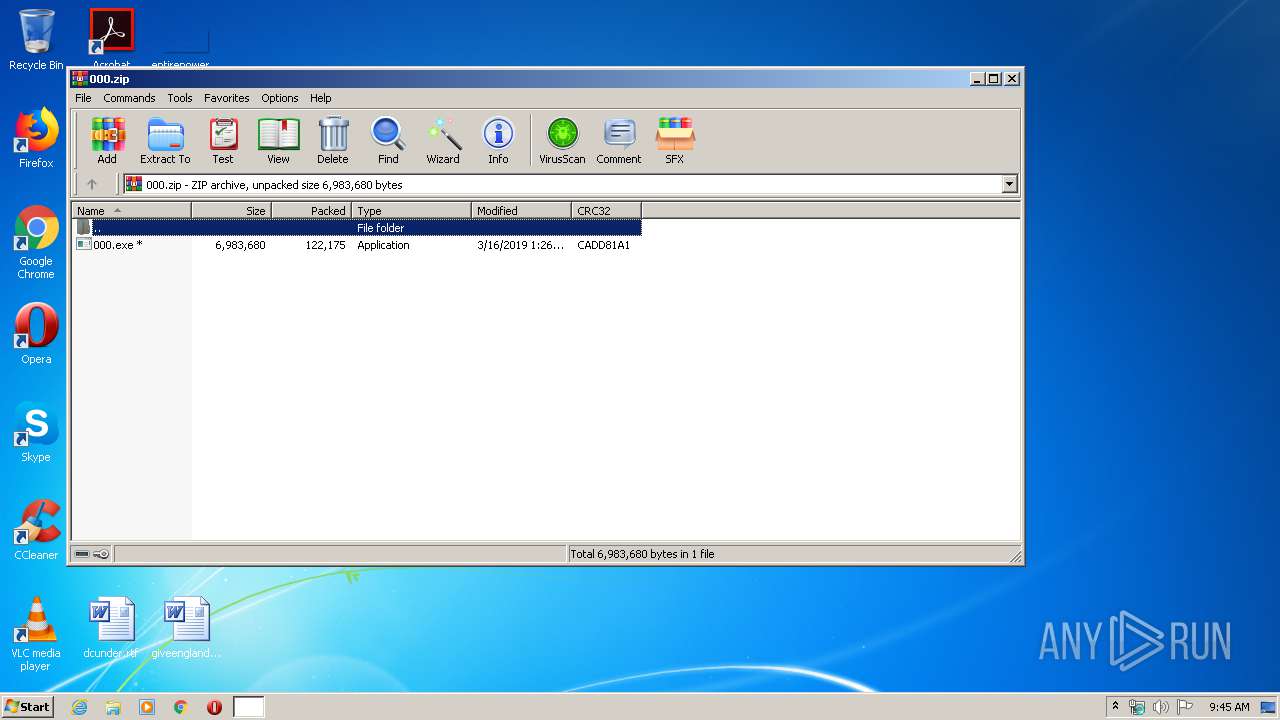
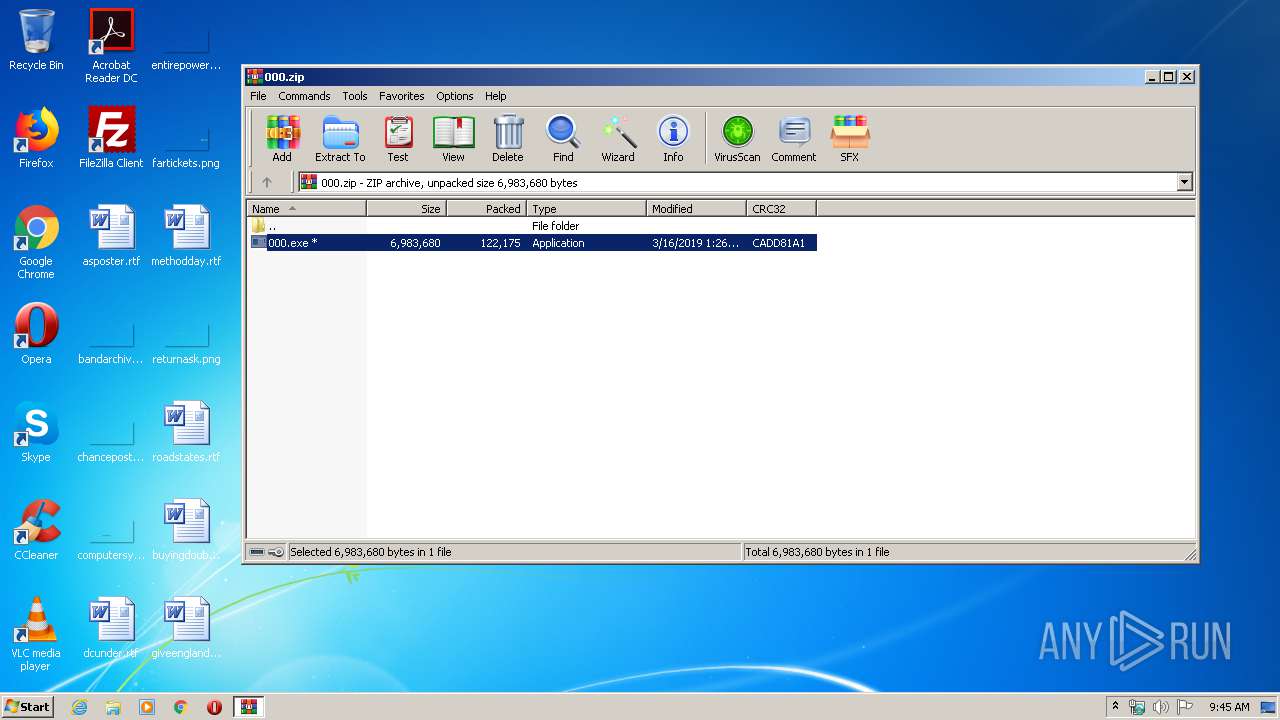
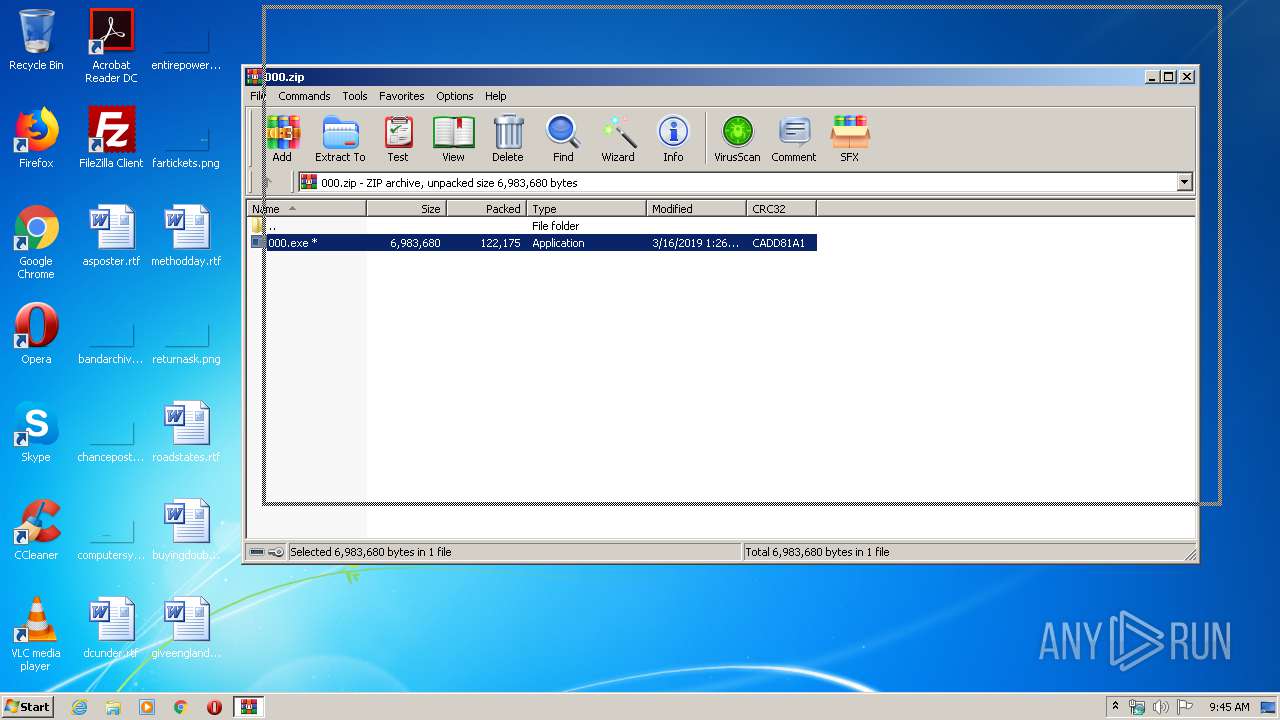
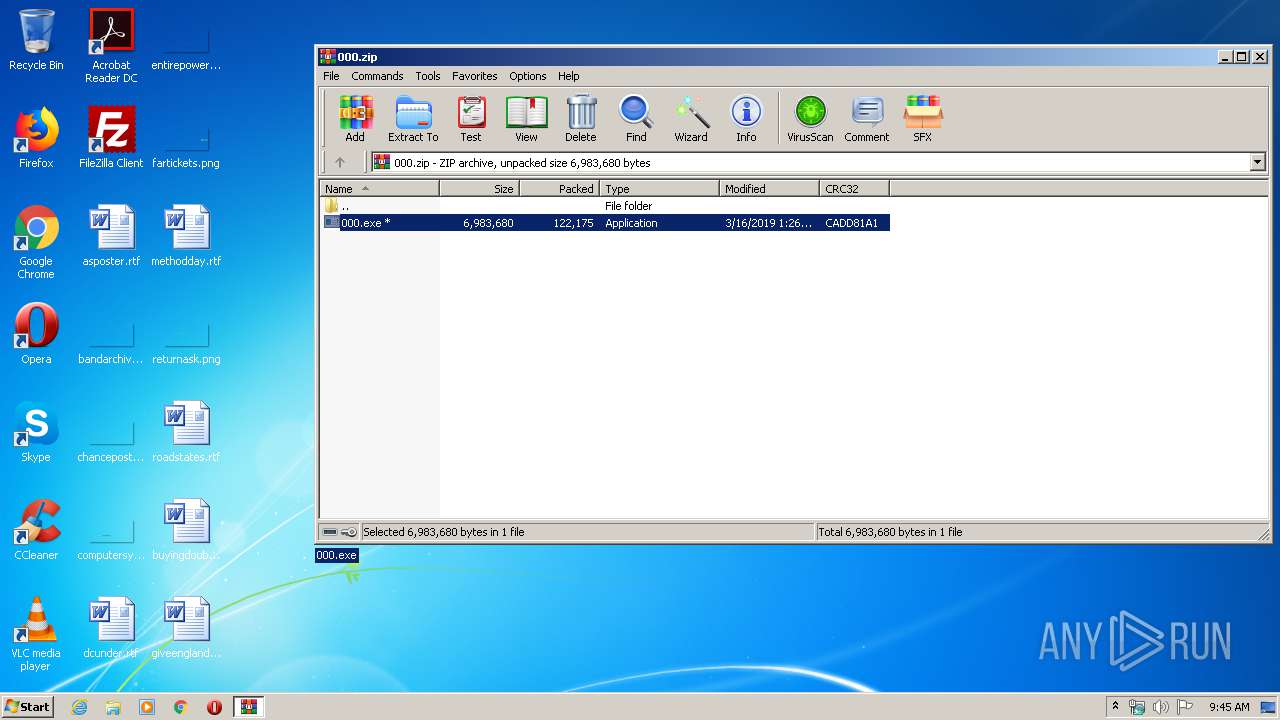
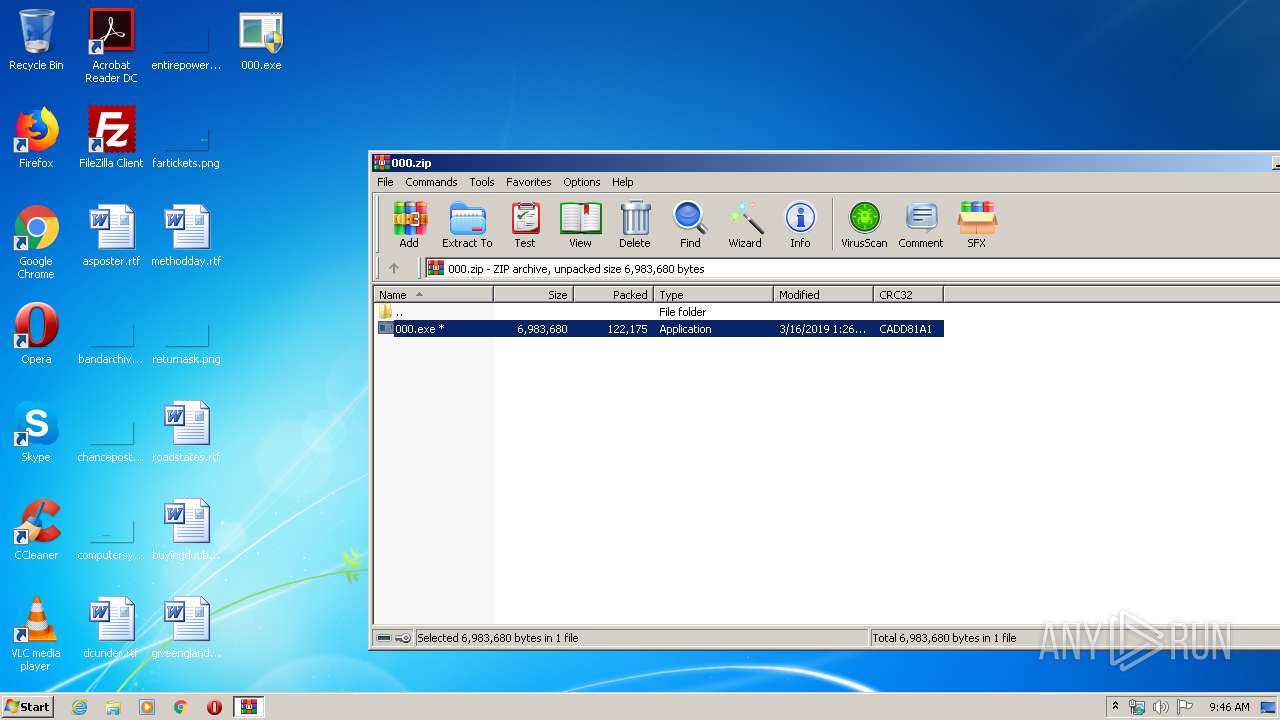
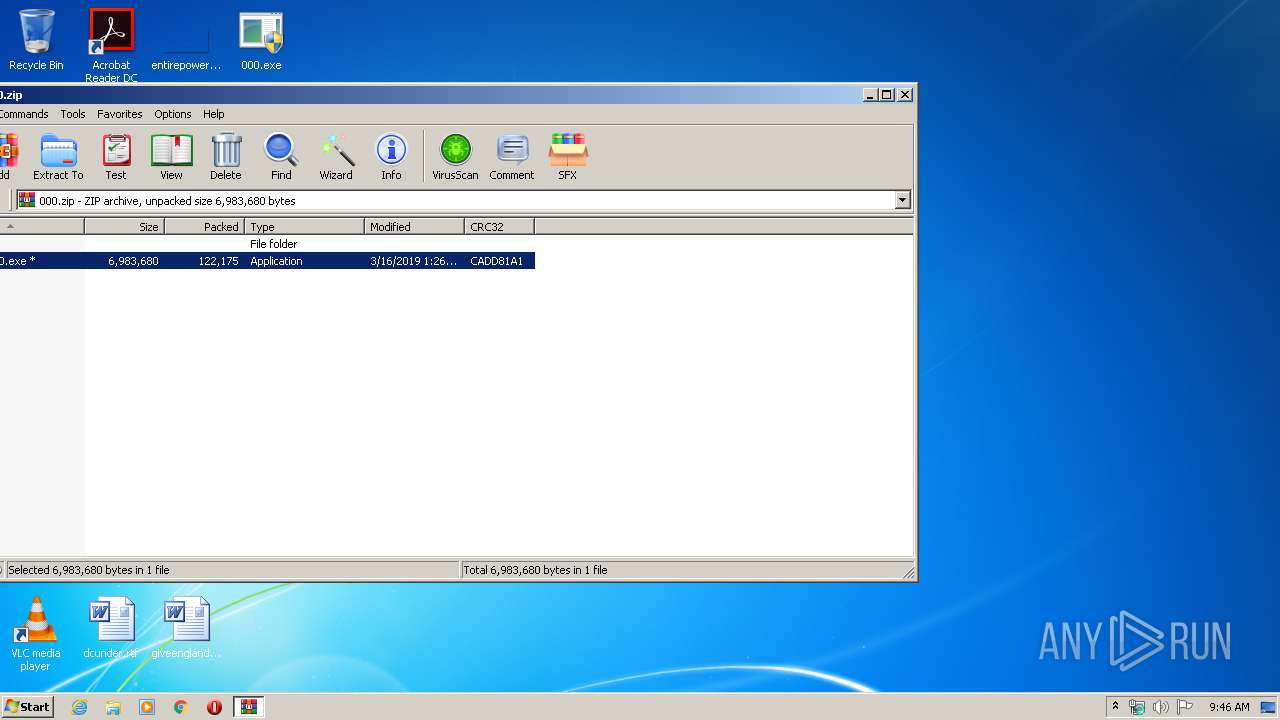
| File name: | 000.zip |
| Full analysis: | https://app.any.run/tasks/b7bc24d1-5079-421c-9886-136b50f0a664 |
| Verdict: | Malicious activity |
| Analysis date: | April 19, 2020, 08:45:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | F5D73448DBE1EC4F9A8EC187F216D9E5 |
| SHA1: | 6F76561BD09833C75AE8F0035DCB2BC87709E2E5 |
| SHA256: | D66C4C08833F9E8AF486AF44F879A0A5FB3113110874CC04BD53EE6351C92064 |
| SSDEEP: | 3072:/msQvkoawLvldUo1OvAGczlPDloVCUfcU:C8oaiPOvA/zl7jUcU |
MALICIOUS
Application was dropped or rewritten from another process
- 000.exe (PID: 660)
- 000.exe (PID: 3420)
Task Manager has been disabled (taskmgr)
- 000.exe (PID: 3420)
Changes the login/logoff helper path in the registry
- 000.exe (PID: 3420)
Writes to a start menu file
- cmd.exe (PID: 1692)
SUSPICIOUS
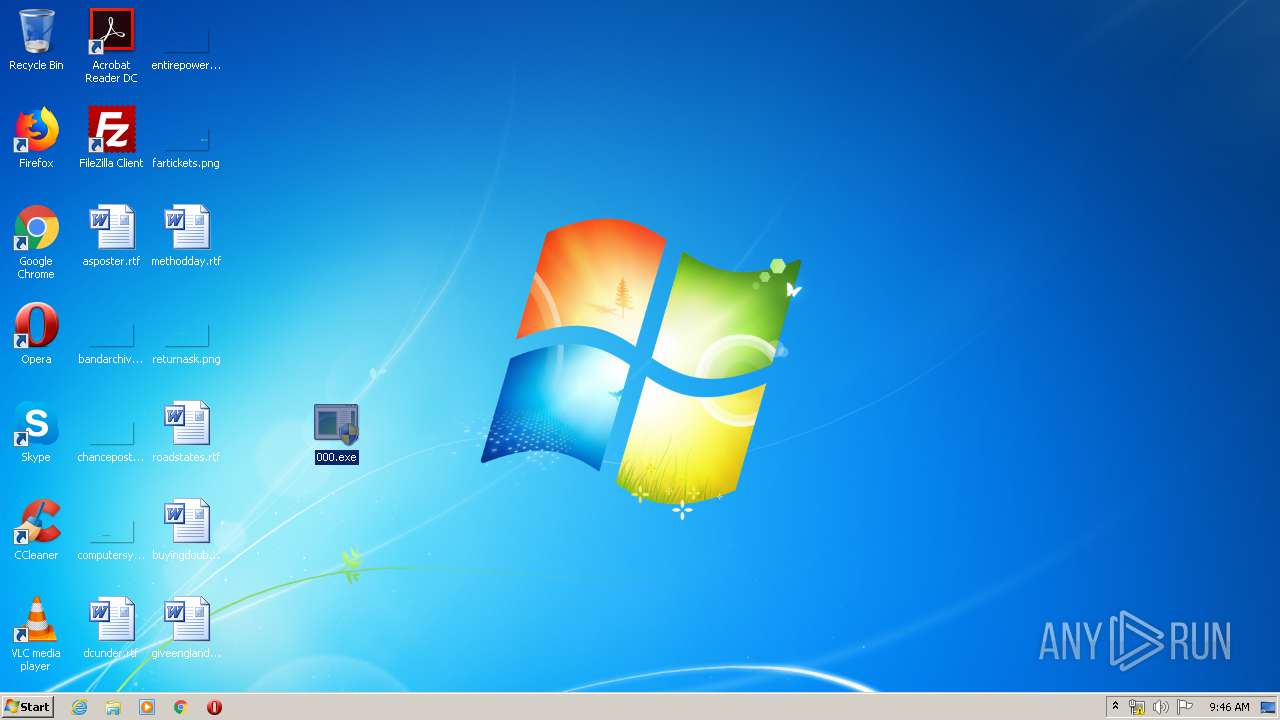
Changes the desktop background image
- 000.exe (PID: 3420)
Executable content was dropped or overwritten
- 000.exe (PID: 3420)
- cmd.exe (PID: 1692)
Starts CMD.EXE for commands execution
- 000.exe (PID: 3420)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 1692)
Reads Internet Cache Settings
- 000.exe (PID: 3420)
Creates files in the program directory
- cmd.exe (PID: 1692)
INFO
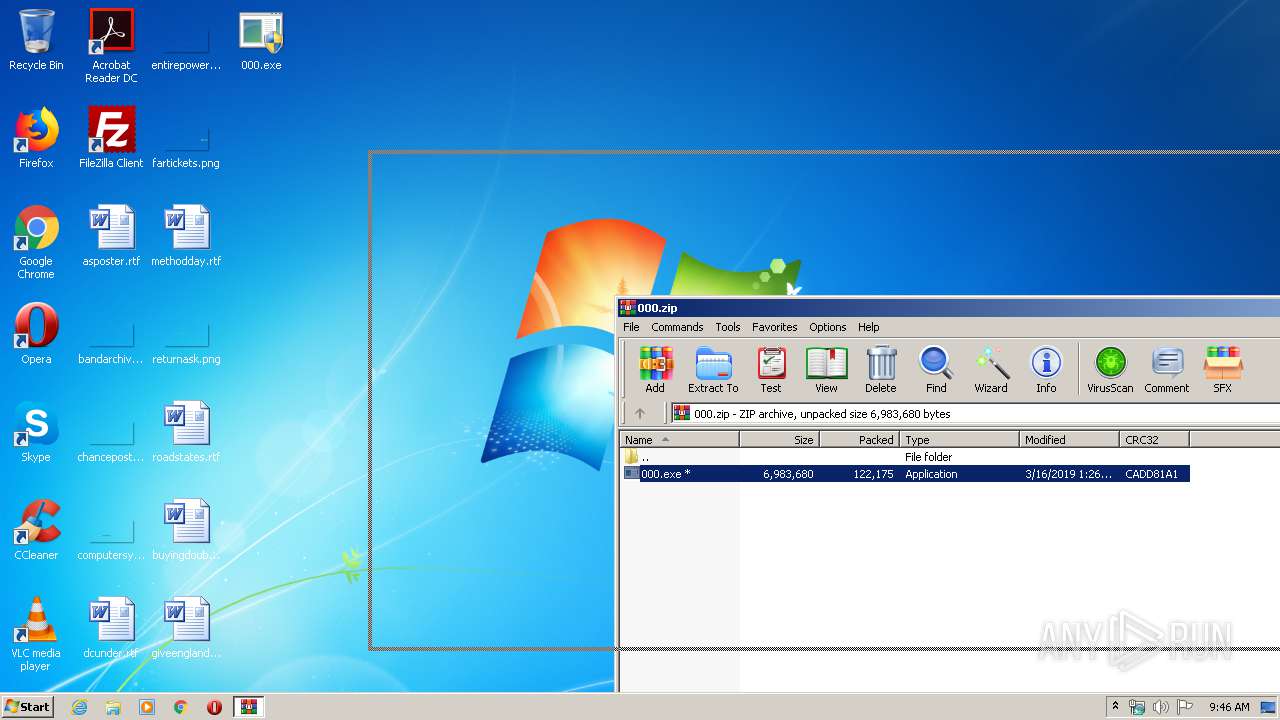
Manual execution by user
- 000.exe (PID: 660)
- 000.exe (PID: 3420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:03:16 14:26:16 |
| ZipCRC: | 0xcadd81a1 |
| ZipCompressedSize: | 122175 |
| ZipUncompressedSize: | 6983680 |
| ZipFileName: | 000.exe |
Total processes
50
Monitored processes
9
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Users\admin\Desktop\000.exe" | C:\Users\admin\Desktop\000.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: 000 Exit code: 3221226540 Version: 0.0.0.0 Modules
| |||||||||||||||
| 1344 | wmic useraccount where name='admin' rename 'UR NEXT' | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1692 | cmd /c ""C:\Users\admin\AppData\Local\Temp\windl.bat"" | C:\Windows\system32\cmd.exe | 000.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2280 | taskkill /f /im explorer.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2320 | taskkill /f /im taskmgr.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2656 | wmic useraccount where name='admin' set FullName='UR NEXT' | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2716 | shutdown /f /r /t 0 | C:\Windows\system32\shutdown.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Shutdown and Annotation Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3420 | "C:\Users\admin\Desktop\000.exe" | C:\Users\admin\Desktop\000.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: 000 Exit code: 0 Version: 0.0.0.0 Modules
| |||||||||||||||
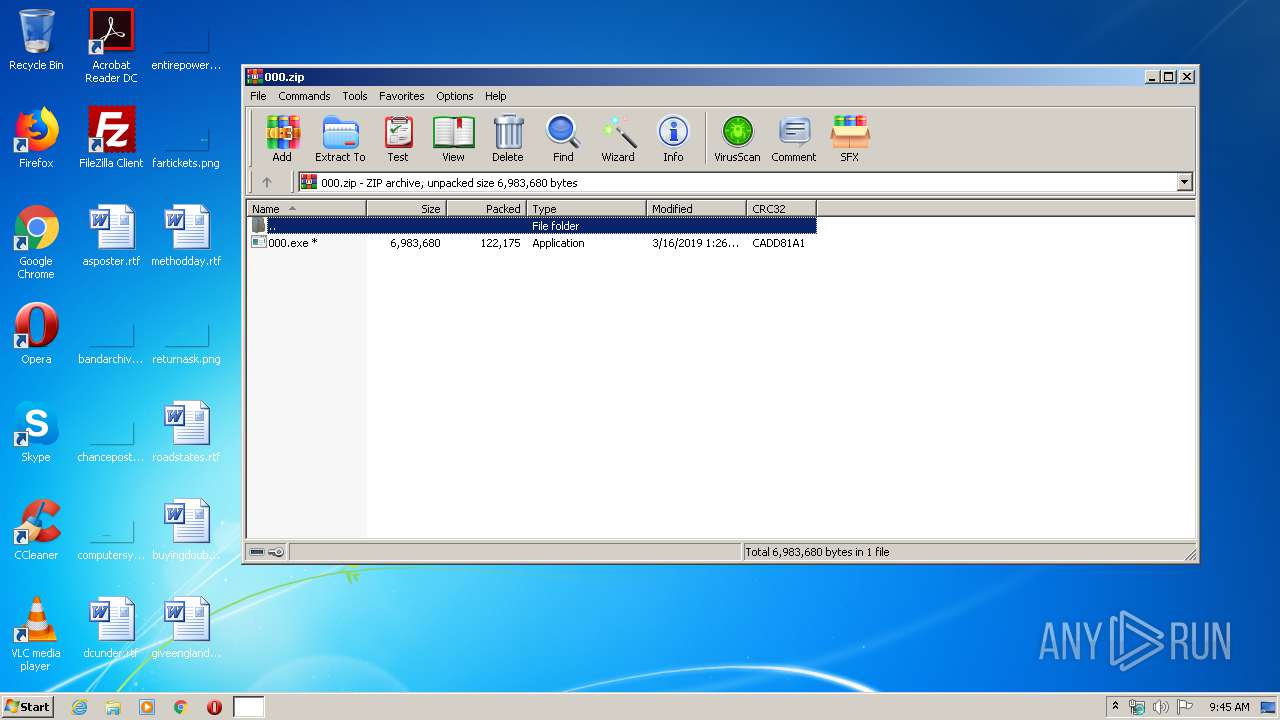
| 4092 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\000.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
895
Read events
845
Write events
50
Delete events
0
Modification events
| (PID) Process: | (4092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4092) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\000.zip | |||
| (PID) Process: | (4092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
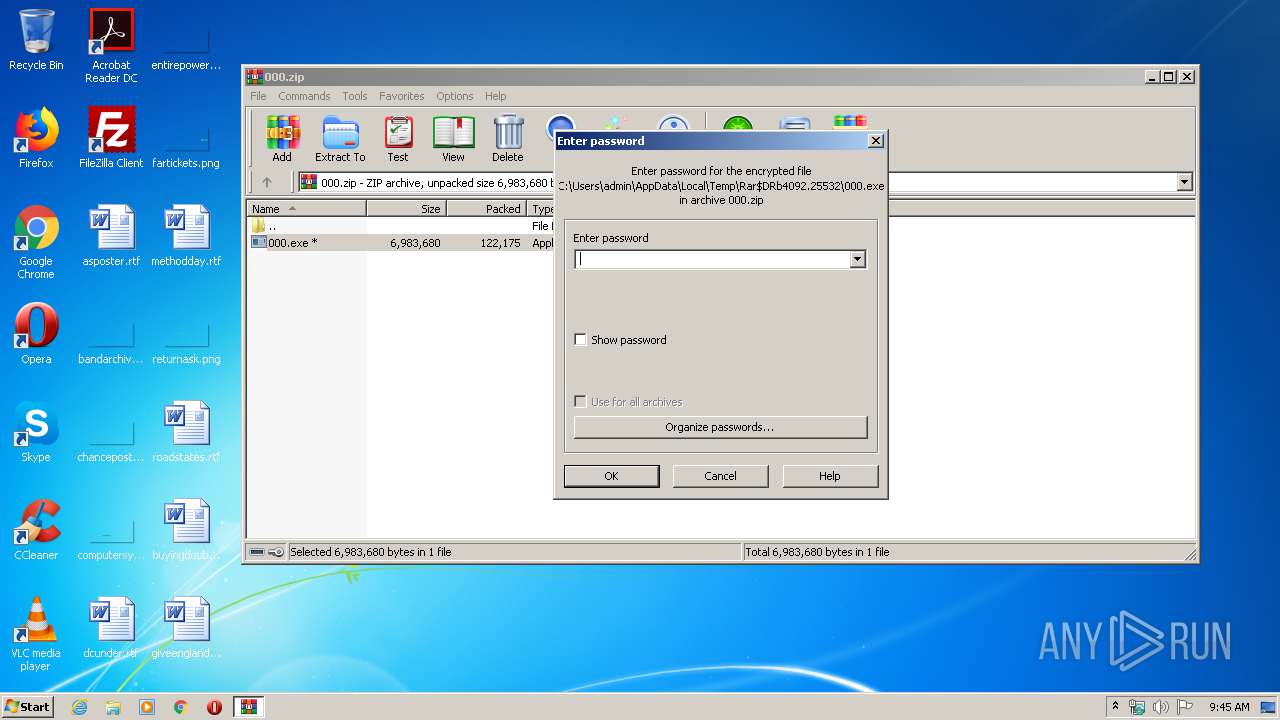
| (PID) Process: | (4092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (4092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFD7FFFFFF520000009703000047020000 | |||
Executable files
2
Suspicious files
0
Text files
405
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4092 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb4092.25532\000.exe | — | |
MD5:— | SHA256:— | |||
| 3420 | 000.exe | C:\Users\admin\AppData\Local\Temp\text.txt | text | |
MD5:9037EBF0A18A1C17537832BC73739109 | SHA256:38C889B5D7BDCB79BBCB55554C520A9CE74B5BFC29C19D1E4CB1419176C99F48 | |||
| 1692 | cmd.exe | C:\Users\admin\Desktop\UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR N1XT.txt | text | |
MD5:9037EBF0A18A1C17537832BC73739109 | SHA256:38C889B5D7BDCB79BBCB55554C520A9CE74B5BFC29C19D1E4CB1419176C99F48 | |||
| 3420 | 000.exe | C:\Users\admin\AppData\Local\Temp\icon.ico | image | |
MD5:A4B9662CF3B6EA6626F6081C0D8C13F3 | SHA256:84A1C2713642090523F05D9FB015C537FD210D3200CADAF442BB67CF1834B356 | |||
| 3420 | 000.exe | C:\Users\admin\AppData\Local\Temp\windl.bat | text | |
MD5:A9401E260D9856D1134692759D636E92 | SHA256:B551FBA71DFD526D4916AE277D8686D83FFF36D22FCF6F18457924A070B30EF7 | |||
| 3420 | 000.exe | C:\Users\admin\AppData\Local\Temp\one.rtf | text | |
MD5:6FBD6CE25307749D6E0A66EBBC0264E7 | SHA256:E152B106733D9263D3CF175F0B6197880D70ACB753F8BDE8035A3E4865B31690 | |||
| 1692 | cmd.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Startup\rniw.exe | executable | |
MD5:9232120B6FF11D48A90069B25AA30ABC | SHA256:70FAA0E1498461731F873D3594F20CBF2BEAA6F123A06B66F9DF59A9CDF862BE | |||
| 1692 | cmd.exe | C:\Users\admin\Desktop\UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR N0XT.txt | text | |
MD5:9037EBF0A18A1C17537832BC73739109 | SHA256:38C889B5D7BDCB79BBCB55554C520A9CE74B5BFC29C19D1E4CB1419176C99F48 | |||
| 1692 | cmd.exe | C:\Users\admin\Desktop\UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR N3XT.txt | text | |
MD5:9037EBF0A18A1C17537832BC73739109 | SHA256:38C889B5D7BDCB79BBCB55554C520A9CE74B5BFC29C19D1E4CB1419176C99F48 | |||
| 1692 | cmd.exe | C:\Users\admin\Desktop\UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR NEXT UR N4XT.txt | text | |
MD5:9037EBF0A18A1C17537832BC73739109 | SHA256:38C889B5D7BDCB79BBCB55554C520A9CE74B5BFC29C19D1E4CB1419176C99F48 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report