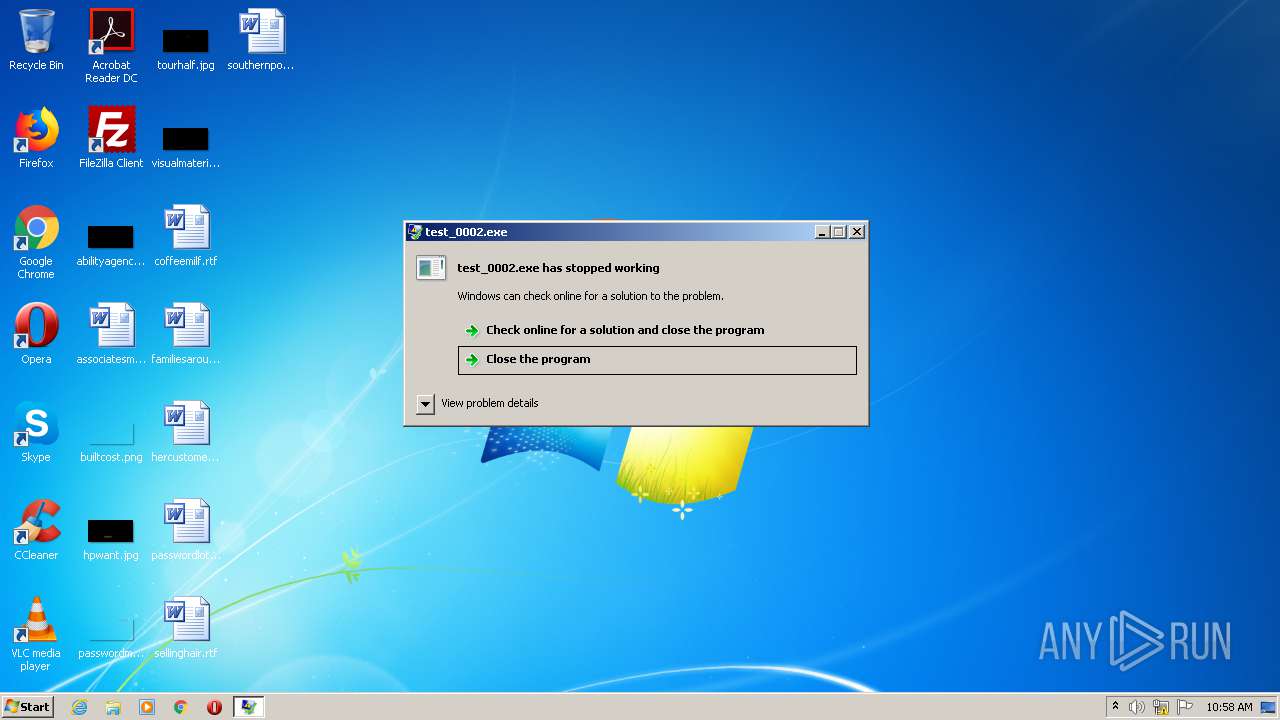
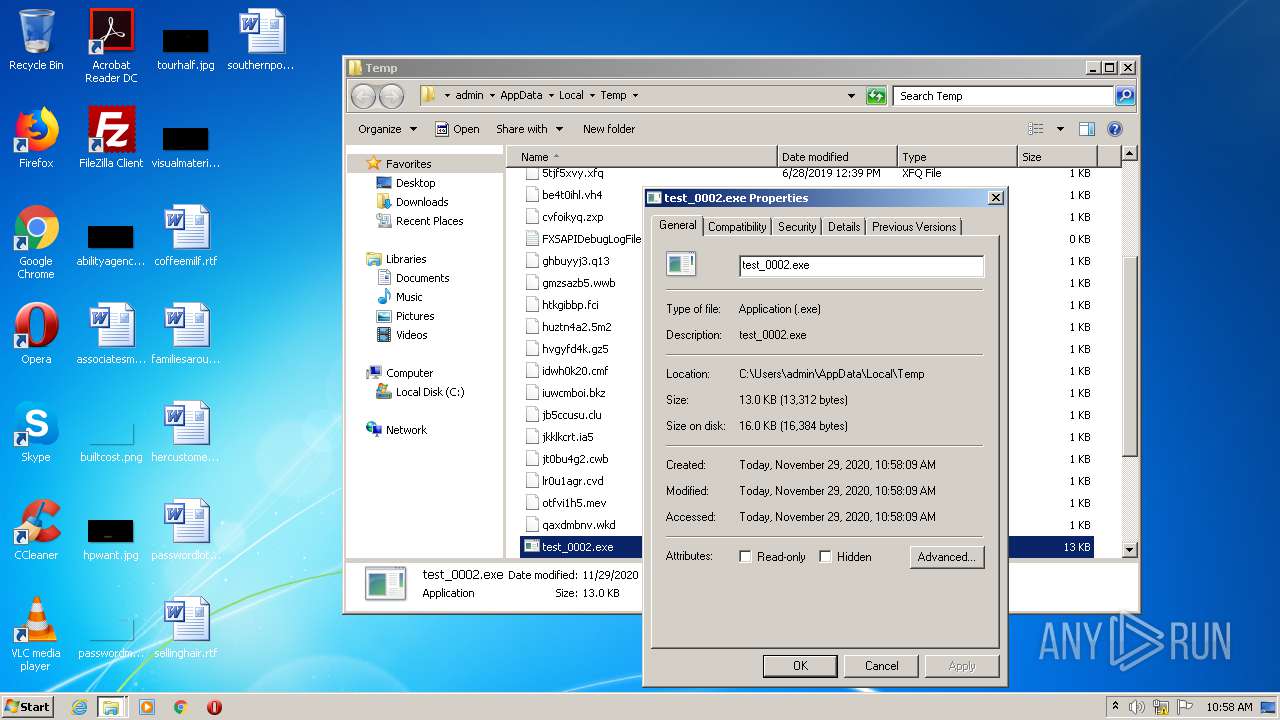
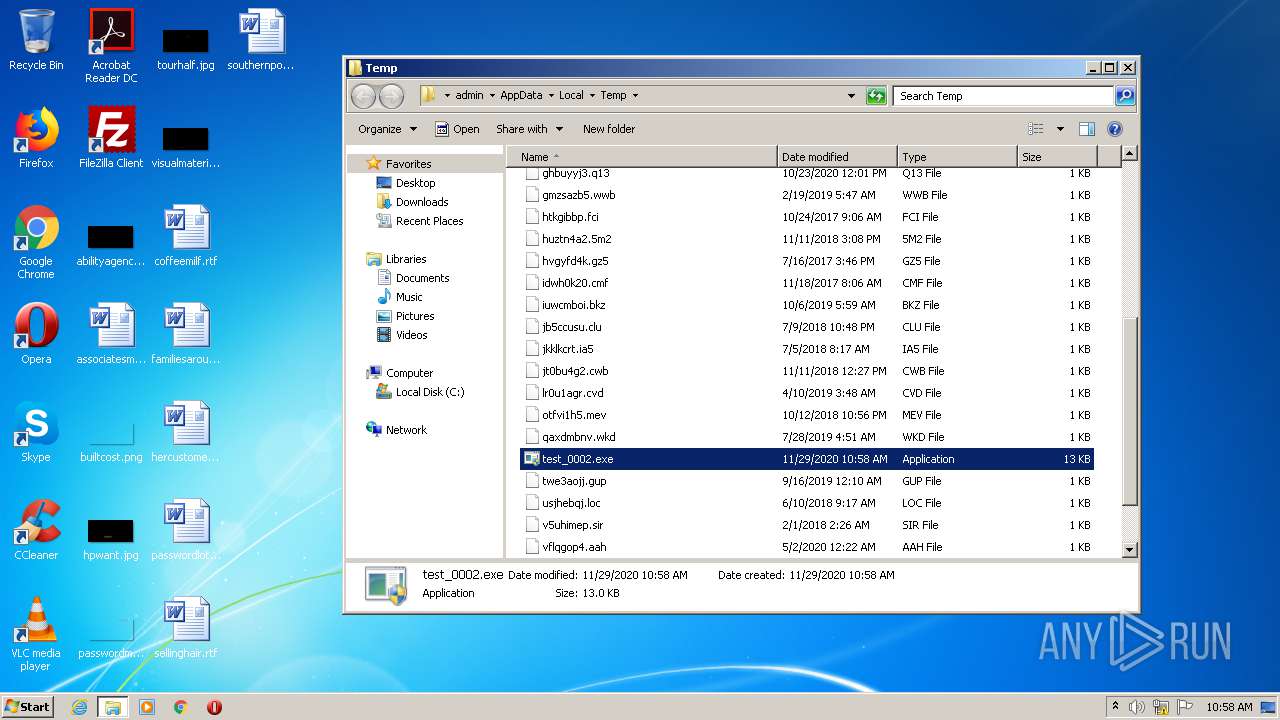
| File name: | test_0002.exe |
| Full analysis: | https://app.any.run/tasks/9221de5c-269f-40a8-b39c-d35ad3fa3ee9 |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 10:57:48 |
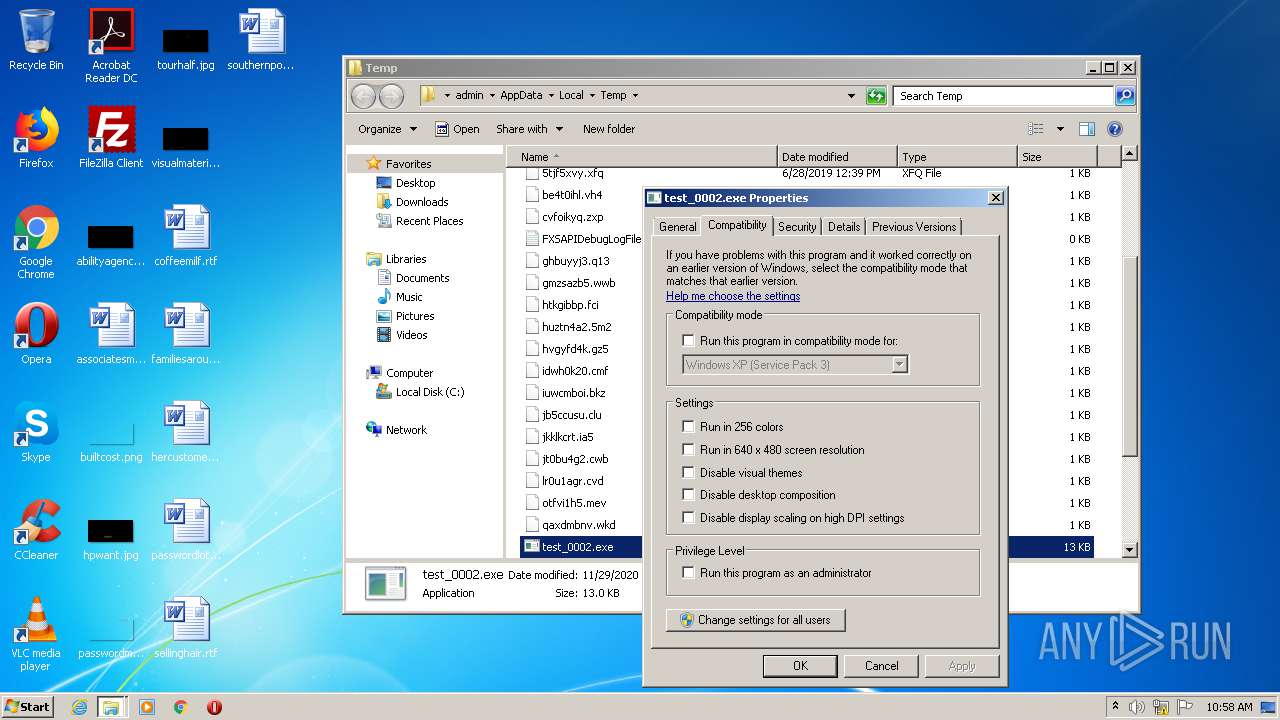
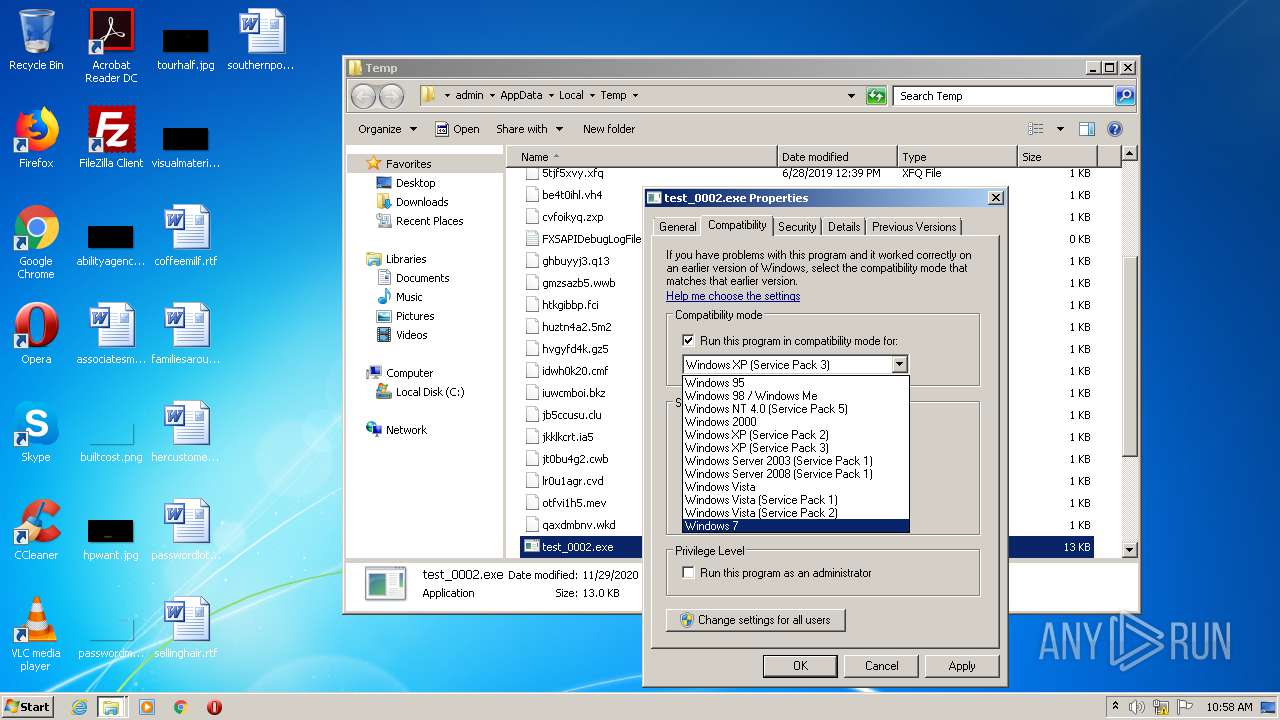
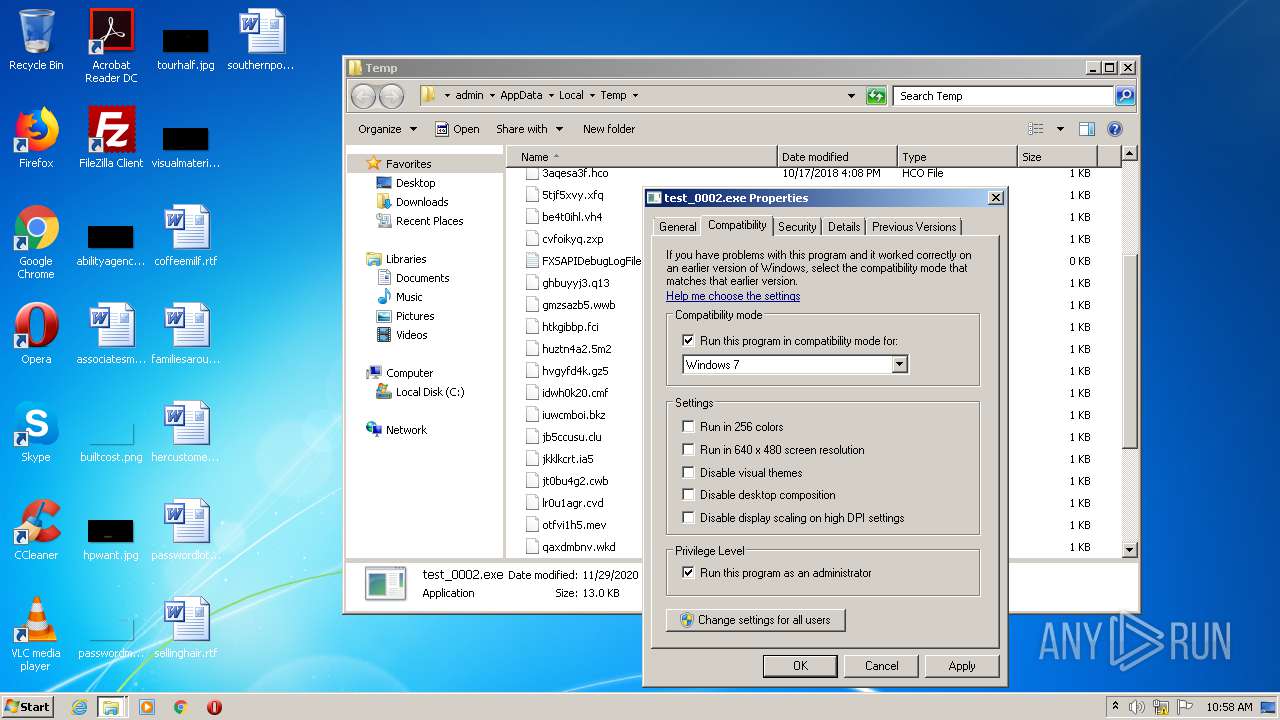
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 7C386DF44A7673B9F04C89B6B490041E |
| SHA1: | 5A8482570FAC0A030059ADB3C886FFDB9FCD4B5A |
| SHA256: | D63DA8876CA2A8423E526118681BC25E0488DE9662B6215C1B2DD354E8F37224 |
| SSDEEP: | 192:6yqBeQTa/oHdZnstvd12ulY5TJnW7A8fus3vlwhzWljM5Qxy6C3O99Z6mqFD:tqAcfnbulsW7Ss/lMU4Ay4 |
MALICIOUS
Changes settings of System certificates
- test_0002.exe (PID: 1840)
- test_0002.exe (PID: 4052)
SUSPICIOUS
Adds / modifies Windows certificates
- test_0002.exe (PID: 1840)
- test_0002.exe (PID: 4052)
INFO
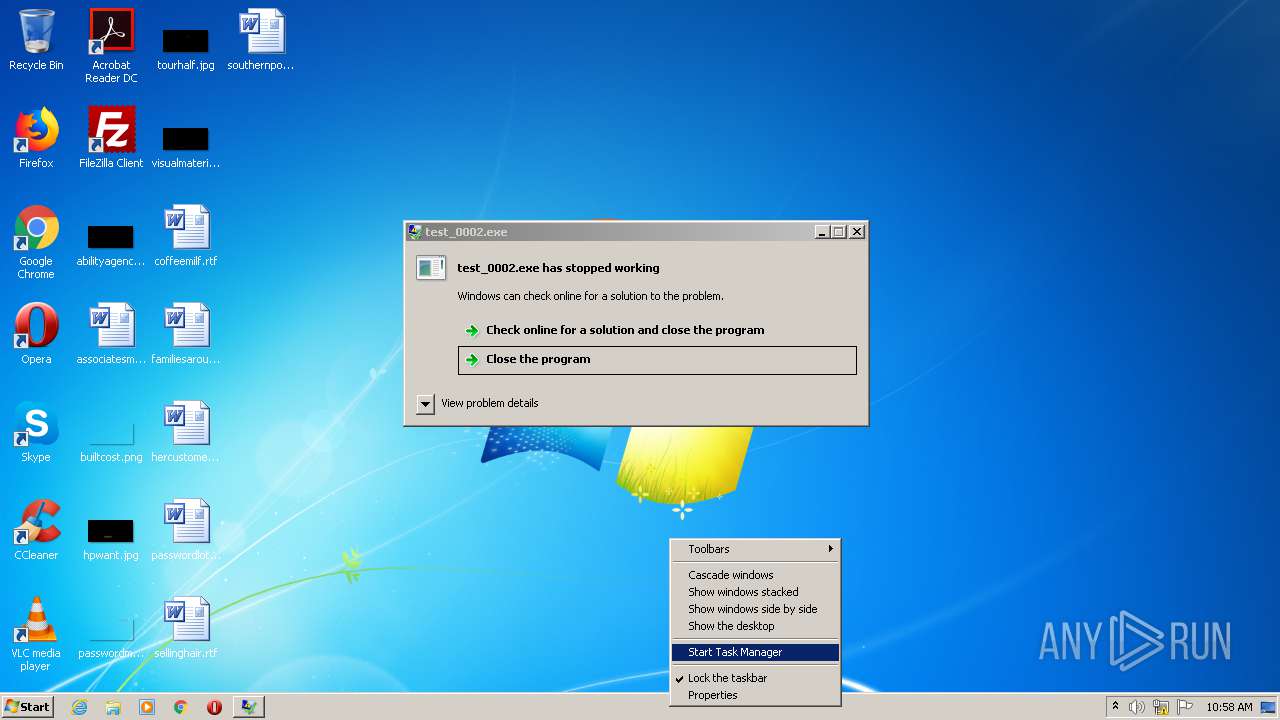
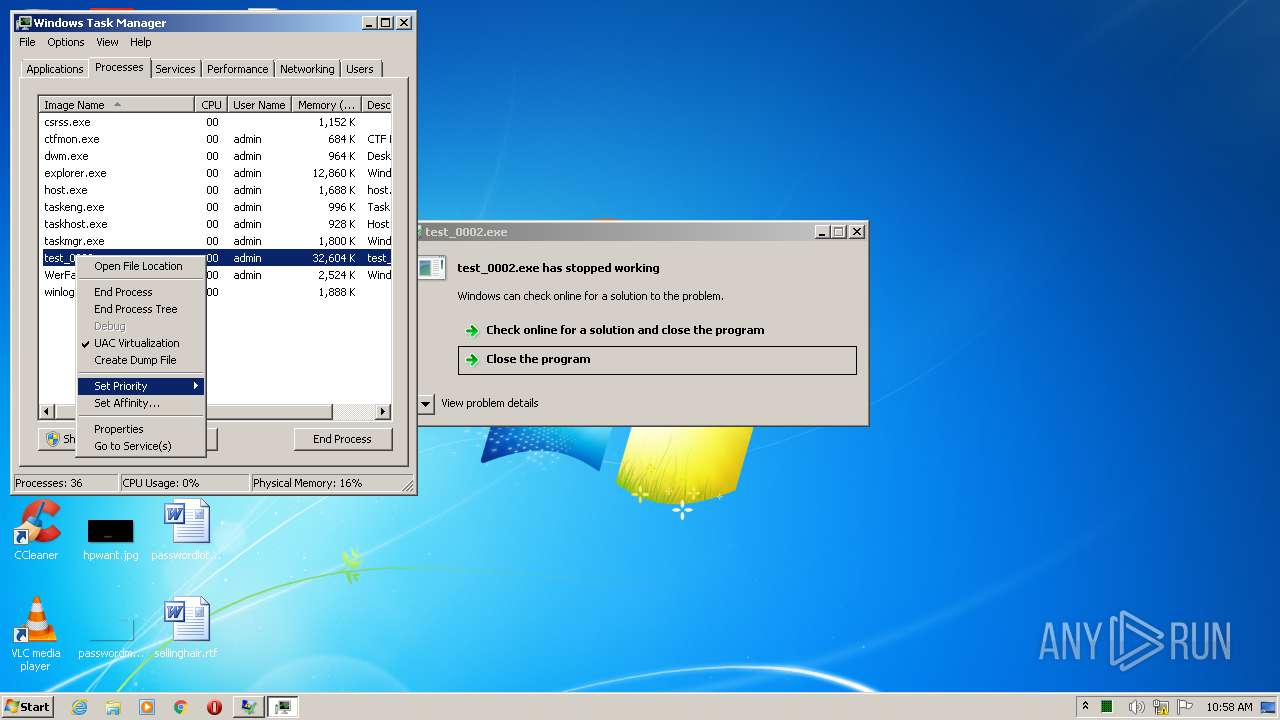
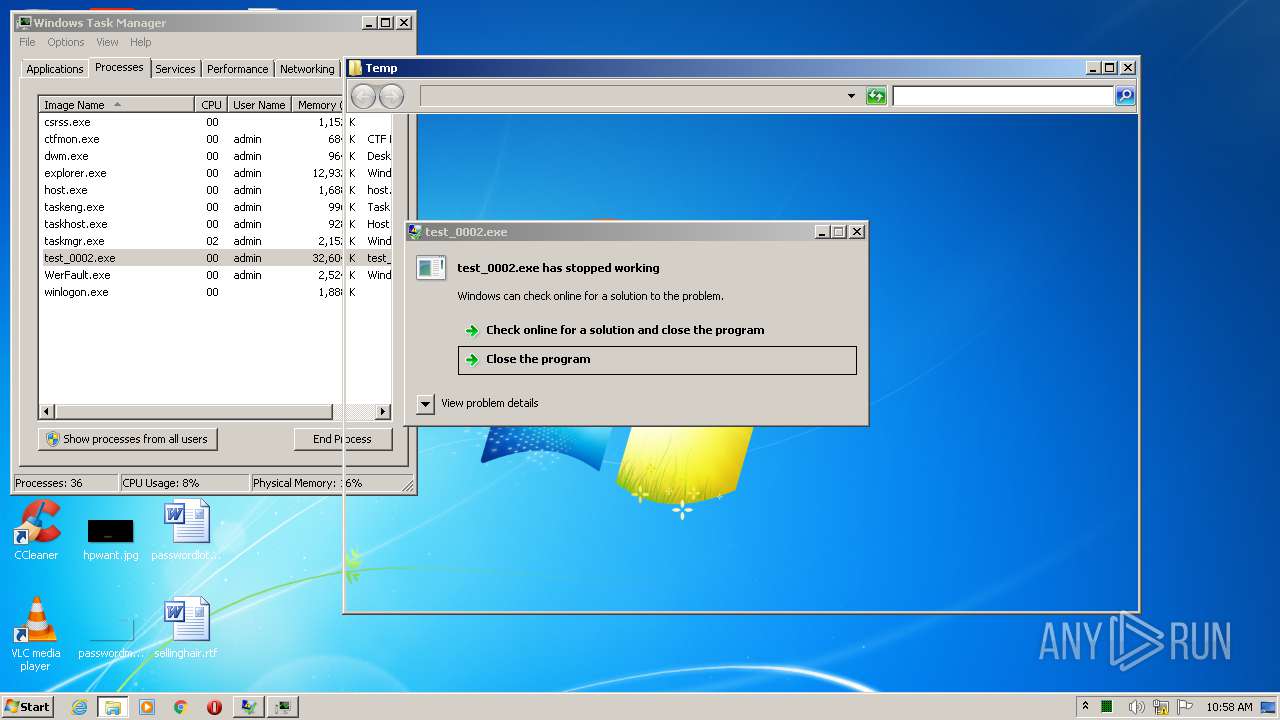
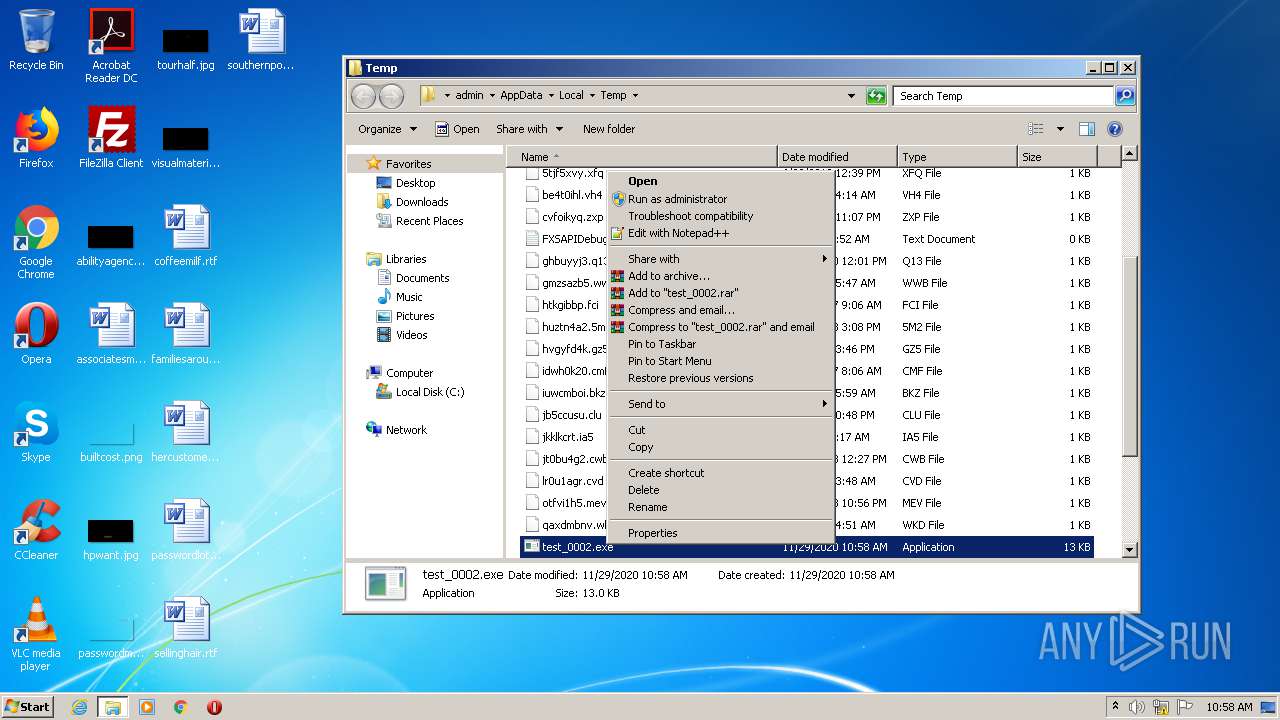
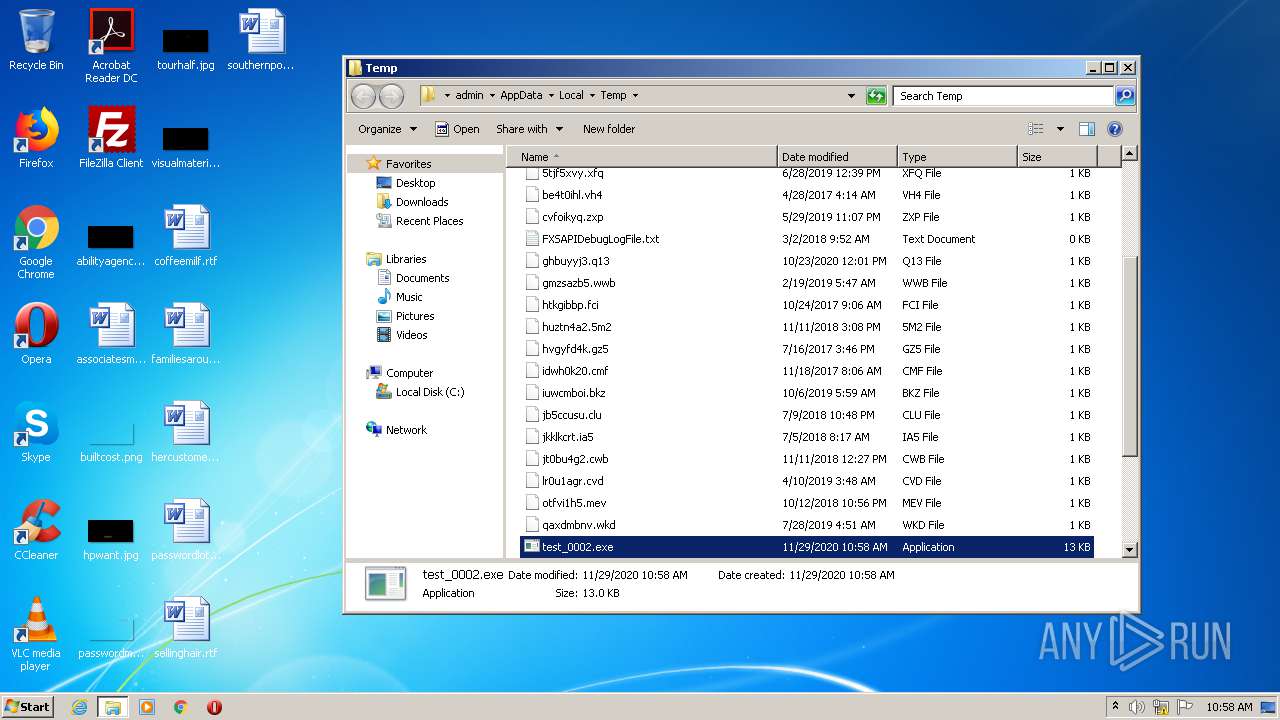
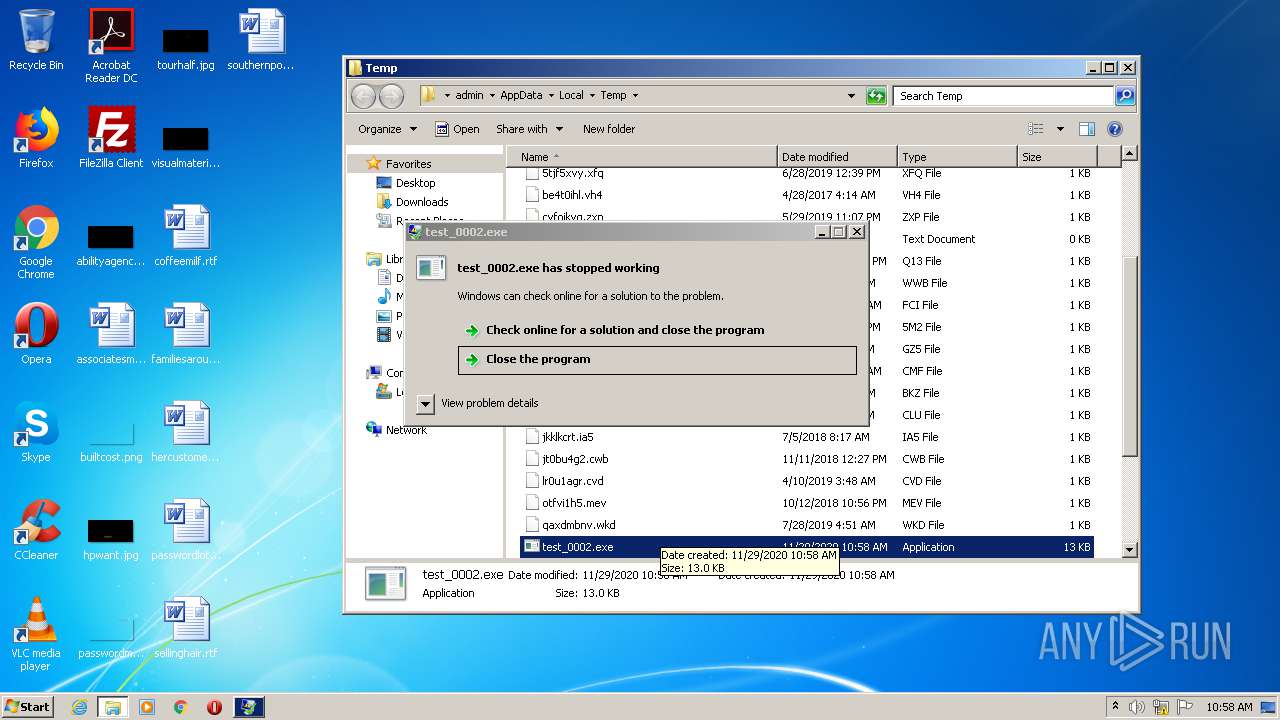
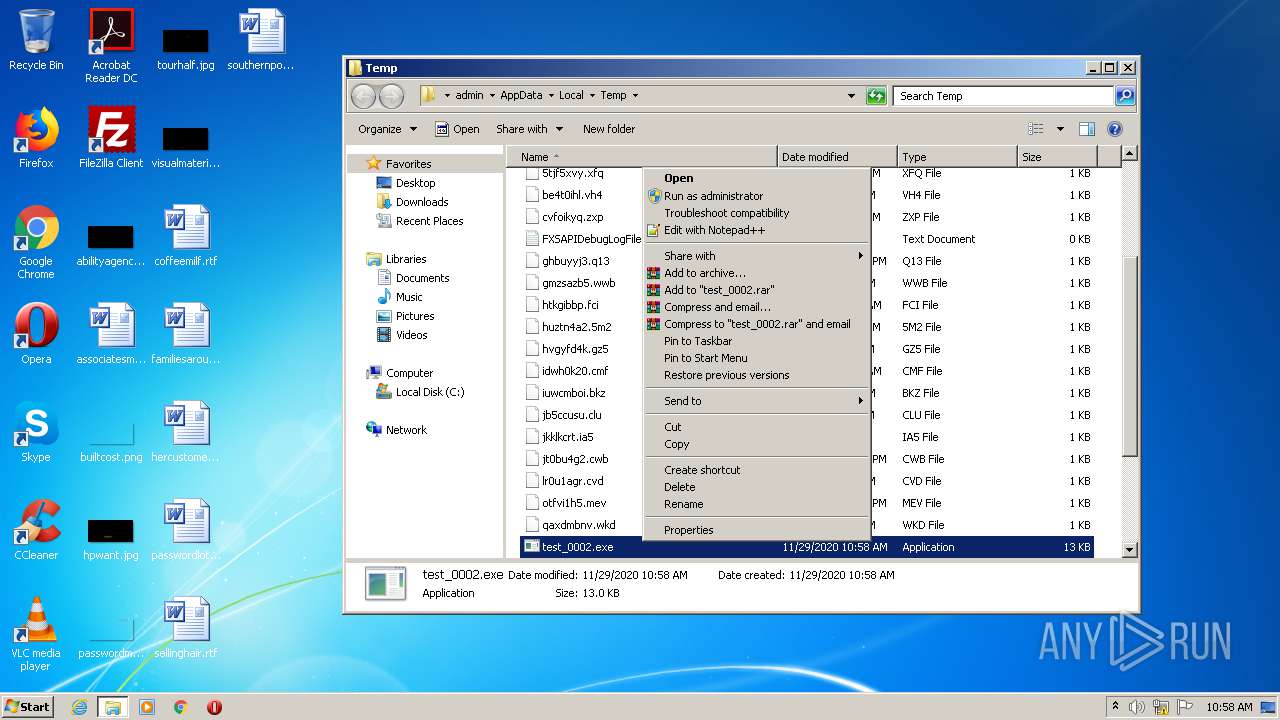
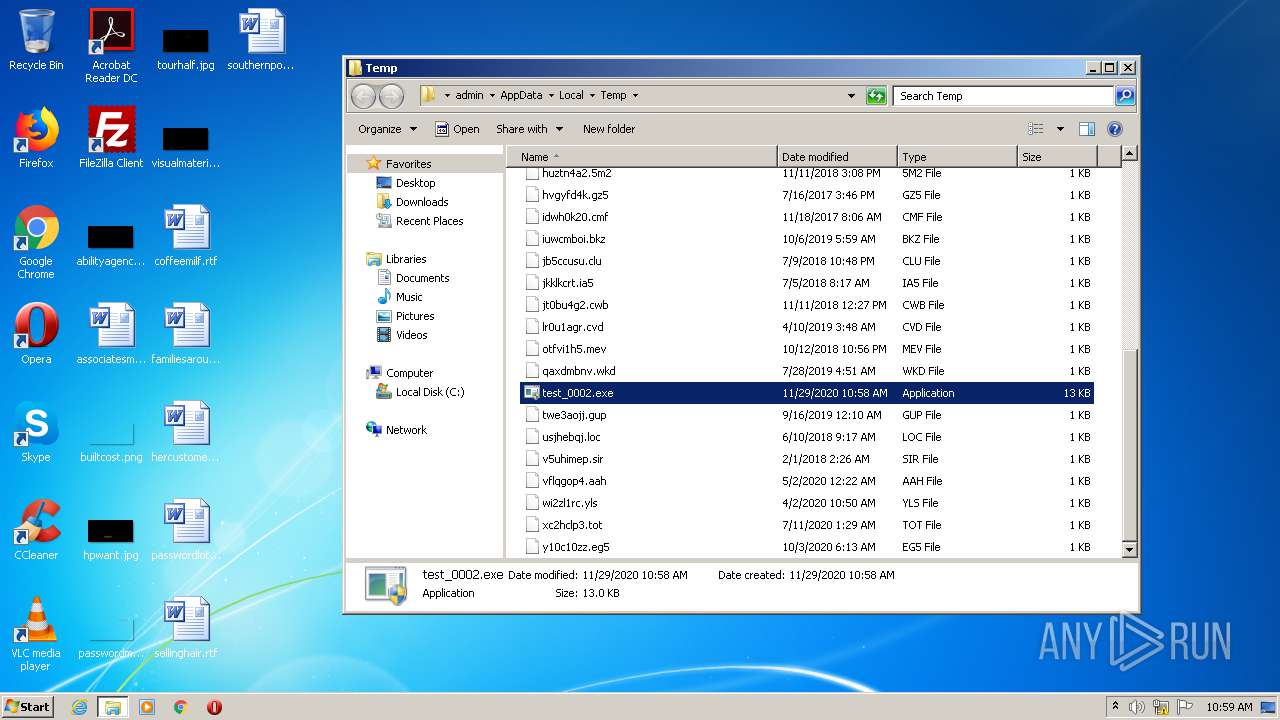
Manual execution by user
- test_0002.exe (PID: 4052)
- test_0002.exe (PID: 780)
- wermgr.exe (PID: 2076)
- test_0002.exe (PID: 1296)
- wermgr.exe (PID: 2356)
- taskmgr.exe (PID: 3236)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (82.9) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (7.4) |
| .exe | | | Win32 Executable (generic) (5.1) |
| .exe | | | Generic Win/DOS Executable (2.2) |
| .exe | | | DOS Executable Generic (2.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:29 11:57:35+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 12288 |
| InitializedDataSize: | 512 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4e7e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Nov-2020 10:57:35 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 2 |
| Time date stamp: | 29-Nov-2020 10:57:35 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x00002E84 | 0x00003000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.12203 |
.reloc | 0x00006000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Imports
mscoree.dll |
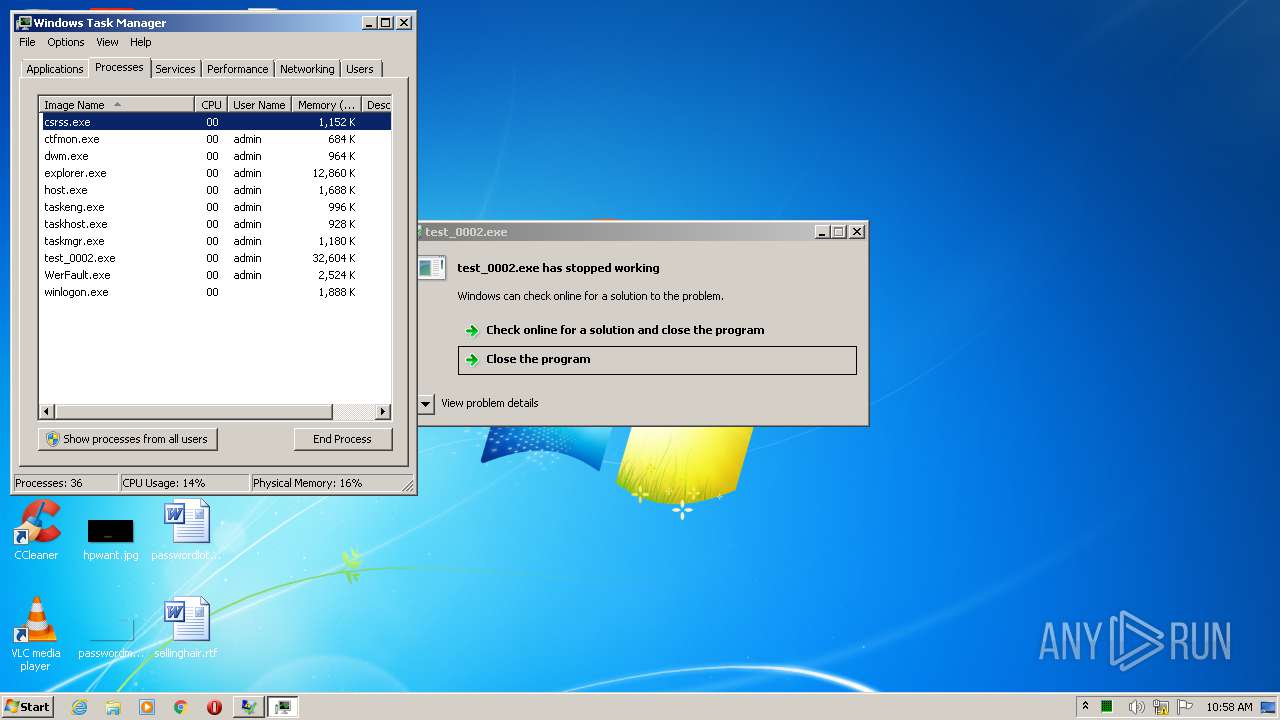
Total processes
50
Monitored processes
7
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
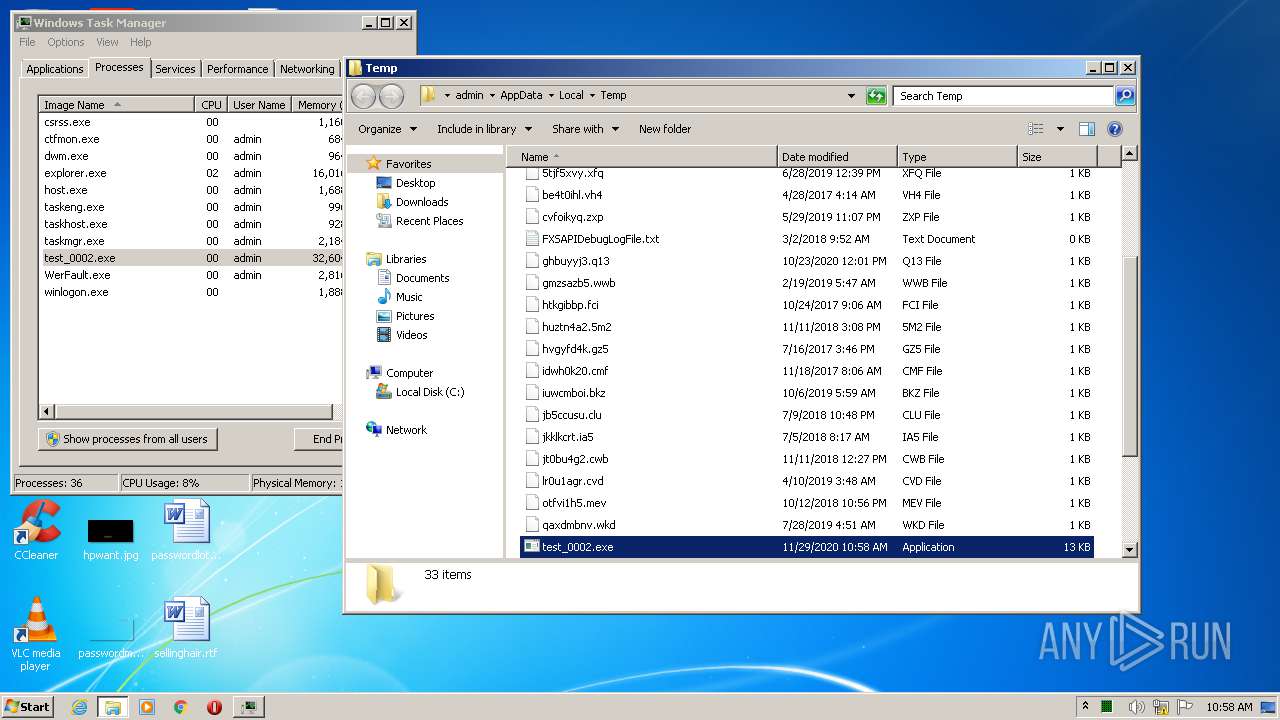
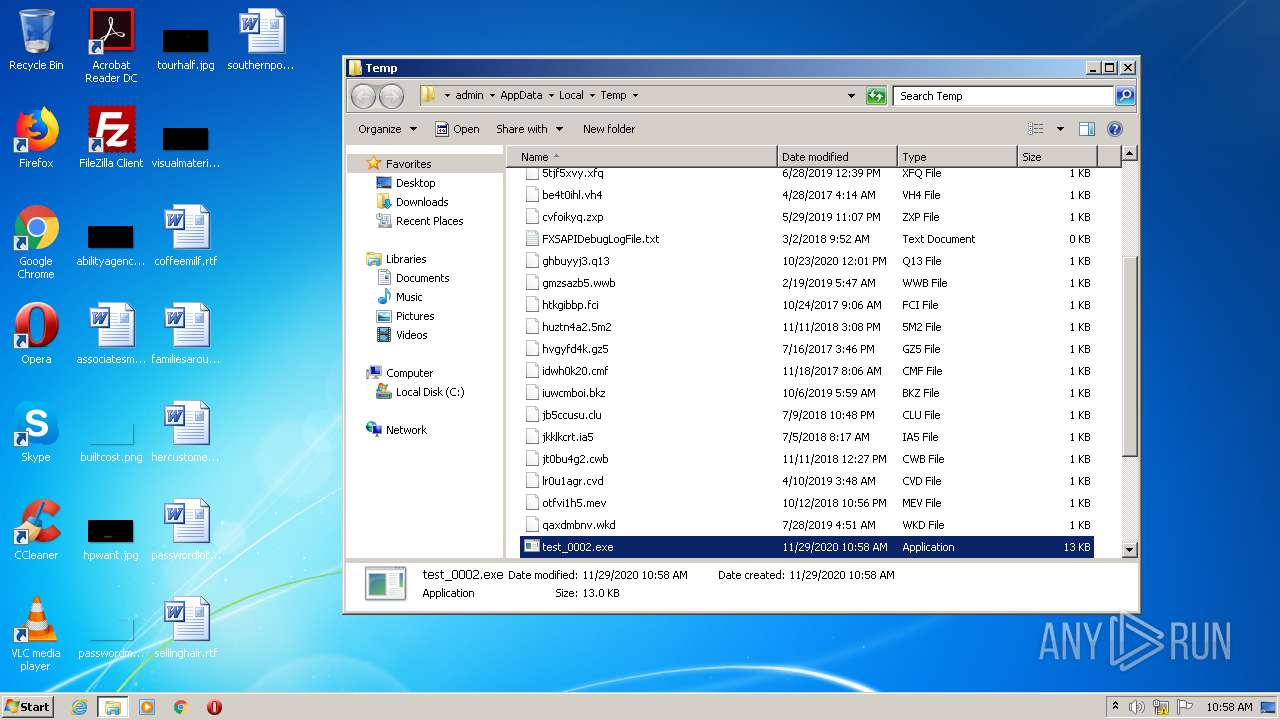
| 780 | "C:\Users\admin\AppData\Local\Temp\test_0002.exe" | C:\Users\admin\AppData\Local\Temp\test_0002.exe | — | explorer.exe | |||||||||||
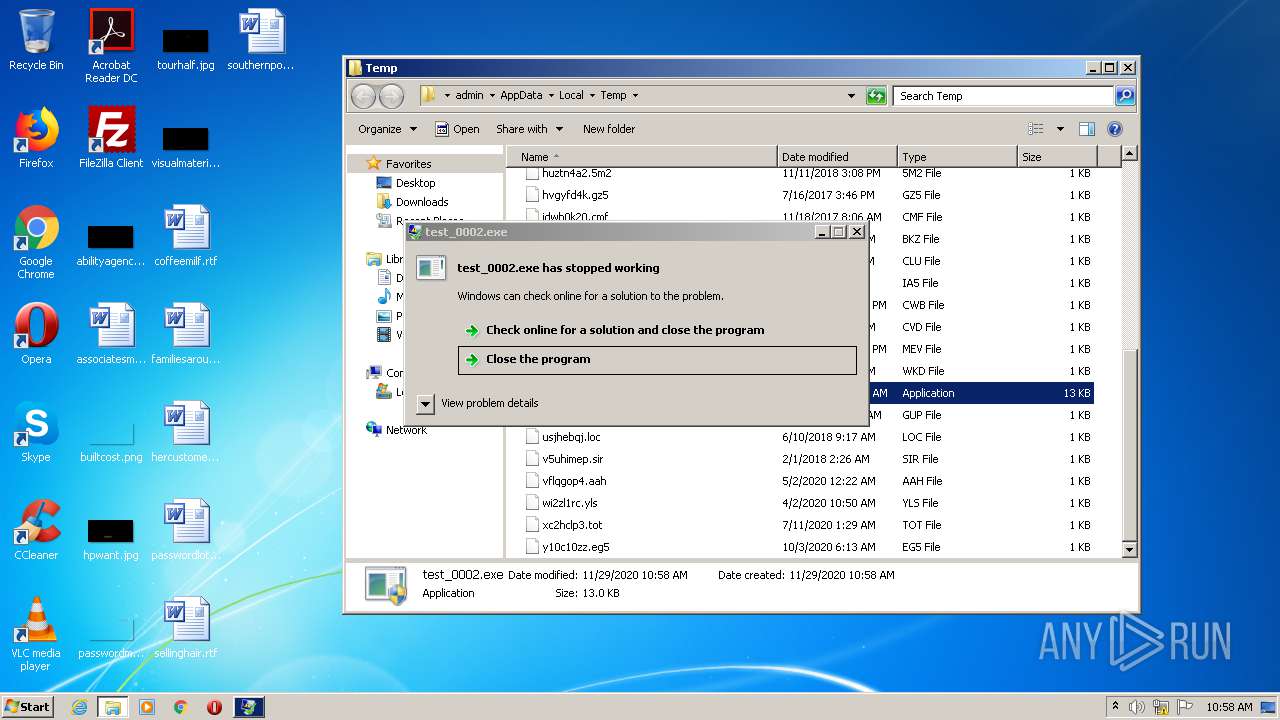
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1296 | "C:\Users\admin\AppData\Local\Temp\test_0002.exe" | C:\Users\admin\AppData\Local\Temp\test_0002.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3762504530 Modules
| |||||||||||||||
| 1840 | "C:\Users\admin\AppData\Local\Temp\test_0002.exe" | C:\Users\admin\AppData\Local\Temp\test_0002.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3762504530 Modules
| |||||||||||||||
| 2076 | "C:\Windows\system32\wermgr.exe" "-outproc" "372" "3724" | C:\Windows\system32\wermgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2356 | "C:\Windows\system32\wermgr.exe" "-outproc" "372" "3864" | C:\Windows\system32\wermgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3236 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4052 | "C:\Users\admin\AppData\Local\Temp\test_0002.exe" | C:\Users\admin\AppData\Local\Temp\test_0002.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 3762504530 Modules
| |||||||||||||||
Total events
579
Read events
529
Write events
49
Delete events
1
Modification events
| (PID) Process: | (1840) test_0002.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test_0002_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1840) test_0002.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test_0002_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1840) test_0002.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test_0002_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1840) test_0002.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test_0002_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1840) test_0002.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test_0002_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1840) test_0002.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test_0002_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1840) test_0002.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test_0002_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1840) test_0002.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test_0002_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1840) test_0002.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test_0002_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1840) test_0002.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\test_0002_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2356 | wermgr.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\NonCritical_test_0002.exe_5a62d797d24a4bd0f3645248ef3fc3c26fea5ca0_0920ea3f\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 2076 | wermgr.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\NonCritical_test_0002.exe_5a62d797d24a4bd0f3645248ef3fc3c26fea5ca0_cab_0808e33a\appcompat.txt | xml | |
MD5:— | SHA256:— | |||
| 2076 | wermgr.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\NonCritical_test_0002.exe_5a62d797d24a4bd0f3645248ef3fc3c26fea5ca0_cab_0808e33a\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 2076 | wermgr.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\NonCritical_test_0002.exe_5a62d797d24a4bd0f3645248ef3fc3c26fea5ca0_cab_0808e33a\TabE2CD.tmp | text | |
MD5:A888880617592FACA7384726060482F4 | SHA256:812742C959B6752D300080FB56459B04332EF91CC895A0846C2333C8B0C15FD6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1840 | test_0002.exe | 35.177.48.231:443 | authenticatorutility-v6.tiiny.site | Amazon.com, Inc. | GB | unknown |
4052 | test_0002.exe | 35.177.48.231:443 | authenticatorutility-v6.tiiny.site | Amazon.com, Inc. | GB | unknown |
1296 | test_0002.exe | 35.177.48.231:443 | authenticatorutility-v6.tiiny.site | Amazon.com, Inc. | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
authenticatorutility-v6.tiiny.site |
| suspicious |
Threats
Process | Message |
|---|---|
test_0002.exe | FTH: (1296): *** Fault tolerant heap shim applied to current process. This is usually due to previous crashes. ***
|