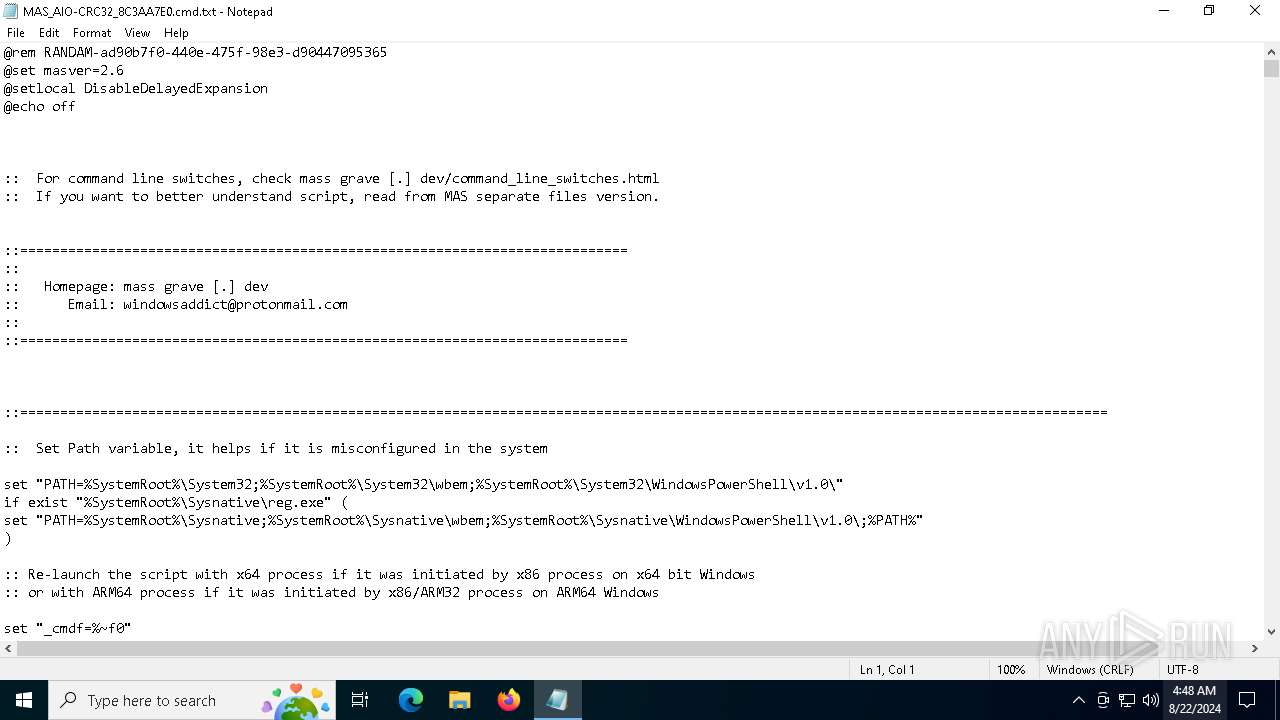
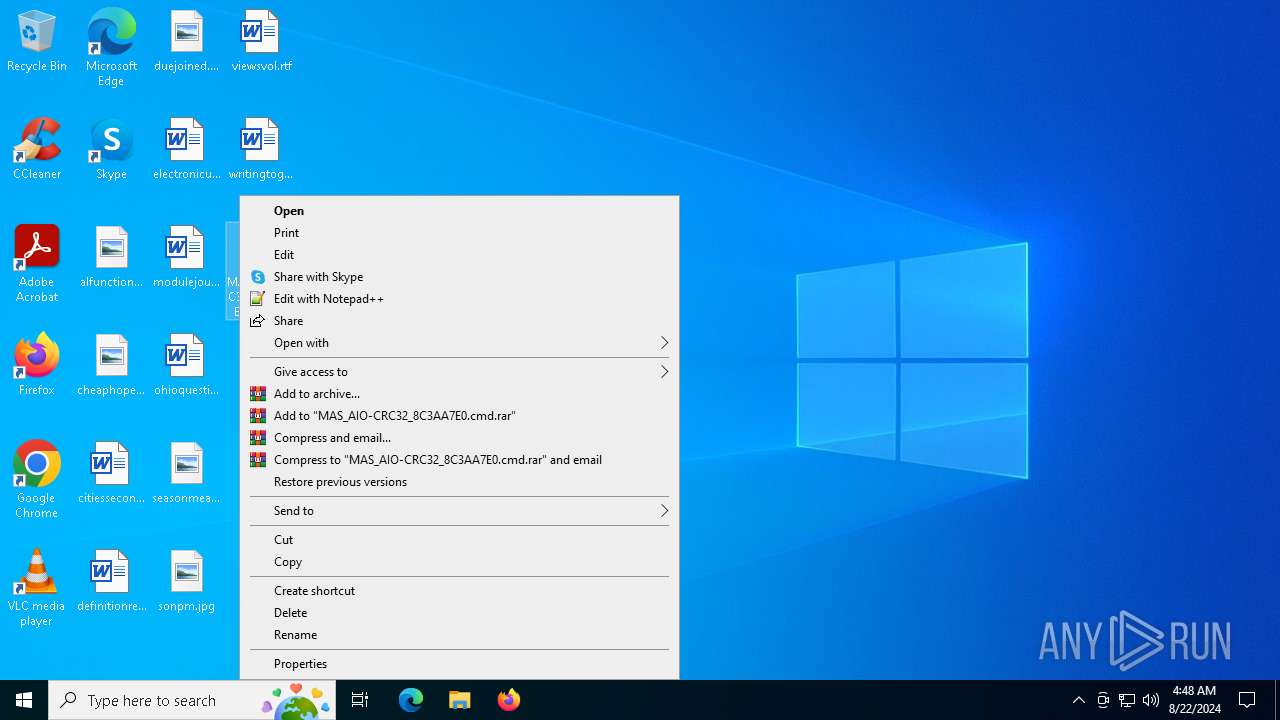
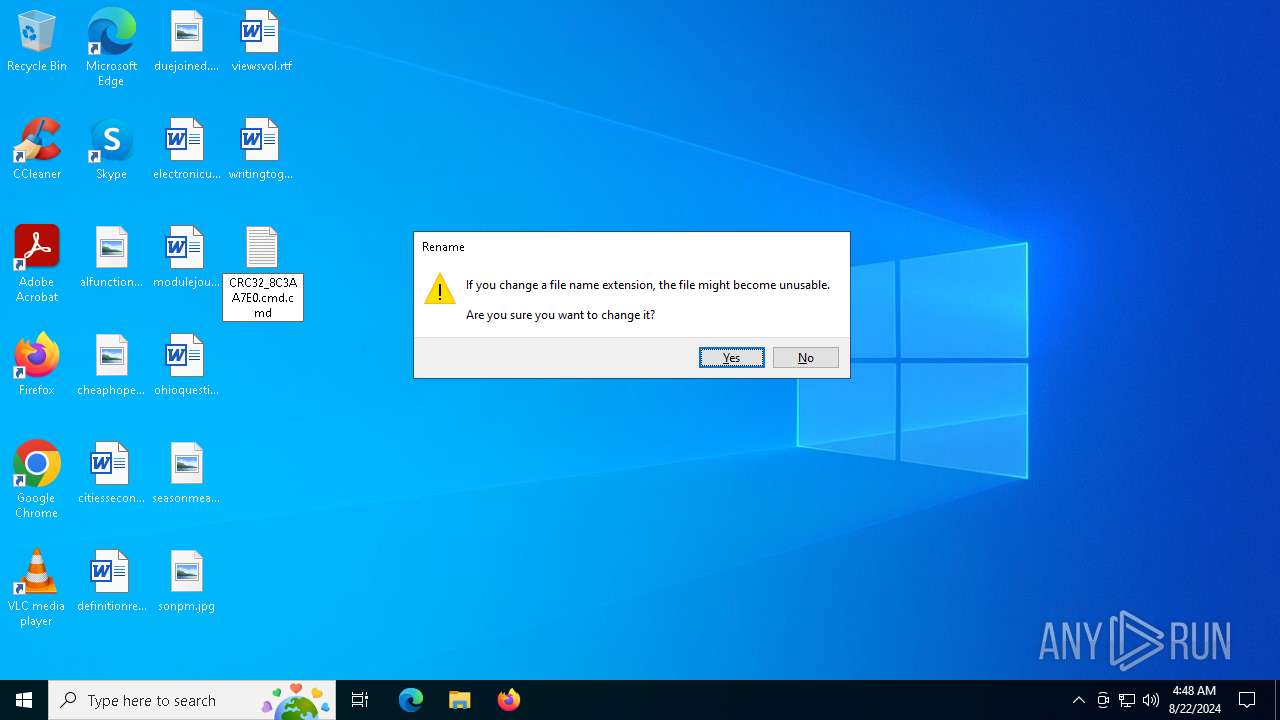
| File name: | MAS_AIO-CRC32_8C3AA7E0.cmd |
| Full analysis: | https://app.any.run/tasks/cc738ffa-cea2-4ef6-8a9a-19556c3b6489 |
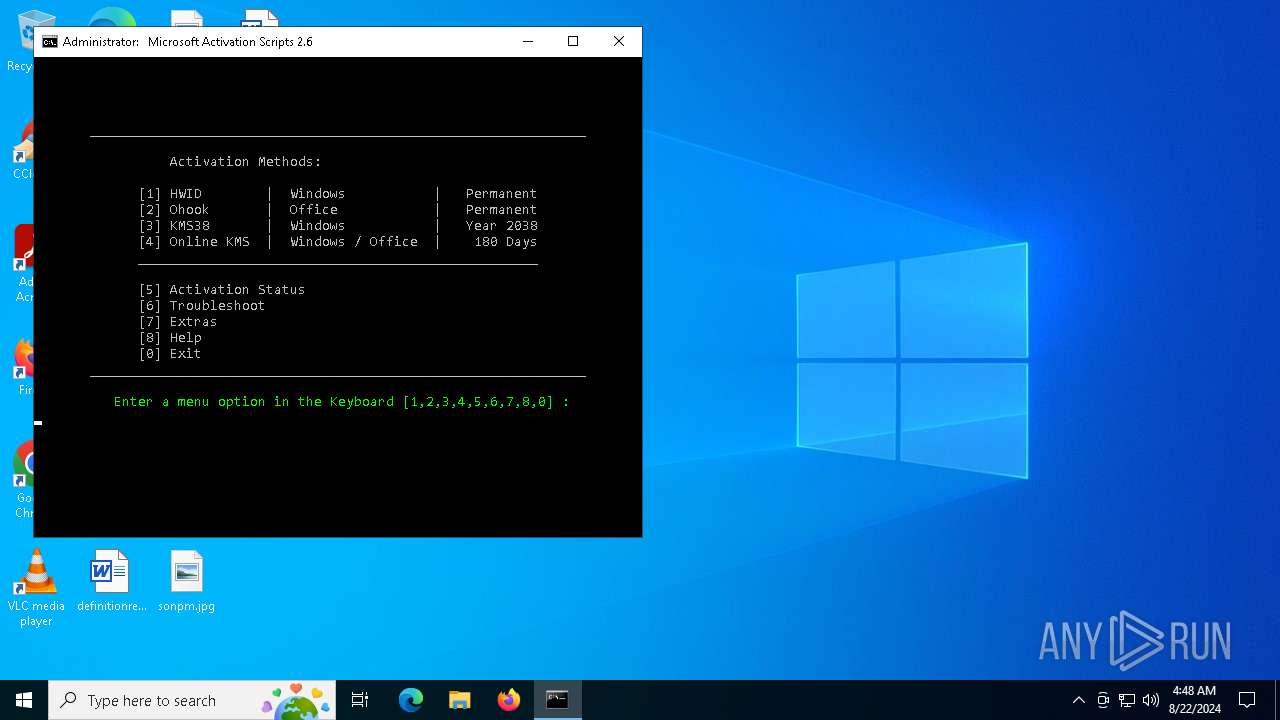
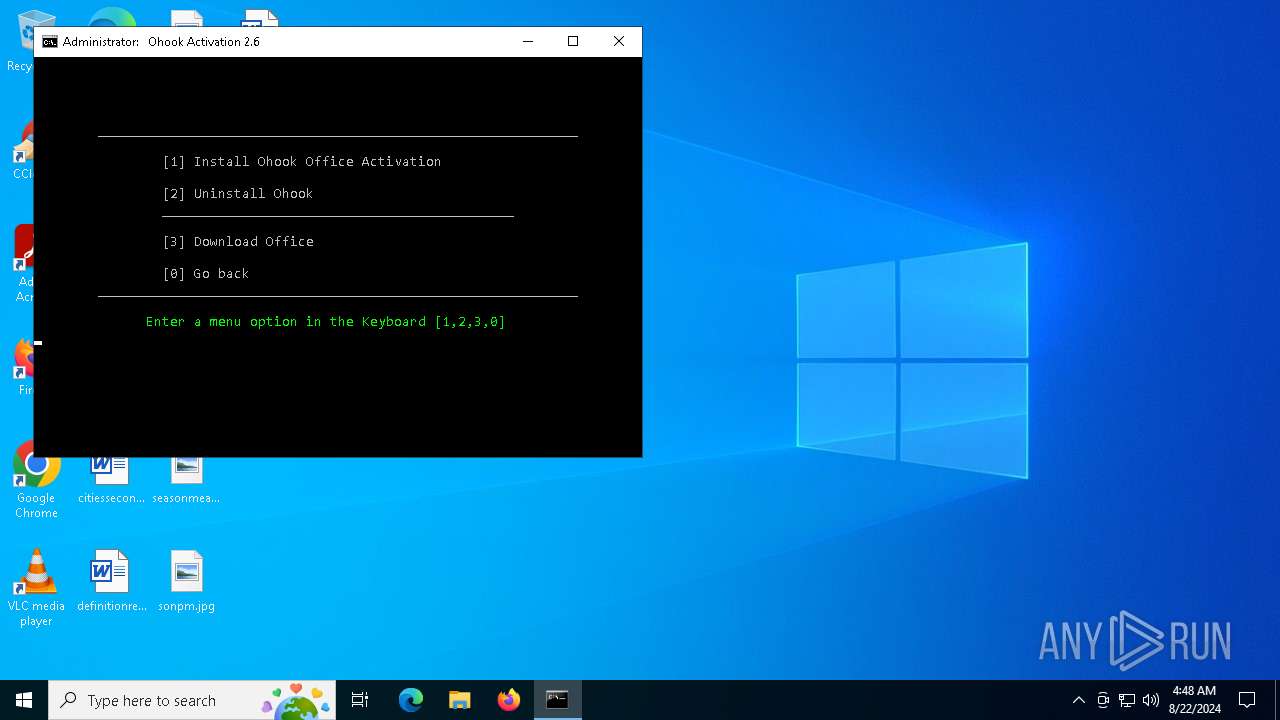
| Verdict: | Malicious activity |
| Analysis date: | August 22, 2024, 04:48:19 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with very long lines (311), with CRLF line terminators |
| MD5: | 92CC8F1F67A875563D1299E7DD7B5723 |
| SHA1: | BEE4ADFE87603F91067B9F868F7F42B34B2FBDEB |
| SHA256: | D666A4C7810B9D3FE9749F2D4E15C5A65D4AC0D7F0B14A144D6631CE61CC5DF3 |
| SSDEEP: | 3072:O/dR3S9mF2TJRMP0u+RciNiYFRd8nVFR3mP5sLtV7bJuAMTVFp6zGDNSCE2K0xOn:UAnHu+R7VLo97bJu9p6zGDNS0KgOuCV |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts SC.EXE for service management
- cmd.exe (PID: 6468)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 2728)
Application launched itself
- cmd.exe (PID: 6468)
- cmd.exe (PID: 6376)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 6204)
- cmd.exe (PID: 2728)
- cmd.exe (PID: 7068)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 5152)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6468)
- powershell.exe (PID: 6824)
- cmd.exe (PID: 6376)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 7068)
- cmd.exe (PID: 6204)
- cmd.exe (PID: 2728)
- cmd.exe (PID: 6252)
- cmd.exe (PID: 5152)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6468)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 2728)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 6468)
- cmd.exe (PID: 2728)
- cmd.exe (PID: 4820)
Executing commands from ".cmd" file
- cmd.exe (PID: 6468)
- powershell.exe (PID: 6824)
- cmd.exe (PID: 2728)
- cmd.exe (PID: 5400)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 5400)
- cmd.exe (PID: 2728)
Hides command output
- cmd.exe (PID: 6180)
- cmd.exe (PID: 6468)
- cmd.exe (PID: 6700)
- cmd.exe (PID: 4604)
- cmd.exe (PID: 6512)
- cmd.exe (PID: 6268)
- cmd.exe (PID: 3992)
- cmd.exe (PID: 6884)
- cmd.exe (PID: 6472)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 2728)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 2728)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 6704)
- WMIC.exe (PID: 6336)
- WMIC.exe (PID: 1668)
Manual execution by a user
- cmd.exe (PID: 6468)
Checks operating system version
- cmd.exe (PID: 6468)
- cmd.exe (PID: 5400)
- cmd.exe (PID: 2728)
Checks supported languages
- mode.com (PID: 6328)
- mode.com (PID: 6988)
- mode.com (PID: 7076)
- mode.com (PID: 6276)
- mode.com (PID: 7088)
Reads Microsoft Office registry keys
- reg.exe (PID: 7112)
- reg.exe (PID: 5920)
- reg.exe (PID: 6624)
- reg.exe (PID: 6216)
- reg.exe (PID: 6424)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .bib/bibtex/txt | | | BibTeX references (100) |
|---|
Total processes
252
Monitored processes
119
Malicious processes
4
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 252 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 252 | C:\WINDOWS\system32\cmd.exe /c ver | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 448 | find /i "0x0" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 888 | powershell.exe $AssemblyBuilder = [AppDomain]::CurrentDomain.DefineDynamicAssembly(4, 1); $ModuleBuilder = $AssemblyBuilder.DefineDynamicModule(2, $False); $TypeBuilder = $ModuleBuilder.DefineType(0); $meth = $TypeBuilder.DefinePInvokeMethod('BrandingFormatString', 'winbrand.dll', 'Public, Static', 1, [String], @([String]), 1, 3); $meth.SetImplementationFlags(128); $TypeBuilder.CreateType()::BrandingFormatString('%WINDOWS_LONG%') | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | find "127.69.2.6" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 936 | reg query HKLM\SOFTWARE\Microsoft\Office\15.0\Common\InstallRoot /v Path | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1116 | C:\WINDOWS\system32\cmd.exe /c ping -4 -n 1 updatecheck.massgrave.dev | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1280 | sc start sppsvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1056 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1432 | ping -4 -n 1 updatecheck.massgrave.dev | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1668 | wmic path SoftwareLicensingProduct where (LicenseStatus='1' and GracePeriodRemaining='0' and PartialProductKey is not NULL) get Name /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
17 931
Read events
17 921
Write events
10
Delete events
0
Modification events
| (PID) Process: | (6824) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6824) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6824) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6824) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6428) reg.exe | Key: | HKEY_CURRENT_USER\Console |
| Operation: | write | Name: | QuickEdit |
Value: 0 | |||
| (PID) Process: | (6876) reg.exe | Key: | HKEY_CURRENT_USER\Console |
| Operation: | write | Name: | QuickEdit |
Value: 1 | |||
Executable files
0
Suspicious files
1
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6824 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_fiut51no.p51.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6824 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:9BA8F0C3F57BDF7A5A55C30657F9732A | SHA256:14B6346015C35604980187EA8C53357018D39788B01F216B1F561F6CF9076560 | |||
| 6884 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_sse51hdm.0zc.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6884 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1nyezrsu.uuk.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 888 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_dsqec2ta.kqe.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6824 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zwrrzzja.2ha.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 888 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_ianposm1.iw1.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
28
DNS requests
16
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6936 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
6380 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
420 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3412 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3304 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3412 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3260 | svchost.exe | 40.113.110.67:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
420 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
420 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
2120 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6936 | backgroundTaskHost.exe | 20.199.58.43:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
updatecheck.massgrave.dev |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |