| File name: | Stealth.exe |
| Full analysis: | https://app.any.run/tasks/8cf616d9-f0c1-44cd-aa2f-525a2ab01355 |
| Verdict: | Malicious activity |
| Analysis date: | June 03, 2024, 13:18:54 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (console) x86-64, for MS Windows |
| MD5: | 4E50213716582B292E7F0FACFA21E662 |
| SHA1: | D2B59642F77801279D88F6C8341894CD82582E21 |
| SHA256: | D67D83DC5B43E45D377B44C1F96B219D5AC349886734B059B2854B74E1E8F454 |
| SSDEEP: | 98304:z8WmpdqM39nM31eWLSAKcsUb2yeJIimUCf0yxDdMRULdSpCC/oU36P99F9dKxmBz:Q68QHqxeMhUljY4C83B6E |
MALICIOUS
Drops the executable file immediately after the start
- Stealth.exe (PID: 1428)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 2876)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2876)
- Stealth.exe (PID: 1428)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 1636)
Executes application which crashes
- Stealth.exe (PID: 1428)
Reads the BIOS version
- Stealth.exe (PID: 1428)
INFO
Checks supported languages
- Stealth.exe (PID: 1428)
Process checks whether UAC notifications are on
- Stealth.exe (PID: 1428)
Reads the computer name
- Stealth.exe (PID: 1428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:05:31 21:13:50+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.39 |
| CodeSize: | 573440 |
| InitializedDataSize: | 152064 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xefa058 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
126
Monitored processes
12
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 628 | certutil -hashfile "C:\Users\admin\Desktop\Stealth.exe" MD5 | C:\Windows\System32\certutil.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: CertUtil.exe Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1364 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1428 | "C:\Users\admin\Desktop\Stealth.exe" | C:\Users\admin\Desktop\Stealth.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3221226505 Modules
| |||||||||||||||
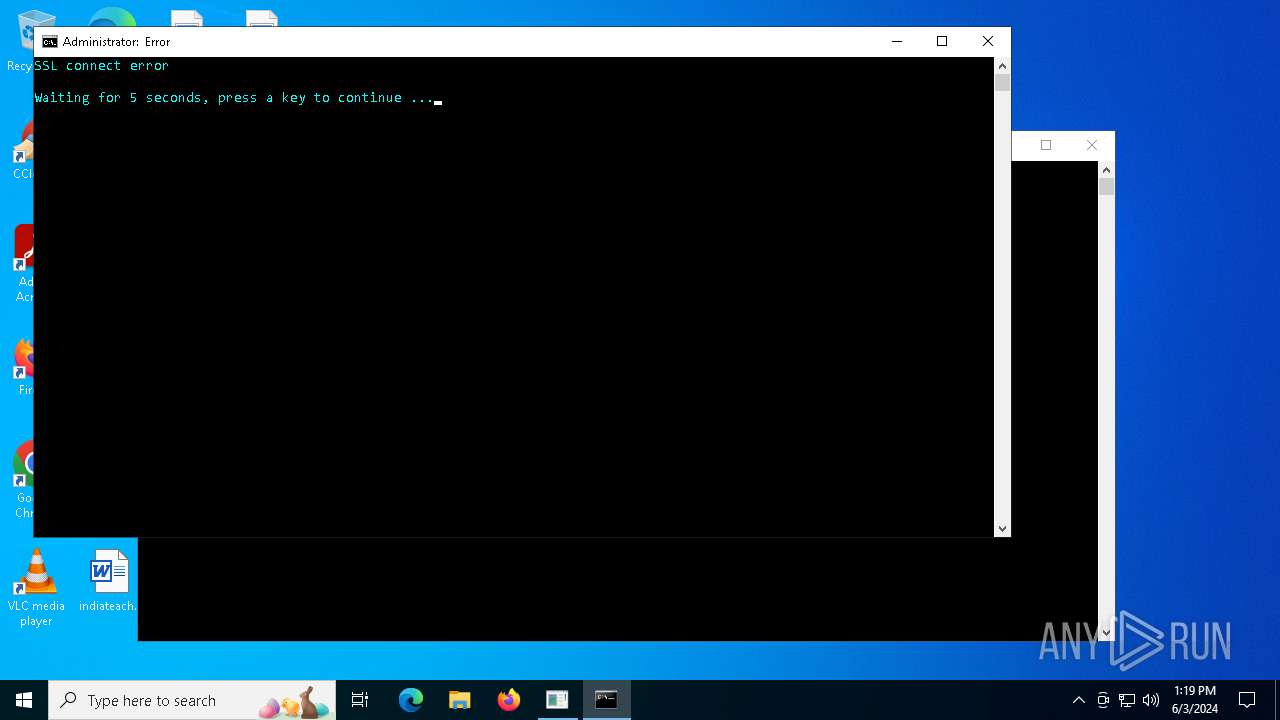
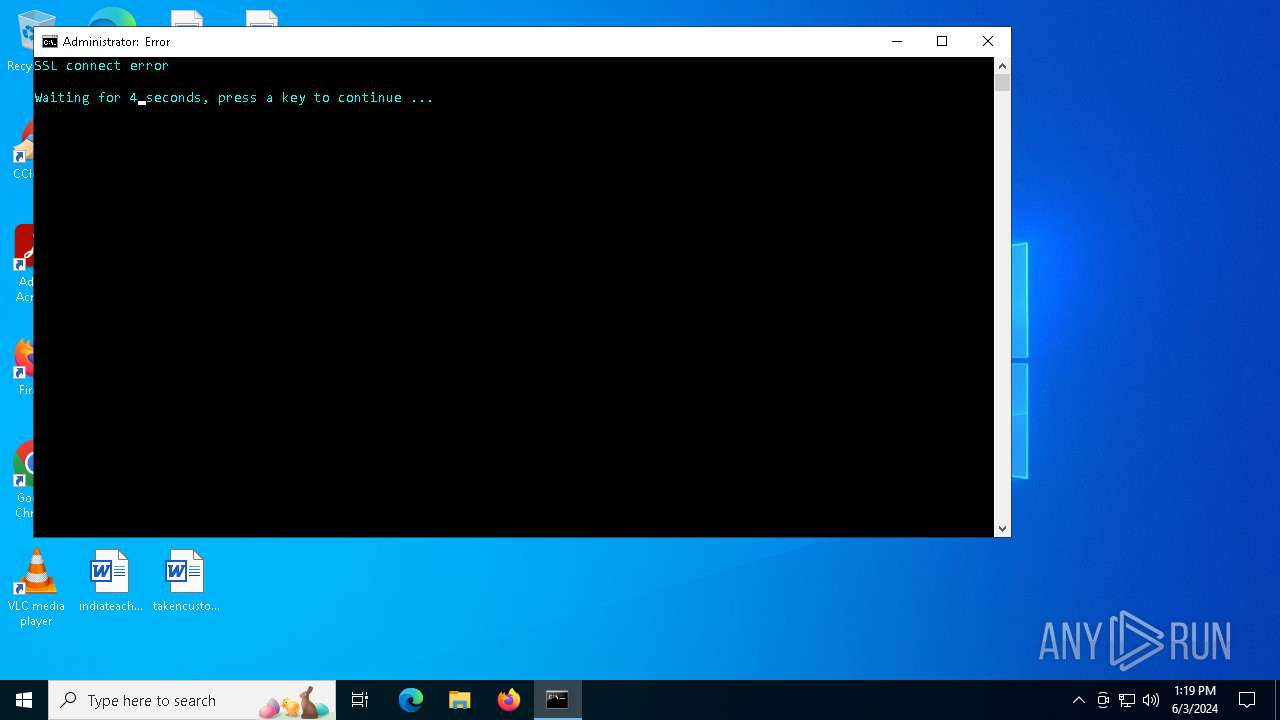
| 1636 | cmd /C "color b && title Error && echo SSL connect error && timeout /t 5" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1676 | "C:\Users\admin\Desktop\Stealth.exe" | C:\Users\admin\Desktop\Stealth.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2392 | find /i /v "md5" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2588 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | Stealth.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2876 | C:\WINDOWS\system32\cmd.exe /c start cmd /C "color b && title Error && echo SSL connect error && timeout /t 5" | C:\Windows\System32\cmd.exe | — | Stealth.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4280 | find /i /v "certutil" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4424 | C:\WINDOWS\system32\cmd.exe /c certutil -hashfile "C:\Users\admin\Desktop\Stealth.exe" MD5 | find /i /v "md5" | find /i /v "certutil" | C:\Windows\System32\cmd.exe | — | Stealth.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
1 193
Read events
1 190
Write events
3
Delete events
0
Modification events
| (PID) Process: | (628) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.1!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_AUTO_UPDATE_CA_REVOCATION | |||
| (PID) Process: | (628) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.2!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_AUTO_UPDATE_END_REVOCATION | |||
| (PID) Process: | (628) certutil.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Cryptography\OID\EncodingType 0\CryptDllFindOIDInfo\1.3.6.1.4.1.311.60.3.3!7 |
| Operation: | write | Name: | Name |
Value: szOID_ROOT_PROGRAM_NO_OCSP_FAILOVER_TO_CRL | |||
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
22
DNS requests
5
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.61.152.46:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | BR | binary | 973 b | unknown |
5448 | svchost.exe | GET | 200 | 2.18.244.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | FR | binary | 1.01 Kb | unknown |
5448 | svchost.exe | GET | 200 | 23.61.152.46:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | BR | binary | 973 b | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 2.18.244.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | FR | binary | 1.01 Kb | unknown |
— | — | GET | 200 | 2.18.244.211:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | FR | binary | 1.01 Kb | unknown |
— | — | POST | 200 | 20.189.173.7:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | US | binary | 9 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 239.255.255.250:1900 | — | — | — | unknown |
5140 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5140 | MoUsoCoreWorker.exe | 2.18.244.211:80 | crl.microsoft.com | Akamai International B.V. | FR | unknown |
— | — | 2.18.244.211:80 | crl.microsoft.com | Akamai International B.V. | FR | unknown |
5448 | svchost.exe | 2.18.244.211:80 | crl.microsoft.com | Akamai International B.V. | FR | unknown |
— | — | 23.61.152.46:80 | www.microsoft.com | AKAMAI-AS | BR | unknown |
5448 | svchost.exe | 23.61.152.46:80 | www.microsoft.com | AKAMAI-AS | BR | unknown |
5448 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1428 | Stealth.exe | 172.67.72.57:443 | keyauth.win | CLOUDFLARENET | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
keyauth.win |
| malicious |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2184 | svchost.exe | Potentially Bad Traffic | ET INFO Fake Game Cheat Related Domain in DNS Lookup (keyauth .win) |
1428 | Stealth.exe | Potentially Bad Traffic | ET INFO Fake Game Cheat Related Domain (keyauth .win) in TLS SNI |