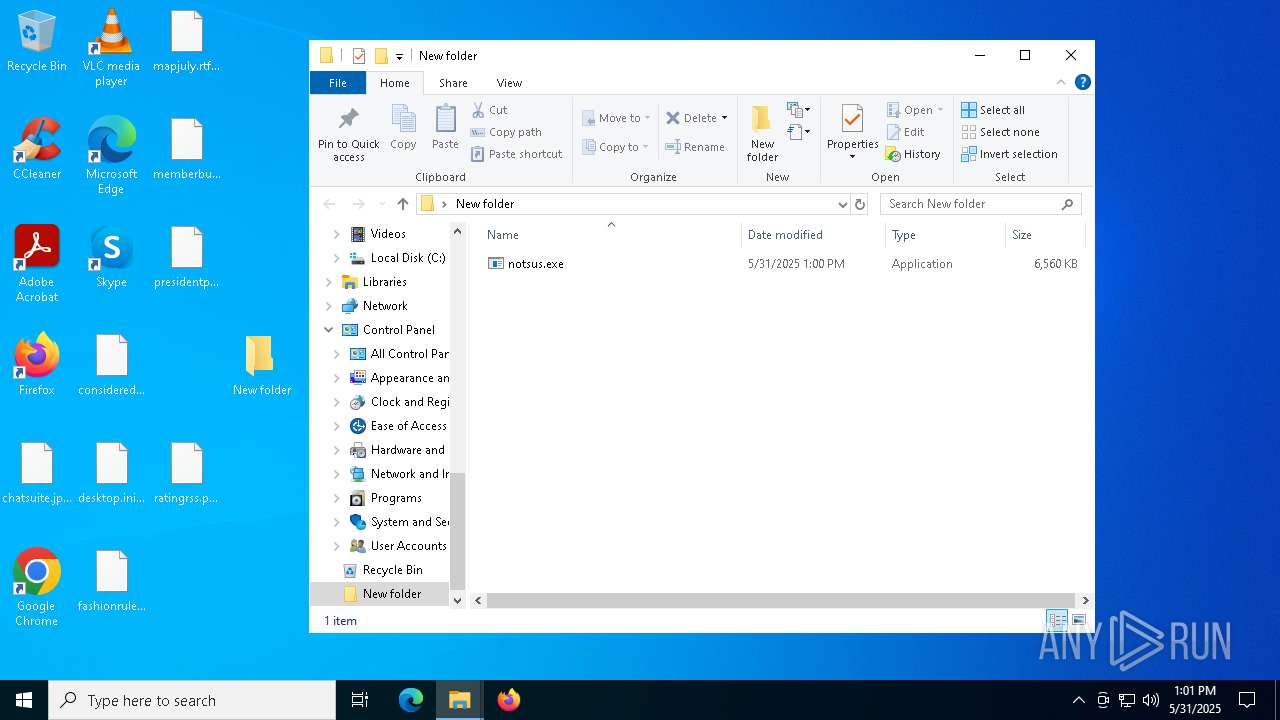
| File name: | notsus.exe |
| Full analysis: | https://app.any.run/tasks/79f3a192-2ad7-4faf-801c-b6b083550a58 |
| Verdict: | Malicious activity |
| Analysis date: | May 31, 2025, 13:00:39 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 1516B0F95C0CDA6FECD8B2D5EE01A127 |
| SHA1: | 76CDE596845C0E4D5C611E2EFBA78B0794844BE8 |
| SHA256: | D6A8B666A2BC1CD5BAD4FB26445AC85AEEE01567DBC015D2B9022F470AA1FF95 |
| SSDEEP: | 98304:r6CzVyXqwvvYQ5XVBumtHfktEzafhOsE+XZ0TvGnRig50VwT8amL2/fqqQVH68DZ:DrHTP44amXOg5W |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process drops C-runtime libraries
- notsus.exe (PID: 4180)
- notsus.exe (PID: 7916)
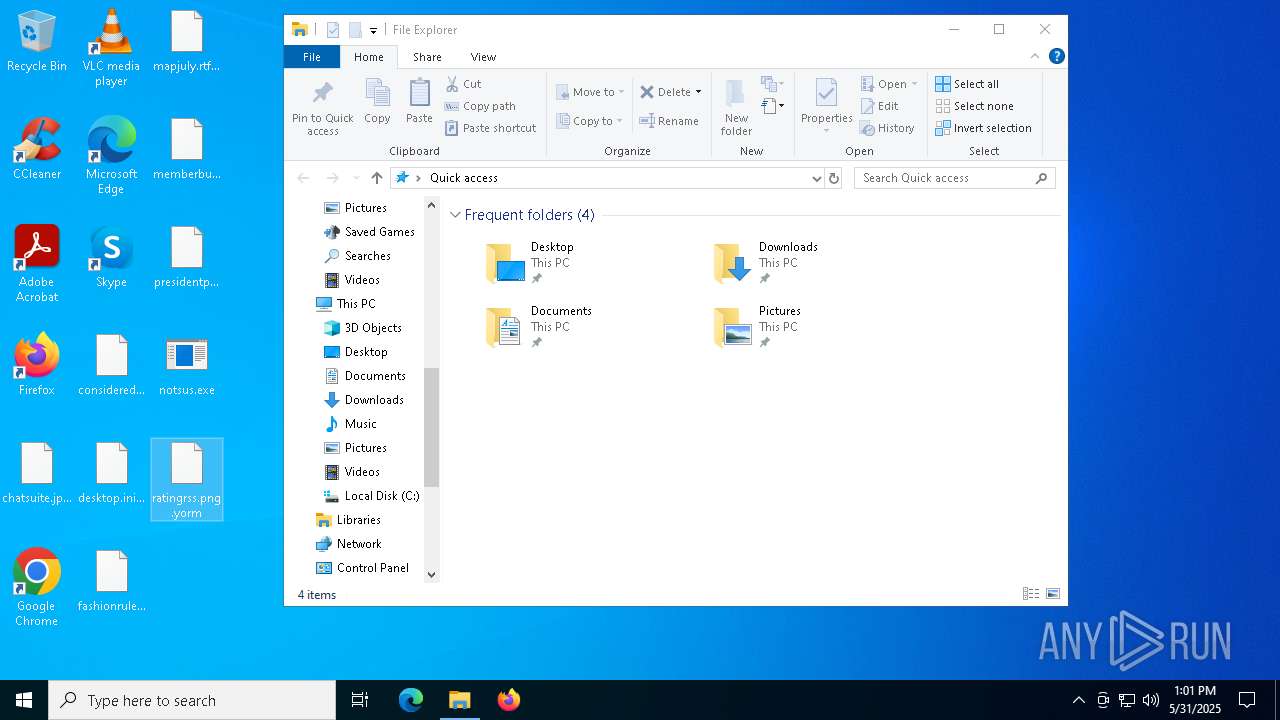
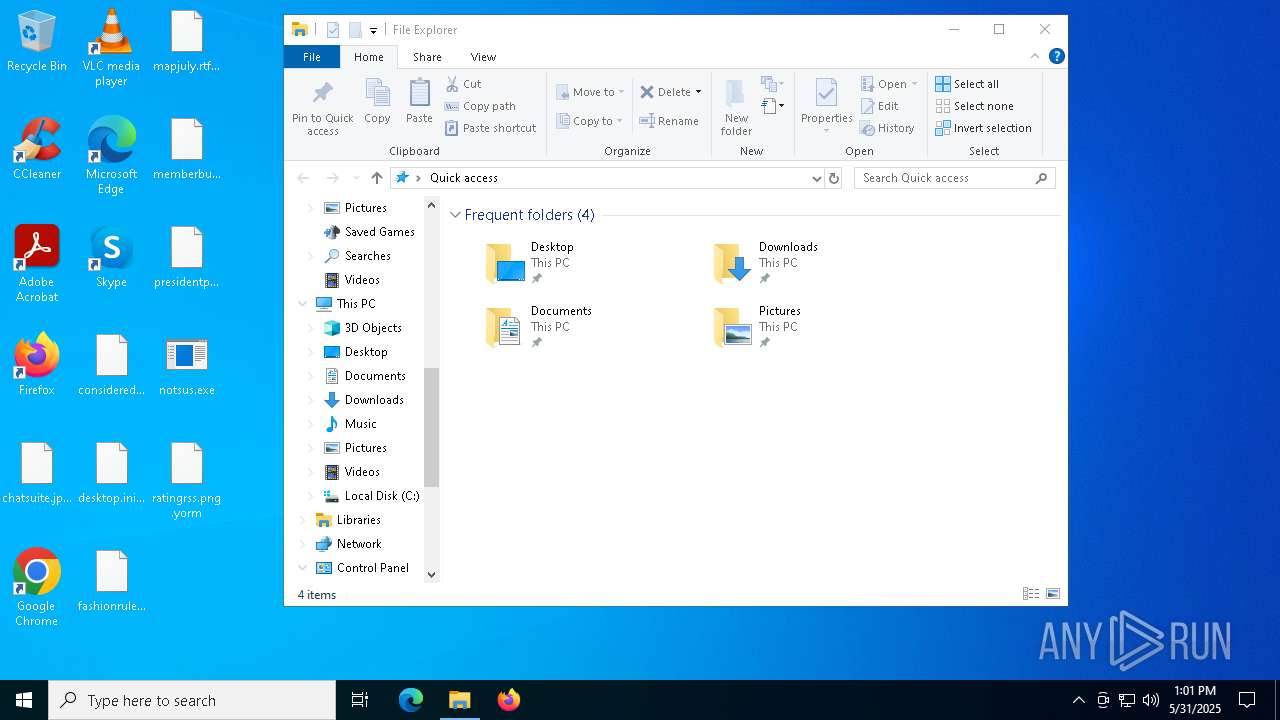
Executable content was dropped or overwritten
- notsus.exe (PID: 4180)
- notsus.exe (PID: 7916)
Process drops python dynamic module
- notsus.exe (PID: 4180)
- notsus.exe (PID: 7916)
Process drops legitimate windows executable
- notsus.exe (PID: 4180)
- notsus.exe (PID: 7916)
Application launched itself
- notsus.exe (PID: 4180)
- notsus.exe (PID: 7916)
INFO
Checks supported languages
- notsus.exe (PID: 4180)
- notsus.exe (PID: 5776)
- notsus.exe (PID: 7916)
- notsus.exe (PID: 1764)
The sample compiled with english language support
- notsus.exe (PID: 4180)
- notsus.exe (PID: 7916)
Reads the computer name
- notsus.exe (PID: 4180)
- notsus.exe (PID: 7916)
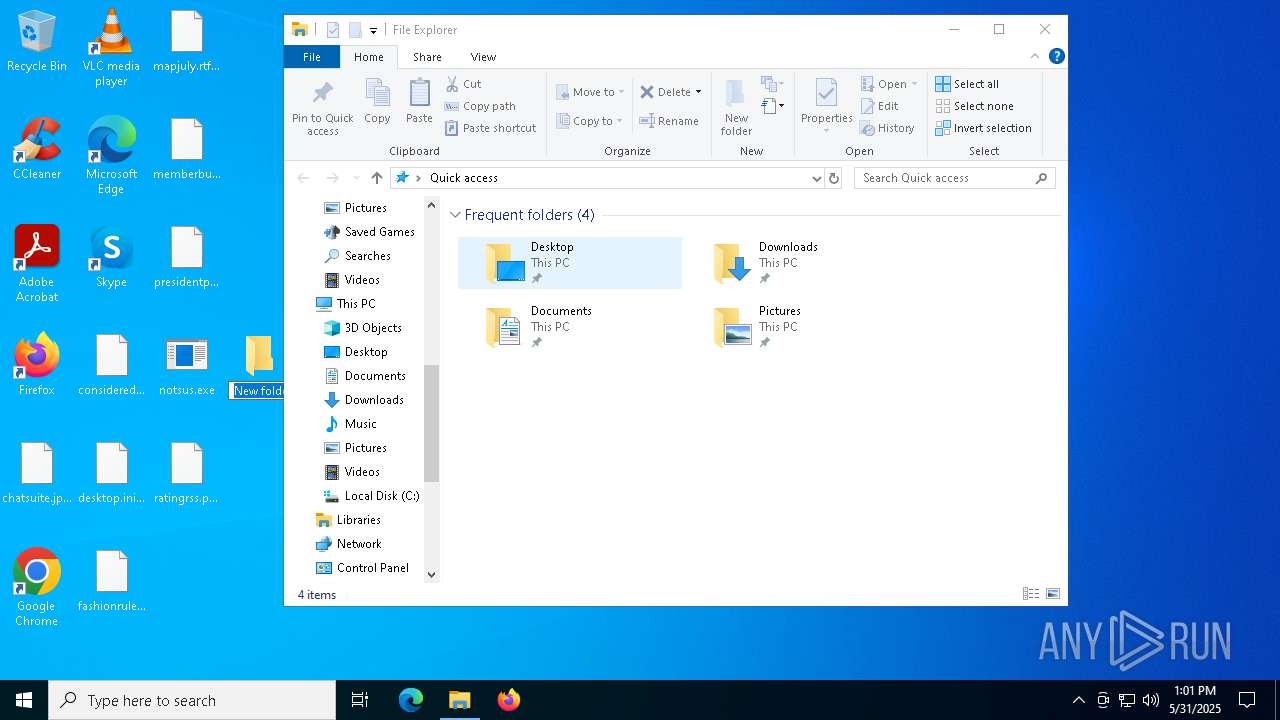
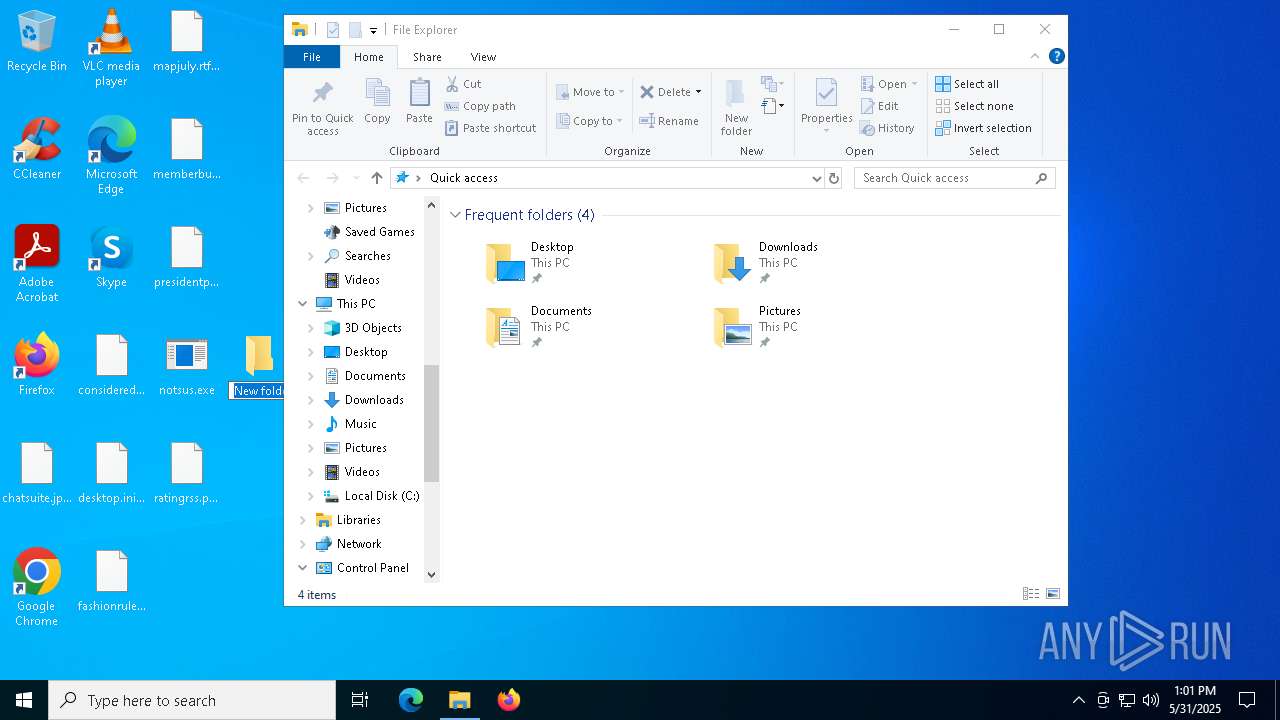
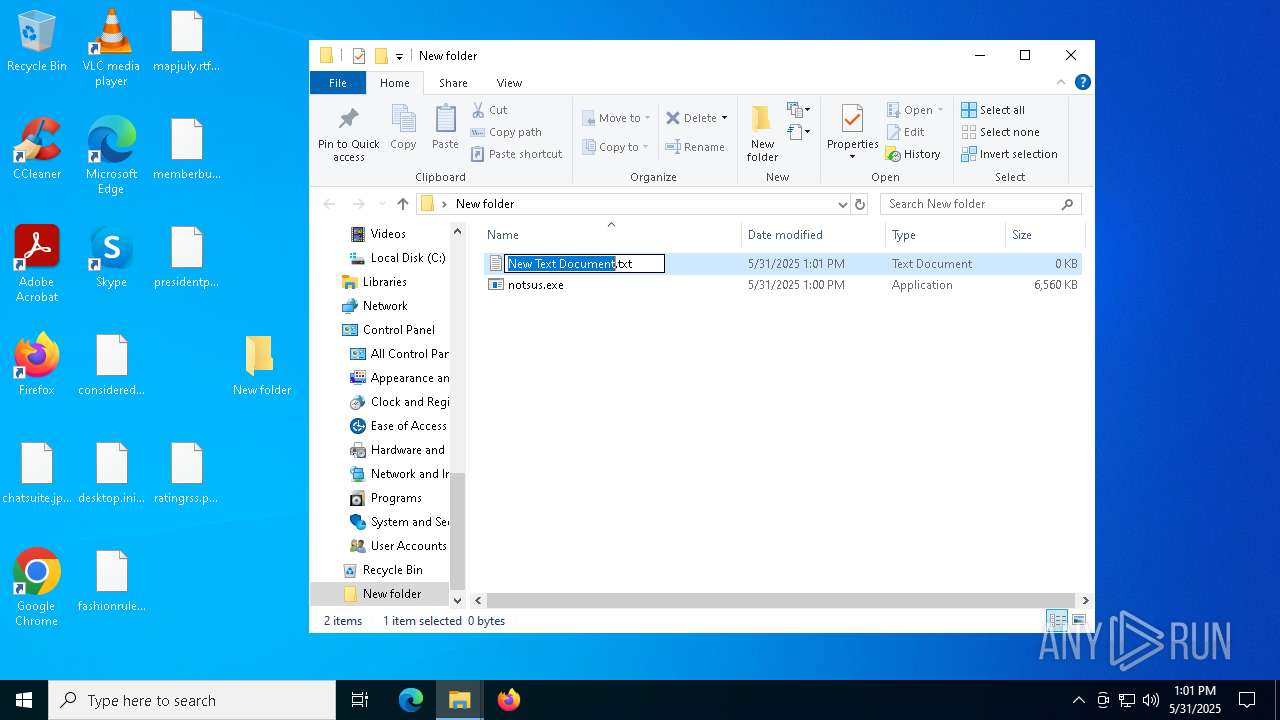
Create files in a temporary directory
- notsus.exe (PID: 4180)
- notsus.exe (PID: 7916)
Reads security settings of Internet Explorer
- notepad.exe (PID: 2268)
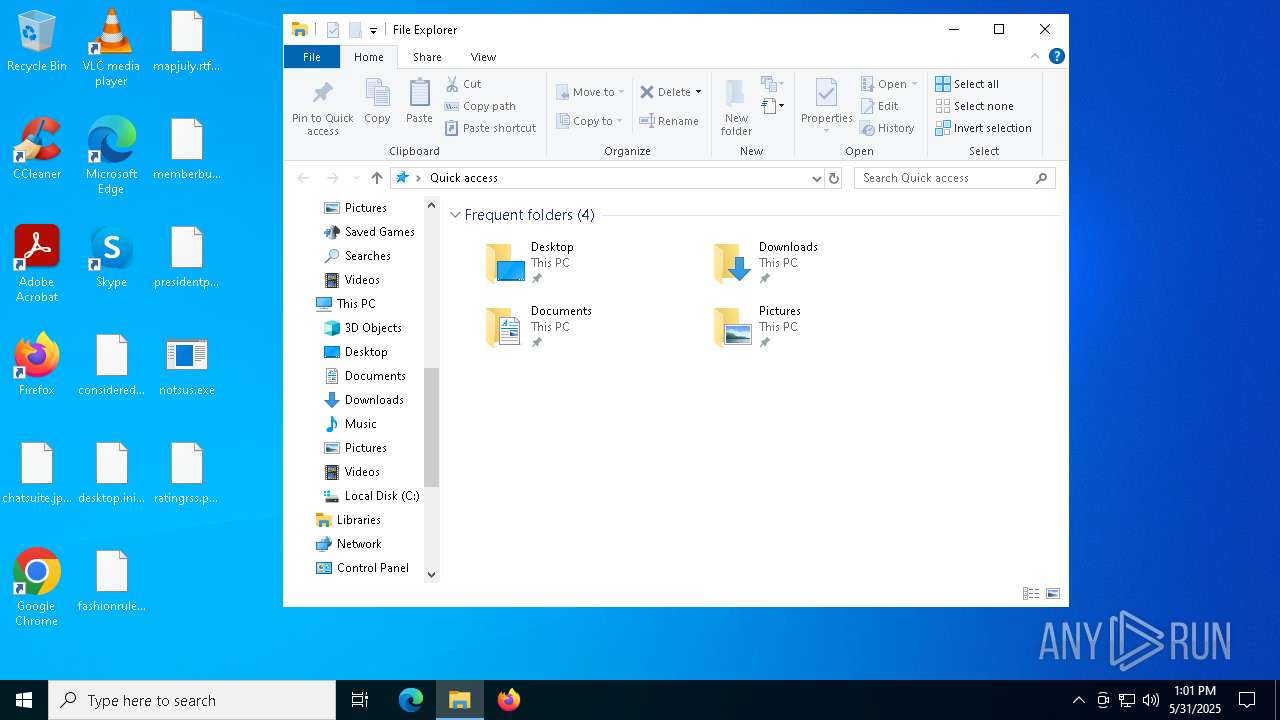
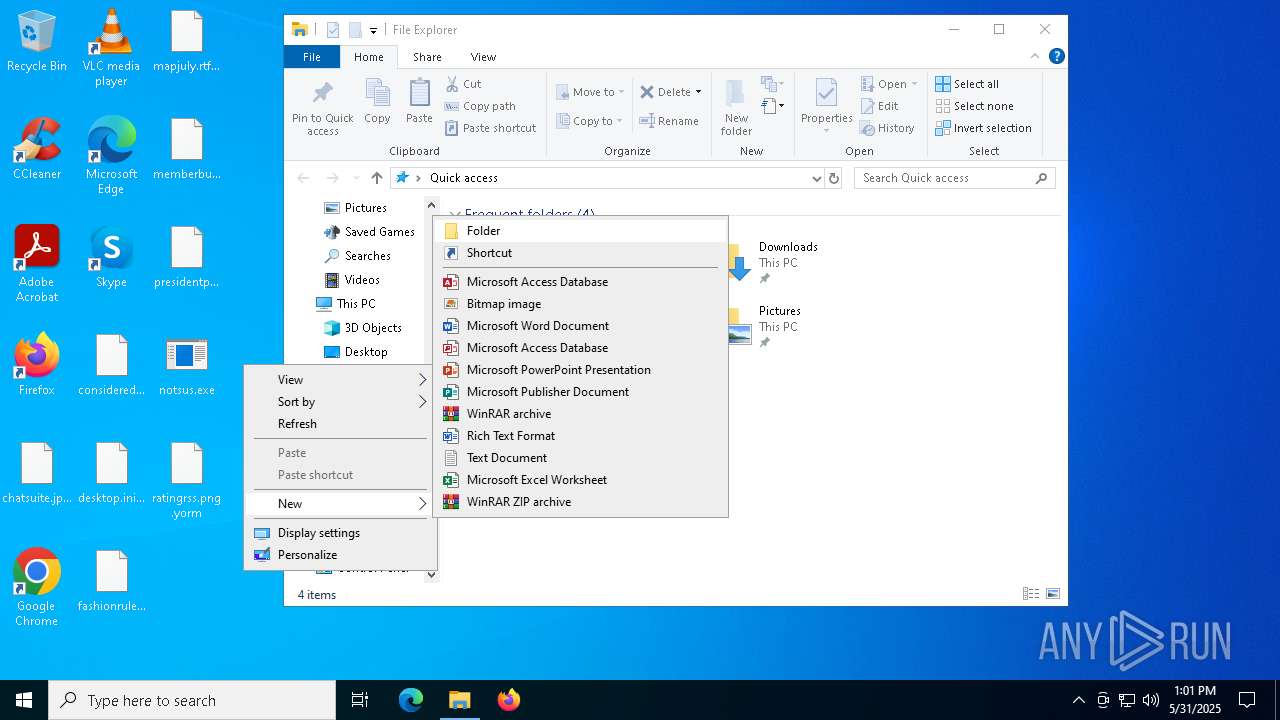
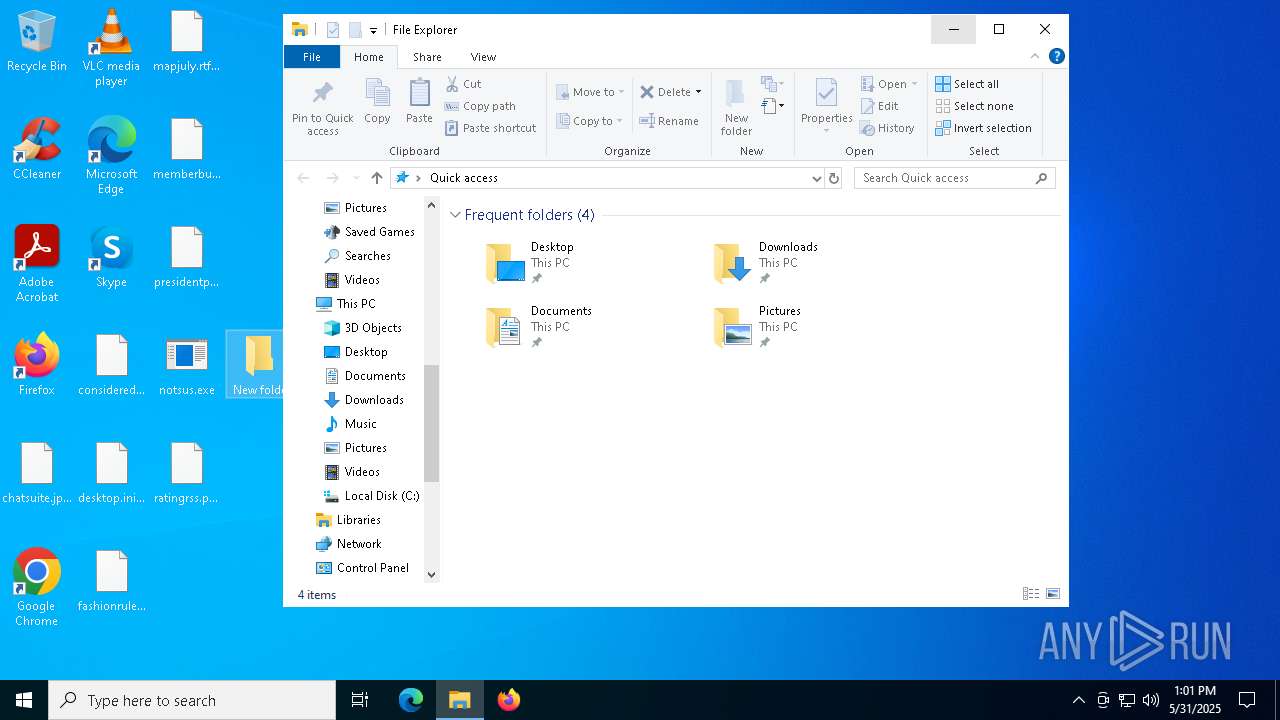
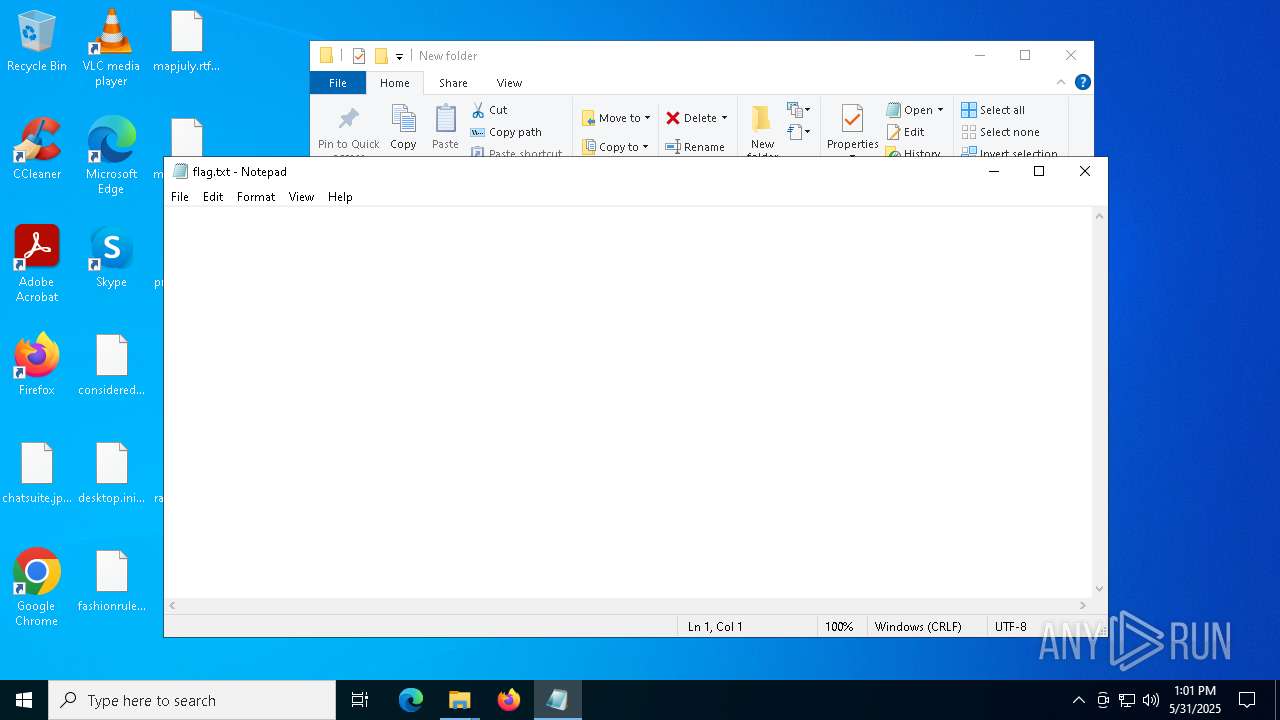
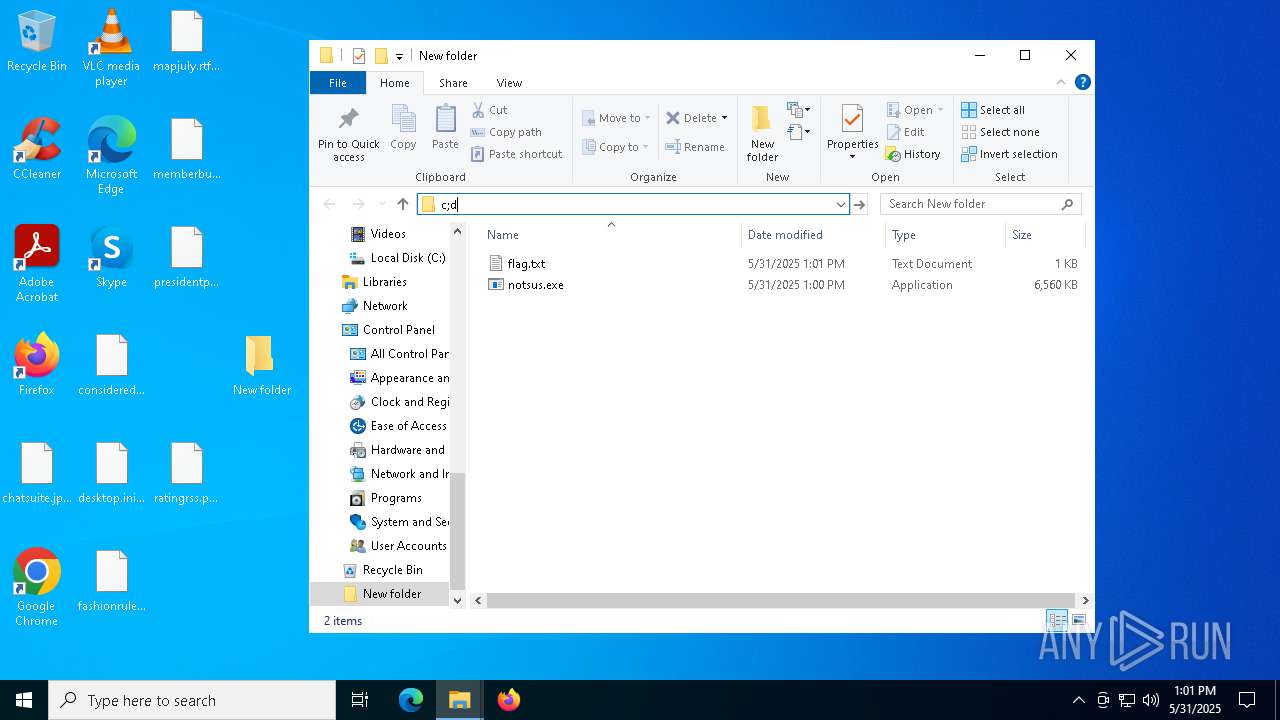
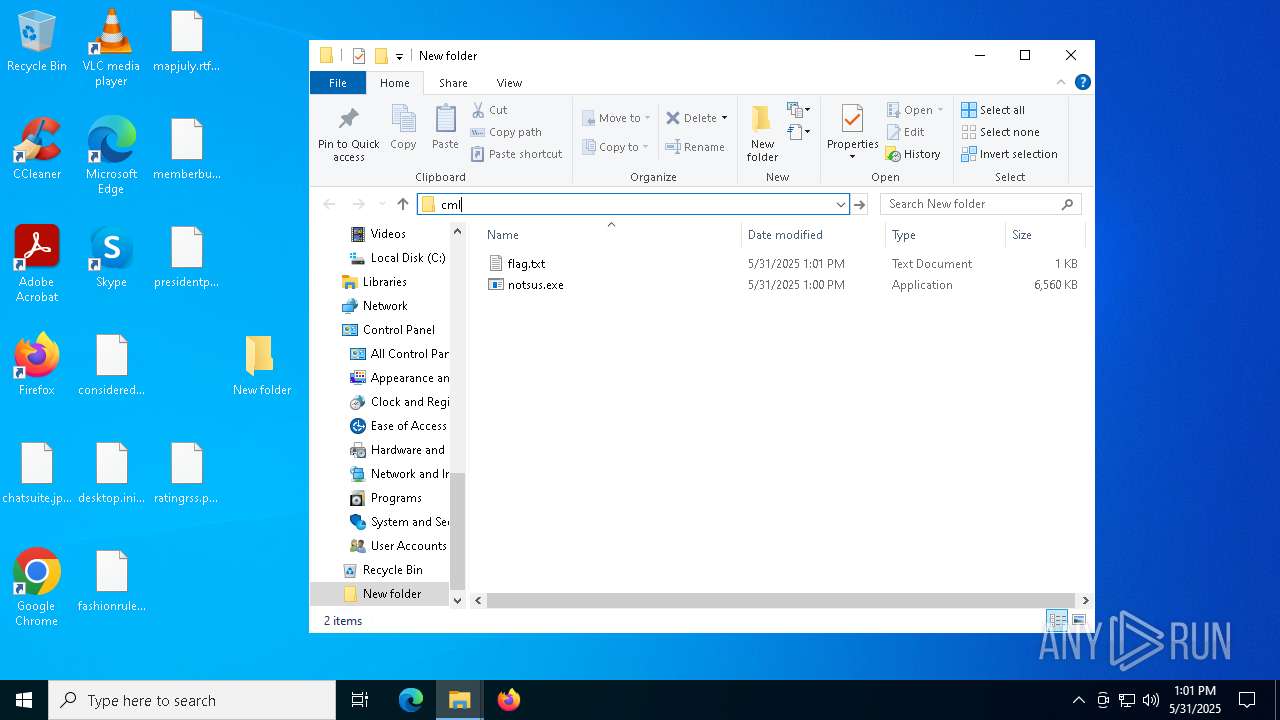
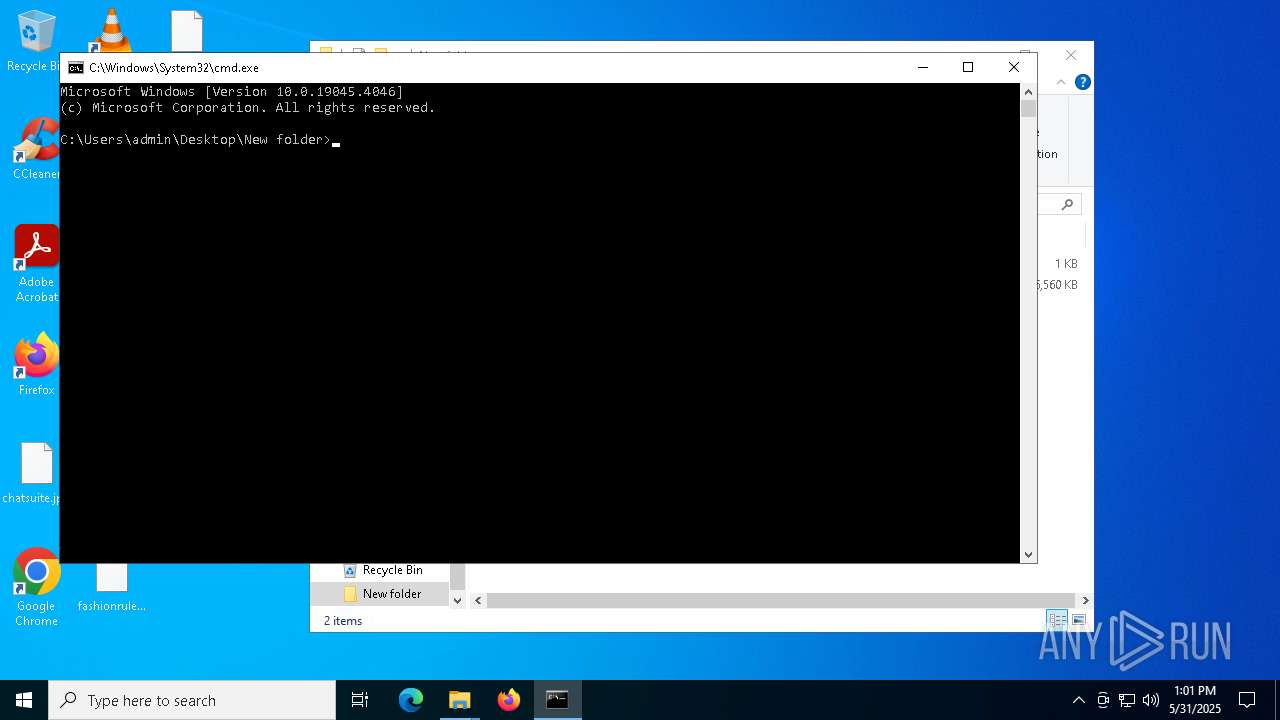
Manual execution by a user
- cmd.exe (PID: 5248)
- notepad.exe (PID: 2268)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:04:07 07:19:04+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 172032 |
| InitializedDataSize: | 93184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xcdb0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
128
Monitored processes
9
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1764 | notsus.exe | C:\Users\admin\Desktop\New folder\notsus.exe | — | notsus.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
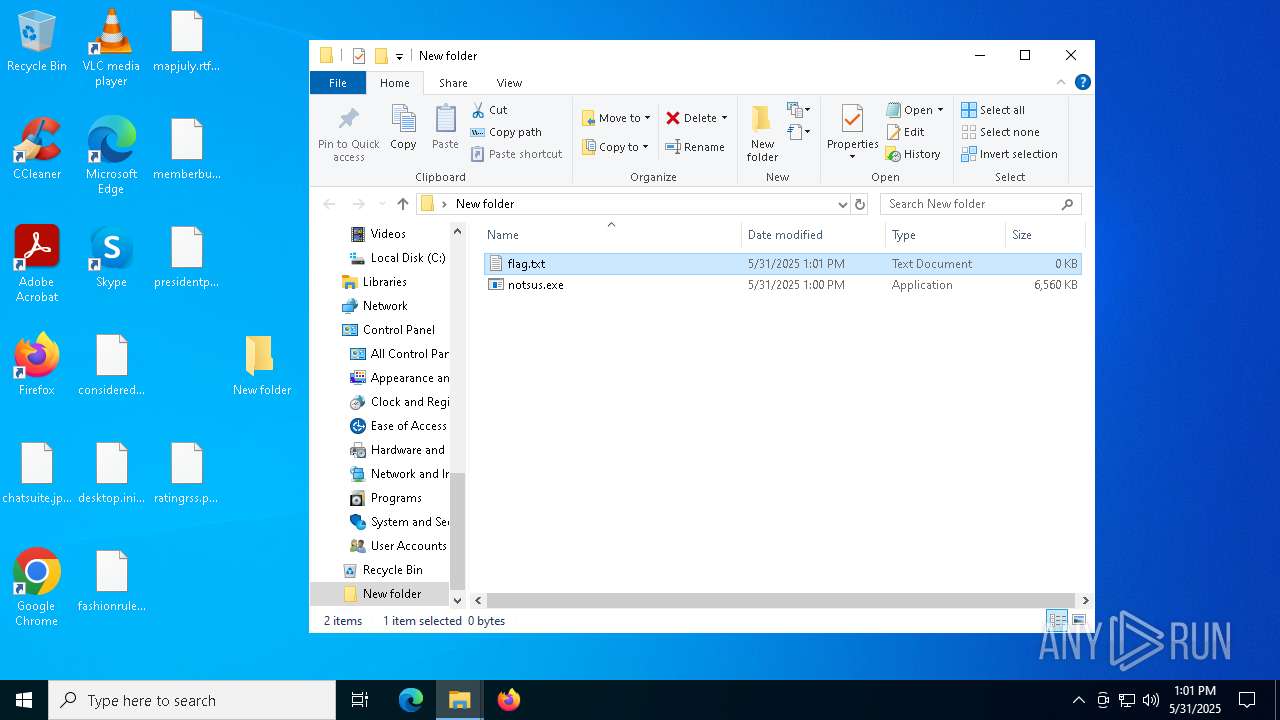
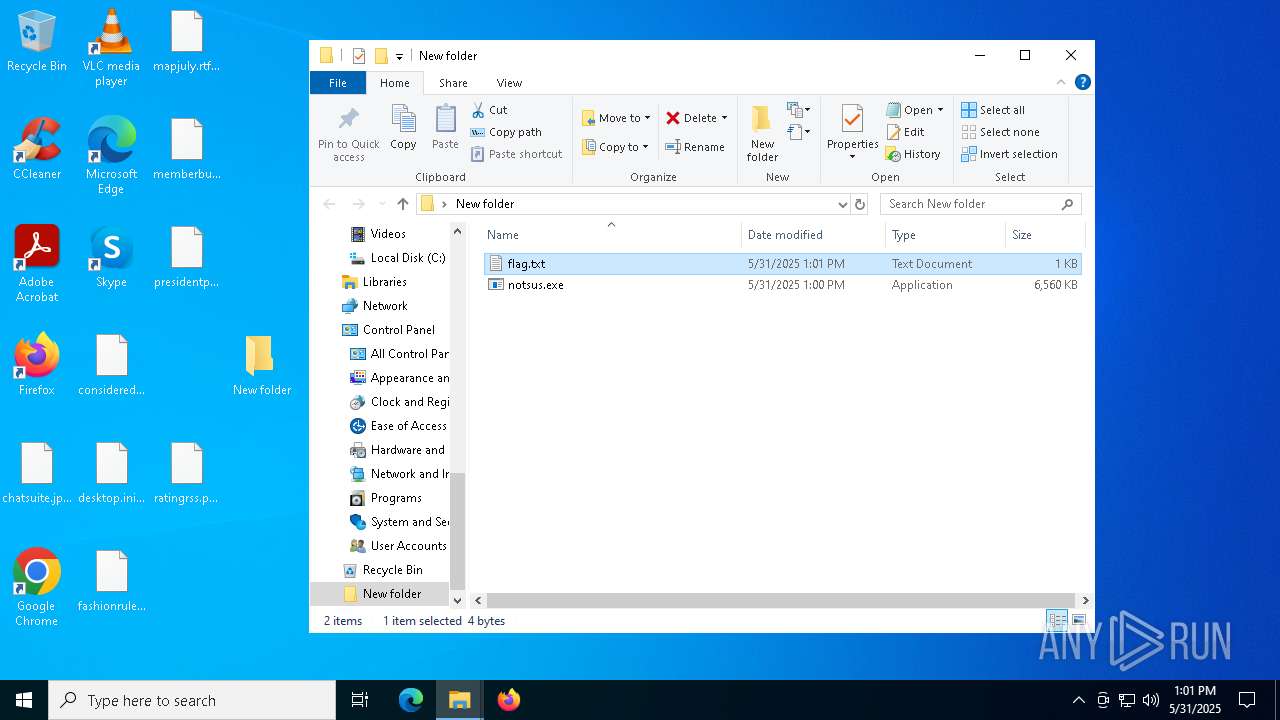
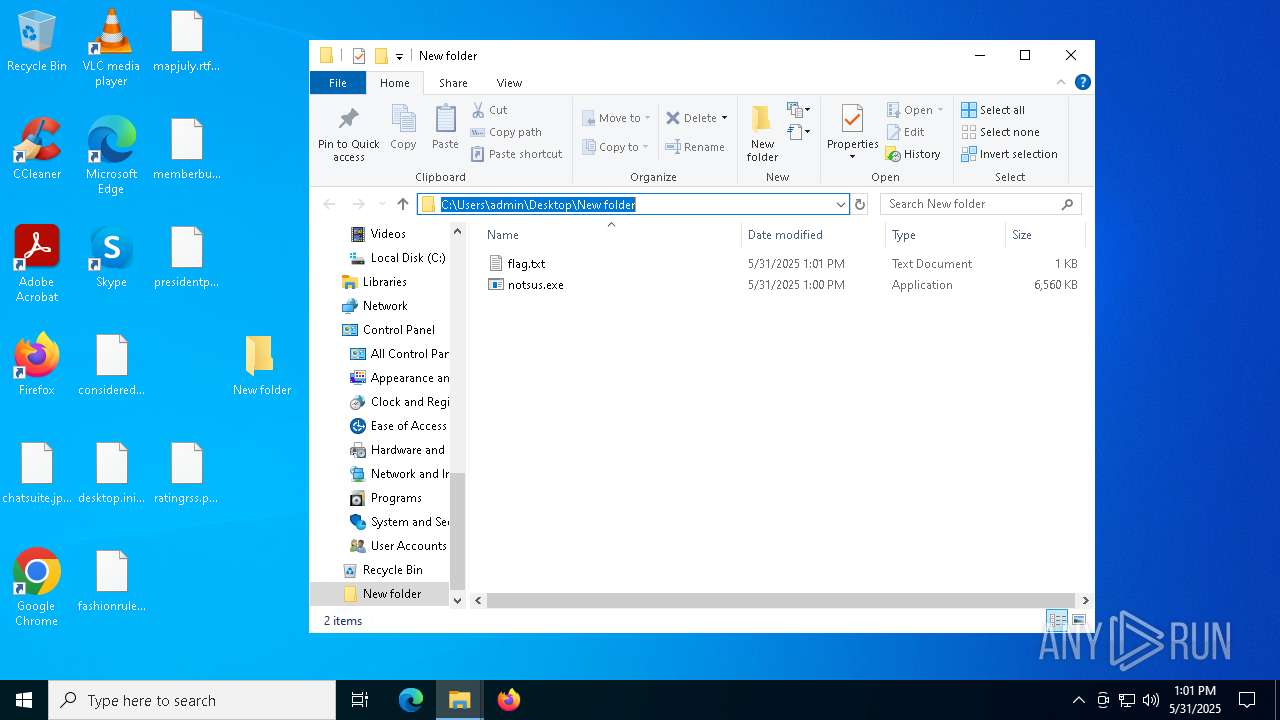
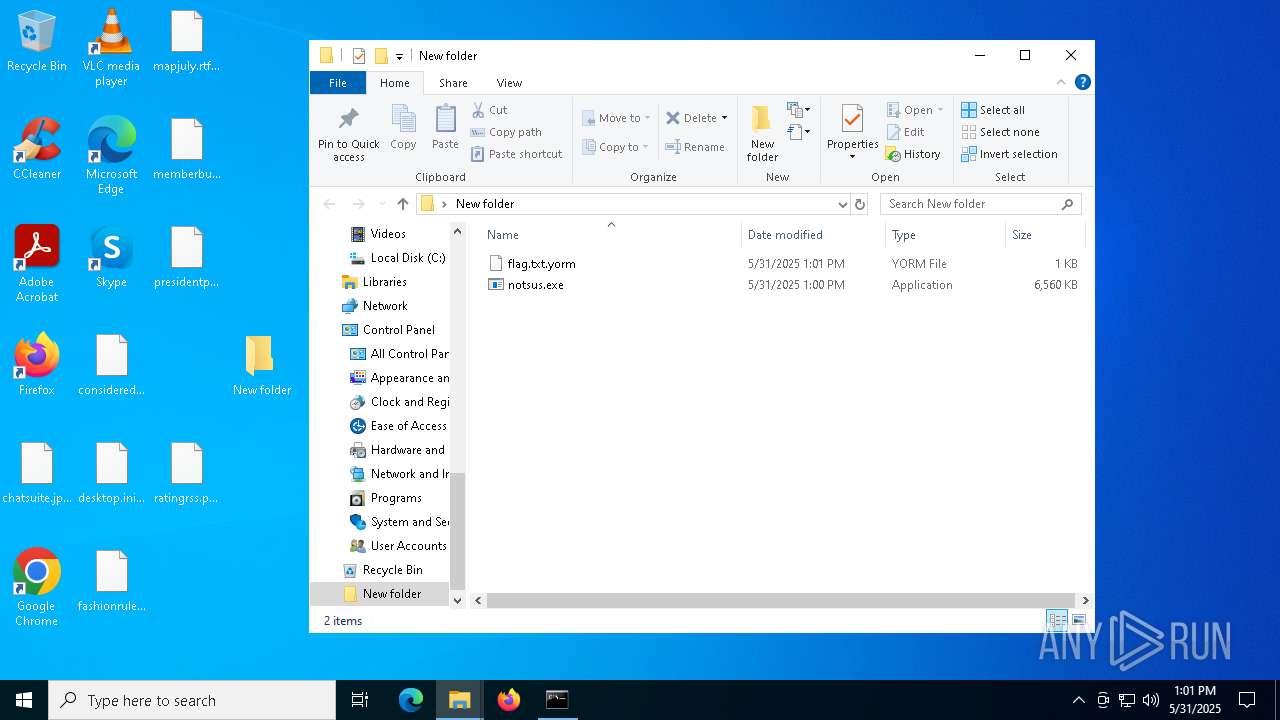
| 2268 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\New folder\flag.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4180 | "C:\Users\admin\Desktop\notsus.exe" | C:\Users\admin\Desktop\notsus.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5248 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5404 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5776 | "C:\Users\admin\Desktop\notsus.exe" | C:\Users\admin\Desktop\notsus.exe | — | notsus.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 7916 | notsus.exe | C:\Users\admin\Desktop\New folder\notsus.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 8044 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
370
Read events
370
Write events
0
Delete events
0
Modification events
Executable files
98
Suspicious files
11
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4180 | notsus.exe | C:\Users\admin\AppData\Local\Temp\_MEI41802\VCRUNTIME140.dll | executable | |
MD5:862F820C3251E4CA6FC0AC00E4092239 | SHA256:36585912E5EAF83BA9FEA0631534F690CCDC2D7BA91537166FE53E56C221E153 | |||
| 4180 | notsus.exe | C:\Users\admin\AppData\Local\Temp\_MEI41802\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:CFE0C1DFDE224EA5FED9BD5FF778A6E0 | SHA256:0D0F80CBF476AF5B1C9FD3775E086ED0DFDB510CD0CC208EC1CCB04572396E3E | |||
| 4180 | notsus.exe | C:\Users\admin\AppData\Local\Temp\_MEI41802\_decimal.pyd | executable | |
MD5:4C1FAF34695BB6BD80733887764E6AE1 | SHA256:8F09B7A917105CE679BC3BFE2AA017359CB62A000A08EC72B456AEC0EC1143BC | |||
| 4180 | notsus.exe | C:\Users\admin\AppData\Local\Temp\_MEI41802\_bz2.pyd | executable | |
MD5:341CB80C00875DC23EDD790DB235BA91 | SHA256:DE3D1177DA00E60AE820446071AE5FB3A94DB5B24A35D17C5013312B4DABC8EC | |||
| 4180 | notsus.exe | C:\Users\admin\AppData\Local\Temp\_MEI41802\api-ms-win-core-handle-l1-1-0.dll | executable | |
MD5:E89CDCD4D95CDA04E4ABBA8193A5B492 | SHA256:1A489E0606484BD71A0D9CB37A1DC6CA8437777B3D67BFC8C0075D0CC59E6238 | |||
| 4180 | notsus.exe | C:\Users\admin\AppData\Local\Temp\_MEI41802\api-ms-win-core-heap-l1-1-0.dll | executable | |
MD5:ACCC640D1B06FB8552FE02F823126FF5 | SHA256:332BA469AE84AA72EC8CCE2B33781DB1AB81A42ECE5863F7A3CB5A990059594F | |||
| 4180 | notsus.exe | C:\Users\admin\AppData\Local\Temp\_MEI41802\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:EFAD0EE0136532E8E8402770A64C71F9 | SHA256:3D2C55902385381869DB850B526261DDEB4628B83E690A32B67D2E0936B2C6ED | |||
| 4180 | notsus.exe | C:\Users\admin\AppData\Local\Temp\_MEI41802\api-ms-win-core-file-l2-1-0.dll | executable | |
MD5:BFFFA7117FD9B1622C66D949BAC3F1D7 | SHA256:1EA267A2E6284F17DD548C6F2285E19F7EDB15D6E737A55391140CE5CB95225E | |||
| 4180 | notsus.exe | C:\Users\admin\AppData\Local\Temp\_MEI41802\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:1C58526D681EFE507DEB8F1935C75487 | SHA256:EF13DCE8F71173315DFC64AB839B033AB19A968EE15230E9D4D2C9D558EFEEE2 | |||
| 4180 | notsus.exe | C:\Users\admin\AppData\Local\Temp\_MEI41802\api-ms-win-core-libraryloader-l1-1-0.dll | executable | |
MD5:1F2A00E72BC8FA2BD887BDB651ED6DE5 | SHA256:9C8A08A7D40B6F697A21054770F1AFA9FFB197F90EF1EEE77C67751DF28B7142 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
21
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7548 | svchost.exe | GET | 200 | 2.20.245.137:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7548 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
516 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
516 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7636 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
7548 | svchost.exe | 2.20.245.137:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
7548 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6544 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |