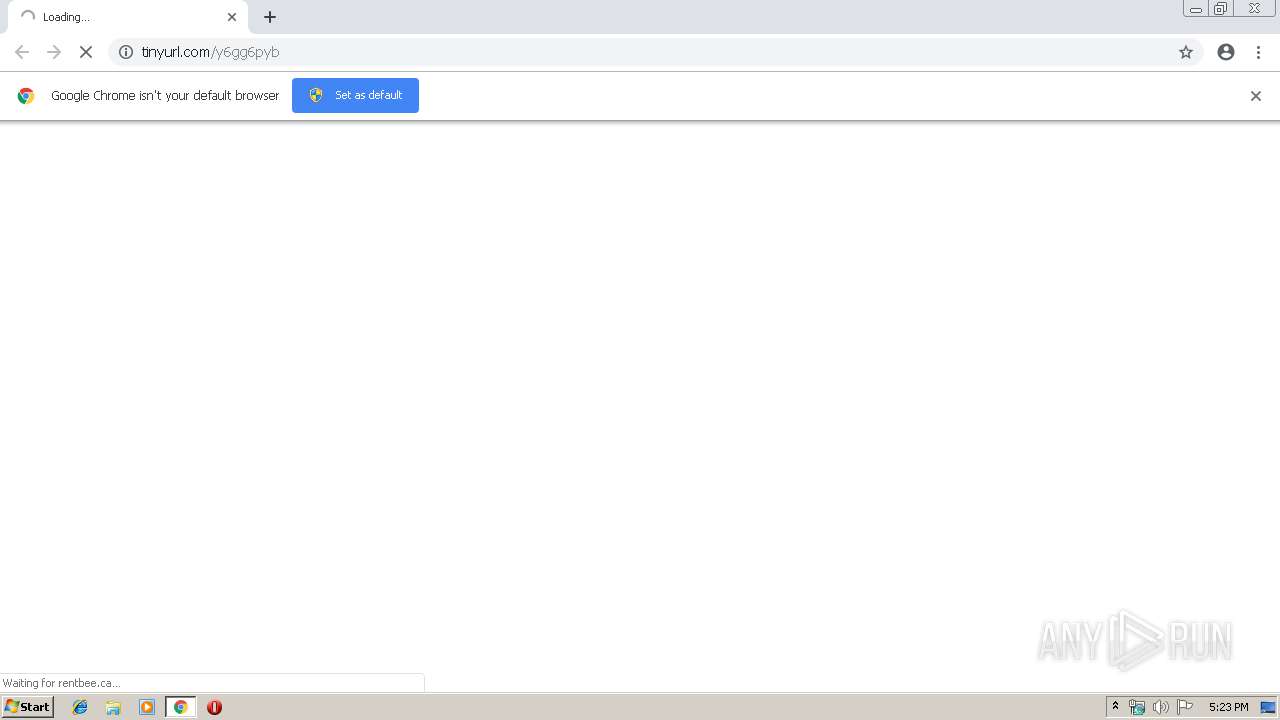
| URL: | http://tinyurl.com/y6gg6pyb |
| Full analysis: | https://app.any.run/tasks/905fcbdc-9a33-47b1-8384-cf15ee6164c5 |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 17:23:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D8B586BA19DD944670AF81E0C9E8FAD4 |
| SHA1: | C36CB2C95F2A1D3D9B4CED8C86F0A2043A9F726D |
| SHA256: | D679F256D812435CFF1FD4B6B41F4B318A8B306C51976203577A4FD31A40B25E |
| SSDEEP: | 3:N1KKMzLdIHOA2:CKwdsOZ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1620)
INFO
Application launched itself
- chrome.exe (PID: 1620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
51
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15109782762715602913 --mojo-platform-channel-handle=3508 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --service-pipe-token=14996147638628409404 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14996147638628409404 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2104 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1004 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17914700575382615116 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17914700575382615116 --renderer-client-id=17 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3436 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://tinyurl.com/y6gg6pyb | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --service-pipe-token=11134657182131731638 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11134657182131731638 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2080 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=584 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=4450442875104892800 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4450442875104892800 --renderer-client-id=18 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3320 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3935606887949571416 --mojo-platform-channel-handle=3412 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=1630841773506158231 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1630841773506158231 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3692 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,12179717286889362226,17125760168722129364,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11333307599425585115 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11333307599425585115 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3104 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
578
Read events
476
Write events
97
Delete events
5
Modification events
| (PID) Process: | (1620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2032) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1620-13197662619515625 |
Value: 259 | |||
| (PID) Process: | (1620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (1620) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
74
Text files
140
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fd83e5f2-e0aa-4b24-86f4-512d39398dd1.tmp | — | |
MD5:— | SHA256:— | |||
| 1620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
95
DNS requests
59
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
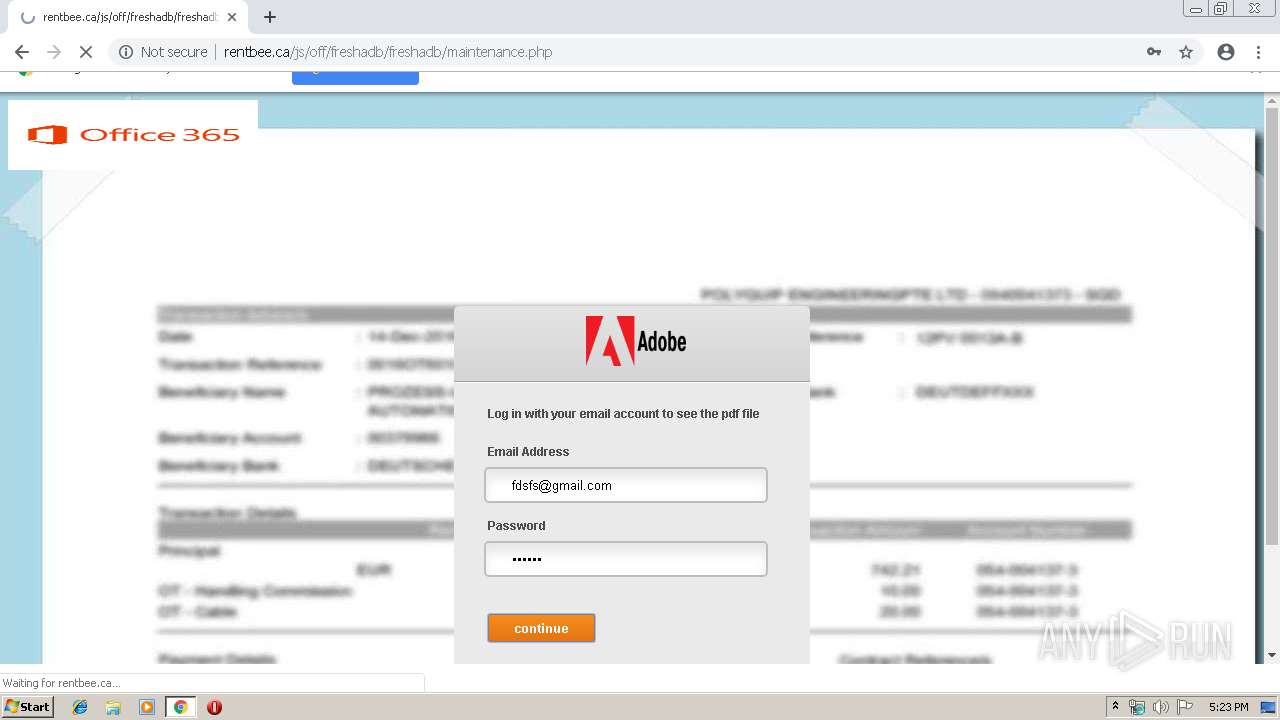
3900 | chrome.exe | GET | 301 | 104.20.218.42:80 | http://tinyurl.com/y6gg6pyb | US | — | — | shared |
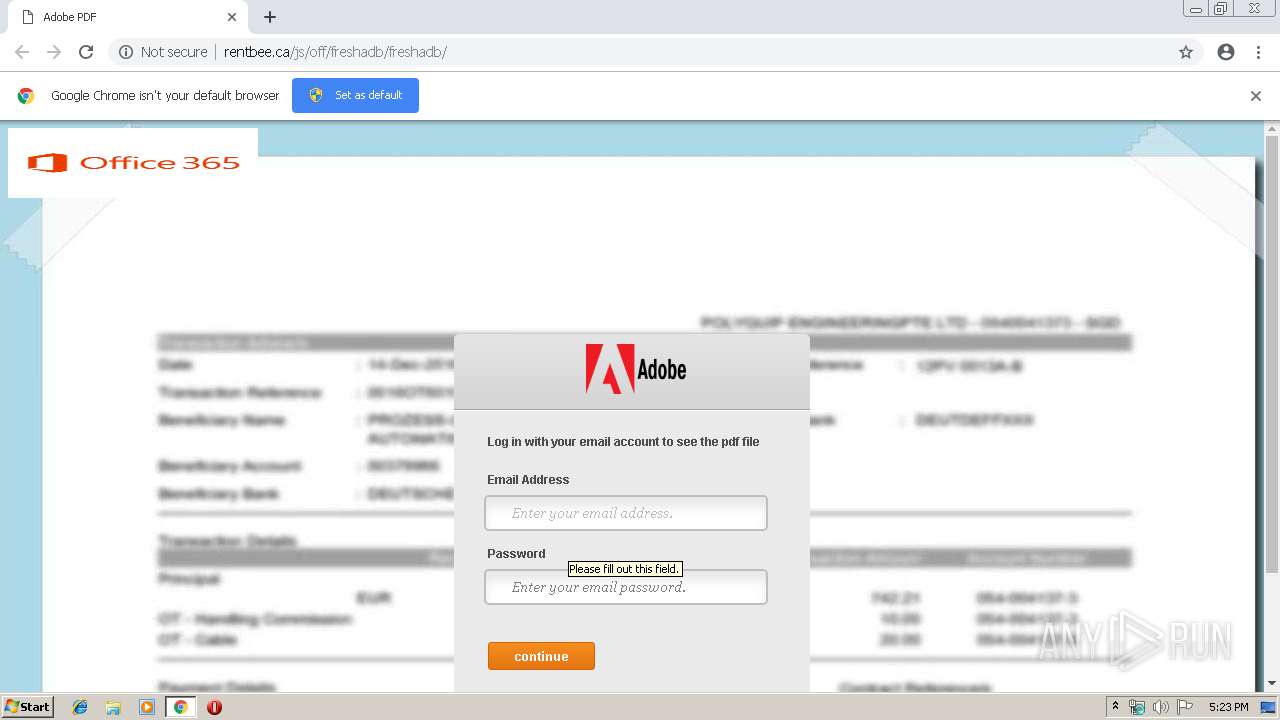
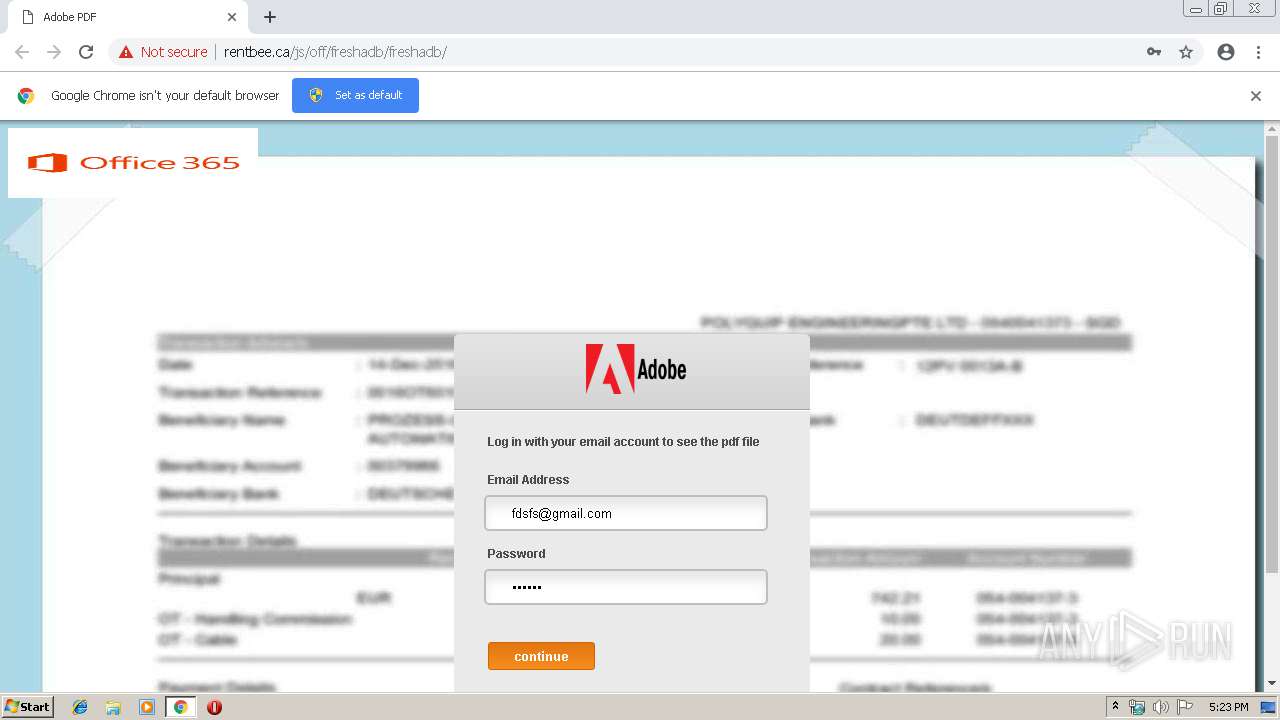
3900 | chrome.exe | GET | 200 | 198.46.86.117:80 | http://rentbee.ca/js/off/freshadb/freshadb/ | US | html | 23.3 Kb | suspicious |
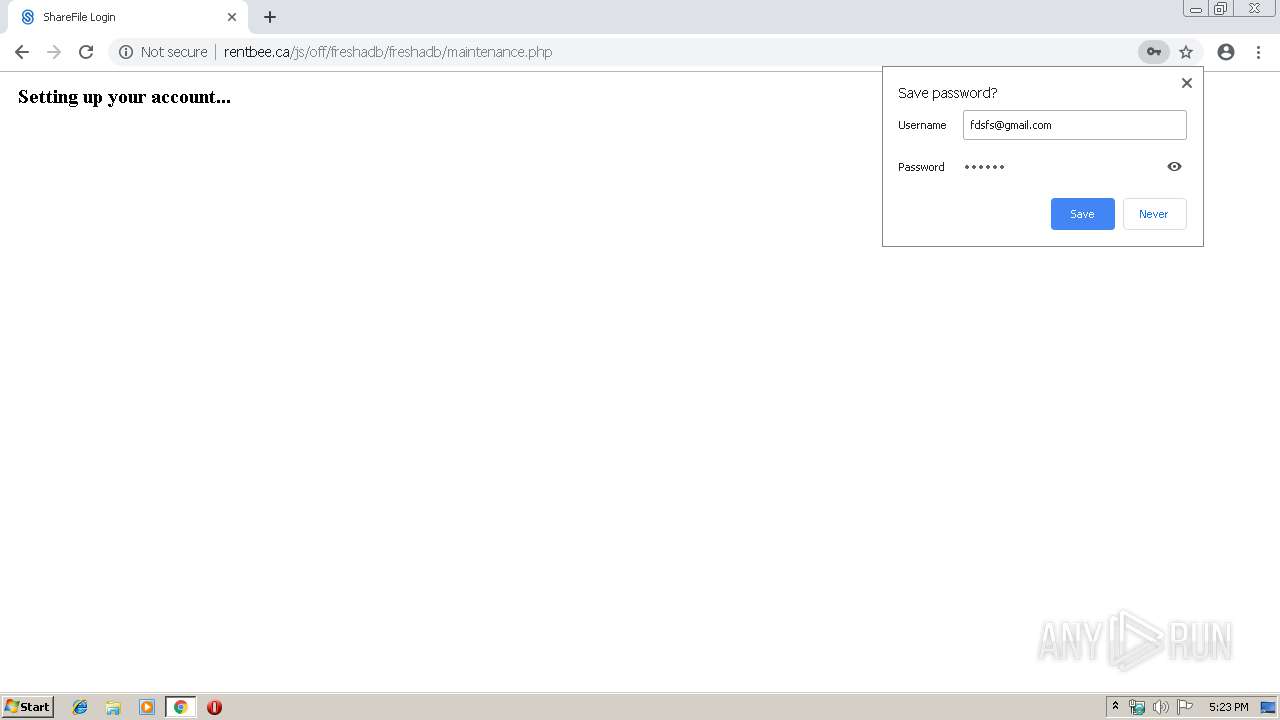
3900 | chrome.exe | POST | 200 | 198.46.86.117:80 | http://rentbee.ca/js/off/freshadb/freshadb/maintenance.php | US | html | 1.13 Kb | suspicious |
3900 | chrome.exe | GET | 404 | 198.46.86.117:80 | http://rentbee.ca/cPanel_magic_revision_1352765682/unprotected/cpanel/images/notice-error.png | US | html | 236 b | suspicious |
3900 | chrome.exe | GET | 404 | 198.46.86.117:80 | http://rentbee.ca/cPanel_magic_revision_1335428098/unprotected/cpanel/images/icon-username.png | US | html | 236 b | suspicious |
3900 | chrome.exe | GET | 404 | 198.46.86.117:80 | http://rentbee.ca/cPanel_magic_revision_1352765682/unprotected/cpanel/images/notice-info.png | US | html | 236 b | suspicious |
3900 | chrome.exe | GET | 404 | 198.46.86.117:80 | http://rentbee.ca/cPanel_magic_revision_1352765682/unprotected/cpanel/images/notice-success.png | US | html | 236 b | suspicious |
3900 | chrome.exe | GET | 404 | 198.46.86.117:80 | http://rentbee.ca/cPanel_magic_revision_1352765682/unprotected/cpanel/images/warning.png | US | html | 236 b | suspicious |
3900 | chrome.exe | GET | 404 | 198.46.86.117:80 | http://rentbee.ca/js/off/freshadb/freshadb/index_files/onecitrix.css | US | html | 236 b | suspicious |
3900 | chrome.exe | GET | 200 | 13.32.222.120:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3900 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 104.20.218.42:80 | tinyurl.com | Cloudflare Inc | US | shared |
3900 | chrome.exe | 198.46.86.117:80 | rentbee.ca | InMotion Hosting, Inc. | US | suspicious |
3900 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 151.101.120.193:443 | i.imgur.com | Fastly | US | malicious |
3900 | chrome.exe | 172.217.22.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 52.22.72.157:443 | secure.sharefile.com | Amazon.com, Inc. | US | unknown |
3900 | chrome.exe | 23.34.185.248:443 | www.adobe.com | Akamai Technologies, Inc. | NL | whitelisted |
3900 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3900 | chrome.exe | 172.217.16.174:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
tinyurl.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
rentbee.ca |
| suspicious |
i.imgur.com |
| malicious |
clients1.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r5---sn-5goeen7r.gvt1.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3900 | chrome.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Possible Adobe PDF Phishing Landing - Title over non SSL |
1 ETPRO signatures available at the full report