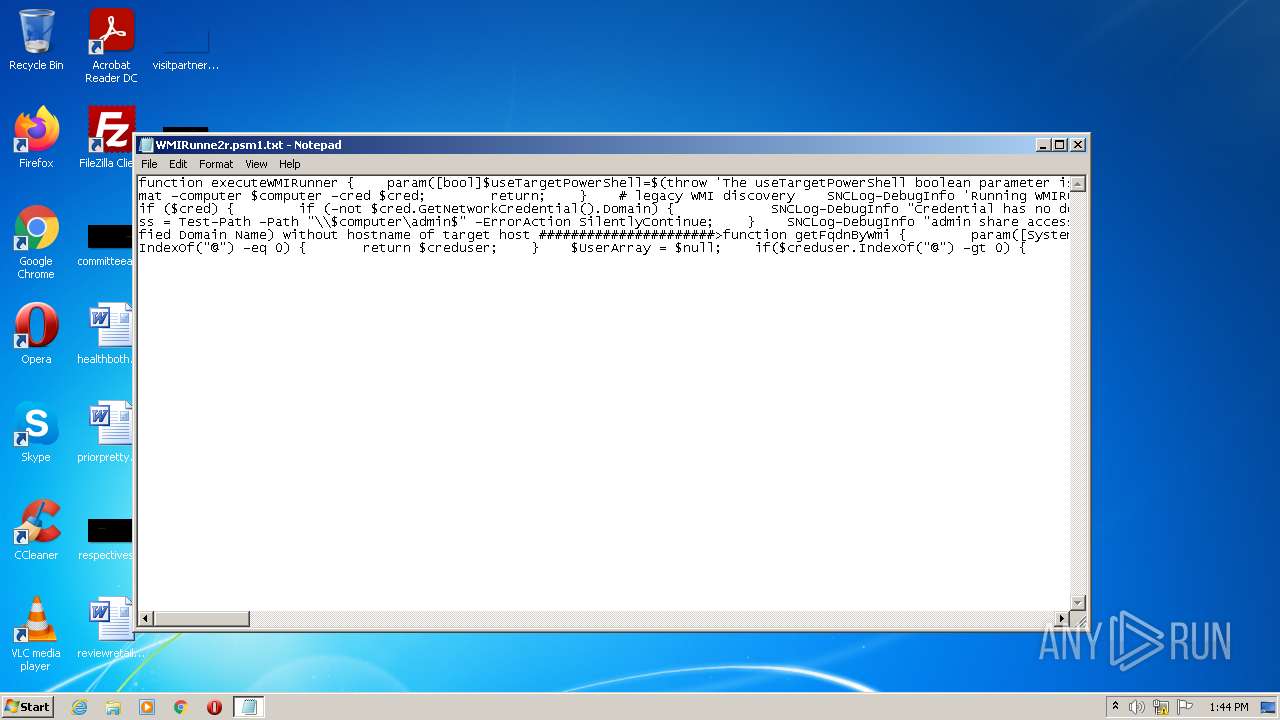
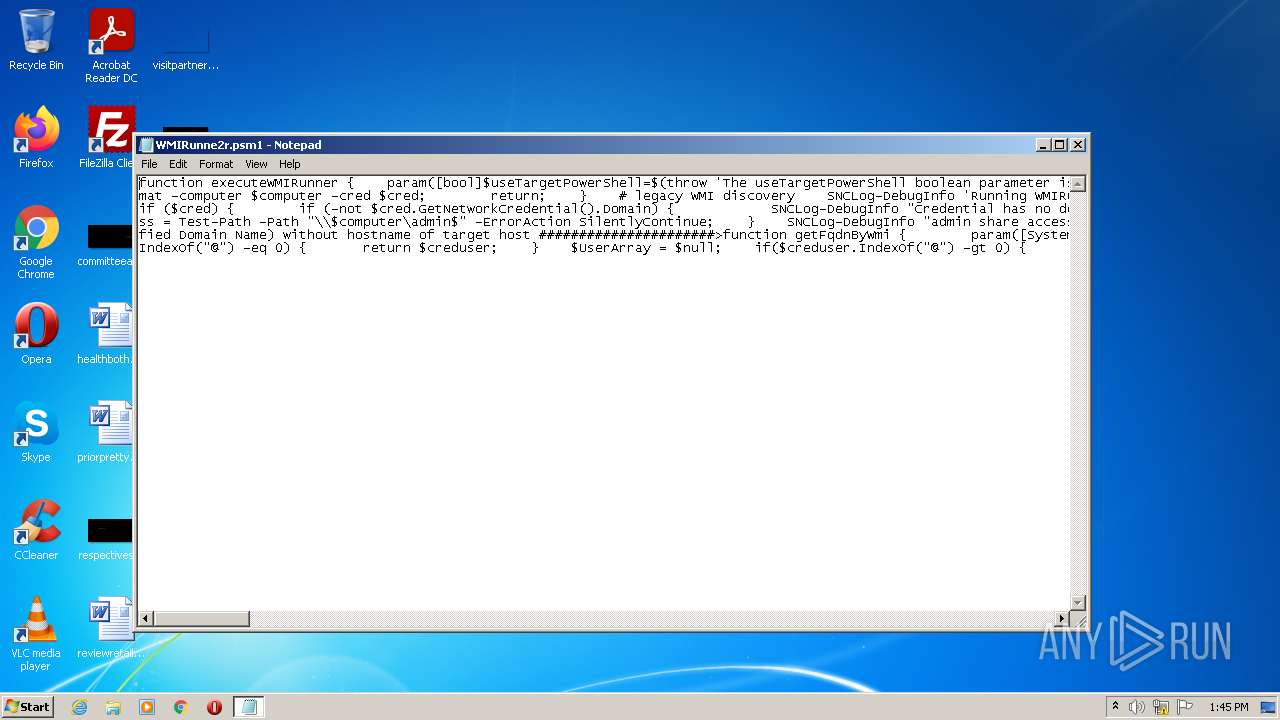
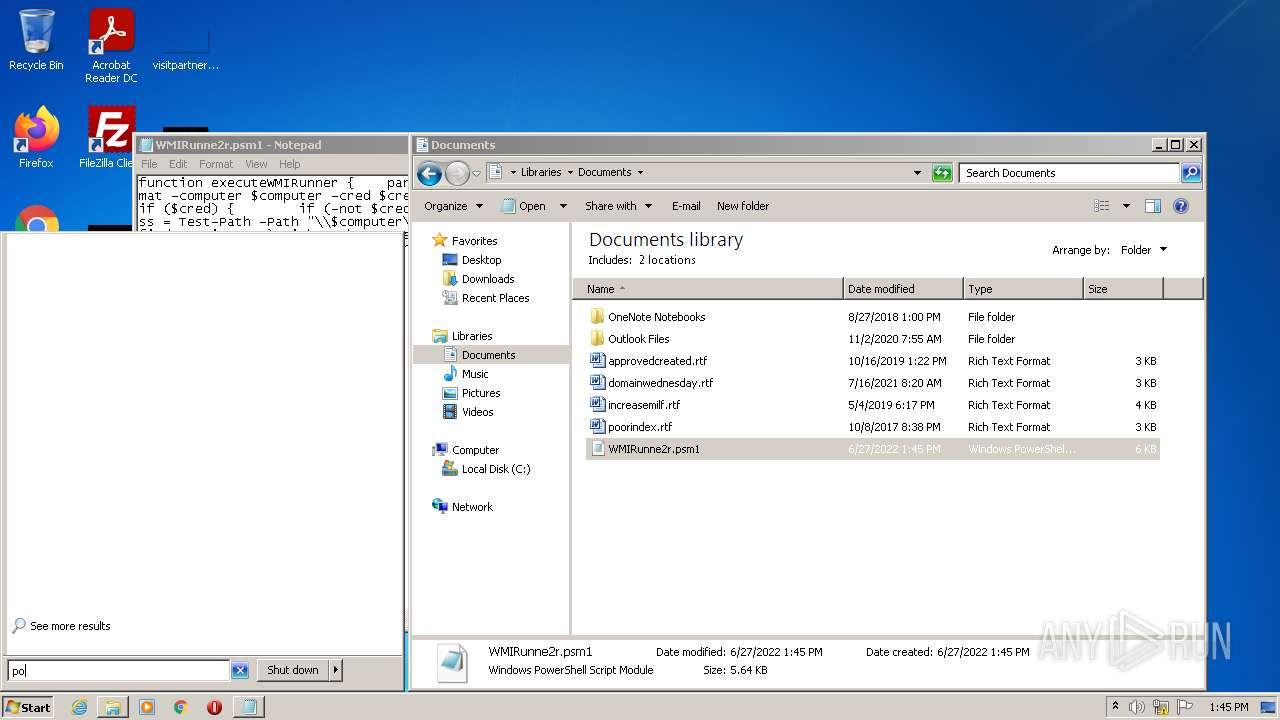
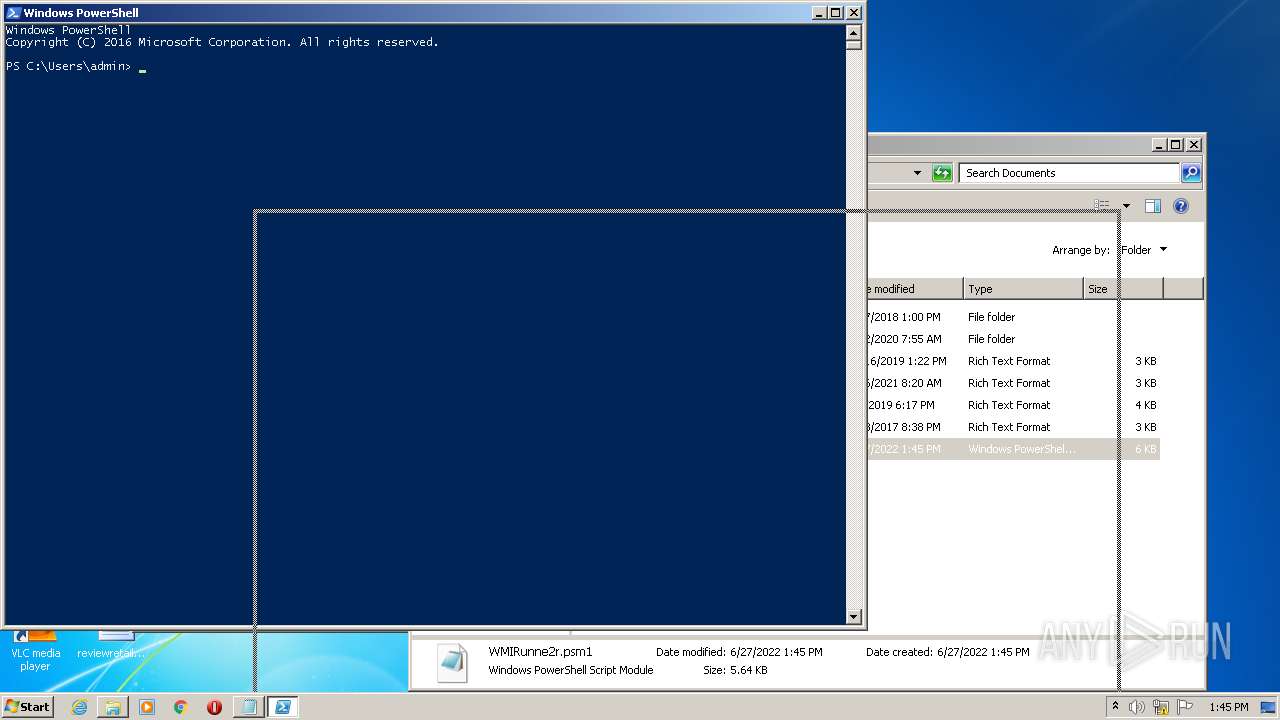
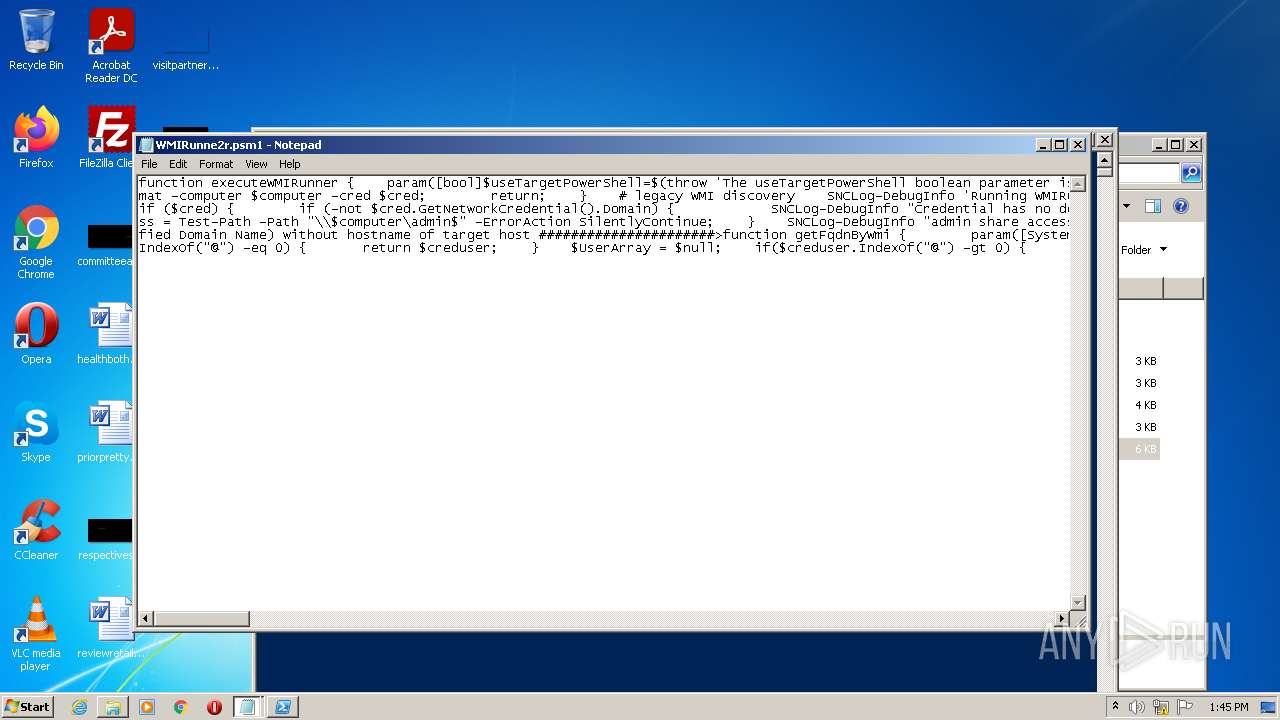
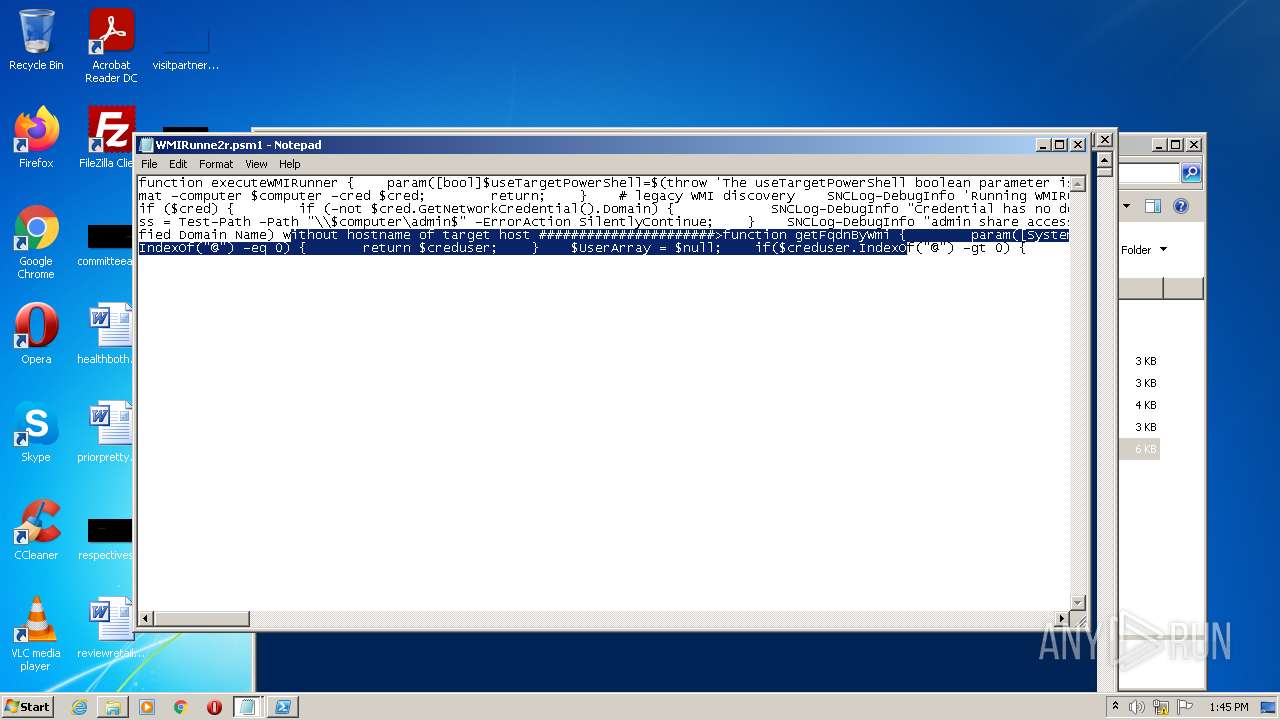
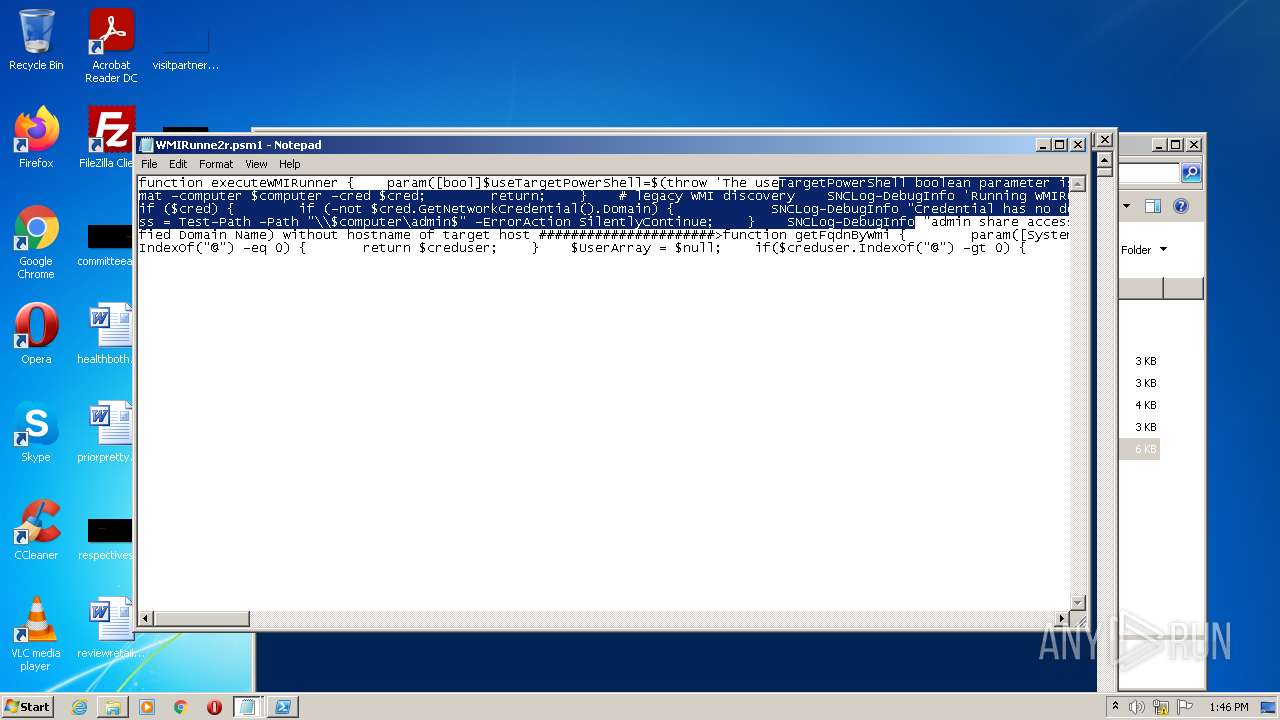
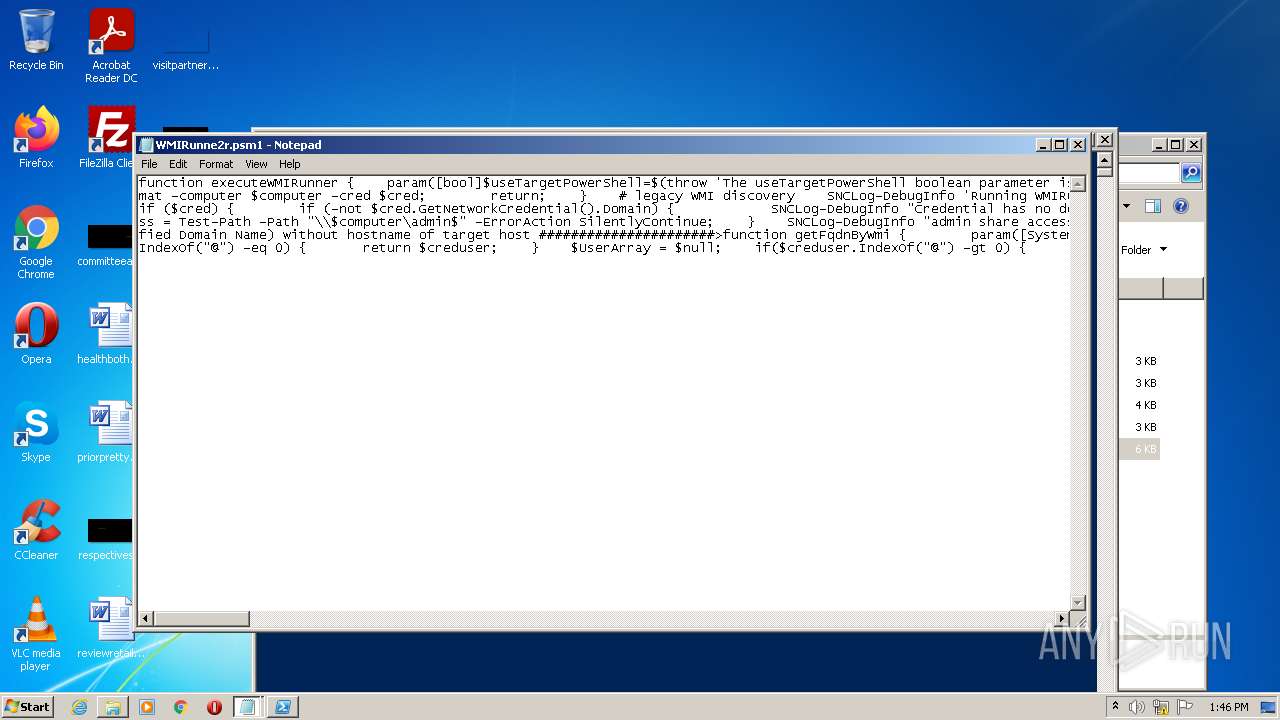
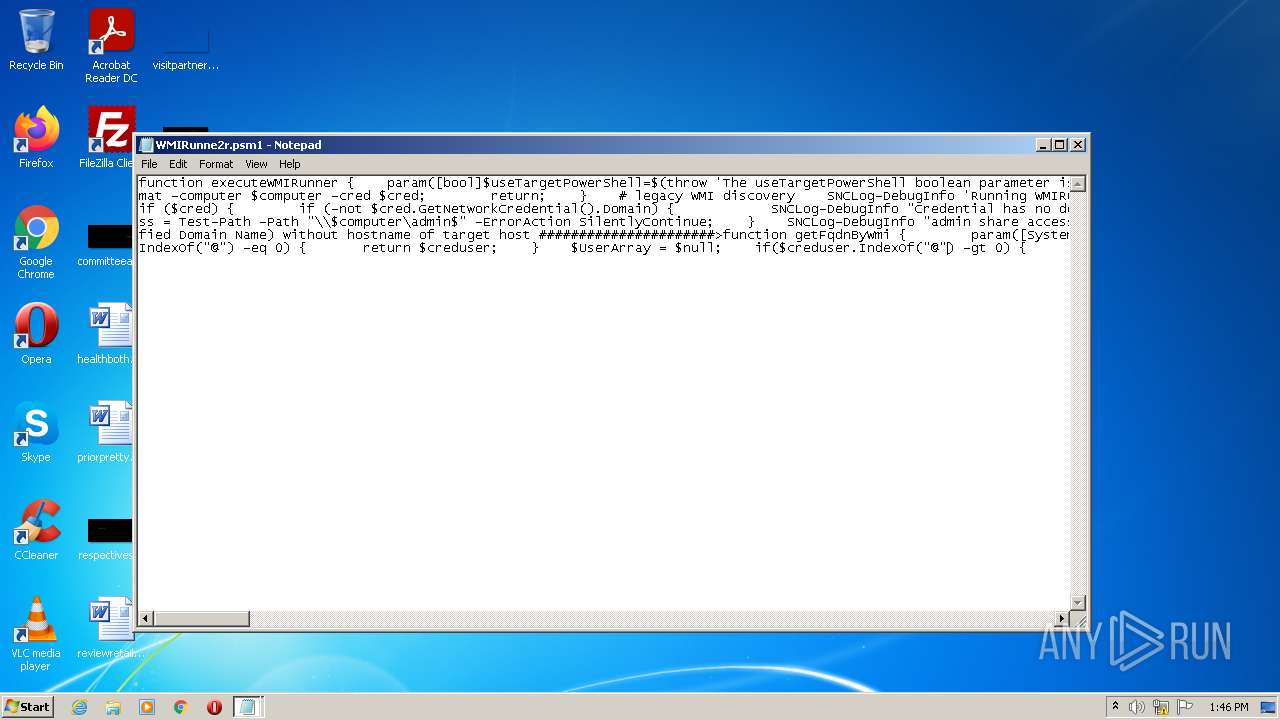
| File name: | WMIRunne2r.psm1 |
| Full analysis: | https://app.any.run/tasks/1c59daba-39b2-4363-8aae-2736a9de74b4 |
| Verdict: | Malicious activity |
| Analysis date: | June 27, 2022, 12:44:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | UTF-8 Unicode (with BOM) text |
| MD5: | B60A1AE801B188FAA9F75CCF4170FAE7 |
| SHA1: | 53911C5919D694017F6A714F67CD019F5036DD91 |
| SHA256: | D65330B4FD1181EC01FBCC7261CF4E663E153E3D57FCD9E6ABA2A138B7CA3CA3 |
| SSDEEP: | 96:BHKKfUb3ralcek90EKKSzIcNjLNyrLPh/tN+S6miYbLjHYnYYnG8r0RFzHTdx:BHBcb3ralaTBSzZ1ByrtVN+S6m5bnHYm |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the date of Windows installation
- powershell.exe (PID: 952)
Reads the computer name
- powershell.exe (PID: 952)
Checks supported languages
- powershell.exe (PID: 952)
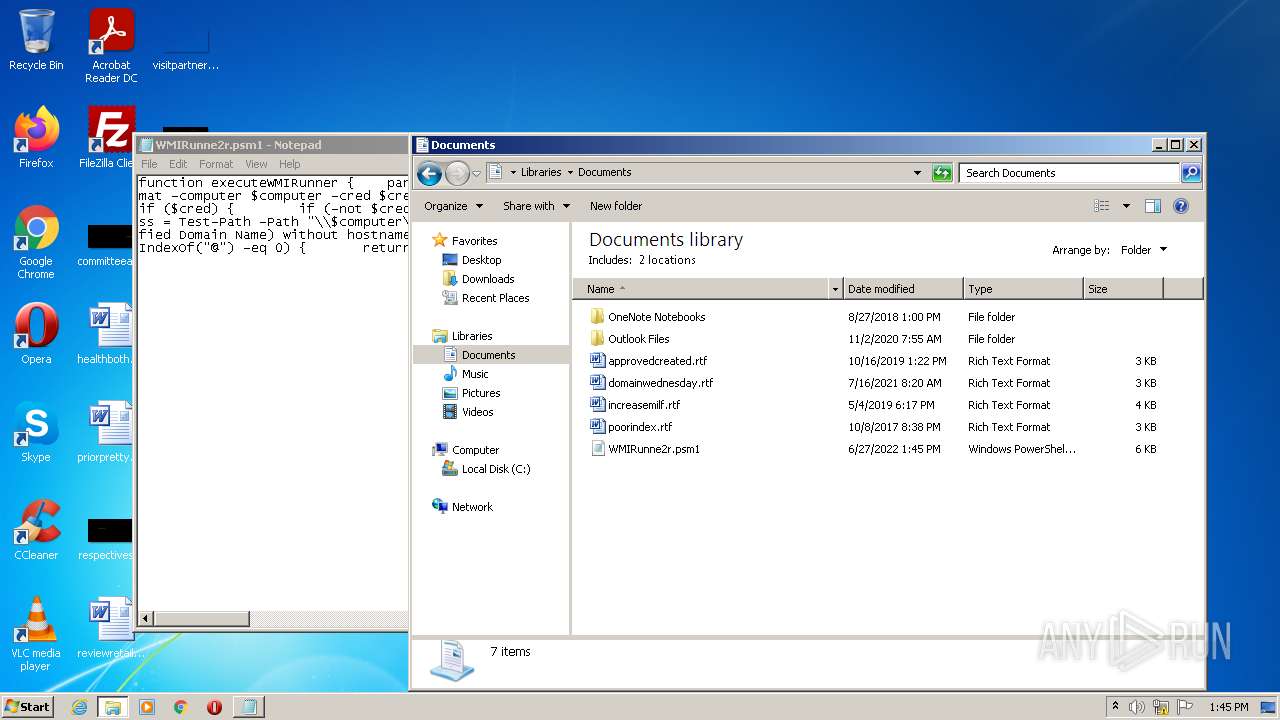
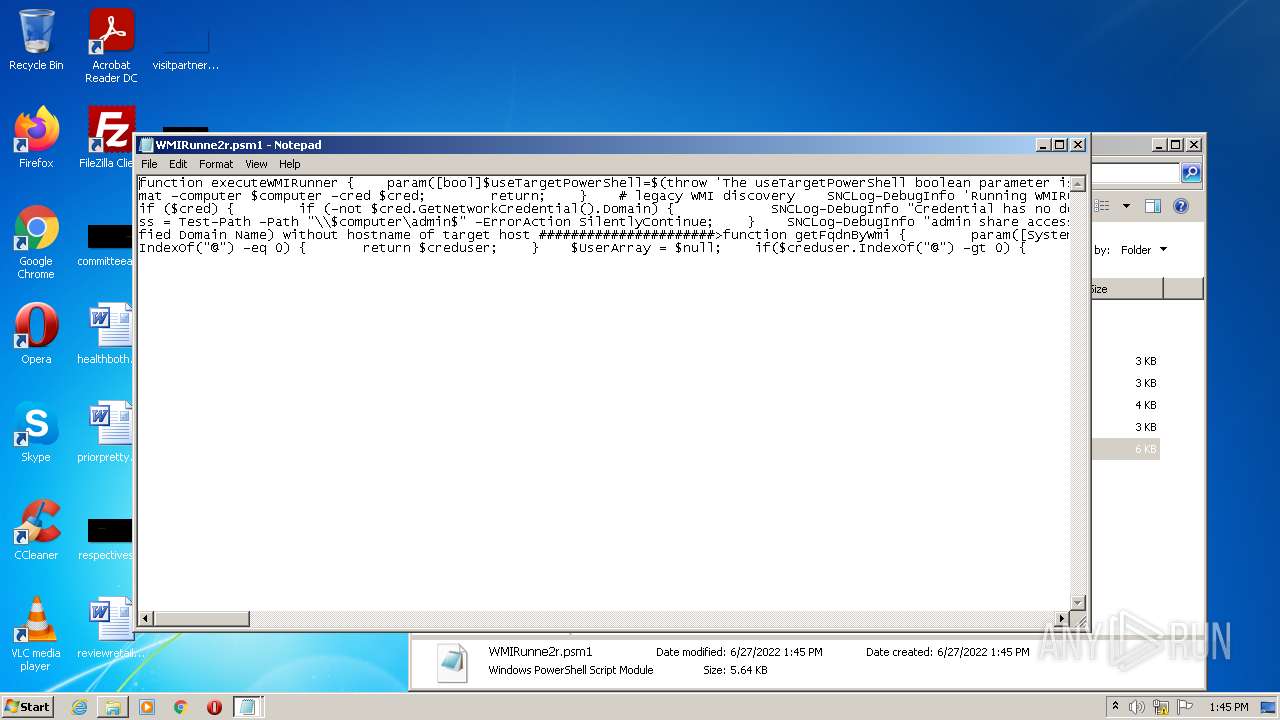
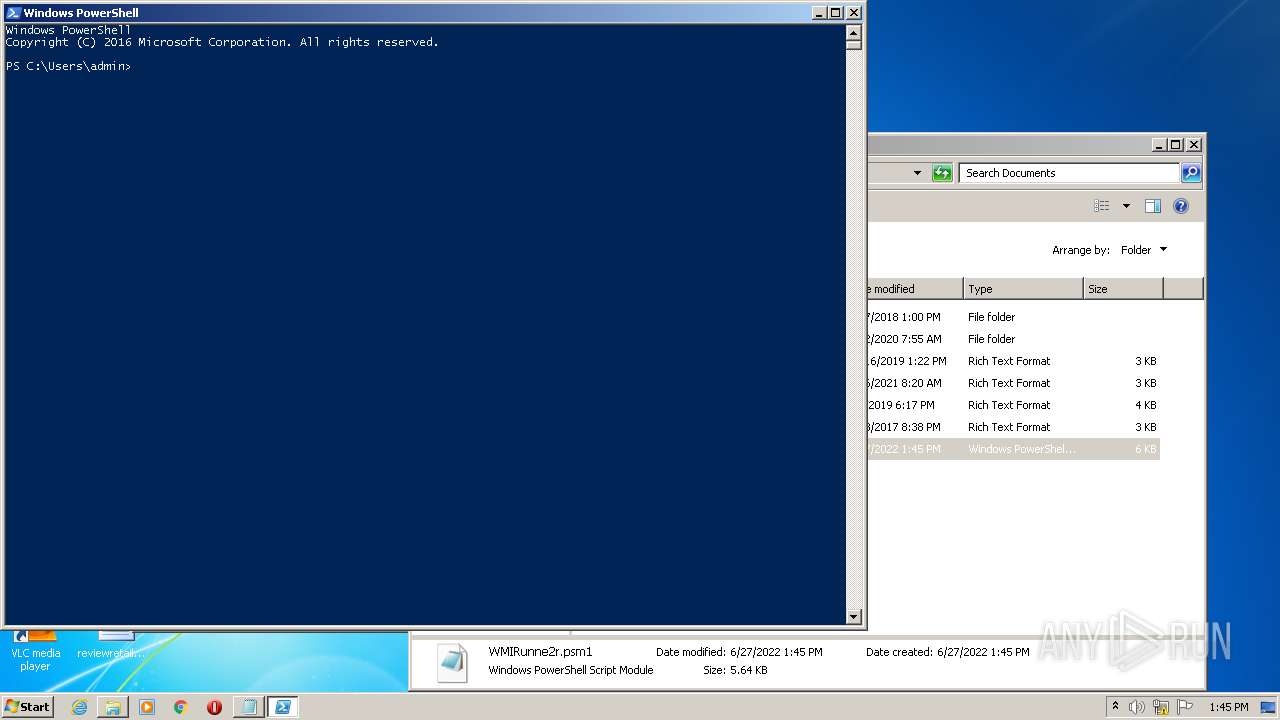
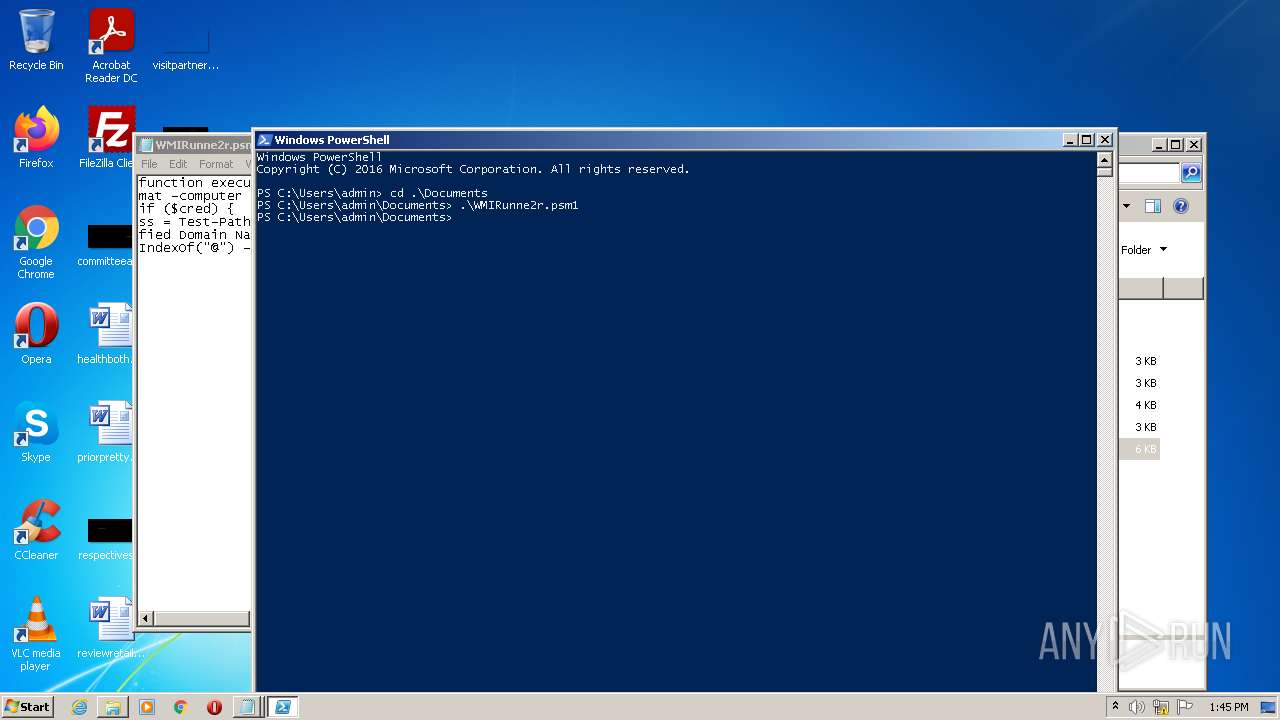
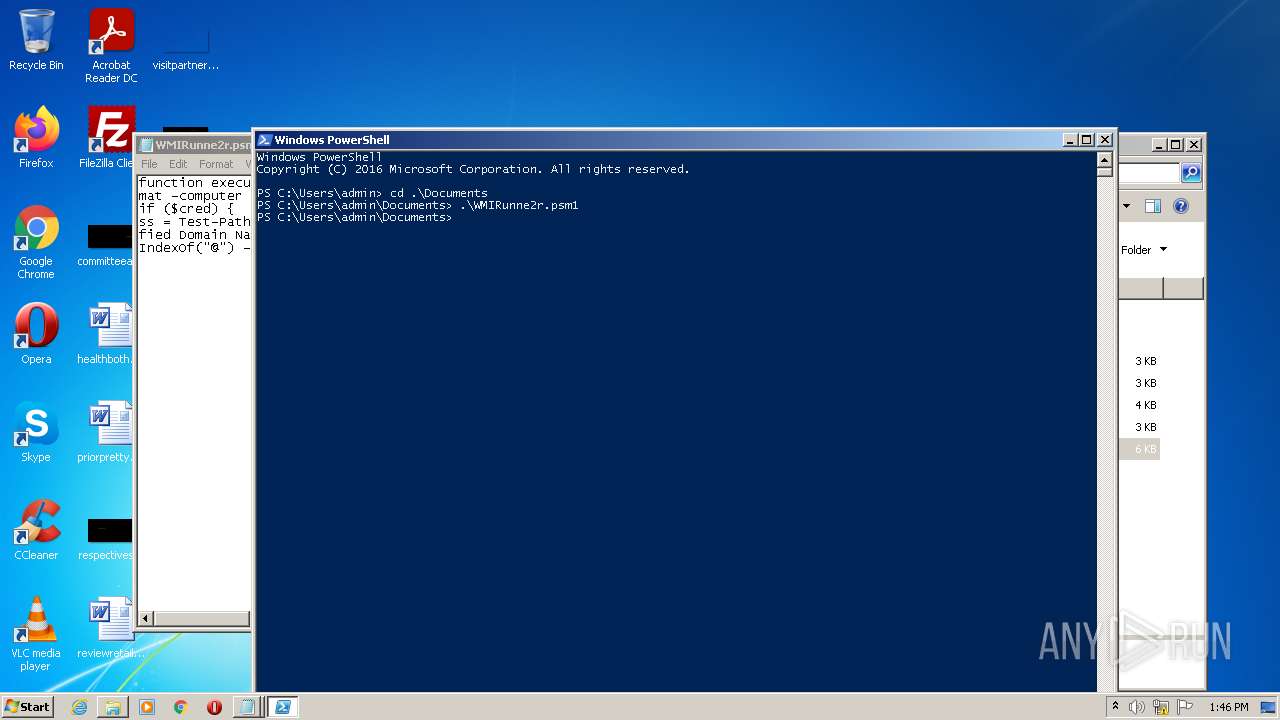
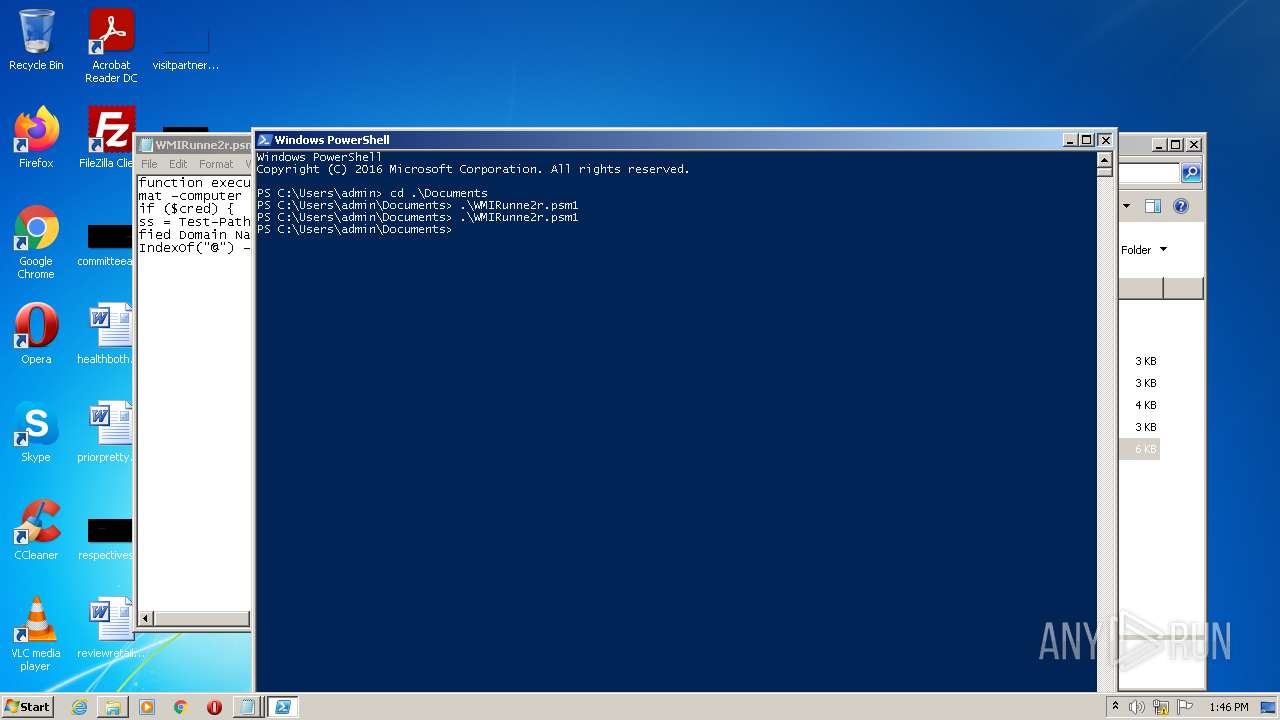
Executes PowerShell scripts
- powershell.exe (PID: 952)
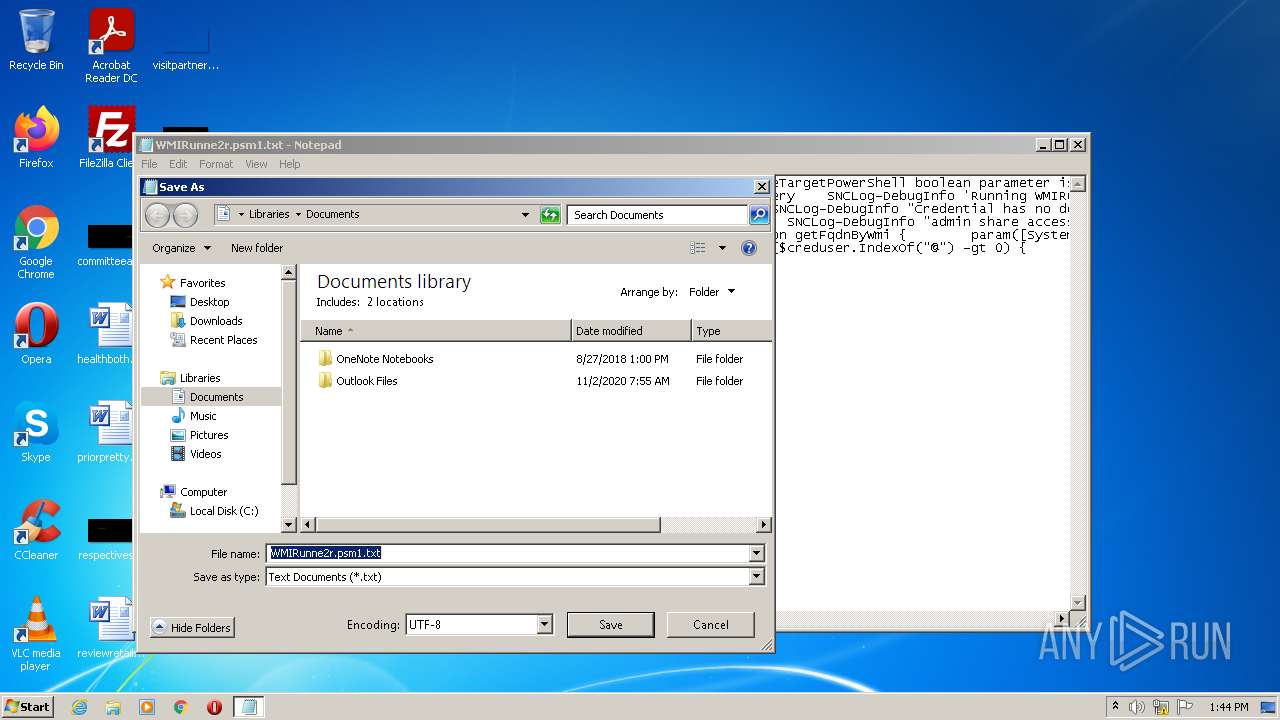
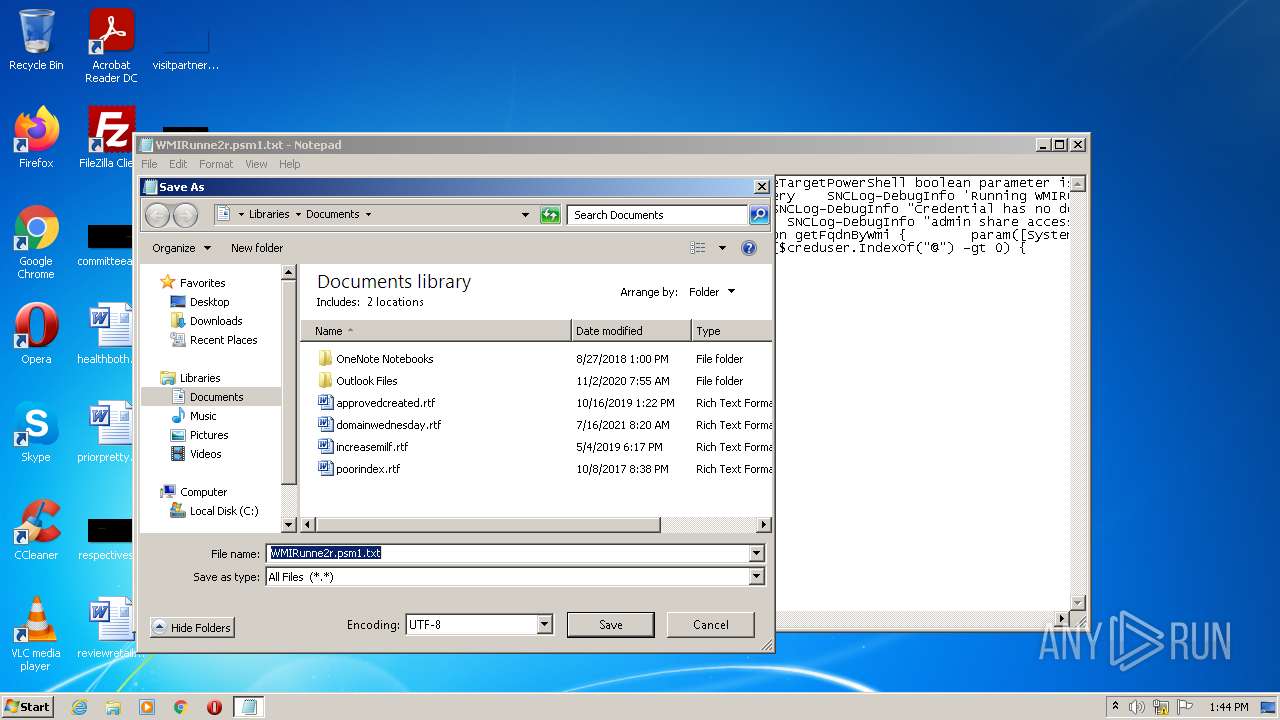
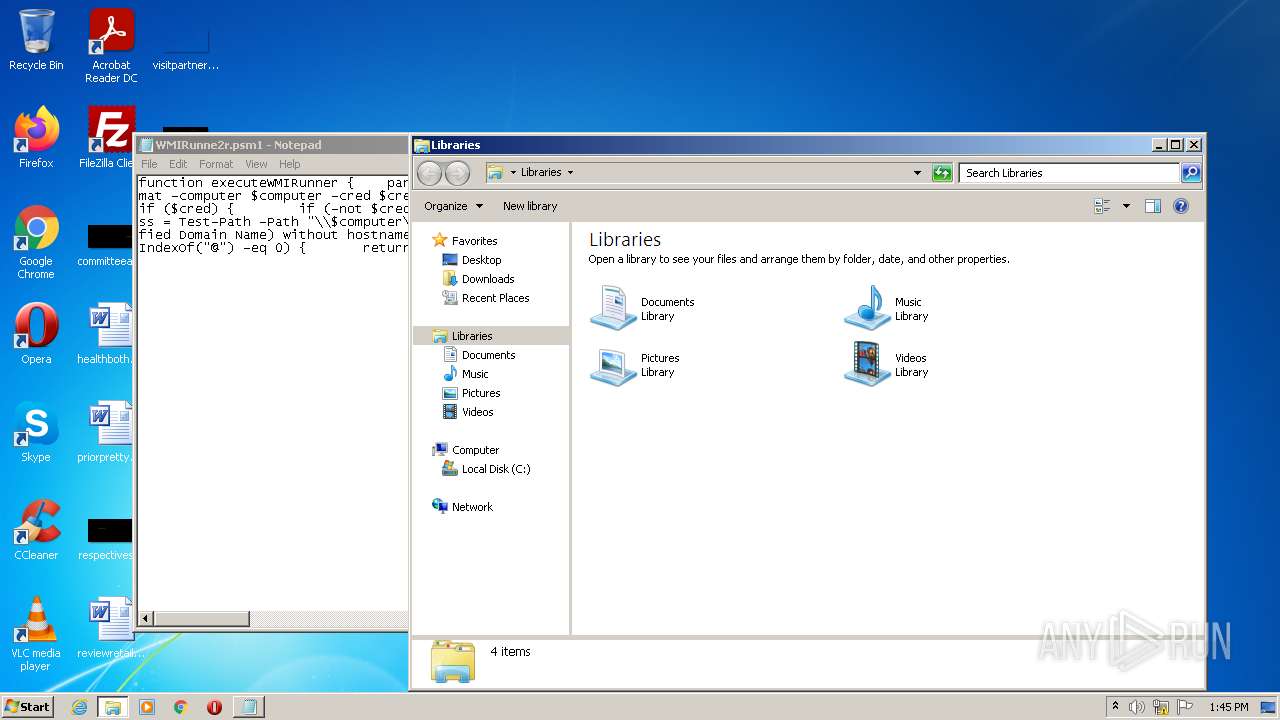
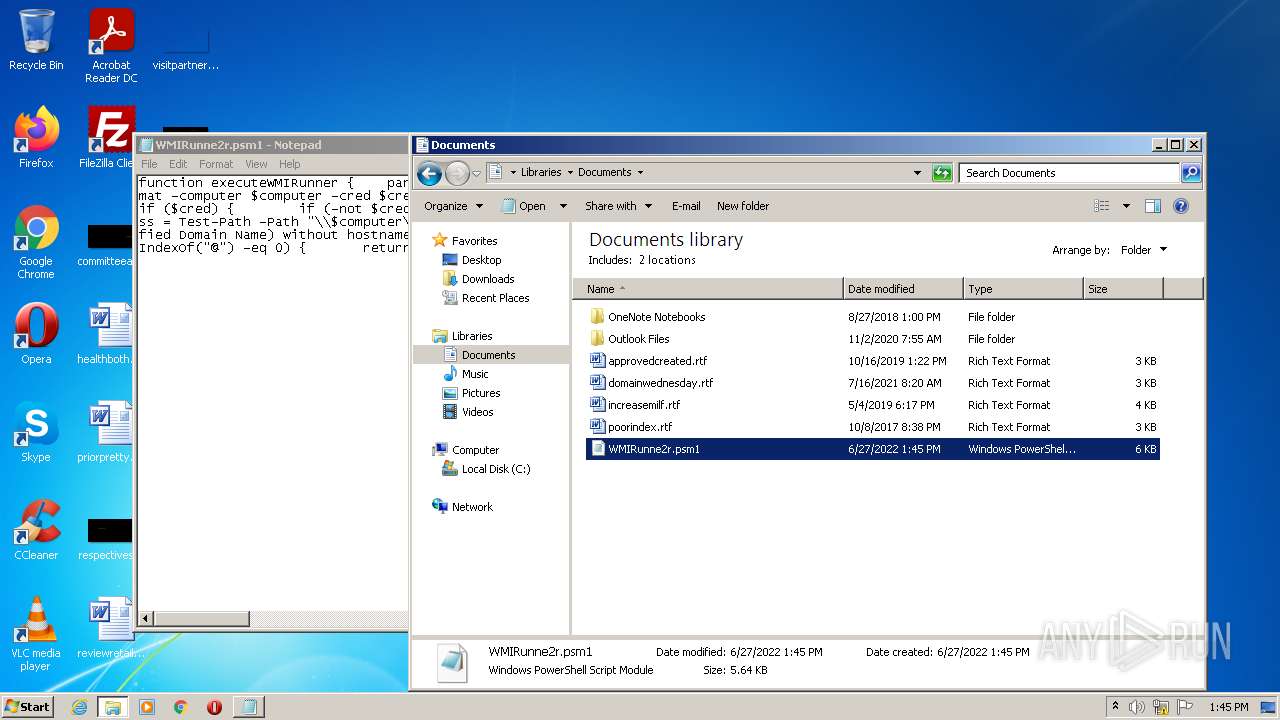
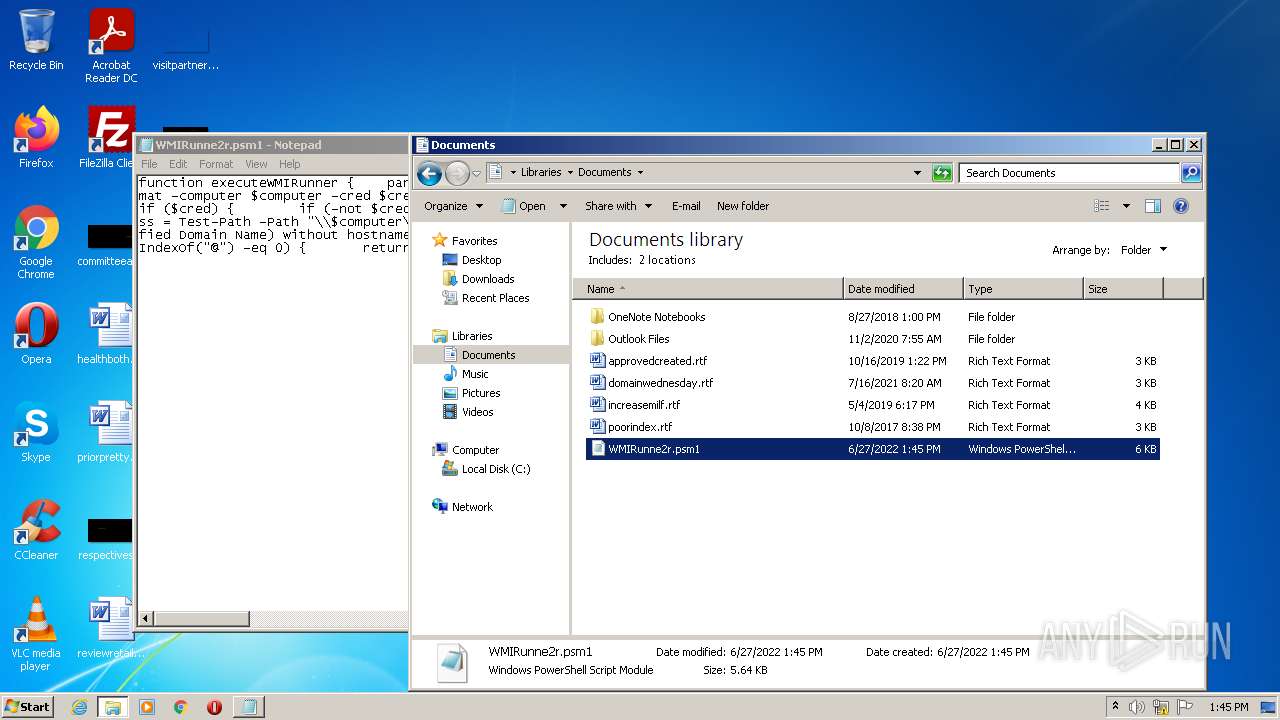
Creates files in the user directory
- powershell.exe (PID: 952)
INFO
Reads the computer name
- explorer.exe (PID: 3616)
- NOTEPAD.EXE (PID: 956)
Checks supported languages
- explorer.exe (PID: 3616)
- notepad.exe (PID: 1164)
- NOTEPAD.EXE (PID: 956)
- notepad.exe (PID: 2168)
- notepad.exe (PID: 1584)
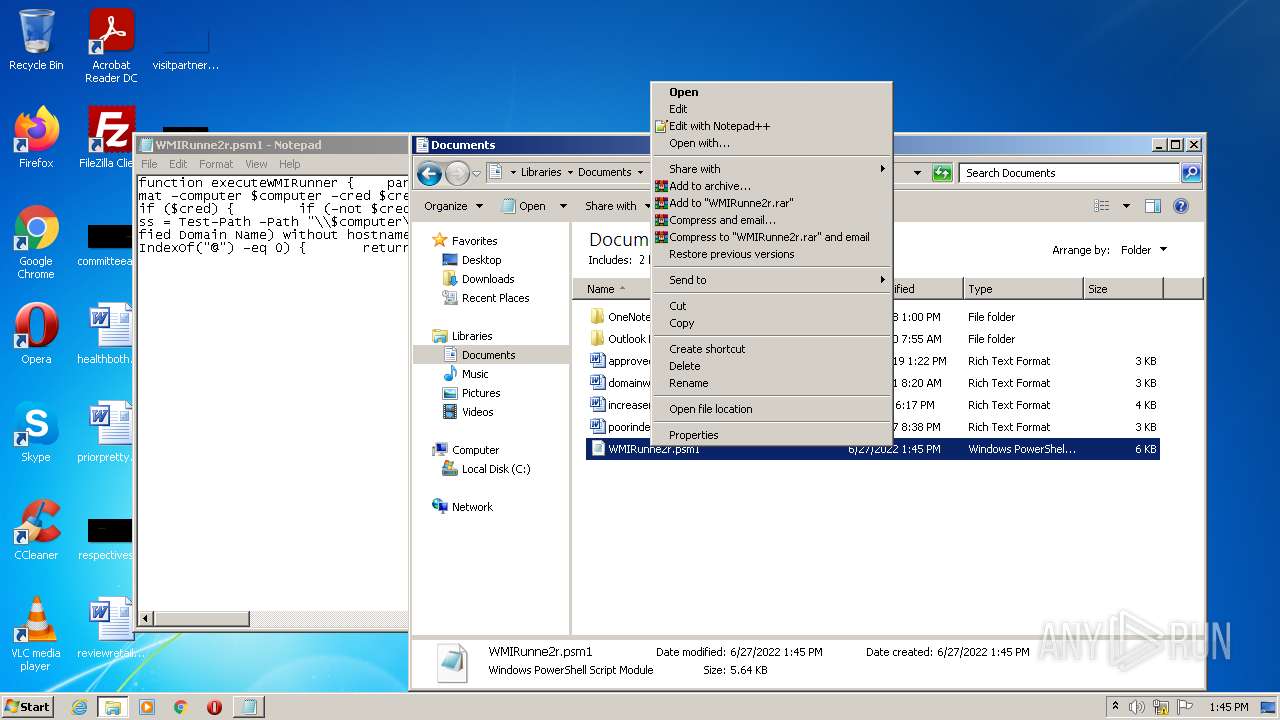
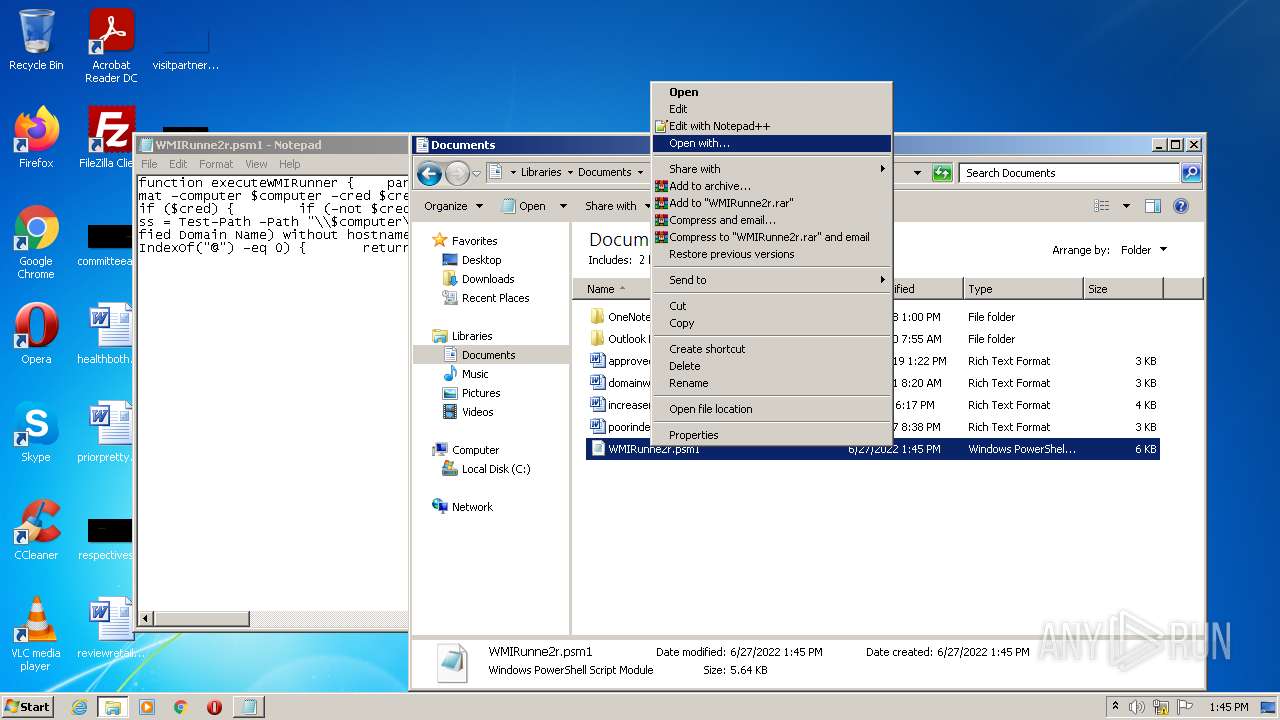
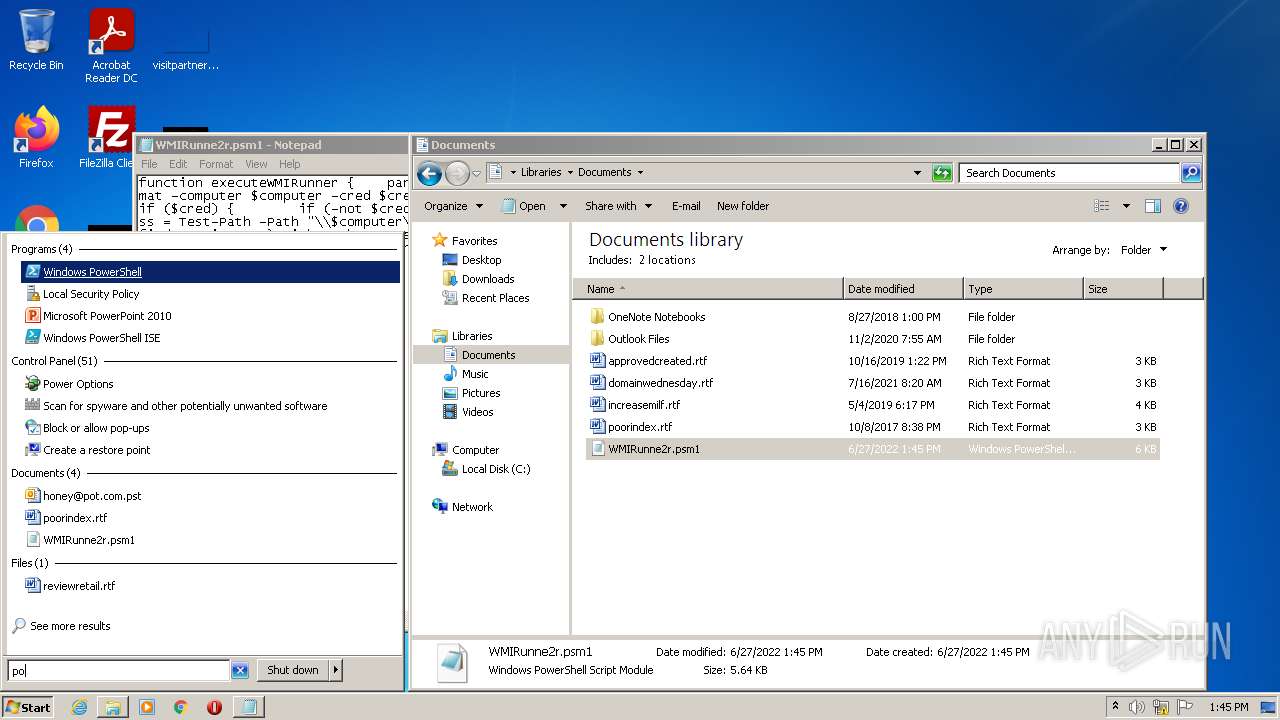
Manual execution by user
- explorer.exe (PID: 3616)
- notepad.exe (PID: 1164)
- powershell.exe (PID: 952)
Reads settings of System Certificates
- powershell.exe (PID: 952)
Checks Windows Trust Settings
- powershell.exe (PID: 952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .txt | | | Text - UTF-8 encoded (100) |
|---|
Total processes
42
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
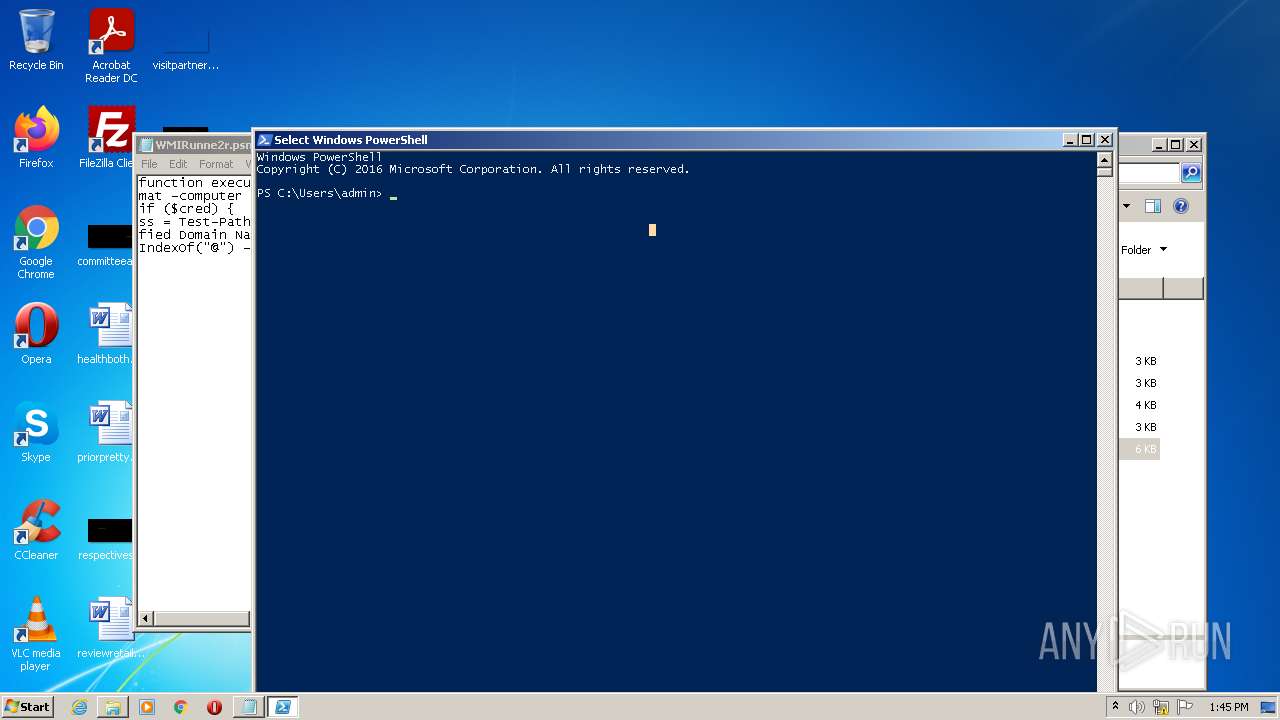
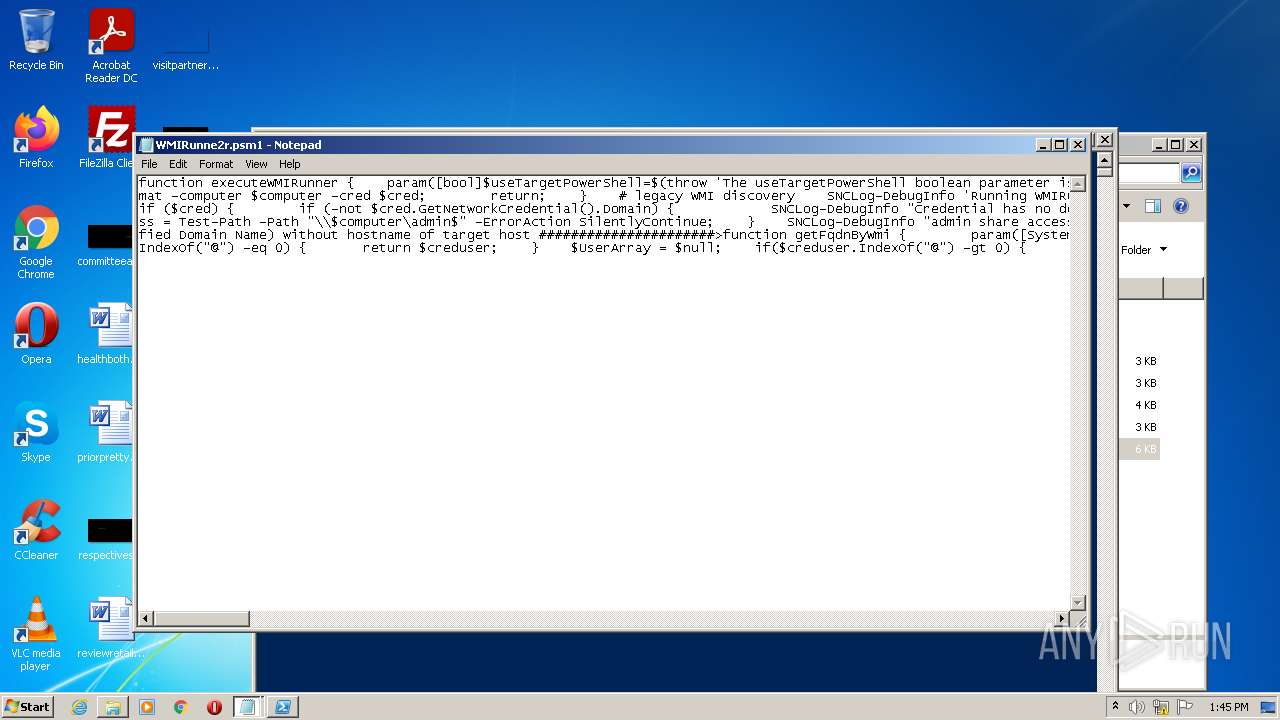
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 952 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 956 | "C:\Windows\system32\NOTEPAD.EXE" "C:\Users\admin\AppData\Local\Temp\WMIRunne2r.psm1.txt" | C:\Windows\system32\NOTEPAD.EXE | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1164 | "C:\Windows\System32\notepad.exe" "C:\Users\admin\Documents\WMIRunne2r.psm1" | C:\Windows\System32\notepad.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1584 | "C:\Windows\System32\notepad.exe" "C:\Users\admin\Documents\WMIRunne2r.psm1" | C:\Windows\System32\notepad.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2168 | "C:\Windows\System32\notepad.exe" "C:\Users\admin\Documents\WMIRunne2r.psm1" | C:\Windows\System32\notepad.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3616 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 183
Read events
6 070
Write events
111
Delete events
2
Modification events
| (PID) Process: | (956) NOTEPAD.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (956) NOTEPAD.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000010000000D0000000C000000000000000B00000007000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (956) NOTEPAD.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (956) NOTEPAD.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
| (PID) Process: | (956) NOTEPAD.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewVersion |
Value: 0 | |||
| (PID) Process: | (956) NOTEPAD.EXE | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (956) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | 3 |
Value: 4E004F00540045005000410044002E00450058004500000014001F4225481E03947BC34DB131E946B44C8DD5740000001A00EEBBFE23000010007DB10D7BD29C934A973346CC89022E7C00002A0000000000EFBE000000200000000000000000000000000000000000000000000000000100000020002A0000001900EFBE7E47B3FBE4C93B4BA2BAD3F5D3CD46F98207BA827A5B6945B5D7EC83085F08CC20000000 | |||
| (PID) Process: | (956) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | MRUListEx |
Value: 03000000020000000100000000000000FFFFFFFF | |||
| (PID) Process: | (956) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\psm1 |
| Operation: | write | Name: | 0 |
Value: 14001F4225481E03947BC34DB131E946B44C8DD5740000001A00EEBBFE23000010007DB10D7BD29C934A973346CC89022E7C00002A0000000000EFBE000000200000000000000000000000000000000000000000000000000100000020002A0000001900EFBE7E47B3FBE4C93B4BA2BAD3F5D3CD46F98207BA827A5B6945B5D7EC83085F08CC2000900300008A0381191410600320000000484000000000000000000000000000000000000000000000000000000000730000003153505330F125B7EF471A10A5F102608C9EEBAC310000000A000000001F0000001000000057004D004900520075006E006E006500320072002E00700073006D0031000000150000000C00000000150000000000000000000000110000000D000000001300000080000000000000006802000031535053A66A63283D95D211B5D600C04FD918D01100000019000000001300000077014840ED010000200000000011100000D901000014001F50E04FD020EA3A6910A2D808002B30309D19002F433A5C000000000000000000000000000000000000007400310000000000454B314E1100557365727300600008000400EFBEEE3AA314454B314E2A0000005A01000000000100000000000000000036000000000055007300650072007300000040007300680065006C006C00330032002E0064006C006C002C002D0032003100380031003300000014004C003100000000001C4D9960100061646D696E00380008000400EFBE454B804A1C4D99602A0000002D000000000004000000000000000000000000000000610064006D0069006E000000140080003100000000006554D08D1100444F43554D457E310000680008000400EFBE454B814A6554D08D2A0000007A0100000000020000000000000000003E000000000044006F00630075006D0065006E0074007300000040007300680065006C006C00330032002E0064006C006C002C002D0032003100370037003000000018006A00320000000000000000008000574D4952756E6E6532722E70736D31004C0008000400EFBE00000000000000002A0000000000000000000000000000000000000000000000000057004D004900520075006E006E006500320072002E00700073006D00310000001E0000000000003100000018000000001F0000001000000057004D004900520075006E006E006500320072002E00700073006D00310000001D0000000B000000001F000000060000002E00700073006D003100000000000000810000003153505340E83E1E2BBC6C4782372ACD1A839B226500000008000000001F0000002900000043003A005C00550073006500720073005C00610064006D0069006E005C0044006F00630075006D0065006E00740073005C0057004D004900520075006E006E006500320072002E00700073006D00310000000000000000000000000000000000 | |||
| (PID) Process: | (956) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\psm1 |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
Executable files
0
Suspicious files
6
Text files
1
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 952 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\E35WHTQ9G87I9WSPOFF3.temp | binary | |
MD5:— | SHA256:— | |||
| 952 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF102aac.TMP | binary | |
MD5:— | SHA256:— | |||
| 952 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:— | SHA256:— | |||
| 956 | NOTEPAD.EXE | C:\Users\admin\Documents\WMIRunne2r.psm1 | text | |
MD5:— | SHA256:— | |||
| 952 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 952 | powershell.exe | C:\Users\admin\AppData\Local\Temp\a3qiduck.edi.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 952 | powershell.exe | C:\Users\admin\AppData\Local\Temp\aucewy1g.2er.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 952 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-Interactive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report