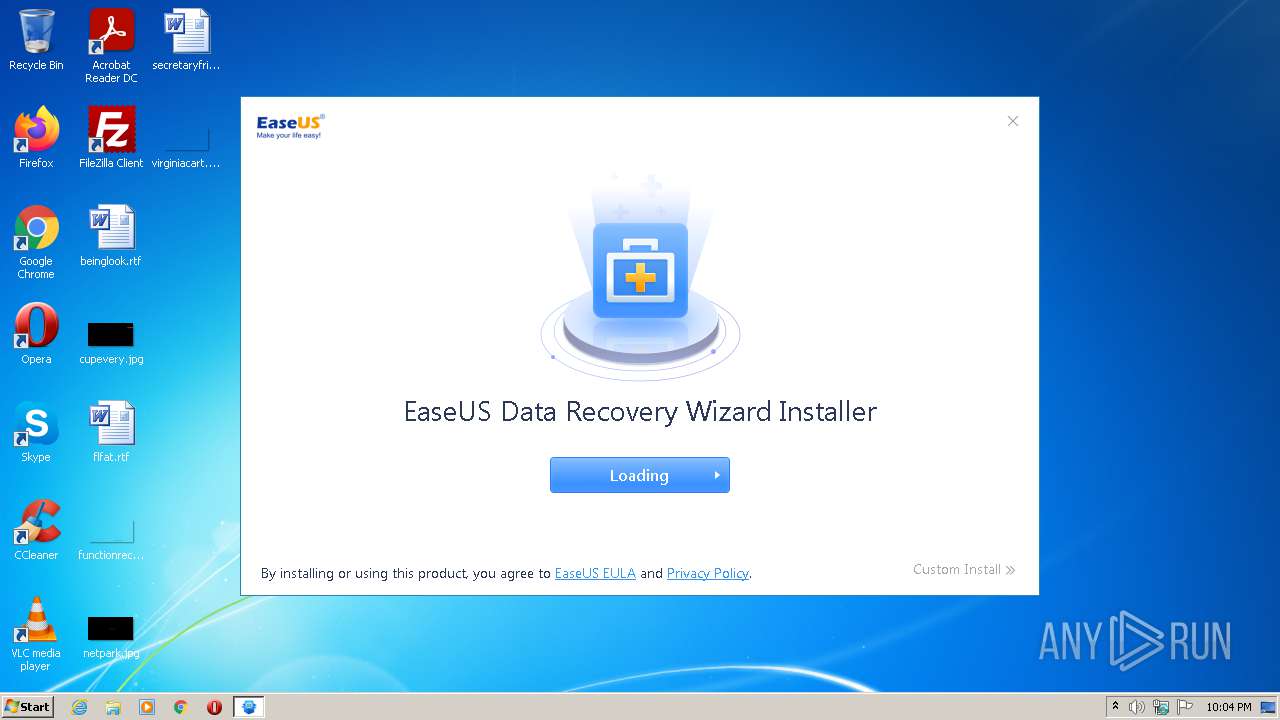
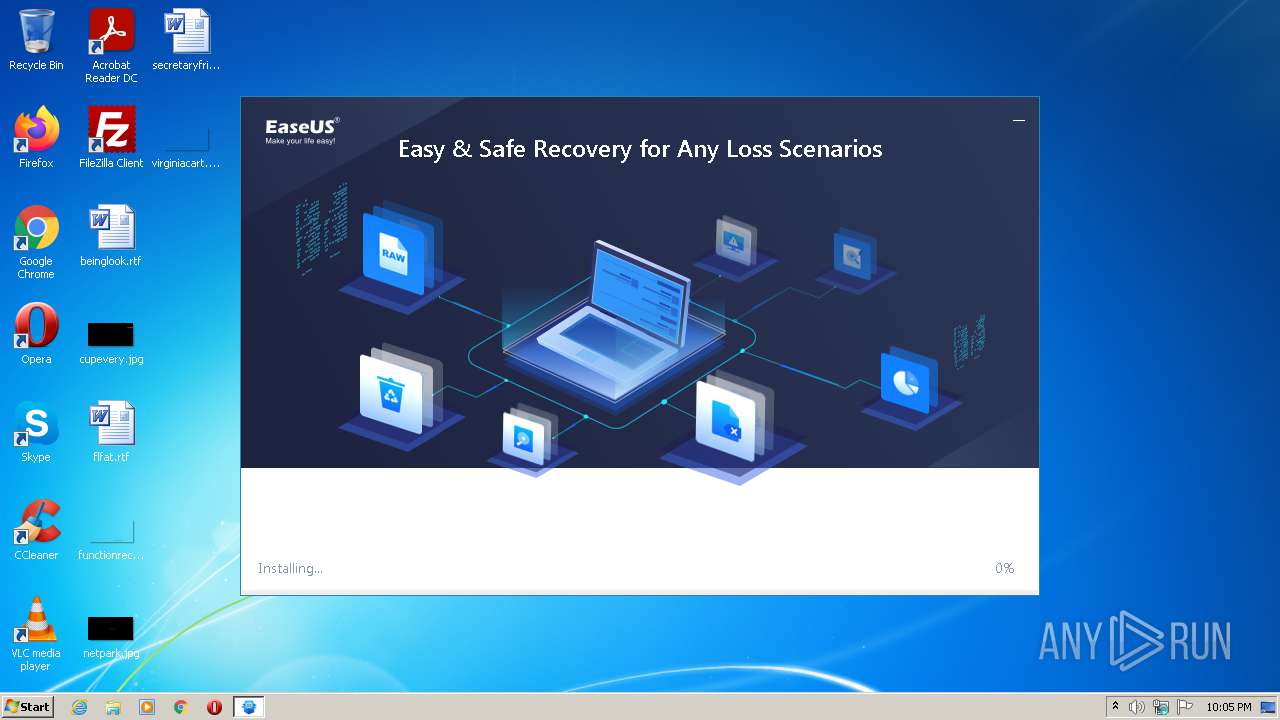
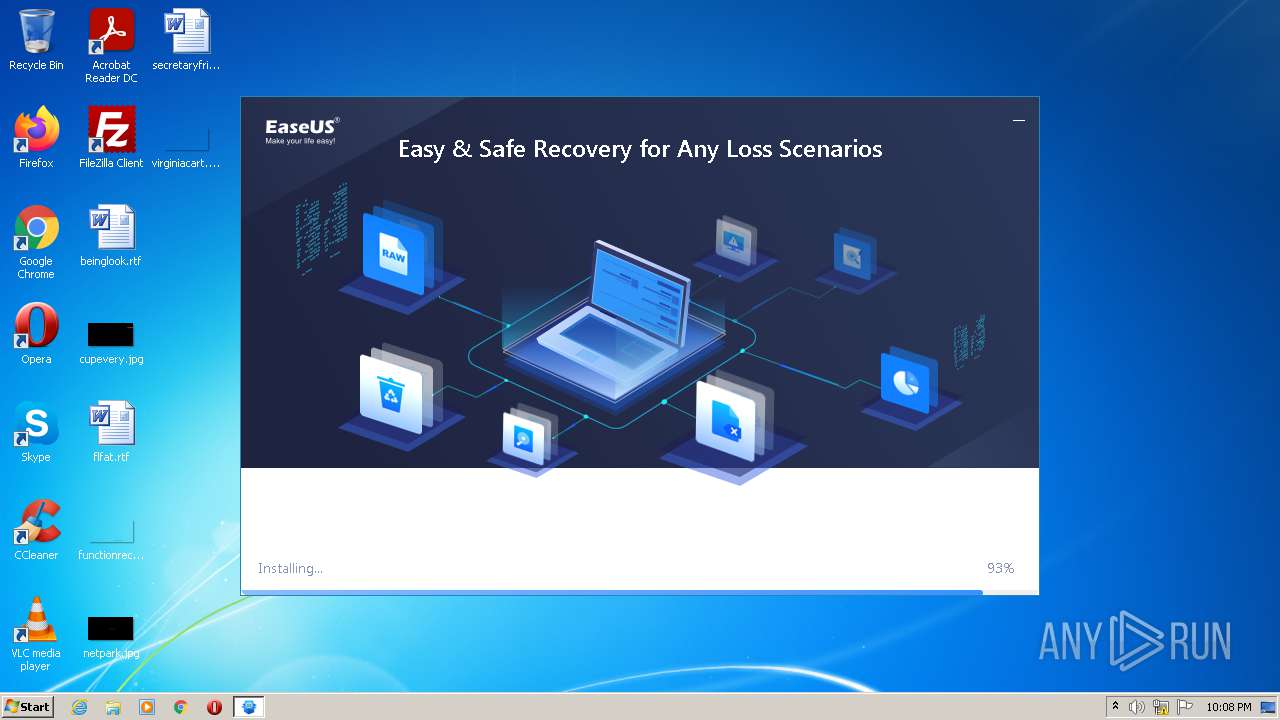
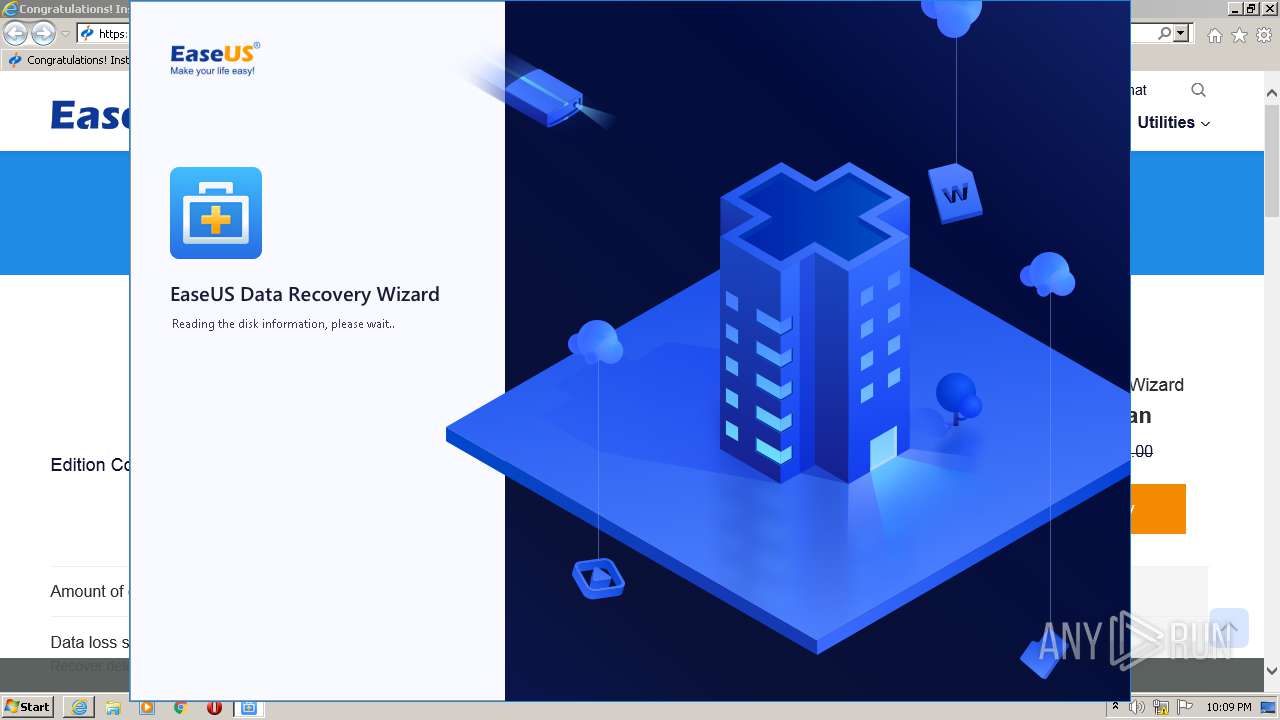
| File name: | DRW_Ad_Google_Installer_20211011.387080.exe |
| Full analysis: | https://app.any.run/tasks/a38828d4-cdec-4bc6-b407-572bcbc5cf3b |
| Verdict: | Malicious activity |
| Analysis date: | October 11, 2021, 21:04:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 3595689432C5E3F604EE27F522E2DE03 |
| SHA1: | 13E8BEFB92535BADE66DD5477032E53782AC0079 |
| SHA256: | D67D017A77BFAF9FC89FFE578AC07F3D5B4B51629B20992B78C132CAA7C363A2 |
| SSDEEP: | 49152:S/eviMJKDPTn92FW6HgprKebEQVkZPGOdCRyBin8dYMH:FHJEPTn274bjWfdCRKi8ug |
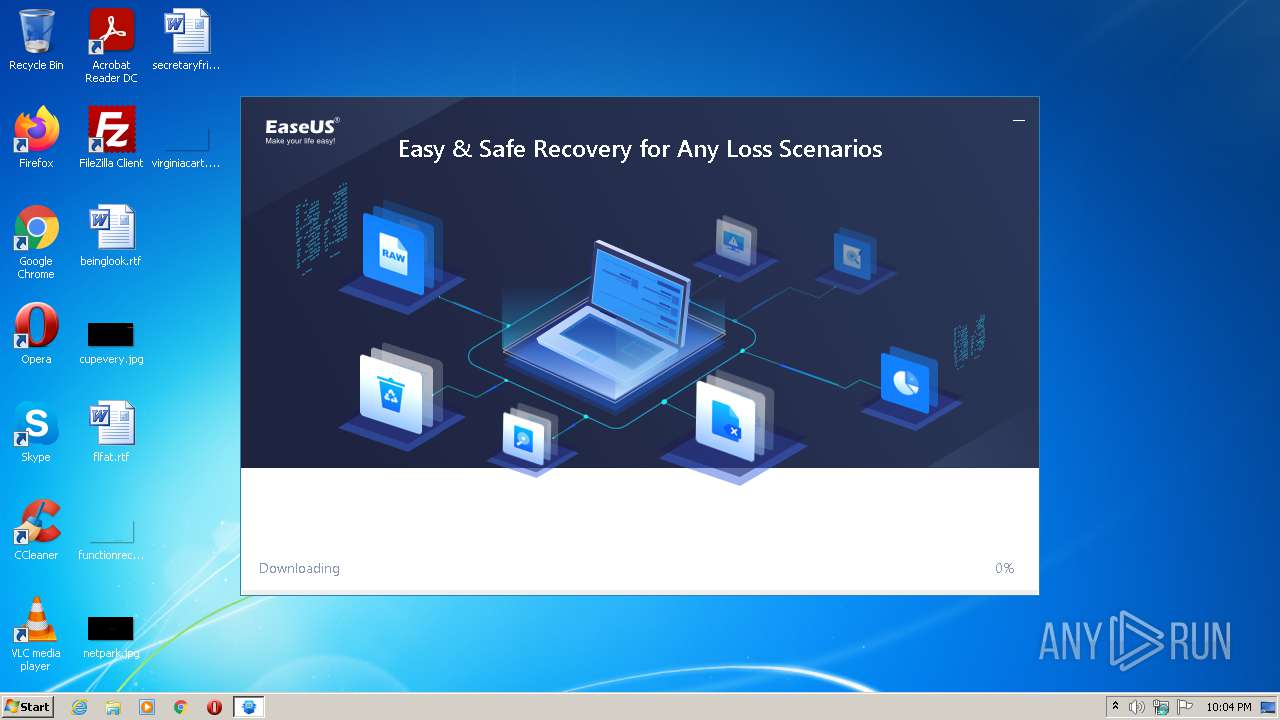
MALICIOUS
Drops executable file immediately after starts
- DRW_Ad_Google_Installer_20211011.387080.exe (PID: 3880)
- drw_trial.exe (PID: 2256)
- drw_trial.tmp (PID: 1264)
- EnsUtils.exe (PID: 2984)
Application was dropped or rewritten from another process
- InfoForSetup.exe (PID: 2168)
- EDownloader.exe (PID: 3996)
- AliyunWrapExe.Exe (PID: 1160)
- InfoForSetup.exe (PID: 4080)
- InfoForSetup.exe (PID: 3408)
- InfoForSetup.exe (PID: 332)
- InfoForSetup.exe (PID: 1900)
- InfoForSetup.exe (PID: 4020)
- InfoForSetup.exe (PID: 4088)
- AliyunWrapExe.Exe (PID: 2932)
- InfoForSetup.exe (PID: 3876)
- EUinApp.exe (PID: 3592)
- EnsUtils.exe (PID: 2984)
- EuSendMessage.exe (PID: 3020)
- InfoForSetup.exe (PID: 3724)
- InfoForSetup.exe (PID: 1476)
- ensserver.exe (PID: 3844)
- SetupUE.exe (PID: 2320)
- AliyunWrapExe.Exe (PID: 3024)
- wpn-grant.exe (PID: 3716)
- InfoForSetup.exe (PID: 3328)
- wpn.exe (PID: 4020)
- InfoForSetup.exe (PID: 1604)
- DRW.exe (PID: 3376)
- DRWUI.exe (PID: 2928)
- InfoForSetup.exe (PID: 3404)
- EuDownloader.exe (PID: 3572)
- InfoForSetup.exe (PID: 3524)
- InfoForSetup.exe (PID: 3364)
- InfoForSetup.exe (PID: 1840)
- InfoForSetup.exe (PID: 920)
- InfoForSetup.exe (PID: 272)
- InfoForSetup.exe (PID: 2608)
- InfoForSetup.exe (PID: 2004)
- InfoForSetup.exe (PID: 2956)
- InfoForSetup.exe (PID: 4020)
- InfoForSetup.exe (PID: 3772)
- InfoForSetup.exe (PID: 2664)
- InfoForSetup.exe (PID: 3104)
- InfoForSetup.exe (PID: 3584)
- EuDownloader.exe (PID: 1844)
- EUUnZip.exe (PID: 1300)
- InfoForSetup.exe (PID: 1900)
Loads dropped or rewritten executable
- InfoForSetup.exe (PID: 4080)
- AliyunWrapExe.Exe (PID: 1160)
- InfoForSetup.exe (PID: 2168)
- InfoForSetup.exe (PID: 3408)
- InfoForSetup.exe (PID: 332)
- InfoForSetup.exe (PID: 1900)
- InfoForSetup.exe (PID: 4020)
- InfoForSetup.exe (PID: 4088)
- InfoForSetup.exe (PID: 3876)
- AliyunWrapExe.Exe (PID: 2932)
- EnsUtils.exe (PID: 2984)
- InfoForSetup.exe (PID: 3724)
- InfoForSetup.exe (PID: 1476)
- AliyunWrapExe.Exe (PID: 3024)
- ensserver.exe (PID: 3844)
- wpn-grant.exe (PID: 3716)
- wpn.exe (PID: 4020)
- InfoForSetup.exe (PID: 3328)
- InfoForSetup.exe (PID: 1604)
- DRW.exe (PID: 3376)
- DRWUI.exe (PID: 2928)
- InfoForSetup.exe (PID: 3404)
- InfoForSetup.exe (PID: 3364)
- InfoForSetup.exe (PID: 3524)
- InfoForSetup.exe (PID: 1840)
- InfoForSetup.exe (PID: 272)
- InfoForSetup.exe (PID: 2004)
- InfoForSetup.exe (PID: 2956)
- InfoForSetup.exe (PID: 920)
- InfoForSetup.exe (PID: 2608)
- InfoForSetup.exe (PID: 4020)
- InfoForSetup.exe (PID: 3772)
- InfoForSetup.exe (PID: 3104)
- InfoForSetup.exe (PID: 2664)
- InfoForSetup.exe (PID: 1900)
- InfoForSetup.exe (PID: 3584)
Changes settings of System certificates
- ensserver.exe (PID: 3844)
SUSPICIOUS
Checks supported languages
- DRW_Ad_Google_Installer_20211011.387080.exe (PID: 3880)
- EDownloader.exe (PID: 3996)
- AliyunWrapExe.Exe (PID: 1160)
- InfoForSetup.exe (PID: 4080)
- InfoForSetup.exe (PID: 2168)
- InfoForSetup.exe (PID: 3408)
- InfoForSetup.exe (PID: 332)
- InfoForSetup.exe (PID: 1900)
- InfoForSetup.exe (PID: 4020)
- InfoForSetup.exe (PID: 4088)
- drw_trial.exe (PID: 2256)
- drw_trial.tmp (PID: 1264)
- AliyunWrapExe.Exe (PID: 2932)
- InfoForSetup.exe (PID: 2532)
- InfoForSetup.exe (PID: 1924)
- InfoForSetup.exe (PID: 2008)
- InfoForSetup.exe (PID: 3796)
- EUinApp.exe (PID: 3592)
- EuSendMessage.exe (PID: 3020)
- EnsUtils.exe (PID: 2984)
- InfoForSetup.exe (PID: 1976)
- SetupUE.exe (PID: 2320)
- InfoForSetup.exe (PID: 3724)
- InfoForSetup.exe (PID: 1476)
- ensserver.exe (PID: 3844)
- AliyunWrapExe.Exe (PID: 3024)
- wpn-grant.exe (PID: 3716)
- InfoForSetup.exe (PID: 3328)
- wpn.exe (PID: 4020)
- InfoForSetup.exe (PID: 1604)
- DRW.exe (PID: 3376)
- DRWUI.exe (PID: 2928)
- InfoForSetup.exe (PID: 3876)
- InfoForSetup.exe (PID: 3404)
- EuDownloader.exe (PID: 3572)
- InfoForSetup.exe (PID: 3364)
- InfoForSetup.exe (PID: 3524)
- wmic.exe (PID: 2704)
- InfoForSetup.exe (PID: 1840)
- PowerShell.exe (PID: 2280)
- InfoForSetup.exe (PID: 2004)
- InfoForSetup.exe (PID: 4020)
- InfoForSetup.exe (PID: 2956)
- InfoForSetup.exe (PID: 272)
- InfoForSetup.exe (PID: 920)
- InfoForSetup.exe (PID: 2608)
- InfoForSetup.exe (PID: 3772)
- InfoForSetup.exe (PID: 2664)
- InfoForSetup.exe (PID: 3104)
- InfoForSetup.exe (PID: 1900)
- InfoForSetup.exe (PID: 3584)
- EuDownloader.exe (PID: 1844)
- EUUnZip.exe (PID: 1300)
Reads the computer name
- DRW_Ad_Google_Installer_20211011.387080.exe (PID: 3880)
- EDownloader.exe (PID: 3996)
- AliyunWrapExe.Exe (PID: 1160)
- drw_trial.tmp (PID: 1264)
- AliyunWrapExe.Exe (PID: 2932)
- EnsUtils.exe (PID: 2984)
- AliyunWrapExe.Exe (PID: 3024)
- ensserver.exe (PID: 3844)
- wpn-grant.exe (PID: 3716)
- wpn.exe (PID: 4020)
- DRWUI.exe (PID: 2928)
- EuDownloader.exe (PID: 3572)
- wmic.exe (PID: 2704)
- PowerShell.exe (PID: 2280)
- EuDownloader.exe (PID: 1844)
Drops a file that was compiled in debug mode
- DRW_Ad_Google_Installer_20211011.387080.exe (PID: 3880)
- drw_trial.tmp (PID: 1264)
- EnsUtils.exe (PID: 2984)
Executable content was dropped or overwritten
- DRW_Ad_Google_Installer_20211011.387080.exe (PID: 3880)
- drw_trial.exe (PID: 2256)
- drw_trial.tmp (PID: 1264)
- EnsUtils.exe (PID: 2984)
Reads Microsoft Outlook installation path
- EDownloader.exe (PID: 3996)
- iexplore.exe (PID: 3784)
Reads internet explorer settings
- EDownloader.exe (PID: 3996)
Reads Windows owner or organization settings
- drw_trial.tmp (PID: 1264)
Reads the Windows organization settings
- drw_trial.tmp (PID: 1264)
Drops a file with a compile date too recent
- drw_trial.tmp (PID: 1264)
- EnsUtils.exe (PID: 2984)
Drops a file with too old compile date
- drw_trial.tmp (PID: 1264)
- EnsUtils.exe (PID: 2984)
Changes IE settings (feature browser emulation)
- EUinApp.exe (PID: 3592)
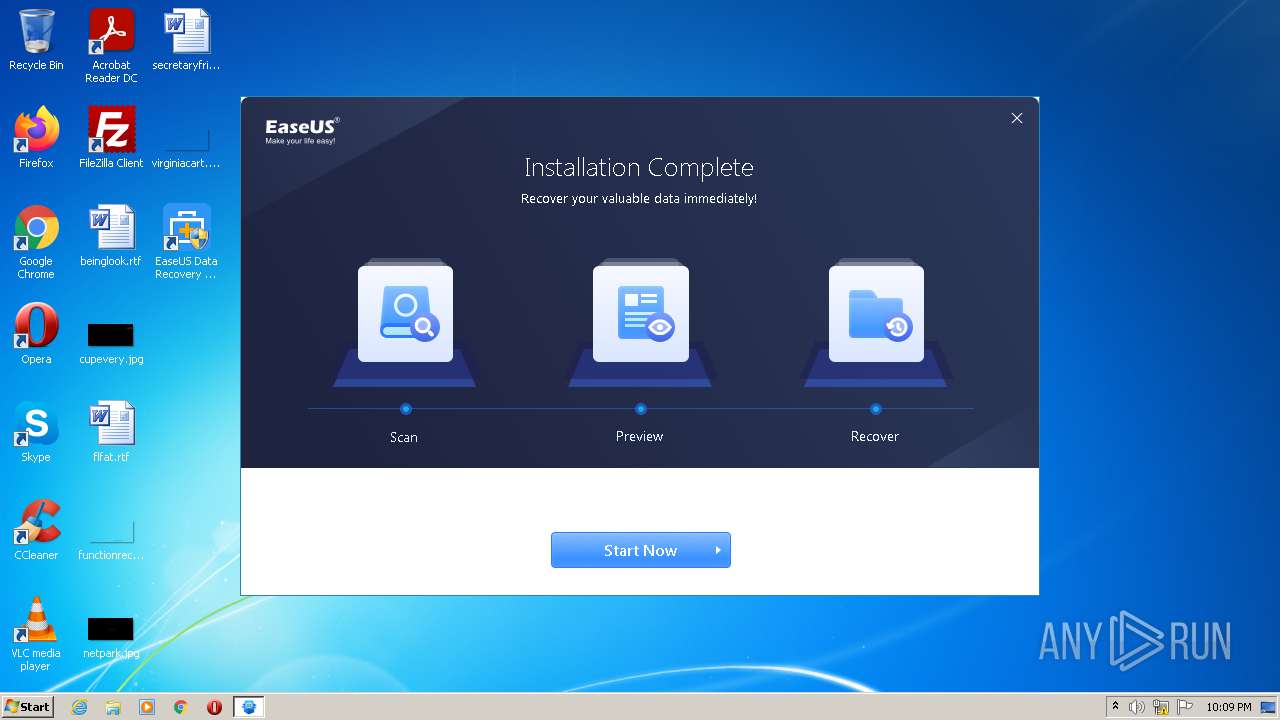
Creates a directory in Program Files
- EnsUtils.exe (PID: 2984)
- ensserver.exe (PID: 3844)
- drw_trial.tmp (PID: 1264)
- DRWUI.exe (PID: 2928)
Creates files in the program directory
- EnsUtils.exe (PID: 2984)
- ensserver.exe (PID: 3844)
- AliyunWrapExe.Exe (PID: 3024)
- DRW.exe (PID: 3376)
- DRWUI.exe (PID: 2928)
- EuDownloader.exe (PID: 3572)
- EuDownloader.exe (PID: 1844)
Executed as Windows Service
- ensserver.exe (PID: 3844)
Adds / modifies Windows certificates
- ensserver.exe (PID: 3844)
Creates files in the Windows directory
- ensserver.exe (PID: 3844)
Searches for installed software
- EDownloader.exe (PID: 3996)
- DRWUI.exe (PID: 2928)
Starts Internet Explorer
- EDownloader.exe (PID: 3996)
Executes PowerShell scripts
- DRWUI.exe (PID: 2928)
Reads the date of Windows installation
- PowerShell.exe (PID: 2280)
Creates files in the user directory
- PowerShell.exe (PID: 2280)
Reads CPU info
- DRWUI.exe (PID: 2928)
INFO
Application was dropped or rewritten from another process
- drw_trial.tmp (PID: 1264)
- InfoForSetup.exe (PID: 2008)
- InfoForSetup.exe (PID: 3796)
- InfoForSetup.exe (PID: 2532)
- InfoForSetup.exe (PID: 1924)
- InfoForSetup.exe (PID: 1976)
Loads dropped or rewritten executable
- InfoForSetup.exe (PID: 3796)
- InfoForSetup.exe (PID: 1924)
- InfoForSetup.exe (PID: 2008)
- InfoForSetup.exe (PID: 2532)
- InfoForSetup.exe (PID: 1976)
Creates a software uninstall entry
- drw_trial.tmp (PID: 1264)
Reads settings of System Certificates
- ensserver.exe (PID: 3844)
- iexplore.exe (PID: 3784)
- iexplore.exe (PID: 3600)
Checks Windows Trust Settings
- ensserver.exe (PID: 3844)
- iexplore.exe (PID: 3784)
- iexplore.exe (PID: 3600)
Checks supported languages
- iexplore.exe (PID: 3600)
- iexplore.exe (PID: 3784)
- fsutil.exe (PID: 2416)
- fsutil.exe (PID: 2328)
Reads the computer name
- iexplore.exe (PID: 3600)
- iexplore.exe (PID: 3784)
Changes internet zones settings
- iexplore.exe (PID: 3600)
Application launched itself
- iexplore.exe (PID: 3600)
Dropped object may contain Bitcoin addresses
- drw_trial.tmp (PID: 1264)
Creates files in the program directory
- drw_trial.tmp (PID: 1264)
Changes settings of System certificates
- iexplore.exe (PID: 3784)
Reads internet explorer settings
- iexplore.exe (PID: 3784)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3784)
Creates files in the user directory
- iexplore.exe (PID: 3784)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 04:57:48+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2018 03:57:48 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jan-2018 03:57:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006627 | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45224 |
.rdata | 0x00008000 | 0x0000149A | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00708 |
.data | 0x0000A000 | 0x0002AFF8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03532 |
.ndata | 0x00035000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00045000 | 0x00010D40 | 0x00010E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.14037 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28733 | 841 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 4.86193 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 5.0916 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 3.68334 | 3752 | UNKNOWN | English - United States | RT_ICON |
5 | 3.86293 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 3.67461 | 1640 | UNKNOWN | English - United States | RT_ICON |
7 | 3.5329 | 1384 | UNKNOWN | English - United States | RT_ICON |
8 | 5.22737 | 1128 | UNKNOWN | English - United States | RT_ICON |
9 | 3.99637 | 744 | UNKNOWN | English - United States | RT_ICON |
10 | 3.53259 | 296 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
114
Monitored processes
58
Malicious processes
20
Suspicious processes
12
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | /SendInfo Window "Loading" Activity "Info_Powershell_Getphysicaldisk" Attribute "[\"Get_PhysicalDisk _ The term _Get_PhysicalDisk_ is not recognized as the name __of a cmdlet_ function_ script file_ or operable program. Check the spelling of __the name_ or if a path was included_ verify that the path is correct and try __again.__At line_1 char_1___ Get_PhysicalDisk _ Format_Table _AutoSize___ __________________ _ CategoryInfo _ ObjectNotFound_ _Get_PhysicalDisk_String_ ___ Co __ mmandNotFoundException__ _ FullyQualifiedErrorId _ CommandNotFoundException__ __\"]" | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\aliyun\InfoForSetup.exe | — | DRWUI.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 332 | /SendInfo Window "Home_Installer" Activity "Click_Install" Attribute "{\"Install_Path\":\"C:/Program Files/EaseUS/EaseUS Data Recovery Wizard\",\"Language\":\"English\",\"Os\":\"Microsoft Windows 7\",\"Pageid\":\"387080\",\"Timezone\":\"GMT-00:00\"}" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2Ad_Google\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 776 | "C:\Users\admin\AppData\Local\Temp\DRW_Ad_Google_Installer_20211011.387080.exe" | C:\Users\admin\AppData\Local\Temp\DRW_Ad_Google_Installer_20211011.387080.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 920 | /SendInfo Window "Loading" Activity "Info_Start" | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\aliyun\InfoForSetup.exe | — | DRWUI.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1160 | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2Ad_Google\aliyun\AliyunWrapExe.Exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2Ad_Google\aliyun\AliyunWrapExe.Exe | InfoForSetup.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1264 | "C:\Users\admin\AppData\Local\Temp\is-ET6N0.tmp\drw_trial.tmp" /SL5="$1014A,47224918,192512,C:\Users\admin\AppData\Local\Temp\drw_trial.exe" /verysilent /DIR="C:\Program Files\EaseUS\EaseUS Data Recovery Wizard" /LANG=en agreeImprove= GUID=S-1-5-21-1302019708-1500728564-335382590-1000 xurlID=387080 TestID=AG14400-08261 | C:\Users\admin\AppData\Local\Temp\is-ET6N0.tmp\drw_trial.tmp | drw_trial.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1300 | "C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\EUUnZip.exe" "C:\Program Files\EaseUS\EaseUS Data Recovery Wizard/InnerBuyRSS.zip" "C:\Program Files\EaseUS\EaseUS Data Recovery Wizard/InnerBuyRSS" | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\EUUnZip.exe | — | DRWUI.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\aliyun\InfoForSetup.exe" /SendInfo "Window" "Install" "Activity" "Info_Userinfo" "Attribute" "{\"Language\":\"en\",\"Version\":\"Ad_Google\",\"Version_Num\":\"14.4.0.0\",\"UE\":\"Off\",\"Country\":\"United States\",\"Timezone\":\"GMT-00:00\",\"OS\":\"Microsoft Windows 7 32-bit Service Pack 1 (6.1.7601.1.256)\",\"Test_id\":\"AG14400-08261\"}" | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\aliyun\InfoForSetup.exe | — | SetupUE.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1604 | /SendInfo Window "Install_Finish" Activity "Click_Startnow" | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2Ad_Google\aliyun\InfoForSetup.exe | — | EDownloader.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1840 | /SendInfo Window "Loading" Activity "Info_Wmic_Diskdrive" Attribute "[\"Availability BytesPerSector Capabilities CapabilityDescriptions Caption CompressionMethod ConfigManagerErrorCode ConfigManagerUserConfig CreationClassName DefaultBlockSize Description DeviceID ErrorCleared ErrorDescription ErrorMethodology FirmwareRevision Index InstallDate InterfaceType LastErrorCode Manufacturer MaxBlockSize MaxMediaSize MediaLoaded MediaType MinBlockSize Model Name NeedsCleaning NumberOfMediaSupported Partitions PNPDeviceID PowerManagementCapabilities PowerManagementSupported SCSIBus SCSILogicalUnit SCSIPort SCSITargetId SectorsPerTrack SerialNumber Signature Size Status StatusInfo SystemCreationClassName SystemName TotalCylinders TotalHeads TotalSectors TotalTracks TracksPerCylinder ___ 512 _3_ 4_ 10_ __Random Access__ _Supports Writing__ _SMART Notification__ WDC WD20EARS ATA Device 0 FALSE Win32_DiskDrive Disk drive //./PHYSICALDRIVE0 1.1.0 0 IDE _Standard disk drives_ TRUE Fixed hard disk media WDC WD20EARS ATA Device //./PHYSICALDRIVE0 2 IDE/DISKWDC_WD20EARS____________________________1.1.0___/5&2770A7AF&0&0.0.0 0 0 0 0 63 4d51303030302031202020202020202020202020 1660034144 274872407040 OK Win32_ComputerSystem USER_PC 33418 255 536860170 8521590 255 ______\"]" | C:\Program Files\EaseUS\EaseUS Data Recovery Wizard\aliyun\InfoForSetup.exe | — | DRWUI.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
30 782
Read events
30 424
Write events
350
Delete events
8
Modification events
| (PID) Process: | (1160) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1160) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1160) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1160) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1160) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1160) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000042010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1160) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1160) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1160) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1160) AliyunWrapExe.Exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{C36CCF59-F508-4223-8EB4-3C3308728550} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
323
Suspicious files
35
Text files
3 979
Unknown types
99
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3880 | DRW_Ad_Google_Installer_20211011.387080.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2Ad_Google\EDownloader.exe | executable | |
MD5:— | SHA256:— | |||
| 3880 | DRW_Ad_Google_Installer_20211011.387080.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2Ad_Google\InitConfigure.ini | text | |
MD5:— | SHA256:— | |||
| 3880 | DRW_Ad_Google_Installer_20211011.387080.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2Ad_Google\skin.zip | compressed | |
MD5:— | SHA256:— | |||
| 3880 | DRW_Ad_Google_Installer_20211011.387080.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2Ad_Google\Chinese.ini | text | |
MD5:EE535DABAF3F3F2E6D93016B643A17D1 | SHA256:A1C341F2D50642DF21301DCB29C5BAC1A4F0F0C2184A6A26AD71707E96DF1BB2 | |||
| 3880 | DRW_Ad_Google_Installer_20211011.387080.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2Ad_Google\Japanese.ini | text | |
MD5:C8ABAF56082F7DC95CBEF96ED45796D5 | SHA256:2E56CA201793AE96190C93D07B4E2FE3AC93100C8ECA7291957589BDDA3E55AA | |||
| 3880 | DRW_Ad_Google_Installer_20211011.387080.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2Ad_Google\French.ini | text | |
MD5:7DAABFA7D17D2E8FD1DB1B84DC1E5434 | SHA256:3A2B93EBA48F27F60C5416CA092ACEDCFFA7F1BEEB538EEA1A5A43B41A6462B8 | |||
| 3880 | DRW_Ad_Google_Installer_20211011.387080.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2Ad_Google\LanguageTransfor.ini | text | |
MD5:FFE692A67871185785EC705B1CC12C81 | SHA256:373BEC6E7976324FF879C2988BAB772C69336D7BCB9A32386A6021568350A824 | |||
| 3880 | DRW_Ad_Google_Installer_20211011.387080.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2Ad_Google\Korean.ini | text | |
MD5:FA10579CF0A48B77AABFE00C527E4AB8 | SHA256:61A7DD64C03F9A82201D9E49AA0F724092E39EEF8A1192EC9211AA792863287A | |||
| 3880 | DRW_Ad_Google_Installer_20211011.387080.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2Ad_Google\Portuguese.ini | text | |
MD5:ABE01F464AD8A41B55B85B5D5F828EA5 | SHA256:4850F8BE8D7BC979FC9131B07BD2269B4790640FD20922FDD4813145D21E421A | |||
| 3880 | DRW_Ad_Google_Installer_20211011.387080.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\2Ad_Google\Mungarian.ini | text | |
MD5:3AE5A1C7EEB896D95D0C32E04C5BA9D0 | SHA256:FE8EED515E5F7610B307759201C4B5538C1D0484A442B924AB02650E54AAC397 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
102
DNS requests
38
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
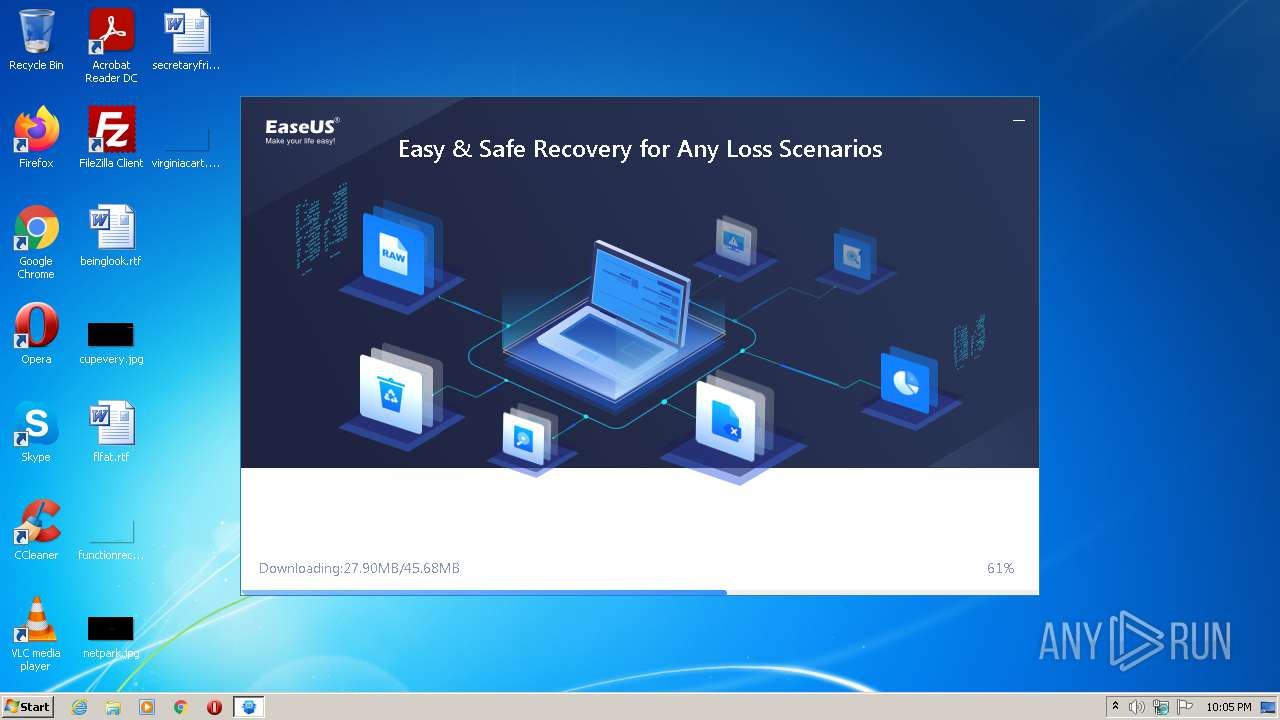
3996 | EDownloader.exe | GET | — | 69.16.175.42:80 | http://download.easeus.com/ad/drw_trial.exe | US | — | — | malicious |
3996 | EDownloader.exe | GET | — | 69.16.175.42:80 | http://download.easeus.com/ad/drw_trial.exe | US | — | — | malicious |
3996 | EDownloader.exe | GET | — | 69.16.175.42:80 | http://download.easeus.com/ad/drw_trial.exe | US | — | — | malicious |
3996 | EDownloader.exe | GET | — | 69.16.175.42:80 | http://download.easeus.com/ad/drw_trial.exe | US | — | — | malicious |
3996 | EDownloader.exe | POST | 200 | 69.16.175.42:80 | http://download.easeus.com/api2/index.php/Apicp/Drwdl202004/index/ | US | text | 476 b | malicious |
1160 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.212:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | US | — | — | unknown |
1160 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.212:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | US | — | — | unknown |
1160 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.212:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | US | — | — | unknown |
1160 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.212:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | US | — | — | unknown |
1160 | AliyunWrapExe.Exe | POST | 200 | 47.252.97.212:80 | http://easeusinfo.us-east-1.log.aliyuncs.com/logstores/logstore_drw_ip/shards/lb | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1160 | AliyunWrapExe.Exe | 216.92.47.198:80 | track.easeus.com | pair Networks | US | suspicious |
1160 | AliyunWrapExe.Exe | 47.252.97.212:80 | easeusinfo.us-east-1.log.aliyuncs.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
3996 | EDownloader.exe | 69.16.175.42:80 | download.easeus.com | Highwinds Network Group, Inc. | US | malicious |
— | — | 47.252.97.212:80 | easeusinfo.us-east-1.log.aliyuncs.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
2932 | AliyunWrapExe.Exe | 216.92.47.198:80 | track.easeus.com | pair Networks | US | suspicious |
2932 | AliyunWrapExe.Exe | 47.252.97.212:80 | easeusinfo.us-east-1.log.aliyuncs.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
3024 | AliyunWrapExe.Exe | 216.92.47.198:80 | track.easeus.com | pair Networks | US | suspicious |
2932 | AliyunWrapExe.Exe | 47.252.97.9:80 | easeusinfo.us-east-1.log.aliyuncs.com | Alibaba (China) Technology Co., Ltd. | US | unknown |
3844 | ensserver.exe | 205.185.216.42:443 | update.easeus.com | Highwinds Network Group, Inc. | US | whitelisted |
3844 | ensserver.exe | 151.139.128.14:80 | ocsp.comodoca.com | Highwinds Network Group, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.easeus.com |
| malicious |
track.easeus.com |
| suspicious |
easeusinfo.us-east-1.log.aliyuncs.com |
| unknown |
dns.msftncsi.com |
| shared |
update.easeus.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
android.clients.google.com |
| whitelisted |
fcm.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3996 | EDownloader.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3996 | EDownloader.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
EDownloader.exe | [3988]-22:04:39:222 ParseCmdLine param=EXEDIR=C:\Users\admin\AppData\Local\Temp ||| EXENAME=DRW_Ad_Google_Installer_20211011.387080.exe ||| DOWNLOAD_VERSION=Ad_Google ||| PRODUCT_VERSION=1.0.0 ||| INSTALL_TYPE=0
|
EDownloader.exe | [3988]-22:04:39:253 Install recomand return=259
|
EDownloader.exe | [3988]-22:04:39:488 Install recomand return=259
|
EDownloader.exe | [2776]-22:04:39:566 PostData Start download url=http://download.easeus.com/api2/index.php/Apicp/Drwdl202004/index/?exeNumber=387080&lang=English&pcVersion=home&pid=2&tid=1&version=Ad_Google
|
EDownloader.exe | [2776]-22:04:43:675 PostData end
|
EDownloader.exe | [2776]-22:04:43:675 Json parse Data Start
|
EDownloader.exe | [2776]-22:04:43:675 Json parse Data end
|
EDownloader.exe | [3988]-22:04:43:675 CHttpHelper::GetDownloadInfo 45 download info code:0
|
EDownloader.exe | [3988]-22:04:43:675 Install recomand return=259
|
EDownloader.exe | [3988]-22:04:47:550 Install recomand return=259
|