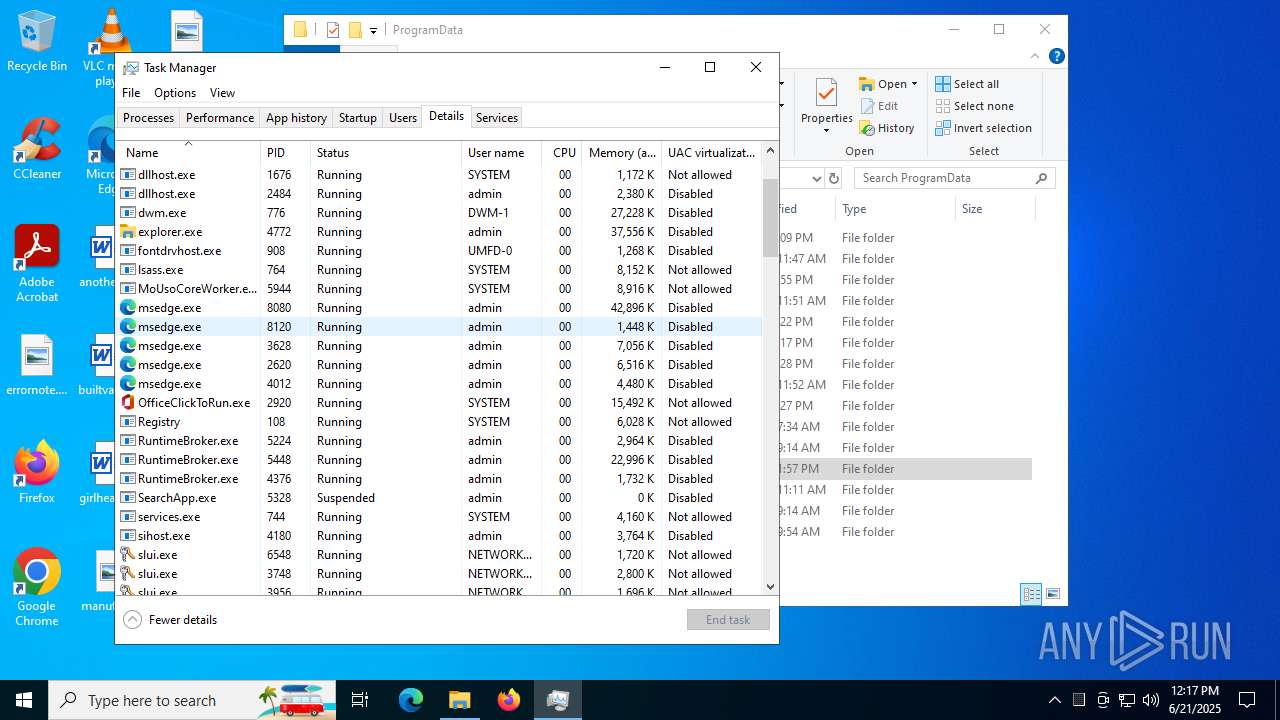
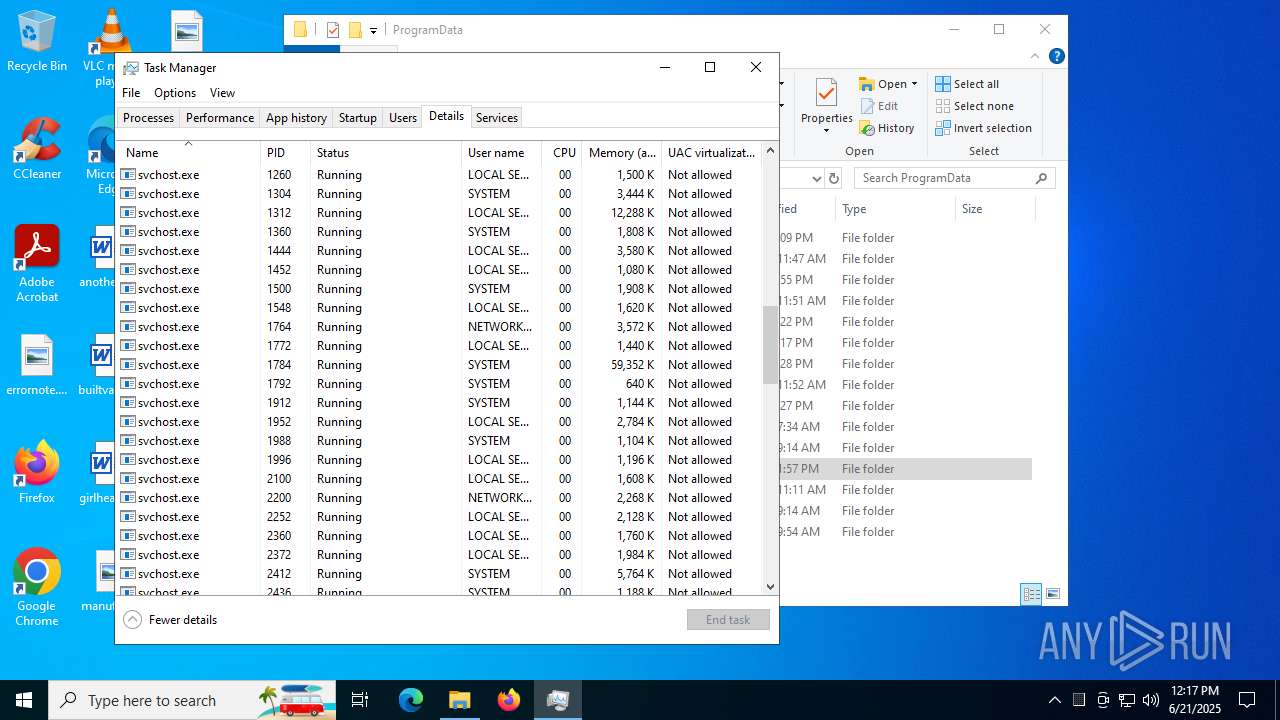
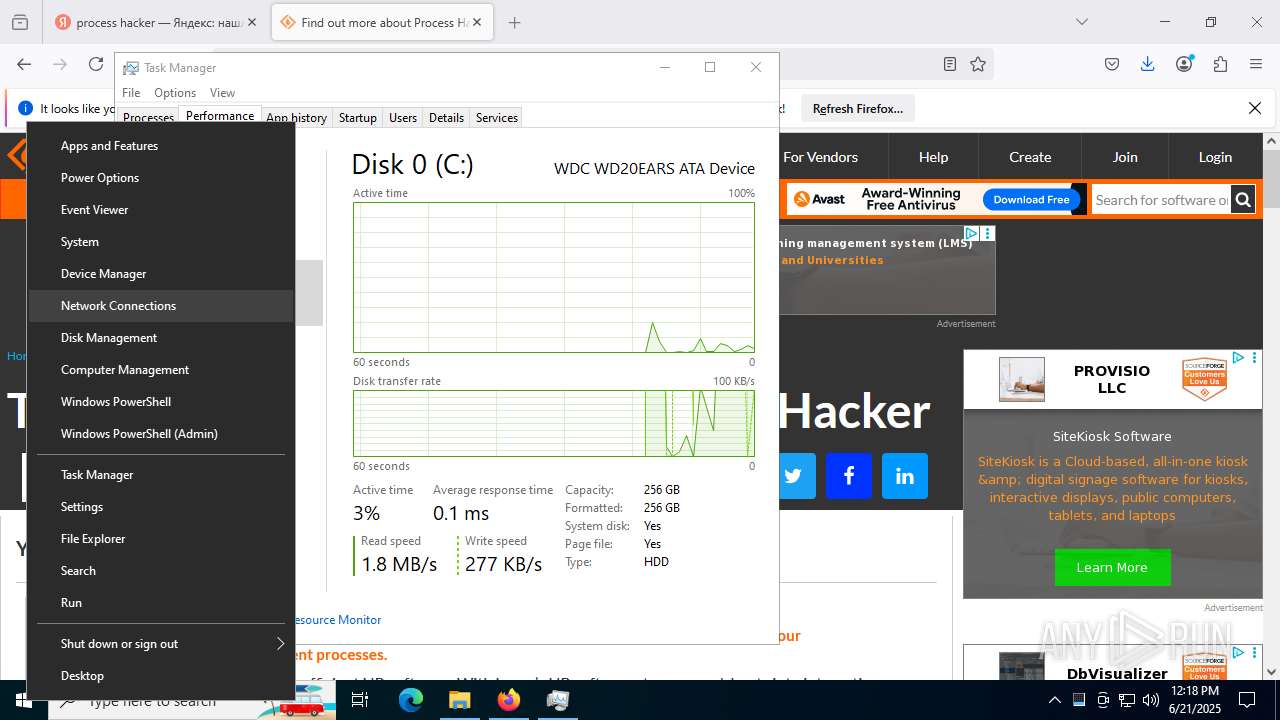
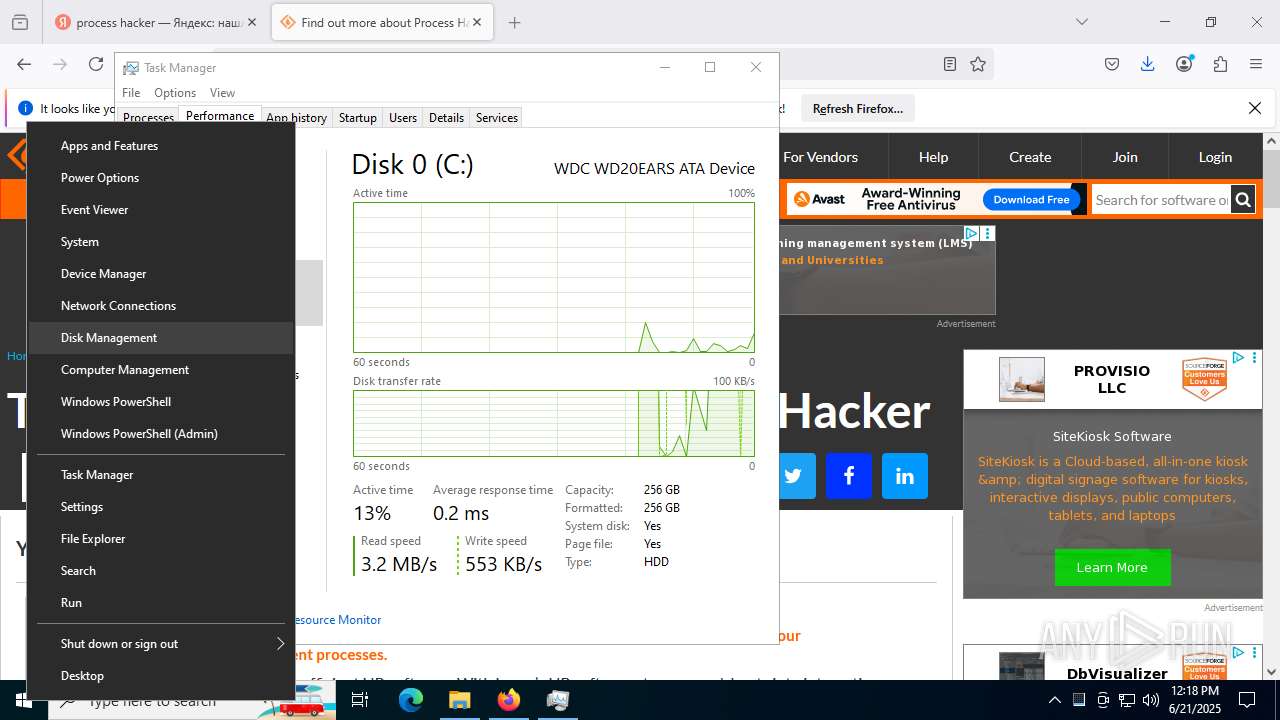
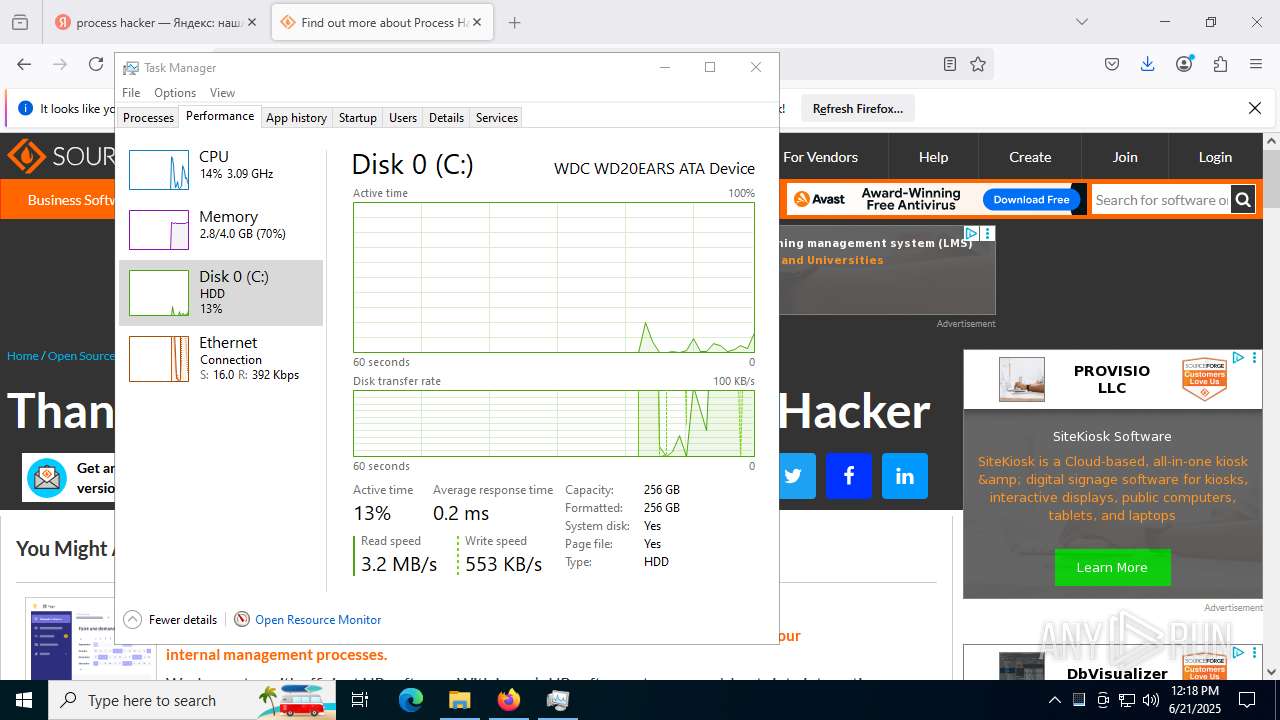
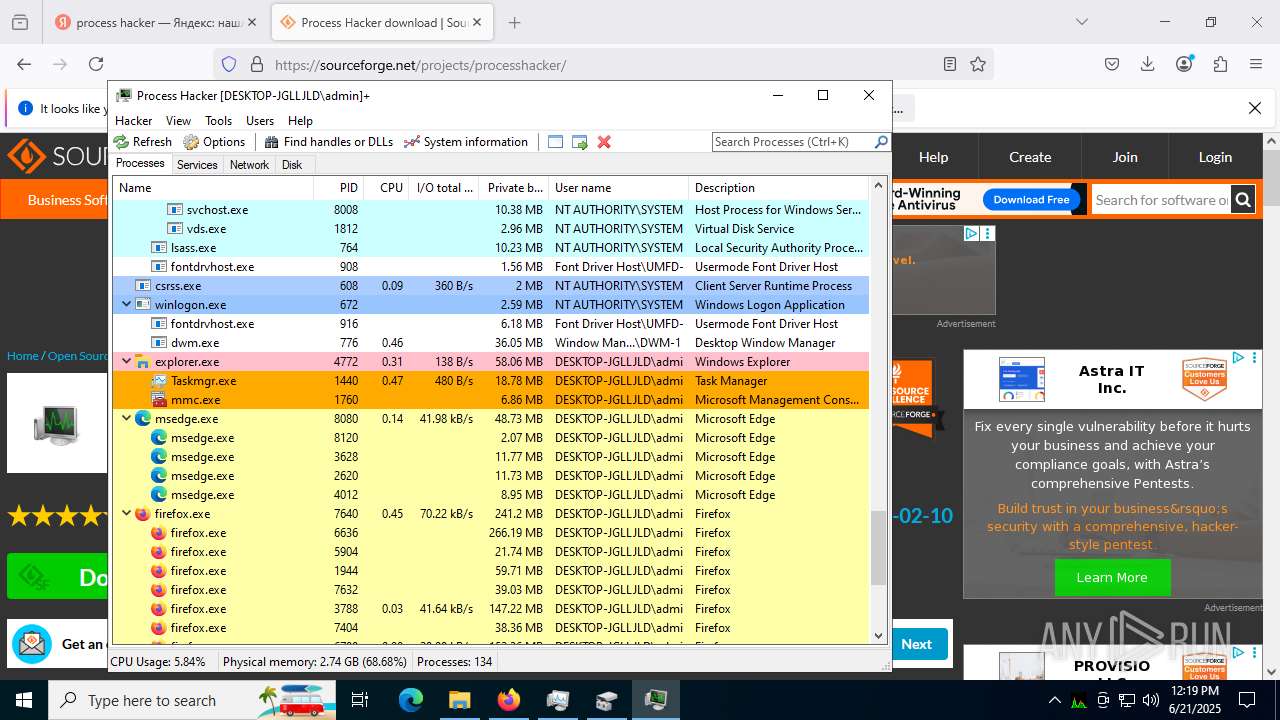
- Taskmgr.exe (PID: 1440)
- mmc.exe (PID: 1760)
- Taskmgr.exe (PID: 7488)
- mmc.exe (PID: 2716)
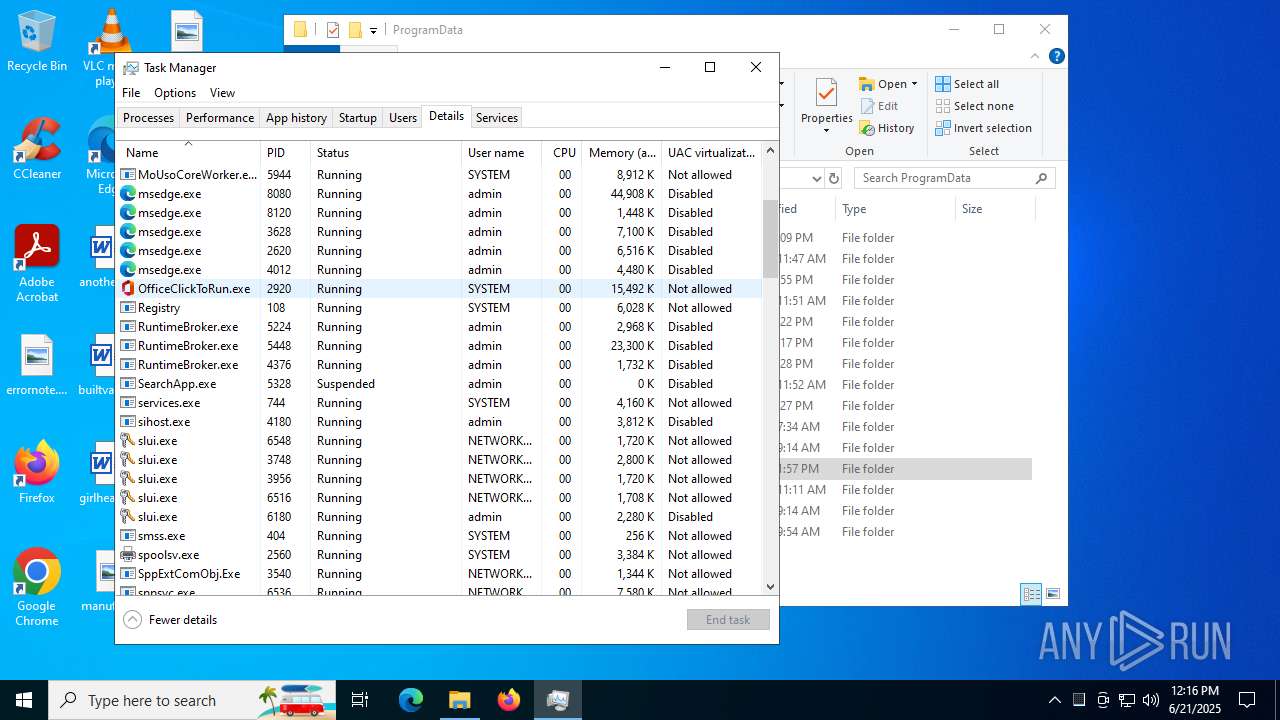
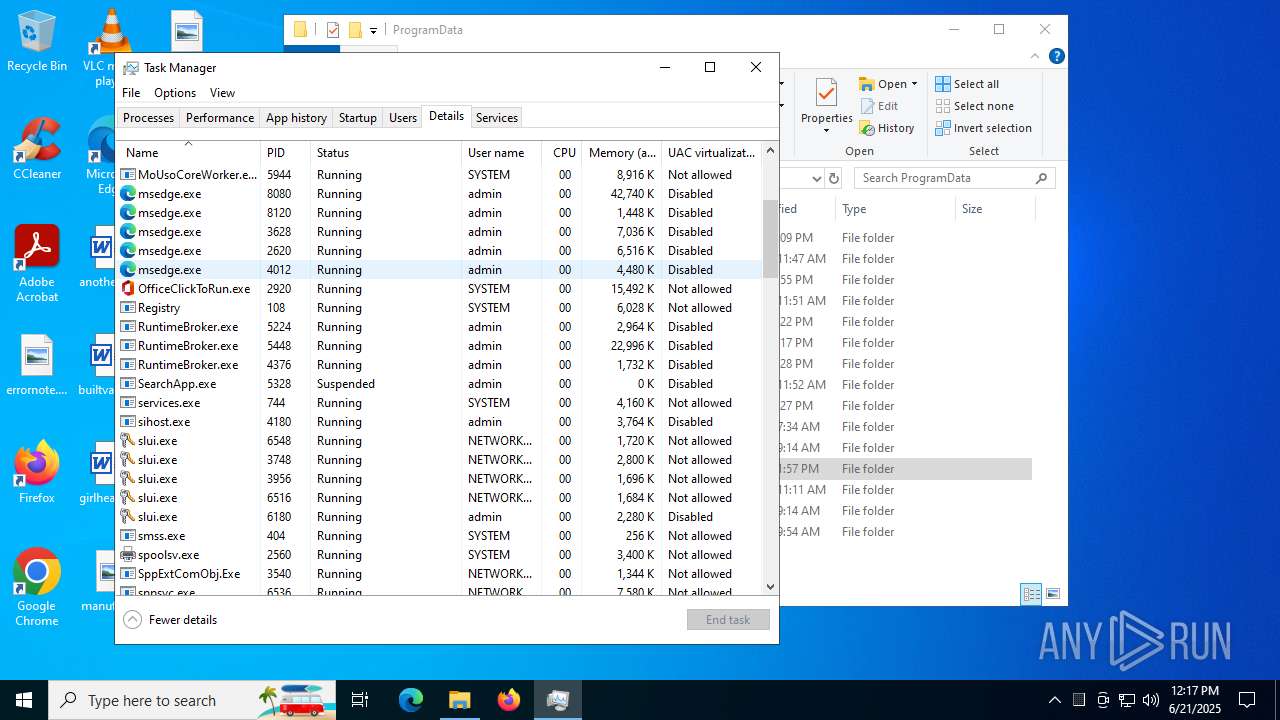
Reads the software policy settings
- slui.exe (PID: 6180)
- ProcessHacker.exe (PID: 7464)
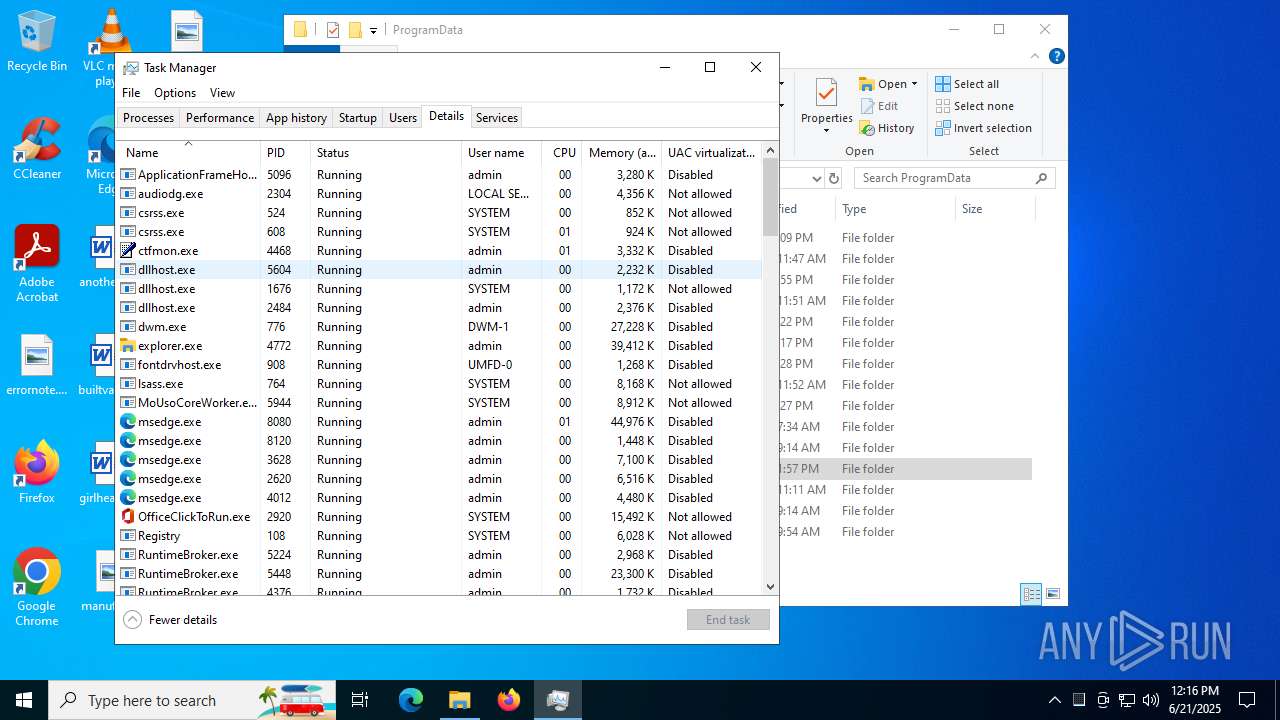
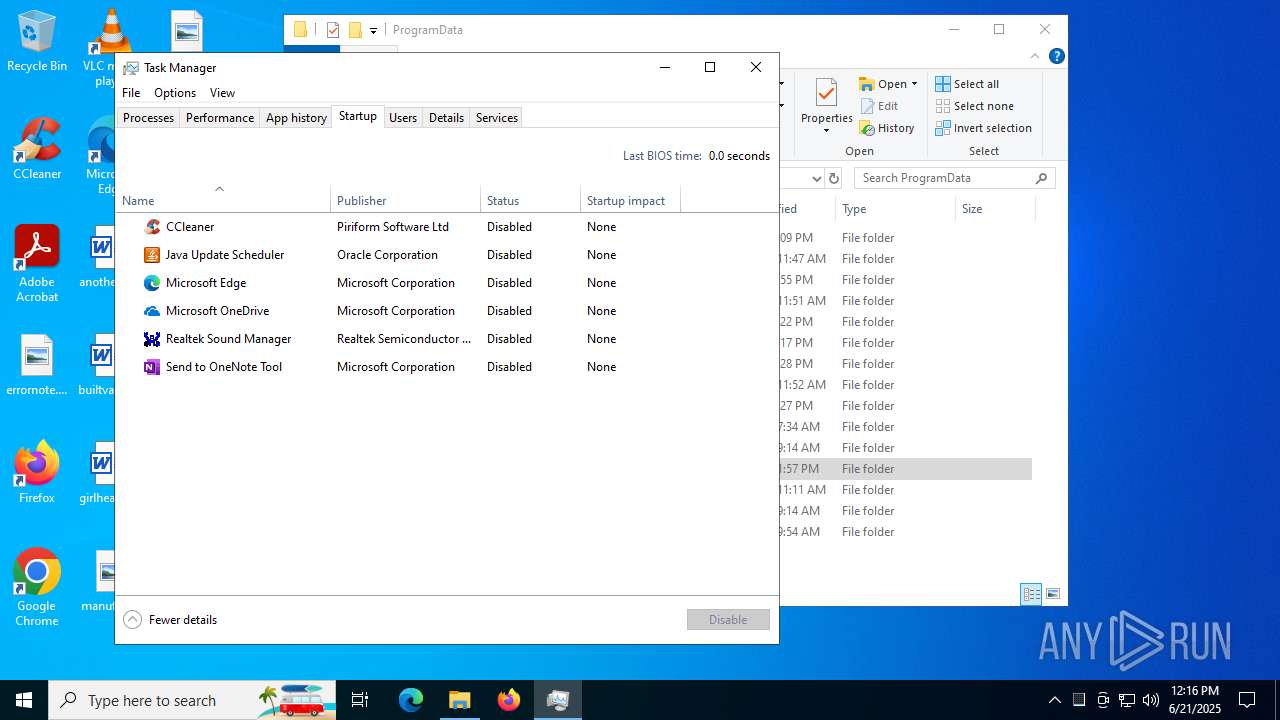
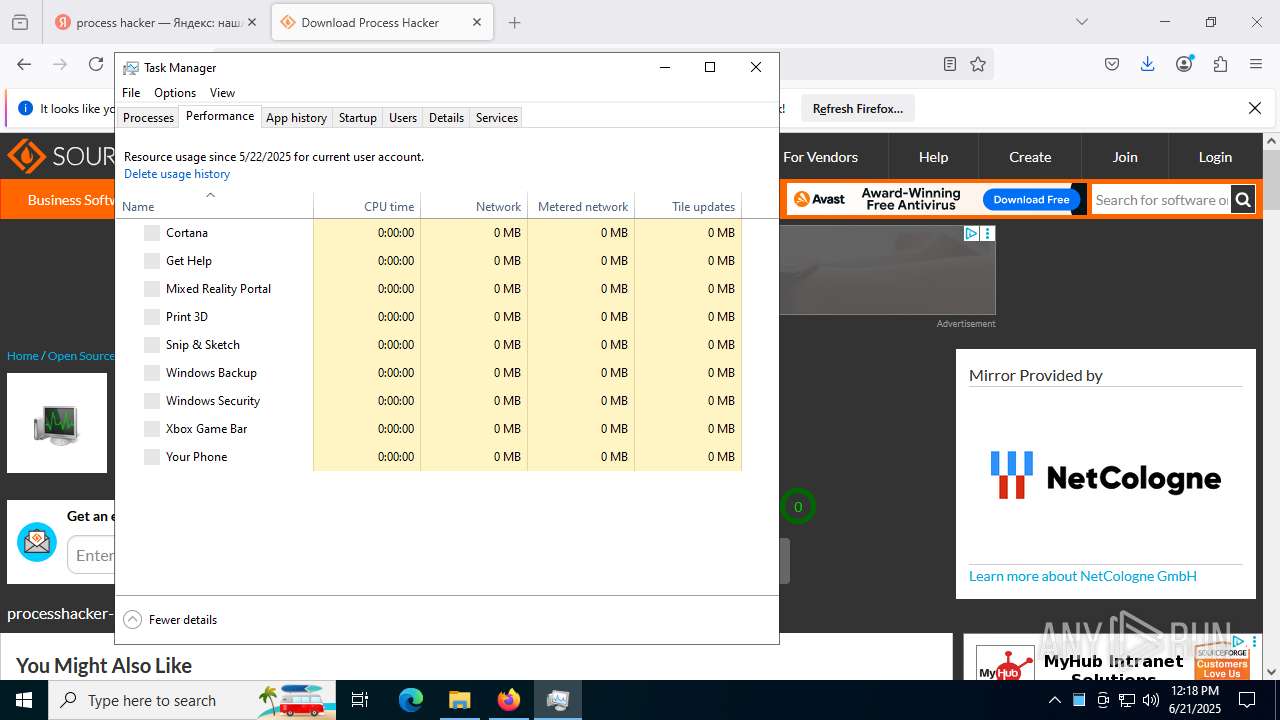
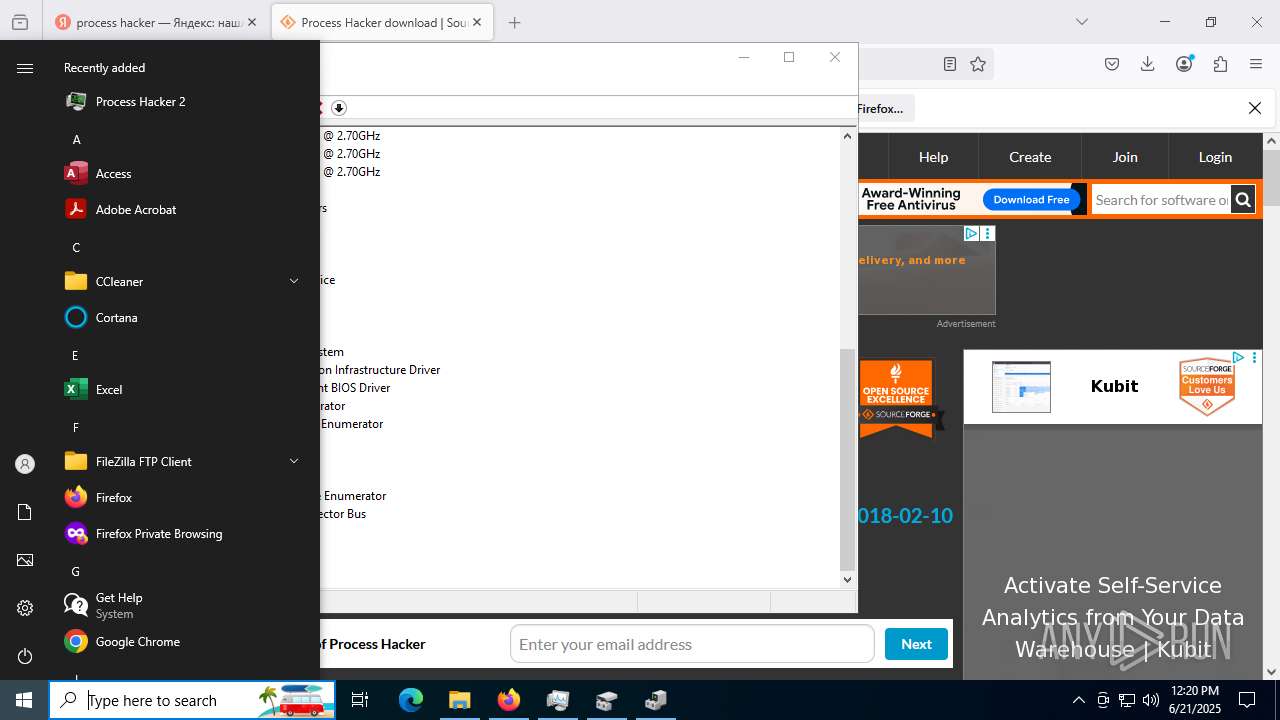
Manual execution by a user
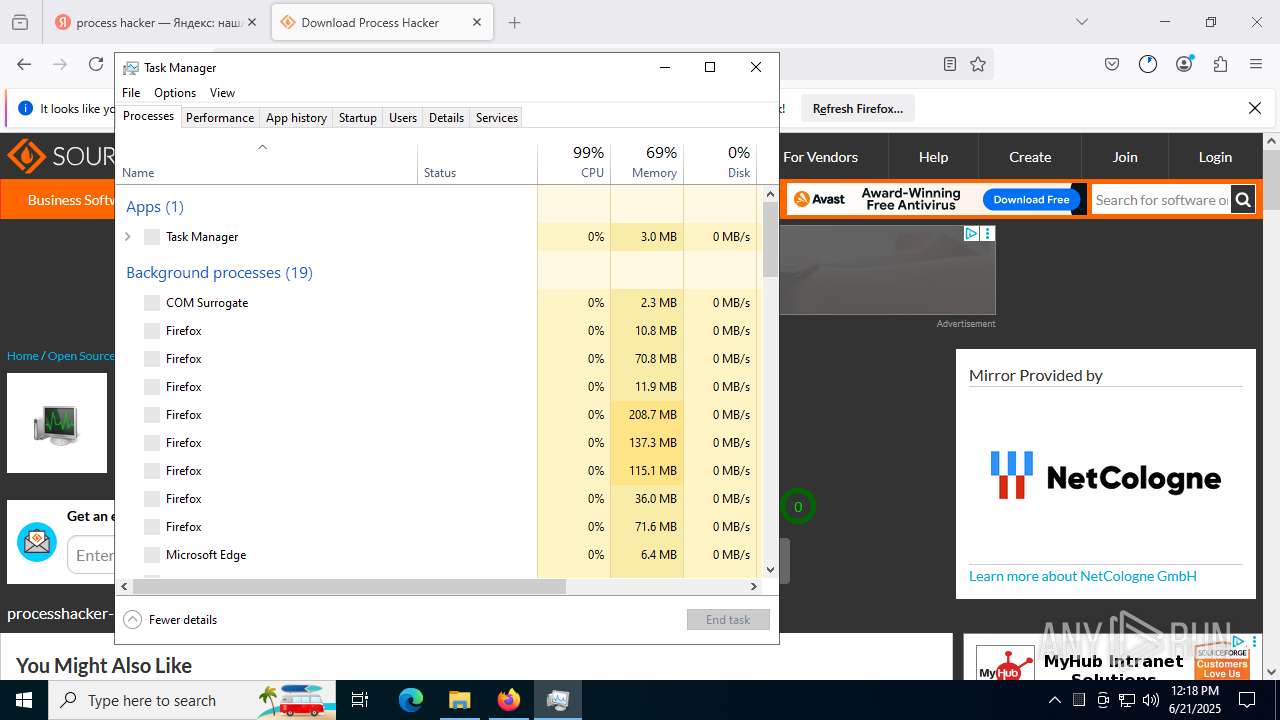
- Taskmgr.exe (PID: 5564)
- Taskmgr.exe (PID: 7488)
- Taskmgr.exe (PID: 2404)
- Taskmgr.exe (PID: 1440)
- mmc.exe (PID: 6796)
- mmc.exe (PID: 1760)
- firefox.exe (PID: 436)
Checks proxy server information
- slui.exe (PID: 6180)
- ProcessHacker.exe (PID: 7464)
Reads Microsoft Office registry keys
- firefox.exe (PID: 7640)
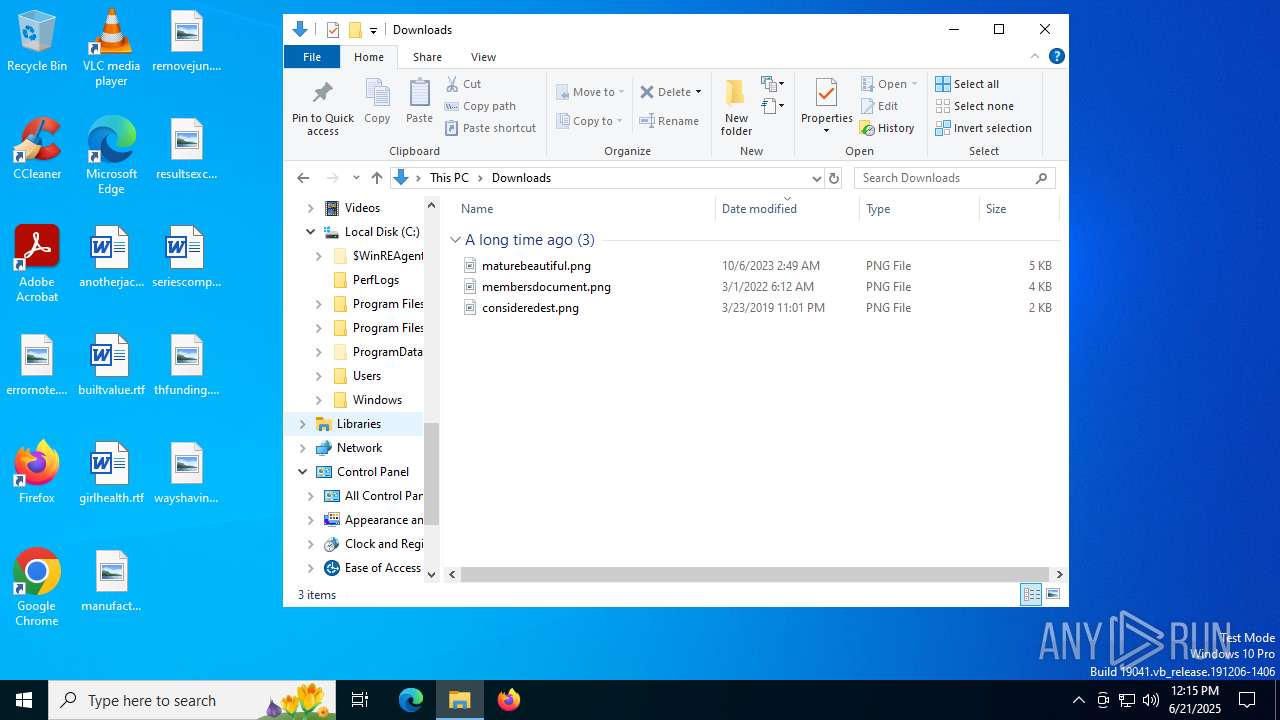
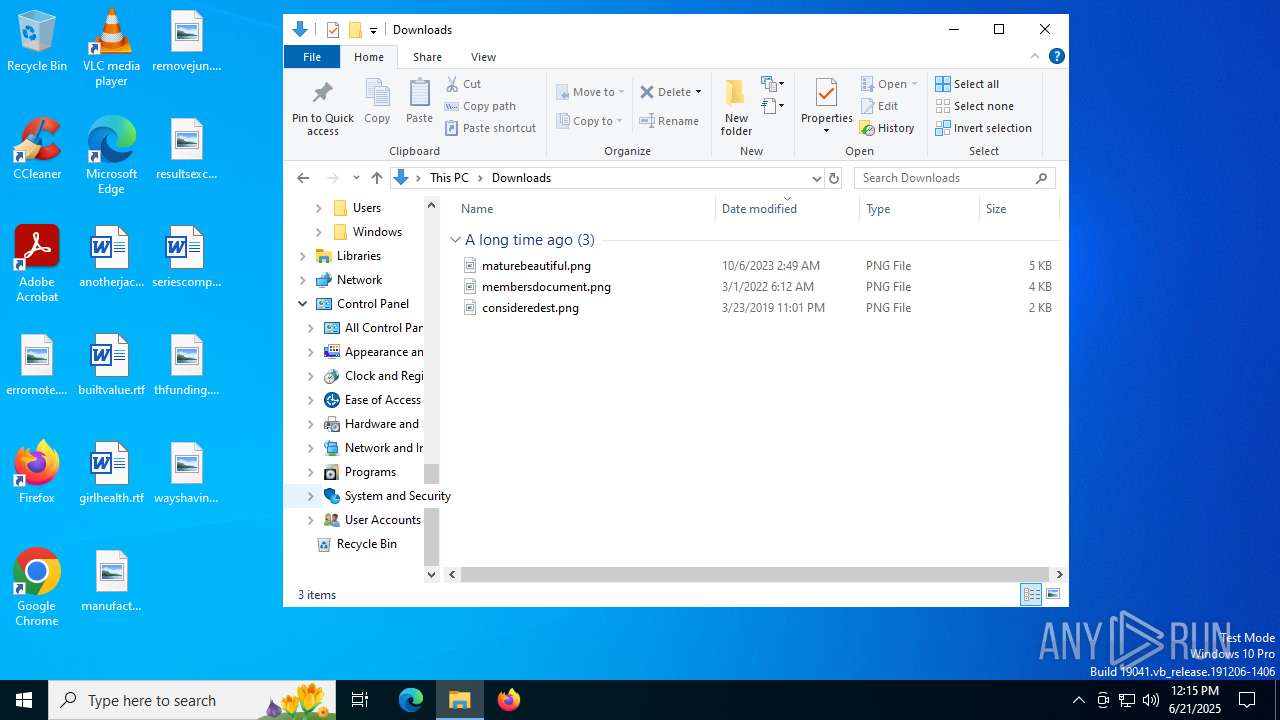
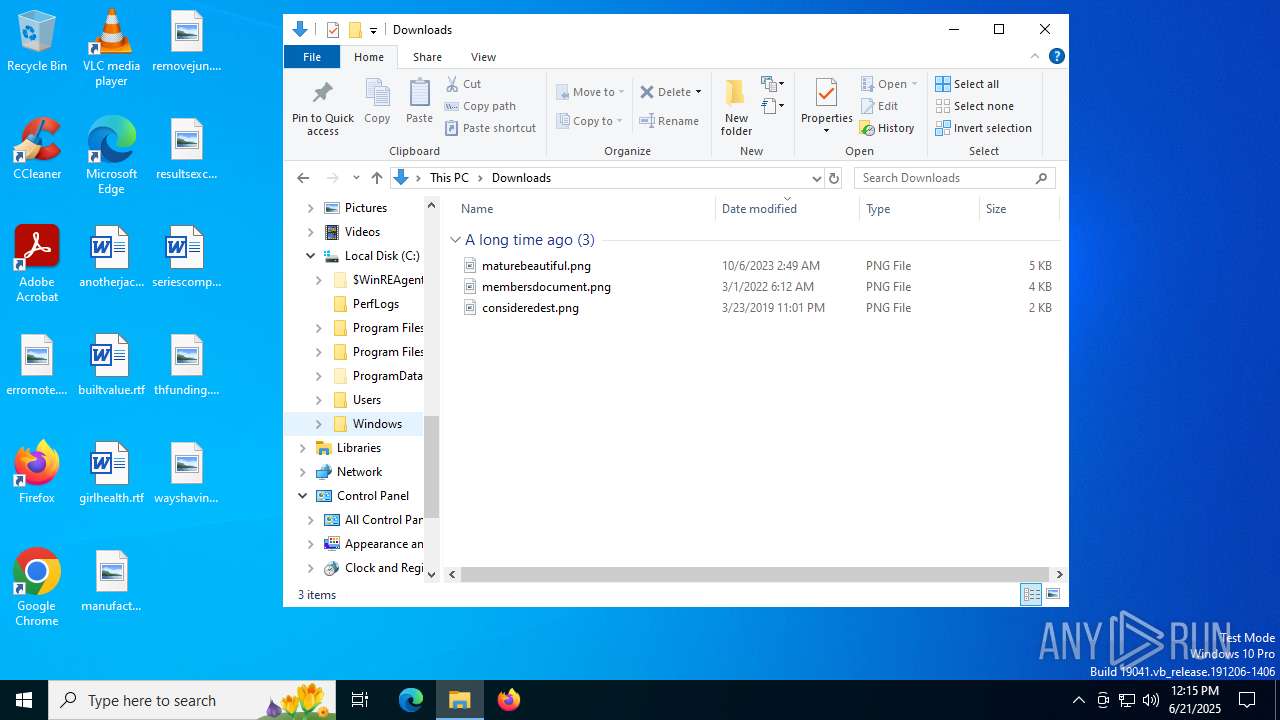
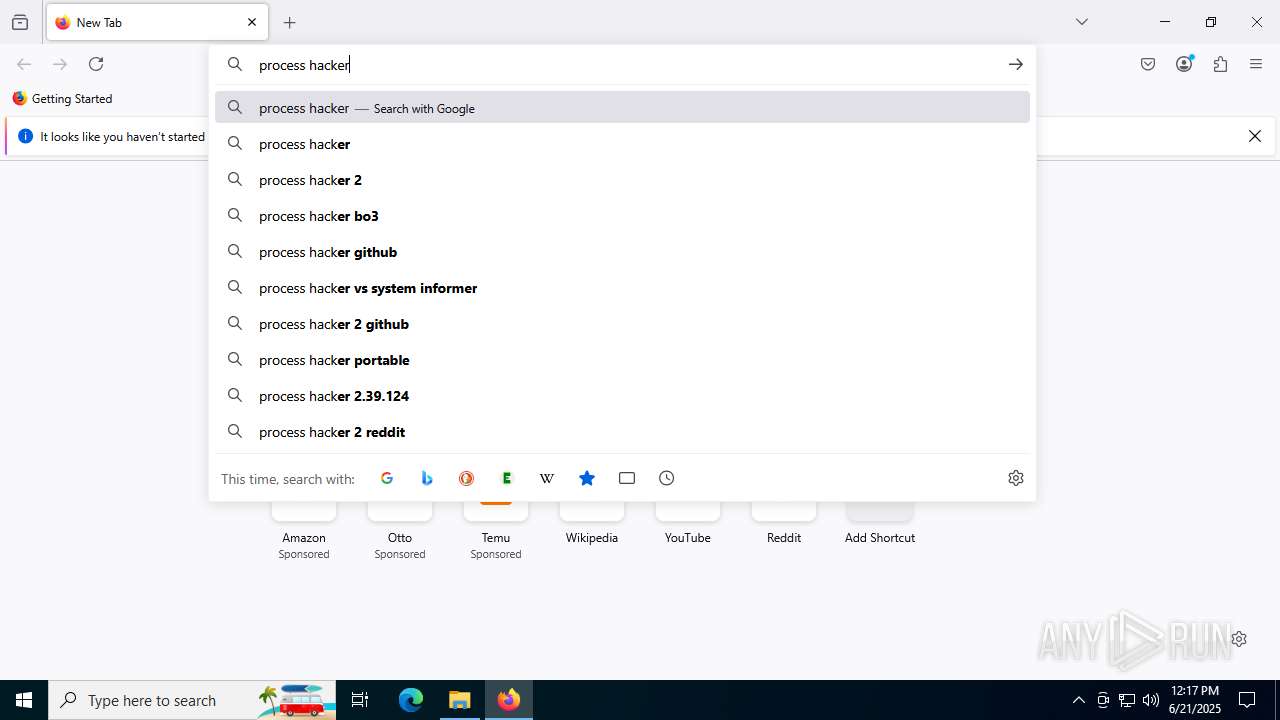
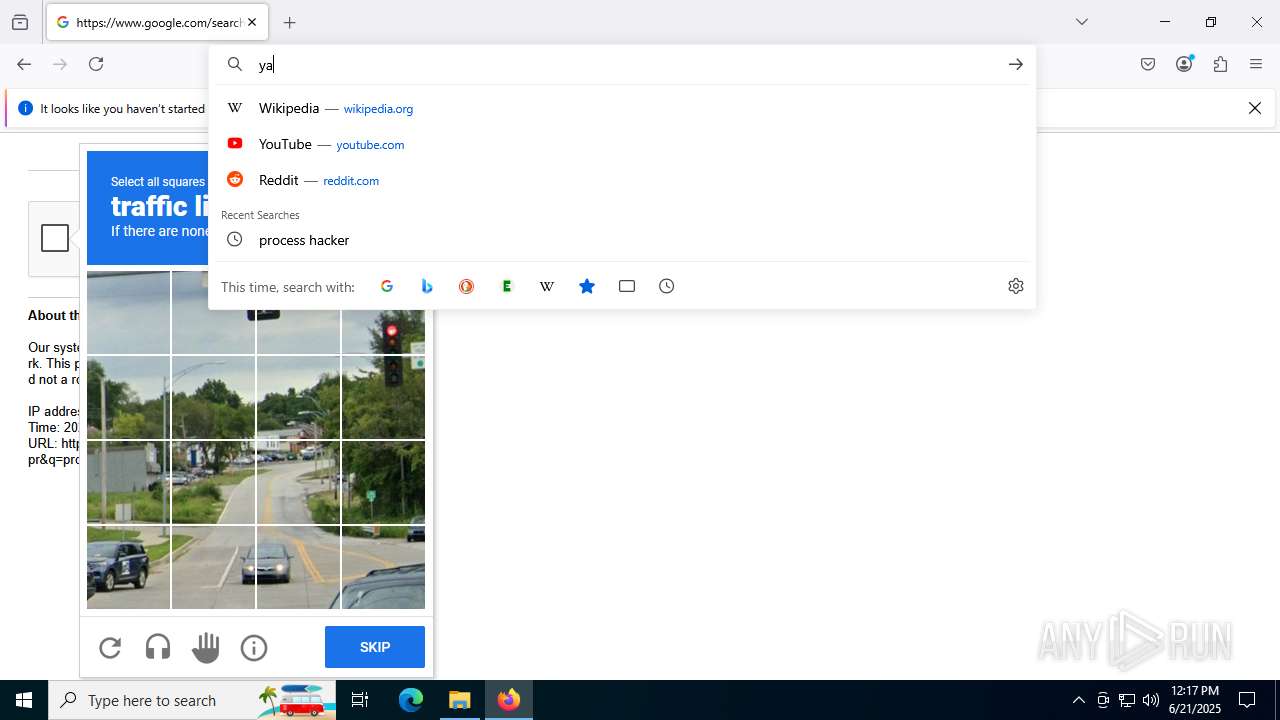
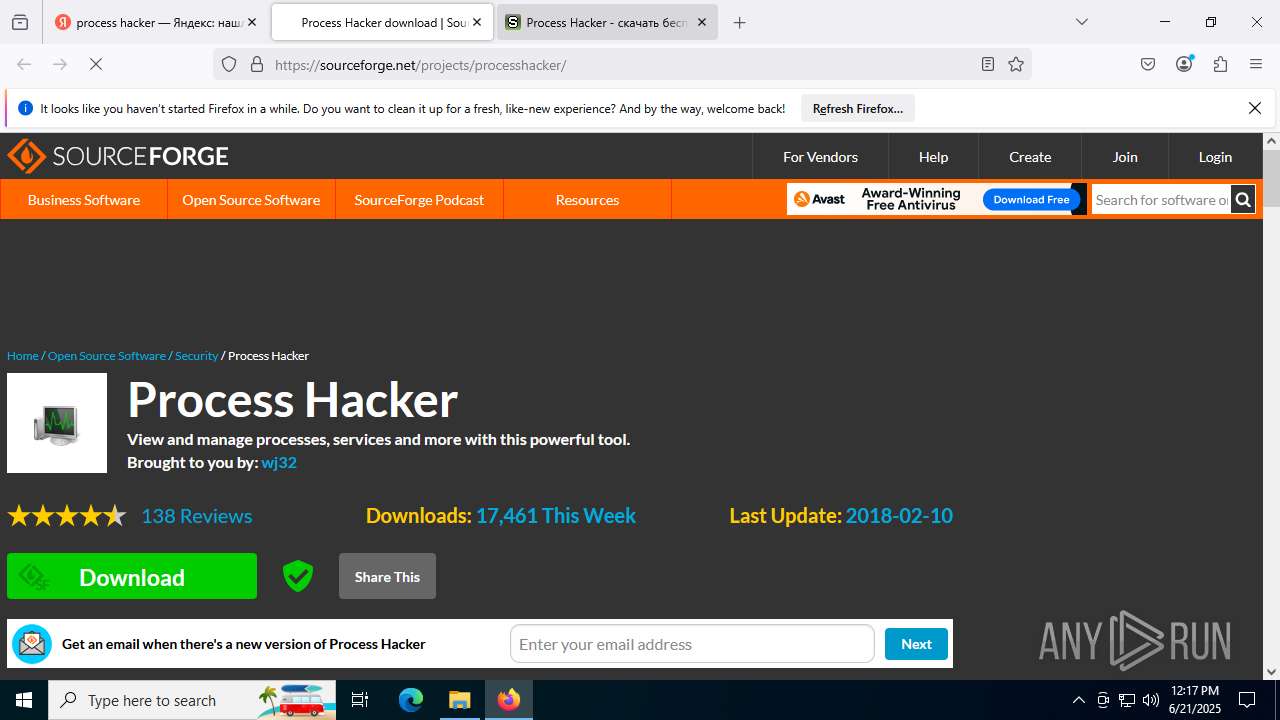
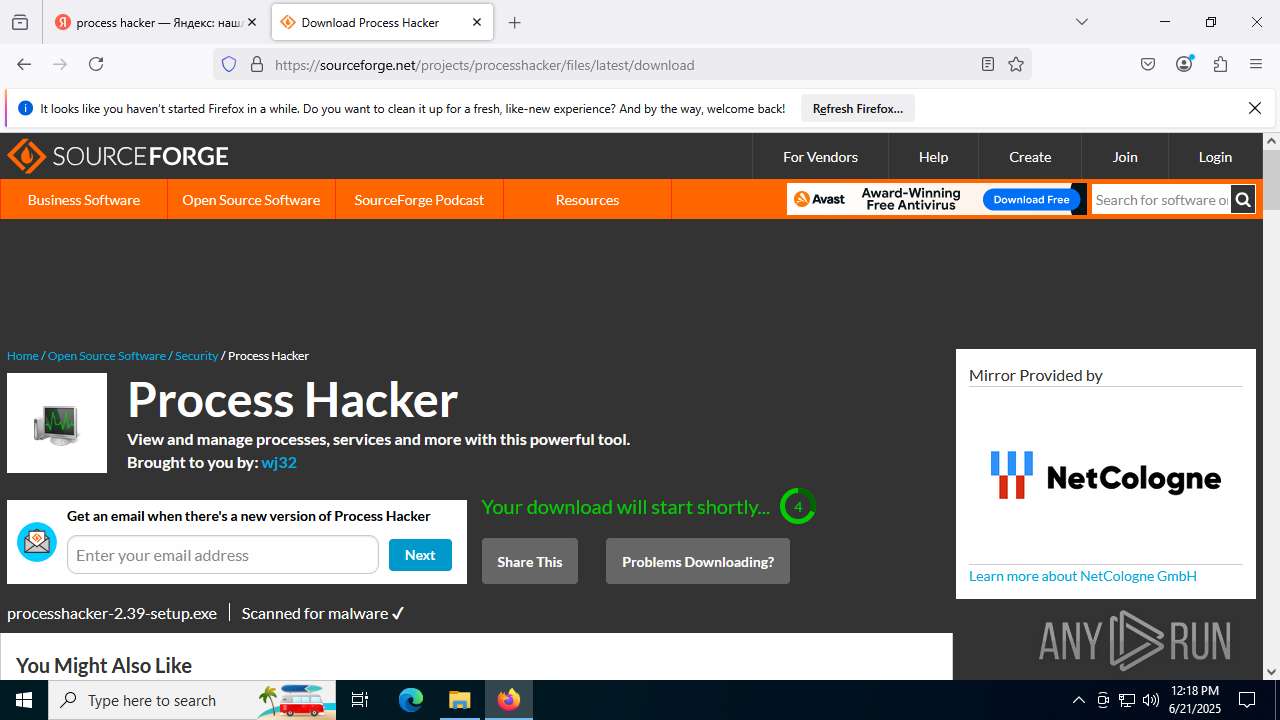
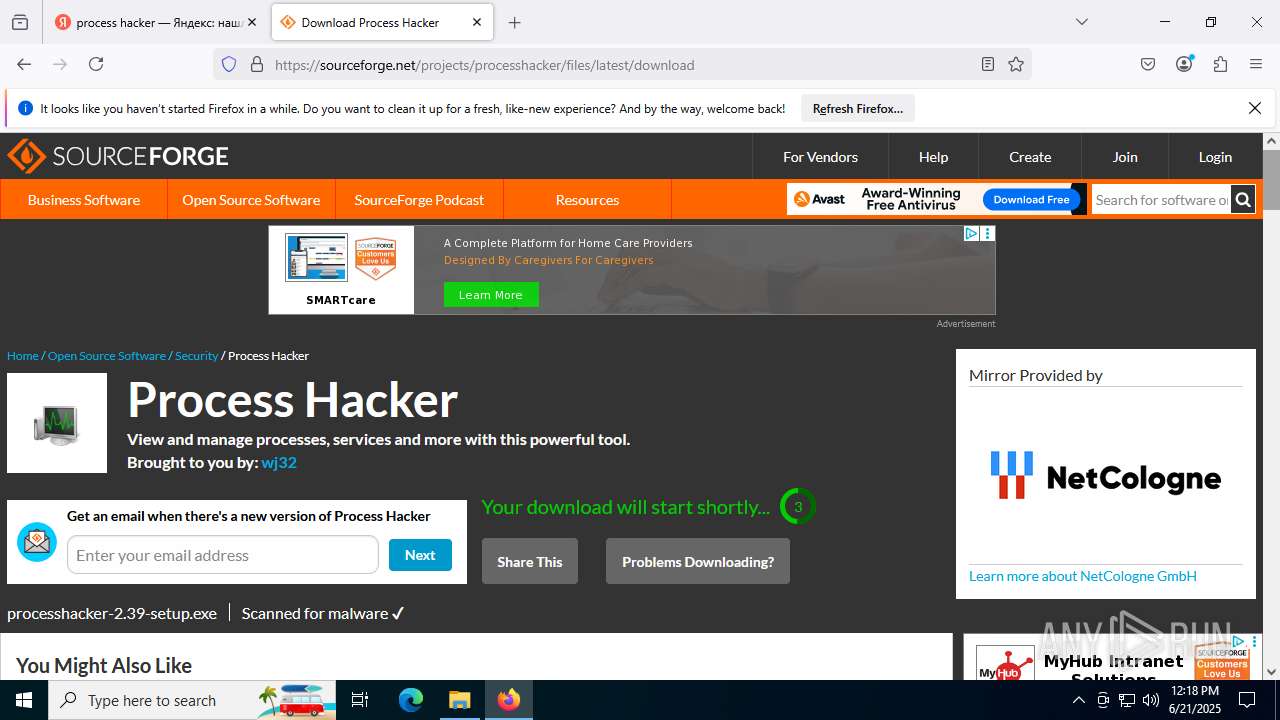
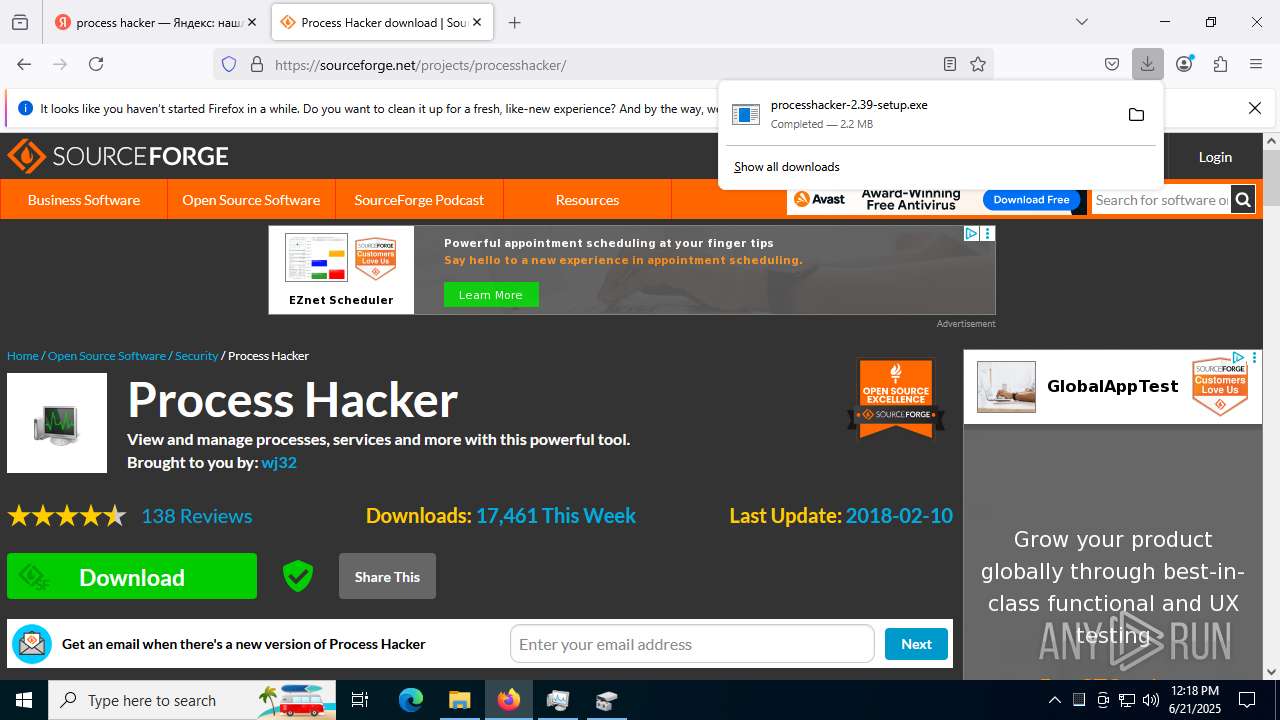
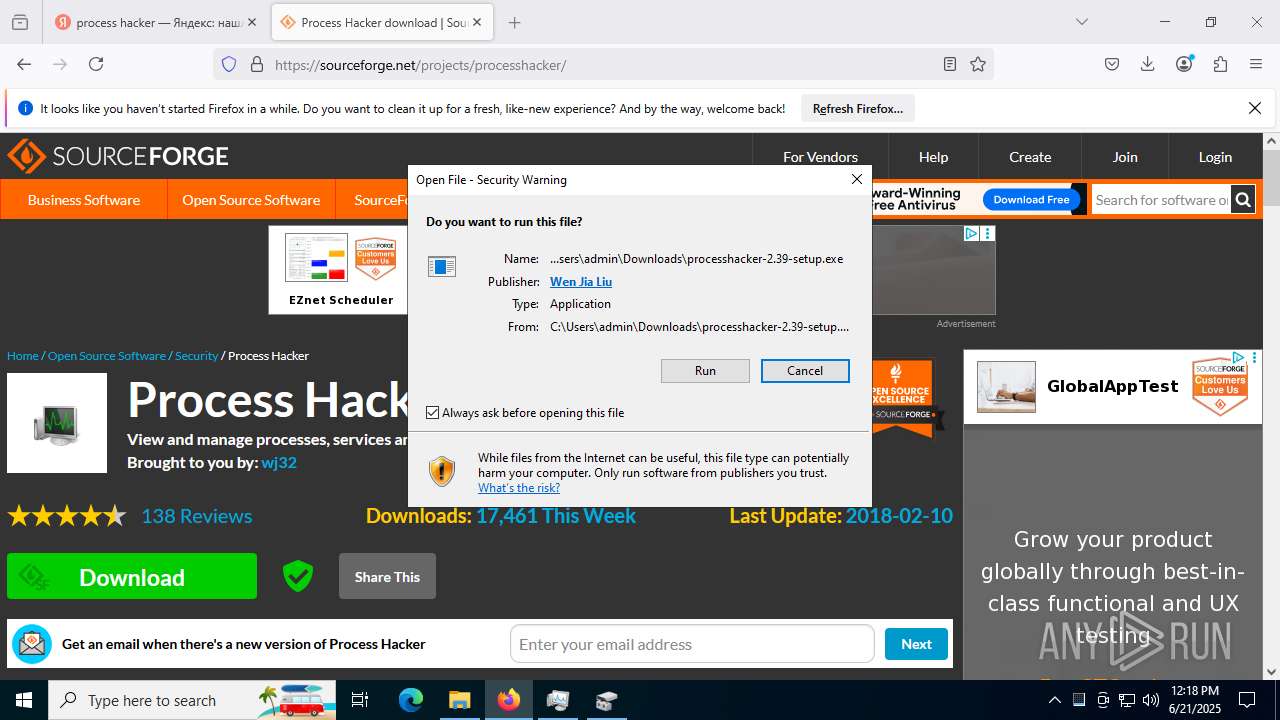
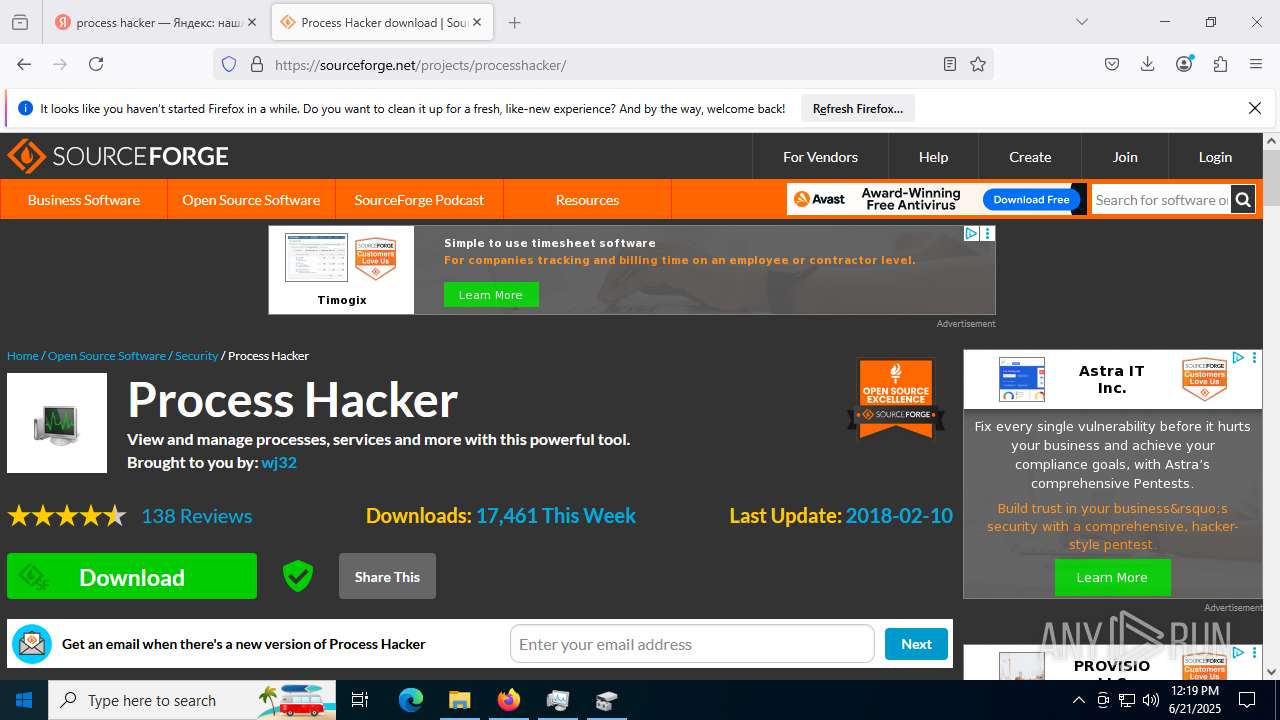
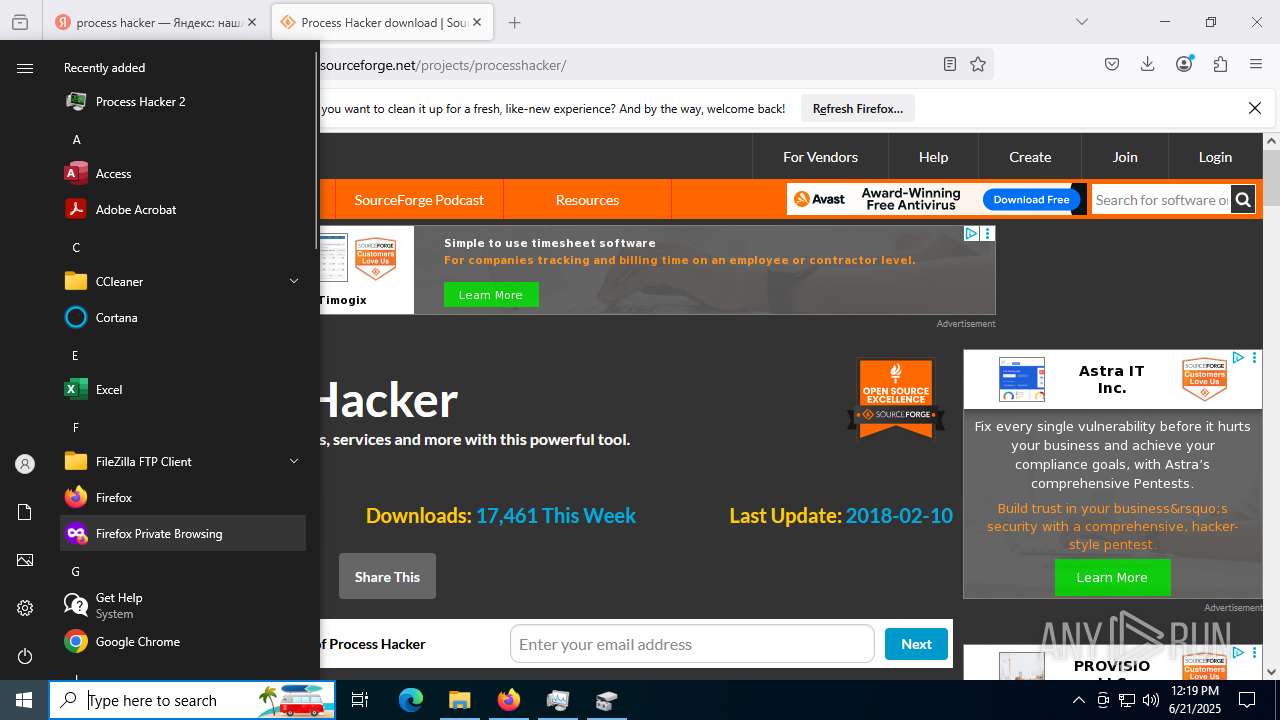
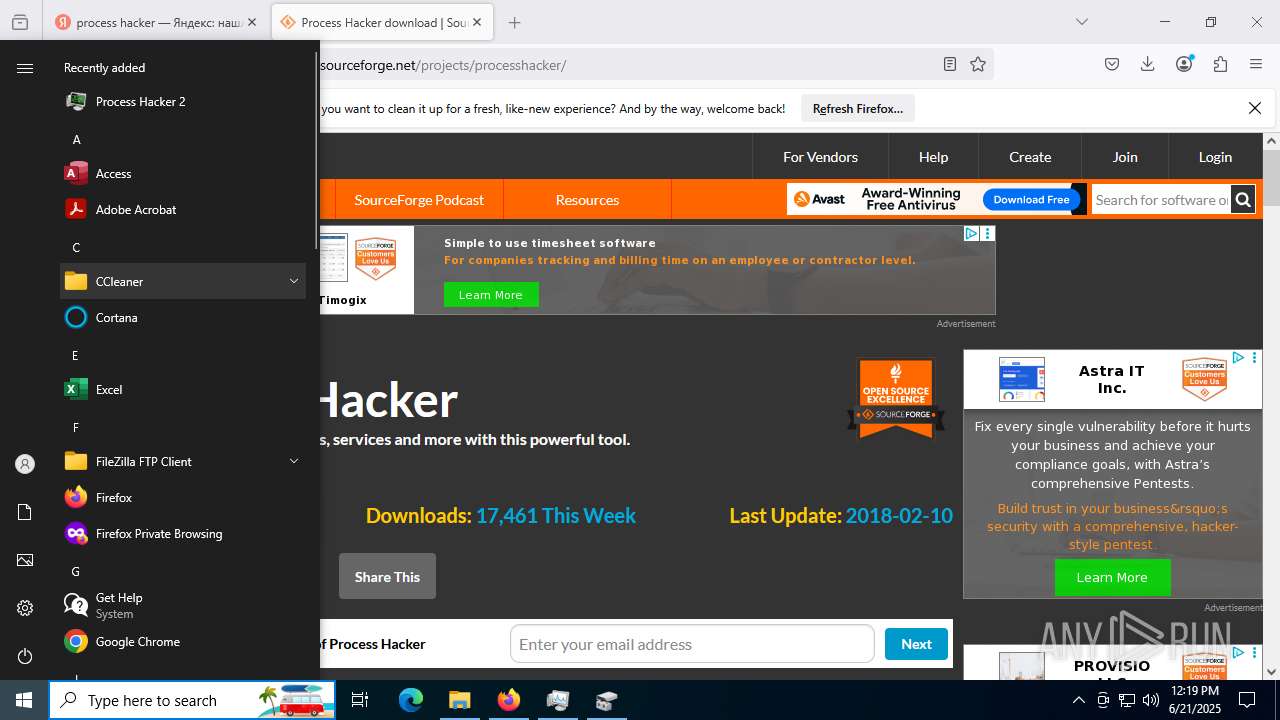
Launching a file from the Downloads directory
- firefox.exe (PID: 7640)
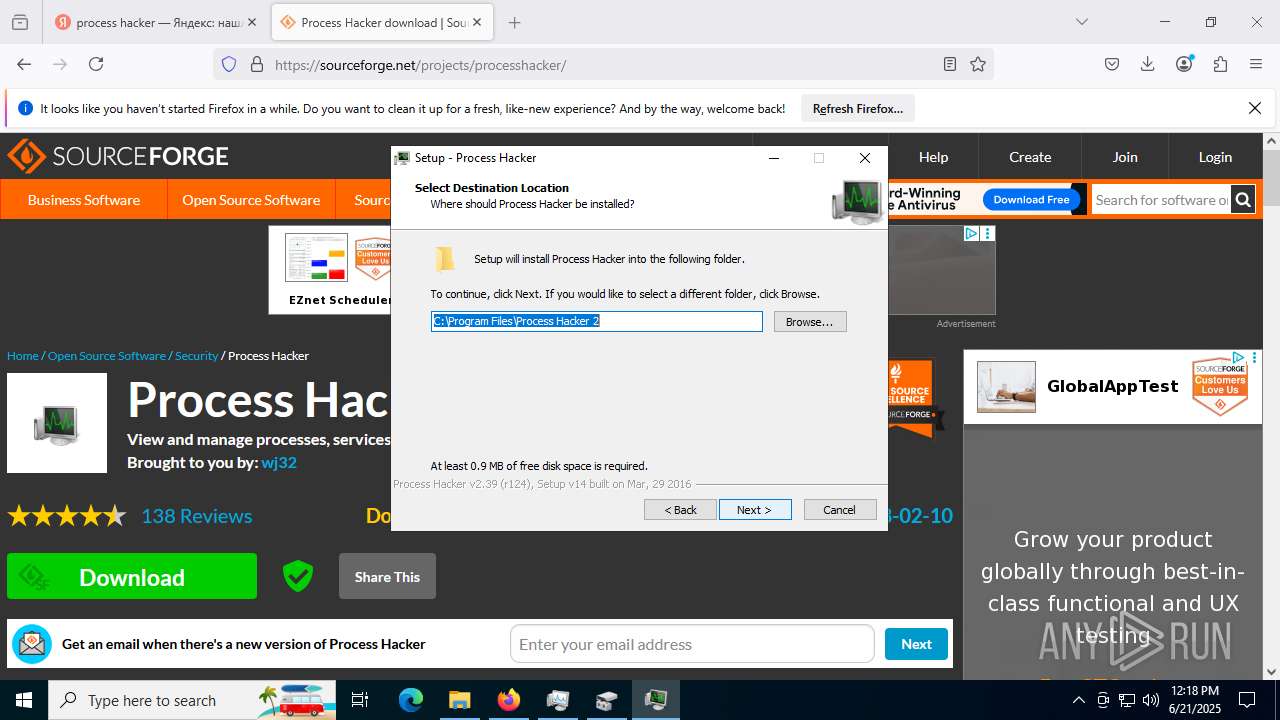
Create files in a temporary directory
- processhacker-2.39-setup.exe (PID: 4916)
- processhacker-2.39-setup.exe (PID: 2396)
- processhacker-2.39-setup.tmp (PID: 8460)
Executable content was dropped or overwritten
- firefox.exe (PID: 7640)
Process checks computer location settings
- processhacker-2.39-setup.tmp (PID: 6572)
PROCESSHACKER mutex has been found
- processhacker-2.39-setup.tmp (PID: 8460)
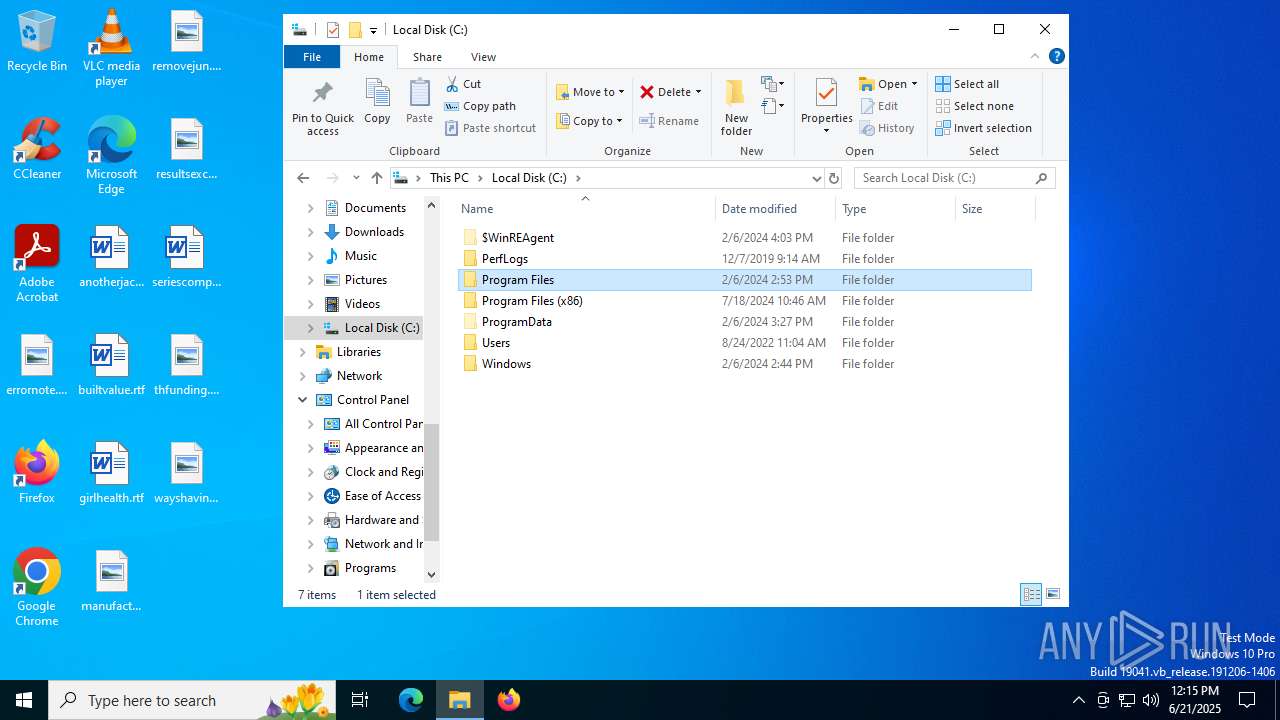
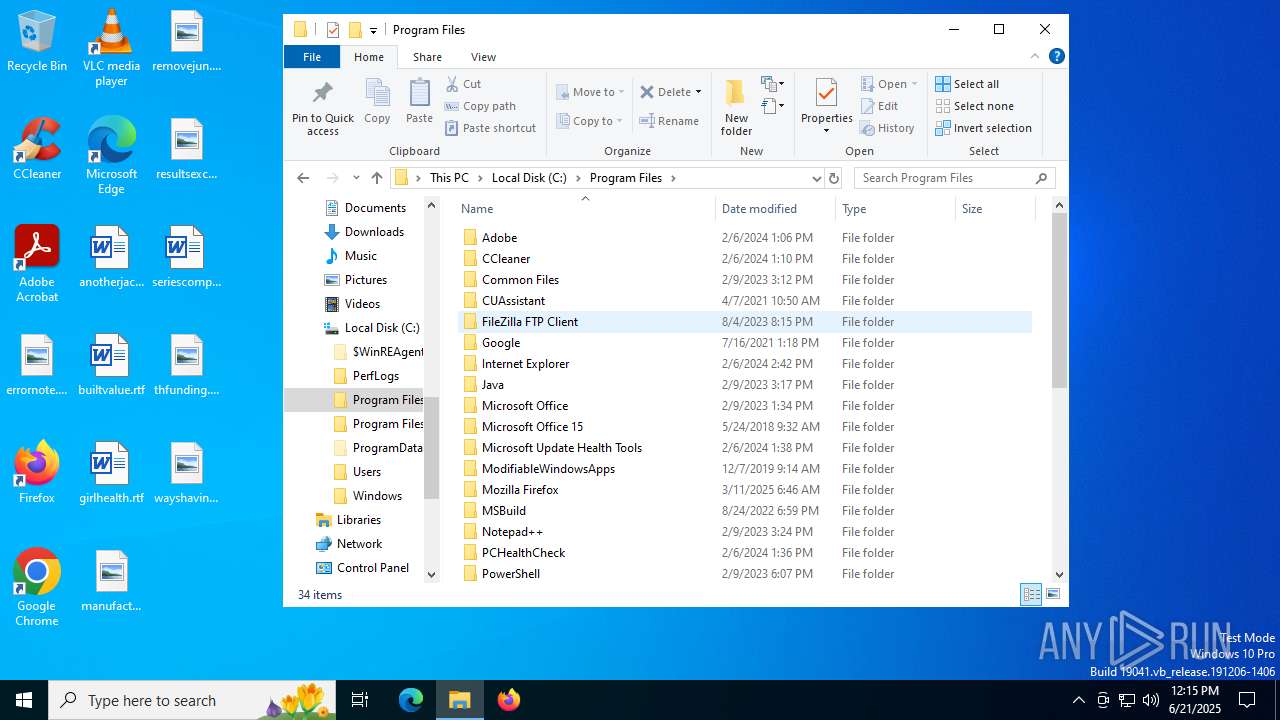
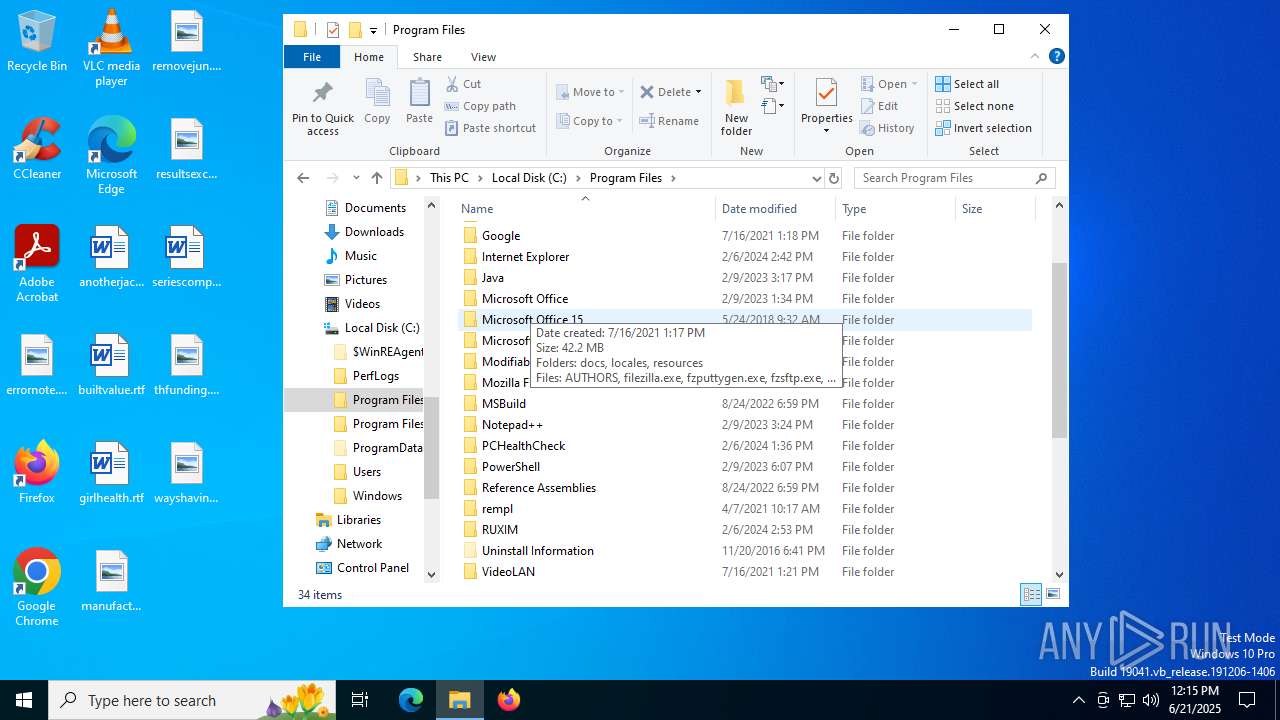
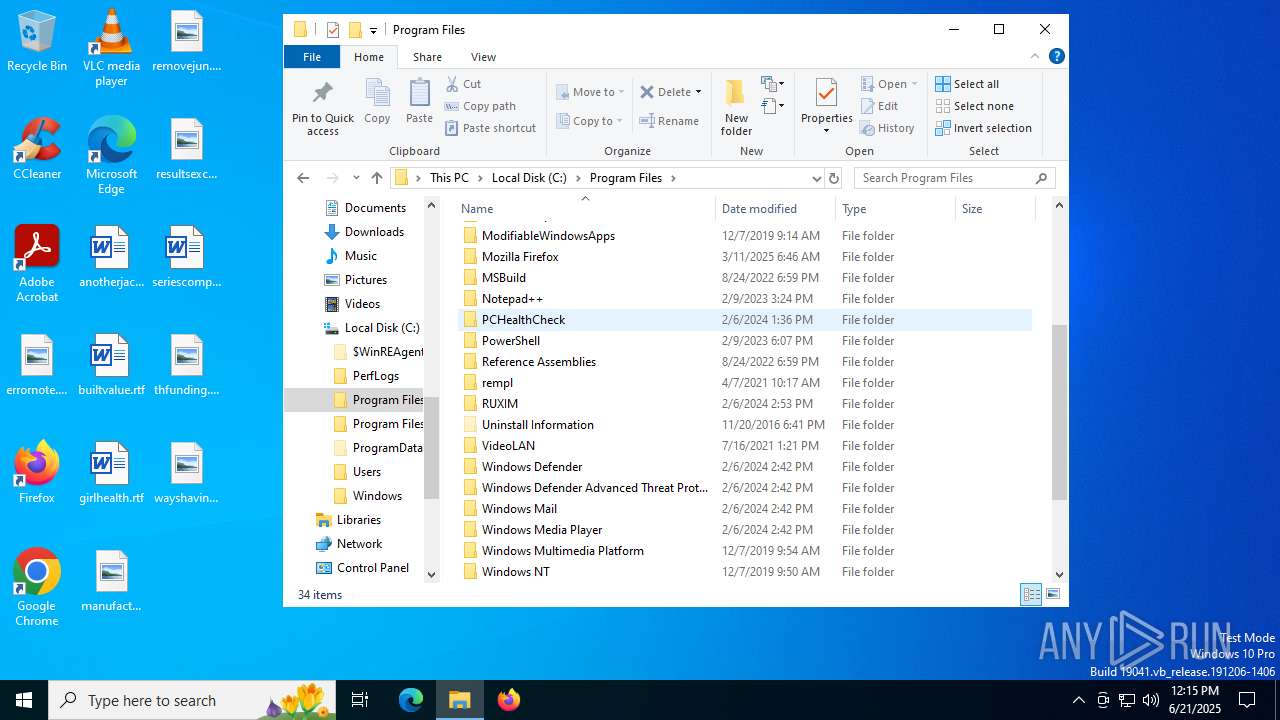
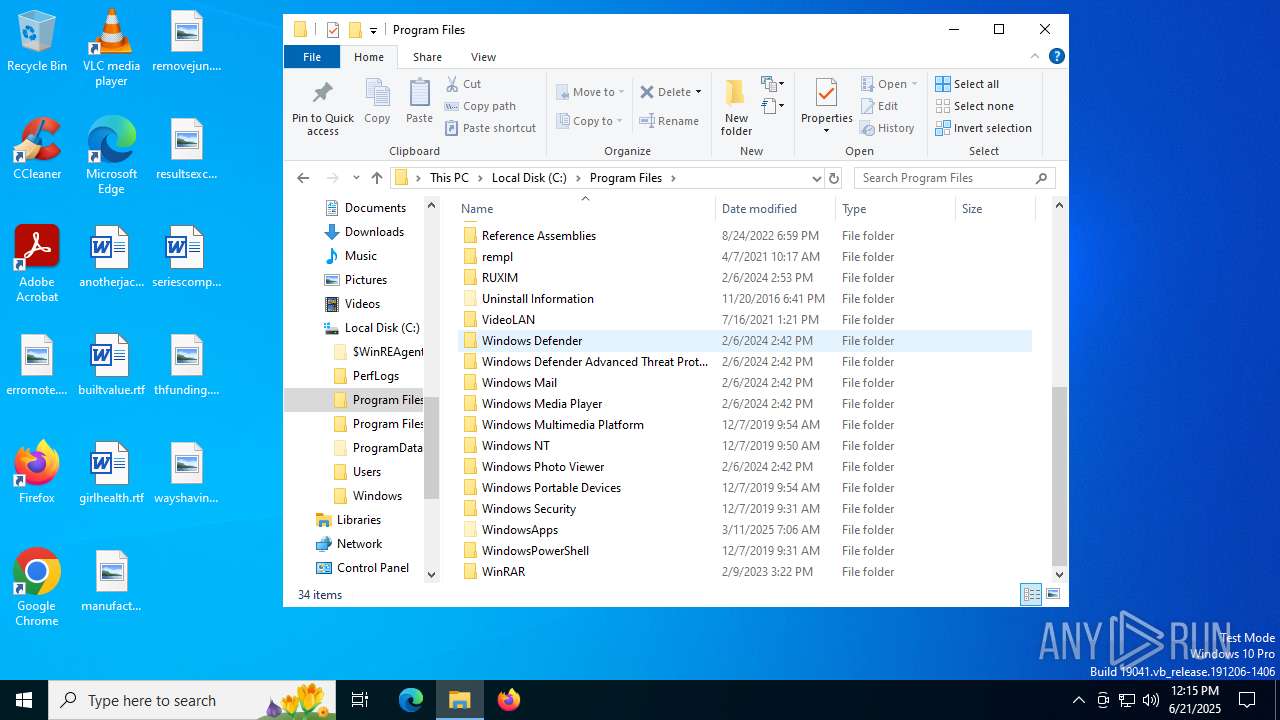
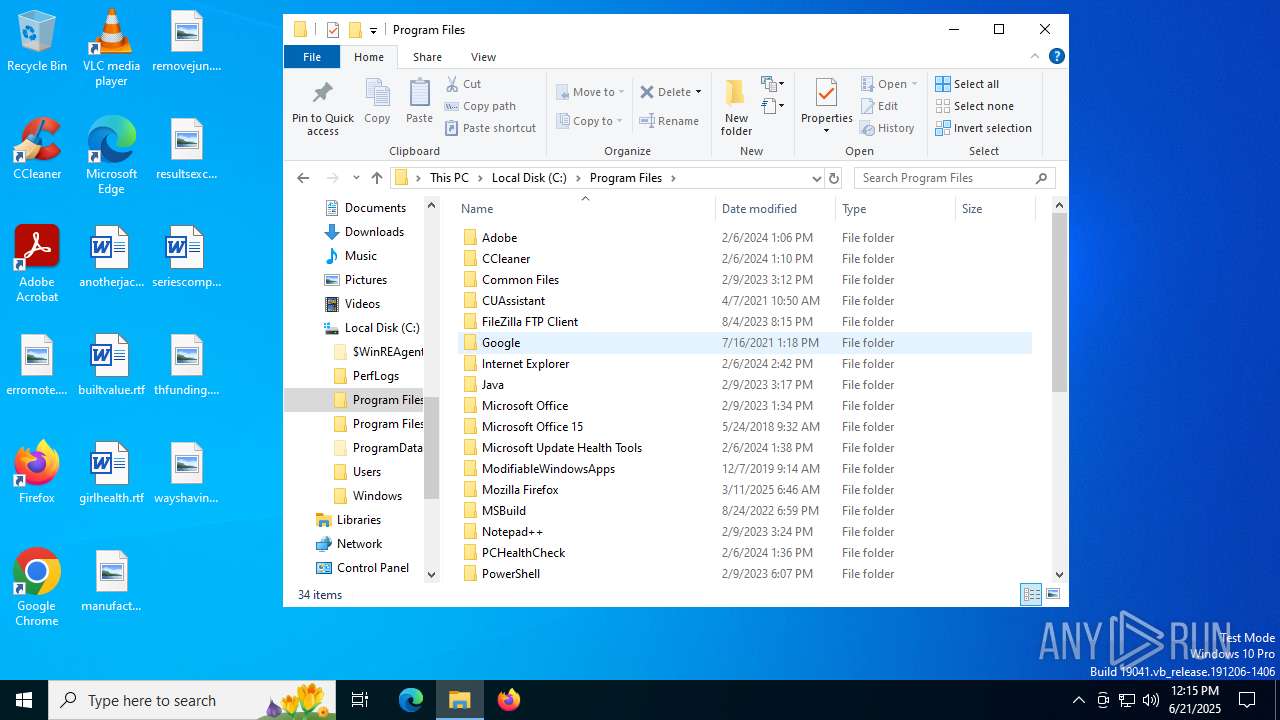
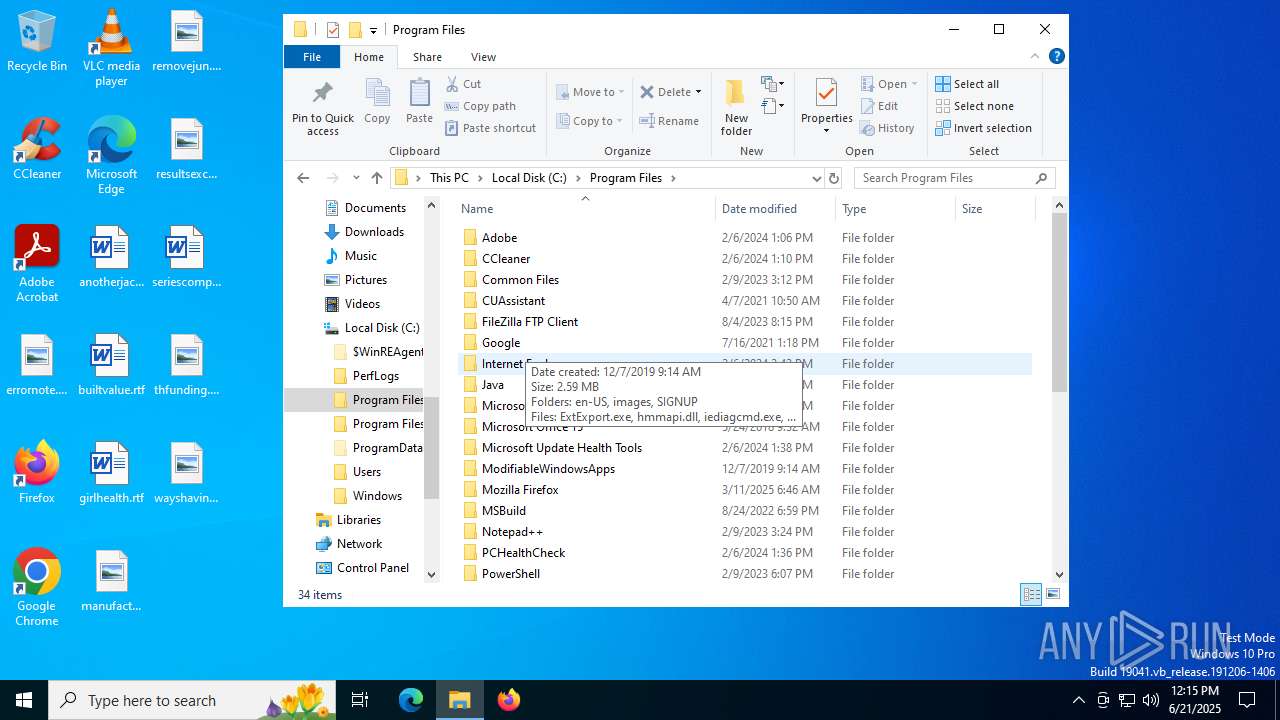
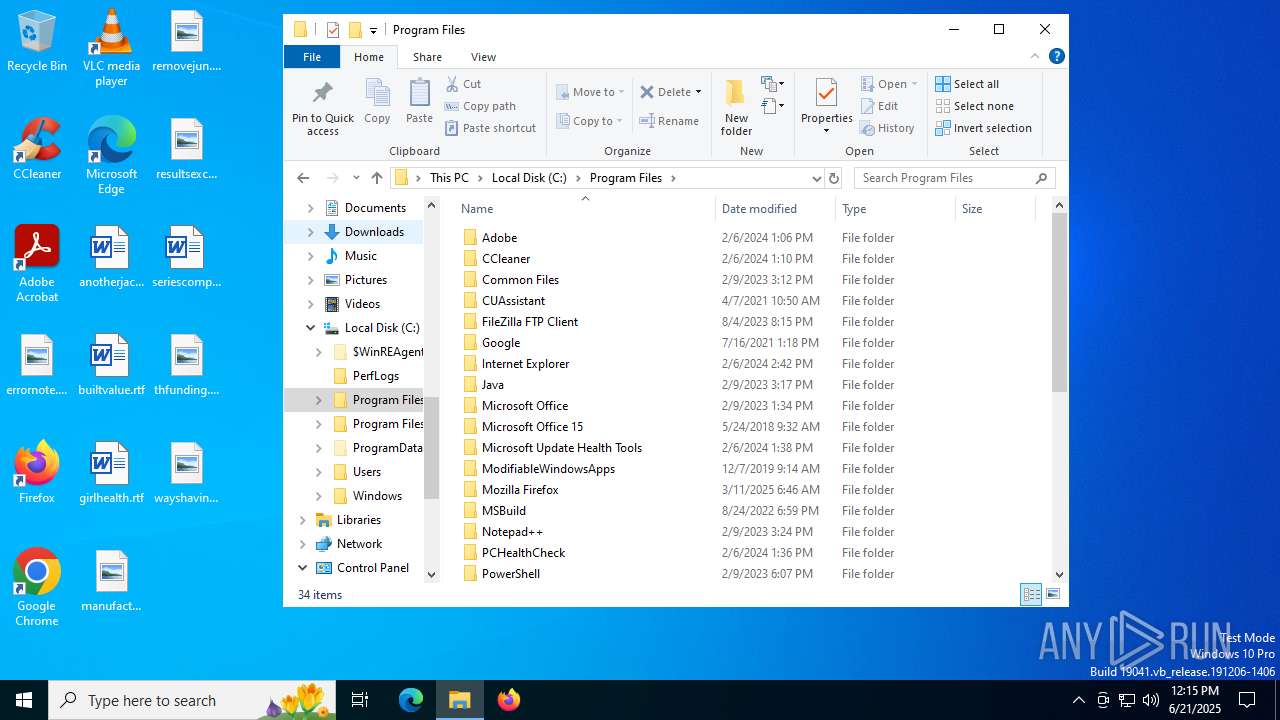
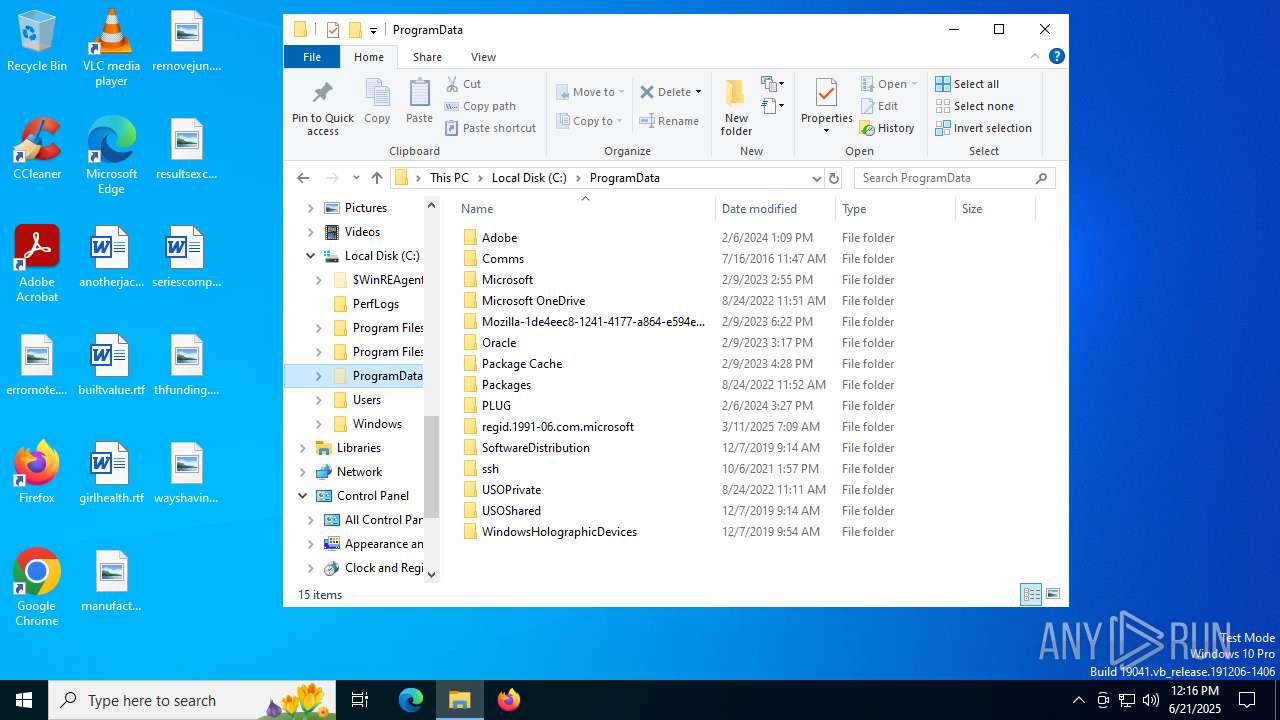
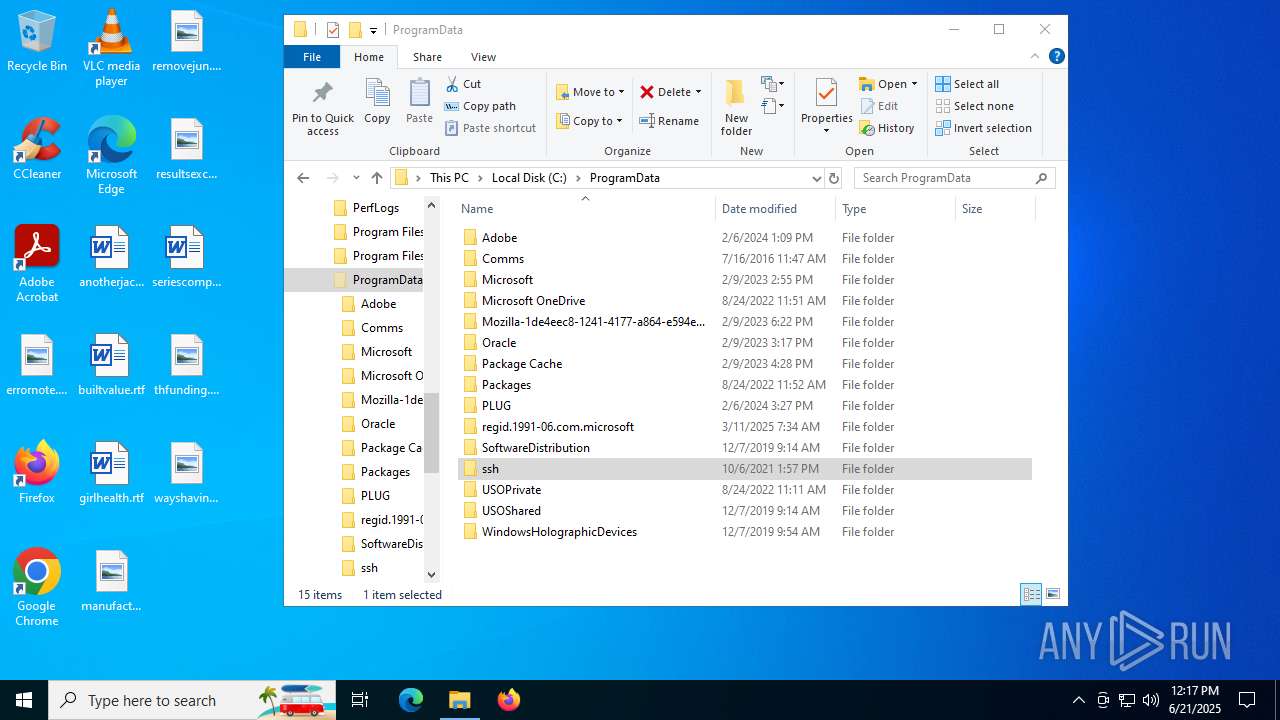
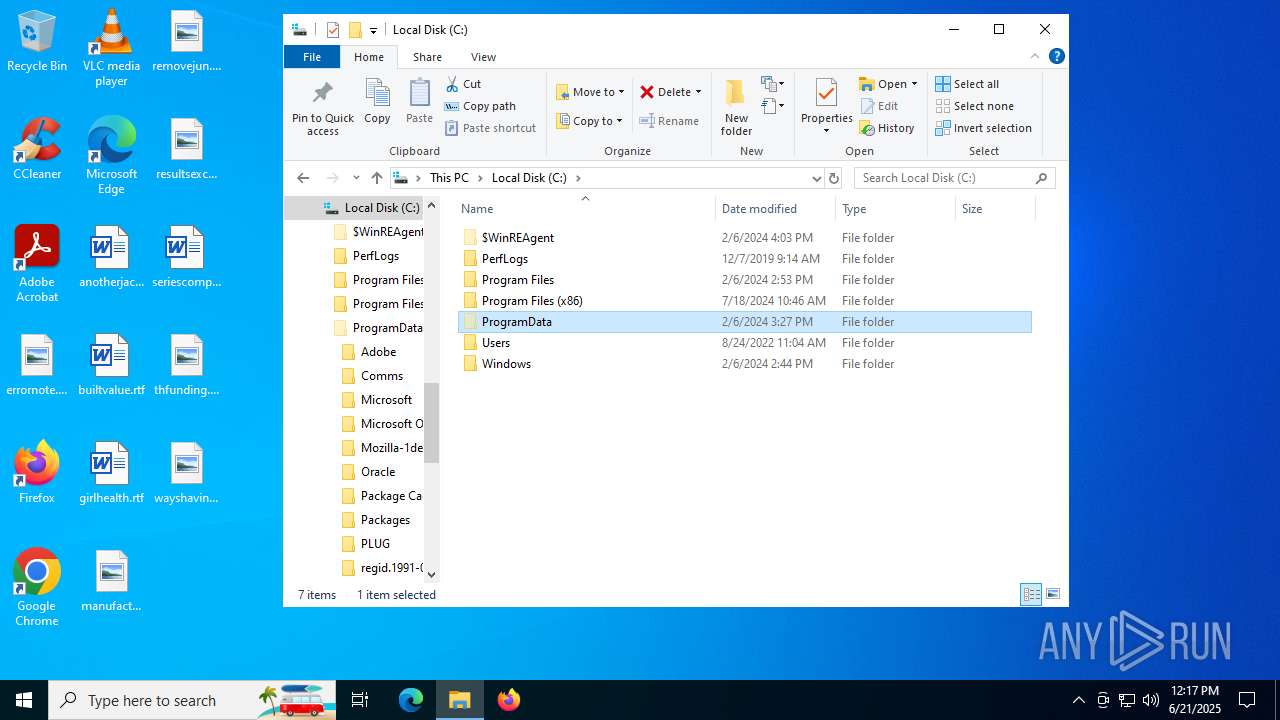
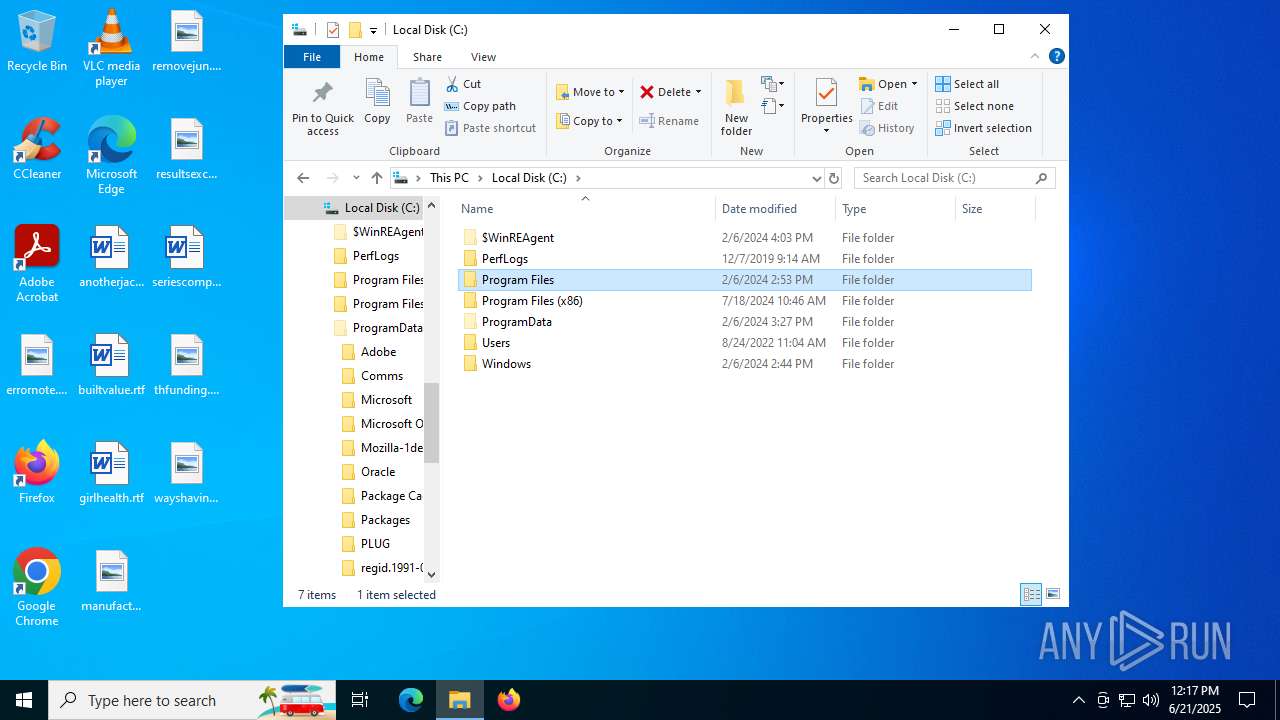
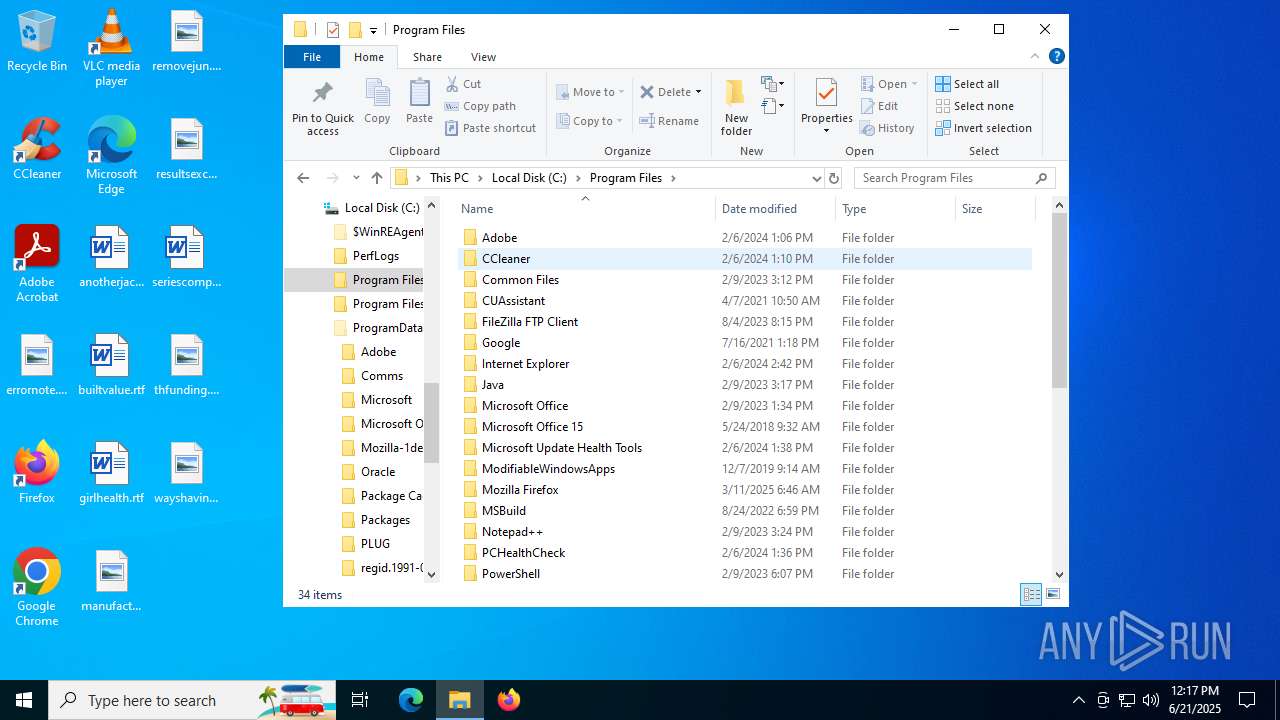
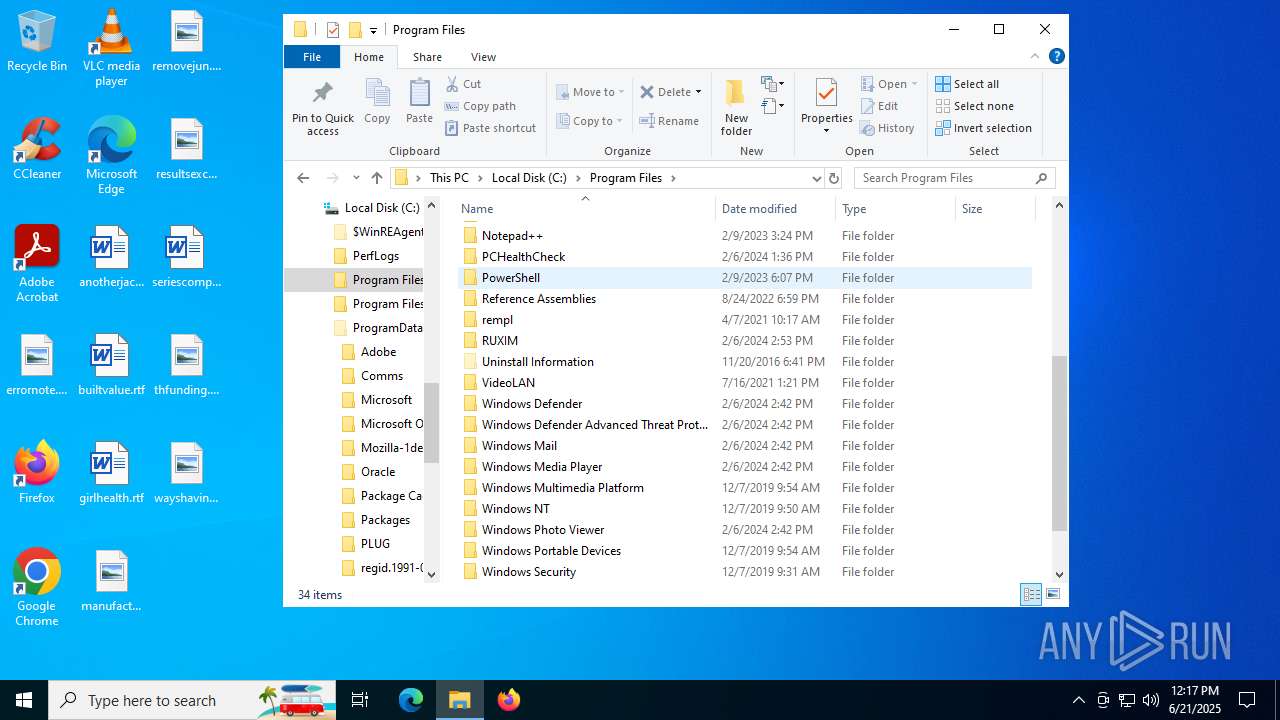
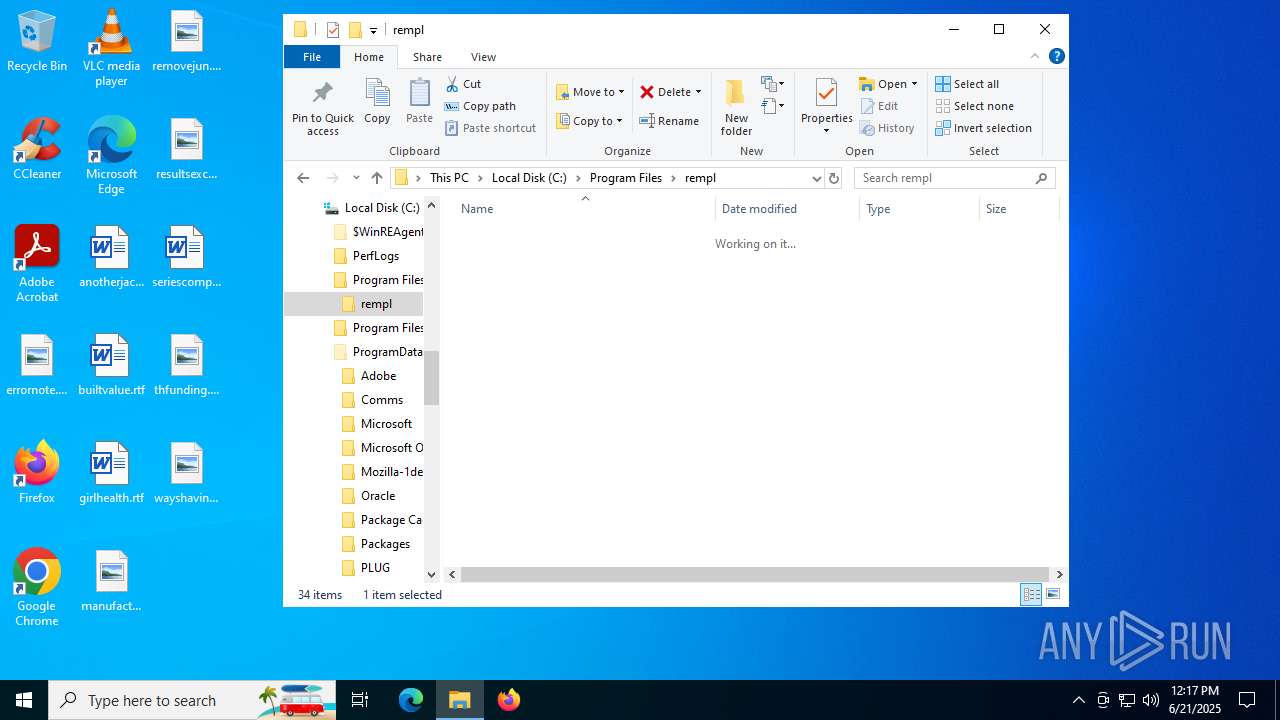
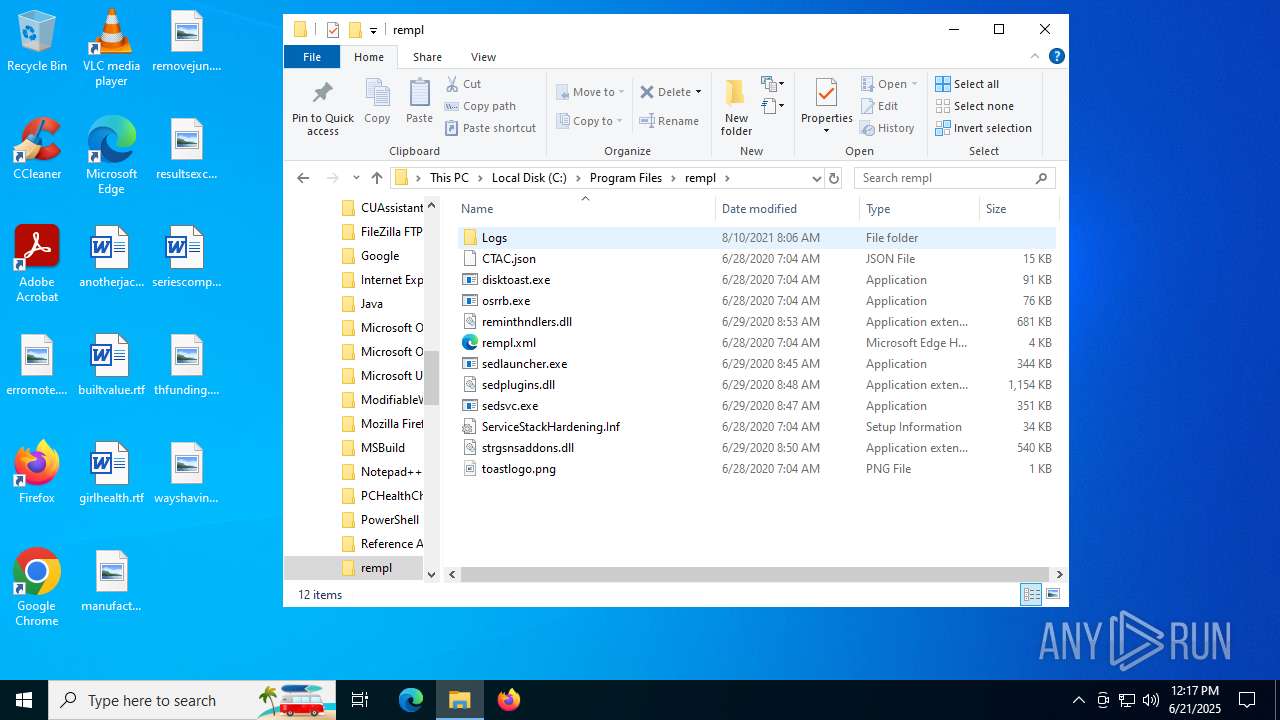
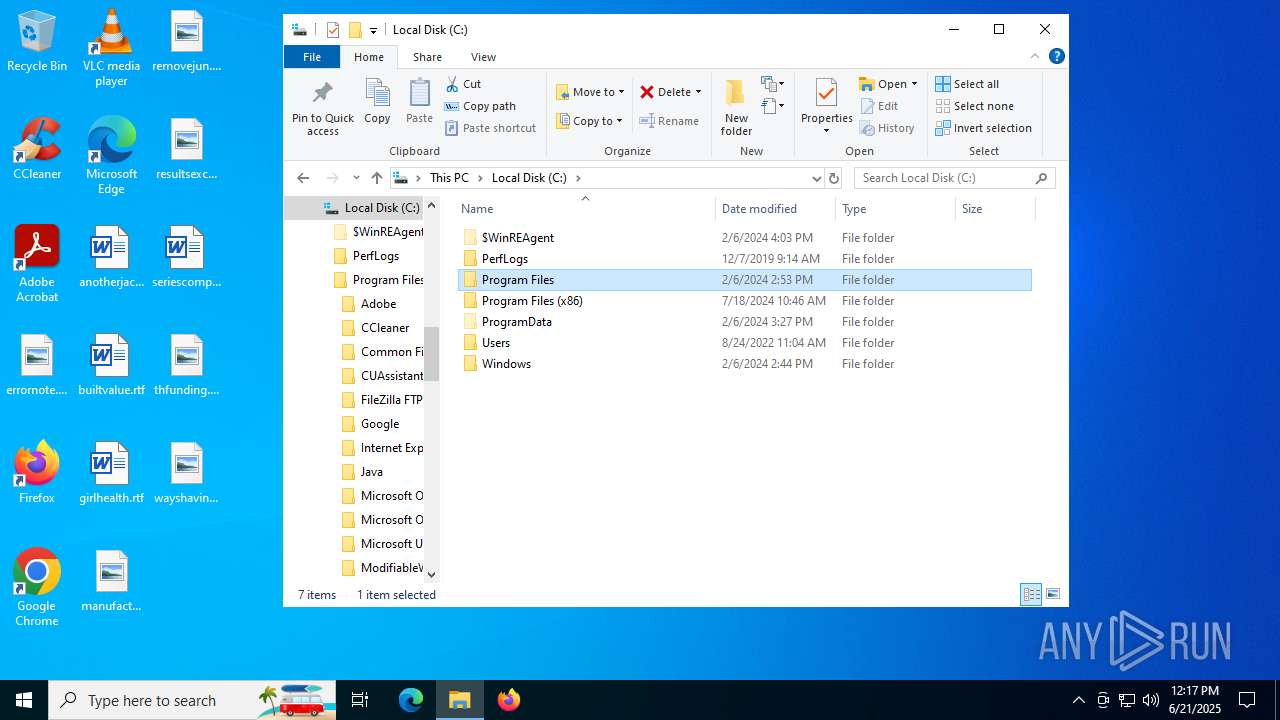
Creates files in the program directory
- processhacker-2.39-setup.tmp (PID: 8460)
Creates a software uninstall entry
- processhacker-2.39-setup.tmp (PID: 8460)
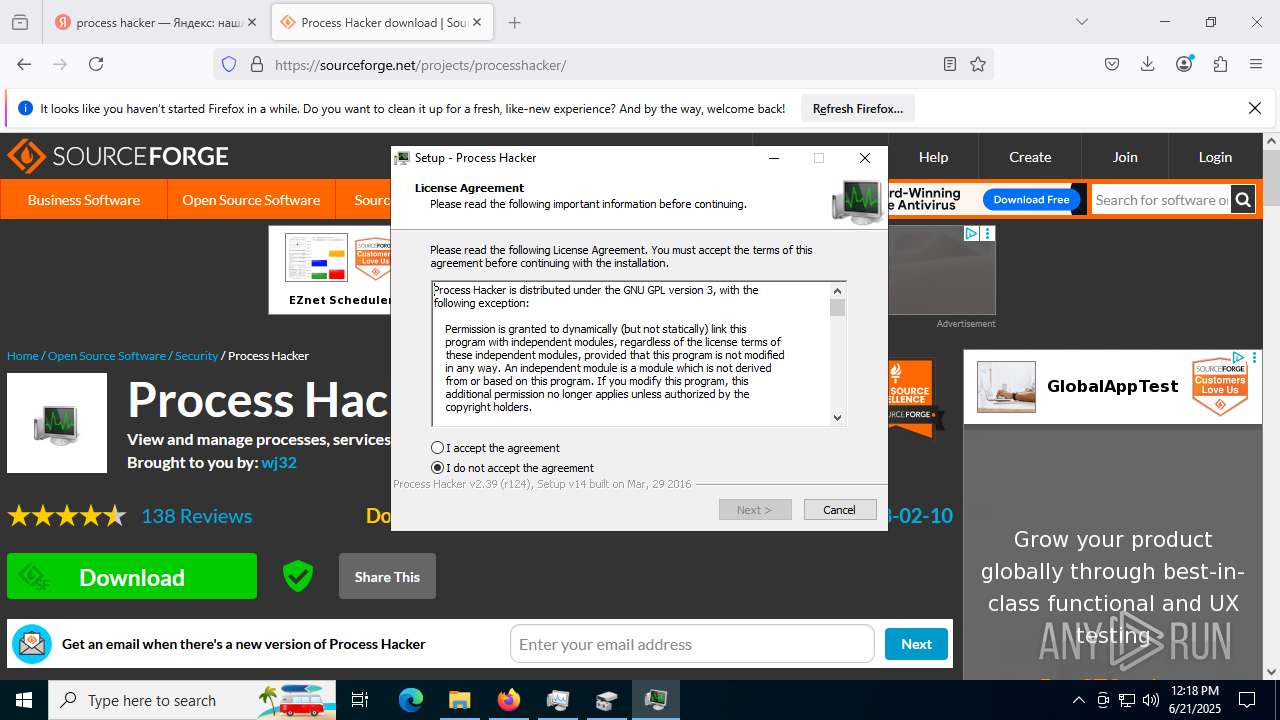
The sample compiled with english language support
- processhacker-2.39-setup.tmp (PID: 8460)
Reads the machine GUID from the registry
- ProcessHacker.exe (PID: 7464)
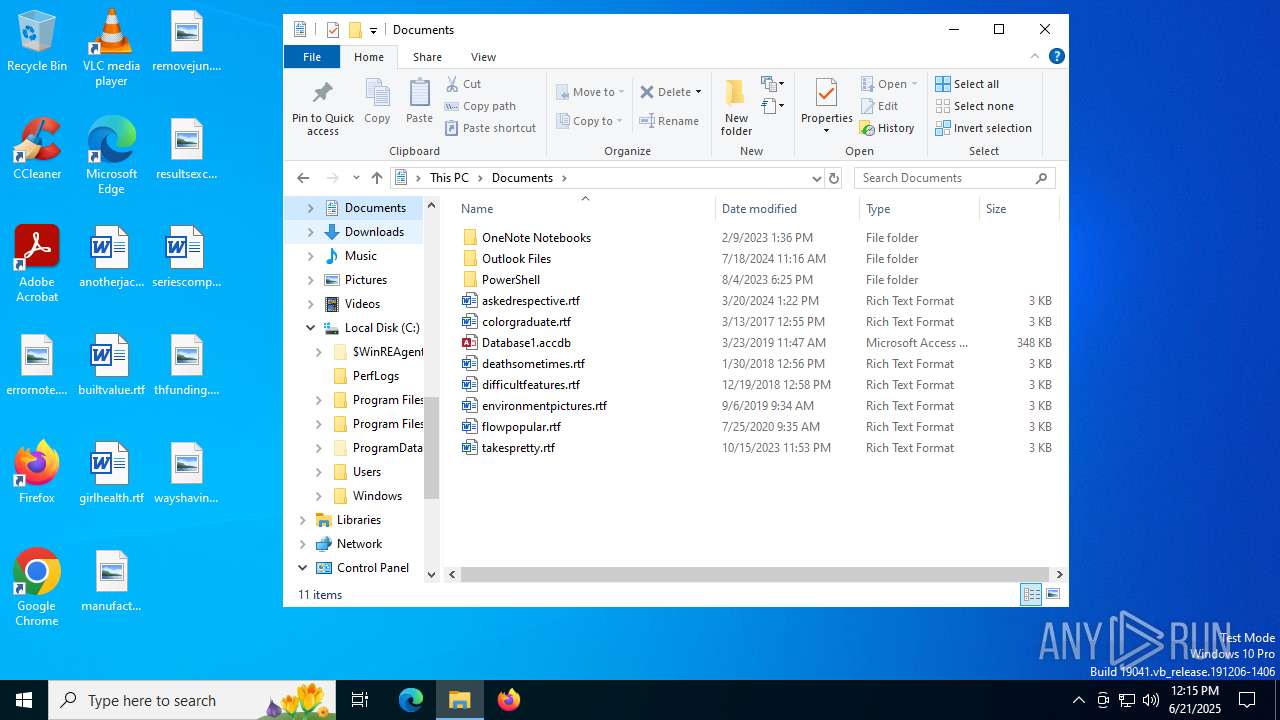
Creates files or folders in the user directory
- ProcessHacker.exe (PID: 7464)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
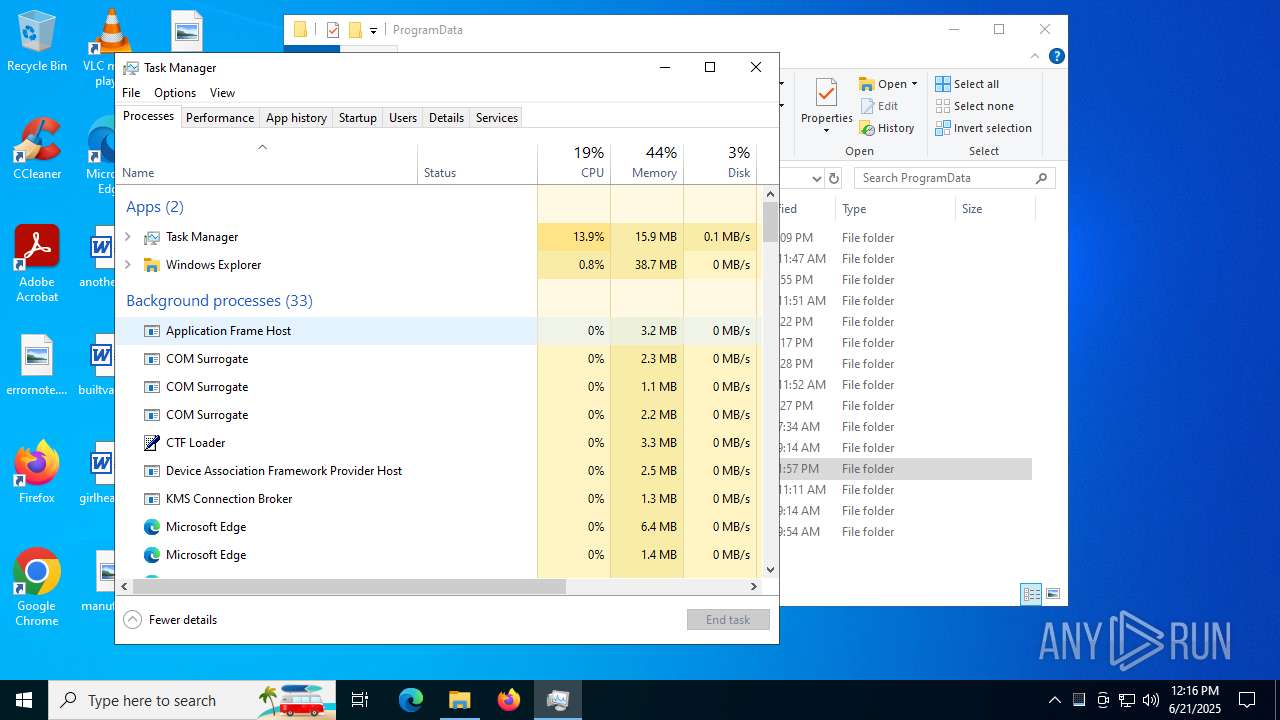
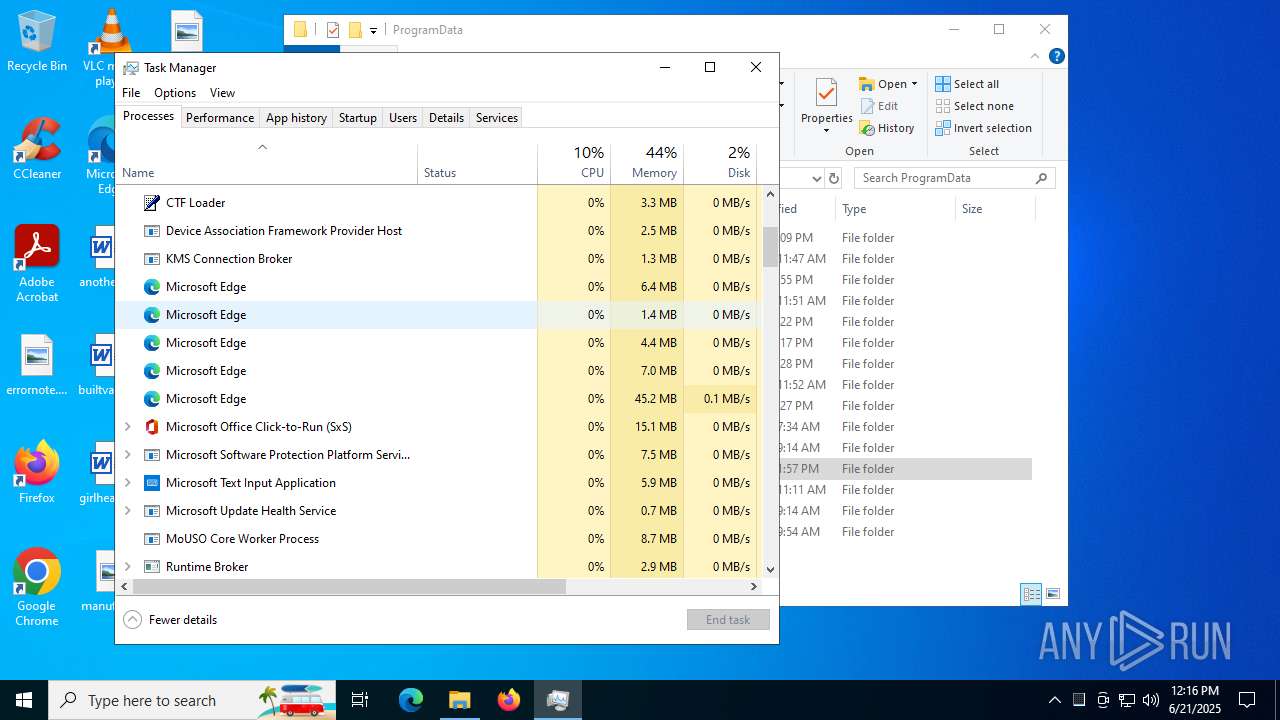
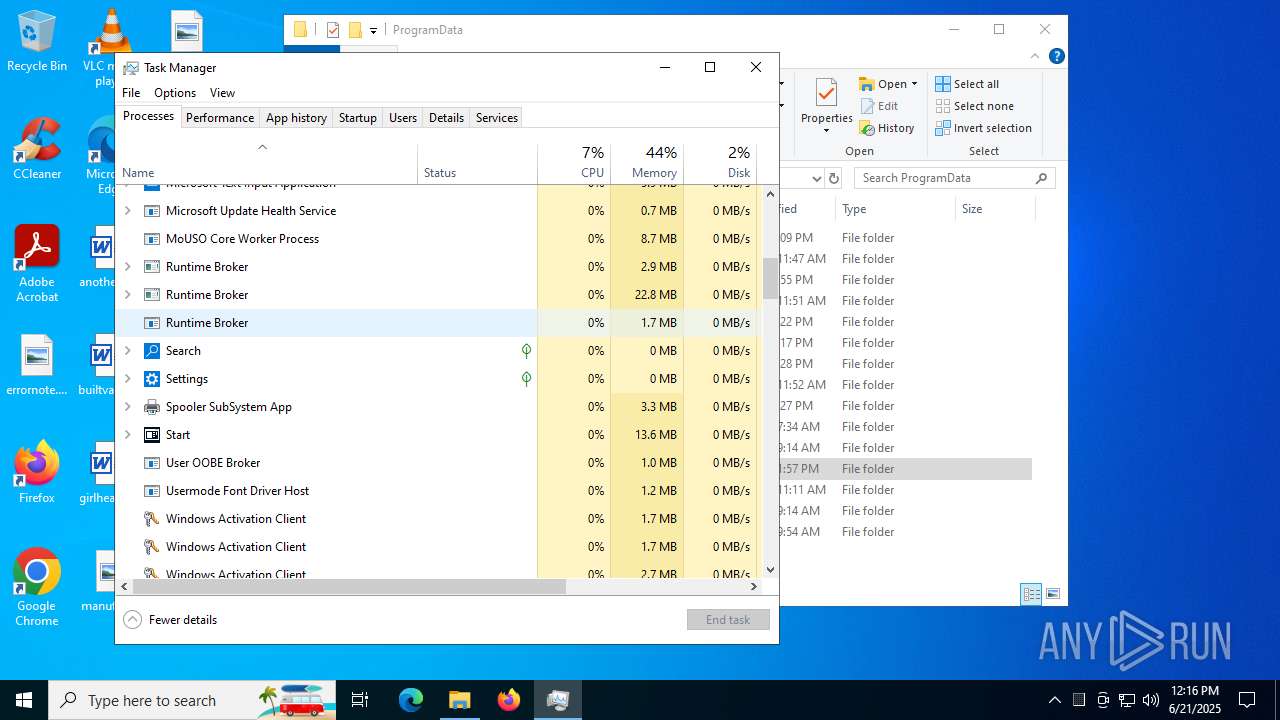
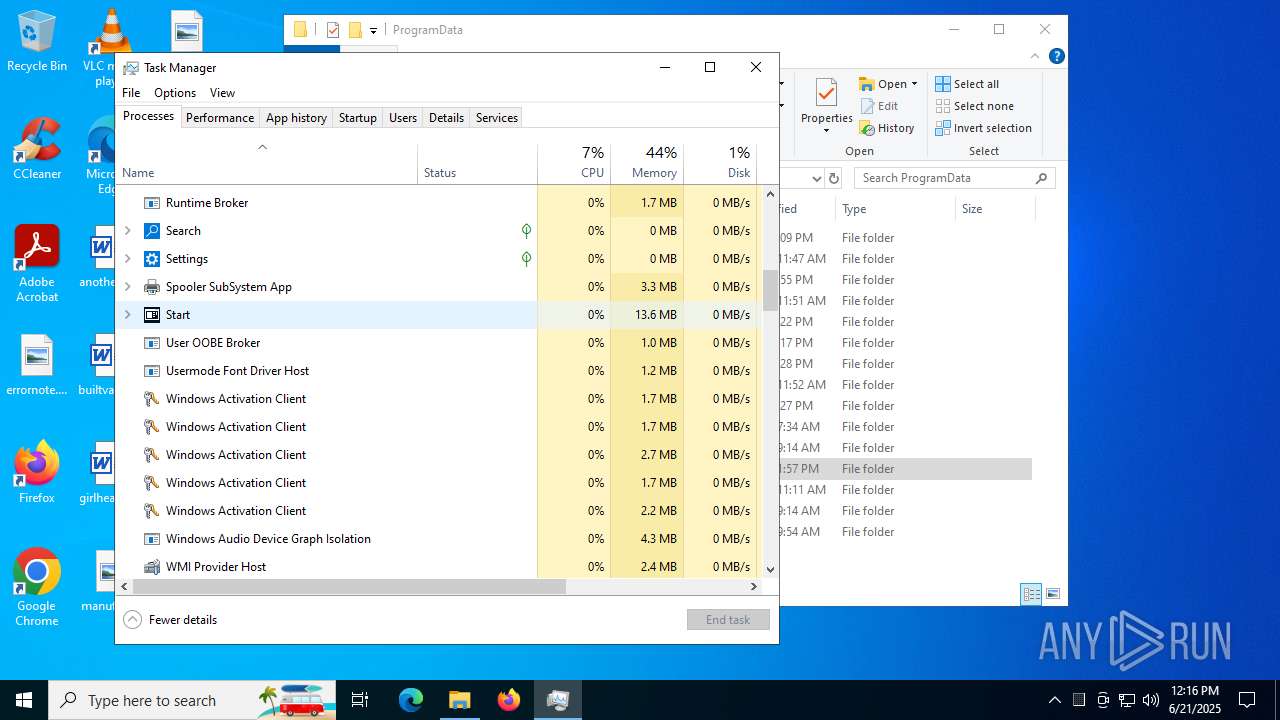
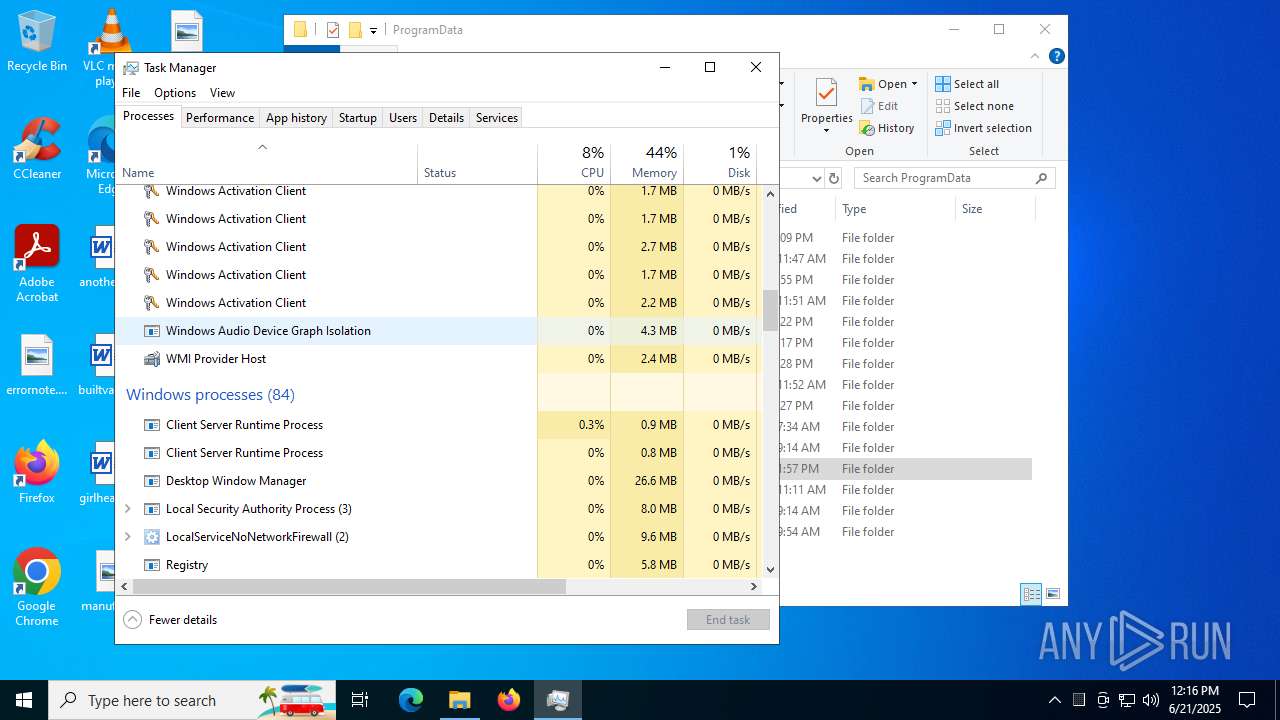
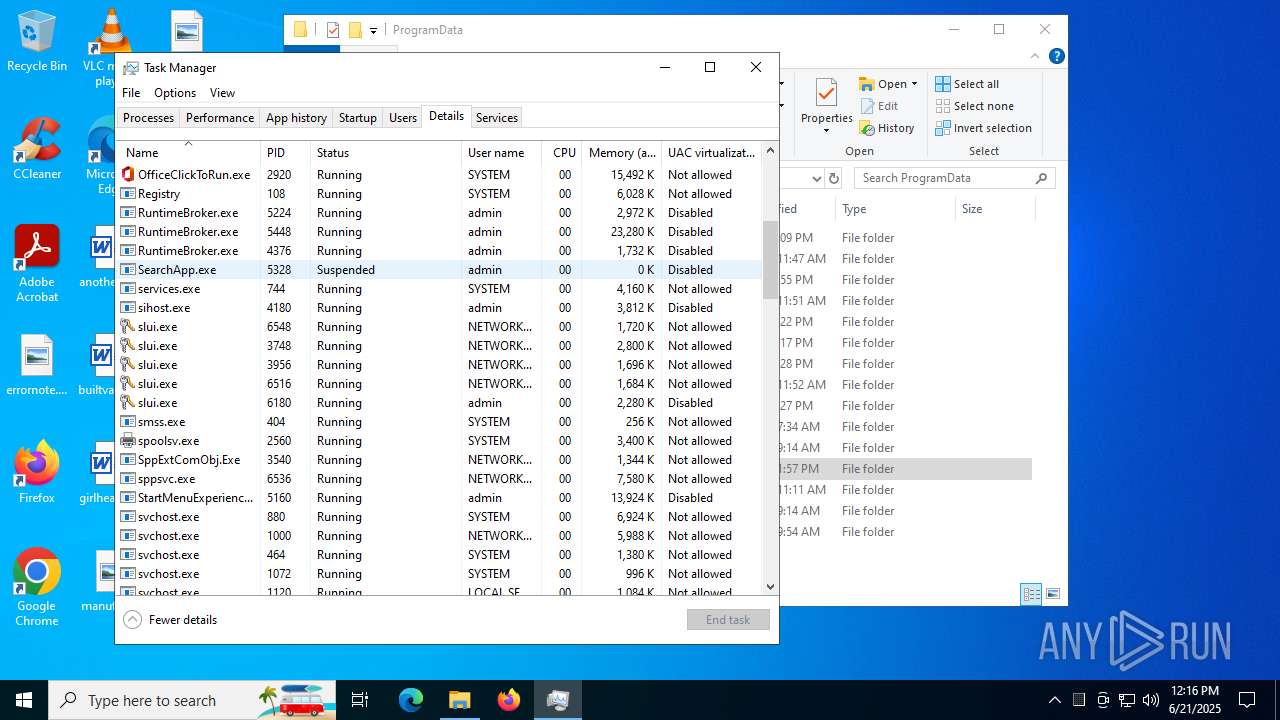
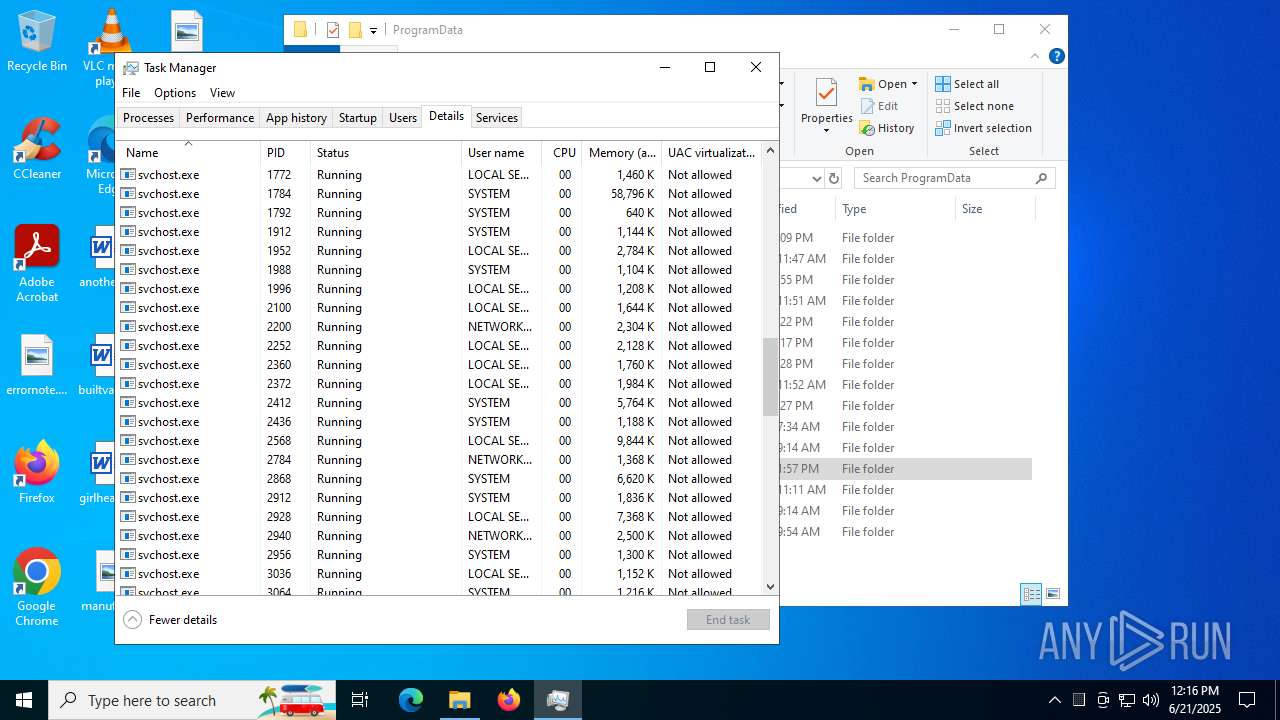
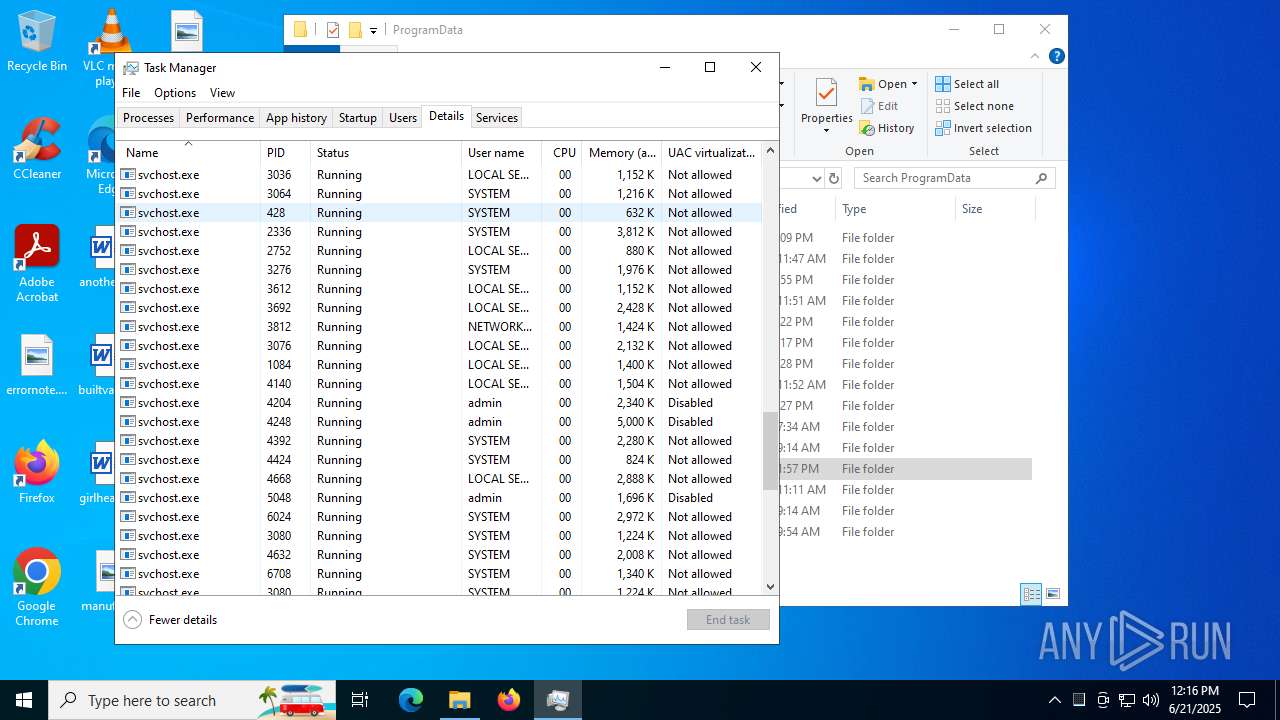
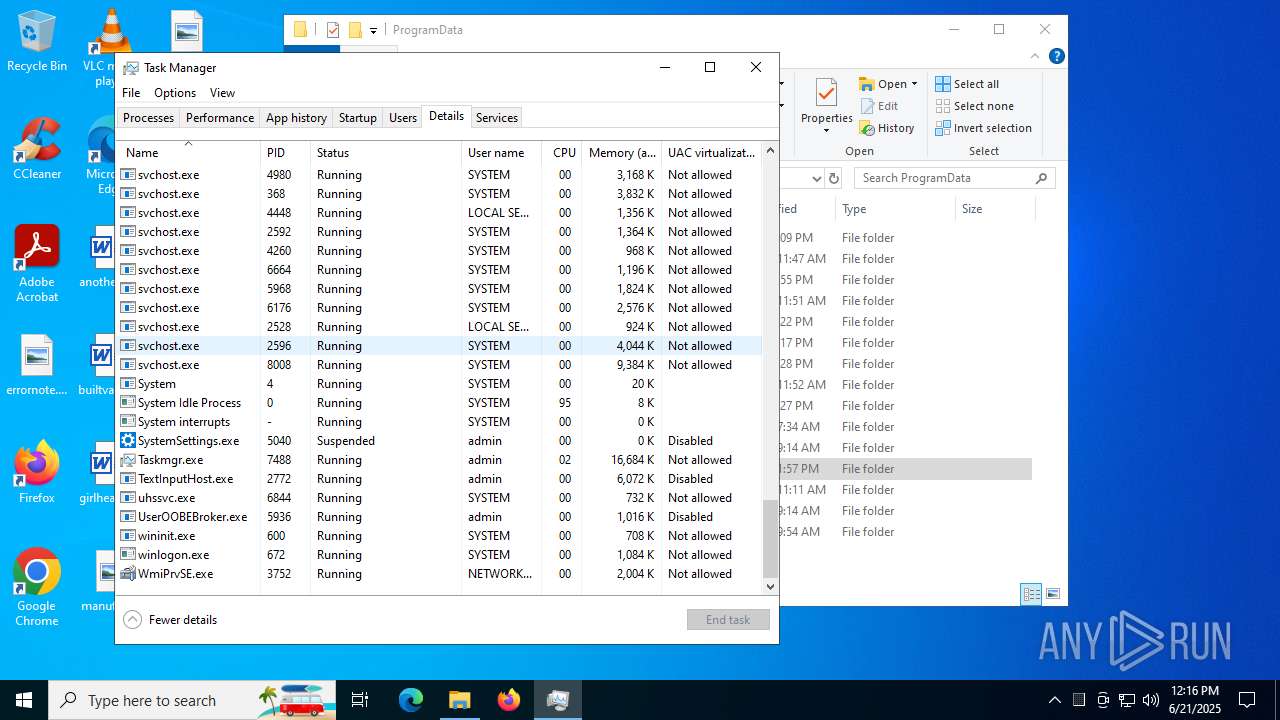
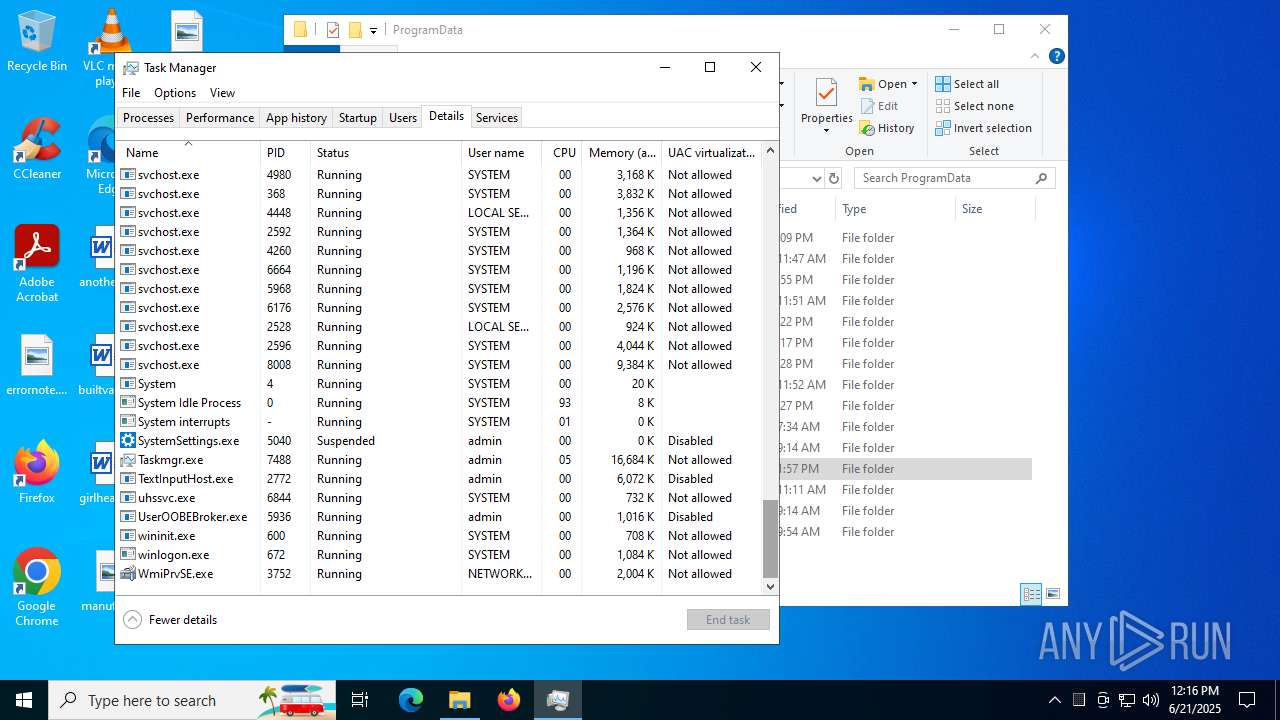
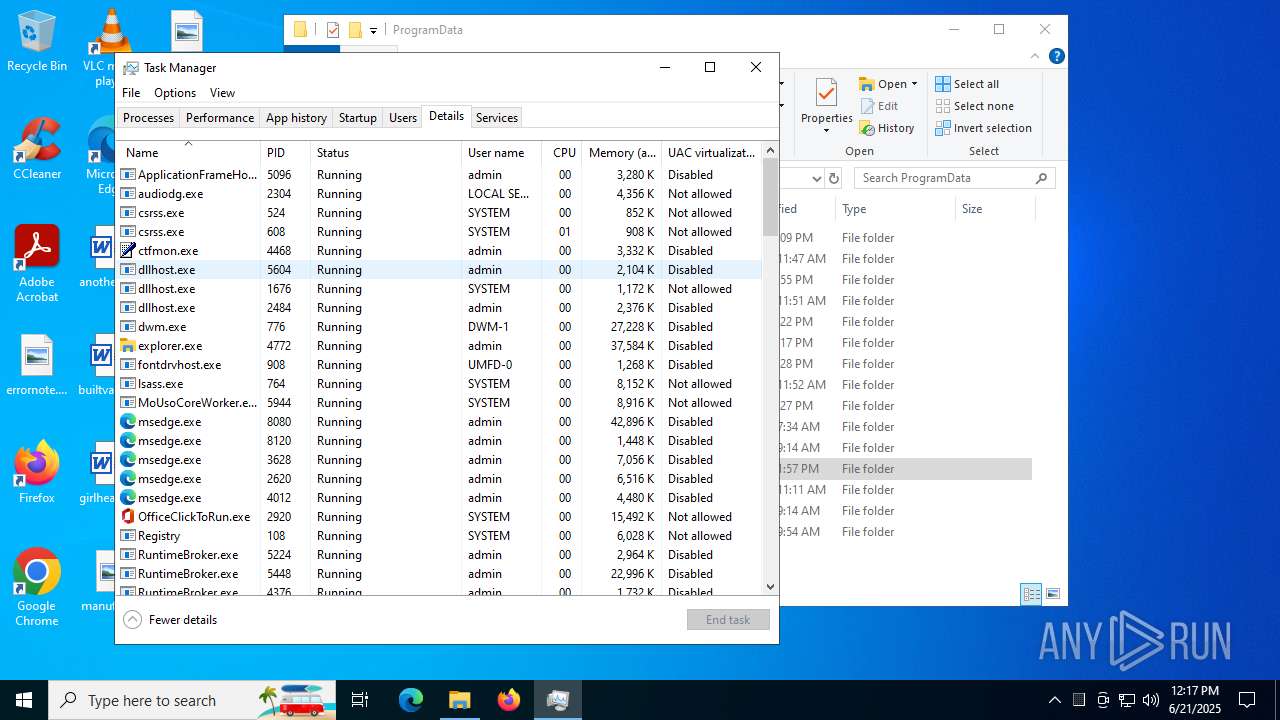
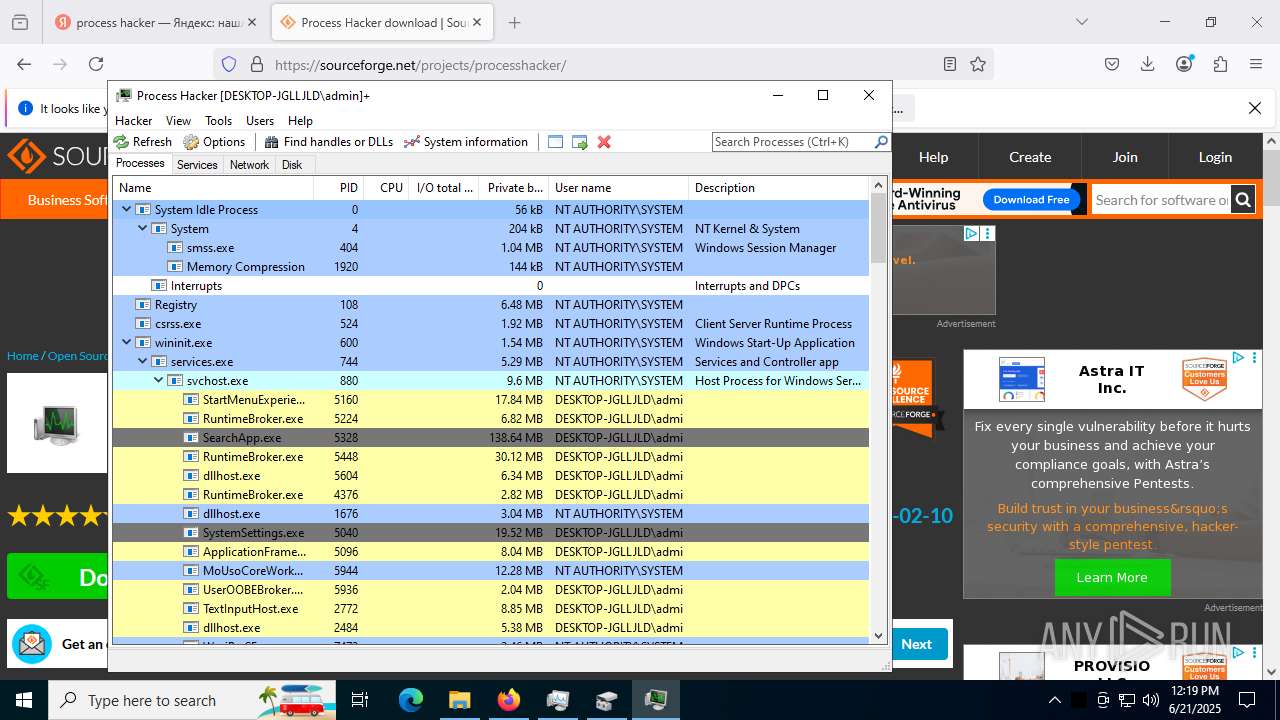
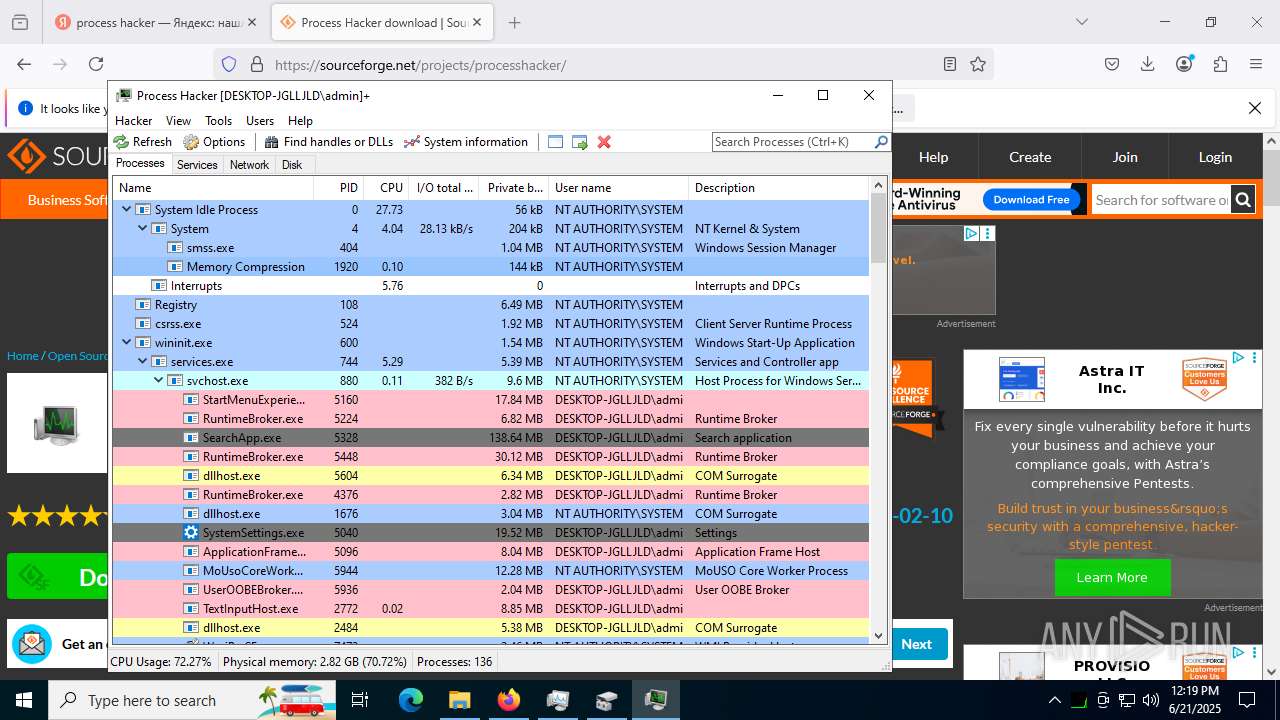
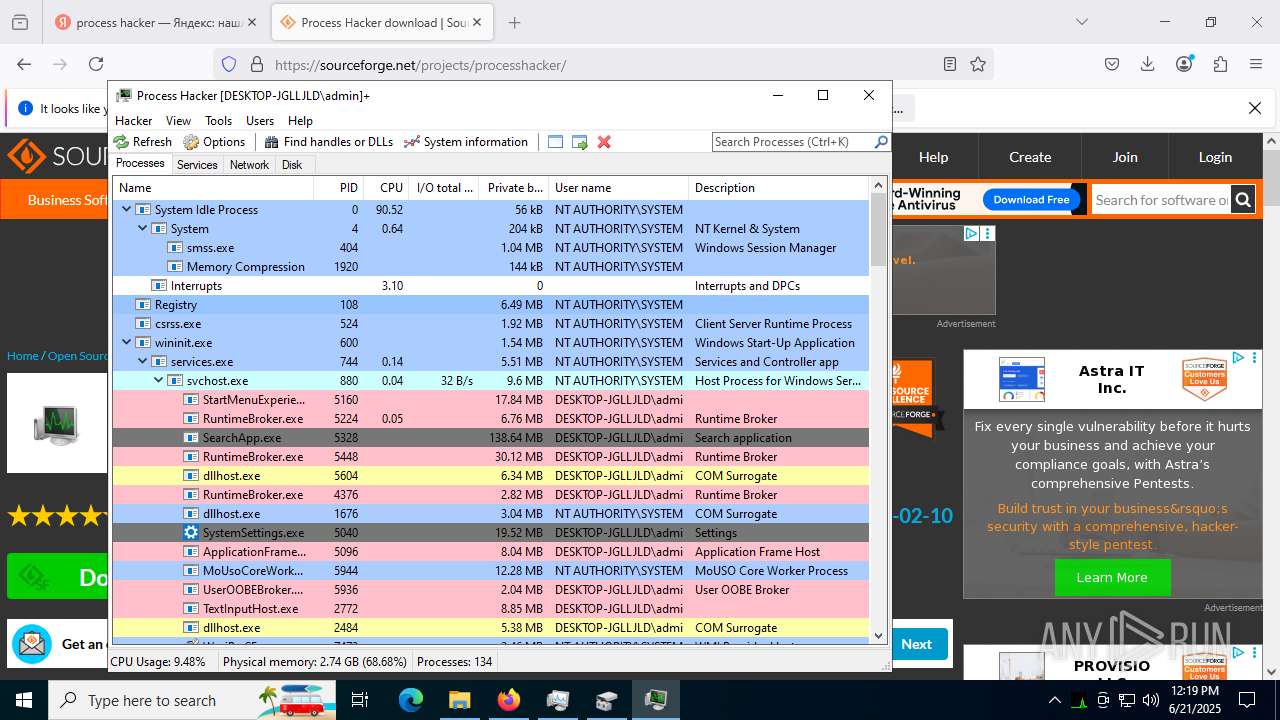
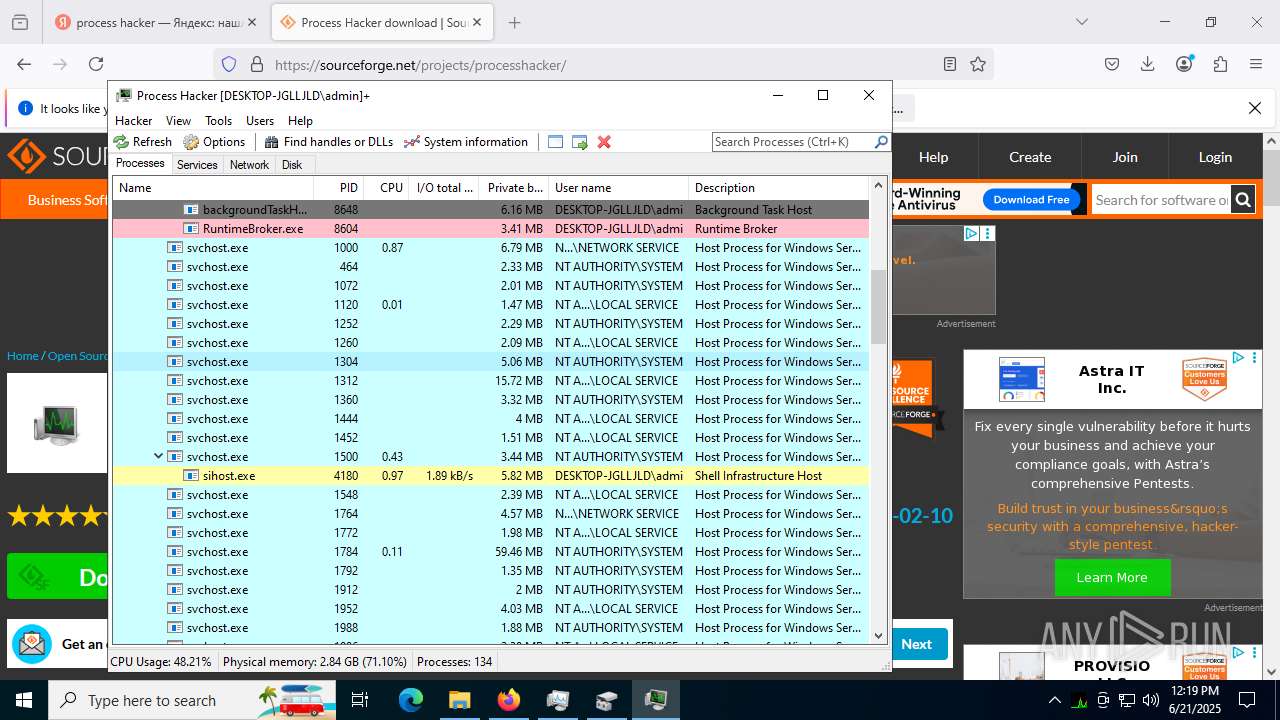
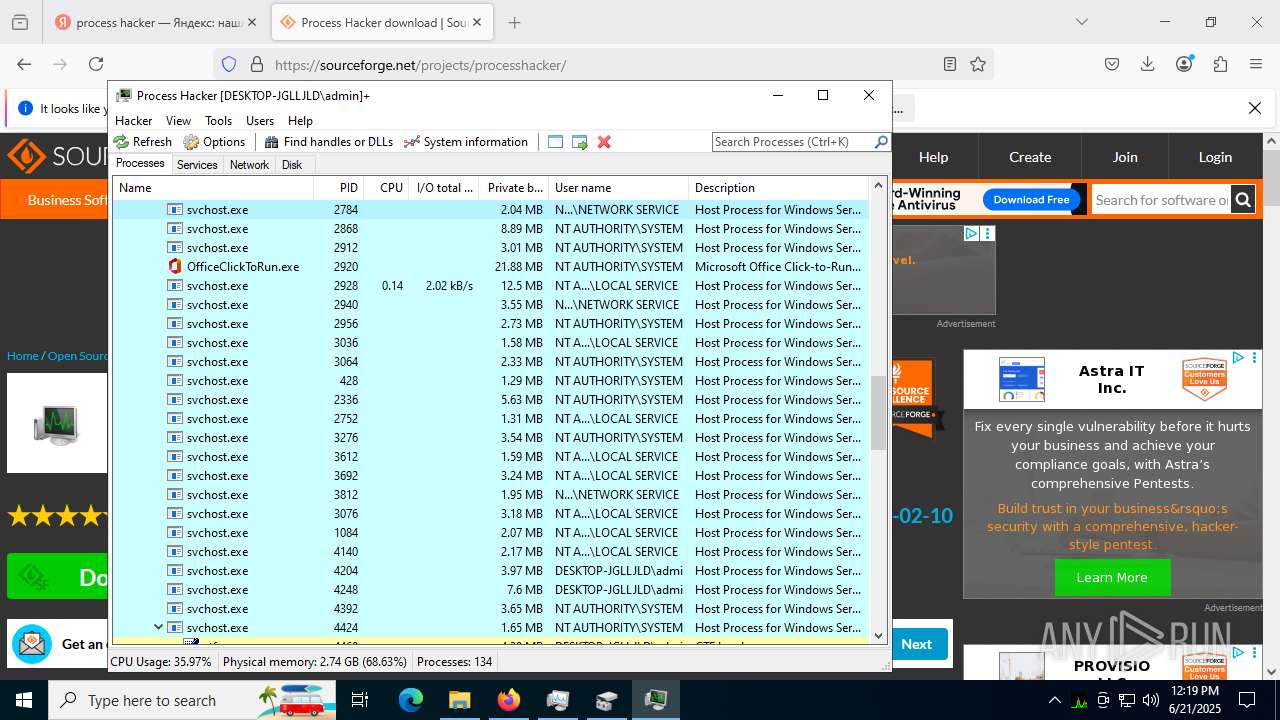
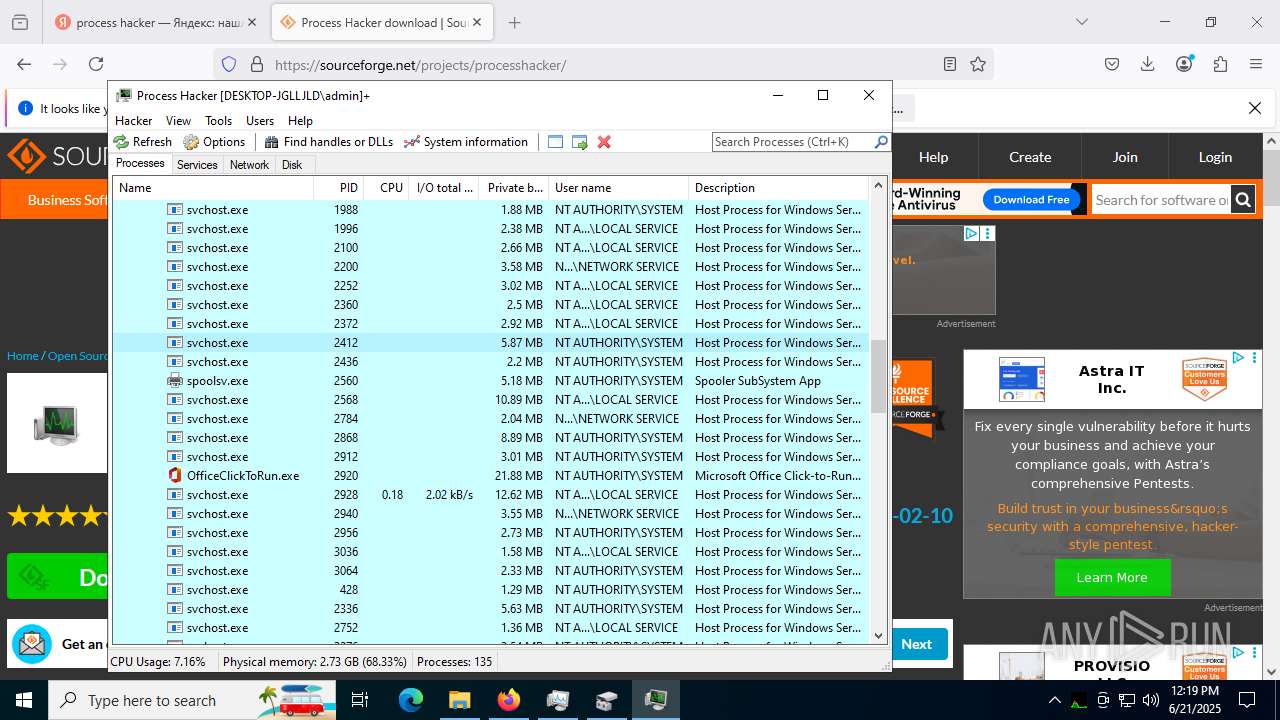
Total processes
258
Monitored processes
96
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
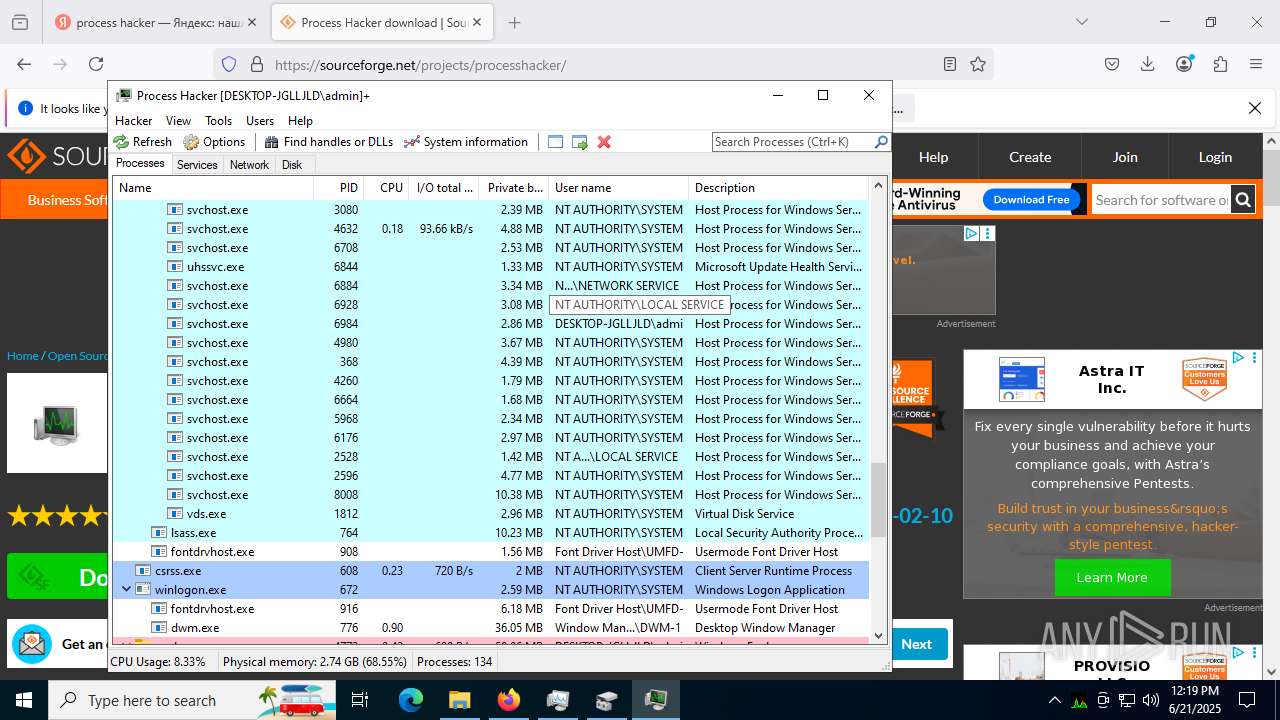
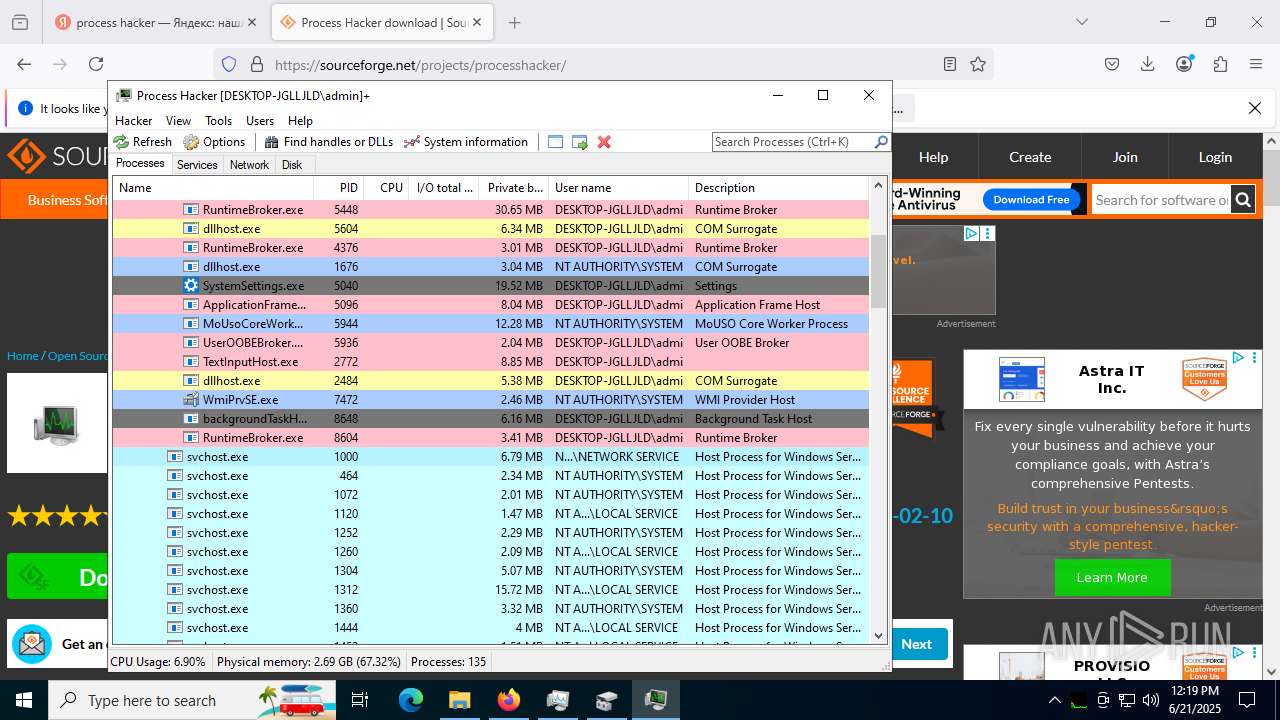
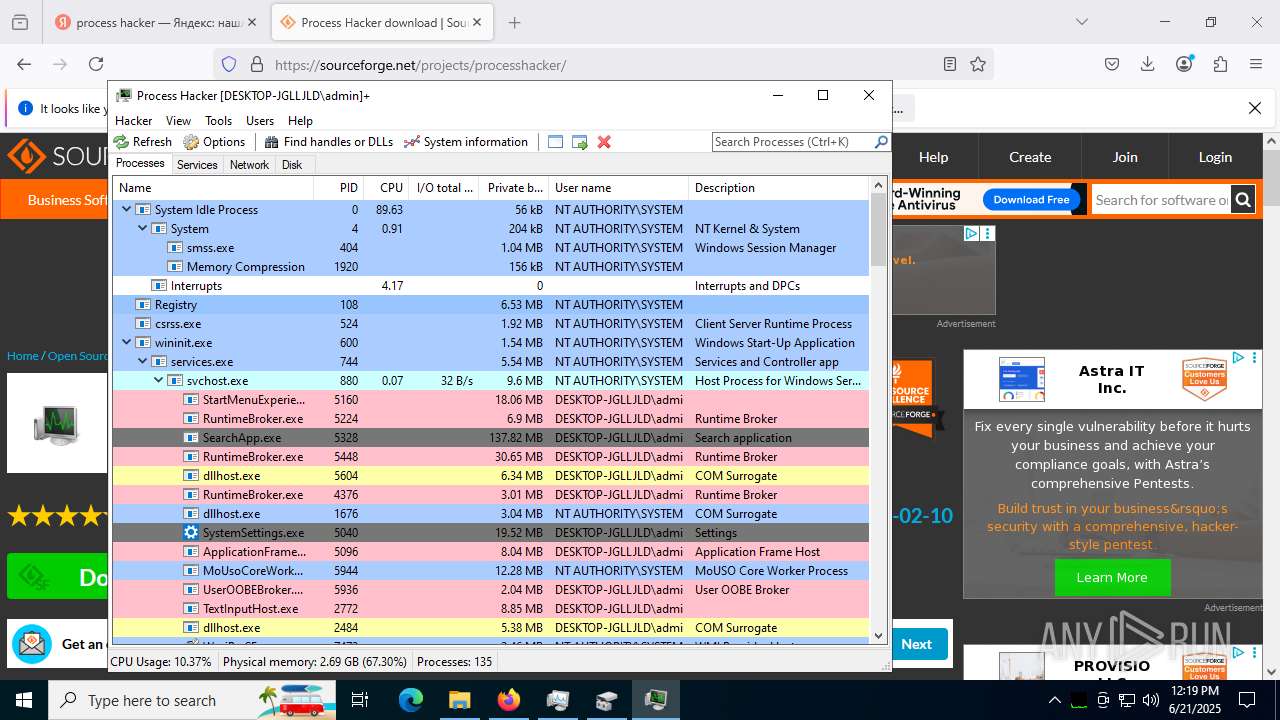
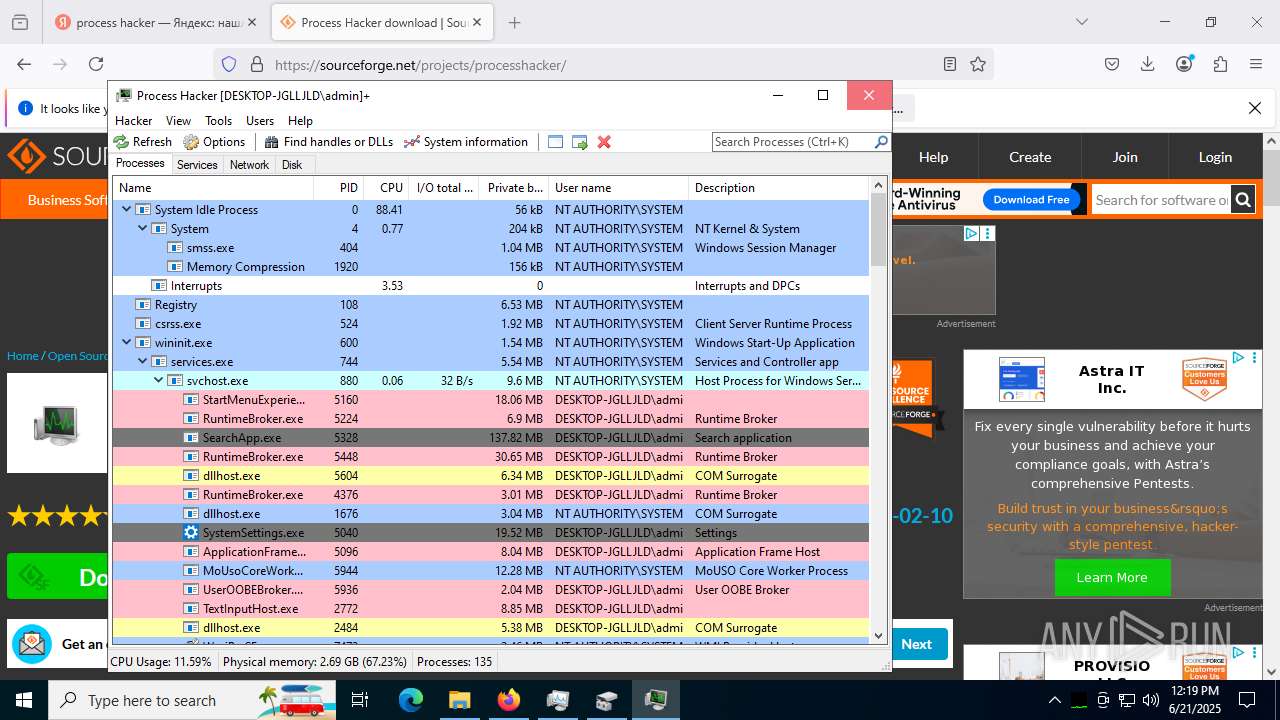
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 436 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1052 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3620,i,4216728398446849539,7208518698637278943,262144 --variations-seed-version --mojo-platform-channel-handle=3672 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1180 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5976 -prefsLen 39231 -prefMapHandle 5968 -prefMapSize 272997 -jsInitHandle 5964 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5696 -initialChannelId {66ad2ce2-d255-485b-ae3e-bbbb5506214b} -parentPid 7640 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7640" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 13 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1440 | "C:\WINDOWS\system32\taskmgr.exe" /4 | C:\Windows\System32\Taskmgr.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Manager Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1560 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4100 -prefsLen 39231 -prefMapHandle 5464 -prefMapSize 272997 -jsInitHandle 5468 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 6376 -initialChannelId {df1db624-cd4e-423d-b28f-2b42476aaf40} -parentPid 7640 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7640" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 16 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1636 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5196,i,14642900811859665843,362731855823462871,262144 --variations-seed-version --mojo-platform-channel-handle=1652 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
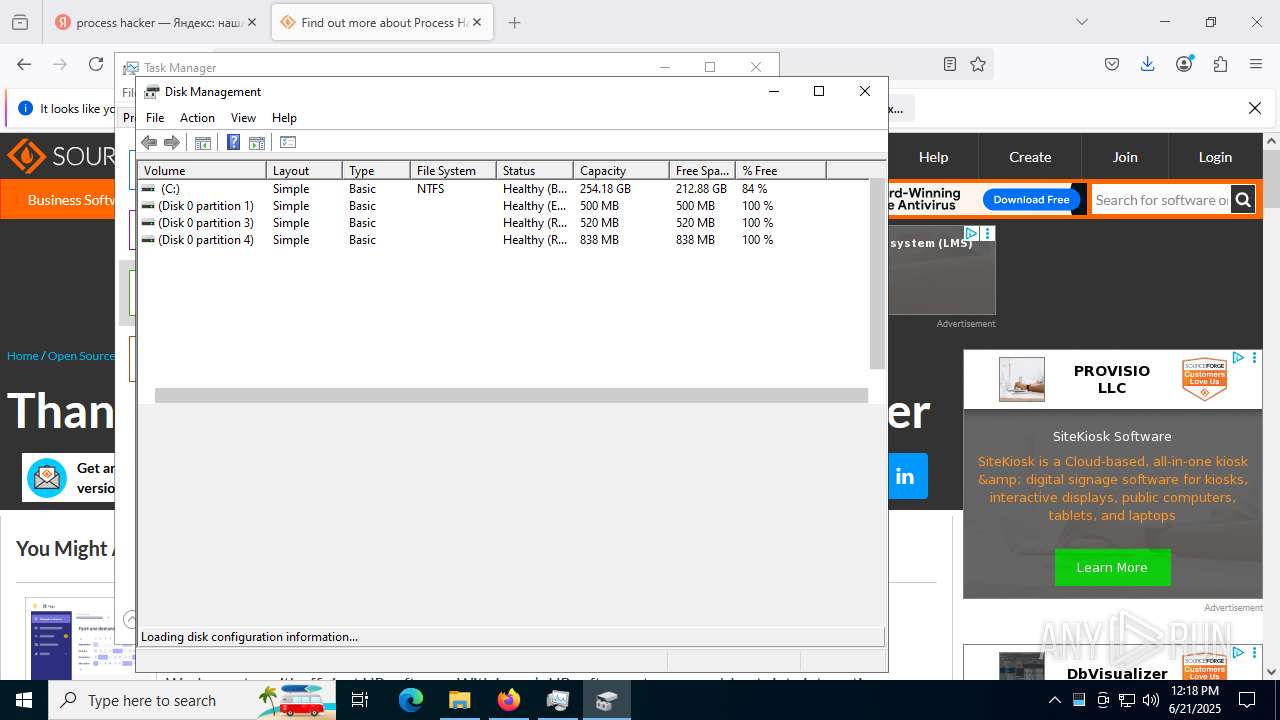
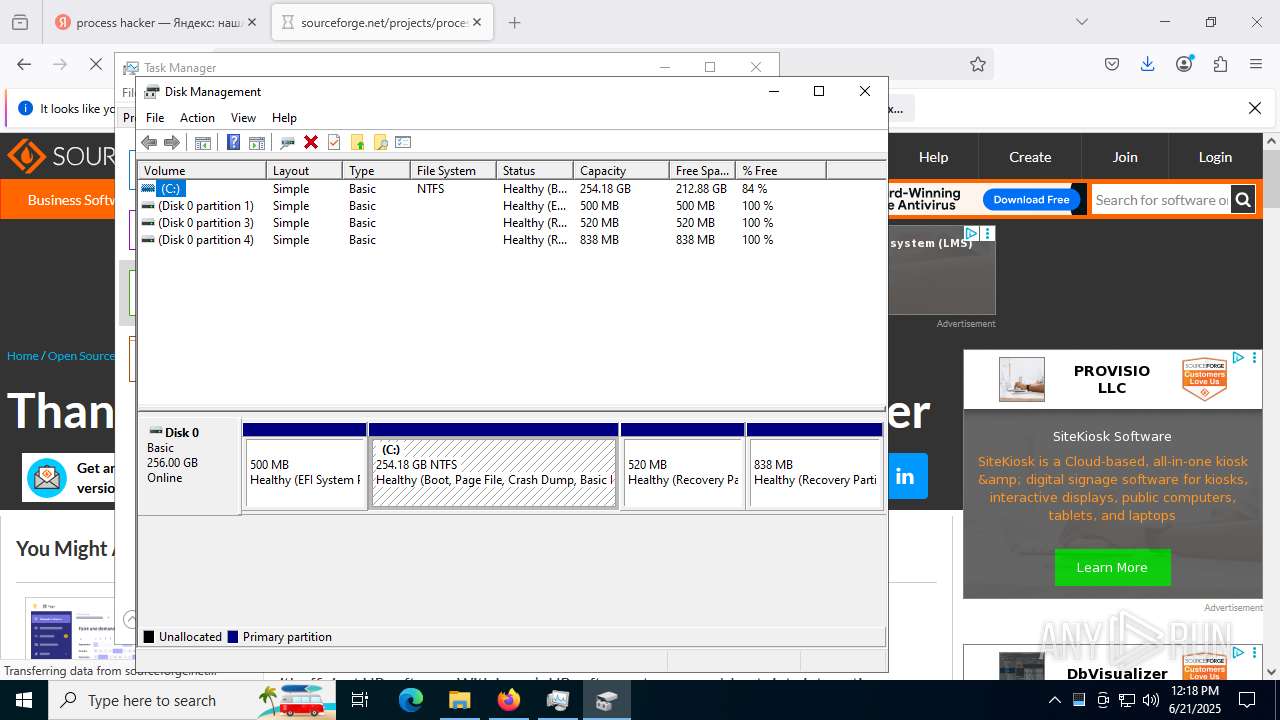
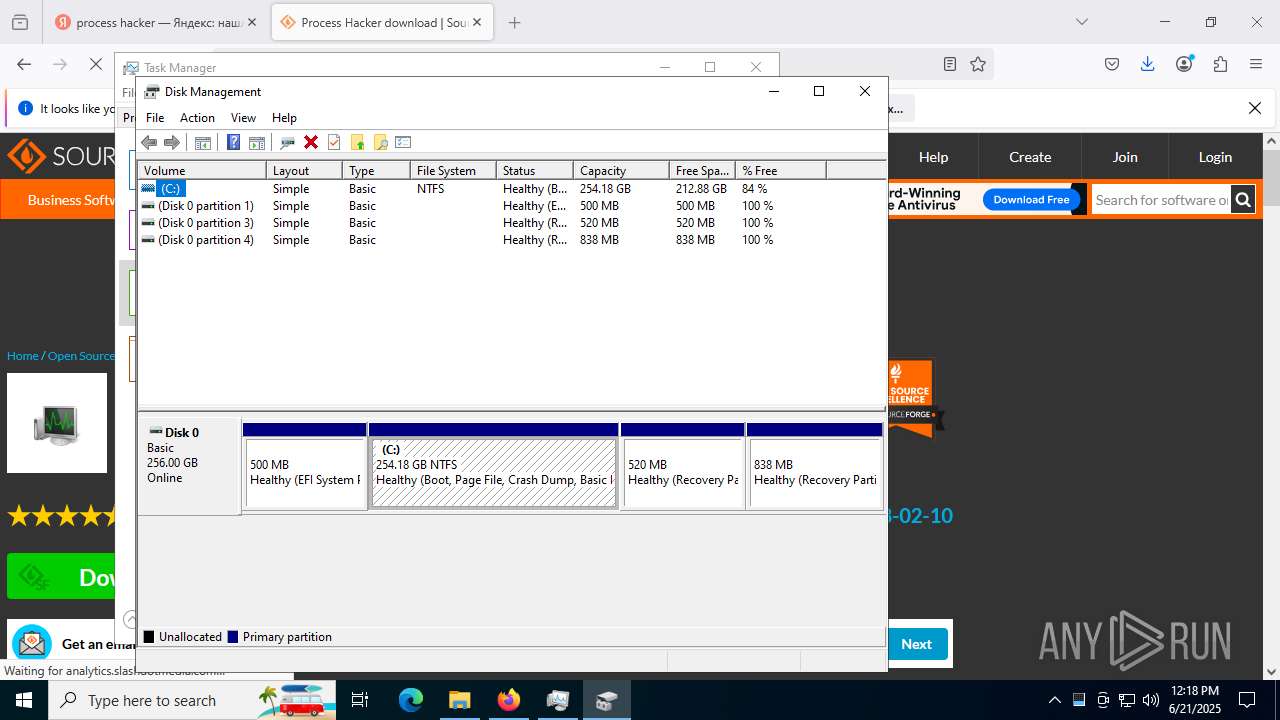
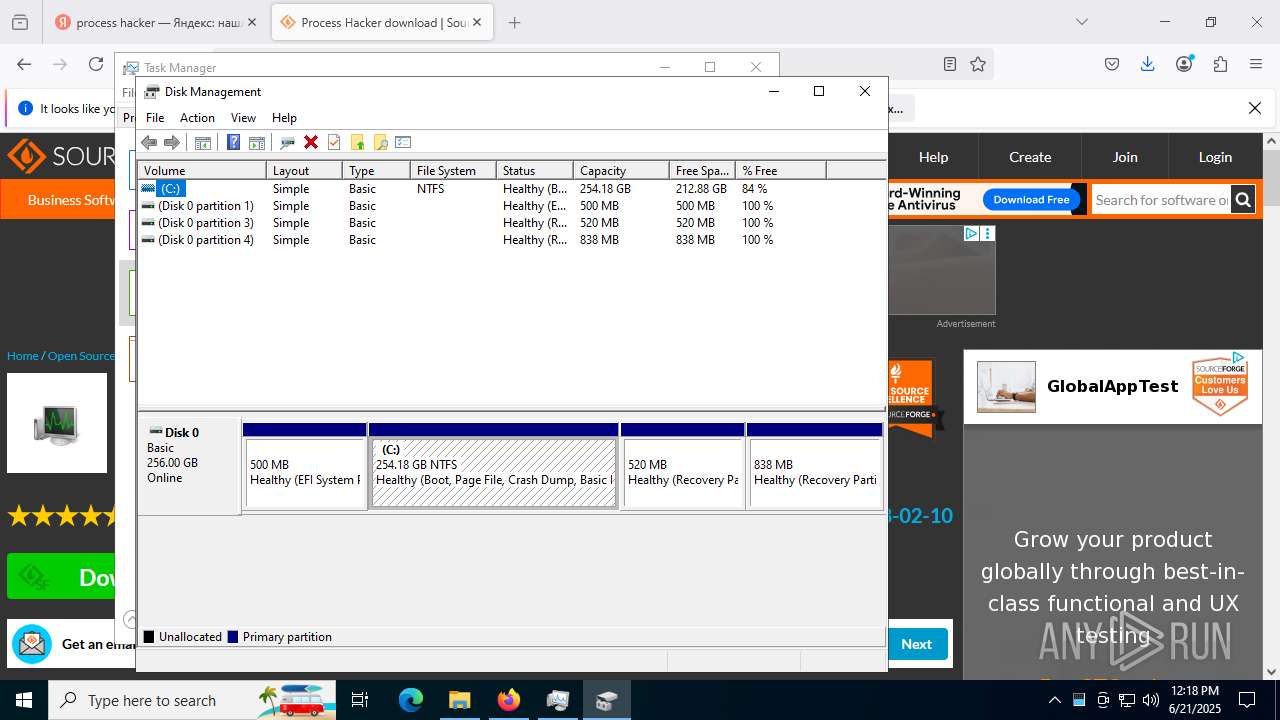
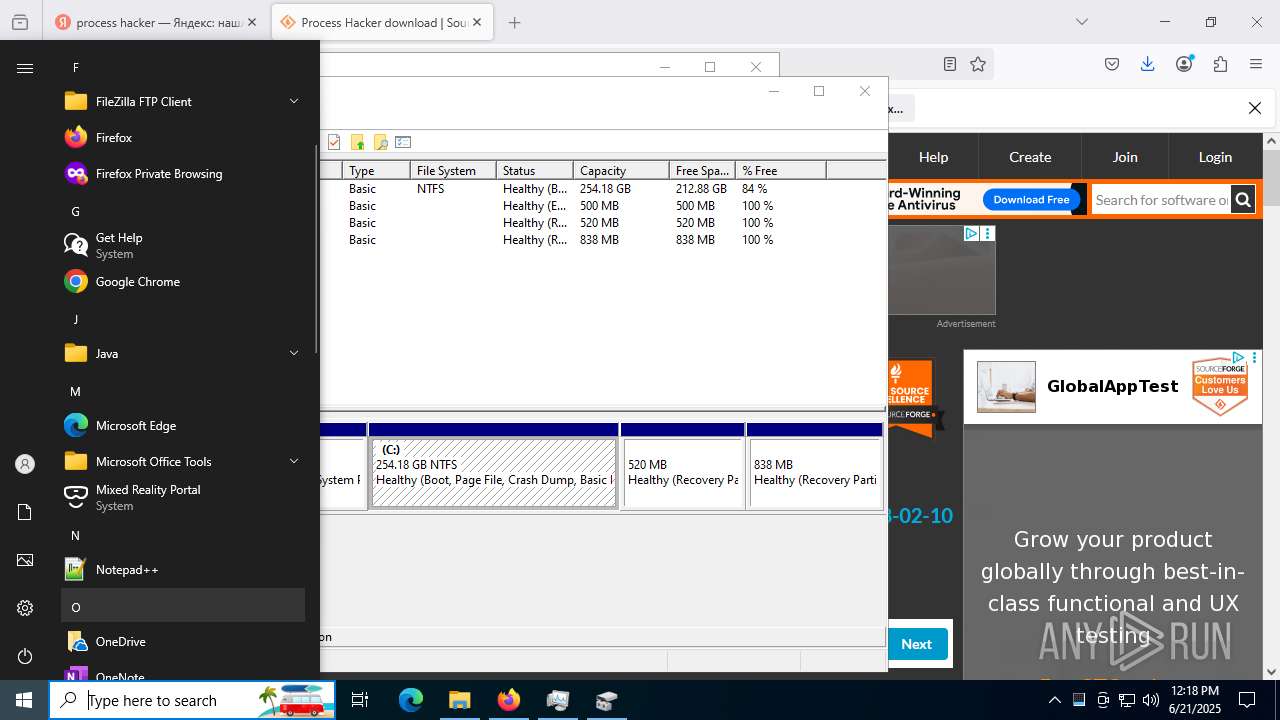
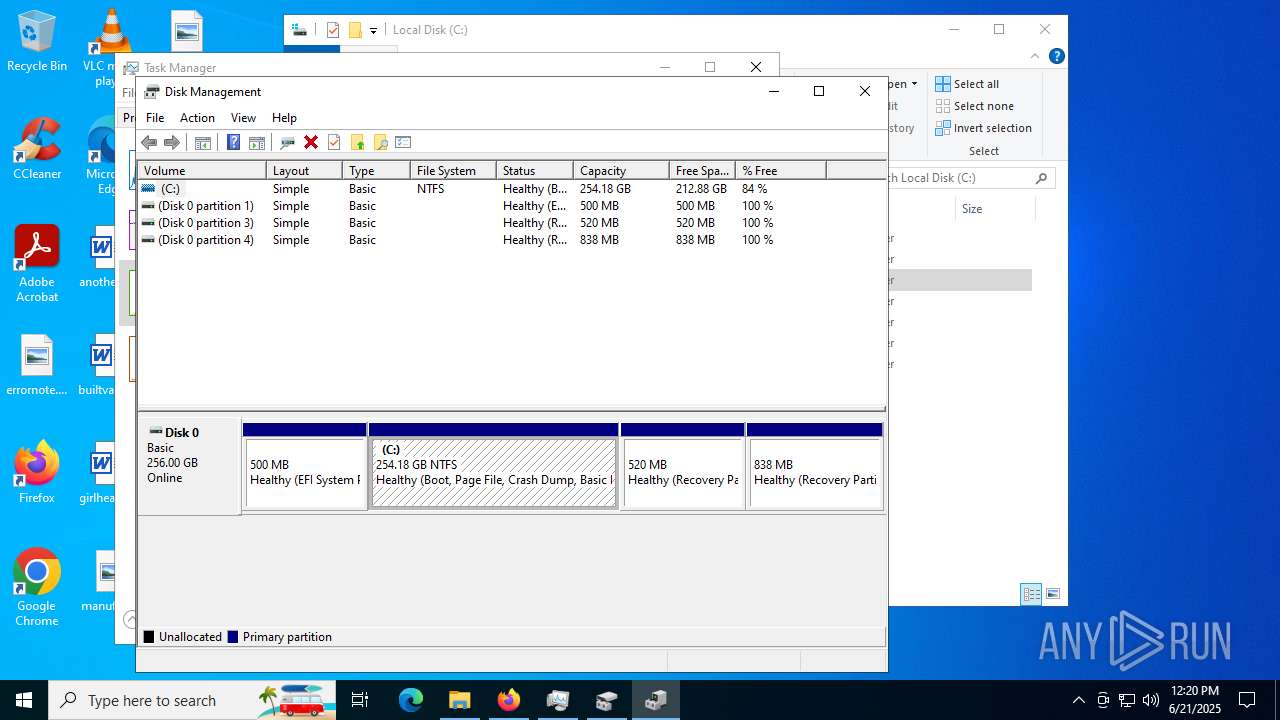
| 1760 | "C:\WINDOWS\system32\mmc.exe" "C:\WINDOWS\system32\diskmgmt.msc" | C:\Windows\System32\mmc.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Management Console Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | C:\WINDOWS\System32\vds.exe | C:\Windows\System32\vds.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Virtual Disk Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 3280 -prefsLen 36996 -prefMapHandle 3284 -prefMapSize 272997 -jsInitHandle 3288 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 3208 -initialChannelId {8e782cc4-cb6b-48f1-9482-922451f40a3d} -parentPid 7640 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7640" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 3 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5148 -prefsLen 39068 -prefMapHandle 5040 -prefMapSize 272997 -jsInitHandle 5156 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5164 -initialChannelId {dc149cab-582c-45eb-9311-652b1341bd0e} -parentPid 7640 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7640" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 7 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
Total events
58 965
Read events
58 890
Write events
72
Delete events
3
Modification events
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2952) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6016) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6016) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6016) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6016) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328466 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {55023829-8529-4FFD-A728-8FEC65A496DB} | |||
Executable files
58
Suspicious files
553
Text files
126
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6016 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF17684f.TMP | — | |
MD5:— | SHA256:— | |||
| 6016 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6016 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF17684f.TMP | — | |
MD5:— | SHA256:— | |||
| 6016 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF17685e.TMP | — | |
MD5:— | SHA256:— | |||
| 6016 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6016 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF17686e.TMP | — | |
MD5:— | SHA256:— | |||
| 6016 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6016 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF17685e.TMP | — | |
MD5:— | SHA256:— | |||
| 6016 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6016 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF17688d.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
150
TCP/UDP connections
380
DNS requests
618
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3768 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3768 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6840 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:DyYUxEE9WFeMZyn6uRh20qenMUydjq0wVkuXFxKekEc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2596 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8008 | svchost.exe | GET | 206 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751048711&P2=404&P3=2&P4=Zfh8e44lQBgJx8M1CjqXr4BIL7zyPYgcx44aravZk4w42M%2b5823hyFcrTacA8IG3cLxGD4%2bdil37Ik2YLwqv5w%3d%3d | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
8008 | svchost.exe | HEAD | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1751048713&P2=404&P3=2&P4=TaG%2fWLcPAjS2FoO9Z7rYmrv%2bldsdjeekxJULvCg9aIQD56Yx4XuxEeFrqSkvjd0f%2f9%2b8I1npGENdkVG16j3OjA%3d%3d | unknown | — | — | whitelisted |
8008 | svchost.exe | GET | 200 | 23.50.131.74:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1751048713&P2=404&P3=2&P4=MzUDlAkS2R5GXz39M4DZ1sJjy7usxtNGj5navUShsHOizPnVLA%2bSCcrpSJNG1HGqwegzsvGATcVRe4NbgtBd9Q%3d%3d | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2368 | RUXIMICS.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6840 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6840 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6840 | msedge.exe | 92.123.104.53:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
6840 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6840 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
a.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
www.bing.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |