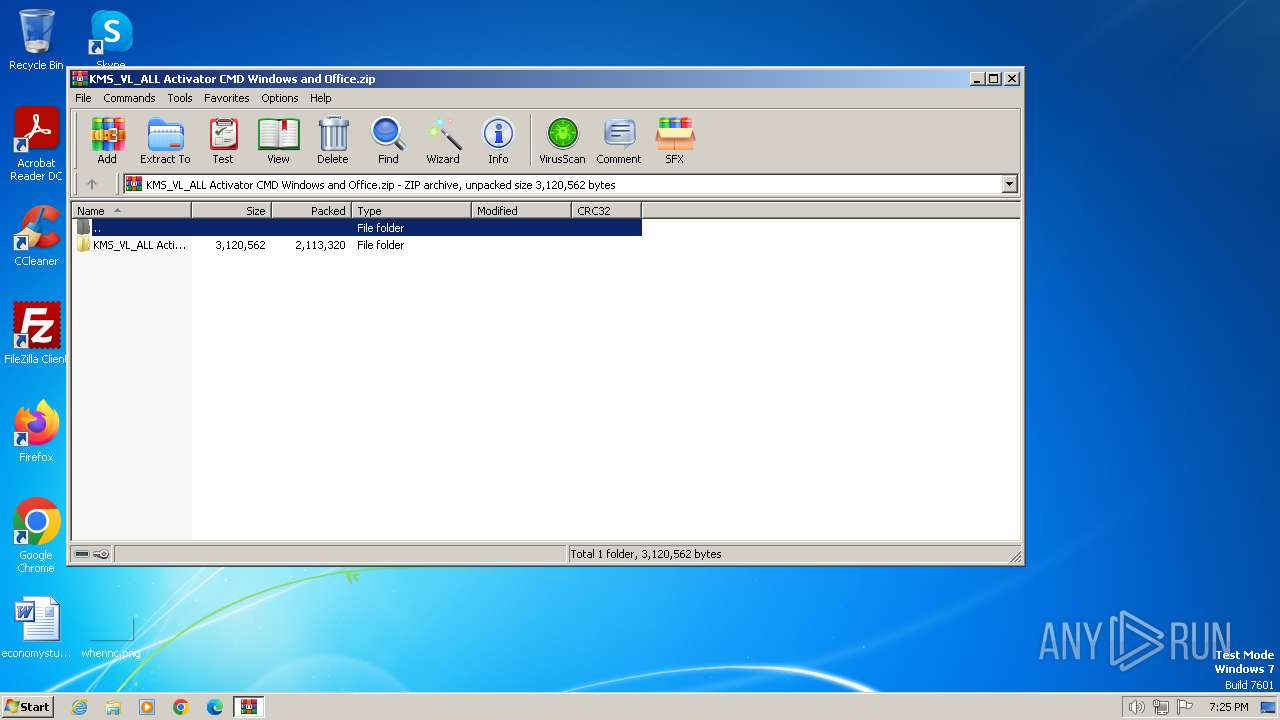
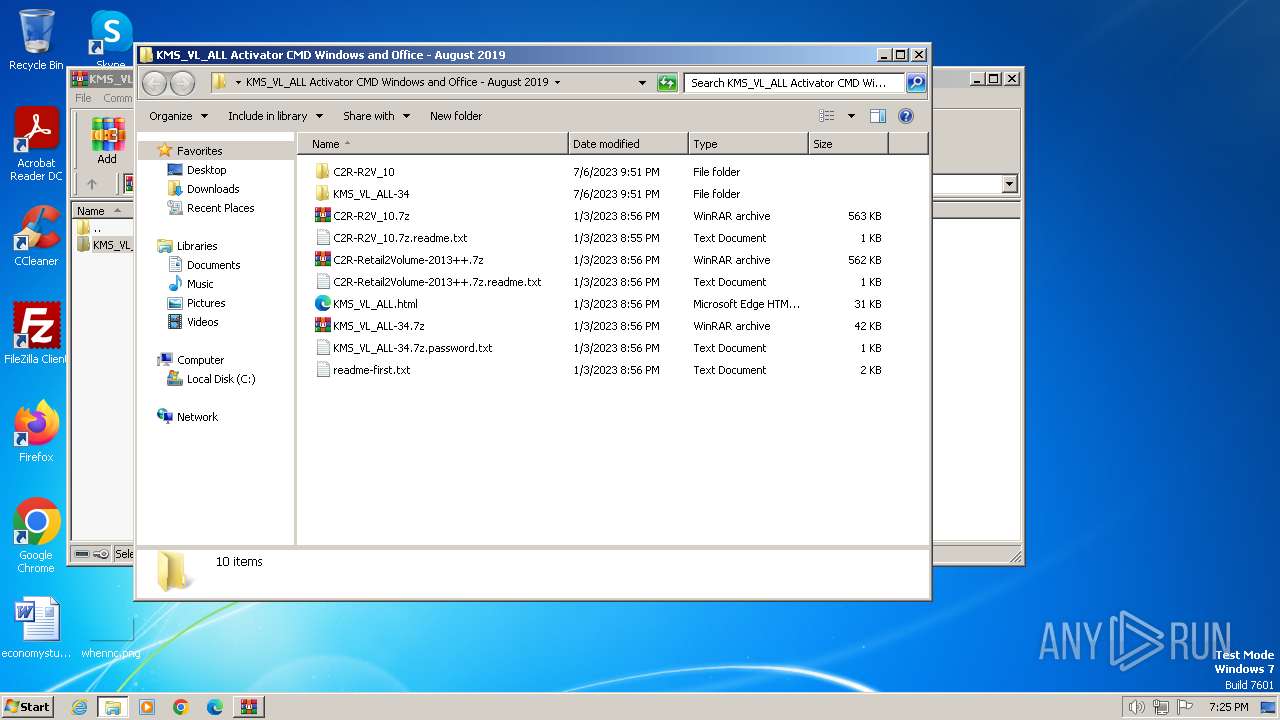
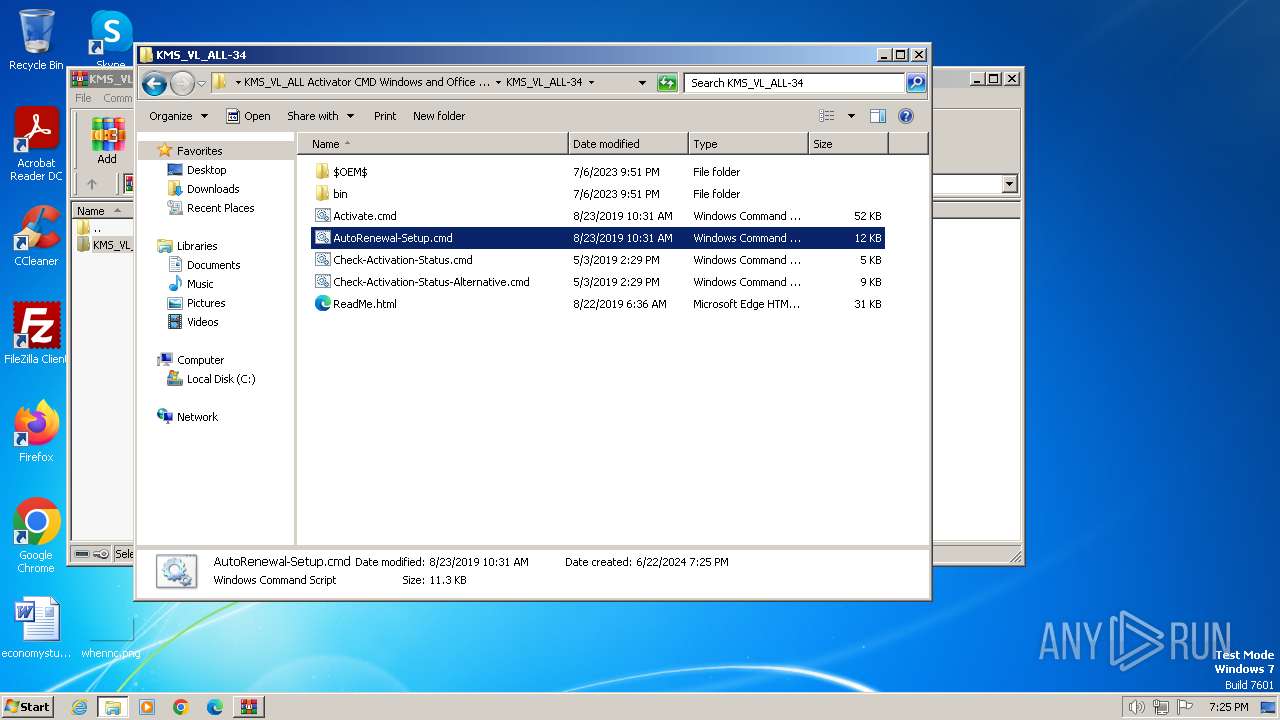
| File name: | KMS_VL_ALL Activator CMD Windows and Office.zip |
| Full analysis: | https://app.any.run/tasks/d4124ede-c32e-43a0-b601-85c63f33513b |
| Verdict: | Malicious activity |
| Analysis date: | June 22, 2024, 18:25:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 70216AC26494D967292E9D63C1CE6E13 |
| SHA1: | 9D66802EC9D00DD5A631C7FCD1330E40BA99D2CB |
| SHA256: | D6A70EF2731814B2F1B03C6693005EB9EC335741EACCD525CC9DF7D72FAEC324 |
| SSDEEP: | 98304:I/U8AEBBeErF7FEmz+zL2AbJJLxKEcgl9Hk6JiFWPmV54F59xa7Z/BvtWldMn8HN:Fb3 |
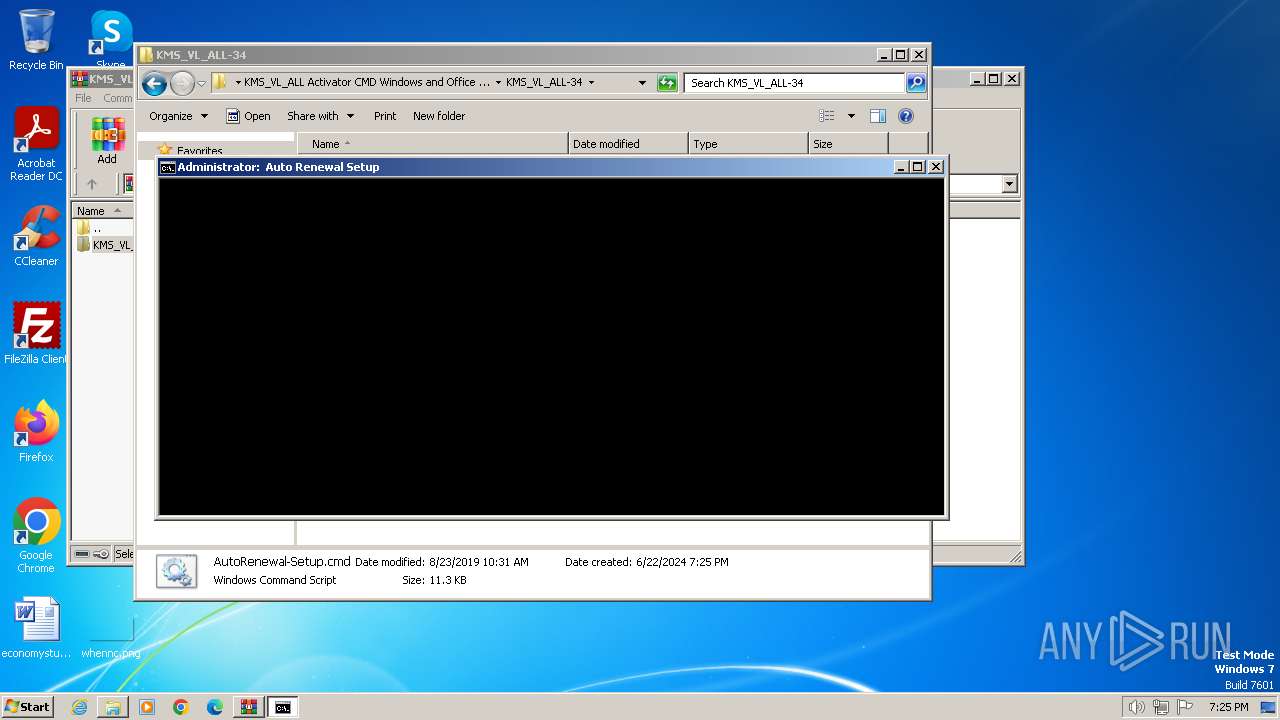
MALICIOUS
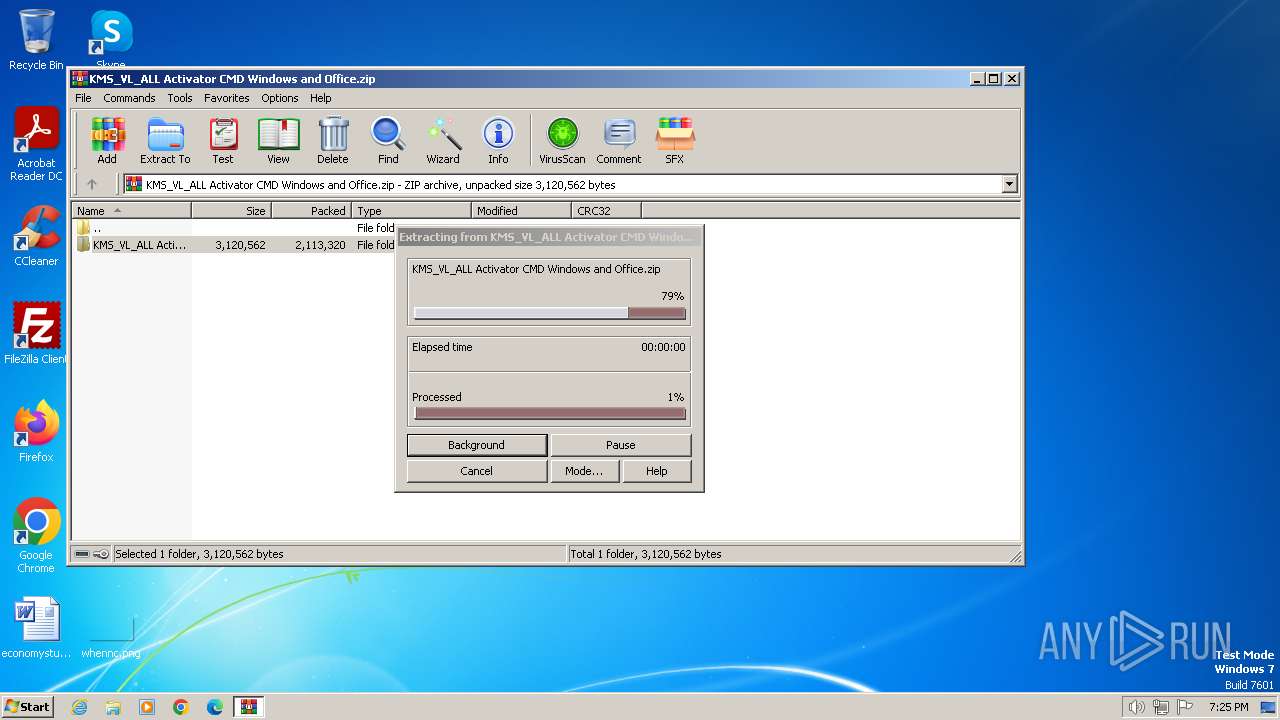
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3392)
- cmd.exe (PID: 3528)
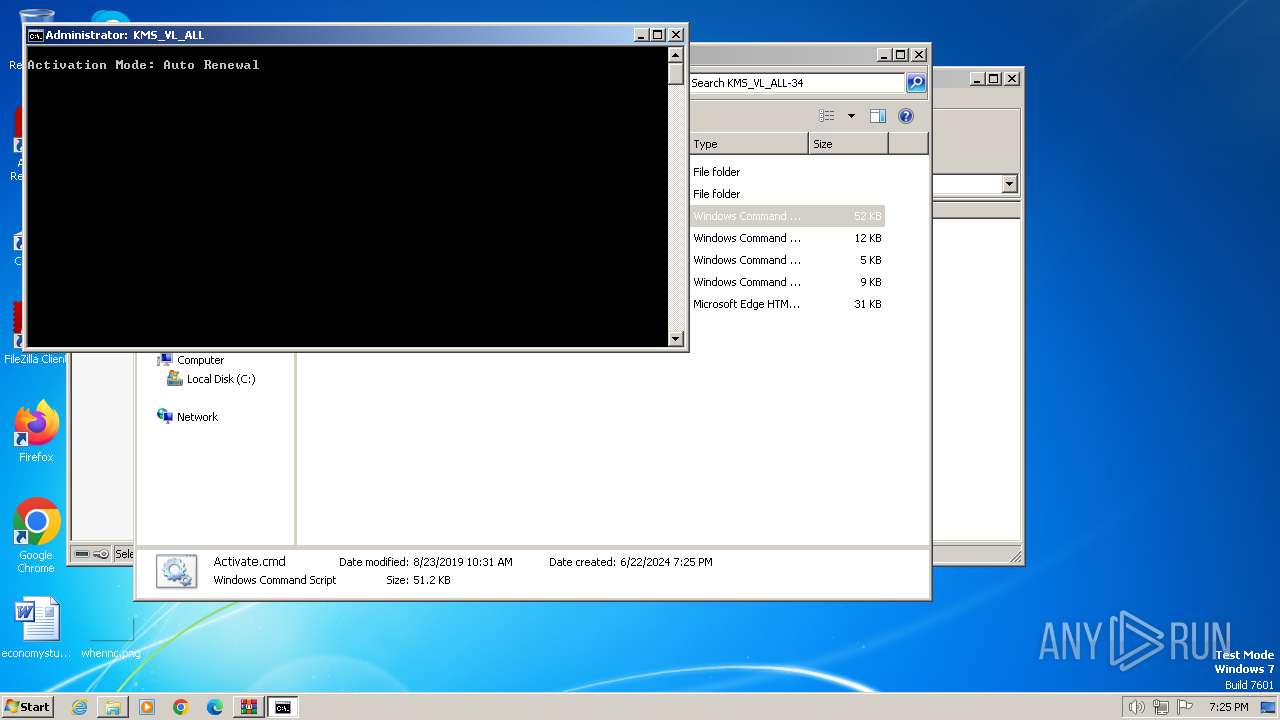
Starts NET.EXE for service management
- cmd.exe (PID: 3528)
- net.exe (PID: 3936)
- cmd.exe (PID: 2876)
- net.exe (PID: 1620)
- net.exe (PID: 2740)
Creates a writable file in the system directory
- cmd.exe (PID: 3528)
SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 3392)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3528)
- cmd.exe (PID: 2876)
Starts SC.EXE for service management
- cmd.exe (PID: 3528)
- cmd.exe (PID: 2876)
Application launched itself
- cmd.exe (PID: 3528)
- cmd.exe (PID: 2876)
Executable content was dropped or overwritten
- cmd.exe (PID: 3528)
The process drops C-runtime libraries
- WinRAR.exe (PID: 3392)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 3528)
- cmd.exe (PID: 2876)
Hides command output
- cmd.exe (PID: 2896)
- cmd.exe (PID: 2880)
- cmd.exe (PID: 3800)
- cmd.exe (PID: 2312)
- cmd.exe (PID: 2332)
- cmd.exe (PID: 3116)
- cmd.exe (PID: 2284)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2876)
Reads the Internet Settings
- WMIC.exe (PID: 3604)
- WMIC.exe (PID: 2260)
- WMIC.exe (PID: 3576)
- WMIC.exe (PID: 3284)
- WMIC.exe (PID: 3704)
- WMIC.exe (PID: 3052)
- WMIC.exe (PID: 828)
- WMIC.exe (PID: 3340)
- WMIC.exe (PID: 2300)
- WMIC.exe (PID: 3652)
- WMIC.exe (PID: 3484)
- WMIC.exe (PID: 3692)
- WMIC.exe (PID: 524)
- WMIC.exe (PID: 2500)
- WMIC.exe (PID: 936)
- WMIC.exe (PID: 1680)
- WMIC.exe (PID: 1044)
- WMIC.exe (PID: 3292)
- WMIC.exe (PID: 2532)
- WMIC.exe (PID: 3428)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 2876)
- cmd.exe (PID: 2660)
- cmd.exe (PID: 1504)
- cmd.exe (PID: 980)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 3564)
- cmd.exe (PID: 2876)
- cmd.exe (PID: 3116)
INFO
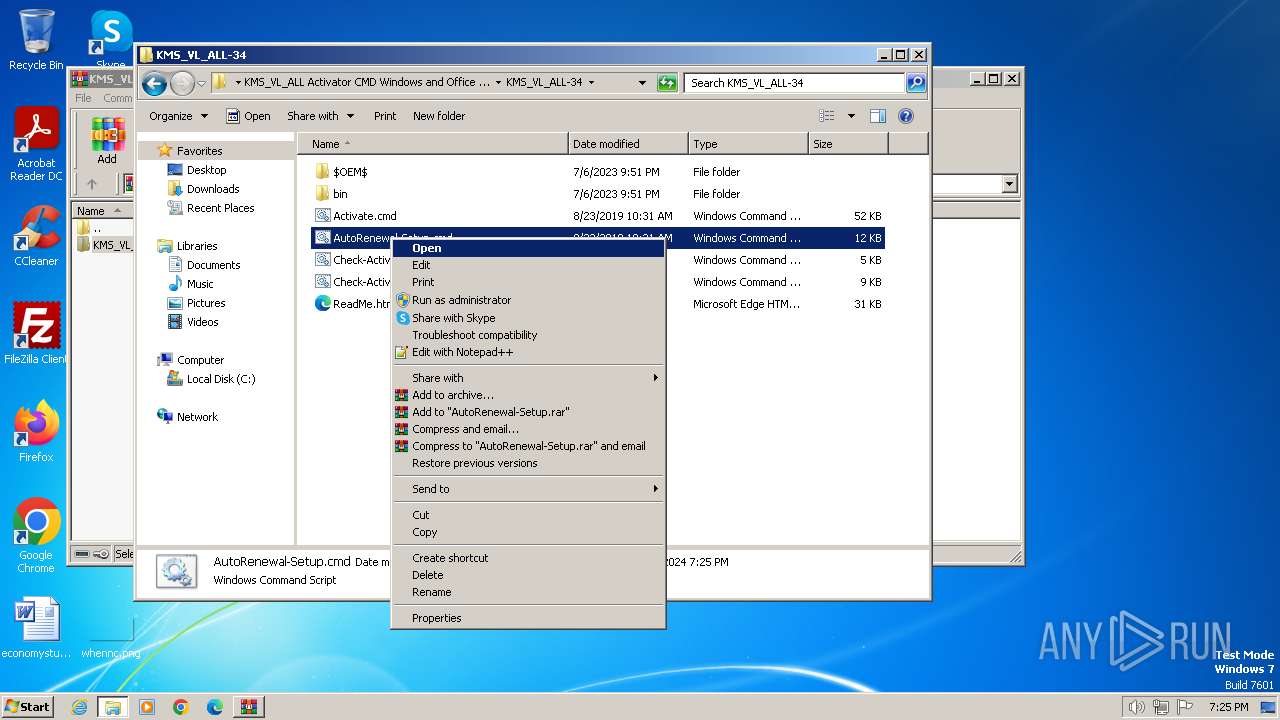
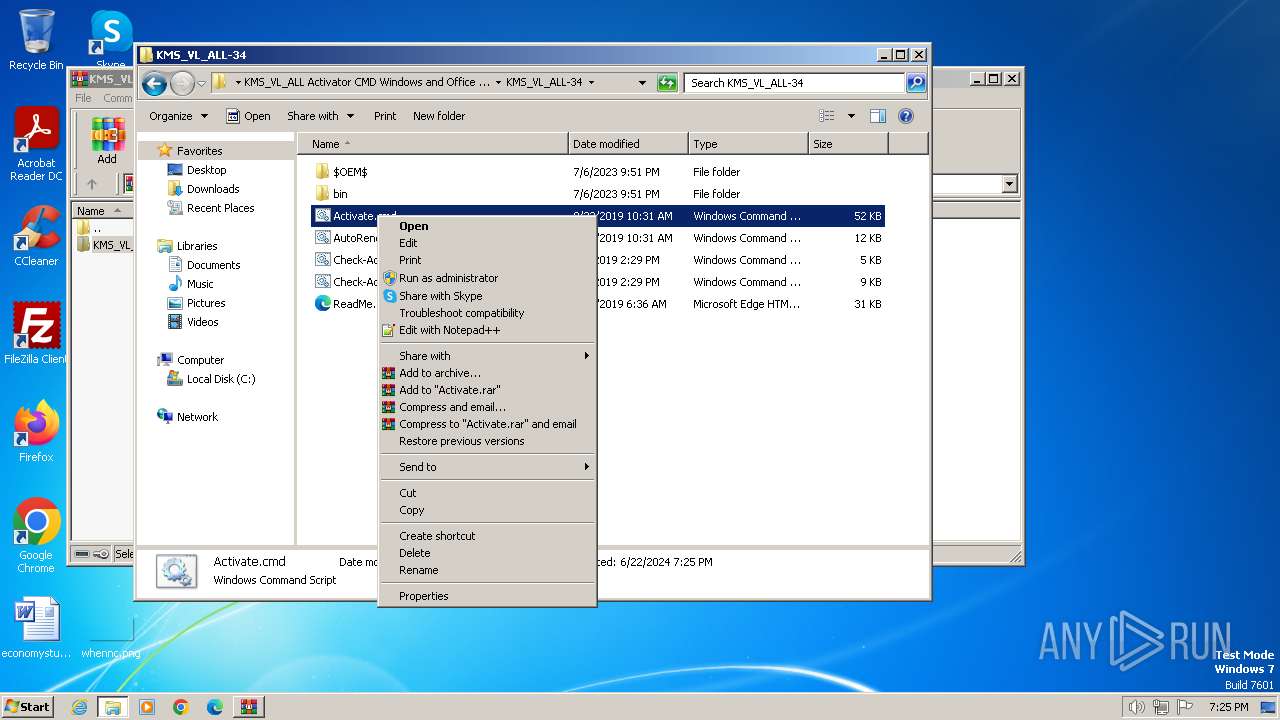
Manual execution by a user
- cmd.exe (PID: 3528)
- cmd.exe (PID: 2876)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3392)
Checks supported languages
- mode.com (PID: 2980)
Checks operating system version
- cmd.exe (PID: 3528)
- cmd.exe (PID: 2876)
Reads Microsoft Office registry keys
- reg.exe (PID: 1516)
- reg.exe (PID: 3324)
- reg.exe (PID: 2444)
- reg.exe (PID: 2892)
- reg.exe (PID: 328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2023:01:03 20:56:04 |
| ZipCRC: | 0x80c9d2a1 |
| ZipCompressedSize: | 576419 |
| ZipUncompressedSize: | 576239 |
| ZipFileName: | KMS_VL_ALL Activator CMD Windows and Office - August 2019/C2R-R2V_10.7z |
Total processes
165
Monitored processes
115
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 328 | reg add "HKLM\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform" /f /v KeyManagementServicePort /t REG_SZ /d 1688 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 368 | reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe" /f /v KMS_RenewalInterval /t REG_DWORD /d 10080 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 448 | reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sppsvc.exe" /f /v KMS_RenewalInterval /t REG_DWORD /d 10080 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 524 | find /i "STOPPED" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 524 | wmic path OfficeSoftwareProtectionService where version='14.0.370.400' call SetKeyManagementServiceMachine MachineName="172.16.0.2" | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 568 | reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\SppExtComObj.exe" /f /v KMS_Emulation /t REG_DWORD /d 1 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 744 | sc query sppsvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 748 | sc query sppsvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 764 | reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sppsvc.exe" /f /v GlobalFlag /t REG_DWORD /d 256 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 828 | wmic path SoftwareLicensingService where version='6.1.7601.17514' call SetKeyManagementServicePort 1688 | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8 422
Read events
8 392
Write events
30
Delete events
0
Modification events
| (PID) Process: | (3392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3392) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\KMS_VL_ALL Activator CMD Windows and Office.zip | |||
| (PID) Process: | (3392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3392) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
9
Suspicious files
3
Text files
17
Unknown types
0
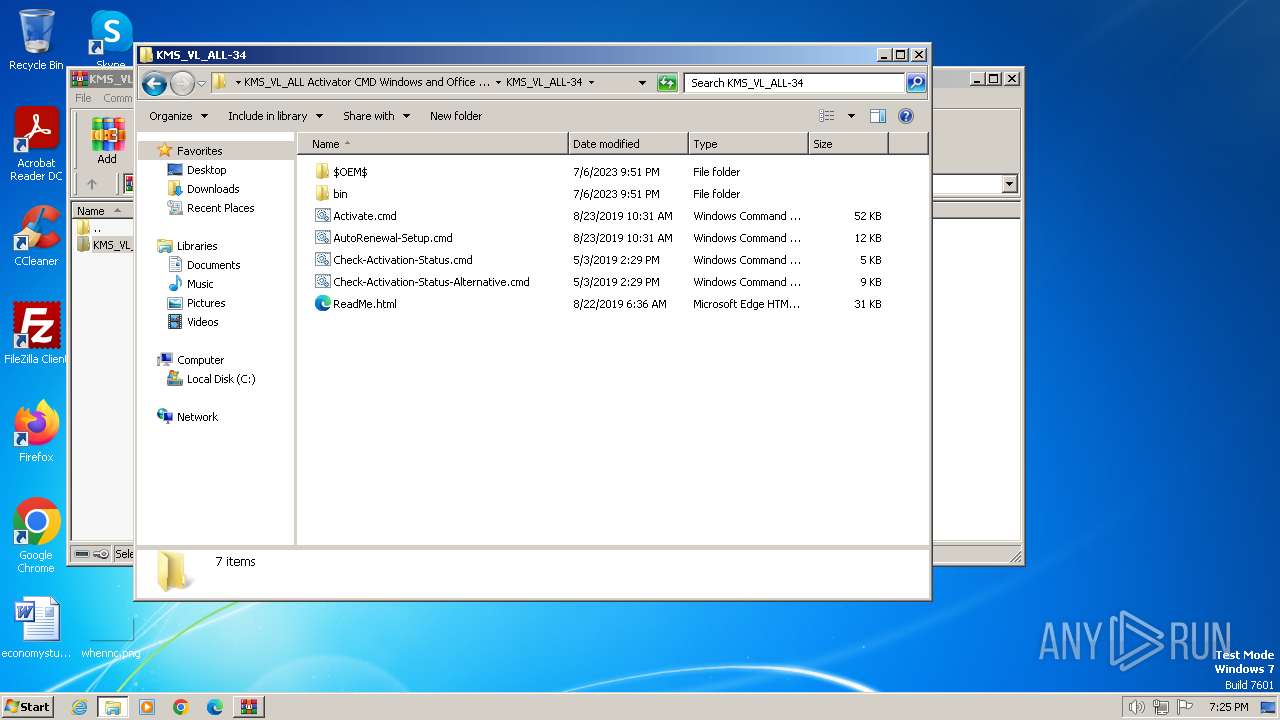
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3392.3497\KMS_VL_ALL Activator CMD Windows and Office - August 2019\C2R-R2V_10\ReadMe.txt | text | |
MD5:74CE1F1056543667C25CAB55494A8F32 | SHA256:9E433B8B216AE9EE9FAF0C2C0ED6C284DDD0F45AEF2D42DABF59E2022F1EE95A | |||
| 3392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3392.3497\KMS_VL_ALL Activator CMD Windows and Office - August 2019\C2R-R2V_10.7z | compressed | |
MD5:B7C7A6F8F964789CFCF354F1BB7DDE2A | SHA256:B6666FCDF10992E4665F196370B9D6F8ADE9657FB9E7A473C2472A7563509C64 | |||
| 3392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3392.3497\KMS_VL_ALL Activator CMD Windows and Office - August 2019\C2R-R2V_10\Convert-C2R.cmd | text | |
MD5:2FA13A10ECE3AADBAC86796D49A375DE | SHA256:1AF6186BD9DBBD38BFB60134CA8B9B532E6D0EA1B961A513C45B6009FDE2D348 | |||
| 3392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3392.3497\KMS_VL_ALL Activator CMD Windows and Office - August 2019\C2R-R2V_10\x64\msvcr100.dll | executable | |
MD5:DF3CA8D16BDED6A54977B30E66864D33 | SHA256:1D1A1AE540BA132F998D60D3622F0297B6E86AE399332C3B47462D7C0F560A36 | |||
| 3392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3392.3497\KMS_VL_ALL Activator CMD Windows and Office - August 2019\KMS_VL_ALL-34\$OEM$\$\Setup\Scripts\bin\x64.dll | executable | |
MD5:95F143EC661A5DA85C3C8199D9FE06E7 | SHA256:F239C27B50CEF792FEA5B34378FBAC83BCC06B8442D508BD9ADD7DDF8CA5C632 | |||
| 3392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3392.3497\KMS_VL_ALL Activator CMD Windows and Office - August 2019\KMS_VL_ALL-34\$OEM$\$\Setup\Scripts\setupcomplete.cmd | text | |
MD5:39D935D40011E9C18D4073156271D38E | SHA256:712E3FDAFD23A808890D64736DDEE015FDEAEEF33487D485BA8D04063297533A | |||
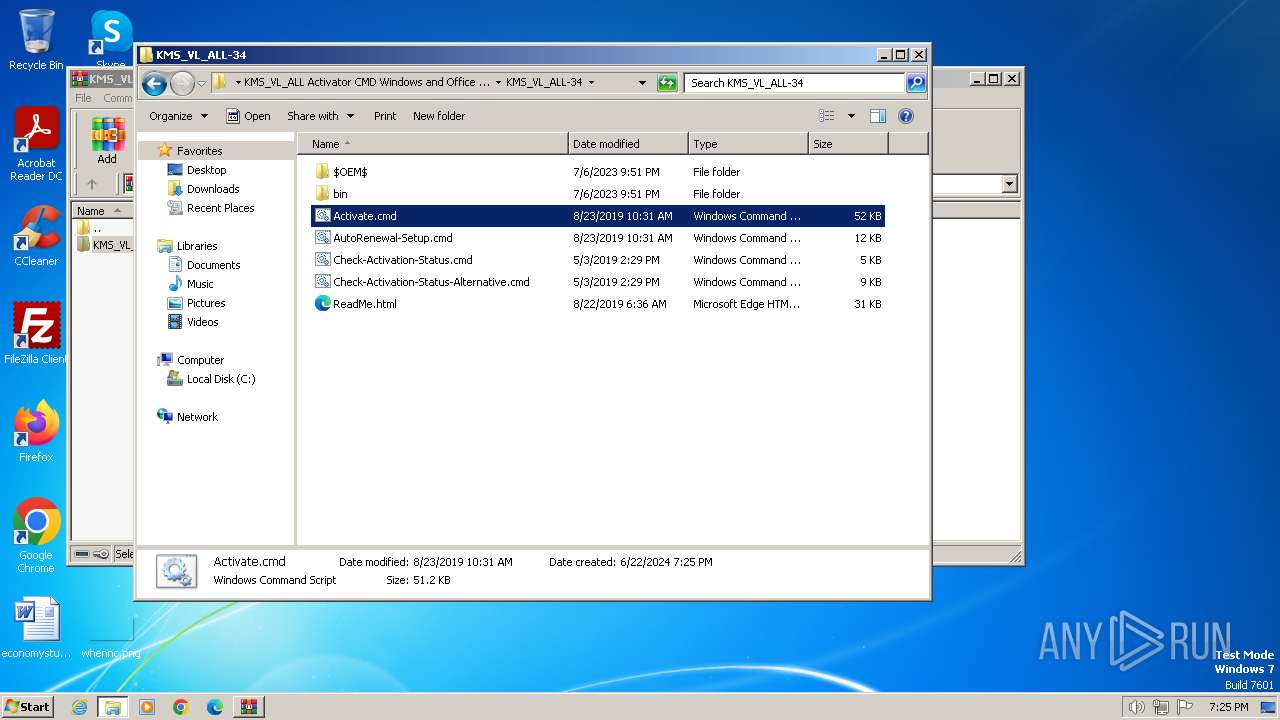
| 3392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3392.3497\KMS_VL_ALL Activator CMD Windows and Office - August 2019\KMS_VL_ALL-34\Activate.cmd | text | |
MD5:9423A173907BE23FE1138F386D01A5B6 | SHA256:2383BE6C1457CC3E320BB3E5108B4B81D47F2DF7DEA6E37A803B037815FBA9CB | |||
| 3392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3392.3497\KMS_VL_ALL Activator CMD Windows and Office - August 2019\C2R-R2V_10\x86\keyOff.cmd | text | |
MD5:02078EAEF801CD3498B7BDF999A026C5 | SHA256:36E273A678DAC6ADB759DF59AB6B46FB7514418B113D07CA14D1A1C8C2CD91DB | |||
| 3392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3392.3497\KMS_VL_ALL Activator CMD Windows and Office - August 2019\C2R-R2V_10.7z.readme.txt | text | |
MD5:1690F1B235018F7F6AEAAEA379537CC9 | SHA256:10DB241297CA5FBF5FF7755BA03A4C3DE0178194EC65D00C4CCBFAA7651C3ABC | |||
| 3392 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3392.3497\KMS_VL_ALL Activator CMD Windows and Office - August 2019\C2R-R2V_10\x64\cleanospp.exe | executable | |
MD5:162AB955CB2F002A73C1530AA796477F | SHA256:5CE462E5F34065FC878362BA58617FAB28C22D631B9D836DDDCF43FB1AD4DE6E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
10
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 2.16.164.43:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 2.19.126.163:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
1372 | svchost.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
1372 | svchost.exe | 2.16.164.43:80 | crl.microsoft.com | Akamai International B.V. | NL | unknown |
1372 | svchost.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
1060 | svchost.exe | 2.19.126.163:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |