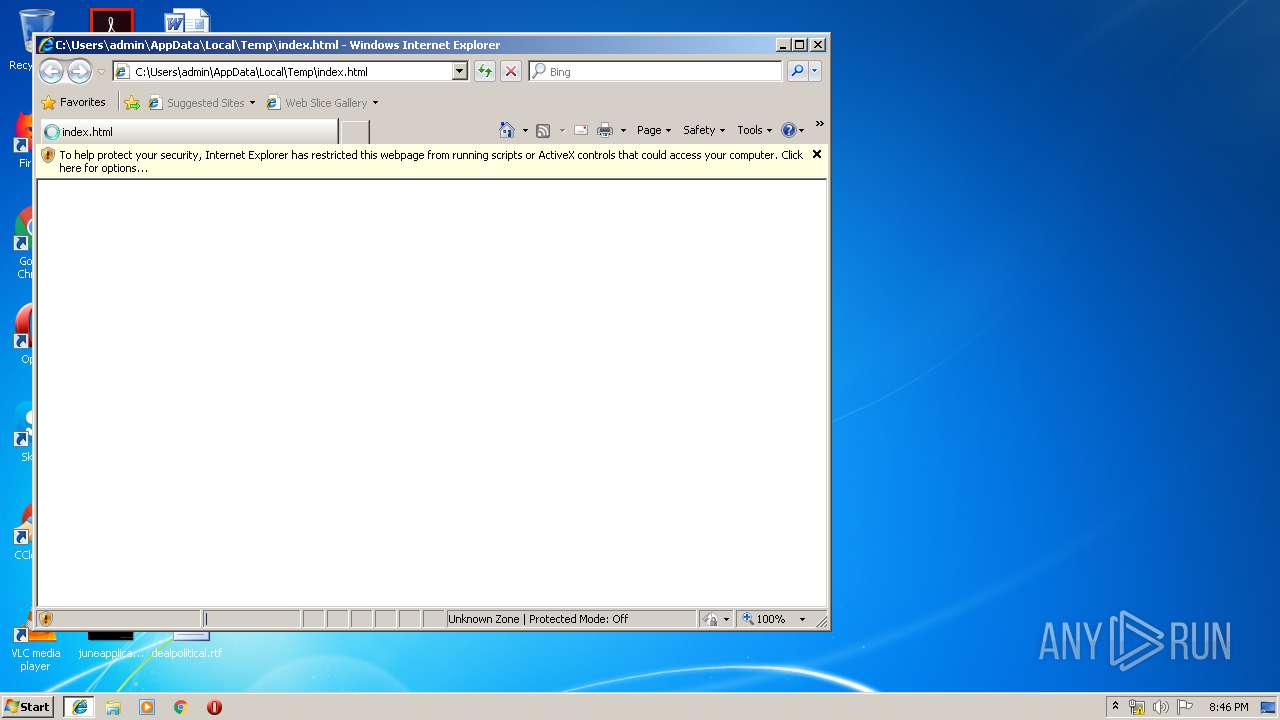
| download: | index.html |
| Full analysis: | https://app.any.run/tasks/5d75fa52-b9bd-4a27-946a-619db6cad271 |
| Verdict: | No threats detected |
| Analysis date: | July 12, 2019, 19:45:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | 1386F676874D8E710C1B1AD95FA9EDD4 |
| SHA1: | 126B8901CF1EE6F8AC7210F034F057CCD0E0BCD5 |
| SHA256: | D647FEDF347C03CB8A794D6A782137EE3CC10F17985CCD660E6F228B00026077 |
| SSDEEP: | 768:xCR9ATqM01yKy668EpxKo2RoHctDJuDThR10HhMrxk5:xiATqNOD66k5 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Creates files in the user directory
- iexplore.exe (PID: 3684)
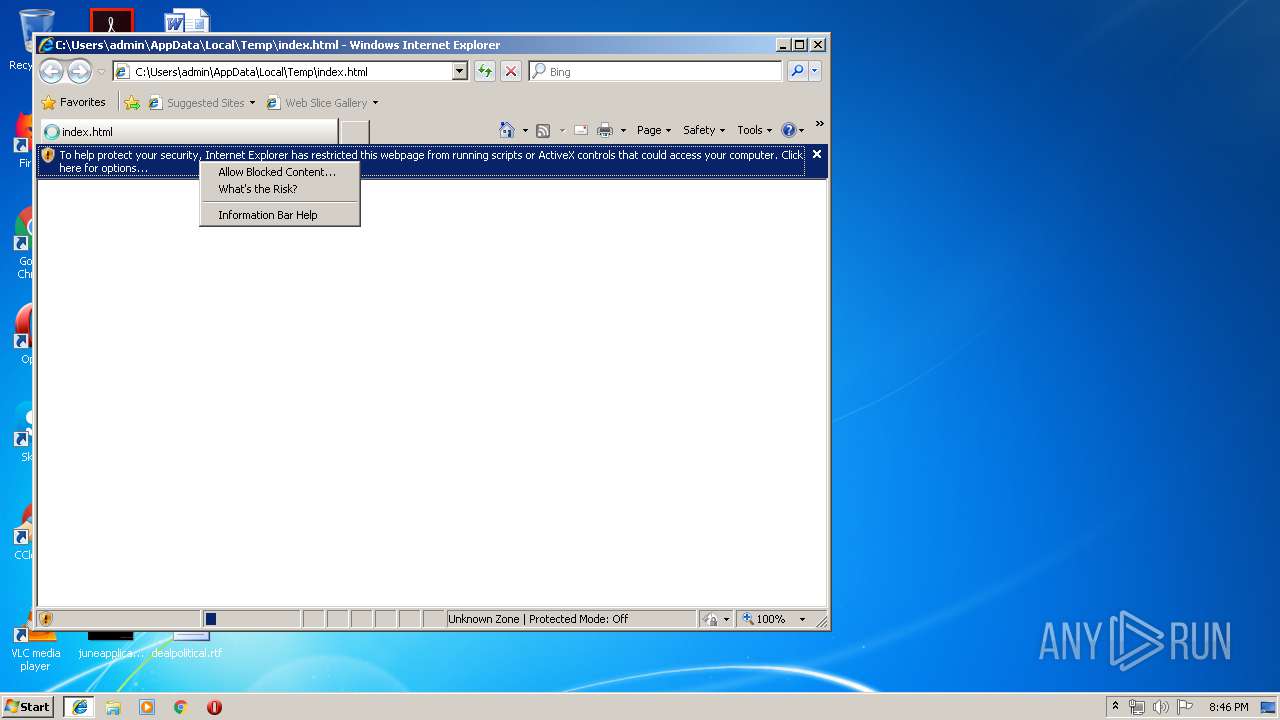
Changes internet zones settings
- iexplore.exe (PID: 3284)
Reads internet explorer settings
- iexplore.exe (PID: 3684)
Reads Internet Cache Settings
- iexplore.exe (PID: 3684)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| hostVerification: | 94c0cf273eafb7eabb41e944d4f52757 |
|---|---|
| rapidgator: | 8f3b9e2b30401bd612046ceabf6586d2648460ad |
| viewport: | width=device-width, initial-scale=1 |
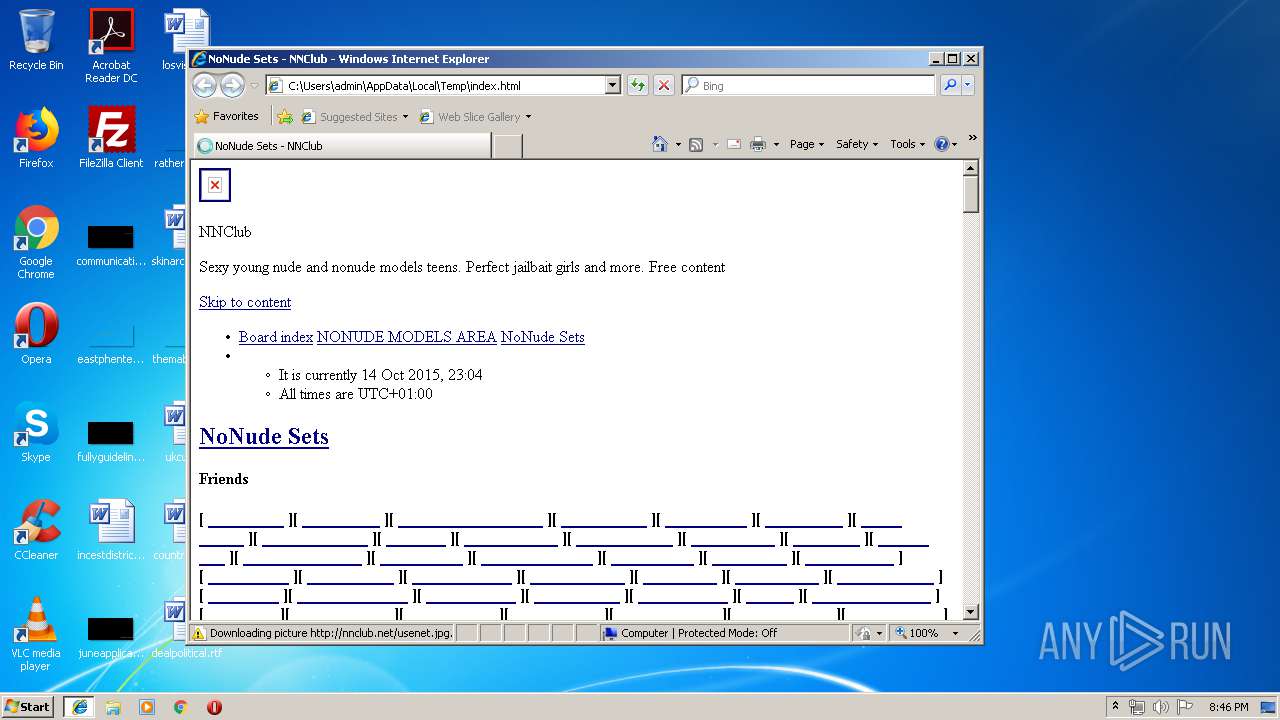
| Title: | NoNude Sets - NNClub |
Total processes
36
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3284 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\index.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3684 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3284 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
350
Read events
286
Write events
63
Delete events
1
Modification events
| (PID) Process: | (3284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000078000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {B111626B-A4DD-11E9-95C0-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (3284) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307070005000C0013002E000800DF03 | |||
Executable files
0
Suspicious files
0
Text files
8
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3284 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3284 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3684 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@~~local~~[1].txt | — | |
MD5:— | SHA256:— | |||
| 3684 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@~~local~~[2].txt | text | |
MD5:02C341FFA800572754BD24C76336CE36 | SHA256:1C293D73B7E95D67C1292F0805C38087EE9FA80383D82760FA3E0A48488C826D | |||
| 3684 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\css[2].txt | text | |
MD5:09EFB688CA4B241F22192BE535C208A4 | SHA256:3050BEC5250A119E3FEDD8BD5057BCA356B231DA5C58B696674D8AD6D0144D43 | |||
| 3684 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\css[3].txt | text | |
MD5:F9B30984A517EC8C099831668862E059 | SHA256:DA5C4E1B7A85B95A3EB235DCC85F334F61B611A4CD363A2059BF3528413072AB | |||
| 3684 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\_gP_1RrxsjcxVyin9l9n_j2hTd5y[1].eot | eot | |
MD5:B8B0EB7971D95D167EA3E5BD09D82BE7 | SHA256:CD1083D5613A650770134EAE2798EB0F4E4F3721F8D23D4EBD54403C59567D76 | |||
| 3684 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\3y976aknfjLm_3lMKjiMgmUUYBs04Y8VH-4[1].eot | eot | |
MD5:E91B4BBDC1B78D52289EDF6E3A604DE5 | SHA256:B6FECB29F3DD072DF541A4E83D71C1568E7749E5C4432F82B641448C854A8185 | |||
| 3684 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\tss0ApVBdCYD5Q7hcxTE1ArZ0bb-iXg[1].eot | eot | |
MD5:65447BB5C1EBF5608034C64934E72700 | SHA256:29E24745B5453EE8754CEF954A3E461B86EDEB9C2785F05D8B520559235366EB | |||
| 3684 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\css[1].txt | text | |
MD5:0569A6A6BC2895536B064AD428110304 | SHA256:1BFE2A9BE3CE8138A53AC1762D63DD30F6DAC1456D5BF48821F540B624DEAC3A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
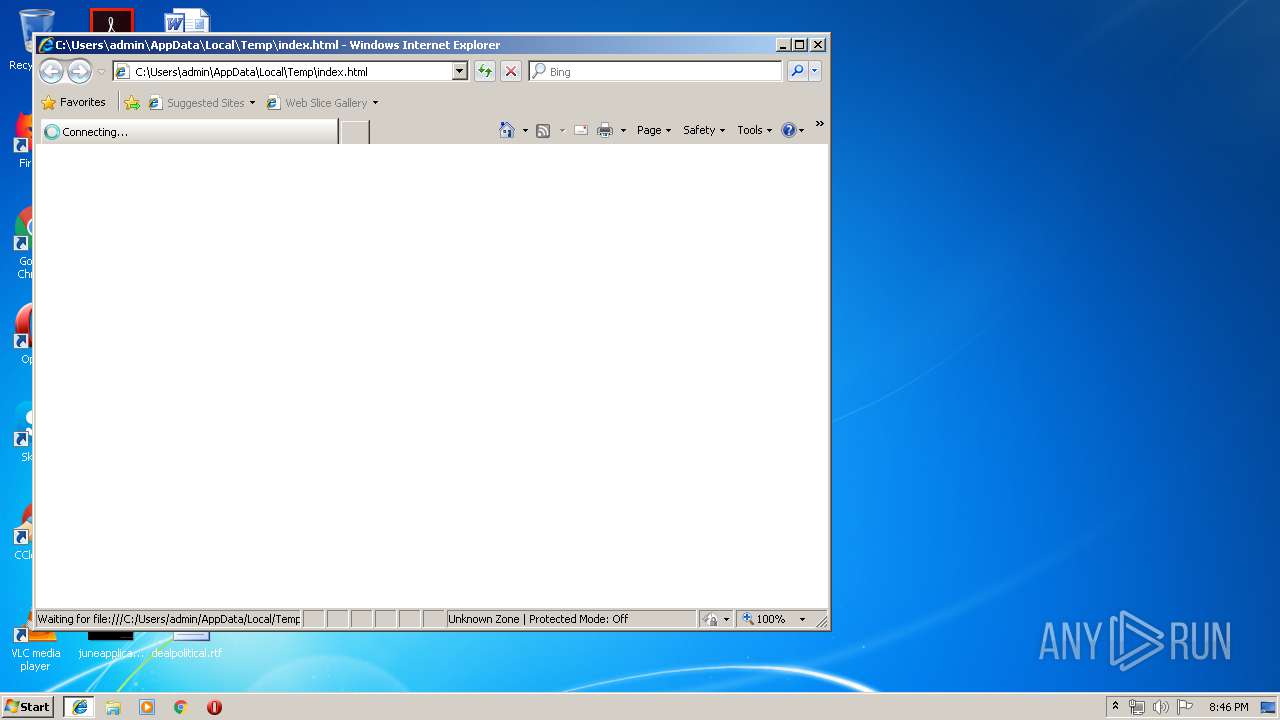
HTTP(S) requests
10
TCP/UDP connections
17
DNS requests
11
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3684 | iexplore.exe | GET | 200 | 18.208.5.78:80 | http://t1.extreme-dm.com/f.js | US | text | 2.37 Kb | suspicious |
3684 | iexplore.exe | GET | 200 | 172.217.16.138:80 | http://fonts.googleapis.com/css?family=Acme&subset=latin,latin-ext | US | text | 154 b | whitelisted |
3684 | iexplore.exe | GET | 200 | 216.58.210.3:80 | http://fonts.gstatic.com/s/archivonarrow/v9/tss0ApVBdCYD5Q7hcxTE1ArZ0bb-iXg.eot | US | eot | 27.3 Kb | whitelisted |
3684 | iexplore.exe | GET | 200 | 216.58.210.3:80 | http://fonts.gstatic.com/s/yanonekaffeesatz/v10/3y976aknfjLm_3lMKjiMgmUUYBs04Y8VH-4.eot | US | eot | 25.8 Kb | whitelisted |
3684 | iexplore.exe | GET | 200 | 216.58.210.3:80 | http://fonts.gstatic.com/s/acme/v8/RrQfboBx-C5_XxrBag.eot | US | eot | 8.85 Kb | whitelisted |
3684 | iexplore.exe | GET | 200 | 216.58.210.3:80 | http://fonts.gstatic.com/s/luckiestguy/v9/_gP_1RrxsjcxVyin9l9n_j2hTd5y.eot | US | eot | 20.4 Kb | whitelisted |
3684 | iexplore.exe | GET | 200 | 172.217.16.138:80 | http://fonts.googleapis.com/css?family=Luckiest+Guy | US | text | 169 b | whitelisted |
3684 | iexplore.exe | GET | 200 | 172.217.16.138:80 | http://fonts.googleapis.com/css?family=Archivo+Narrow&subset=latin,latin-ext | US | text | 176 b | whitelisted |
3684 | iexplore.exe | GET | 200 | 172.217.16.138:80 | http://fonts.googleapis.com/css?family=Yanone+Kaffeesatz:400,700&subset=latin,latin-ext | US | text | 180 b | whitelisted |
3684 | iexplore.exe | GET | 200 | 194.9.70.35:80 | http://nnclub.net/usenet.jpg | UA | image | 29.8 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 23.210.248.44:445 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
3284 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 23.210.248.44:137 | s7.addthis.com | Akamai International B.V. | NL | whitelisted |
3684 | iexplore.exe | 172.217.16.138:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3684 | iexplore.exe | 18.208.5.78:80 | t1.extreme-dm.com | — | US | suspicious |
3684 | iexplore.exe | 216.58.210.3:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3684 | iexplore.exe | 194.9.70.35:80 | nnclub.net | Global Technology Ukraine Ltd | UA | unknown |
4 | System | 18.208.5.78:445 | t1.extreme-dm.com | — | US | suspicious |
4 | System | 18.208.5.78:139 | t1.extreme-dm.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
s7.addthis.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
nnclub.net |
| unknown |
t1.extreme-dm.com |
| suspicious |
fonts.gstatic.com |
| whitelisted |
e0.extreme-dm.com |
| suspicious |
dns.msftncsi.com |
| shared |