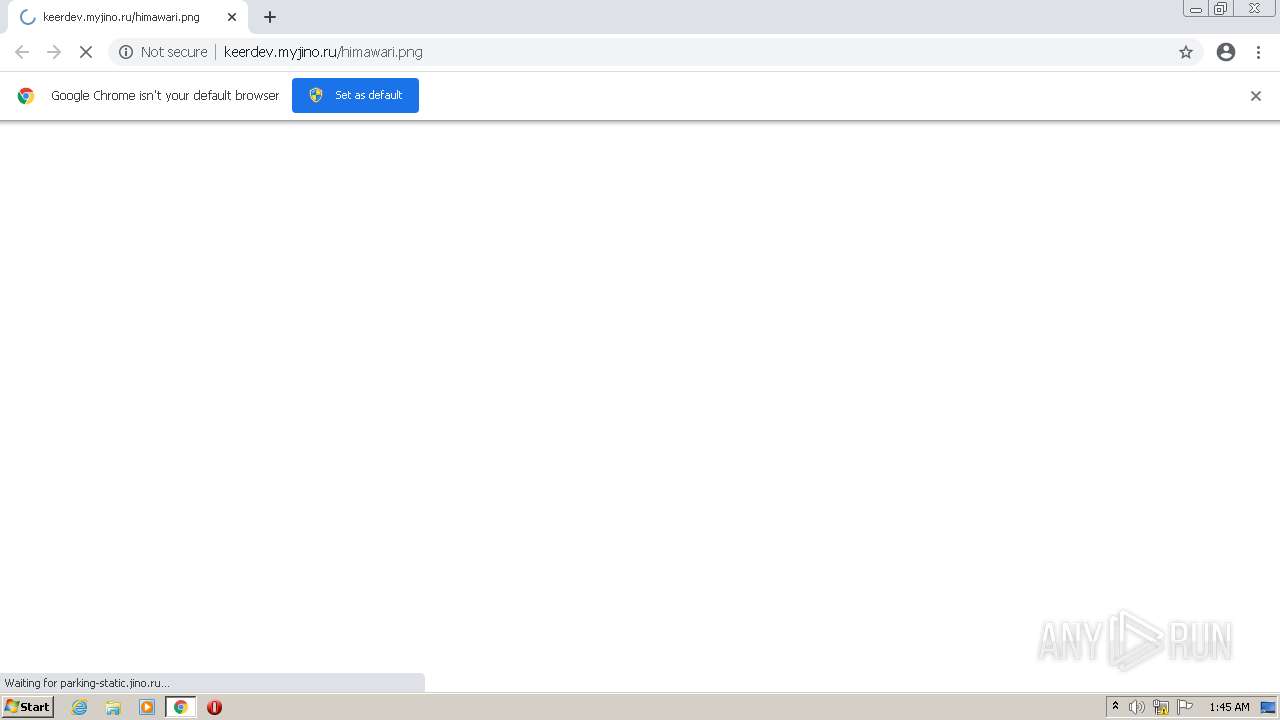
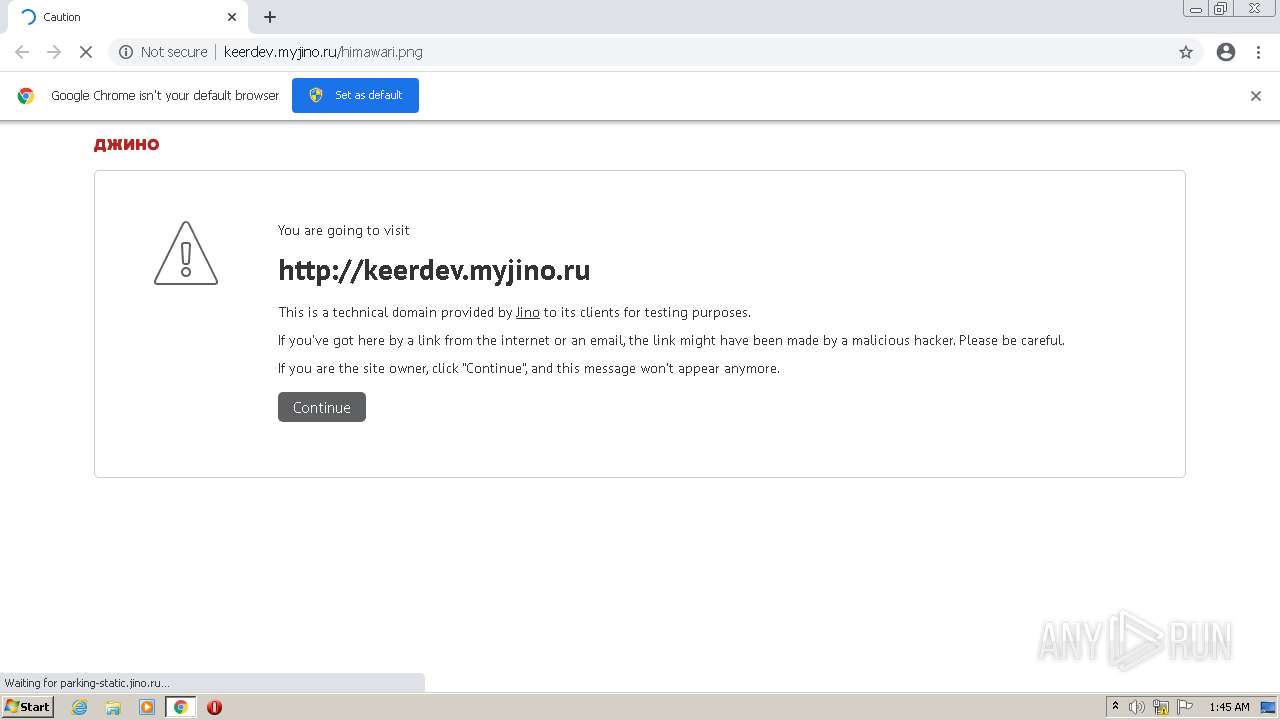
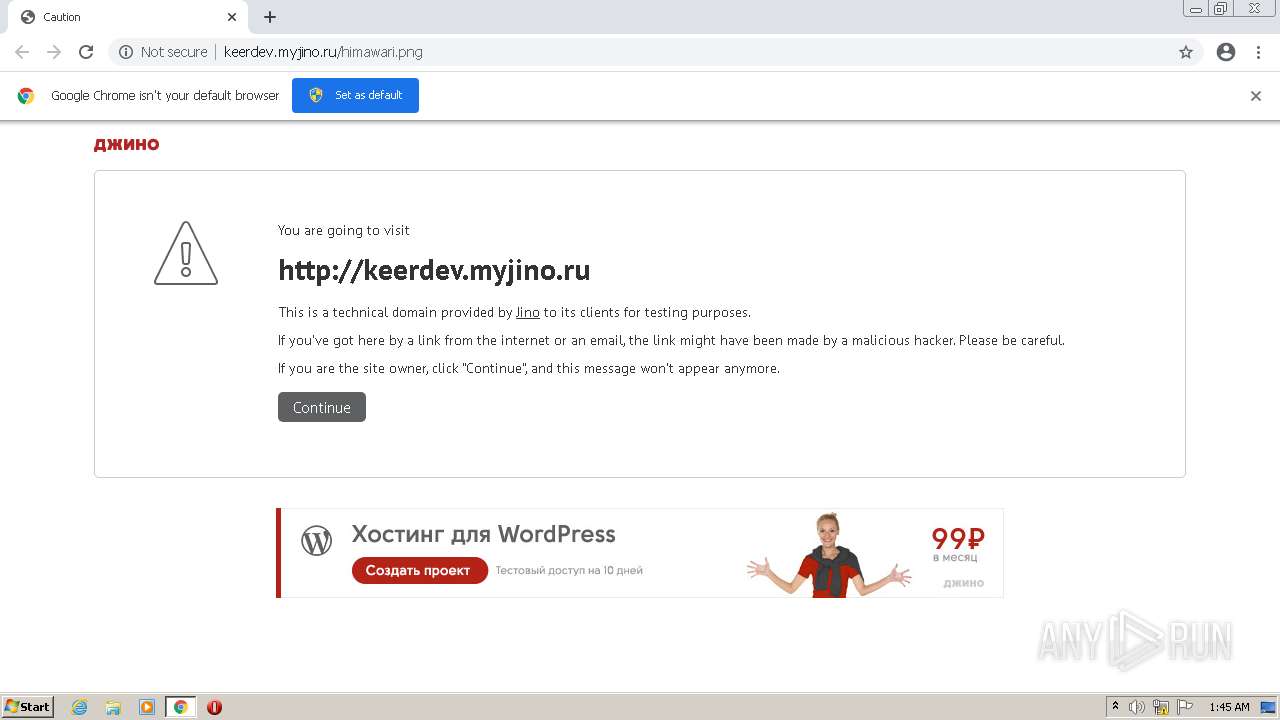
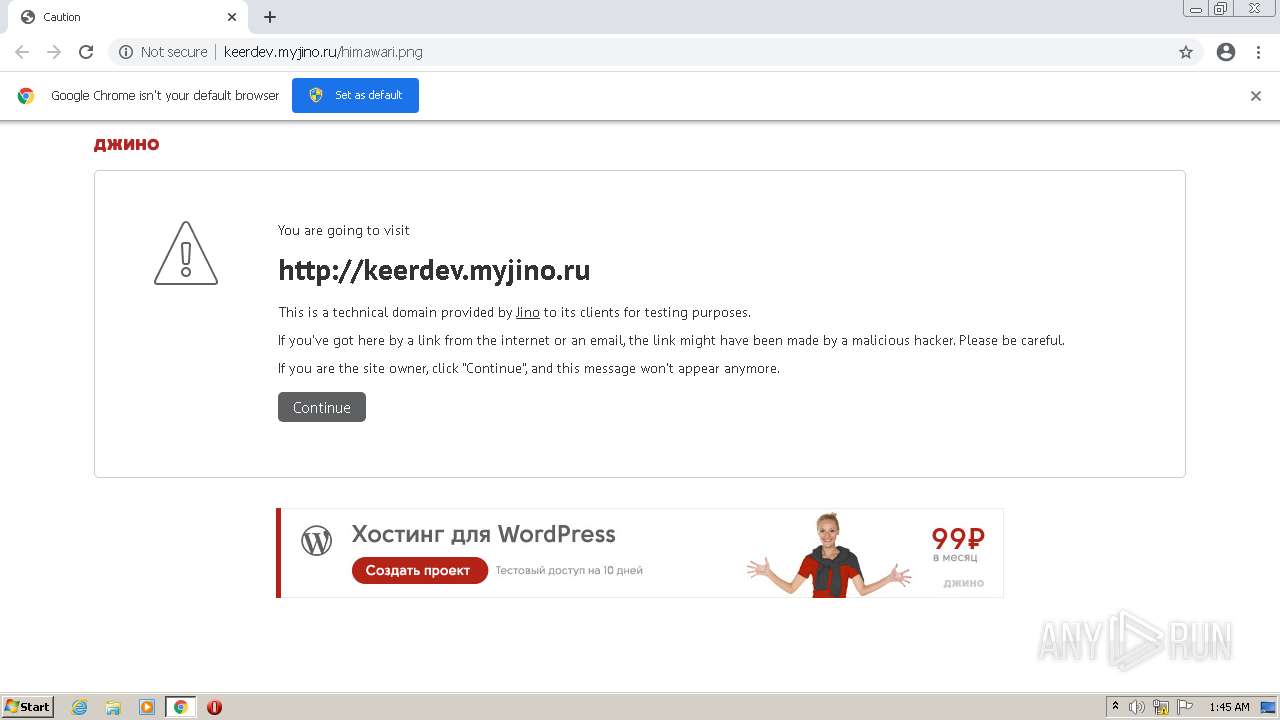
| URL: | http://keerdev.myjino.ru/himawari.png |
| Full analysis: | https://app.any.run/tasks/5e822364-e38d-4325-a31c-369db66ed46c |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 00:45:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 55EDB444A440AE0D897913C19DBB1215 |
| SHA1: | 8EABE277063AB57DB25E874634FAFE5A1FA57C07 |
| SHA256: | D67C5F1C103728D065DCCBD6CBBBD5A3589D44C75181351E80DEEBDEFA90EC18 |
| SSDEEP: | 3:N1KVAFZLAKXAch2:CqPA8Ach2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3364)
INFO
Checks supported languages
- chrome.exe (PID: 3364)
- chrome.exe (PID: 3564)
- chrome.exe (PID: 1652)
- chrome.exe (PID: 2168)
- chrome.exe (PID: 2224)
- chrome.exe (PID: 3020)
- chrome.exe (PID: 1432)
- chrome.exe (PID: 3320)
- chrome.exe (PID: 2480)
- chrome.exe (PID: 2932)
- chrome.exe (PID: 2648)
- chrome.exe (PID: 448)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 3712)
Application launched itself
- chrome.exe (PID: 3364)
Reads the computer name
- chrome.exe (PID: 3364)
- chrome.exe (PID: 2168)
- chrome.exe (PID: 3320)
- chrome.exe (PID: 1652)
- chrome.exe (PID: 3112)
- chrome.exe (PID: 448)
- chrome.exe (PID: 3712)
Reads the hosts file
- chrome.exe (PID: 3364)
- chrome.exe (PID: 2168)
Reads settings of System Certificates
- chrome.exe (PID: 2168)
Reads the date of Windows installation
- chrome.exe (PID: 3712)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
14
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 448 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3764 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1432 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1848 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1652 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgACAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --mojo-platform-channel-handle=1084 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --field-trial-handle=1048,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --mojo-platform-channel-handle=1260 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2224 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1824 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2480 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3792 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3484 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2808 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 3112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1048,6709775911954246668,6484311519900221412,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1728 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
14 325
Read events
14 254
Write events
71
Delete events
0
Modification events
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (3364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
0
Suspicious files
21
Text files
62
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-633CD3A8-D24.pma | — | |
MD5:— | SHA256:— | |||
| 3564 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f2866b98-c385-444b-b008-5187451c6a4b.tmp | text | |
MD5:— | SHA256:— | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFcd6be.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFcd6ae.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFcd6ae.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 3364 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ab4cc902-c010-4910-82c2-2e279634b158.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
68
DNS requests
33
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2168 | chrome.exe | GET | 302 | 77.88.21.119:80 | http://mc.yandex.ru/metrika/watch.js | RU | — | — | whitelisted |
2168 | chrome.exe | GET | 200 | 151.236.71.19:80 | http://cache.betweendigital.com/code/async_rtb.js | RU | text | 108 Kb | whitelisted |
2168 | chrome.exe | GET | 200 | 195.161.41.160:80 | http://parking-static.jino.ru/static/main.js?1.25.2 | RU | text | 37.6 Kb | suspicious |
2168 | chrome.exe | GET | 200 | 195.161.41.160:80 | http://parking-static.jino.ru/static/components/page/logo.svg | RU | image | 1.20 Kb | suspicious |
2168 | chrome.exe | GET | 200 | 195.161.41.160:80 | http://parking-static.jino.ru/static/components/page/icons/page_error.svg | RU | image | 724 b | suspicious |
2168 | chrome.exe | GET | 200 | 104.110.191.133:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?12f7b3612625d5f8 | US | compressed | 60.9 Kb | whitelisted |
2168 | chrome.exe | GET | 200 | 104.16.117.195:80 | http://pre.glotgrx.com/impimg.gif?cb=1664930732175&qid=53532313f523632313f5436393&cid=964&s=http://keerdev.myjino.ru&p=BX&x=&adtg=266562&nsi=&si=&nci=&nai=&ua=Mozilla/5.0%20(Windows%20NT%206.1)%20AppleWebKit/537.36%20(KHTML,%20like%20Gecko)%20Chrome/86.0.4240.198%20Safari/537.36&ai=&flsrc=1 | US | image | 26 b | whitelisted |
2168 | chrome.exe | GET | 200 | 104.110.191.133:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?4f23048a1f80976c | US | compressed | 60.9 Kb | whitelisted |
2168 | chrome.exe | GET | 200 | 104.110.191.133:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?8ced0b099b9e0ddb | US | compressed | 60.9 Kb | whitelisted |
2168 | chrome.exe | GET | 200 | 81.177.141.181:80 | http://keerdev.myjino.ru/himawari.png | RU | html | 1.06 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2168 | chrome.exe | 142.250.186.142:443 | clients2.google.com | GOOGLE | US | whitelisted |
2168 | chrome.exe | 172.217.23.109:443 | accounts.google.com | GOOGLE | US | suspicious |
— | — | 81.177.141.181:80 | keerdev.myjino.ru | JSC RTComm.RU | RU | suspicious |
2168 | chrome.exe | 81.177.141.181:80 | keerdev.myjino.ru | JSC RTComm.RU | RU | suspicious |
2168 | chrome.exe | 195.161.41.160:80 | parking-static.jino.ru | JSC RTComm.RU | RU | suspicious |
2168 | chrome.exe | 77.88.21.119:80 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
2168 | chrome.exe | 172.217.16.129:443 | clients2.googleusercontent.com | GOOGLE | US | whitelisted |
— | — | 151.236.71.19:80 | cache.betweendigital.com | CDNetworks LLC | RU | unknown |
2168 | chrome.exe | 77.88.21.119:443 | mc.yandex.ru | YANDEX LLC | RU | whitelisted |
2168 | chrome.exe | 194.226.130.226:80 | www.tns-counter.ru | JSC ADFACT | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clients2.google.com |
| whitelisted |
keerdev.myjino.ru |
| malicious |
accounts.google.com |
| shared |
parking-static.jino.ru |
| suspicious |
clients2.googleusercontent.com |
| whitelisted |
cache.betweendigital.com |
| whitelisted |
mc.yandex.ru |
| whitelisted |
jino.ru |
| malicious |
pixel.yabidos.com |
| suspicious |
www.tns-counter.ru |
| whitelisted |