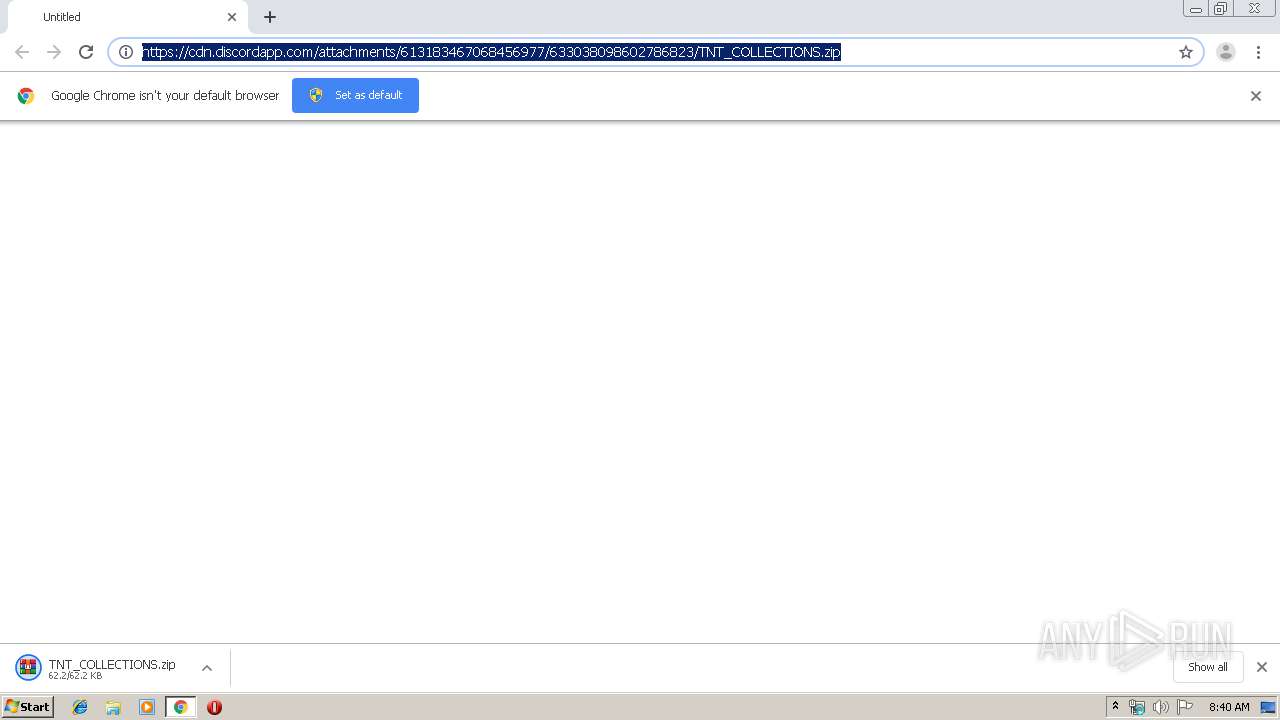
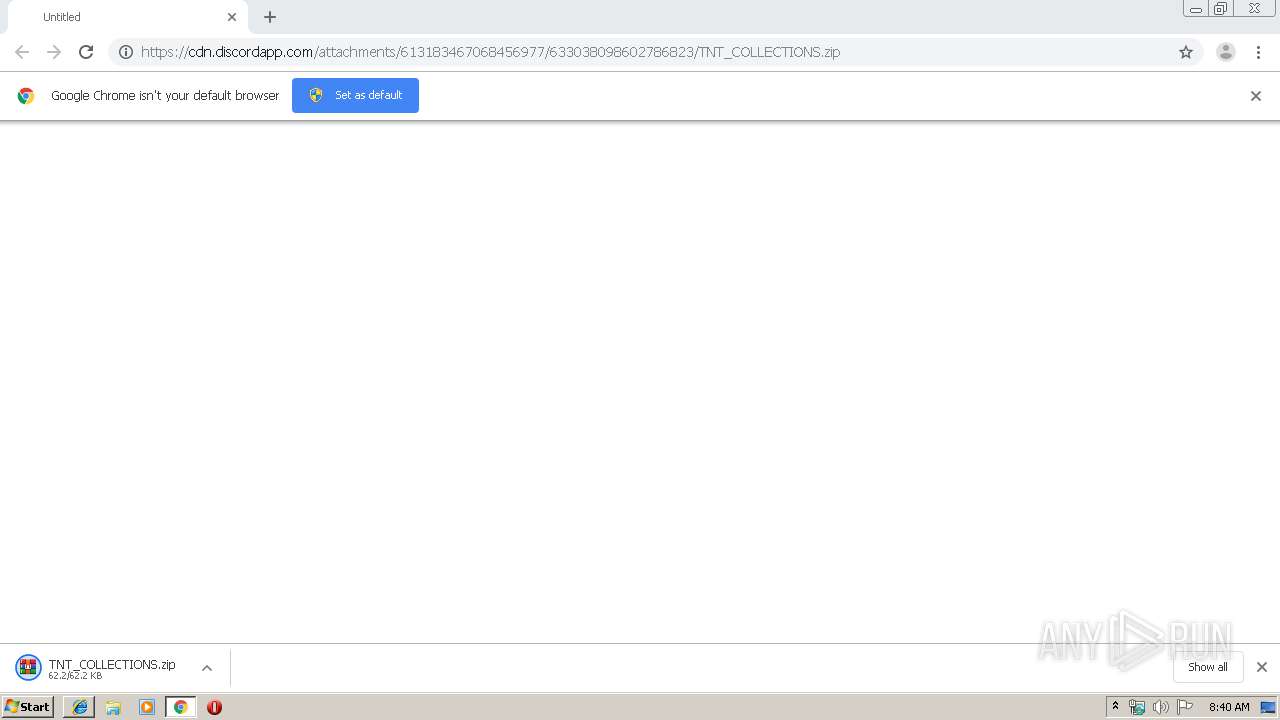
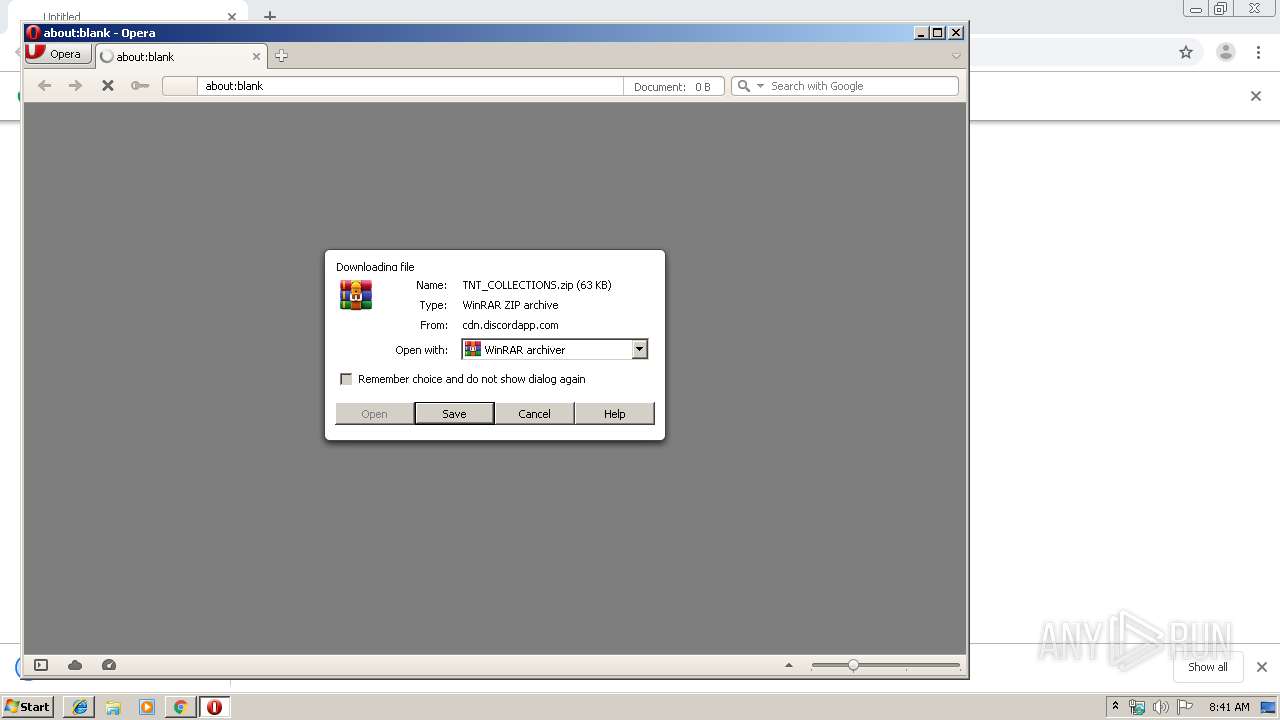
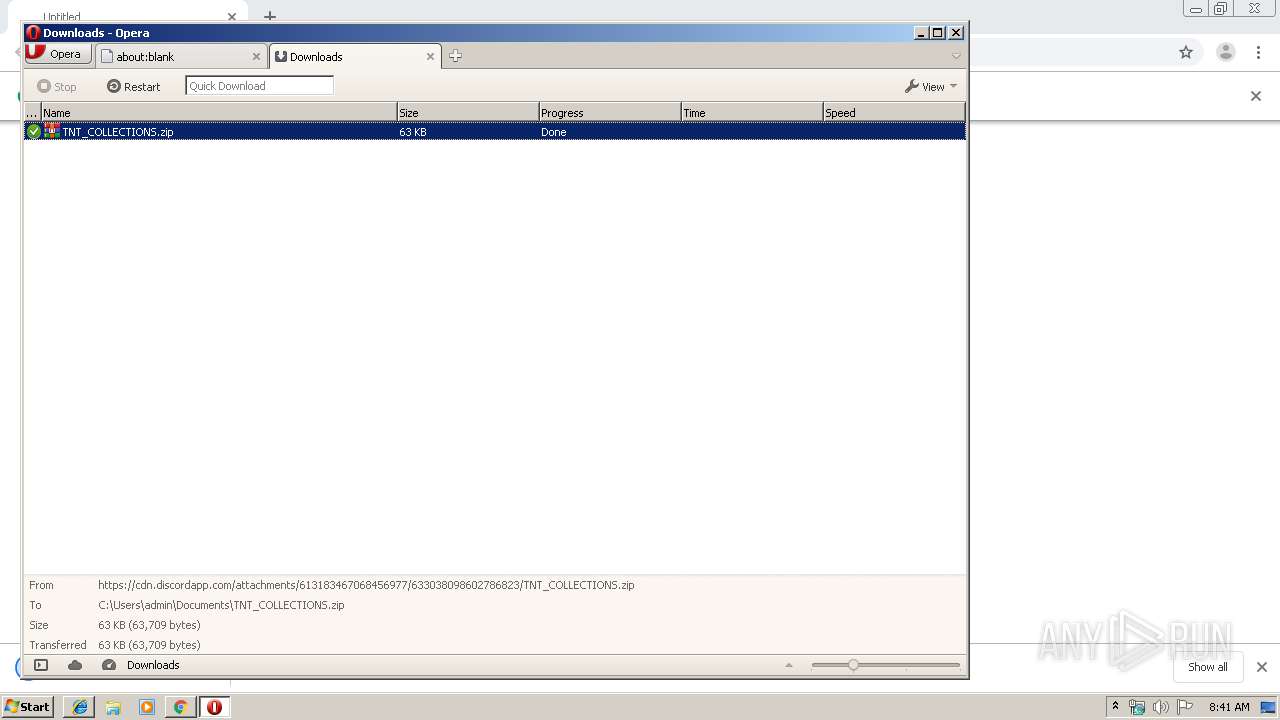
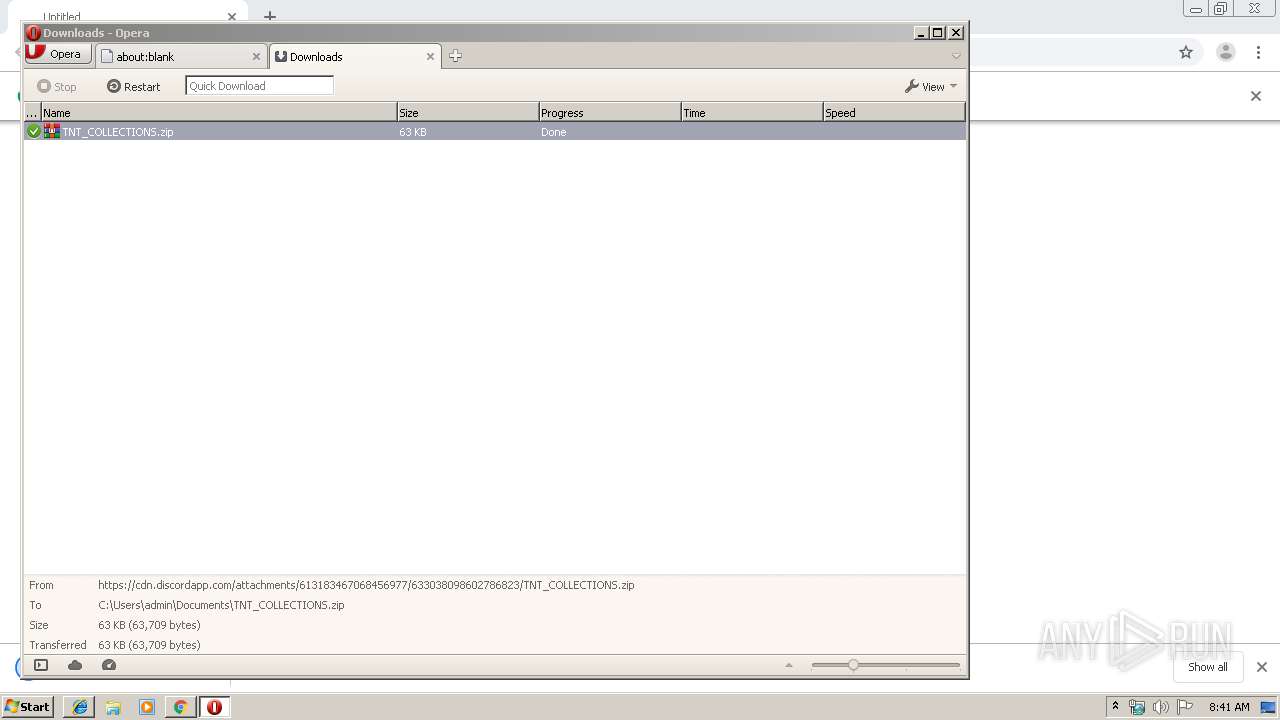
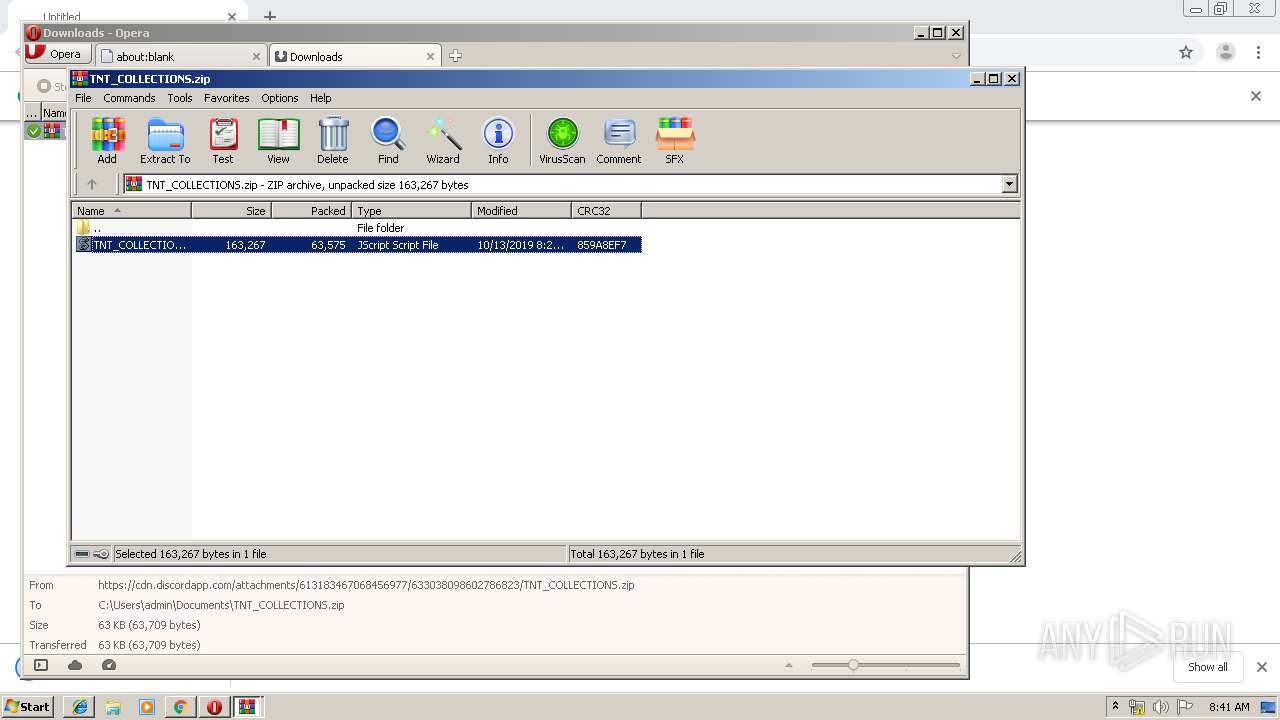
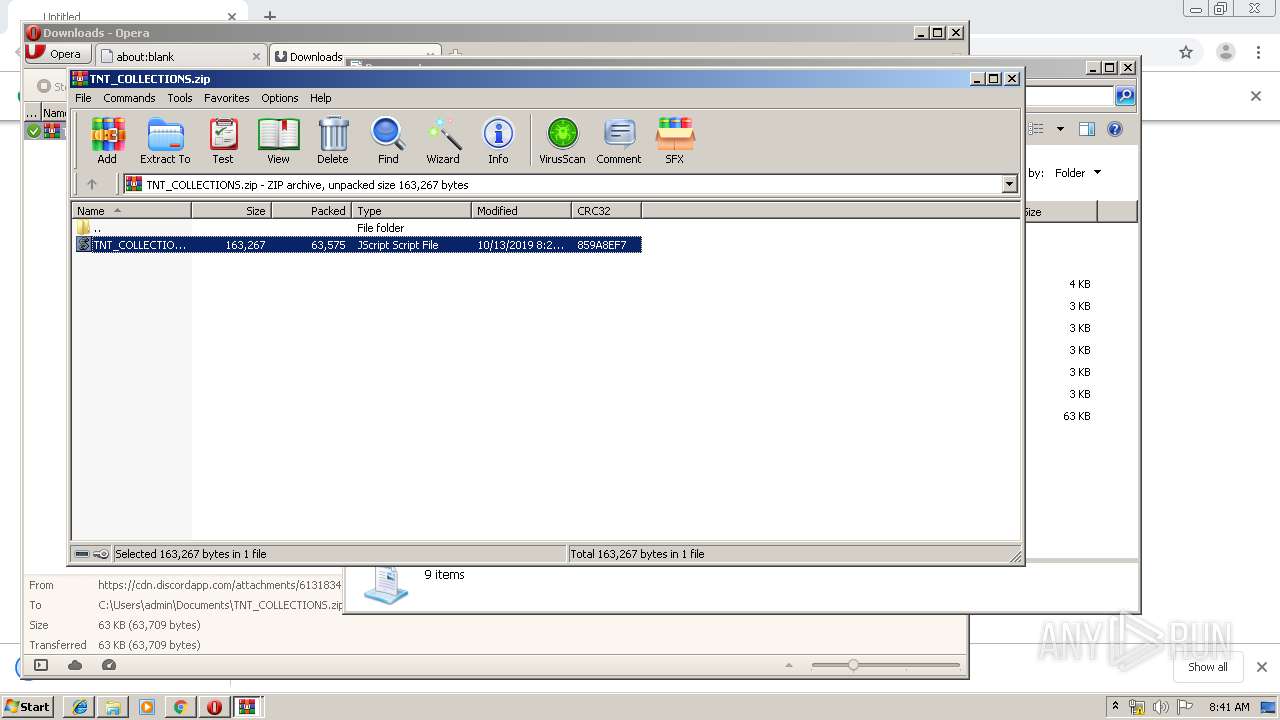
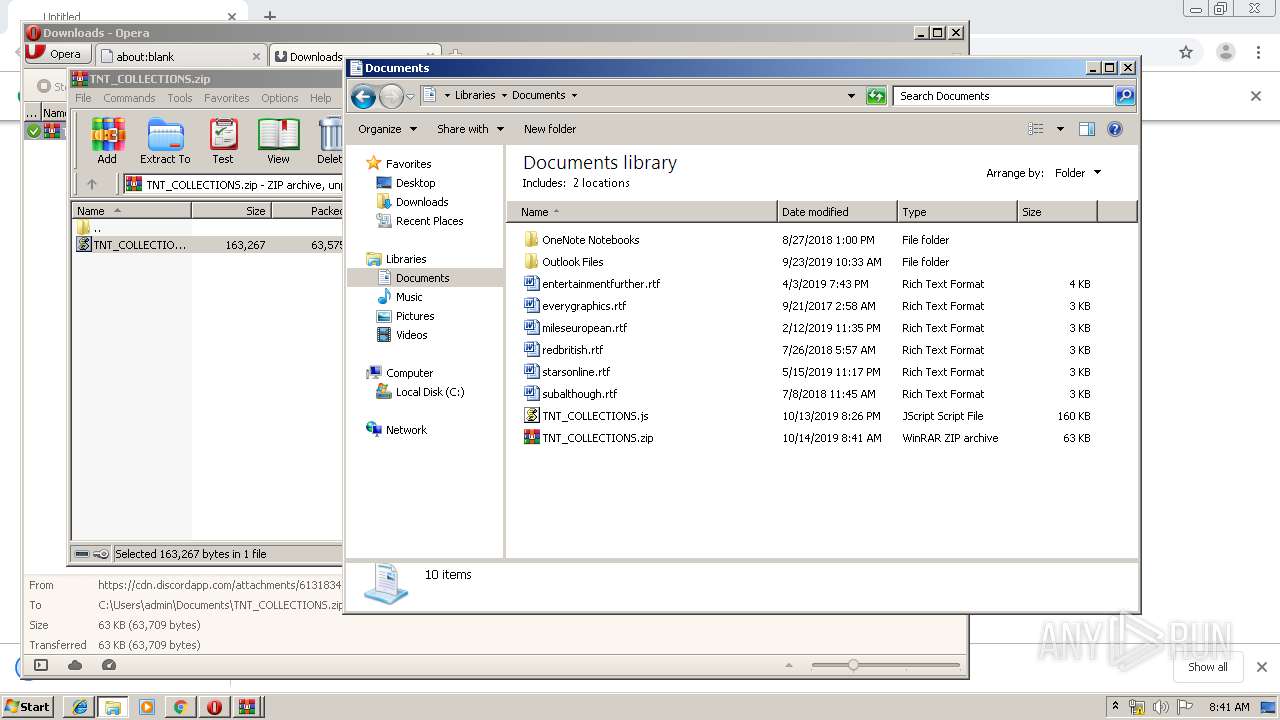
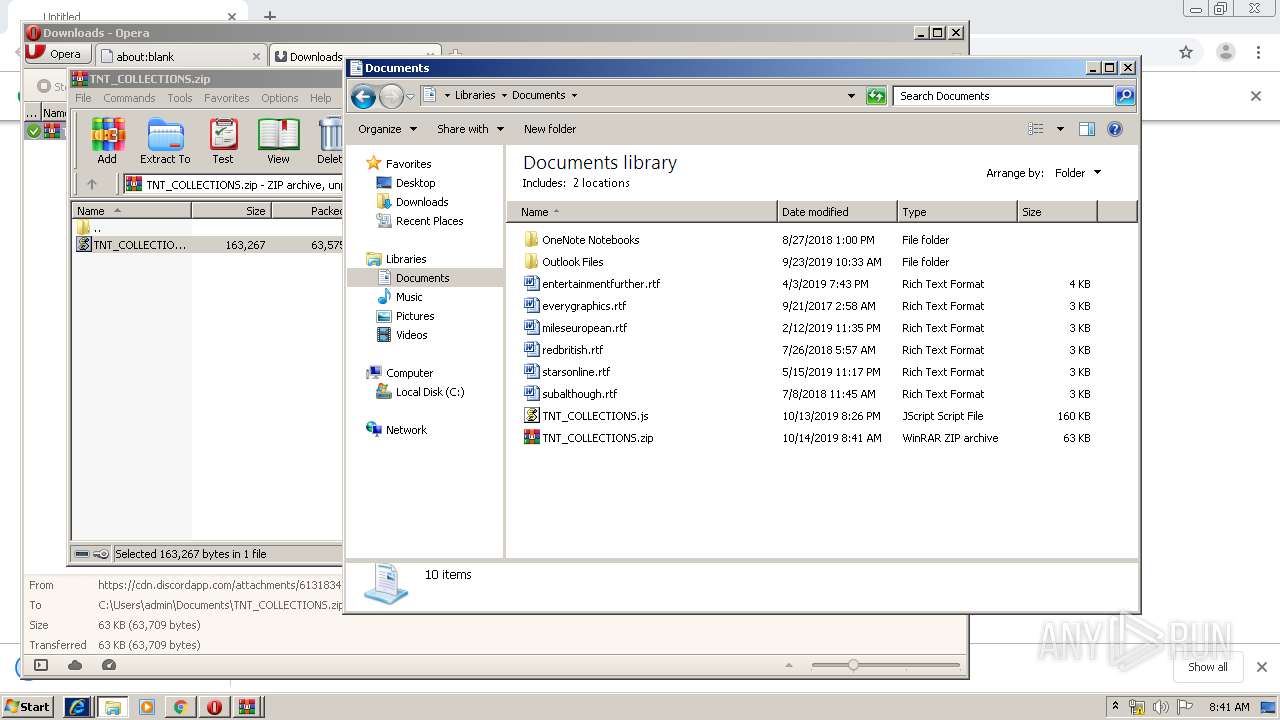
| URL: | https://cdn.discordapp.com/attachments/613183467068456977/633038098602786823/TNT_COLLECTIONS.zip |
| Full analysis: | https://app.any.run/tasks/8bdc5a7f-bb8e-47da-99f9-2f16719371a9 |
| Verdict: | Malicious activity |
| Analysis date: | October 14, 2019, 07:40:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 045E5370C68795983EF92EFDC69B2349 |
| SHA1: | 63C2D0DE43E01829346A3351D1F02034DE6A9142 |
| SHA256: | D6822A153A3BD4632EC2A322397359A20D0CA22D16E69DC41294C5A2A06B99F9 |
| SSDEEP: | 3:N8cCWdy6//QIUQTcSSKTwdXS/sQ+U:2cry6XQIdcSmXHU |
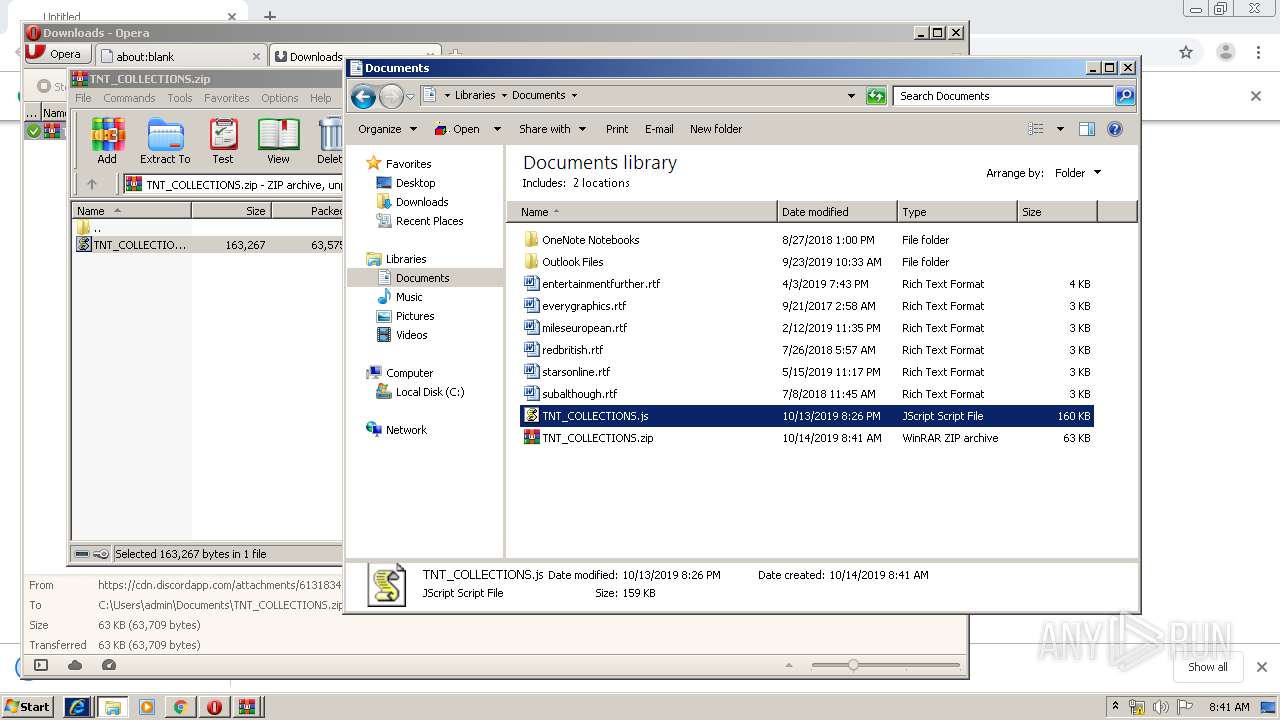
MALICIOUS
Changes the autorun value in the registry
- wscript.exe (PID: 912)
- WScript.exe (PID: 2284)
- WScript.exe (PID: 2064)
Writes to a start menu file
- WScript.exe (PID: 2284)
- wscript.exe (PID: 912)
SUSPICIOUS
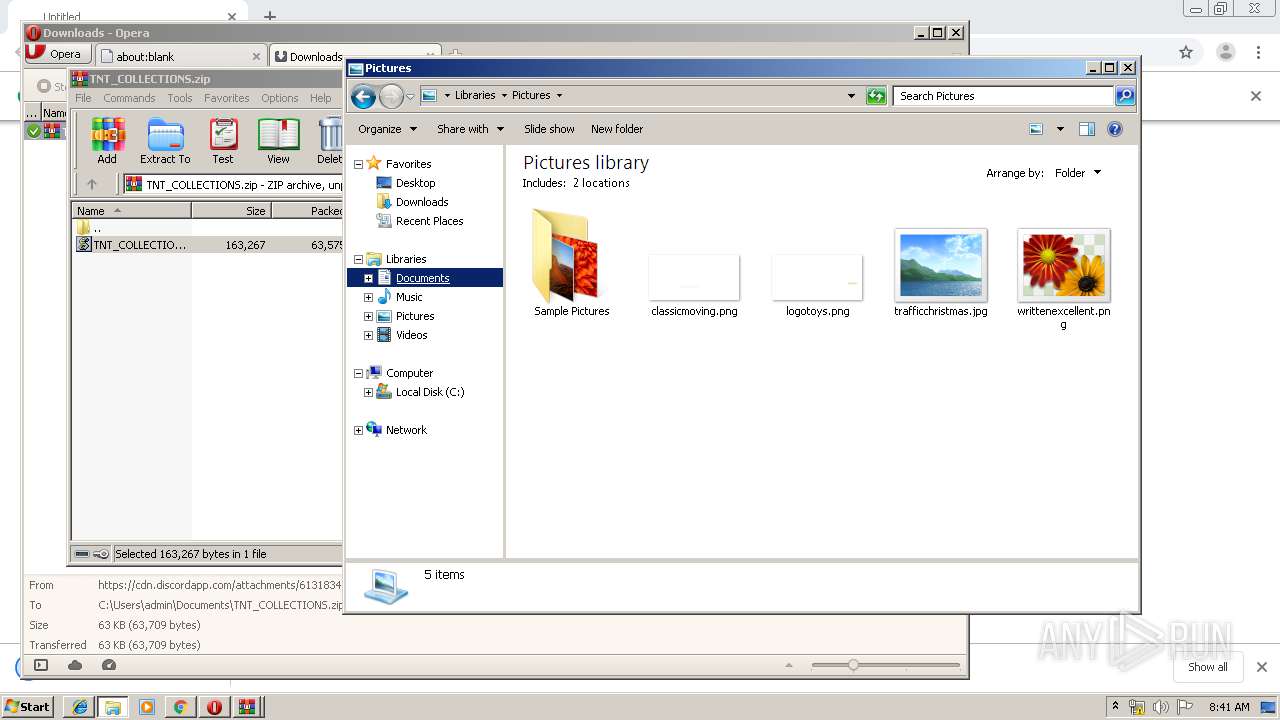
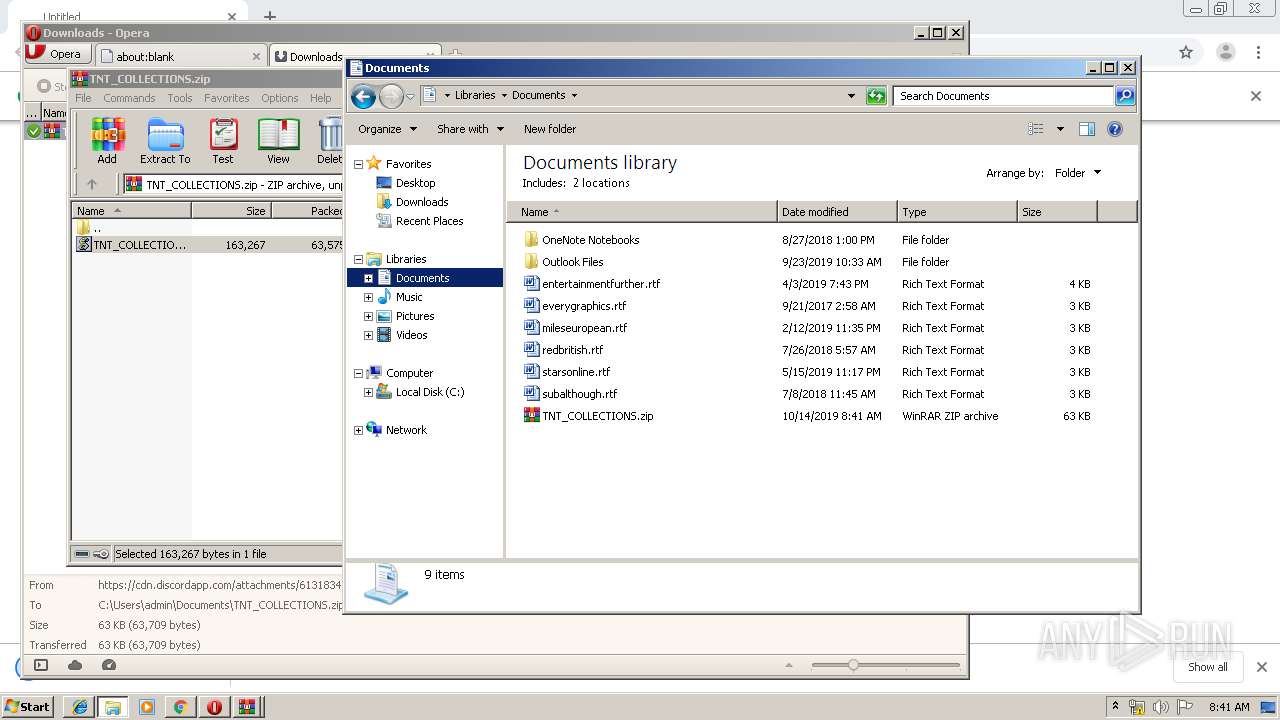
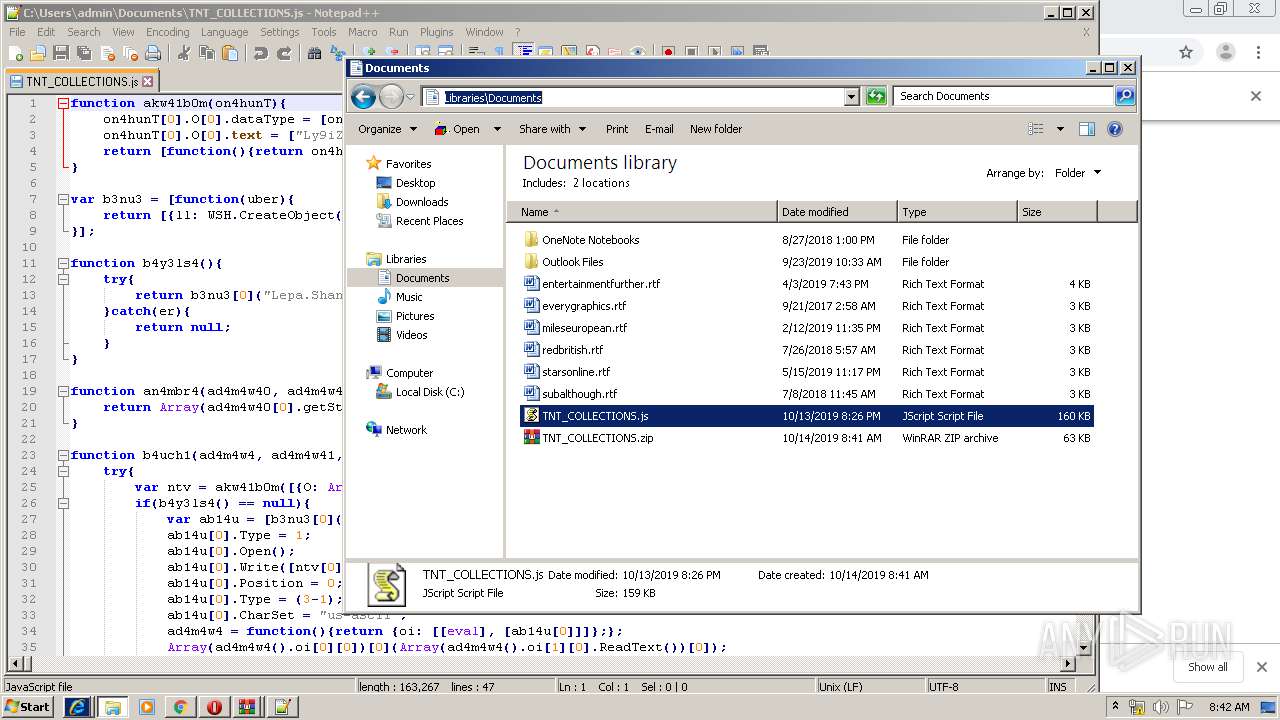
Creates files in the user directory
- WScript.exe (PID: 2284)
- wscript.exe (PID: 912)
- notepad++.exe (PID: 1956)
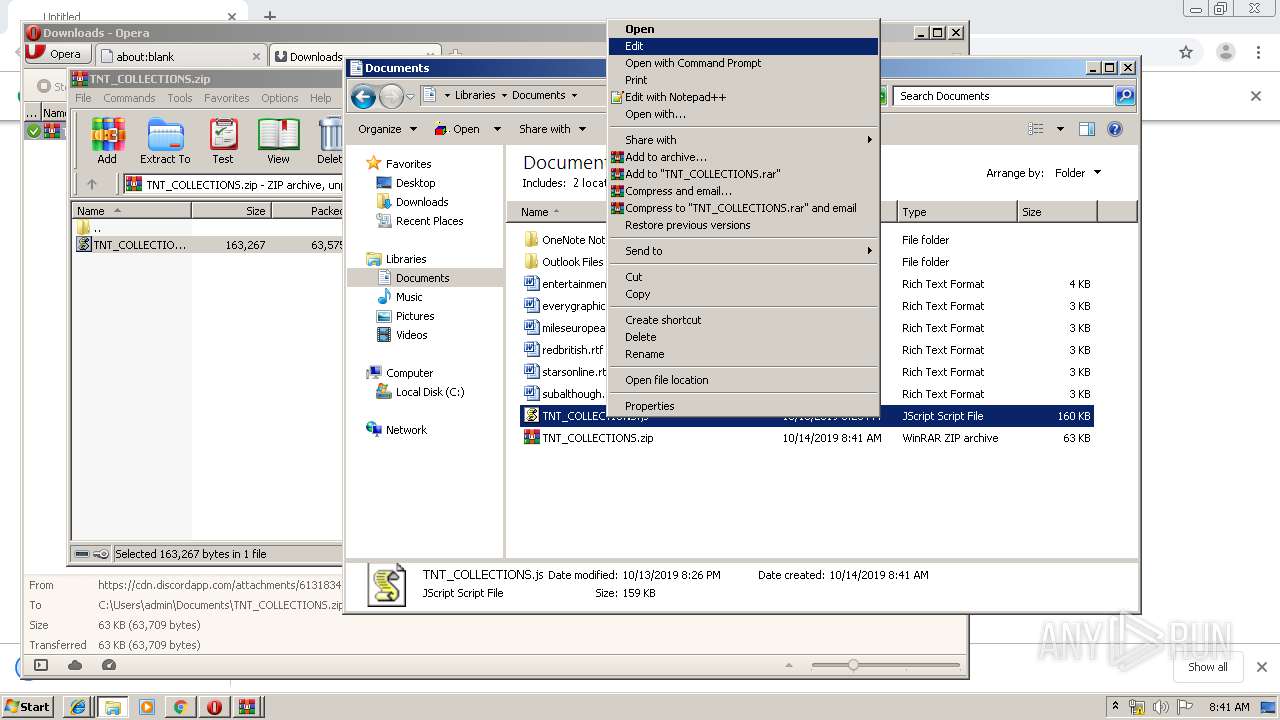
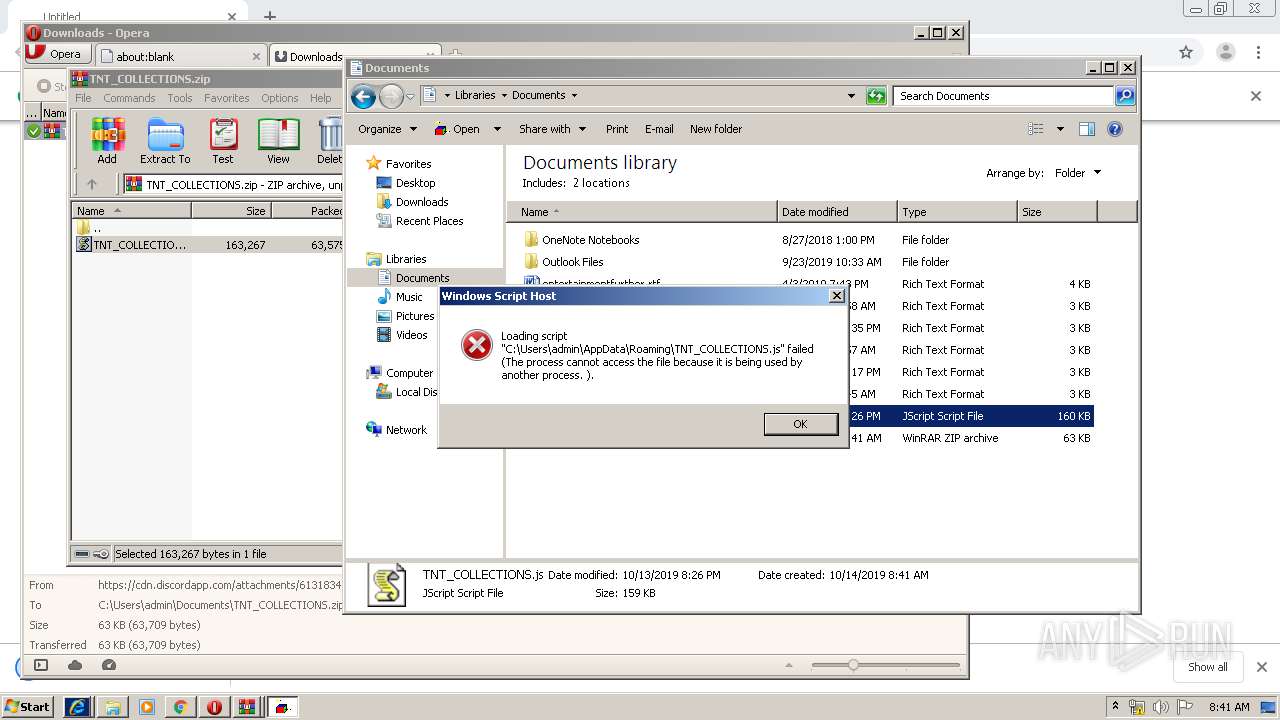
Executes scripts
- WScript.exe (PID: 2284)
- WScript.exe (PID: 2064)
Application launched itself
- WScript.exe (PID: 2284)
- WScript.exe (PID: 2064)
Checks for external IP
- wscript.exe (PID: 912)
INFO
Application launched itself
- chrome.exe (PID: 1044)
- iexplore.exe (PID: 3456)
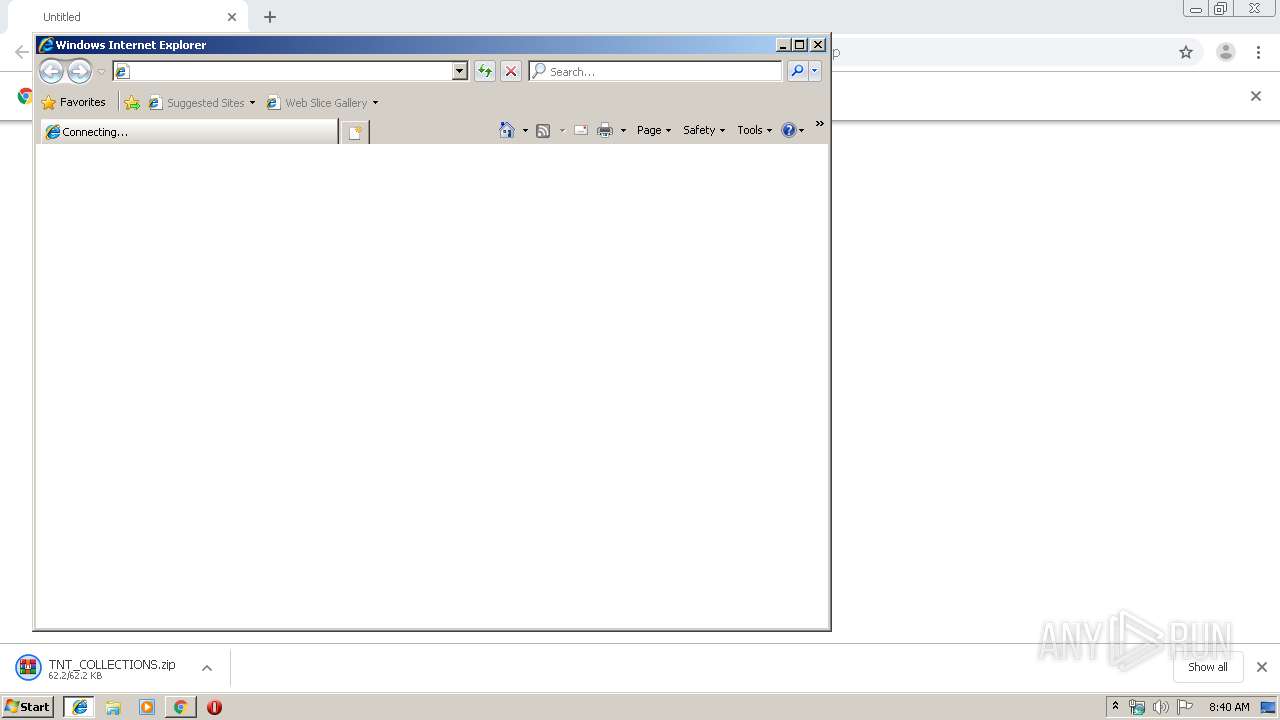
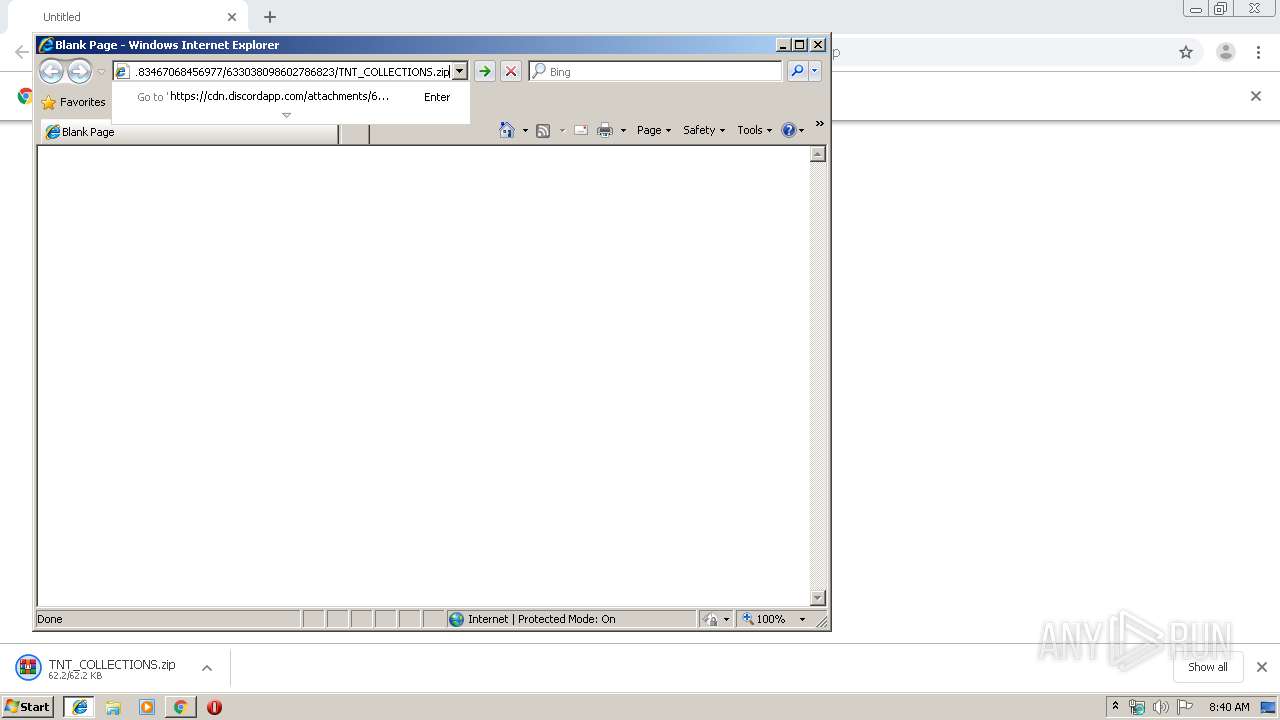
Changes internet zones settings
- iexplore.exe (PID: 3456)
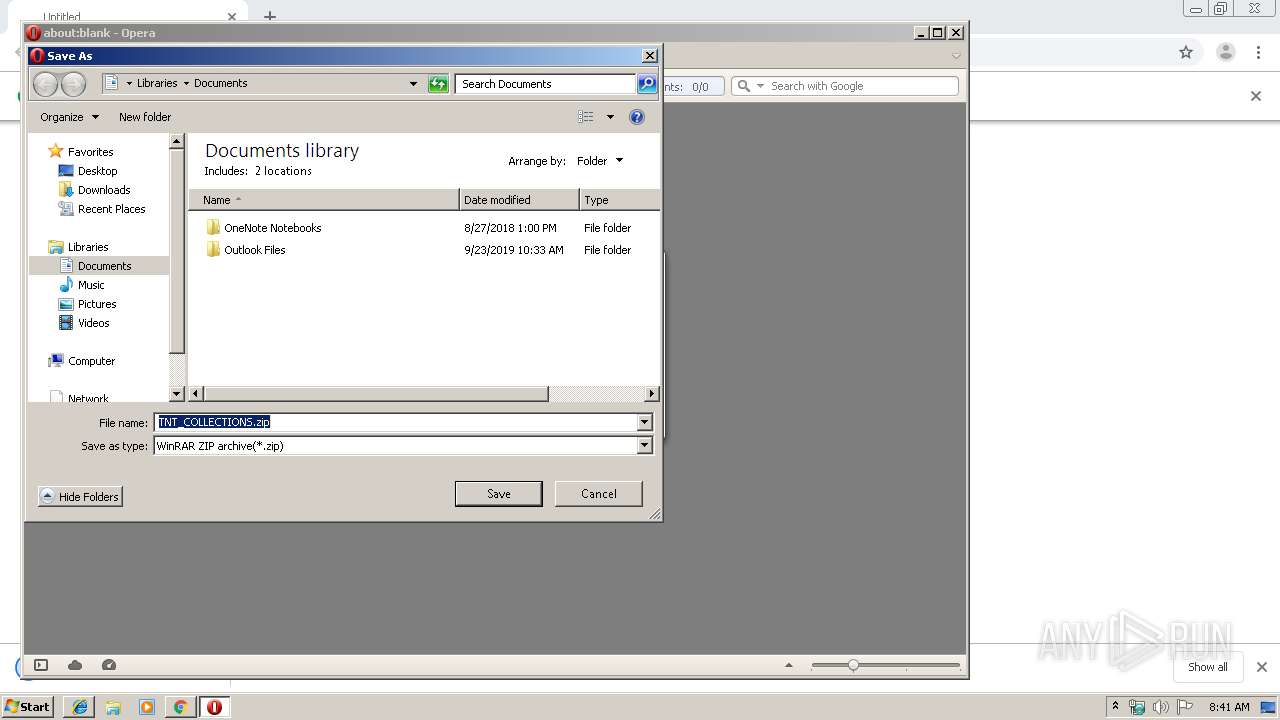
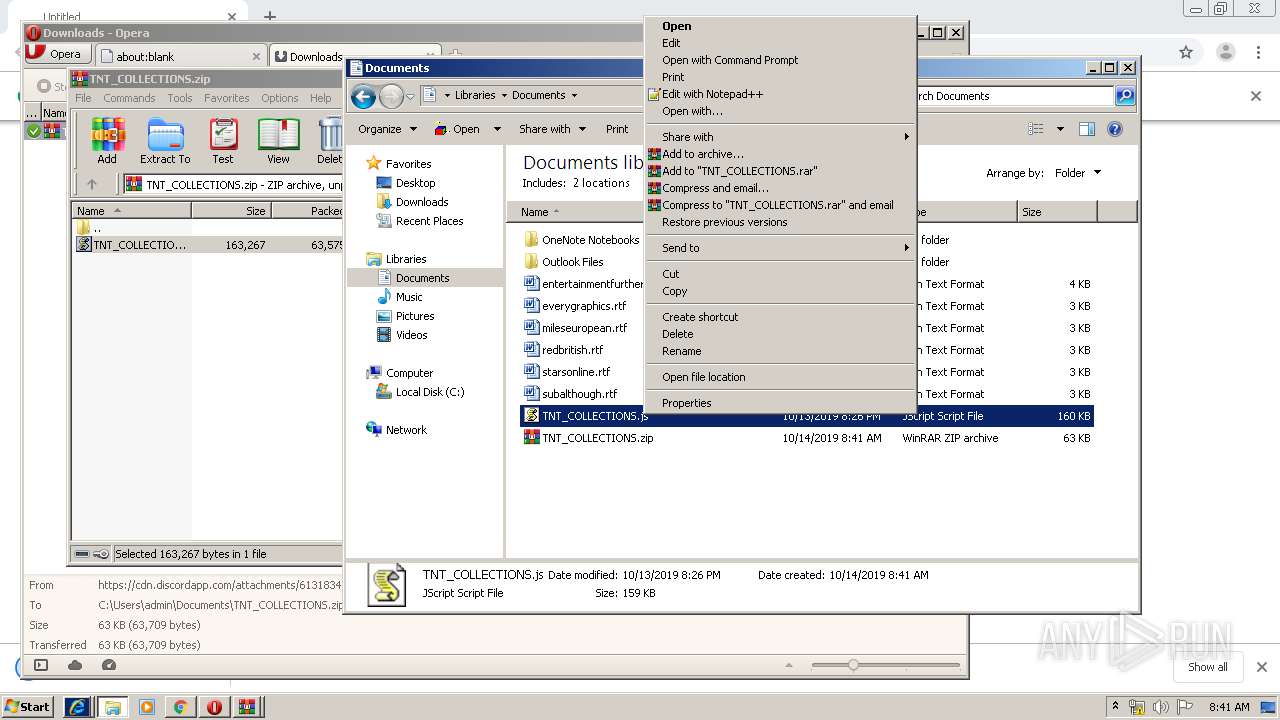
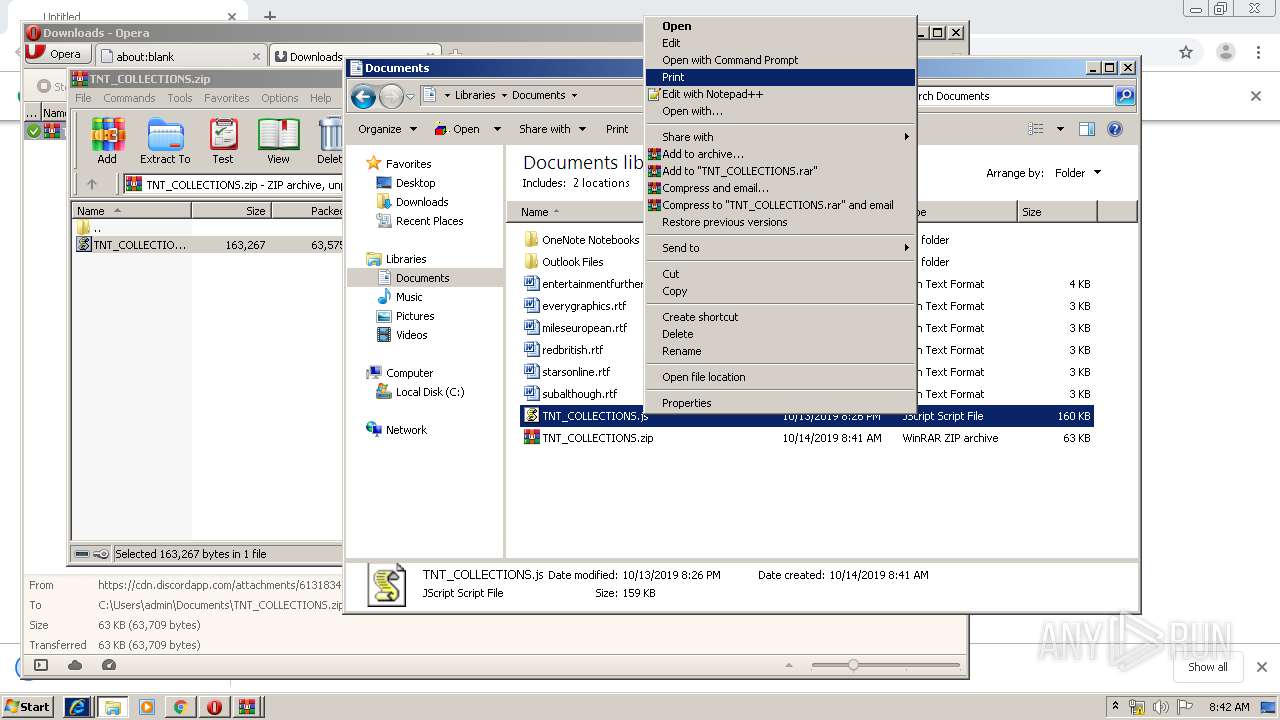
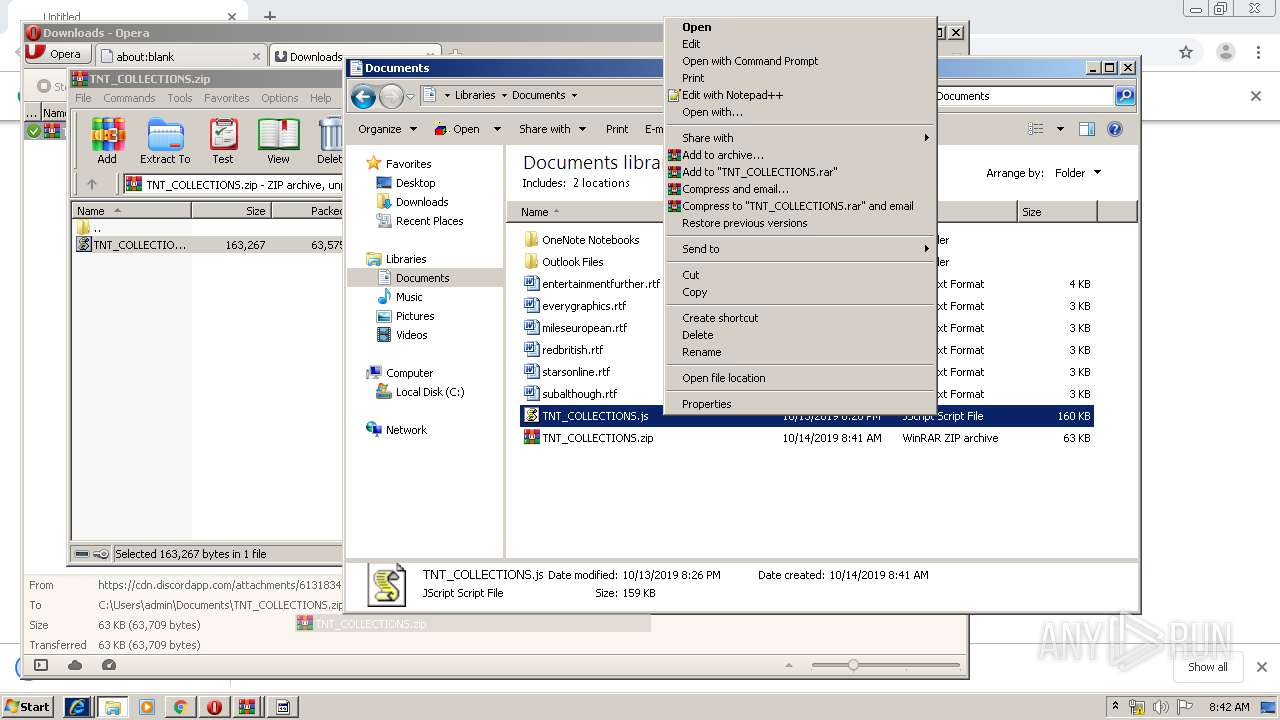
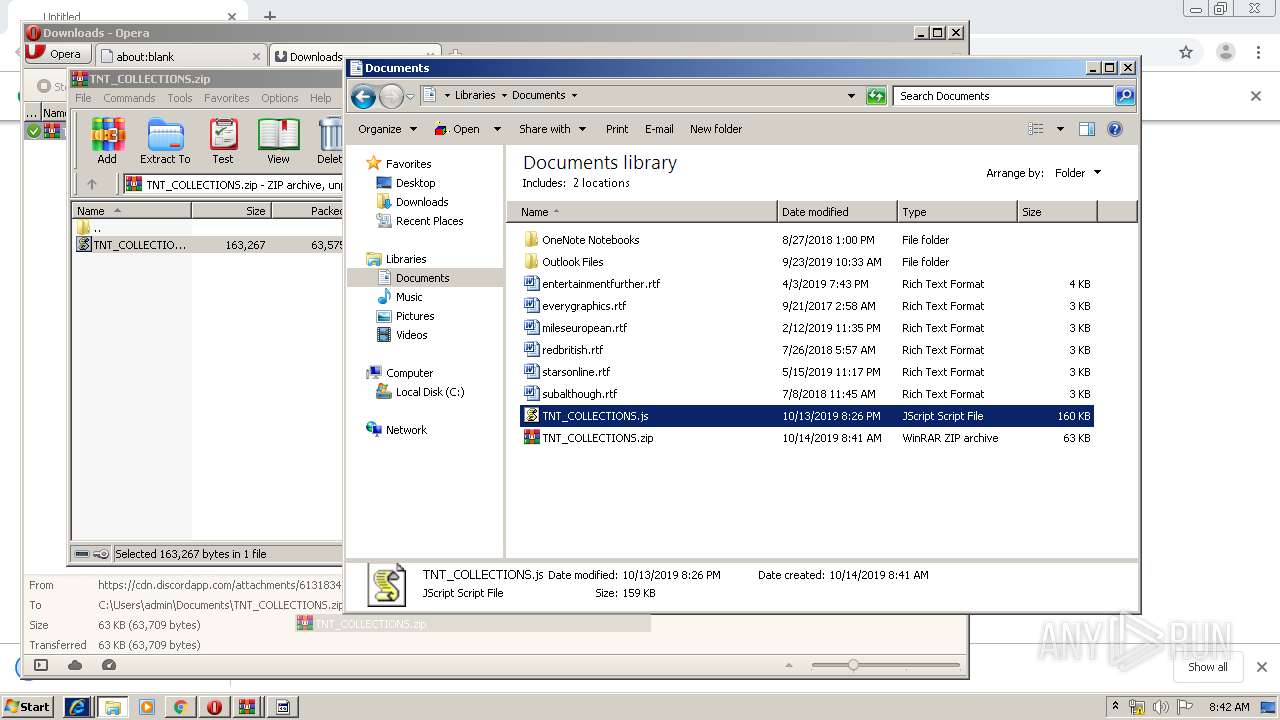
Manual execution by user
- opera.exe (PID: 4068)
- WScript.exe (PID: 2284)
- iexplore.exe (PID: 3456)
- explorer.exe (PID: 564)
- WScript.exe (PID: 2064)
- notepad++.exe (PID: 1956)
- notepad++.exe (PID: 3124)
Reads the hosts file
- chrome.exe (PID: 616)
- chrome.exe (PID: 1044)
Reads Internet Cache Settings
- opera.exe (PID: 4068)
- iexplore.exe (PID: 592)
- iexplore.exe (PID: 3456)
Reads internet explorer settings
- iexplore.exe (PID: 592)
Creates files in the user directory
- opera.exe (PID: 4068)
- iexplore.exe (PID: 592)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
24
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 592 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3456 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=980,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7846392879580430301 --mojo-platform-channel-handle=1648 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Windows\System32\wscript.exe" "C:\Users\admin\AppData\Roaming\TNT_COLLECTIONS.js" | C:\Windows\System32\wscript.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://cdn.discordapp.com/attachments/613183467068456977/633038098602786823/TNT_COLLECTIONS.zip" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
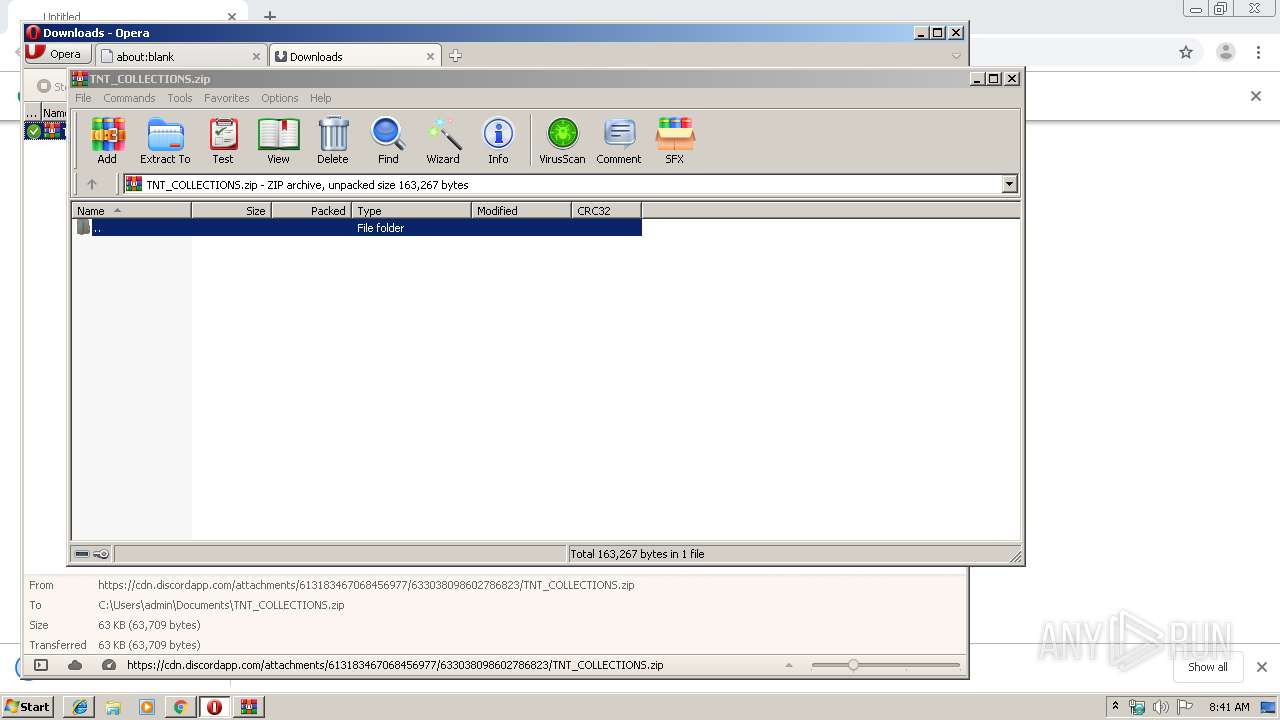
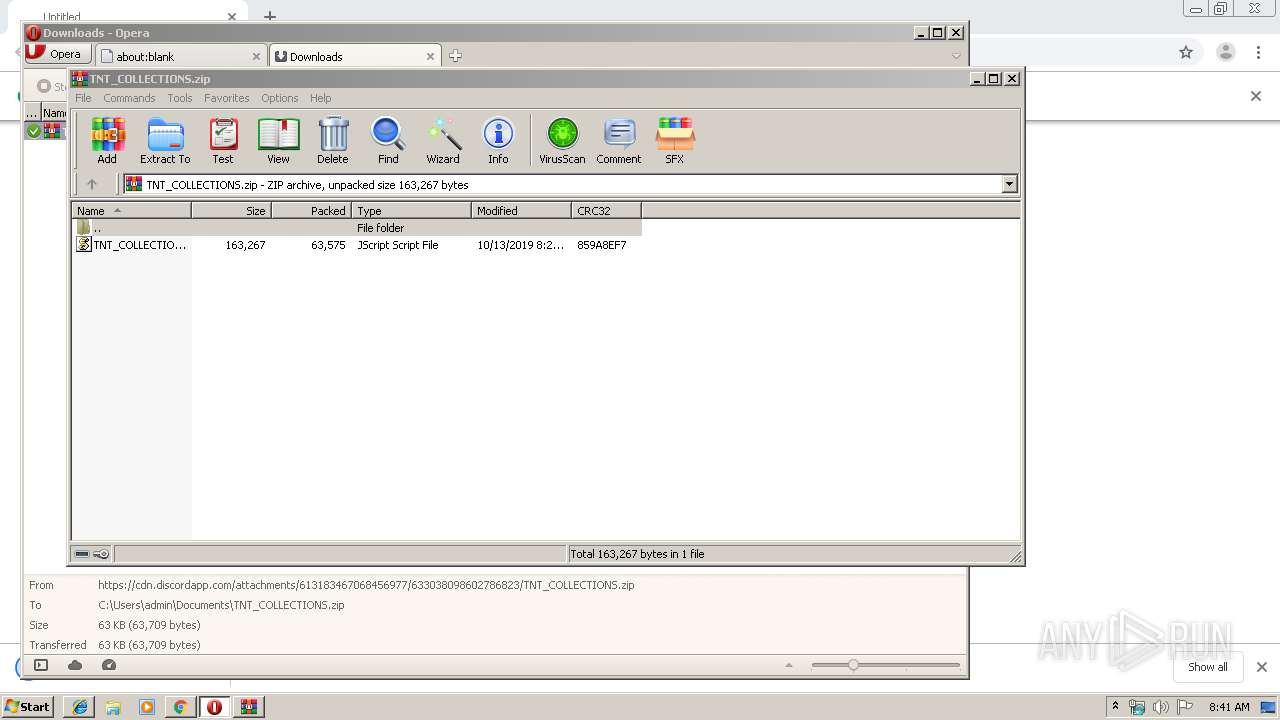
| 1708 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Documents\TNT_COLLECTIONS.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | opera.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=980,13522906091185382535,15076140749420656543,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9032370868528108715 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2216 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
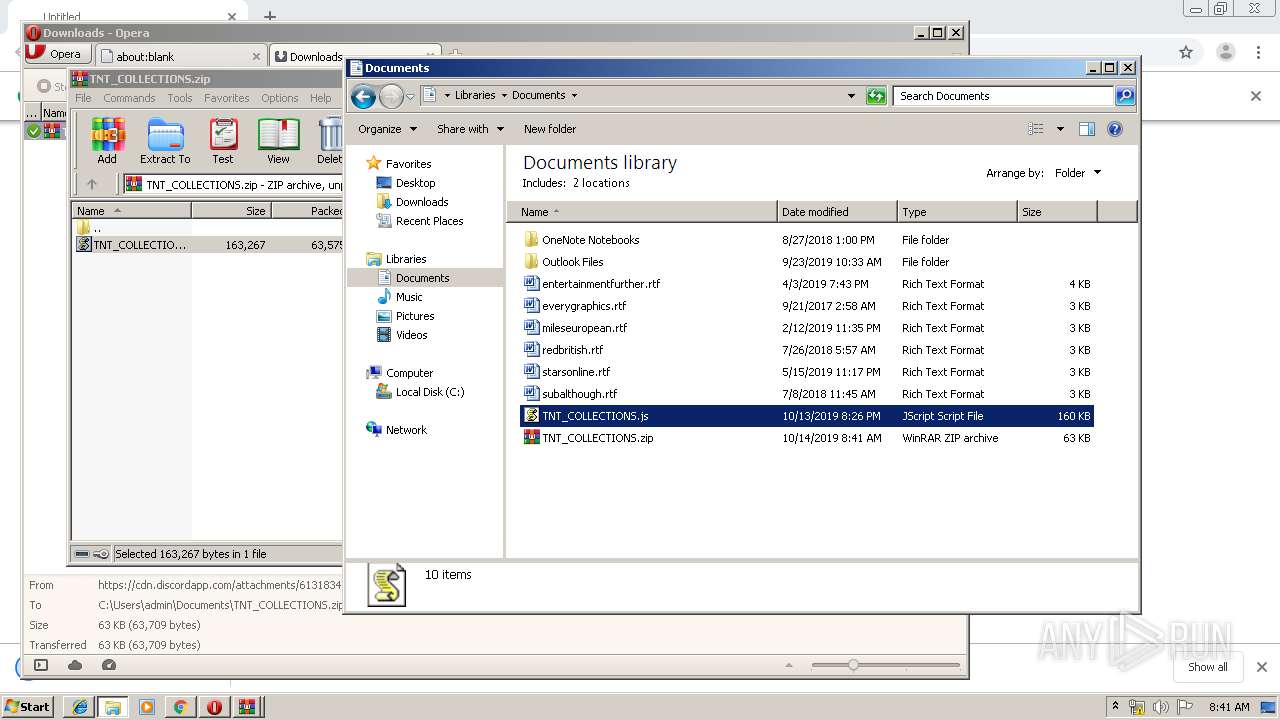
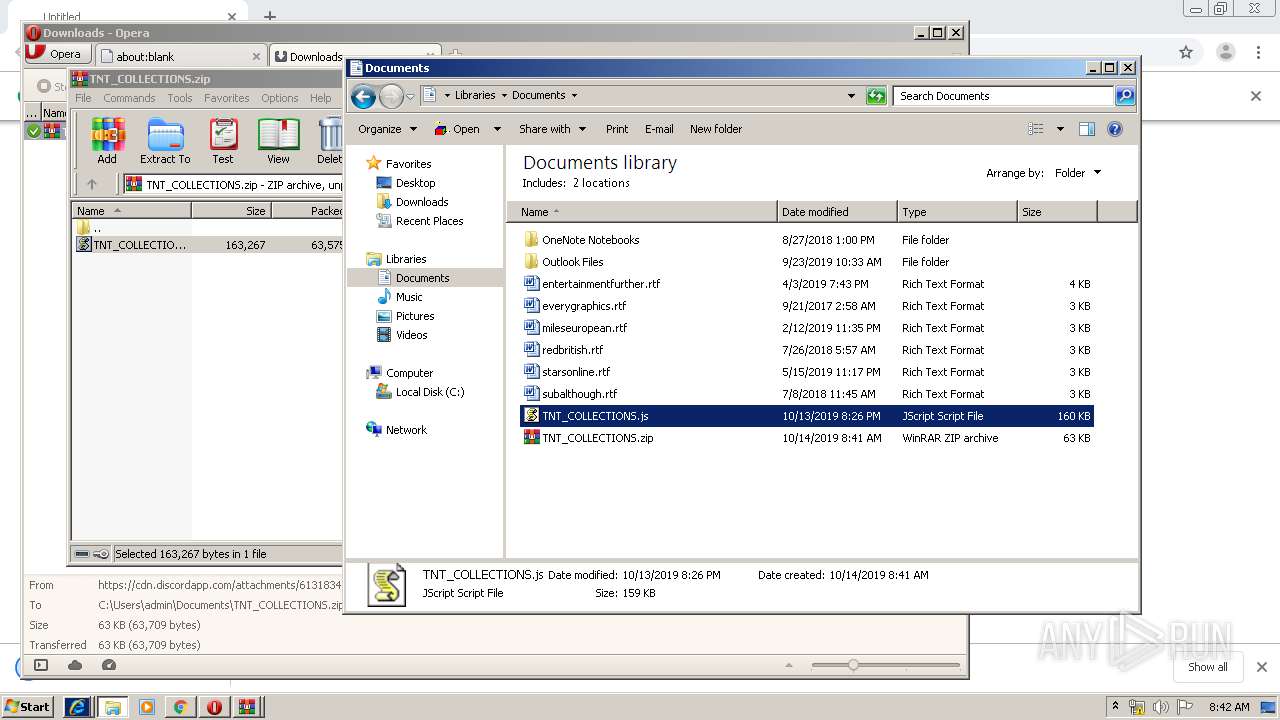
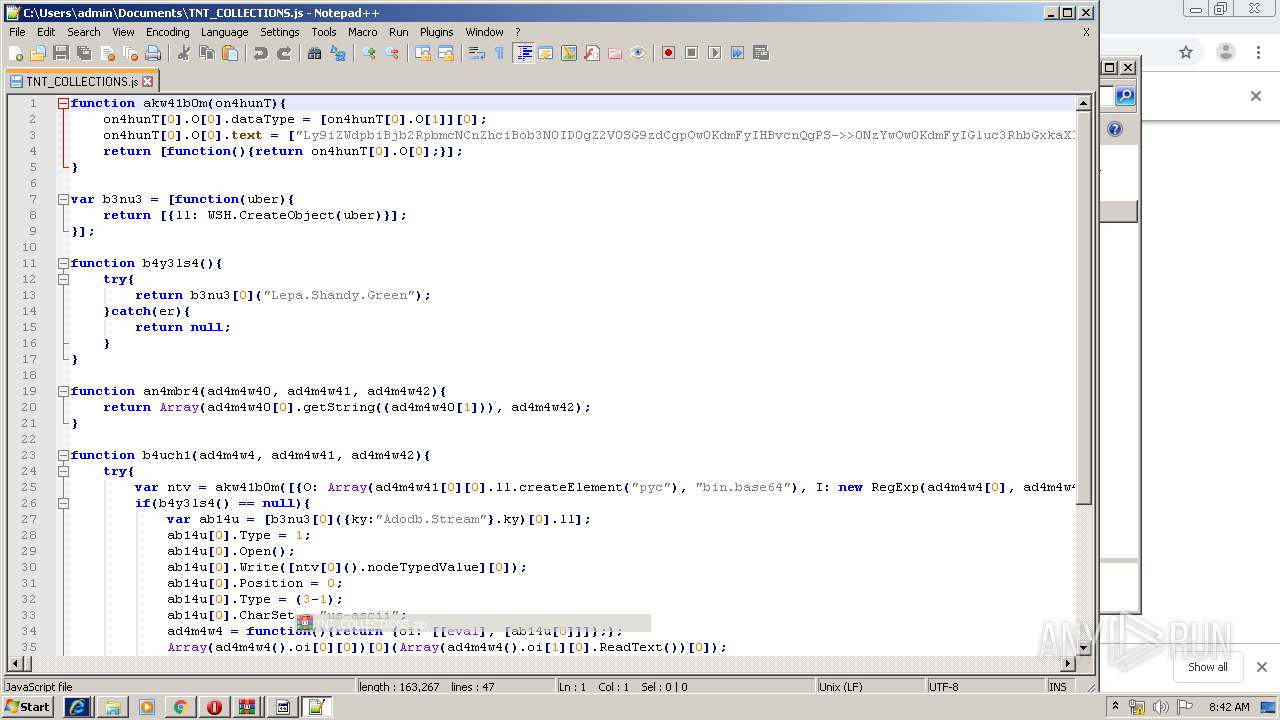
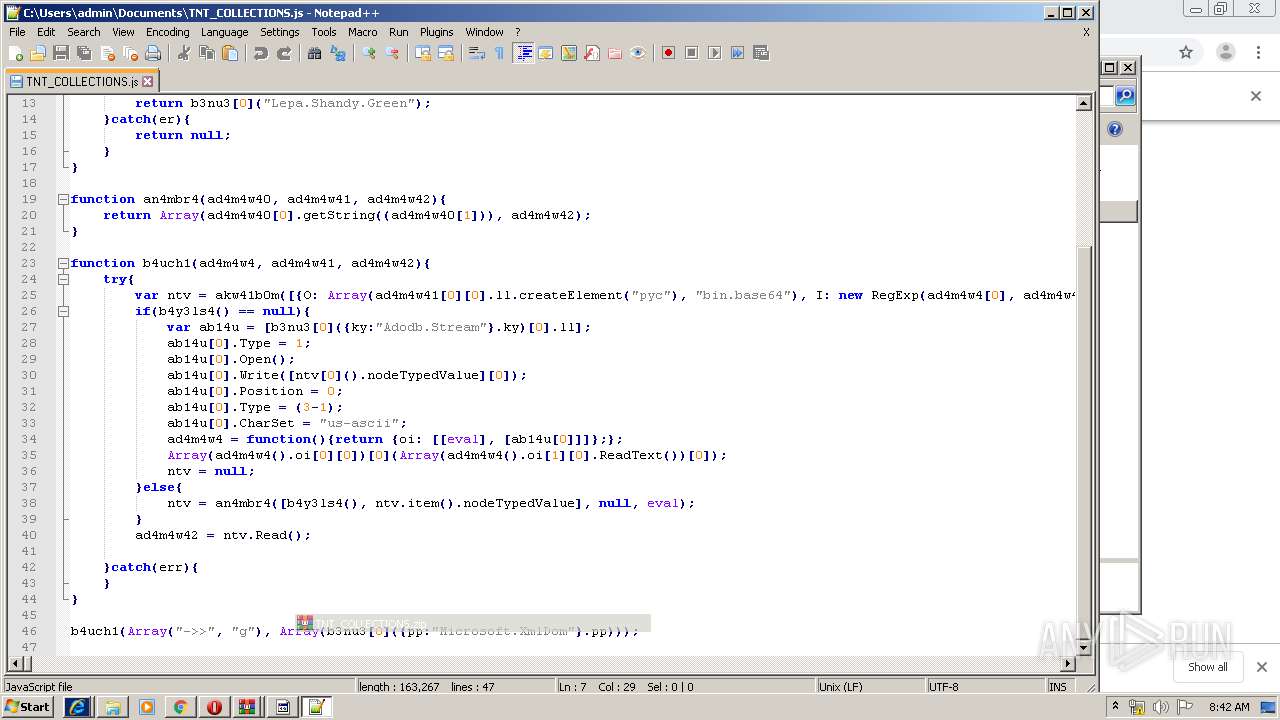
| 1956 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Documents\TNT_COLLECTIONS.js" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
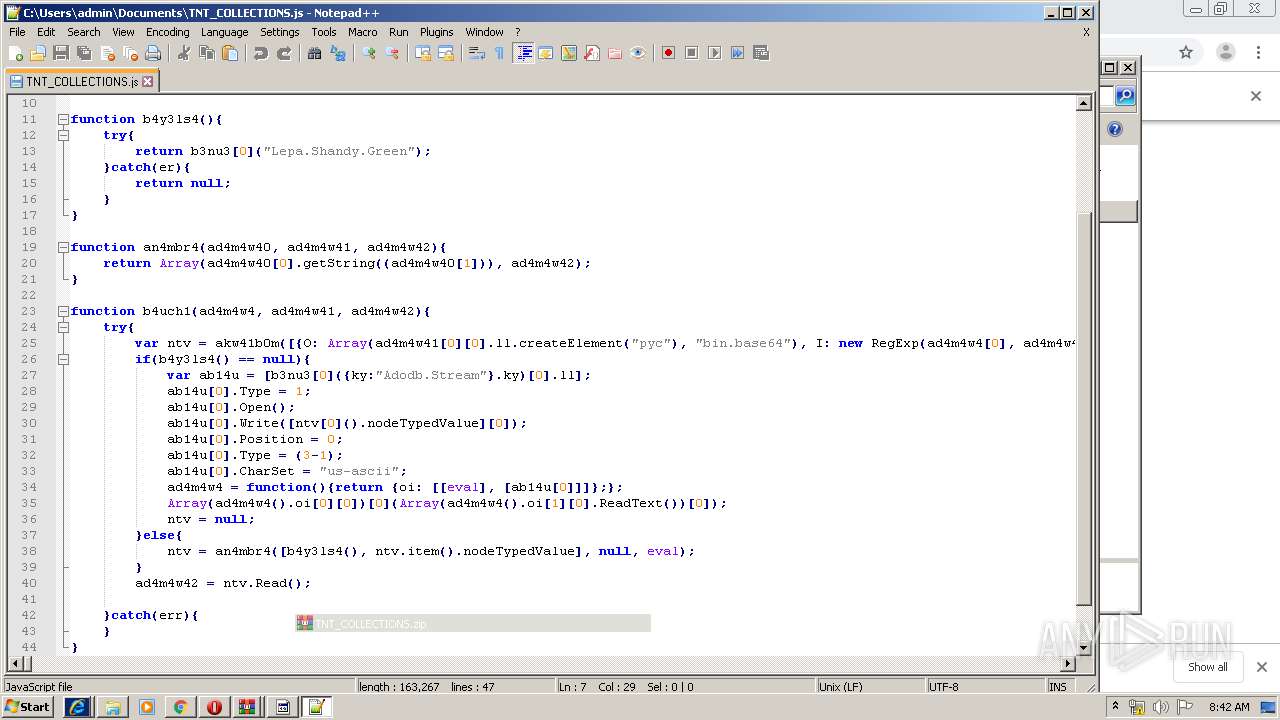
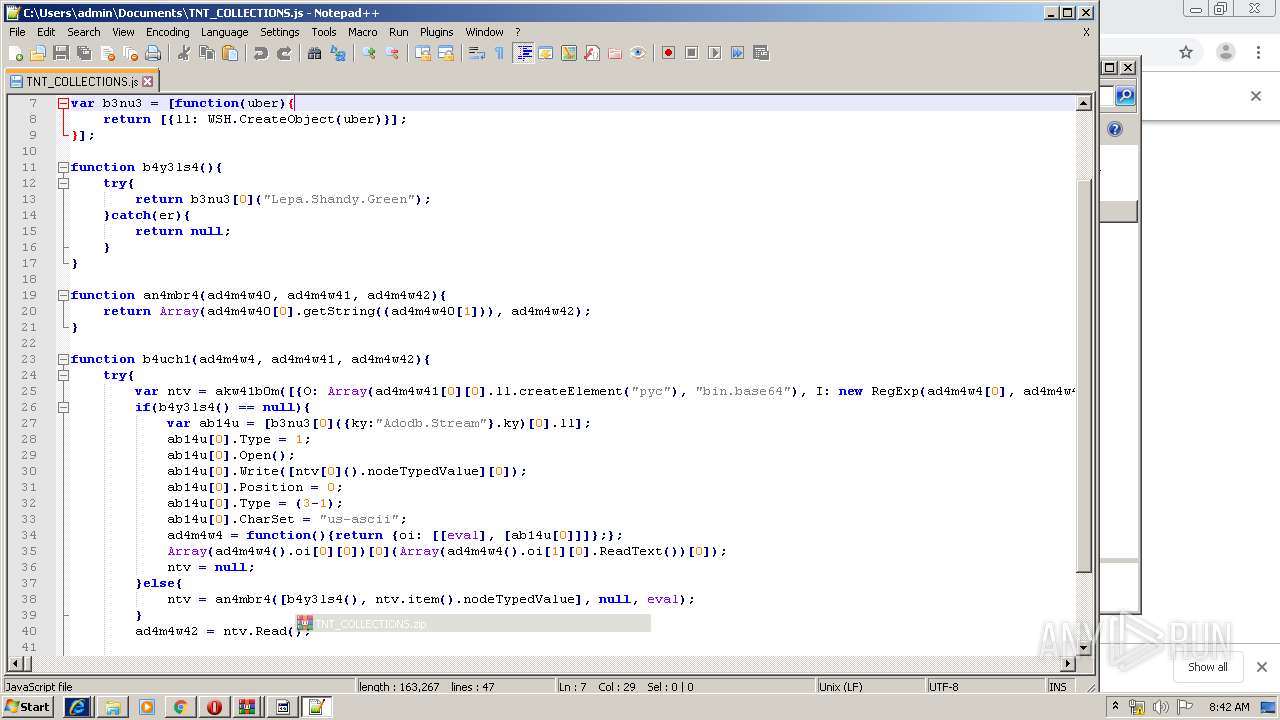
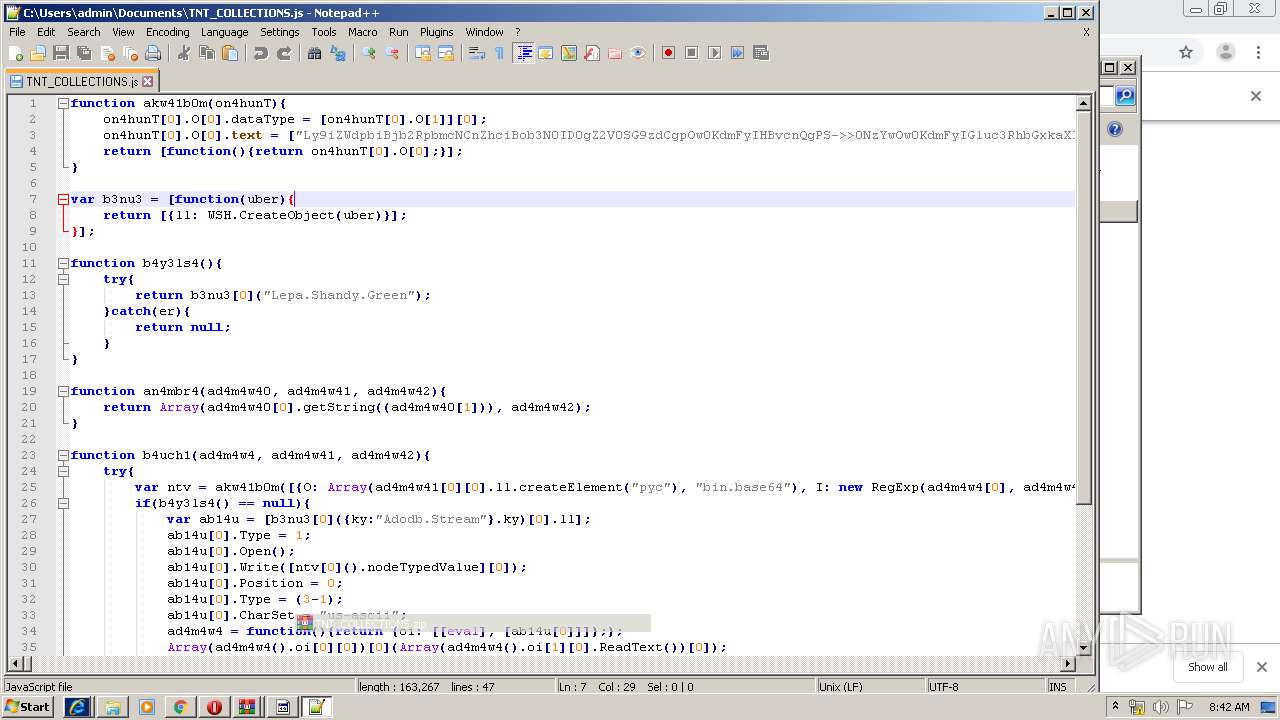
| 2064 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Documents\TNT_COLLECTIONS.js" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2284 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Documents\TNT_COLLECTIONS.js" | C:\Windows\System32\WScript.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
3 252
Read events
2 981
Write events
266
Delete events
5
Modification events
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2480) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1044-13215512430360625 |
Value: 259 | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1044) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
32
Text files
95
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\20b02b6e-1ea3-4e86-bbaa-06476e849f40.tmp | — | |
MD5:— | SHA256:— | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a91b.TMP | text | |
MD5:— | SHA256:— | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a93b.TMP | text | |
MD5:— | SHA256:— | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a93b.TMP | text | |
MD5:— | SHA256:— | |||
| 1044 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
34
DNS requests
19
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
912 | wscript.exe | GET | 200 | 185.194.141.58:80 | http://ip-api.com/json/ | DE | text | 265 b | malicious |
4068 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 528 b | whitelisted |
— | — | GET | 200 | 2.21.242.197:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
4068 | opera.exe | GET | 200 | 151.139.128.14:80 | http://crl.usertrust.com/AddTrustExternalCARoot.crl | US | der | 673 b | whitelisted |
— | — | GET | 200 | 2.21.242.245:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgMpeSsuddjFyk25ZqSQ83ahjg%3D%3D | NL | der | 527 b | whitelisted |
4068 | opera.exe | GET | 200 | 151.139.128.14:80 | http://crl.comodoca.com/COMODORSACertificationAuthority.crl | US | der | 812 b | whitelisted |
3456 | iexplore.exe | GET | 200 | 13.107.21.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
616 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
616 | chrome.exe | 162.159.129.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
3456 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
592 | iexplore.exe | 162.159.134.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
4068 | opera.exe | 107.167.110.216:443 | sitecheck2.opera.com | Opera Software Americas LLC | US | malicious |
4068 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
4068 | opera.exe | 185.26.182.93:443 | certs.opera.com | Opera Software AS | — | whitelisted |
616 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
4068 | opera.exe | 162.159.134.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
4068 | opera.exe | 162.159.129.233:443 | cdn.discordapp.com | Cloudflare Inc | — | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.discordapp.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.bing.com |
| whitelisted |
certs.opera.com |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
crl.comodoca.com |
| whitelisted |
crl.usertrust.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
912 | wscript.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup ip-api.com |
912 | wscript.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|