| URL: | https://m.witskies.click/c/c/115/2256?cid={CLICK_ID}&sc={SOURCE}" |
| Full analysis: | https://app.any.run/tasks/b041541f-674a-4b9b-823c-6f2ffc811fef |
| Verdict: | Malicious activity |
| Analysis date: | September 21, 2021, 18:41:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 94076C119A419339C3B1A9C85E13C545 |
| SHA1: | 3BB13682E64C8C81ED95AA91ABFCD34756DA1361 |
| SHA256: | D64EC1992DECC57FD50250B87B46BFF6C486CC4130BA989526F199E5678F082B |
| SSDEEP: | 3:N8QInGJ/QRAKCmFzNr:2bnGJ0AKZ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1548)
INFO
Reads the computer name
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 1548)
Checks supported languages
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 1548)
Changes internet zones settings
- iexplore.exe (PID: 2956)
Reads internet explorer settings
- iexplore.exe (PID: 1548)
Reads settings of System Certificates
- iexplore.exe (PID: 2956)
- iexplore.exe (PID: 1548)
Application launched itself
- iexplore.exe (PID: 2956)
Checks Windows Trust Settings
- iexplore.exe (PID: 1548)
- iexplore.exe (PID: 2956)
Creates files in the user directory
- iexplore.exe (PID: 1548)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2956)
Changes settings of System certificates
- iexplore.exe (PID: 2956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1548 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2956 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2956 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://m.witskies.click/c/c/115/2256?cid={CLICK_ID}&sc={SOURCE}"" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
12 553
Read events
12 378
Write events
171
Delete events
4
Modification events
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30912280 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30912280 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2956) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
17
Text files
46
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:BD3051190B9D48D4F57272C4C6537629 | SHA256:C4D7E1E838AD59DF673511E92591EA18BD6D6589A5B79BEFA32A6306607424B4 | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\3A6FC93FFB3EBF7DE46D04C79AD48874 | binary | |
MD5:307AAF387A0B8D0D090FDEFFB070D36B | SHA256:231CBAA93066F31F0AB75987277DB1EC9556E6A70301A2D62AA3770FC04C8E11 | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\644B8874112055B5E195ECB0E8F243A4 | der | |
MD5:53A7664406B0FE72E2D7B0679222D997 | SHA256:3318669FA9A75CD9975D2393F042517DA43E2F9C5749954DD6DB75D83160AF6F | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\3EGSHLED.htm | html | |
MD5:2E25DC7C9EA945638B537DC78C14CBF6 | SHA256:869103561EAA82B3270396771FF6B376737E3CE1BC0352004CF84EB283D11C5A | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\91VEGT22.htm | html | |
MD5:548CD53B79075C02D31093535F384B85 | SHA256:73D5A5D61876A0CE8915221720F91869E63DBA046FB8E0AC104DBDAB4FA322D4 | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\proc[1].htm | html | |
MD5:6BAF4A934B1C18D7AC8CABCDF8E20DBE | SHA256:2800FF56EF647137E00B2F374FA7DA6D75CB1615B1C91E356DB11374DC55A73B | |||
| 2956 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | binary | |
MD5:248722AE592E62D265CA806D03AE54B9 | SHA256:9E38B0A2C6E9C214ADD12BE411619D2562C092C375123B7A3E31BF38F33DDBD2 | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\8E9IX1Y8.txt | text | |
MD5:C199DC4D48307627C188143B0BD3BBE9 | SHA256:E9563C823E0CC65EB1EF06D771B466E79D87776F287DB07BDC82480A3A21D9FE | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:E4431F27357A41F9A2C4DD5B63340F87 | SHA256:0DA89E108257CD76AF979C334531DF367A530CD0D8DBB76DE8217E61DB338CE5 | |||
| 1548 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\DKNZ912H.txt | text | |
MD5:2E36242E09287B245A42062BFE22DB42 | SHA256:64C9981708A8EDB82B8FAE0DA7519FDF8CF6214DC90F3D050F60F61E041B5343 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
56
DNS requests
24
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 104.90.178.254:80 | http://x1.c.lencr.org/ | NL | der | 717 b | whitelisted |
— | — | GET | 200 | 95.101.89.35:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | unknown | der | 1.16 Kb | whitelisted |
2956 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?32b58fb86d38c823 | US | — | — | whitelisted |
2956 | iexplore.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?4b8c11ef6fd2902b | US | — | — | whitelisted |
1548 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?dcda14d4635d5291 | US | compressed | 4.70 Kb | whitelisted |
1548 | iexplore.exe | GET | 200 | 95.101.89.74:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgPs4ygforqSQMzxHHGzVmaErQ%3D%3D | unknown | der | 503 b | shared |
1548 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDc6ok2a4jVfAoAAAAA%2FPgi | US | der | 472 b | whitelisted |
1548 | iexplore.exe | GET | 200 | 95.101.89.74:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgNa%2BmCDpH%2BigPBnrp71ciIP9g%3D%3D | unknown | der | 503 b | shared |
1548 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEMsp9LYxlKyCgAAAAD89IY%3D | US | der | 471 b | whitelisted |
1548 | iexplore.exe | GET | 200 | 142.250.186.67:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQCmkxBVY%2F9DQwoAAAAA%2FPiA | US | der | 472 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1548 | iexplore.exe | 23.239.23.128:443 | m.witskies.click | Linode, LLC | US | unknown |
1548 | iexplore.exe | 95.101.89.74:80 | r3.o.lencr.org | Akamai International B.V. | — | suspicious |
— | — | 104.90.178.254:80 | x1.c.lencr.org | Akamai Technologies, Inc. | NL | unknown |
2956 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
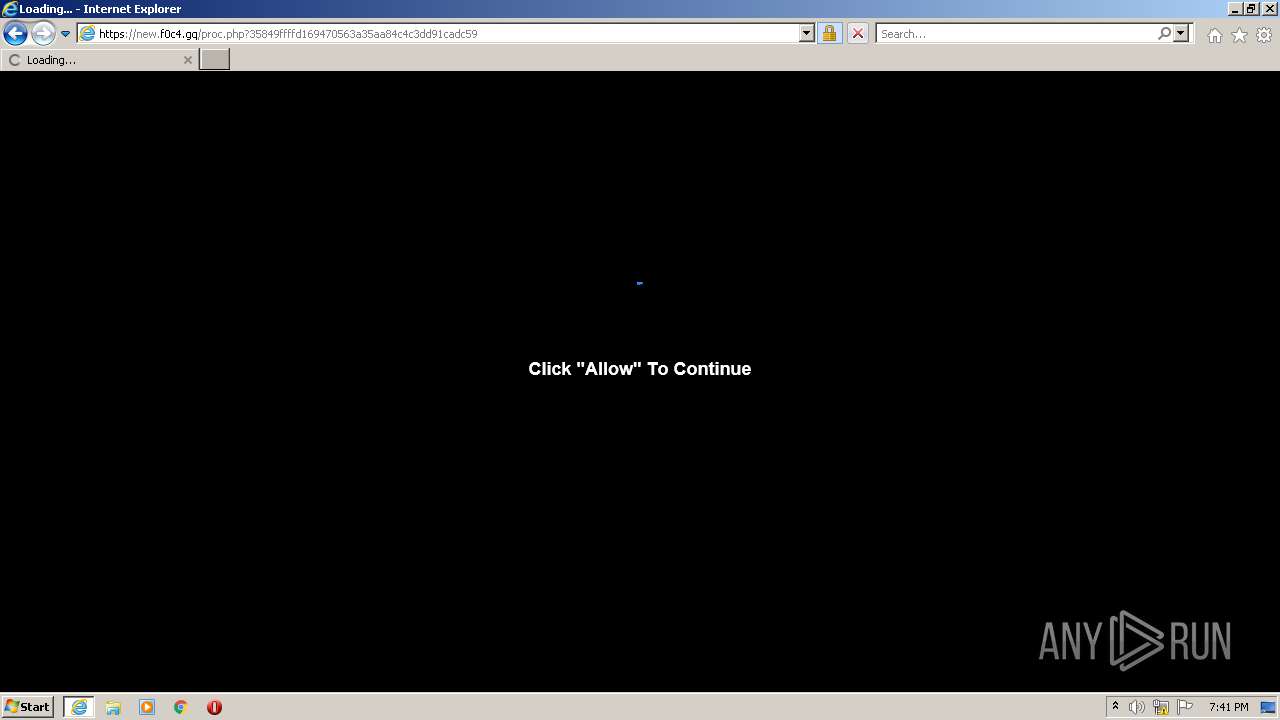
1548 | iexplore.exe | 108.178.23.116:443 | new.f0c4.gq | SingleHop, Inc. | US | suspicious |
2956 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2956 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2956 | iexplore.exe | 108.178.23.116:443 | new.f0c4.gq | SingleHop, Inc. | US | suspicious |
1548 | iexplore.exe | 139.45.197.236:443 | survey2you.com | — | US | malicious |
1548 | iexplore.exe | 162.55.4.52:443 | w8tu.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
m.witskies.click |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
crl.identrust.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
new.f0c4.gq |
| suspicious |
w8tu.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .gq Domain |
1548 | iexplore.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.gq) in TLS SNI |
1548 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.gq) |
2956 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.gq) |
1548 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.gq) |
2956 | iexplore.exe | Potentially Bad Traffic | ET INFO Observed Let's Encrypt Certificate for Suspicious TLD (.gq) |