| File name: | setup-win32-bundle.exe |
| Full analysis: | https://app.any.run/tasks/2afa6bce-8303-41ef-b093-b3be5e6e7210 |
| Verdict: | Malicious activity |
| Analysis date: | May 13, 2024, 10:21:34 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A47B9A738A7391837D36E84DC5ED2078 |
| SHA1: | D2D229263CA34085D51C10258725FA982999E611 |
| SHA256: | D67709AF6DEC9A253DB284635D6A54371E496C0DE16CF48C45425E0F35FCB1E0 |
| SSDEEP: | 24576:qLN9pggkHLWqnivnuhHqaEVYS/HDowwrBcEc:qLN9SgkHLWqnivnuhHqvVYSvDowwrBc3 |
MALICIOUS
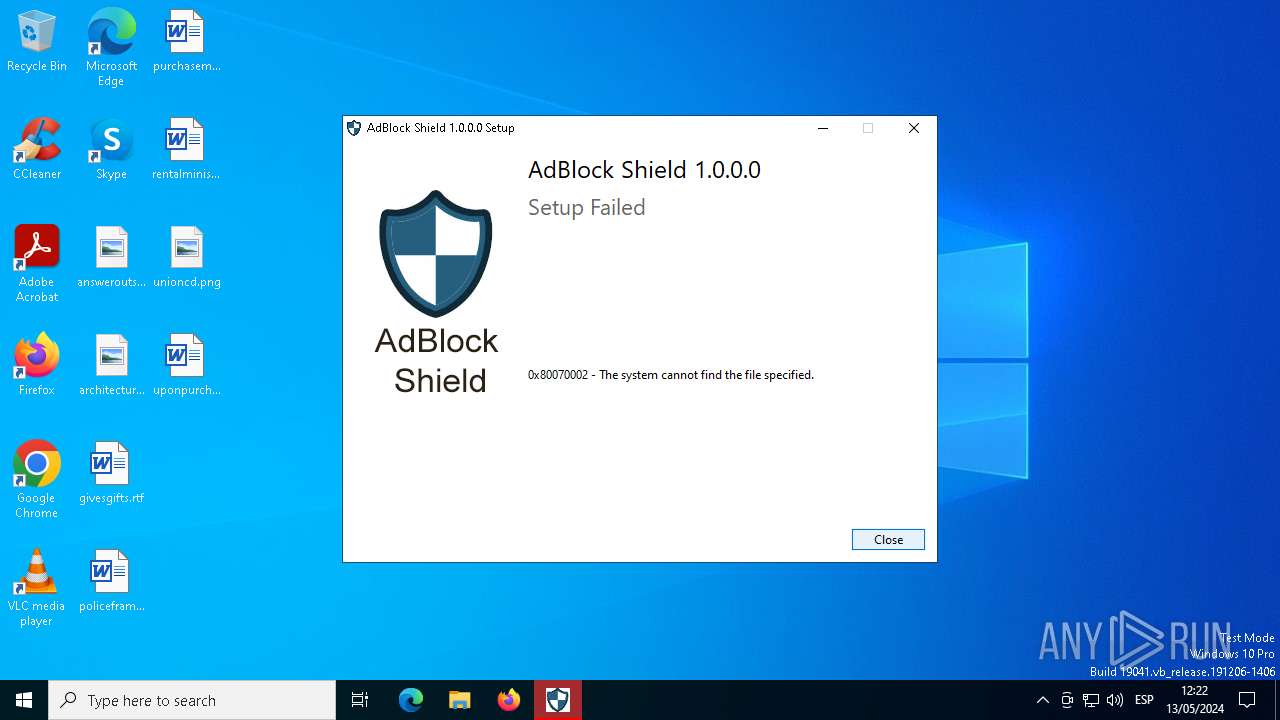
Drops the executable file immediately after the start
- setup-win32-bundle.exe (PID: 6980)
- setup-win32-bundle.exe (PID: 7004)
Changes the autorun value in the registry
- setup-win32-bundle.exe (PID: 7004)
SUSPICIOUS
Starts itself from another location
- setup-win32-bundle.exe (PID: 6980)
Executable content was dropped or overwritten
- setup-win32-bundle.exe (PID: 6980)
- setup-win32-bundle.exe (PID: 7004)
Searches for installed software
- setup-win32-bundle.exe (PID: 7004)
Creates a software uninstall entry
- setup-win32-bundle.exe (PID: 7004)
Checks Windows Trust Settings
- setup-win32-bundle.exe (PID: 7004)
Reads security settings of Internet Explorer
- setup-win32-bundle.exe (PID: 7004)
INFO
Checks supported languages
- setup-win32-bundle.exe (PID: 6980)
- setup-win32-bundle.exe (PID: 7004)
Create files in a temporary directory
- setup-win32-bundle.exe (PID: 6980)
- setup-win32-bundle.exe (PID: 7004)
Reads the computer name
- setup-win32-bundle.exe (PID: 7004)
Checks proxy server information
- setup-win32-bundle.exe (PID: 7004)
Creates files or folders in the user directory
- setup-win32-bundle.exe (PID: 7004)
Reads the machine GUID from the registry
- setup-win32-bundle.exe (PID: 7004)
Reads the software policy settings
- setup-win32-bundle.exe (PID: 7004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:09:17 05:33:38+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit, Removable run from swap, Net run from swap |
| PEType: | PE32 |
| LinkerVersion: | 14.16 |
| CodeSize: | 299008 |
| InitializedDataSize: | 228352 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2df71 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | ivanovsasha224 |
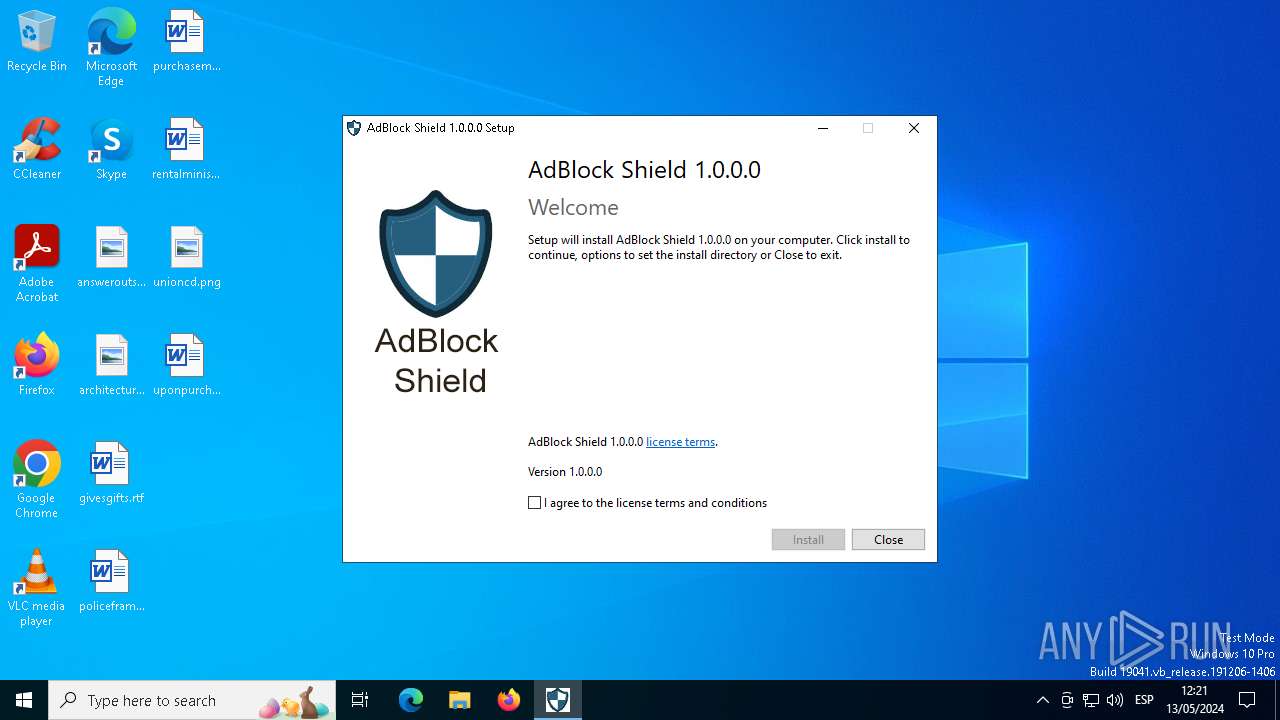
| FileDescription: | AdBlock Shield 1.0.0.0 |
| FileVersion: | 1.0.0.0 |
| InternalName: | setup |
| LegalCopyright: | 2023 (c) ivanovsasha224 |
| OriginalFileName: | setup-win32-bundle.exe |
| ProductName: | AdBlock Shield 1.0.0.0 |
| ProductVersion: | 1.0.0.0 |
Total processes
125
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6752 | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe -Embedding | C:\Users\admin\AppData\Local\Microsoft\OneDrive\19.043.0304.0013\FileCoAuth.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft OneDriveFile Co-Authoring Executable Exit code: 0 Version: 19.043.0304.0013 Modules
| |||||||||||||||
| 6980 | "C:\Users\admin\AppData\Local\Temp\setup-win32-bundle.exe" | C:\Users\admin\AppData\Local\Temp\setup-win32-bundle.exe | explorer.exe | ||||||||||||
User: admin Company: ivanovsasha224 Integrity Level: MEDIUM Description: AdBlock Shield 1.0.0.0 Exit code: 2 Version: 1.0.0.0 Modules
| |||||||||||||||
| 7004 | "C:\Users\admin\AppData\Local\Temp\{E97D013A-6F3B-4BD0-B78E-418DBF585828}\.cr\setup-win32-bundle.exe" -burn.clean.room="C:\Users\admin\AppData\Local\Temp\setup-win32-bundle.exe" -burn.filehandle.attached=736 -burn.filehandle.self=732 | C:\Users\admin\AppData\Local\Temp\{E97D013A-6F3B-4BD0-B78E-418DBF585828}\.cr\setup-win32-bundle.exe | setup-win32-bundle.exe | ||||||||||||
User: admin Company: ivanovsasha224 Integrity Level: MEDIUM Description: AdBlock Shield 1.0.0.0 Exit code: 2 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
1 379
Read events
1 334
Write events
38
Delete events
7
Modification events
| (PID) Process: | (7004) setup-win32-bundle.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{f003d497-0bea-4e89-a61c-2a0e6cbb33ab} |
| Operation: | write | Name: | BundleCachePath |
Value: C:\Users\admin\AppData\Local\Package Cache\{f003d497-0bea-4e89-a61c-2a0e6cbb33ab}\setup-win32-bundle.exe | |||
| (PID) Process: | (7004) setup-win32-bundle.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{f003d497-0bea-4e89-a61c-2a0e6cbb33ab} |
| Operation: | write | Name: | BundleUpgradeCode |
Value: {E14F3FF7-FB63-42A4-9033-C433A21DE8CE} | |||
| (PID) Process: | (7004) setup-win32-bundle.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{f003d497-0bea-4e89-a61c-2a0e6cbb33ab} |
| Operation: | write | Name: | BundleAddonCode |
Value: | |||
| (PID) Process: | (7004) setup-win32-bundle.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{f003d497-0bea-4e89-a61c-2a0e6cbb33ab} |
| Operation: | write | Name: | BundleDetectCode |
Value: | |||
| (PID) Process: | (7004) setup-win32-bundle.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{f003d497-0bea-4e89-a61c-2a0e6cbb33ab} |
| Operation: | write | Name: | BundlePatchCode |
Value: | |||
| (PID) Process: | (7004) setup-win32-bundle.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{f003d497-0bea-4e89-a61c-2a0e6cbb33ab} |
| Operation: | write | Name: | BundleVersion |
Value: 1.0.0.0 | |||
| (PID) Process: | (7004) setup-win32-bundle.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{f003d497-0bea-4e89-a61c-2a0e6cbb33ab} |
| Operation: | write | Name: | VersionMajor |
Value: 1 | |||
| (PID) Process: | (7004) setup-win32-bundle.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{f003d497-0bea-4e89-a61c-2a0e6cbb33ab} |
| Operation: | write | Name: | VersionMinor |
Value: 0 | |||
| (PID) Process: | (7004) setup-win32-bundle.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{f003d497-0bea-4e89-a61c-2a0e6cbb33ab} |
| Operation: | write | Name: | BundleProviderKey |
Value: {f003d497-0bea-4e89-a61c-2a0e6cbb33ab} | |||
| (PID) Process: | (7004) setup-win32-bundle.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{f003d497-0bea-4e89-a61c-2a0e6cbb33ab} |
| Operation: | write | Name: | BundleTag |
Value: | |||
Executable files
4
Suspicious files
7
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7004 | setup-win32-bundle.exe | C:\Users\admin\AppData\Local\Temp\{E57707CB-1D4C-4932-87C5-A6C267156173}\.ba\thm.wxl | xml | |
MD5:FC0DB4142556D3F38B0744A12F5F9D3D | SHA256:8FBEB7F0B546D394D99B49D678D516402E8F54E5DEA590CC91733F502F288019 | |||
| 6980 | setup-win32-bundle.exe | C:\Users\admin\AppData\Local\Temp\{E97D013A-6F3B-4BD0-B78E-418DBF585828}\.cr\setup-win32-bundle.exe | executable | |
MD5:A47B9A738A7391837D36E84DC5ED2078 | SHA256:D67709AF6DEC9A253DB284635D6A54371E496C0DE16CF48C45425E0F35FCB1E0 | |||
| 7004 | setup-win32-bundle.exe | C:\Users\admin\AppData\Local\Temp\{E57707CB-1D4C-4932-87C5-A6C267156173}\.ba\thm.xml | xml | |
MD5:C782782276C9B777DE65154AB442BED5 | SHA256:C9278956FCD92C66D51D5DB42CEF5D2D85F8A8232E2BBC0670B0A1355F69E8EC | |||
| 7004 | setup-win32-bundle.exe | C:\Users\admin\AppData\Local\Temp\{E57707CB-1D4C-4932-87C5-A6C267156173}\.ba\wixstdba.dll | executable | |
MD5:FE7E0BD53F52E6630473C31299A49FDD | SHA256:2BEA14D70943A42D344E09B7C9DE5562FA7E109946E1C615DD584DA30D06CC80 | |||
| 7004 | setup-win32-bundle.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\CAF4703619713E3F18D8A9D5D88D6288_F2DAF19C1F776537105D08FC8D978464 | der | |
MD5:8202A1CD02E7D69597995CABBE881A12 | SHA256:58F381C3A0A0ACE6321DA22E40BD44A597BD98B9C9390AB9258426B5CF75A7A5 | |||
| 7004 | setup-win32-bundle.exe | C:\Users\admin\AppData\Local\Temp\{E57707CB-1D4C-4932-87C5-A6C267156173}\.be\setup-win32-bundle.exe | executable | |
MD5:A47B9A738A7391837D36E84DC5ED2078 | SHA256:D67709AF6DEC9A253DB284635D6A54371E496C0DE16CF48C45425E0F35FCB1E0 | |||
| 7004 | setup-win32-bundle.exe | C:\Users\admin\AppData\Local\Temp\{E57707CB-1D4C-4932-87C5-A6C267156173}\.ba\BootstrapperApplicationData.xml | xml | |
MD5:383EC114E8BBBAE05E5A5EB8EEA590C6 | SHA256:E0F89478595B09193C3580763D0ABA9F25419343CE94781FCD34B5F16B516440 | |||
| 7004 | setup-win32-bundle.exe | C:\Users\admin\AppData\Local\Package Cache\{f003d497-0bea-4e89-a61c-2a0e6cbb33ab}\setup-win32-bundle.exe | executable | |
MD5:A47B9A738A7391837D36E84DC5ED2078 | SHA256:D67709AF6DEC9A253DB284635D6A54371E496C0DE16CF48C45425E0F35FCB1E0 | |||
| 7004 | setup-win32-bundle.exe | C:\Users\admin\AppData\Local\Temp\{E57707CB-1D4C-4932-87C5-A6C267156173}\.ba\logo.png | image | |
MD5:DD4904CC8AE2C4B79A2AF5DAC0A90E59 | SHA256:C3E77A92B70435144BEE04F948A68A3AFA6120B2885810DE784C9A644A95E06F | |||
| 6752 | FileCoAuth.exe | C:\Users\admin\AppData\Local\Microsoft\OneDrive\logs\Common\FileCoAuth-2024-05-13.1023.6752.1.odl | binary | |
MD5:CC2499B70E54395B6361EA526562E89E | SHA256:D262FEB8D20D5CFA3FD847DAF866D0B3A5D97E33F5152E9A10A64D44860691D8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
50
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
7004 | setup-win32-bundle.exe | GET | 200 | 216.58.206.67:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | — | — | unknown |
7004 | setup-win32-bundle.exe | GET | 200 | 216.58.206.67:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFCjJ1PwkYAi7fE%3D | unknown | — | — | unknown |
2592 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | unknown |
4680 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAzlnDD9eoNTLi0BRrMy%2BWU%3D | unknown | — | — | unknown |
6360 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | unknown |
428 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | unknown |
2908 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | unknown |
428 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
4856 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5140 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7004 | setup-win32-bundle.exe | 188.114.96.3:443 | dl.fastcloudapp.com | CLOUDFLARENET | NL | unknown |
7004 | setup-win32-bundle.exe | 216.58.206.67:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
5140 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
2592 | svchost.exe | 40.126.32.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4680 | SearchApp.exe | 2.23.209.150:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dl.fastcloudapp.com |
| unknown |
ocsp.pki.goog |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
www.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |