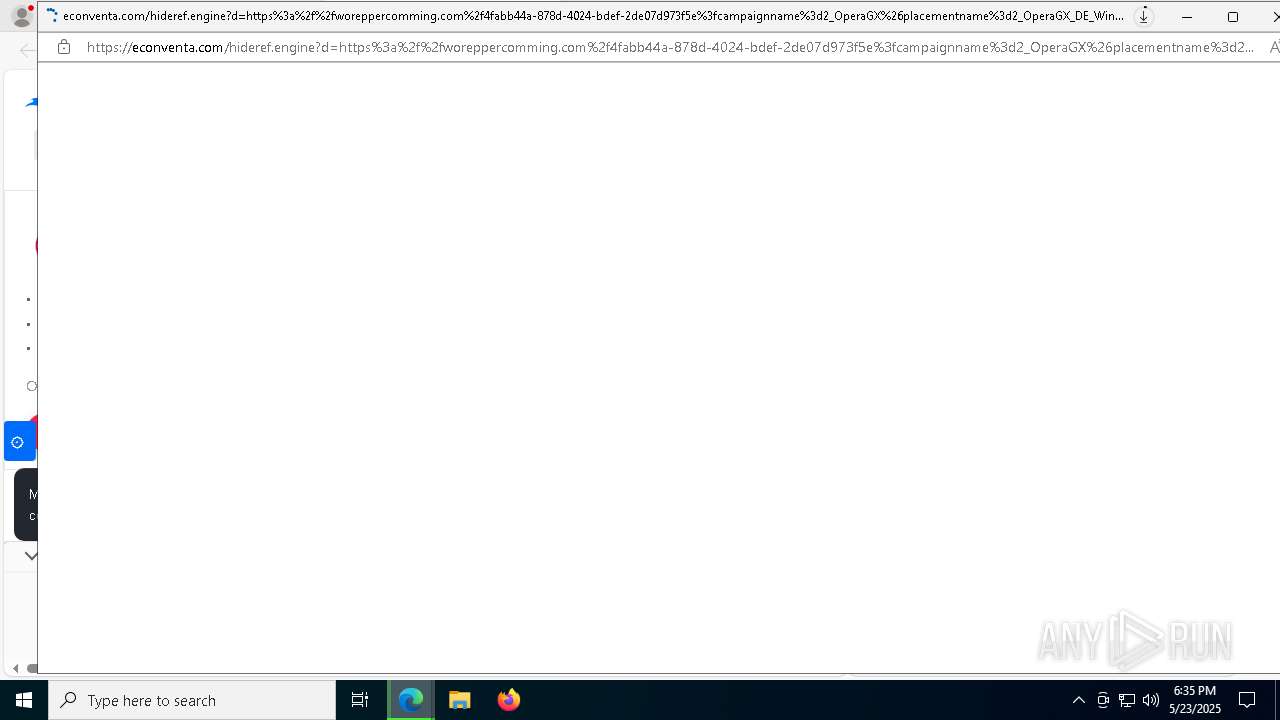
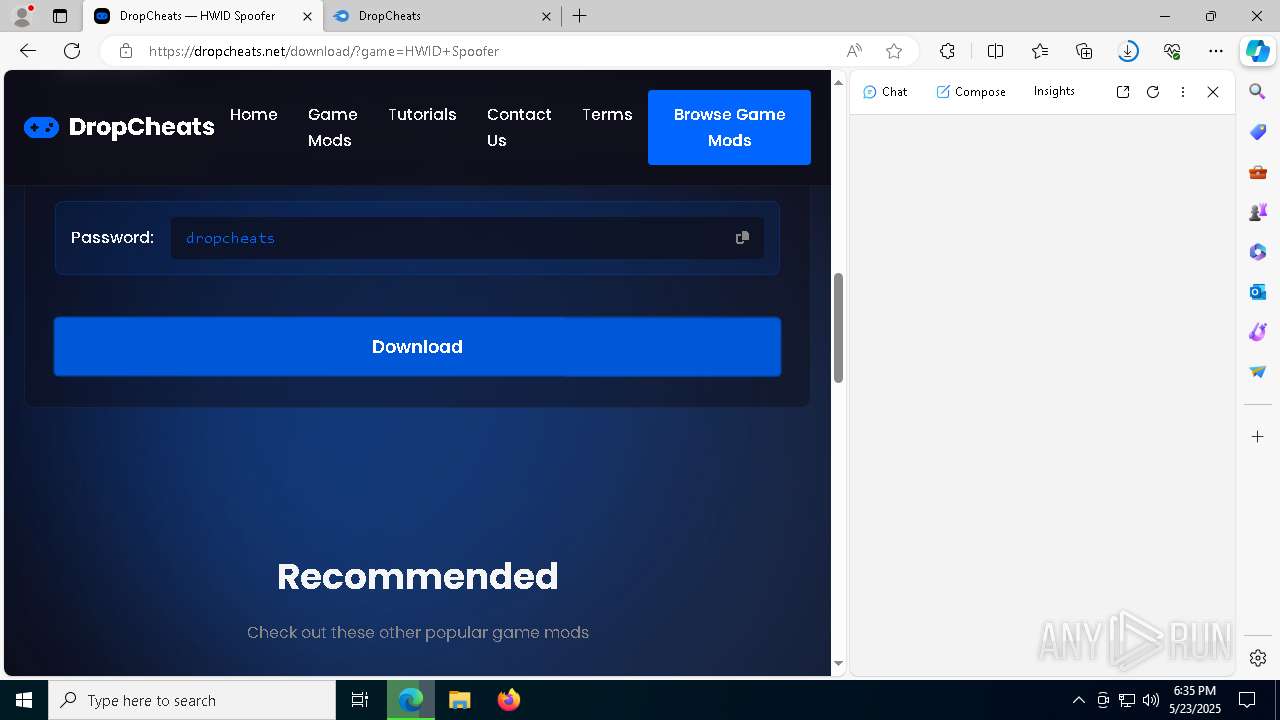
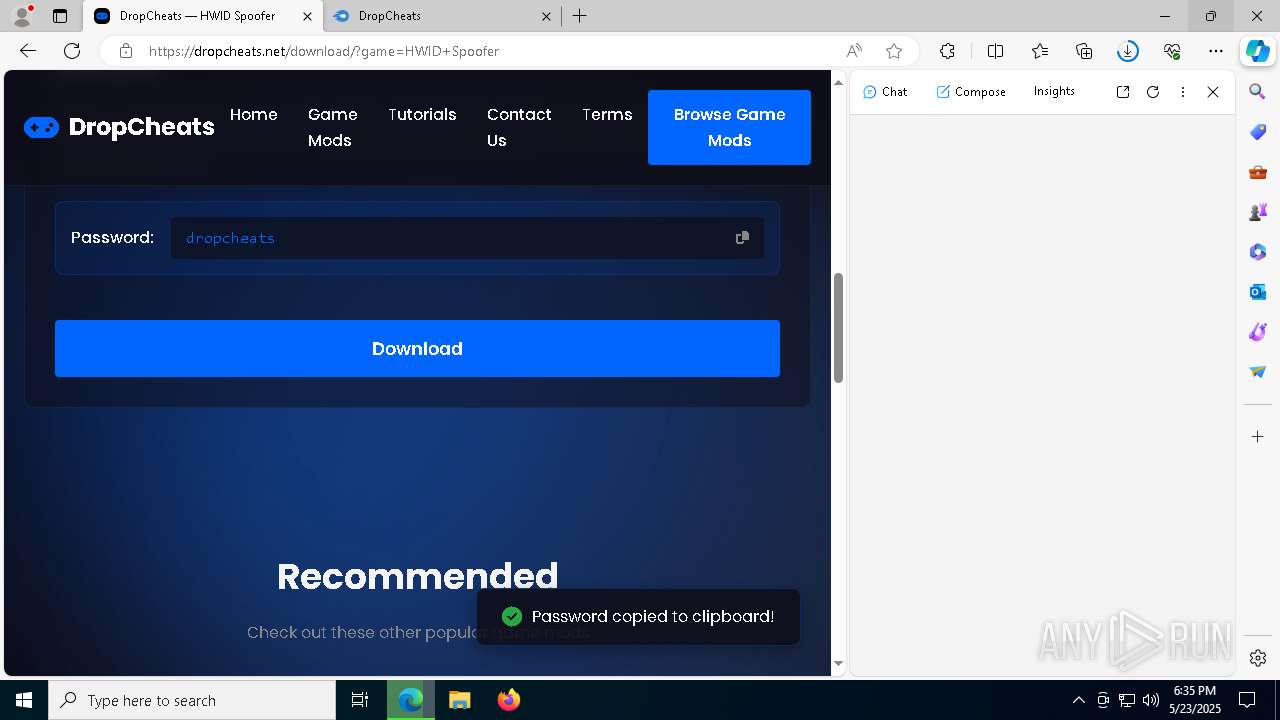
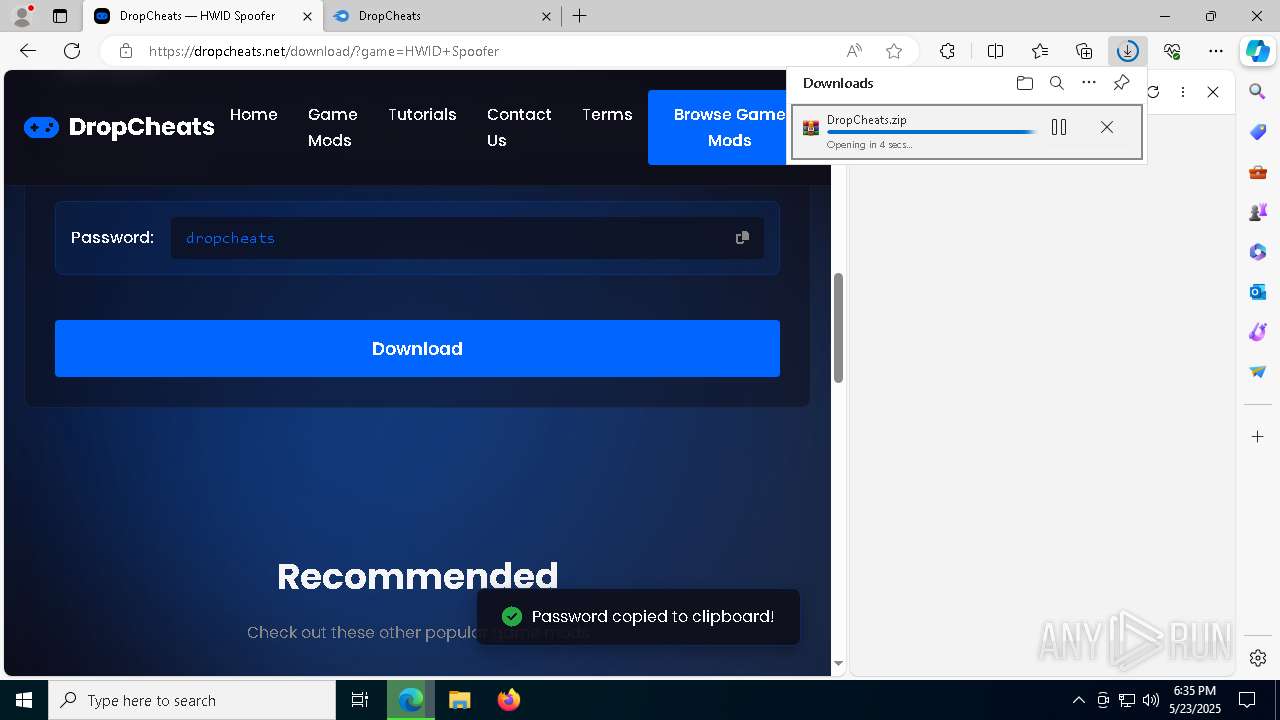
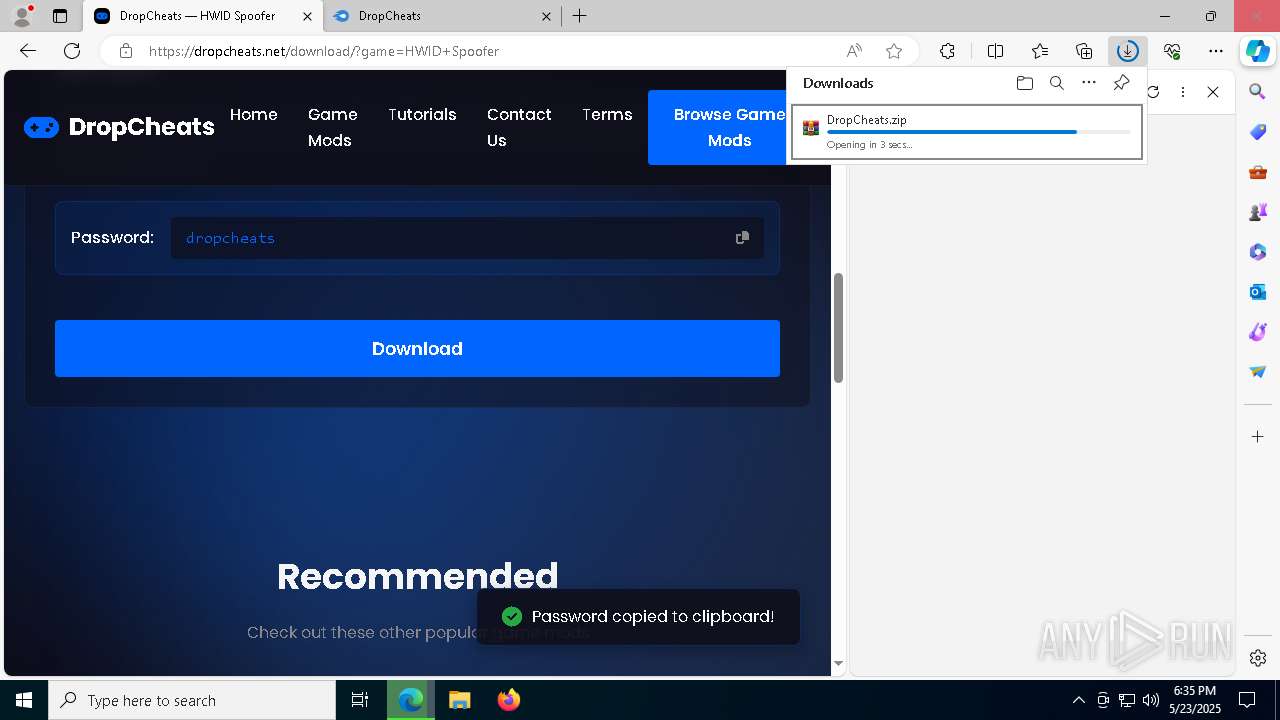
| URL: | https://dropcheats.net/ |
| Full analysis: | https://app.any.run/tasks/fe0f54b3-bba5-48aa-94b1-eb312224c179 |
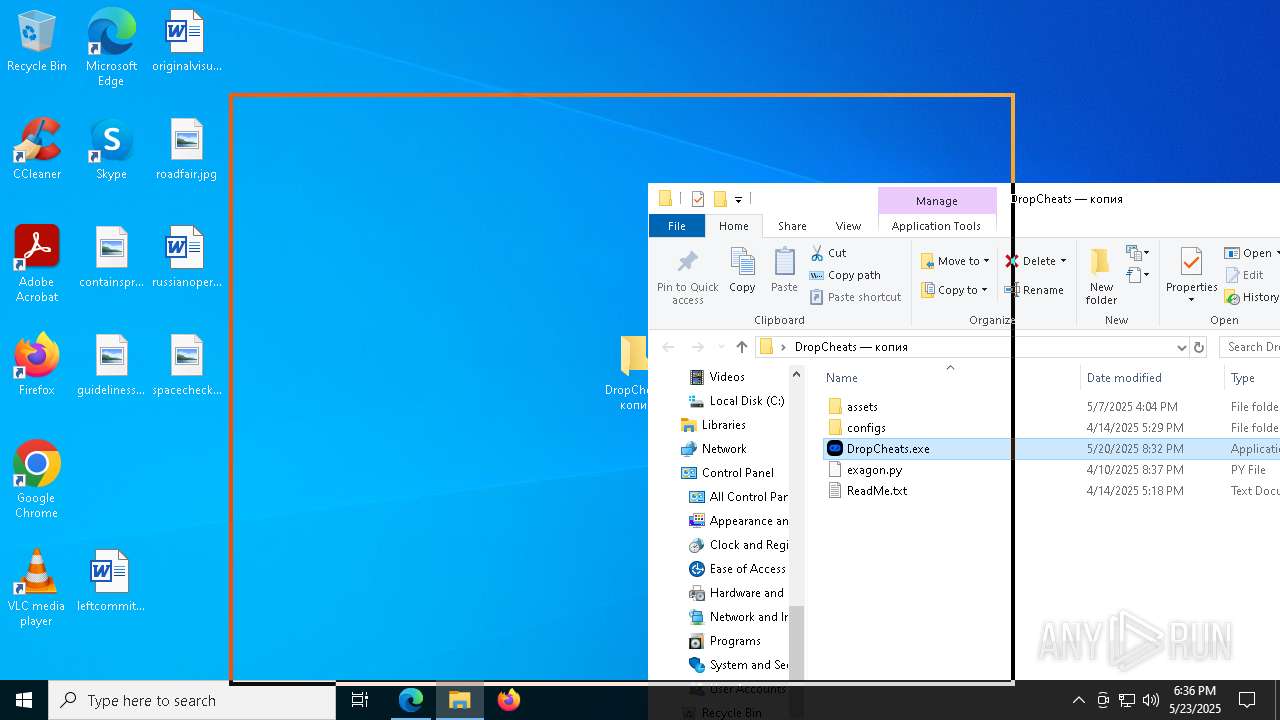
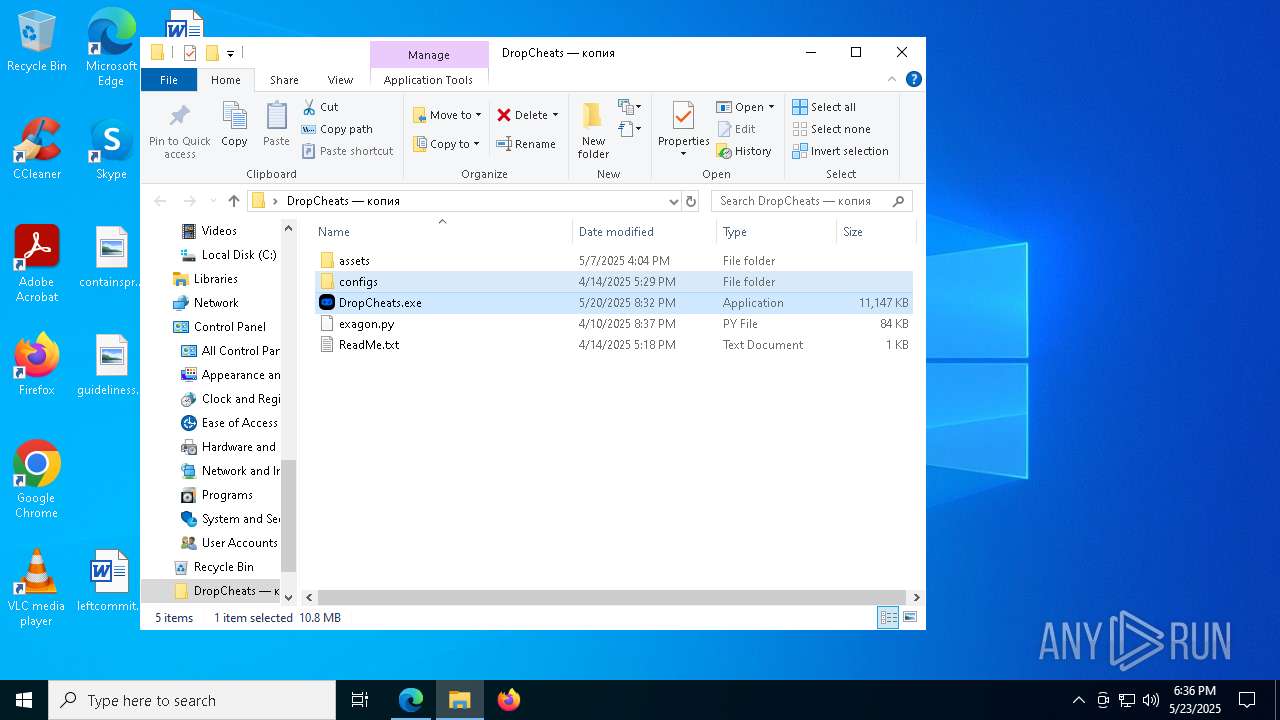
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2025, 18:34:49 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
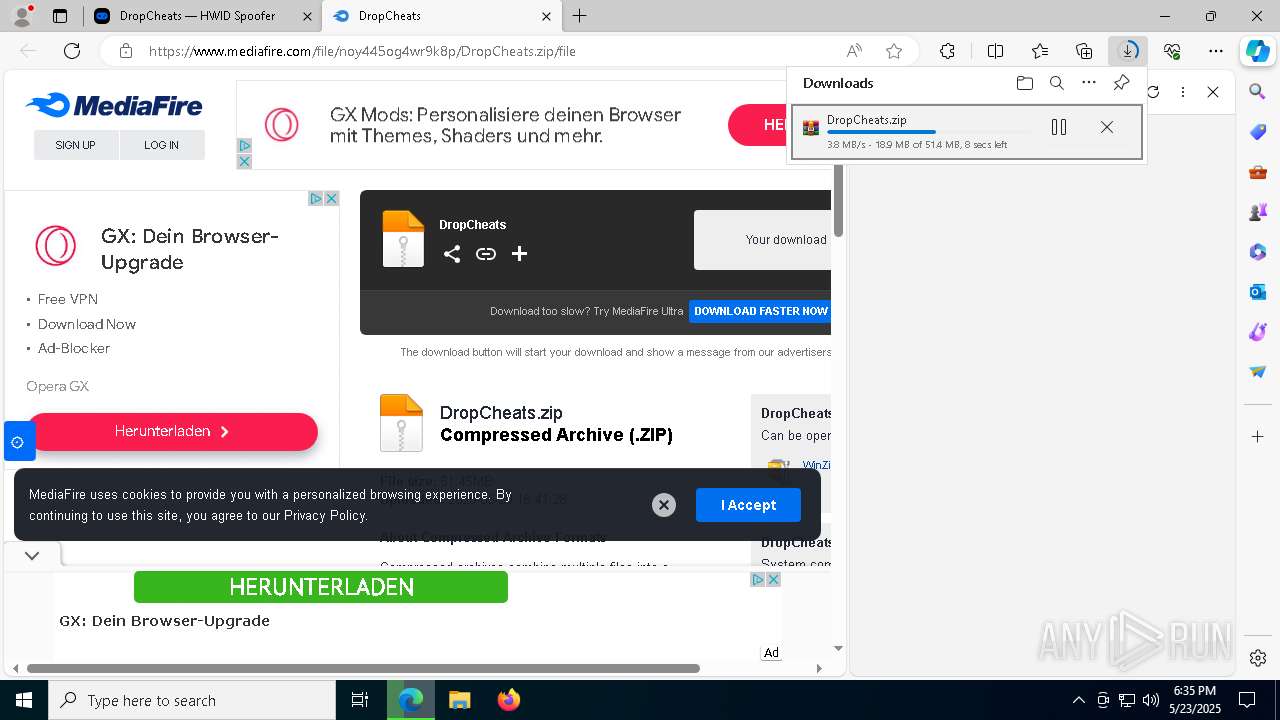
| MD5: | 73DD5B8F808462C7C521FF53FEA5752D |
| SHA1: | 76C9D59B91CBC537BC8CAE601F057734DE1E1849 |
| SHA256: | D62CE7978AB22C6917933DC603A4AA64A6199ED935EA708F17A9F77072318434 |
| SSDEEP: | 3:N8PKVD:2k |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process drops legitimate windows executable
- WinRAR.exe (PID: 8276)
Reads security settings of Internet Explorer
- DropCheats.exe (PID: 5364)
Executing commands from a ".bat" file
- DropCheats.exe (PID: 5364)
- DropCheats.exe (PID: 4988)
- DropCheats.exe (PID: 8656)
Starts the AutoIt3 executable file
- cmd.exe (PID: 7920)
- cmd.exe (PID: 5960)
- cmd.exe (PID: 8376)
Application launched itself
- cmd.exe (PID: 7920)
- cmd.exe (PID: 5960)
- cmd.exe (PID: 8376)
Starts application with an unusual extension
- cmd.exe (PID: 7920)
- cmd.exe (PID: 5960)
- cmd.exe (PID: 8376)
The executable file from the user directory is run by the CMD process
- Greatly.com (PID: 8832)
- Greatly.com (PID: 8744)
- Greatly.com (PID: 3768)
Starts CMD.EXE for commands execution
- DropCheats.exe (PID: 5364)
- cmd.exe (PID: 7920)
- cmd.exe (PID: 5960)
- DropCheats.exe (PID: 8656)
- DropCheats.exe (PID: 4988)
- cmd.exe (PID: 8376)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 7920)
- cmd.exe (PID: 5960)
- cmd.exe (PID: 8376)
Get information on the list of running processes
- cmd.exe (PID: 7920)
- cmd.exe (PID: 8376)
- cmd.exe (PID: 5960)
BASE64 encoded PowerShell command has been detected
- Greatly.com (PID: 8832)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- Greatly.com (PID: 8832)
Base64-obfuscated command line is found
- Greatly.com (PID: 8832)
Starts POWERSHELL.EXE for commands execution
- Greatly.com (PID: 8832)
The process hide an interactive prompt from the user
- Greatly.com (PID: 8832)
The process bypasses the loading of PowerShell profile settings
- Greatly.com (PID: 8832)
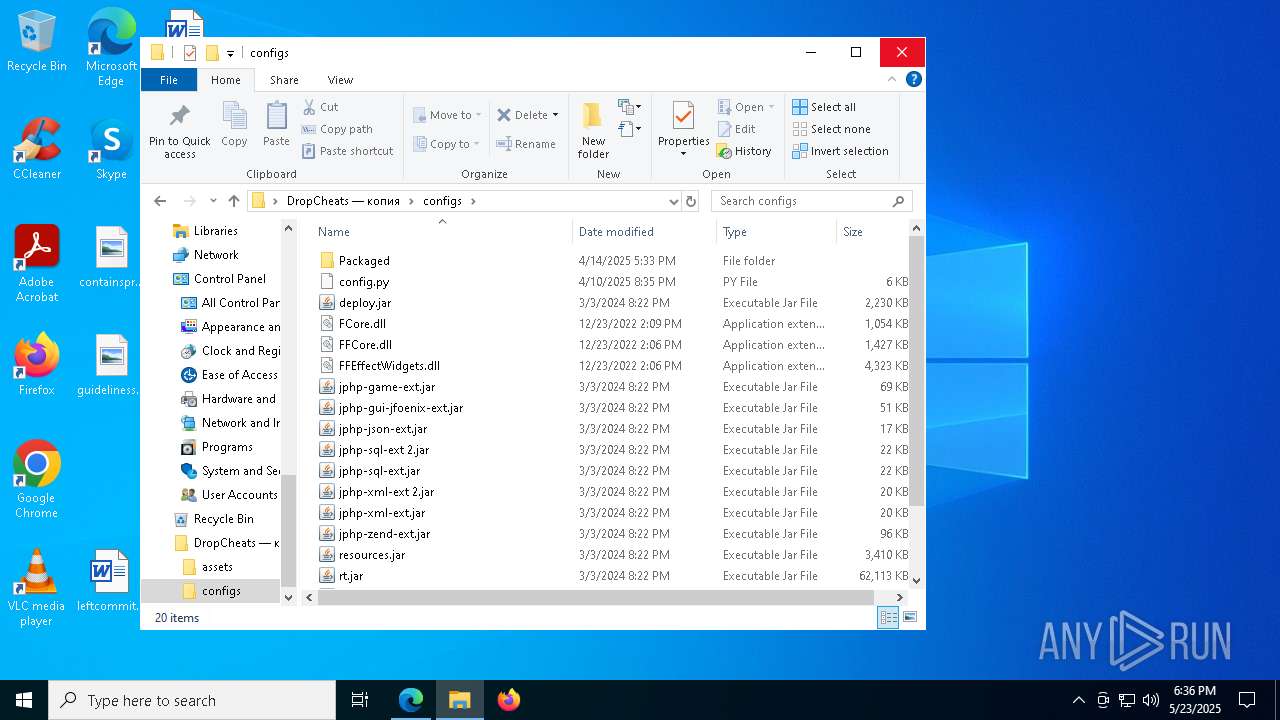
CSC.EXE is used to compile C# code
- csc.exe (PID: 4652)
Executable content was dropped or overwritten
- csc.exe (PID: 4652)
INFO
Reads Environment values
- identity_helper.exe (PID: 616)
Application launched itself
- msedge.exe (PID: 6872)
- chrome.exe (PID: 496)
Checks supported languages
- identity_helper.exe (PID: 616)
- DropCheats.exe (PID: 5364)
- extrac32.exe (PID: 9192)
- Greatly.com (PID: 8832)
Reads the computer name
- identity_helper.exe (PID: 616)
- DropCheats.exe (PID: 5364)
- extrac32.exe (PID: 9192)
Executable content was dropped or overwritten
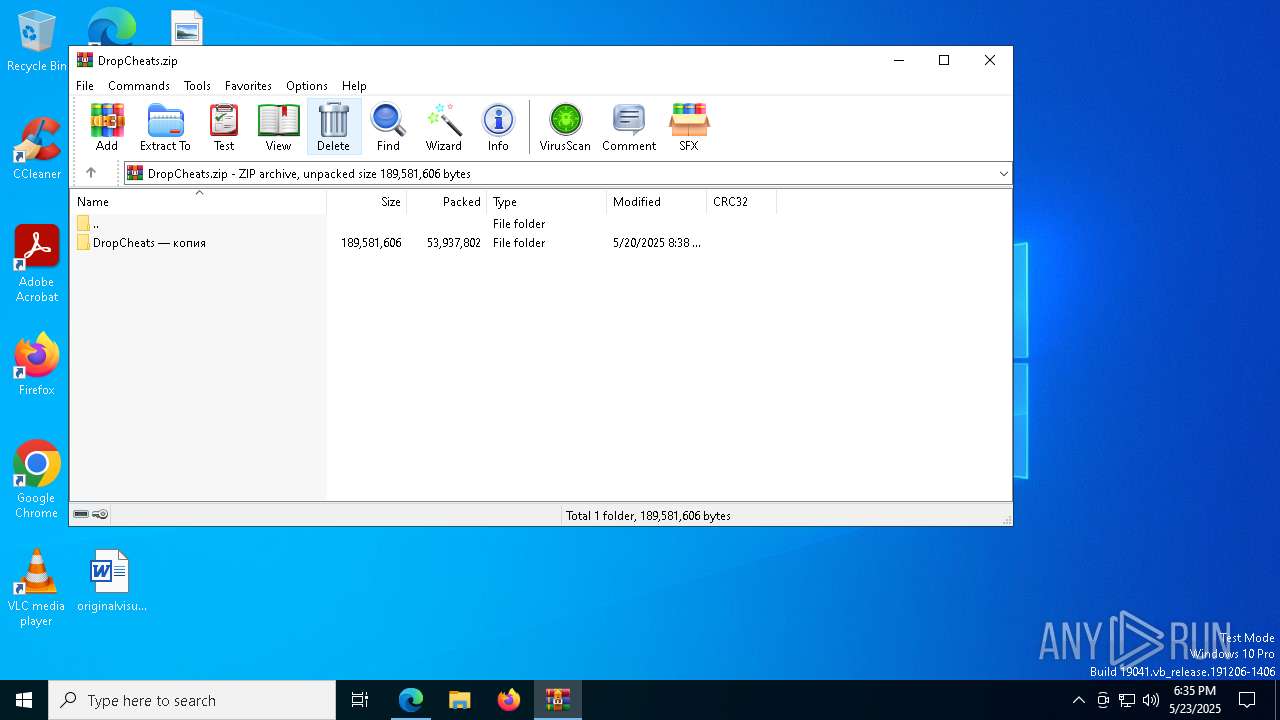
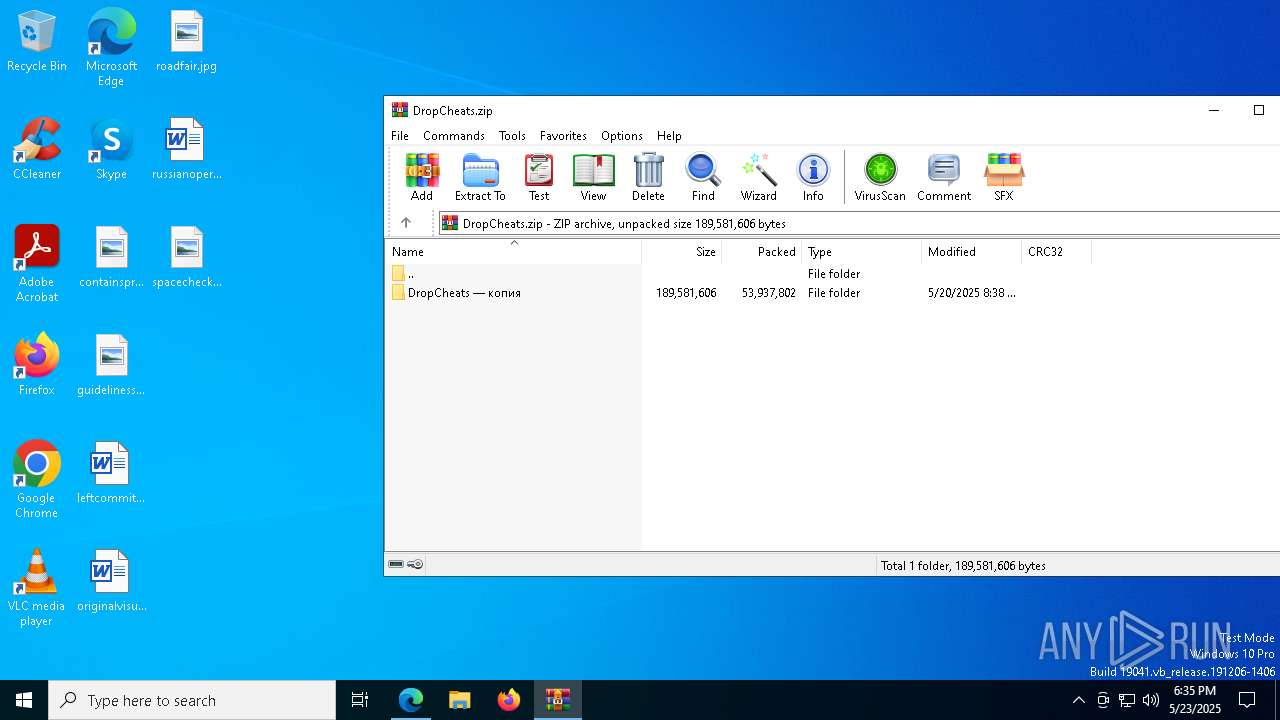
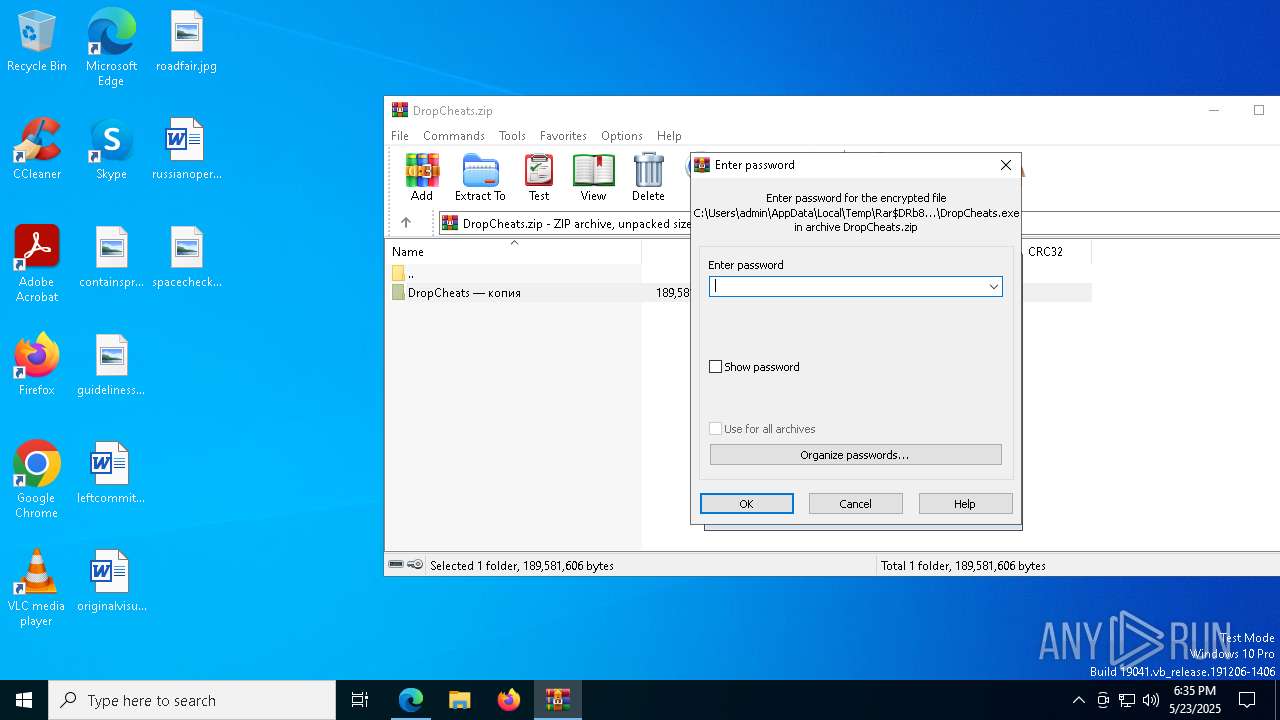
- WinRAR.exe (PID: 8276)
The sample compiled with chinese language support
- WinRAR.exe (PID: 8276)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6872)
The sample compiled with english language support
- WinRAR.exe (PID: 8276)
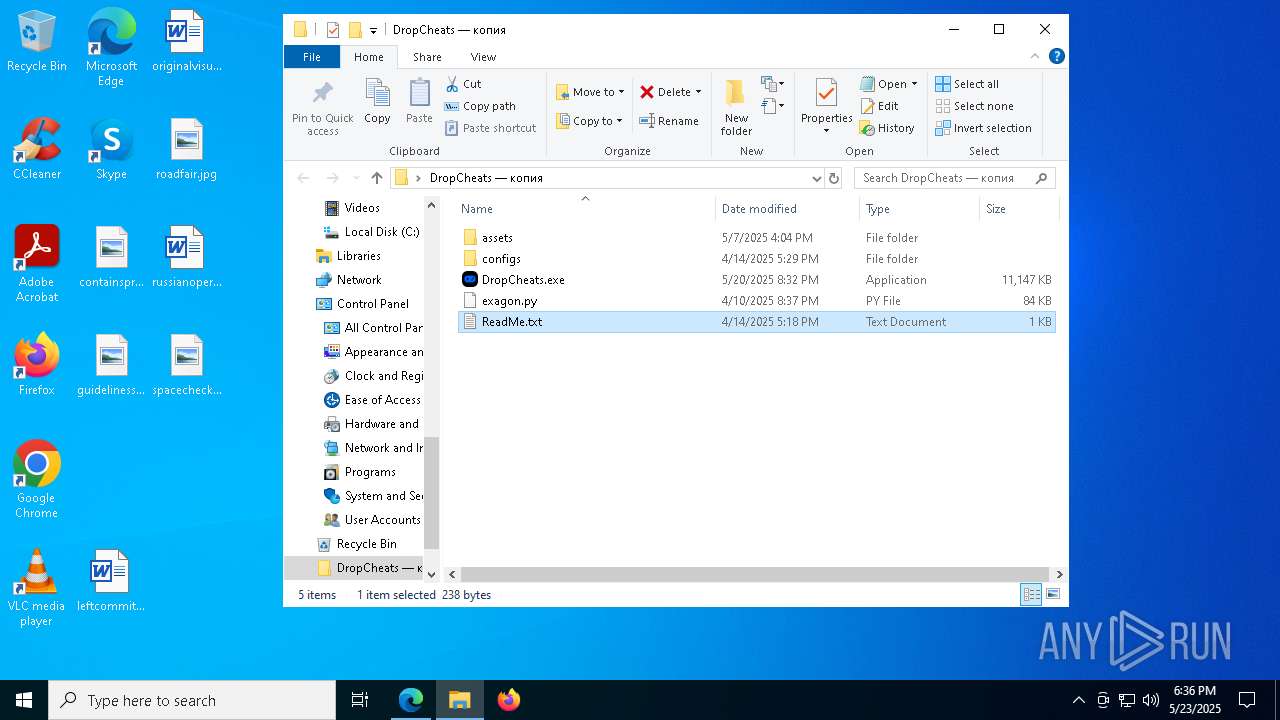
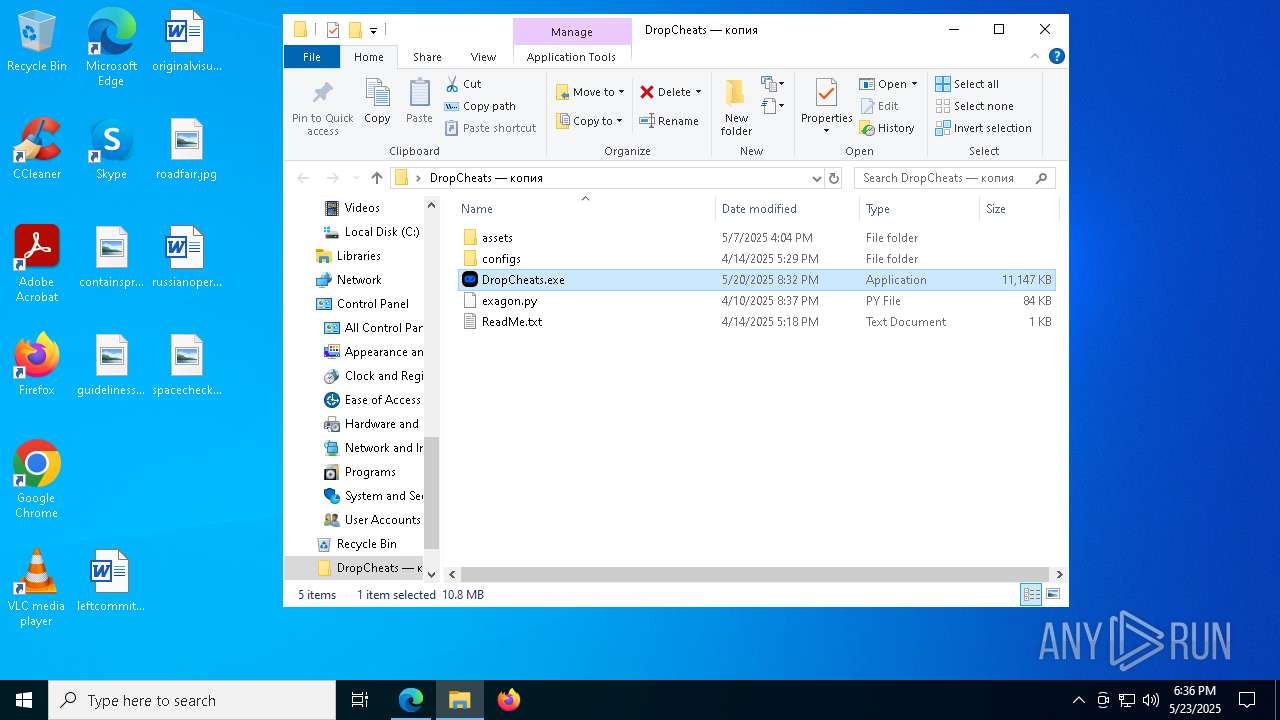
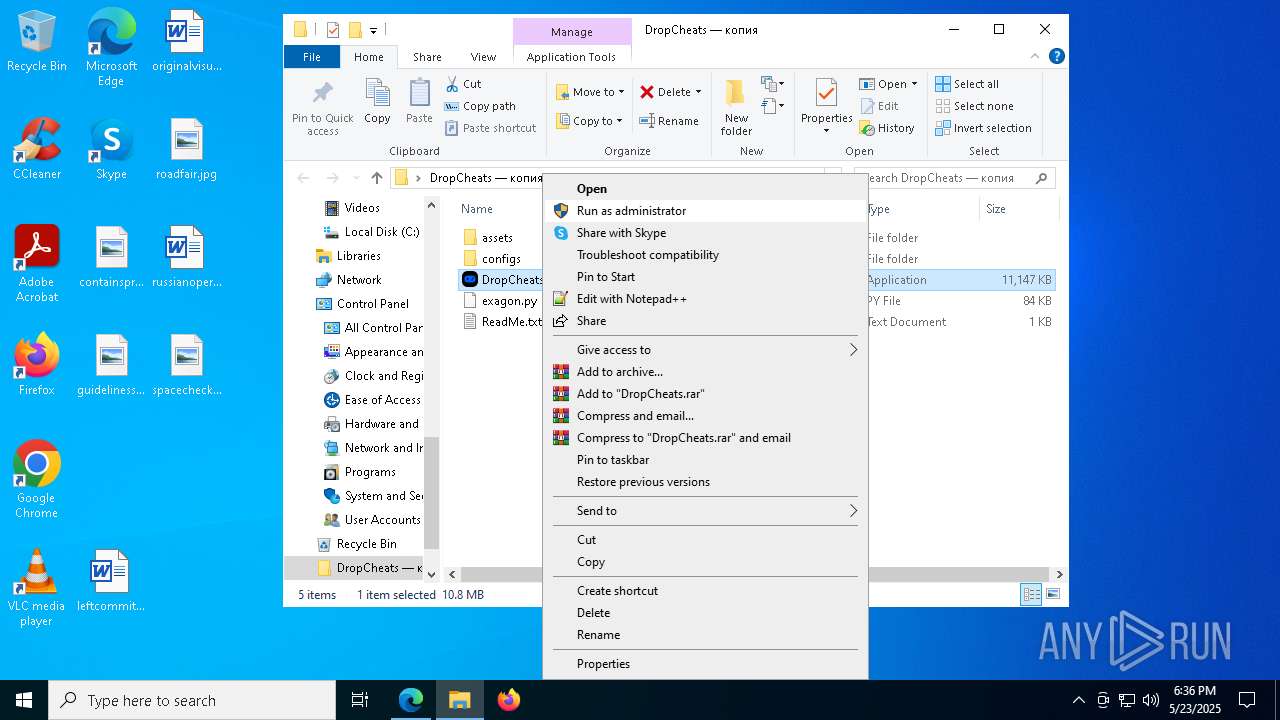
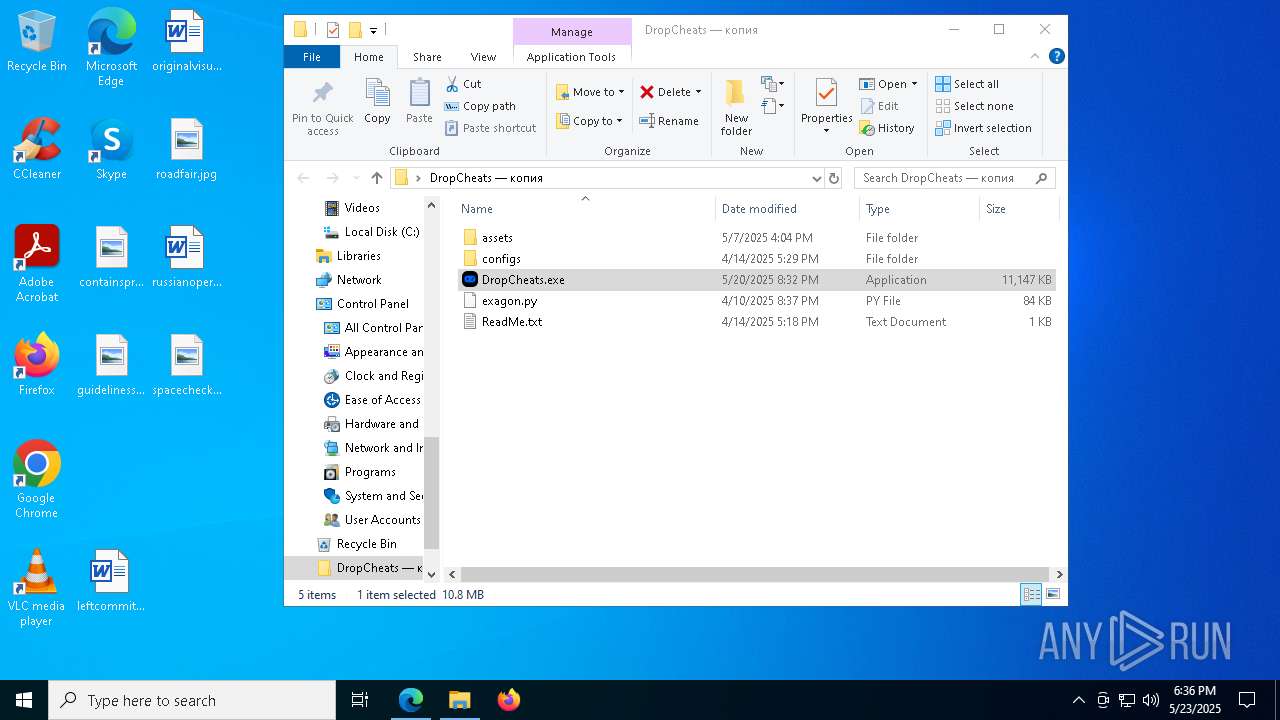
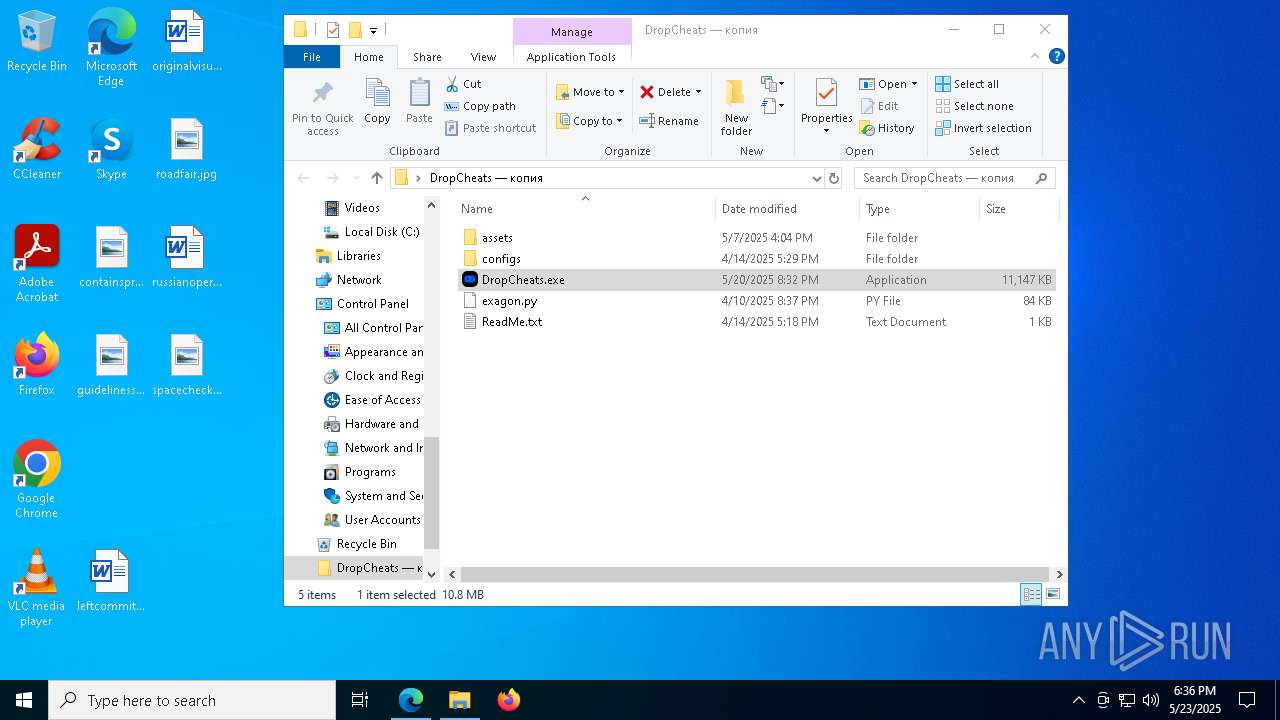
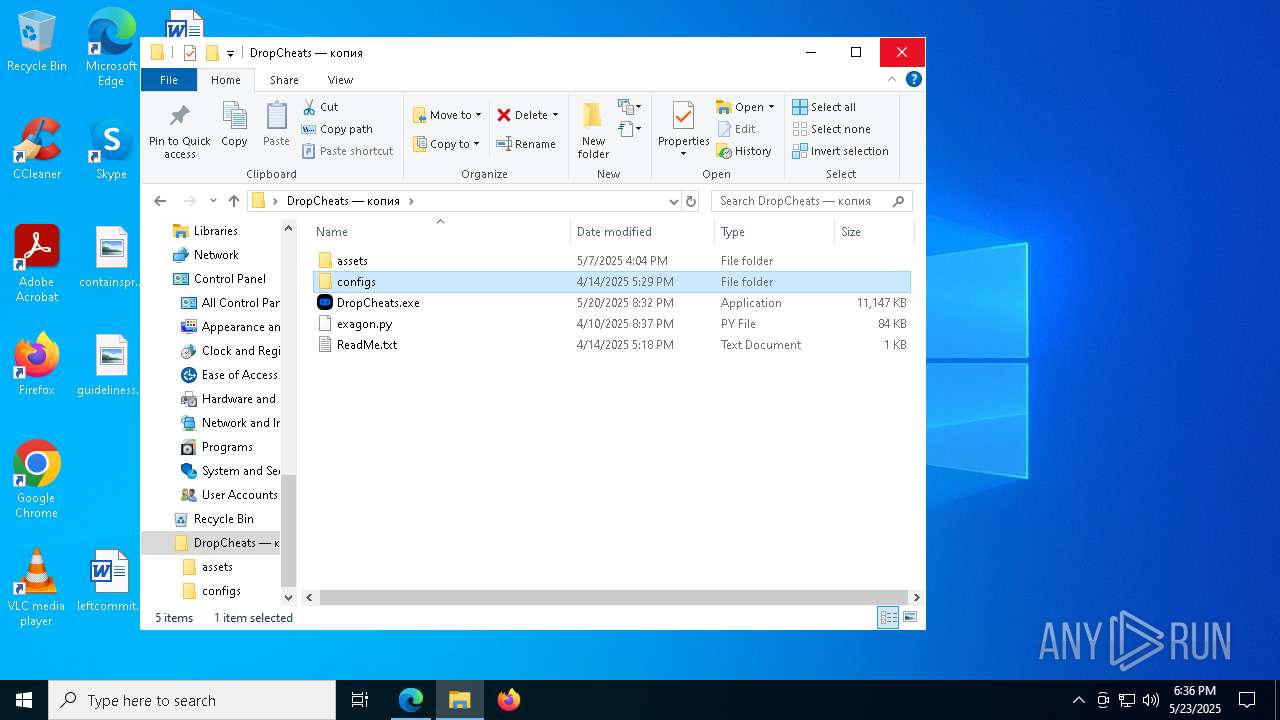
Manual execution by a user
- DropCheats.exe (PID: 5364)
- notepad.exe (PID: 9004)
- DropCheats.exe (PID: 8656)
- DropCheats.exe (PID: 4988)
Create files in a temporary directory
- DropCheats.exe (PID: 5364)
- extrac32.exe (PID: 9192)
Process checks computer location settings
- DropCheats.exe (PID: 5364)
Creates a new folder
- cmd.exe (PID: 9168)
- cmd.exe (PID: 8840)
- cmd.exe (PID: 8088)
Reads mouse settings
- Greatly.com (PID: 8832)
Reads security settings of Internet Explorer
- notepad.exe (PID: 9004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
247
Monitored processes
113
Malicious processes
4
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 472 | findstr "bdservicehost SophosHealth AvastUI AVGUI nsWscSvc ekrn" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 496 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Greatly.com | |
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 | ||||
| 616 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5968 --field-trial-handle=2588,i,6805879448494028516,9822148952419264137,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 | ||||
| 684 | findstr /I "opssvc wrsa" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 900 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2632 --field-trial-handle=2588,i,6805879448494028516,9822148952419264137,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 | ||||
| 924 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --mojo-platform-channel-handle=7080 --field-trial-handle=2588,i,6805879448494028516,9822148952419264137,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 1284 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6004 --field-trial-handle=2588,i,6805879448494028516,9822148952419264137,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 1284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3152 --field-trial-handle=2092,i,7584078130973092634,1738941187540835594,262144 --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe |
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 | ||||
| 2564 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=8760 --field-trial-handle=2588,i,6805879448494028516,9822148952419264137,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 | ||||
| 2568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --message-loop-type-ui --no-appcompat-clear --mojo-platform-channel-handle=8068 --field-trial-handle=2588,i,6805879448494028516,9822148952419264137,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
37
Suspicious files
446
Text files
106
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State | — | |
MD5:— | SHA256:— | |||
| 6872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10a589.TMP | — | |
MD5:— | SHA256:— | |||
| 6872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Local State~RF10a5a8.TMP | — | |
MD5:— | SHA256:— | |||
| 6872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10a5d7.TMP | — | |
MD5:— | SHA256:— | |||
| 6872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10a5d7.TMP | — | |
MD5:— | SHA256:— | |||
| 6872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10a5d7.TMP | — | |
MD5:— | SHA256:— | |||
| 6872 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
312
DNS requests
396
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5796 | svchost.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8772 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
8772 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8260 | svchost.exe | HEAD | 200 | 2.16.168.202:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3aeadfbf-fadd-43ac-a5d9-c143db5f63d8?P1=1748294705&P2=404&P3=2&P4=dMc4ip27nppnGl3Ip7Tfc1e8D6zuS4mxc5tqrdcS5eAS2q%2fmspYWi%2fyVwYbw5IfZI6E7avS9Qe%2f5fyB3QokFlg%3d%3d | unknown | — | — | whitelisted |
8260 | svchost.exe | GET | 206 | 2.16.168.202:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3aeadfbf-fadd-43ac-a5d9-c143db5f63d8?P1=1748294705&P2=404&P3=2&P4=dMc4ip27nppnGl3Ip7Tfc1e8D6zuS4mxc5tqrdcS5eAS2q%2fmspYWi%2fyVwYbw5IfZI6E7avS9Qe%2f5fyB3QokFlg%3d%3d | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8260 | svchost.exe | GET | 206 | 2.16.168.202:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3aeadfbf-fadd-43ac-a5d9-c143db5f63d8?P1=1748294705&P2=404&P3=2&P4=dMc4ip27nppnGl3Ip7Tfc1e8D6zuS4mxc5tqrdcS5eAS2q%2fmspYWi%2fyVwYbw5IfZI6E7avS9Qe%2f5fyB3QokFlg%3d%3d | unknown | — | — | whitelisted |
8260 | svchost.exe | GET | 206 | 2.16.168.202:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/3aeadfbf-fadd-43ac-a5d9-c143db5f63d8?P1=1748294705&P2=404&P3=2&P4=dMc4ip27nppnGl3Ip7Tfc1e8D6zuS4mxc5tqrdcS5eAS2q%2fmspYWi%2fyVwYbw5IfZI6E7avS9Qe%2f5fyB3QokFlg%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6540 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
5796 | svchost.exe | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
6872 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
900 | msedge.exe | 104.21.6.136:443 | dropcheats.net | — | — | unknown |
900 | msedge.exe | 52.123.243.67:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | DE | whitelisted |
900 | msedge.exe | 104.17.24.14:443 | cdnjs.cloudflare.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
dropcheats.net |
| unknown |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |
900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |
900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |
900 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Image Sharing Service (imgur.com) |
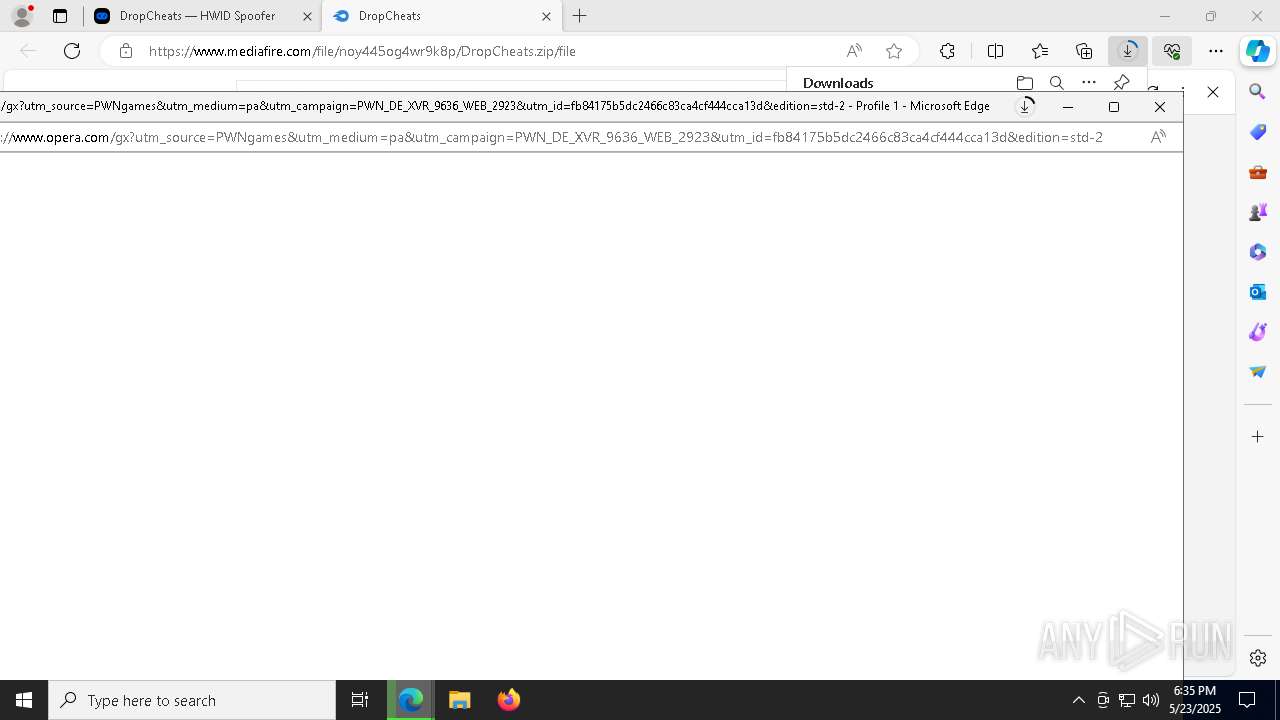
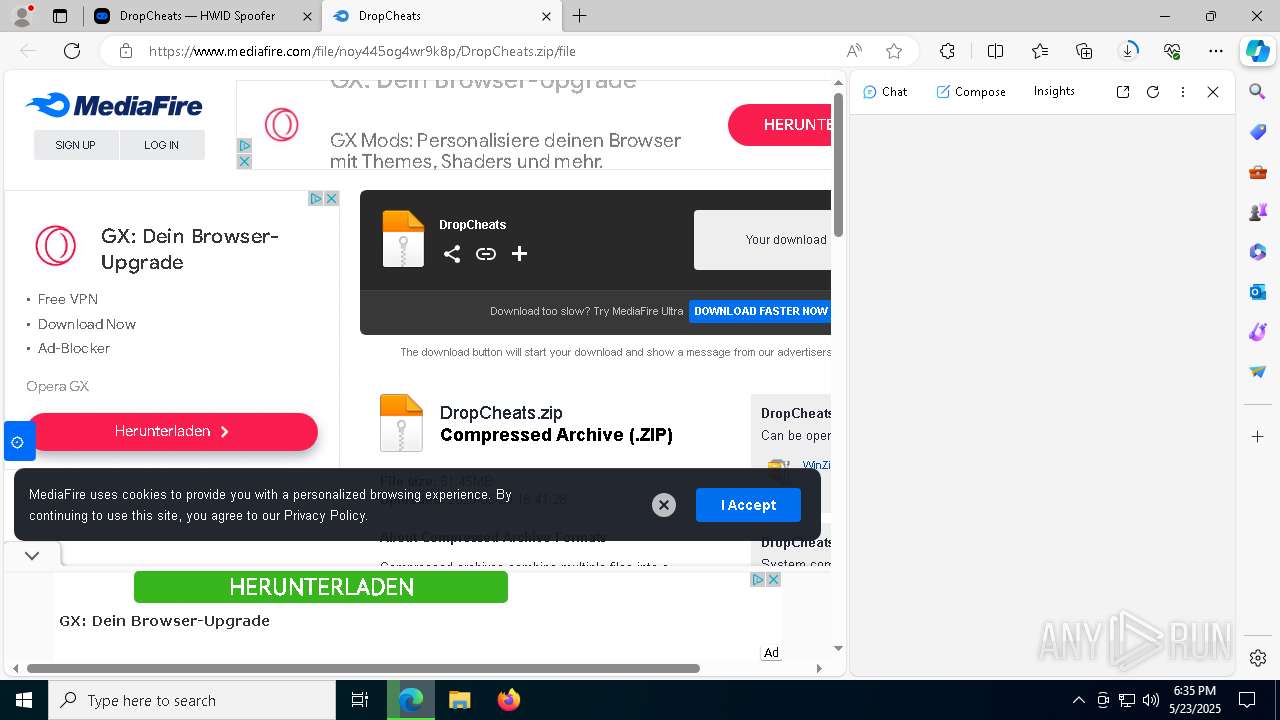
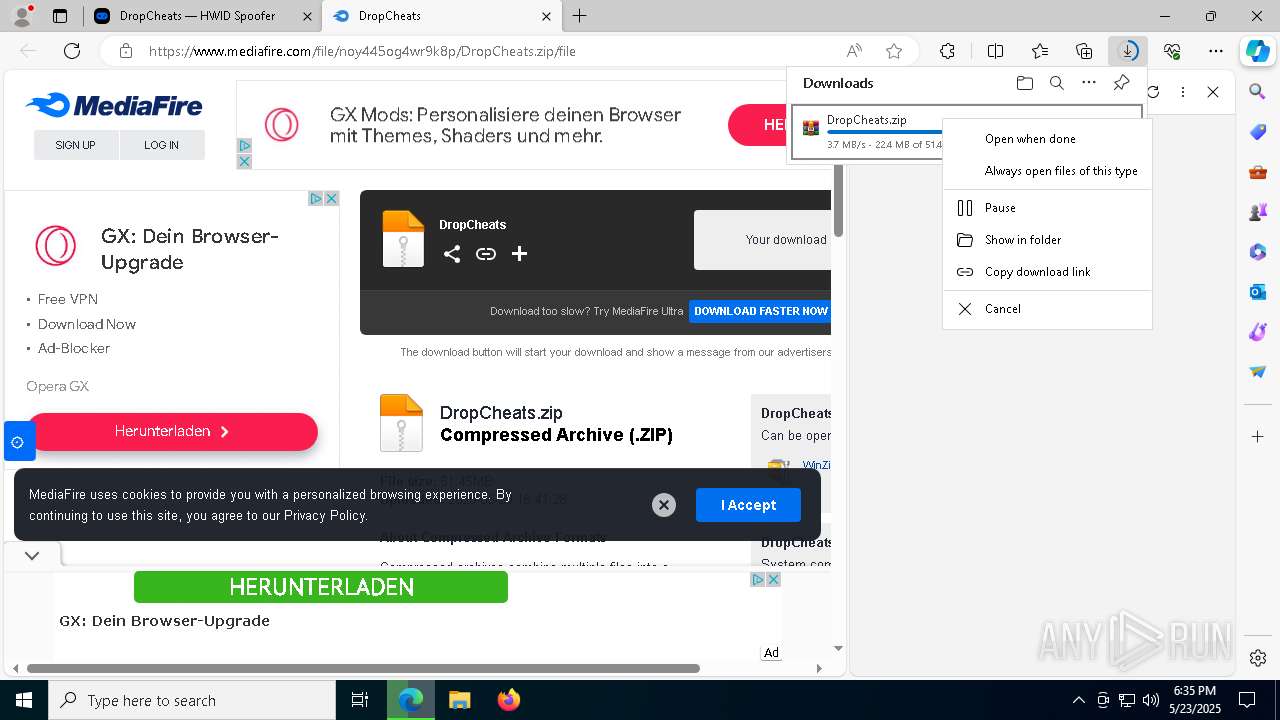
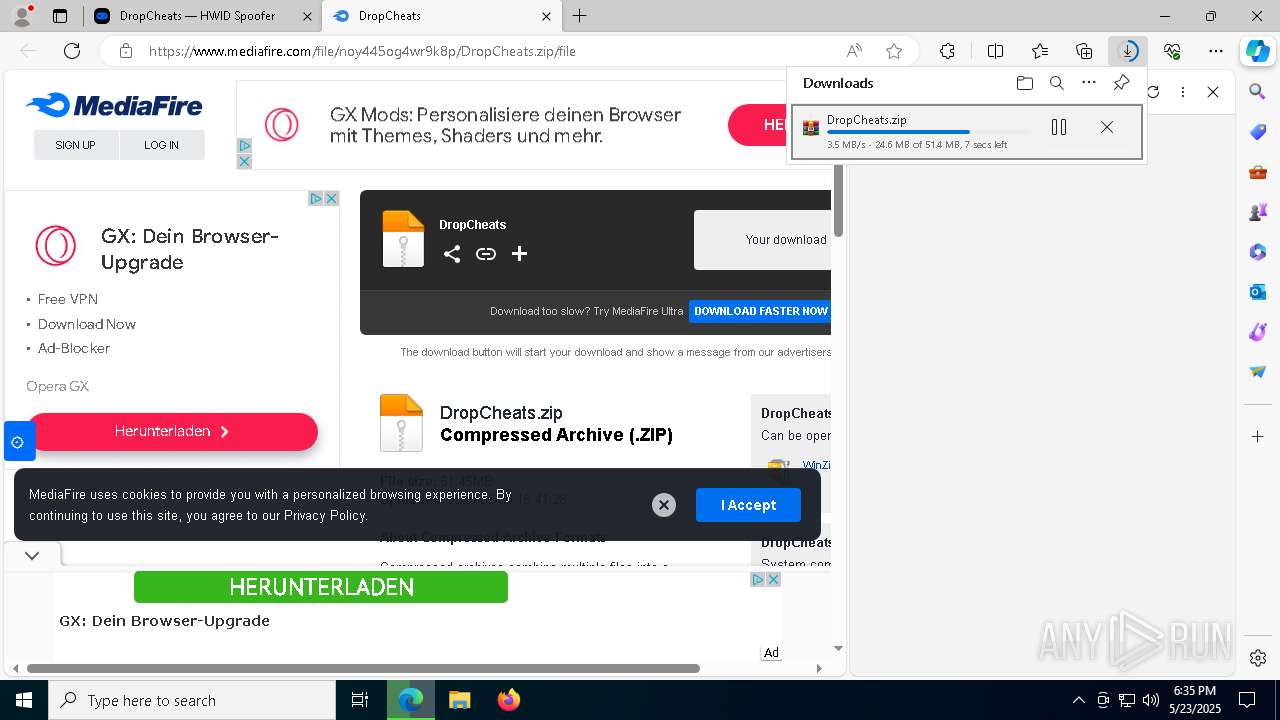
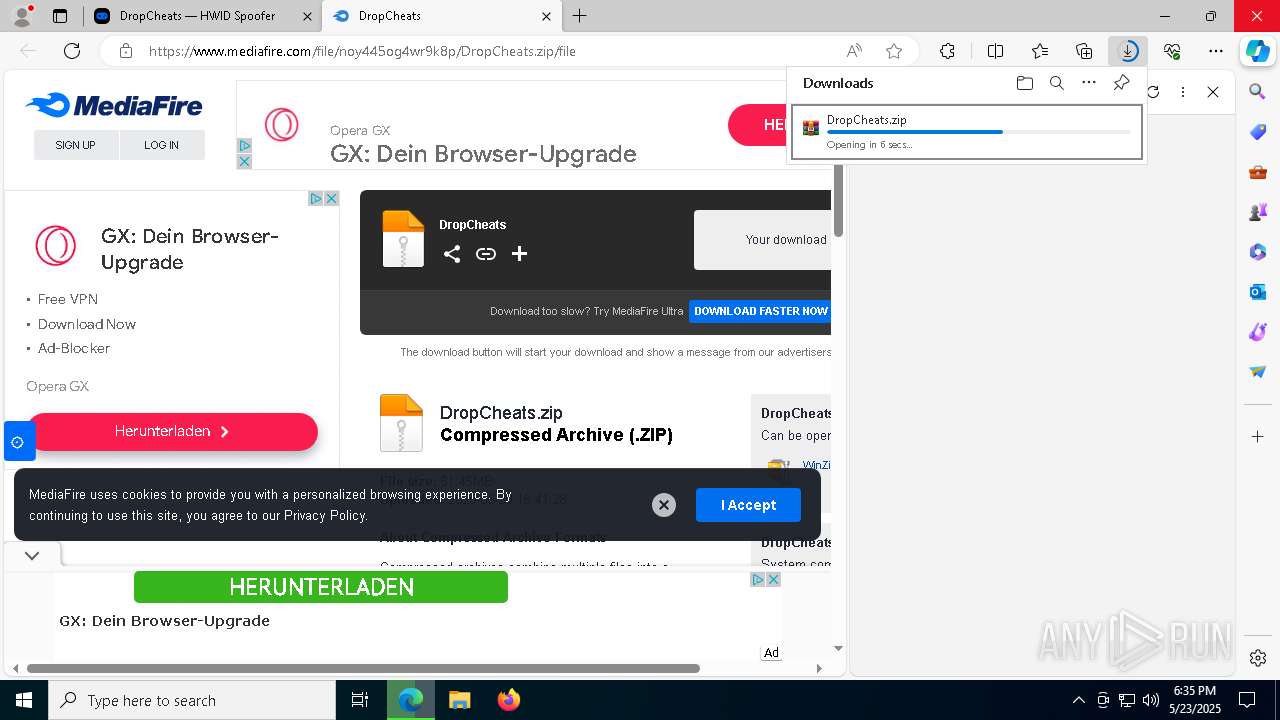
900 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |
900 | msedge.exe | Potentially Bad Traffic | ET HUNTING File Sharing Related Domain (www .mediafire .com) in DNS Lookup |