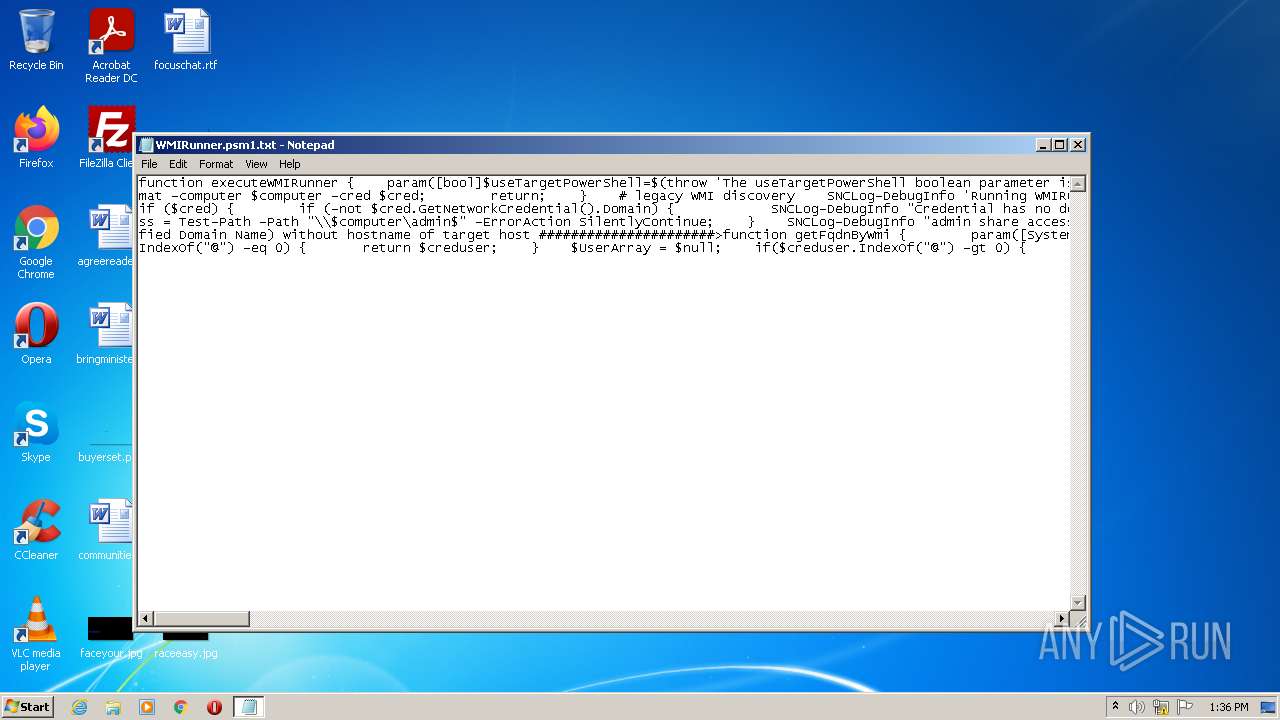
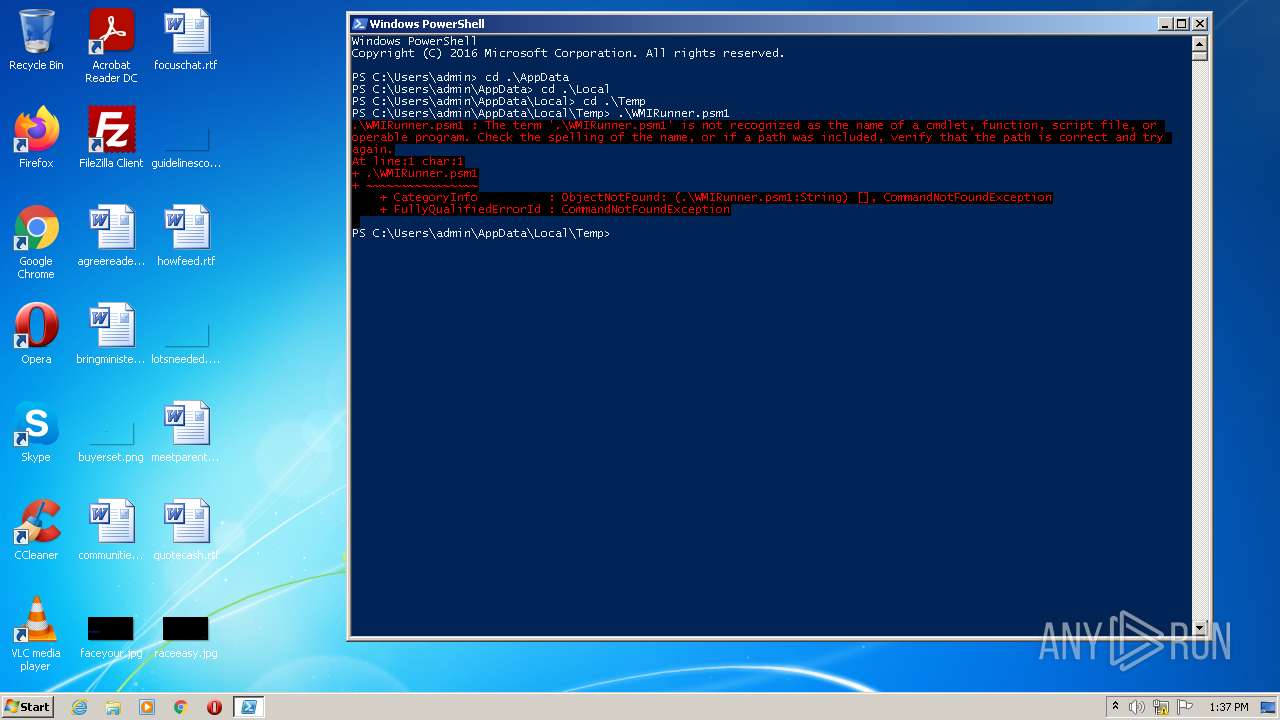
| File name: | WMIRunner.psm1 |
| Full analysis: | https://app.any.run/tasks/7f6f7aef-de46-49c1-8bc9-33775f8b72e6 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 12:36:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | text/plain |
| File info: | UTF-8 Unicode (with BOM) text |
| MD5: | B60A1AE801B188FAA9F75CCF4170FAE7 |
| SHA1: | 53911C5919D694017F6A714F67CD019F5036DD91 |
| SHA256: | D65330B4FD1181EC01FBCC7261CF4E663E153E3D57FCD9E6ABA2A138B7CA3CA3 |
| SSDEEP: | 96:BHKKfUb3ralcek90EKKSzIcNjLNyrLPh/tN+S6miYbLjHYnYYnG8r0RFzHTdx:BHBcb3ralaTBSzZ1ByrtVN+S6m5bnHYm |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- powershell.exe (PID: 1868)
Reads the date of Windows installation
- powershell.exe (PID: 1868)
Reads the computer name
- powershell.exe (PID: 1868)
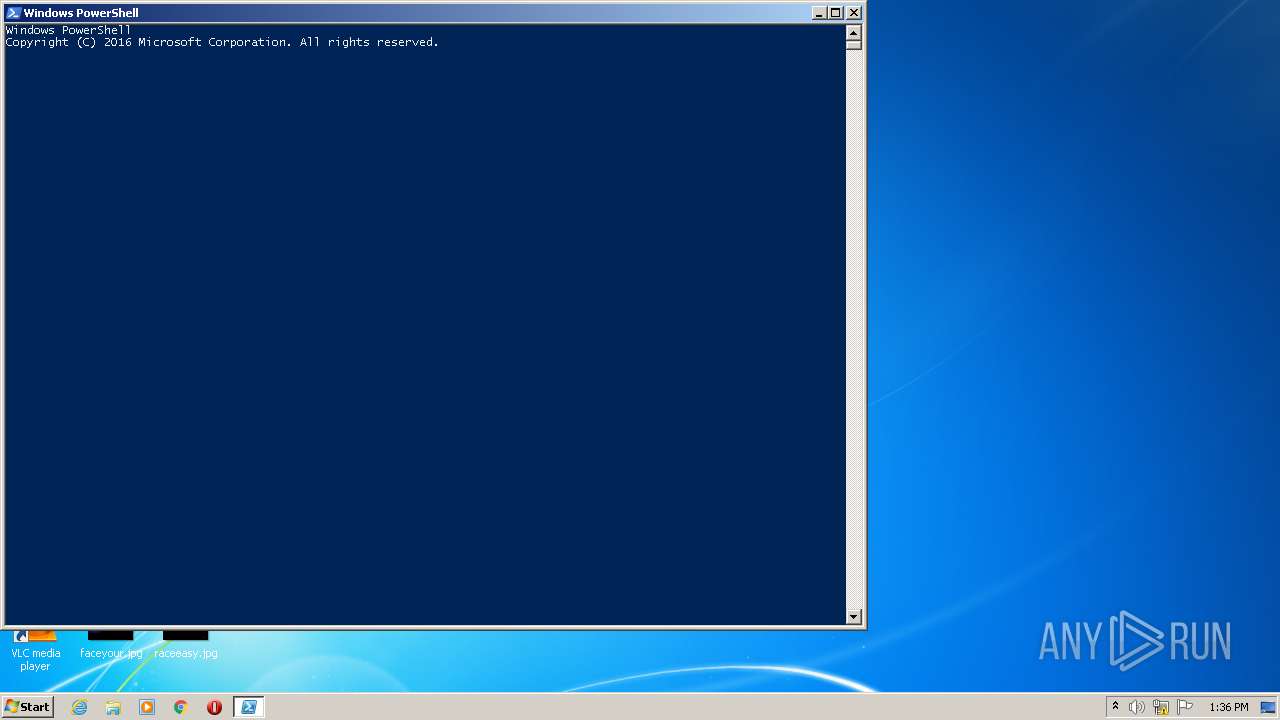
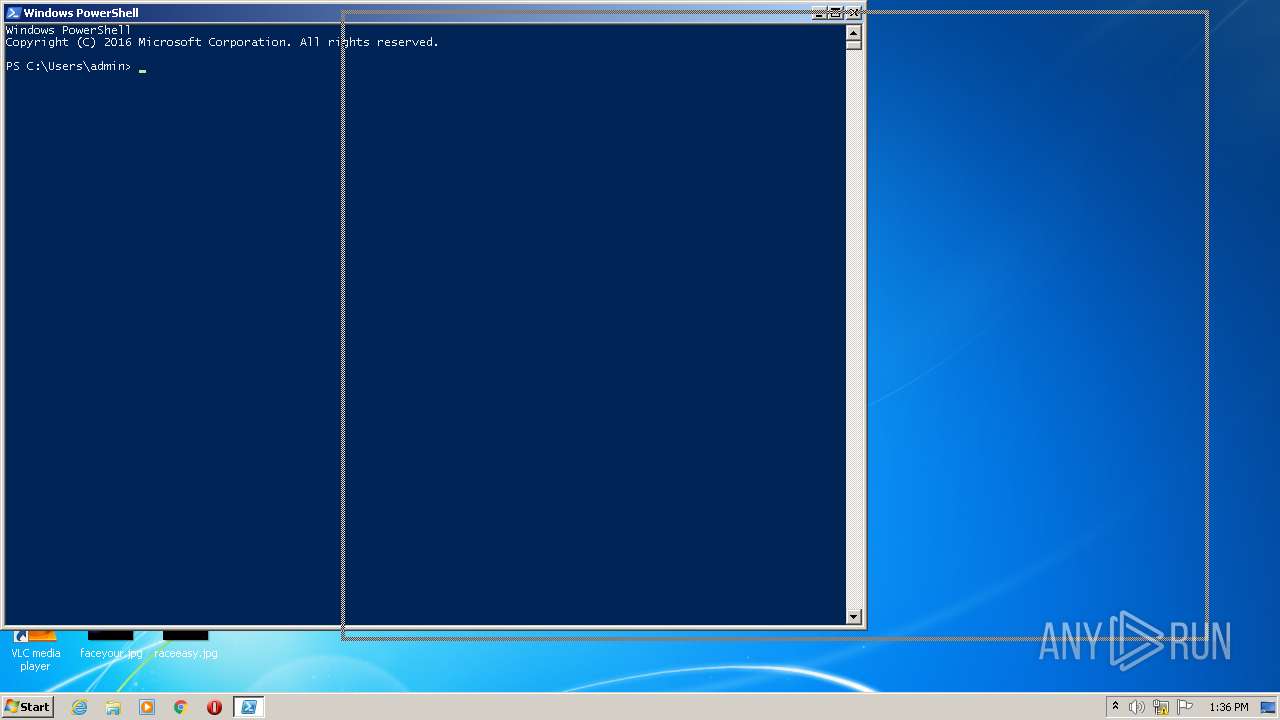
Executes PowerShell scripts
- powershell.exe (PID: 1868)
Creates files in the user directory
- powershell.exe (PID: 1868)
INFO
Checks supported languages
- NOTEPAD.EXE (PID: 2956)
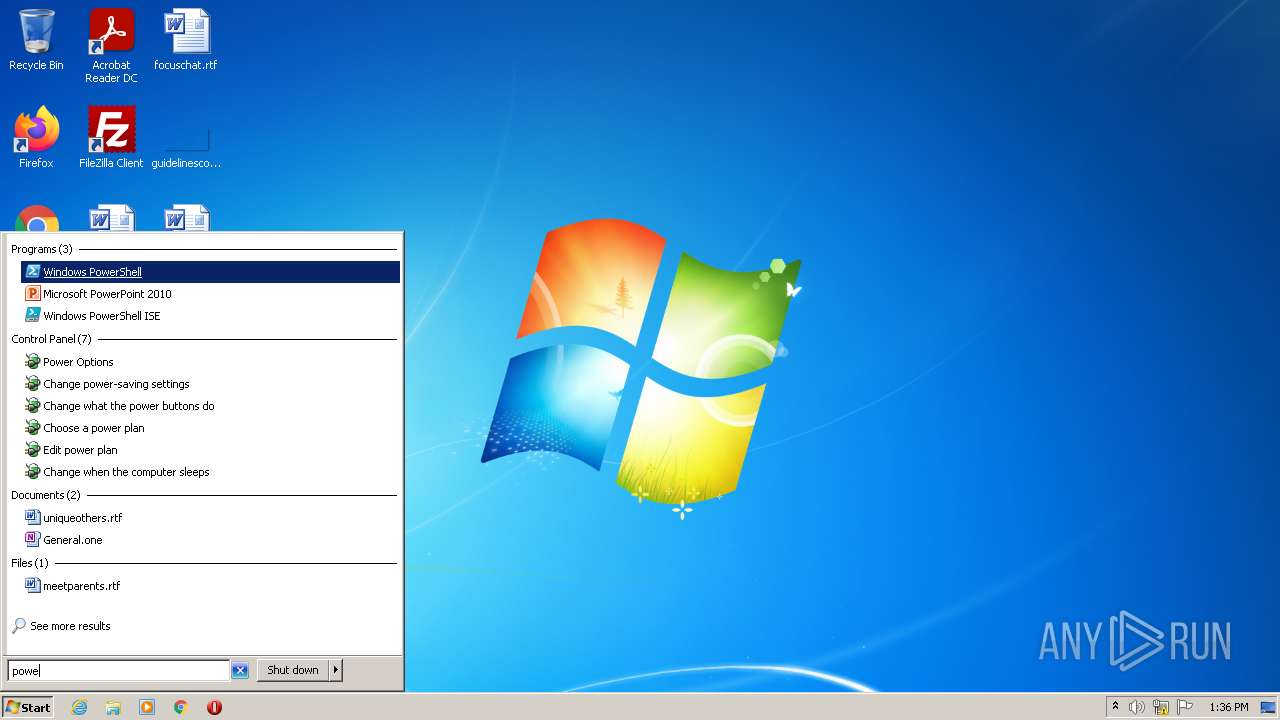
Manual execution by user
- powershell.exe (PID: 1868)
Checks Windows Trust Settings
- powershell.exe (PID: 1868)
Reads settings of System Certificates
- powershell.exe (PID: 1868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-8 encoded (100) |
|---|
Total processes
34
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1868 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2956 | "C:\Windows\system32\NOTEPAD.EXE" "C:\Users\admin\AppData\Local\Temp\WMIRunner.psm1.txt" | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 017
Read events
3 943
Write events
74
Delete events
0
Modification events
| (PID) Process: | (1868) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1868) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1868) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1868) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1868) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
6
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1868 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1868 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:— | SHA256:— | |||
| 1868 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\BL2H8Q8YRFP1EGTU28DH.temp | binary | |
MD5:— | SHA256:— | |||
| 1868 | powershell.exe | C:\Users\admin\AppData\Local\Temp\0y33jbsw.vpz.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1868 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RFffa06.TMP | binary | |
MD5:— | SHA256:— | |||
| 1868 | powershell.exe | C:\Users\admin\AppData\Local\Temp\5vk35lki.qte.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report