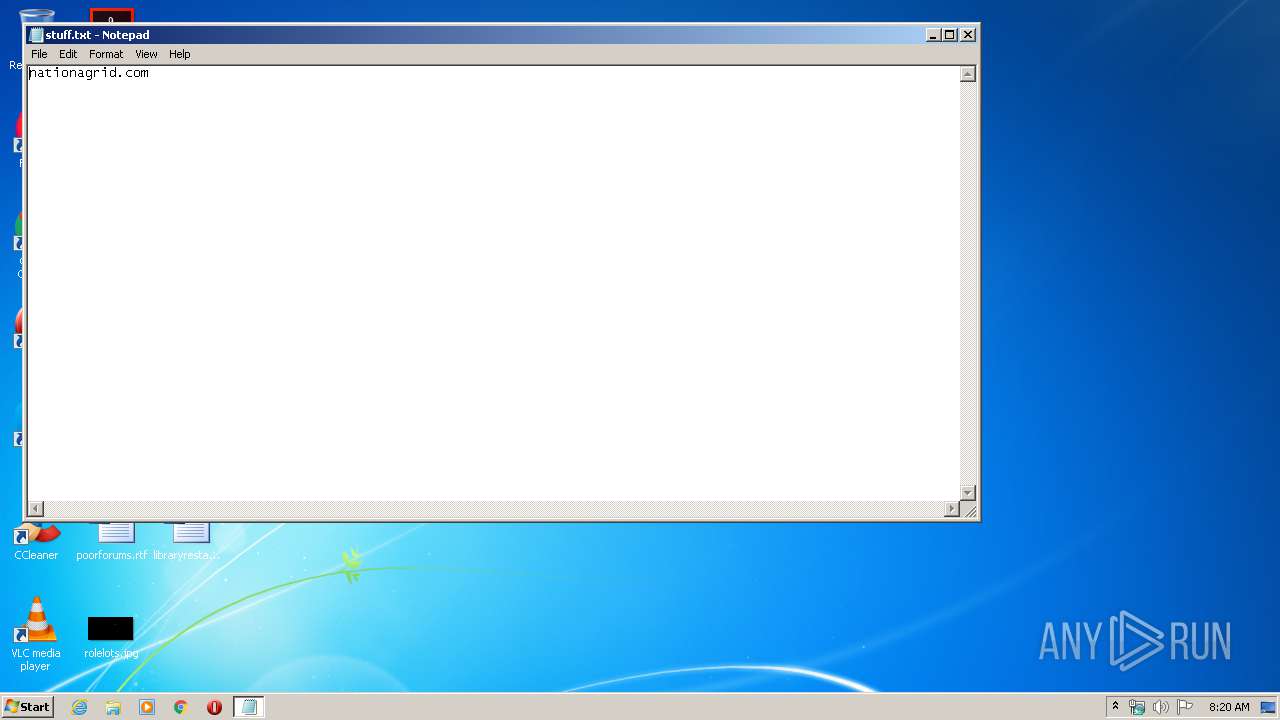
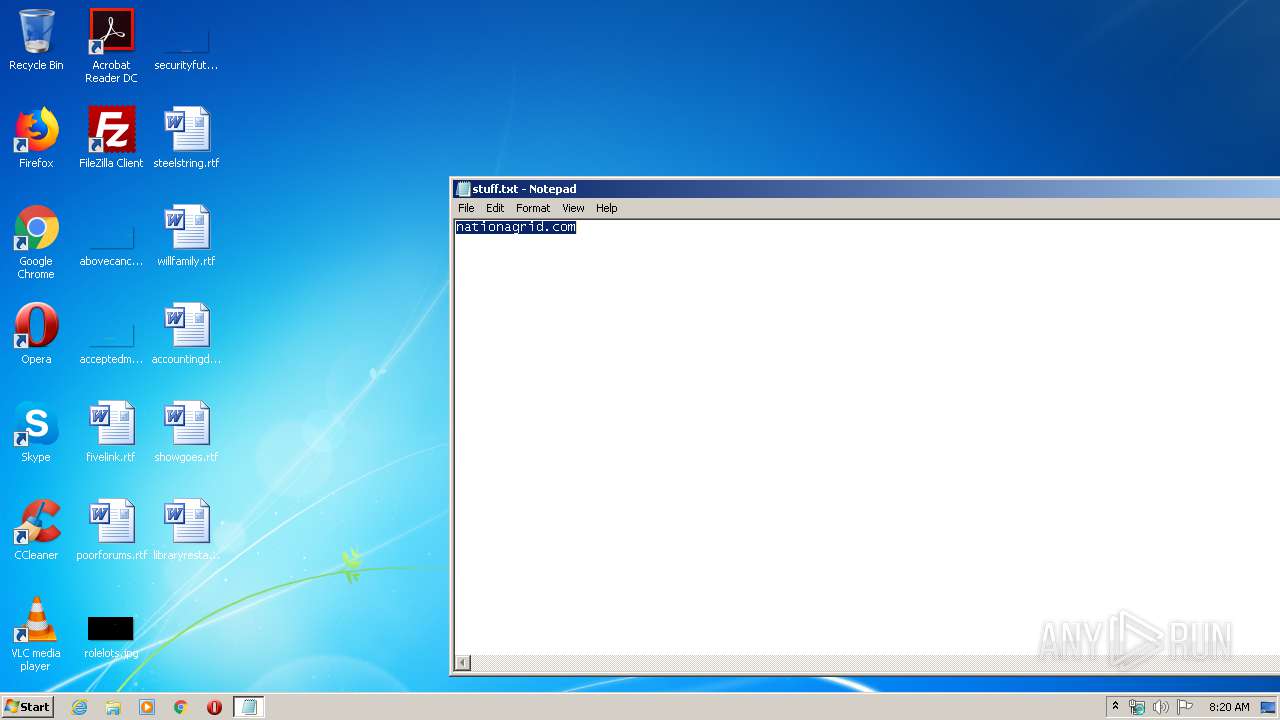
| File name: | stuff.txt |
| Full analysis: | https://app.any.run/tasks/f274cd0a-8e7a-4b22-a3f2-afe06bc8c8df |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2020, 08:20:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | E67C34A59988FE0EC2C0E9F092DCE726 |
| SHA1: | 4135DBA7E7302D744FCA2A48F379A349FB92EAB9 |
| SHA256: | D646ABF7F385470B4AC2D4DE59620938015448D4EA640CB0407283B28B06F08E |
| SSDEEP: | 3:FQDEI:FQt |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2720)
INFO
Reads the hosts file
- chrome.exe (PID: 2720)
- chrome.exe (PID: 1912)
Application launched itself
- chrome.exe (PID: 2720)
Manual execution by user
- chrome.exe (PID: 2720)
Reads settings of System Certificates
- chrome.exe (PID: 1912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
71
Monitored processes
35
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,2309581278961602872,12412976974999127366,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4377831180439619316 --mojo-platform-channel-handle=3424 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,2309581278961602872,12412976974999127366,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11577238721748801574 --mojo-platform-channel-handle=4780 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1064 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,2309581278961602872,12412976974999127366,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1548277366246491632 --mojo-platform-channel-handle=3320 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,2309581278961602872,12412976974999127366,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12286604202887887816 --mojo-platform-channel-handle=4176 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1008,2309581278961602872,12412976974999127366,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6066737035401125829 --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,2309581278961602872,12412976974999127366,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3731183487374862669 --mojo-platform-channel-handle=1636 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,2309581278961602872,12412976974999127366,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6262336142197148631 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1944 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,2309581278961602872,12412976974999127366,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12631248625419497224 --mojo-platform-channel-handle=4588 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1948 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,2309581278961602872,12412976974999127366,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14559694750012213529 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2444 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2012 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,2309581278961602872,12412976974999127366,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12071507290439053341 --mojo-platform-channel-handle=2364 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
805
Read events
721
Write events
79
Delete events
5
Modification events
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2720-13226833250525500 |
Value: 259 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (2720) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
37
Text files
245
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E50E463-AA0.pma | — | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\b5fd938b-a319-4334-a206-80d1b7e447f5.tmp | — | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa6819c.TMP | text | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa681ea.TMP | text | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2720 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa68390.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
29
DNS requests
24
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
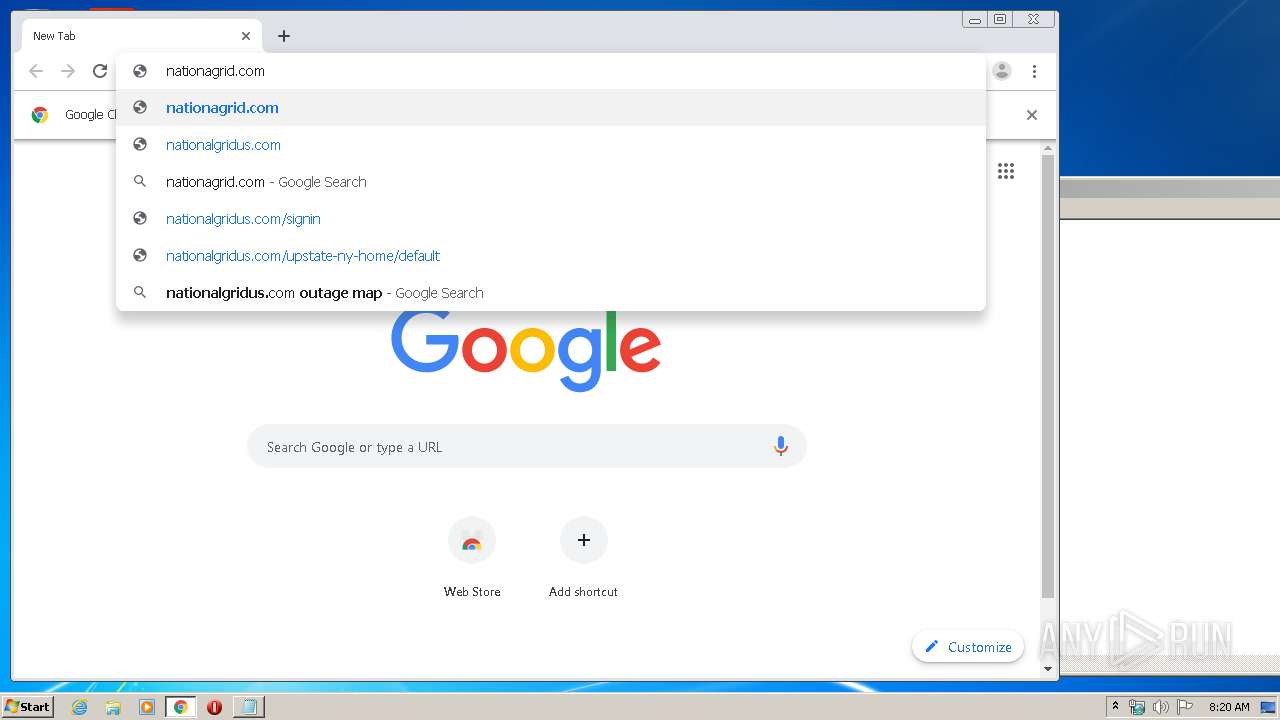
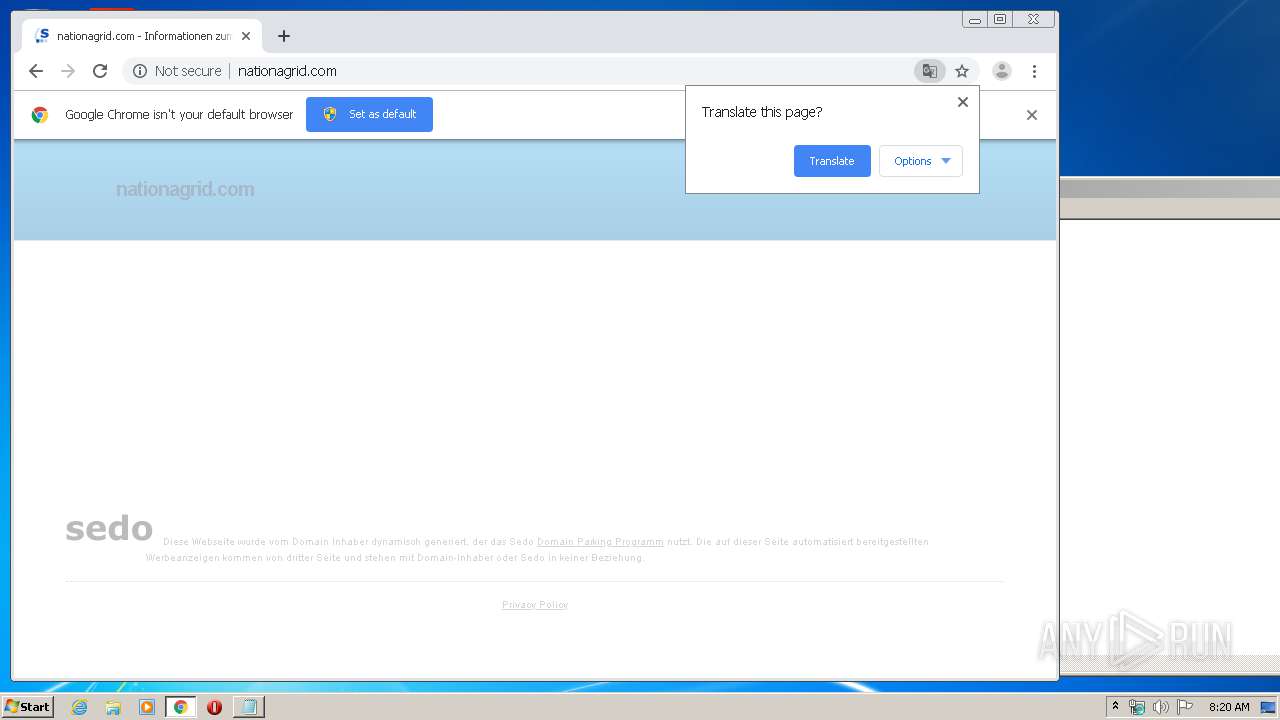
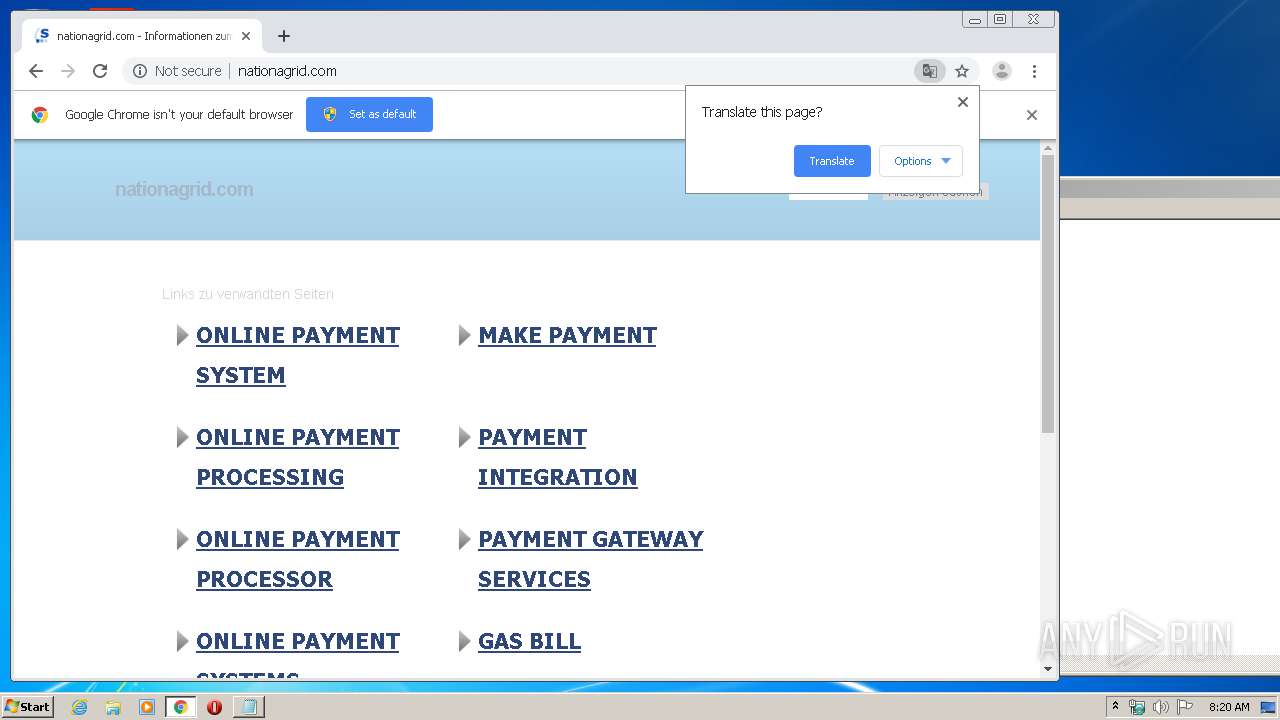
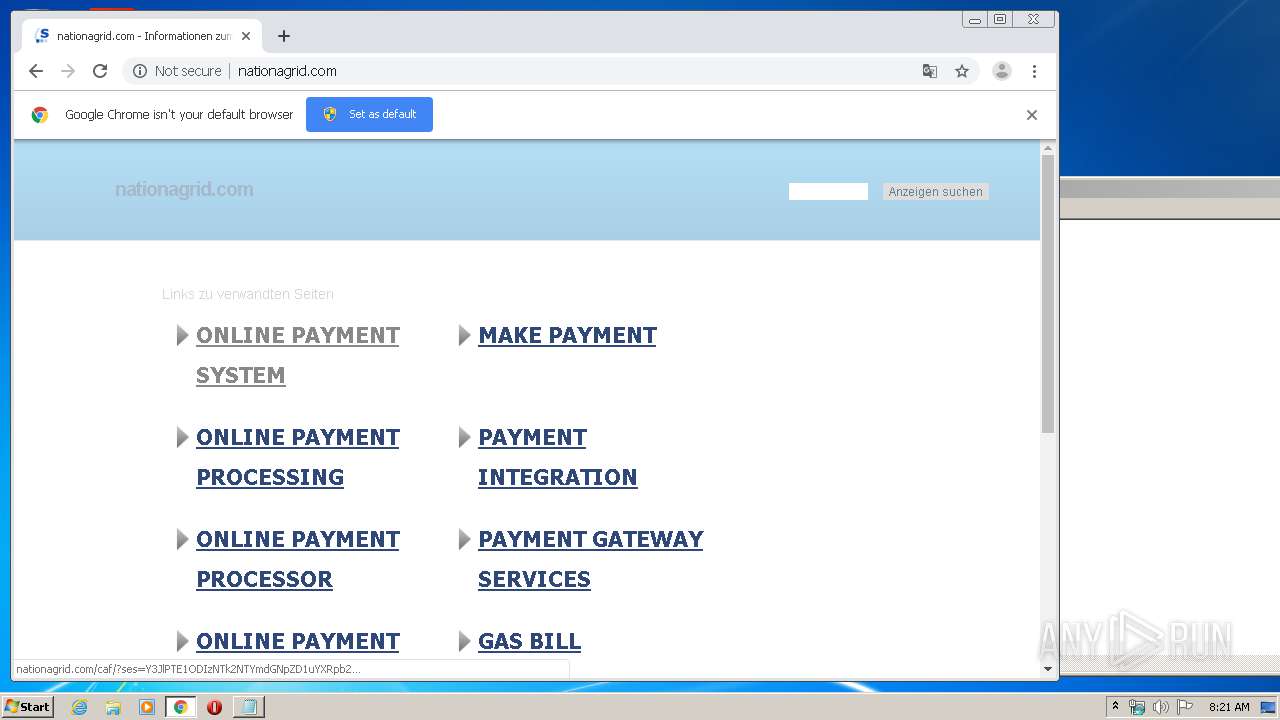
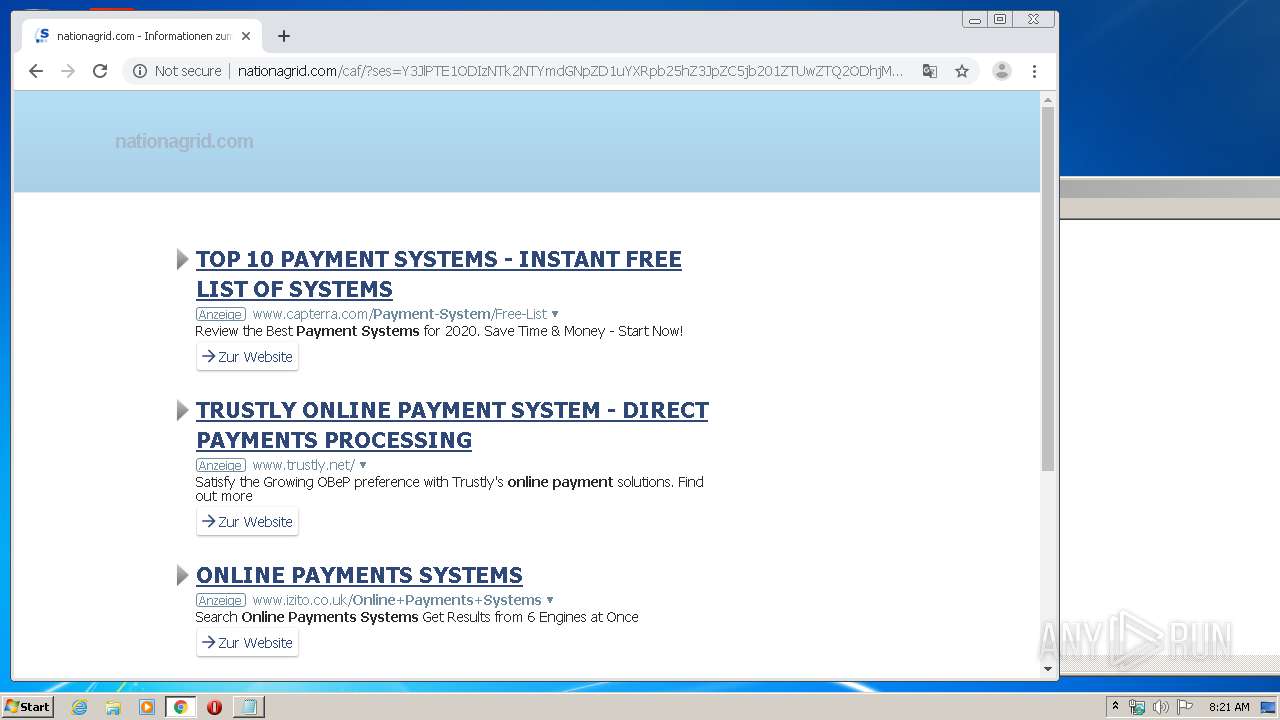
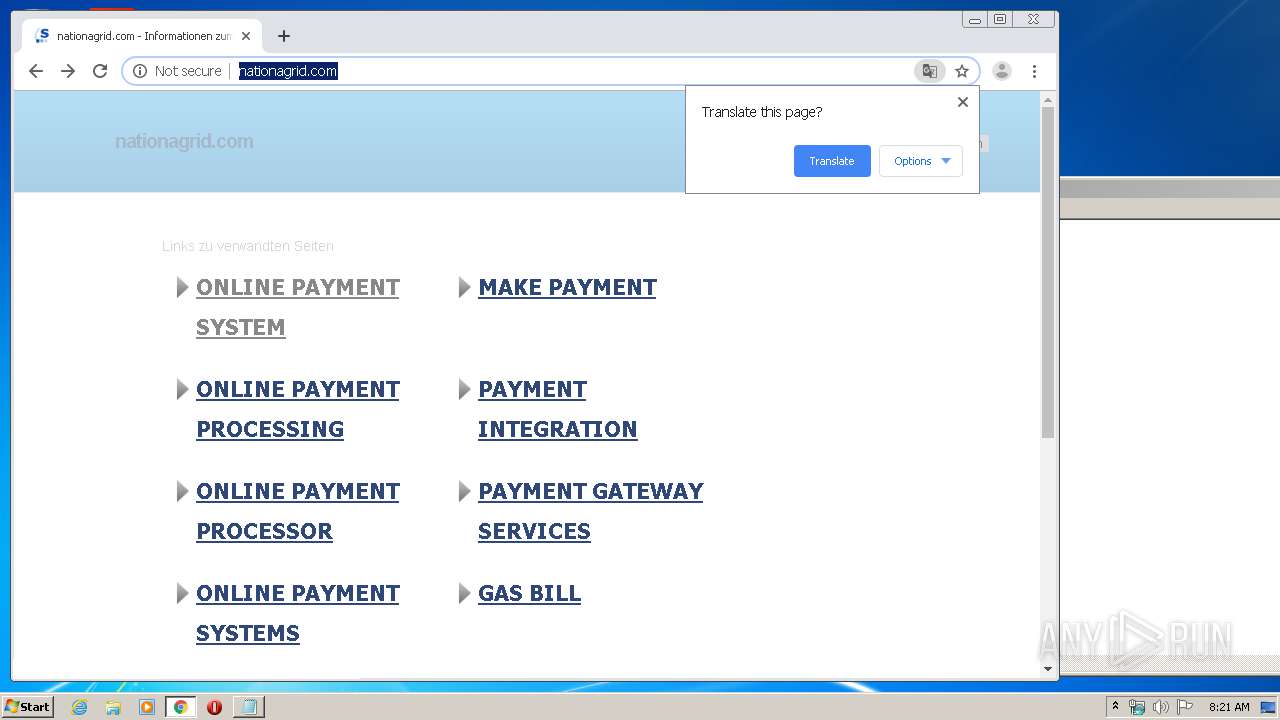
1912 | chrome.exe | GET | 200 | 91.195.240.126:80 | http://nationagrid.com/caf/?ses=Y3JlPTE1ODIzNTk2NzAmdGNpZD1uYXRpb25hZ3JpZC5jb201ZTUwZTQ3NjY3MjZhOS40NTk2OTIwOSZ0YXNrPXNlYXJjaCZkb21haW49bmF0aW9uYWdyaWQuY29tJmxhbmd1YWdlPWRlJmFfaWQ9MyZzZXNzaW9uPVRoRXFzQ1NtbnkwOTU2bkpXa0J2&query=Payment%20Processor&afdToken=3B1g40CzXrL0rSD0wvTMNSmShKxA02kUtpphrX-C4znd-_jsx7ZSGY-lo8FsNatPY3IiClztXgWBxL0R3d9tCgqCwHI0P4mPSeszuaqEUGs | DE | html | 21.6 Kb | malicious |
1912 | chrome.exe | GET | 200 | 91.195.240.126:80 | http://nationagrid.com/search/tsc.php?200=MjAyMzc5MjE4&21=NDUuNDEuMTM4LjIwNA==&681=MTU4MjM1OTY3MDhmNThiOGE4YzdjZDA1NTIzMTAxYTdhZDRlNjQzZWYw&crc=983ddec8ff2f50f1f2b7fef961f128e5c2e1189b&cv=1 | DE | compressed | 21.6 Kb | malicious |
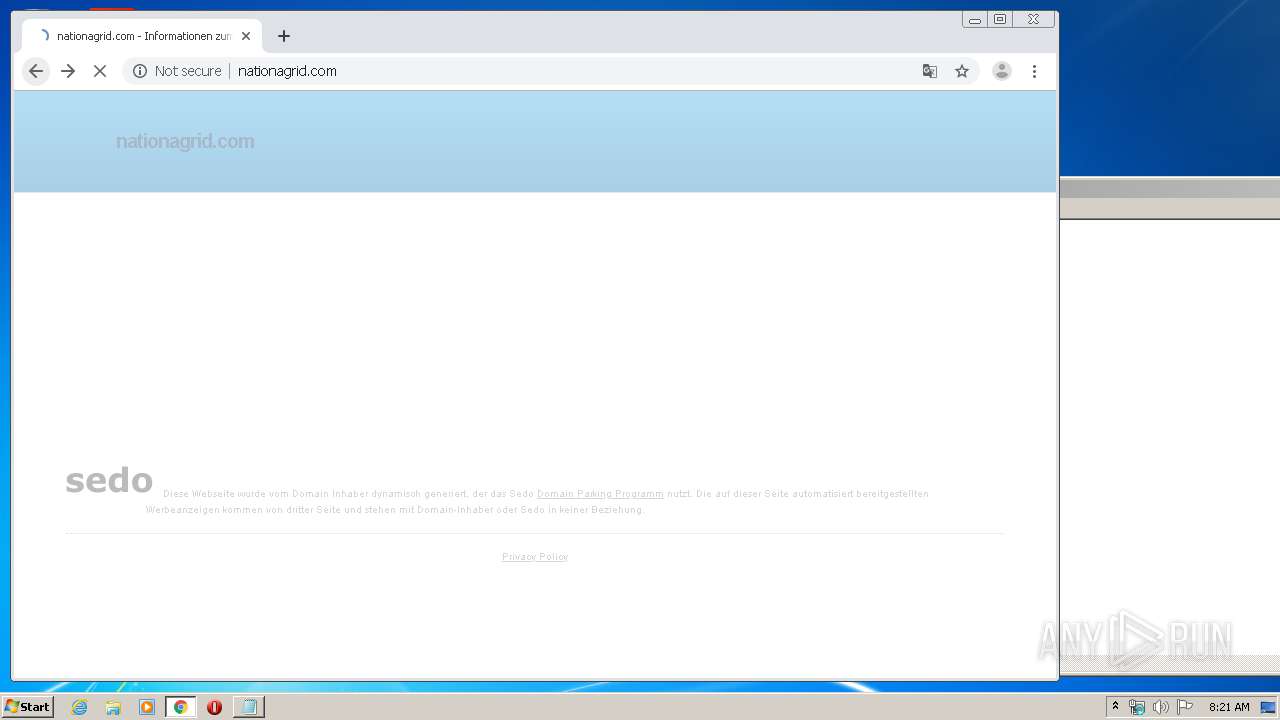
1912 | chrome.exe | GET | 200 | 91.195.240.126:80 | http://nationagrid.com/ | DE | html | 21.5 Kb | malicious |
1912 | chrome.exe | GET | 200 | 91.195.240.126:80 | http://nationagrid.com/search/tsc.php?200=MjAyMzc5MjE4&21=NDUuNDEuMTM4LjIwNA==&681=MTU4MjM1OTY1NmZhNTY2Y2FlYzJiMjZiNDk5ZjFmNDY3ZmJhYWM2OGVh&crc=c67451922336a08bfbf8f491f228fac09a22b4ea&cv=1 | DE | compressed | 21.5 Kb | malicious |
1912 | chrome.exe | GET | 200 | 91.195.240.126:80 | http://nationagrid.com/ | DE | html | 21.6 Kb | malicious |
1912 | chrome.exe | GET | 200 | 91.195.240.126:80 | http://nationagrid.com/ | DE | html | 21.5 Kb | malicious |
1912 | chrome.exe | GET | 200 | 91.195.240.126:80 | http://nationagrid.com/search/tsc.php?200=MjAyMzc5MjE4&21=NDUuNDEuMTM4LjIwNA==&681=MTU4MjM1OTY3NTNjMTFkYzNkNDhkY2I3MTU1NTFhZmM2ZmFiYjk5NjI2&crc=989434858e2030514f01c5844c34a6c75e3b0451&cv=1 | DE | compressed | 21.5 Kb | malicious |
1912 | chrome.exe | GET | 200 | 205.234.175.175:80 | http://img.sedoparking.com/templates/brick_gfx/common/logo_2016_bbbbbb.svg | US | image | 2.02 Kb | whitelisted |
1912 | chrome.exe | GET | 200 | 172.217.16.131:80 | http://www.gstatic.com/domainads/tracking/caf.gif?ts=1582359656552&rid=3816829 | US | image | 43 b | whitelisted |
1912 | chrome.exe | GET | 200 | 195.95.178.206:80 | http://r3---sn-pouxga5o-vu2l.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=45.41.138.204&mm=28&mn=sn-pouxga5o-vu2l&ms=nvh&mt=1582359567&mv=m&mvi=2&pl=24&shardbypass=yes | RO | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1912 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
1912 | chrome.exe | 172.217.23.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1912 | chrome.exe | 172.217.18.10:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1912 | chrome.exe | 172.217.16.131:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1912 | chrome.exe | 172.217.16.142:443 | apis.google.com | Google Inc. | US | whitelisted |
1912 | chrome.exe | 216.58.210.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1912 | chrome.exe | 172.217.22.78:443 | ogs.google.com | Google Inc. | US | whitelisted |
1912 | chrome.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
1912 | chrome.exe | 91.195.240.126:80 | nationagrid.com | SEDO GmbH | DE | malicious |
1912 | chrome.exe | 205.234.175.175:80 | img.sedoparking.com | CacheNetworks, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
www.google.com |
| malicious |
nationagrid.com |
| malicious |