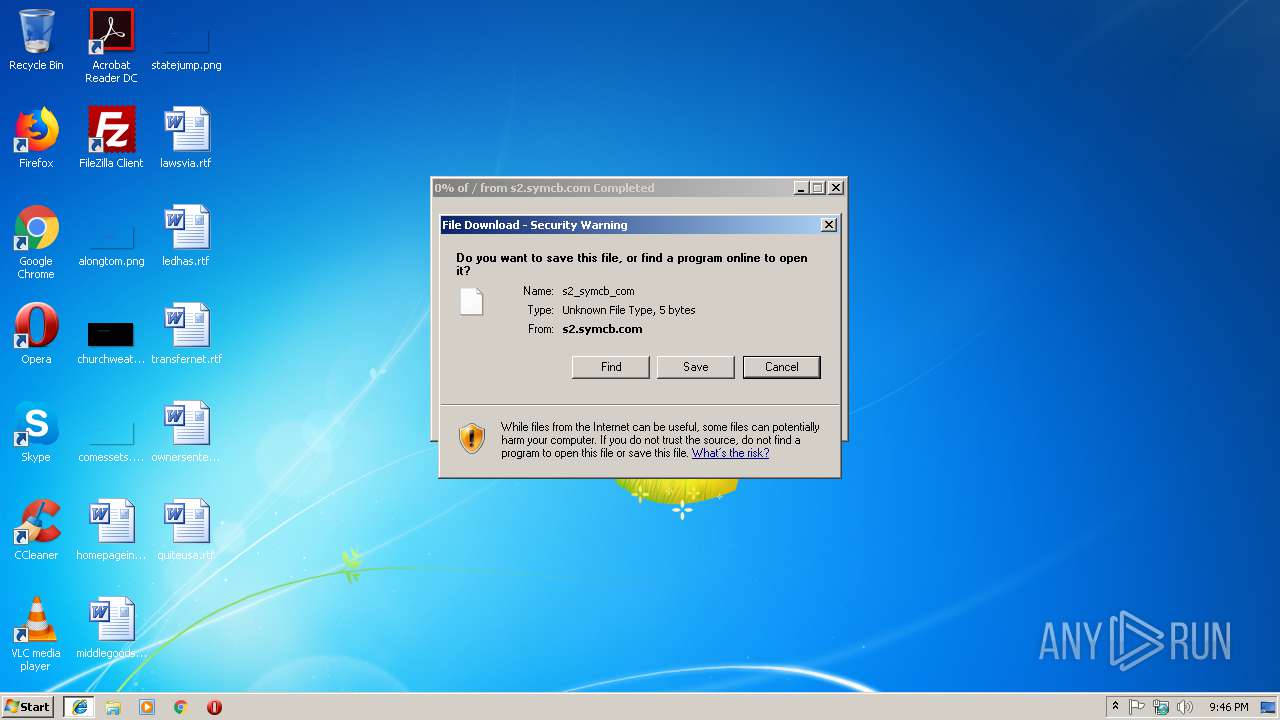
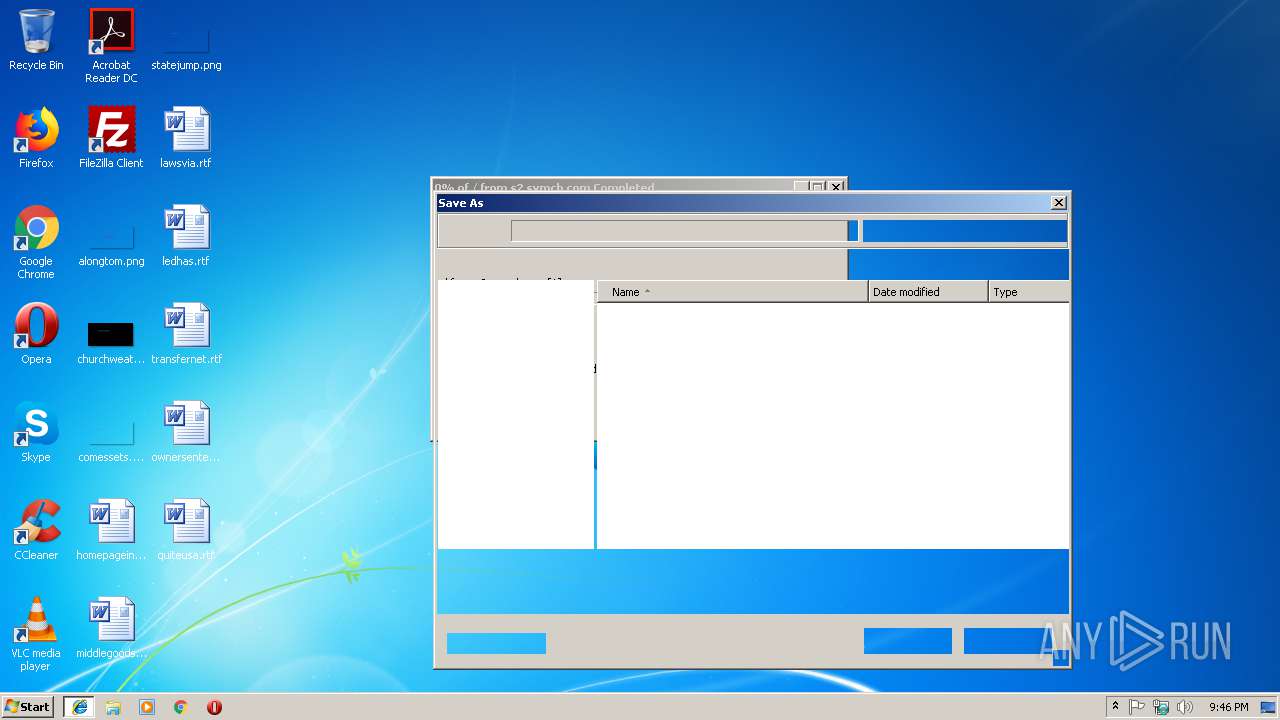
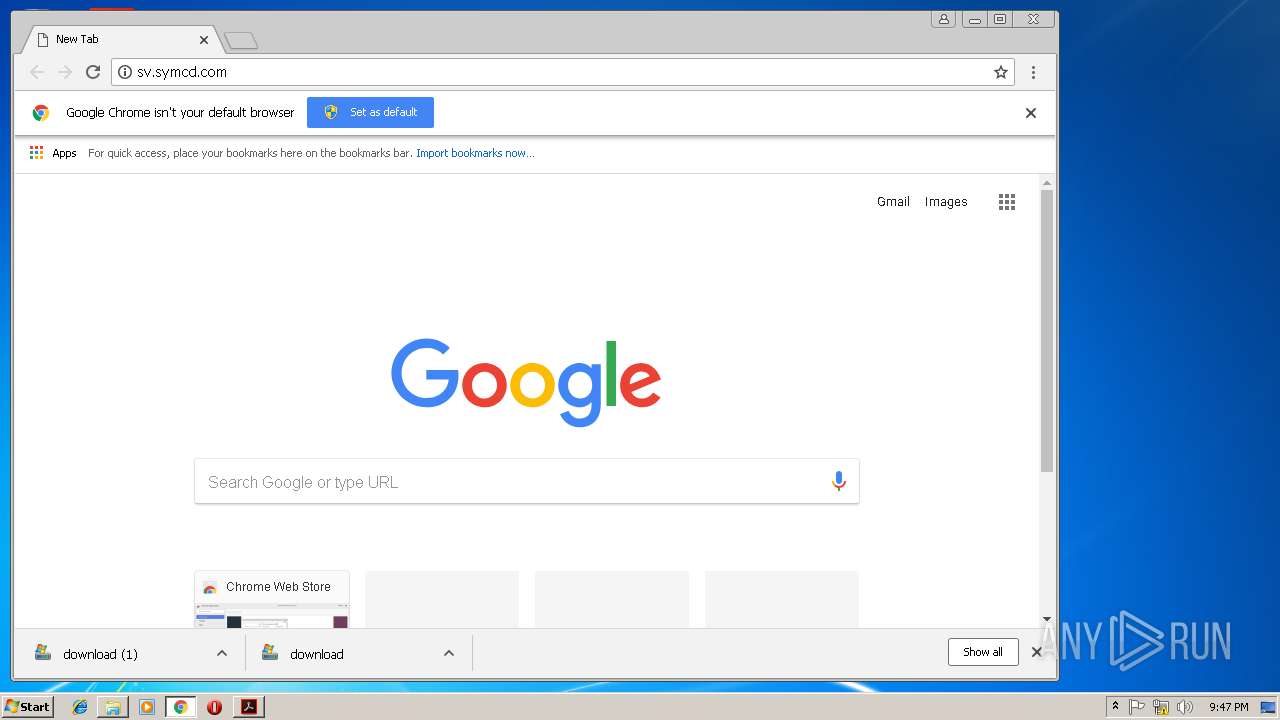
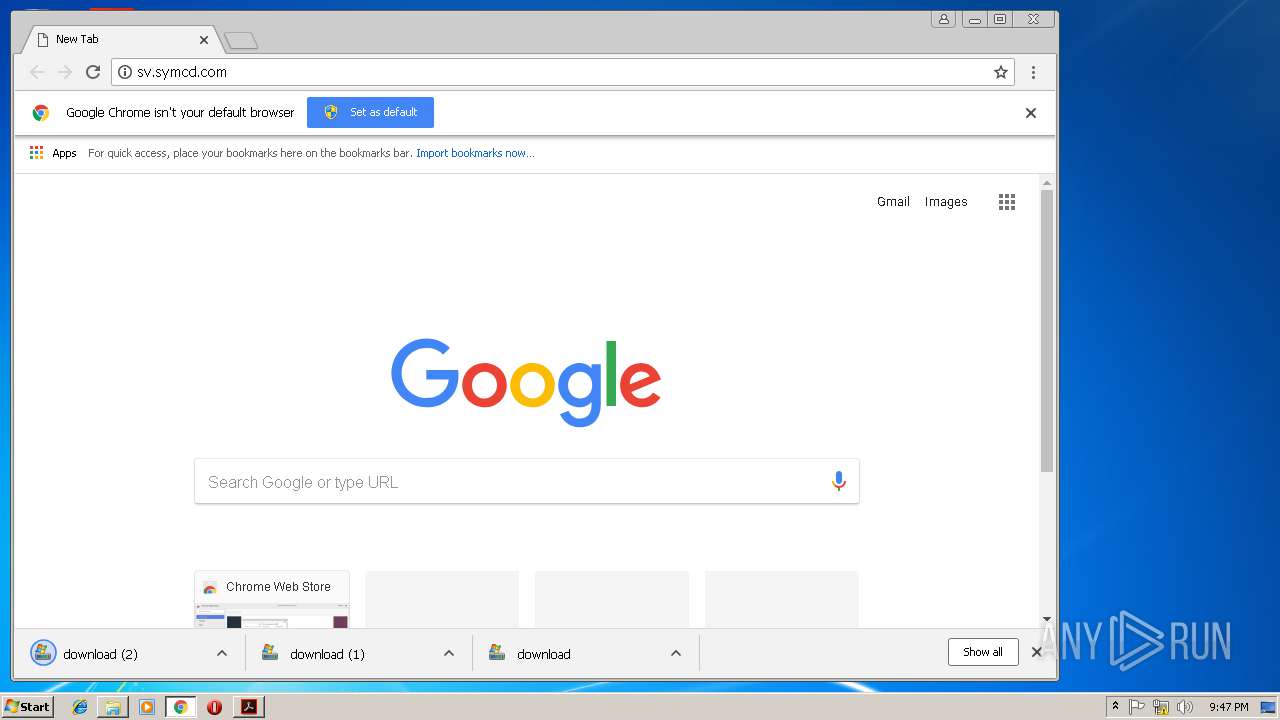
| URL: | http://s2.symcb.com |
| Full analysis: | https://app.any.run/tasks/f8b05dc0-b96a-458d-9650-ff3e2d2ce636 |
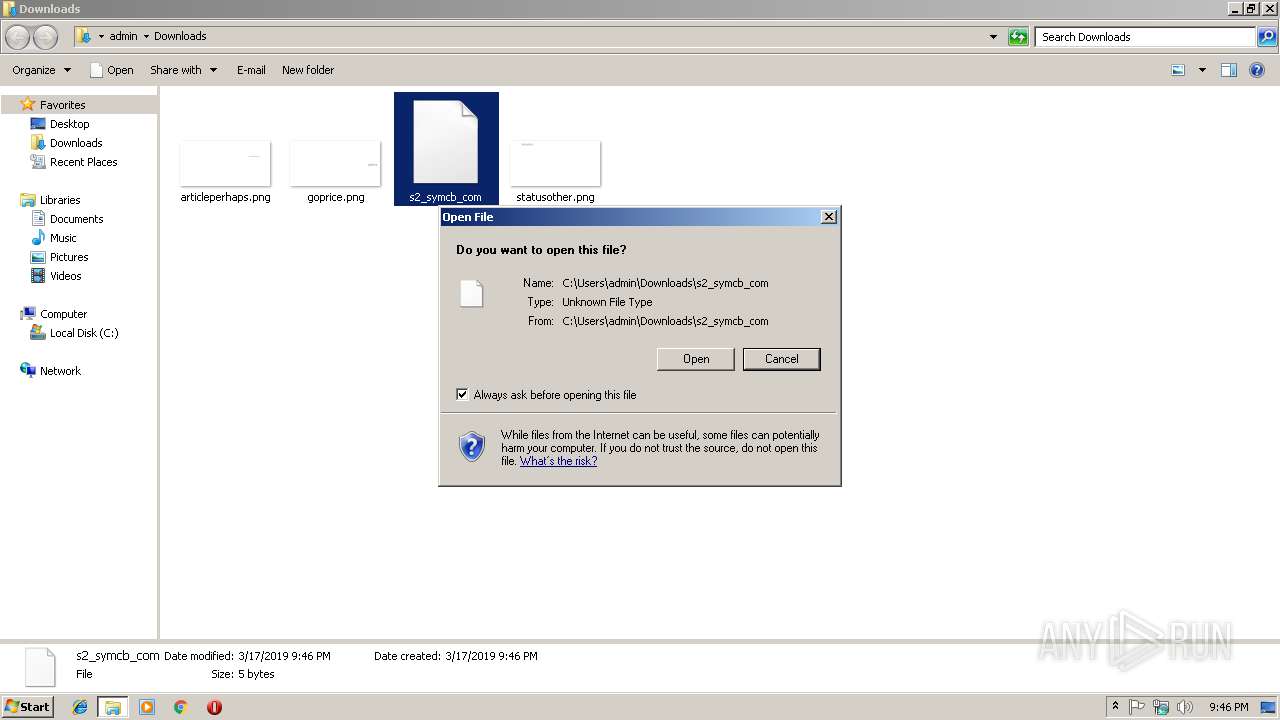
| Verdict: | Malicious activity |
| Analysis date: | March 17, 2019, 21:45:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1D4E6B3C0CA3AF29C9246DF1455935DC |
| SHA1: | B1195B2273D2D9F19D11FB849A41771B0DB5D508 |
| SHA256: | D62850433897EB15440E0F5509497178092EDCEDF09DC029999F42DE055D856D |
| SSDEEP: | 3:N1KNycIeK:CQcIx |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the program directory
- AdobeARM.exe (PID: 2948)
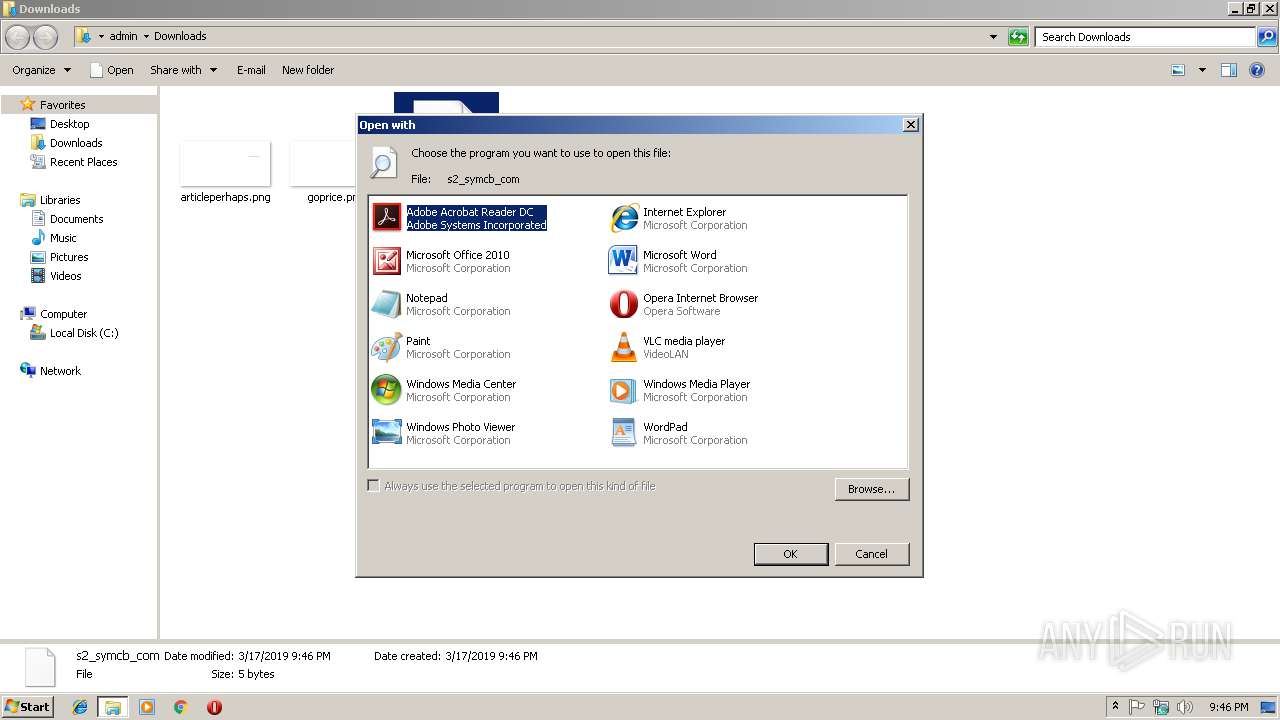
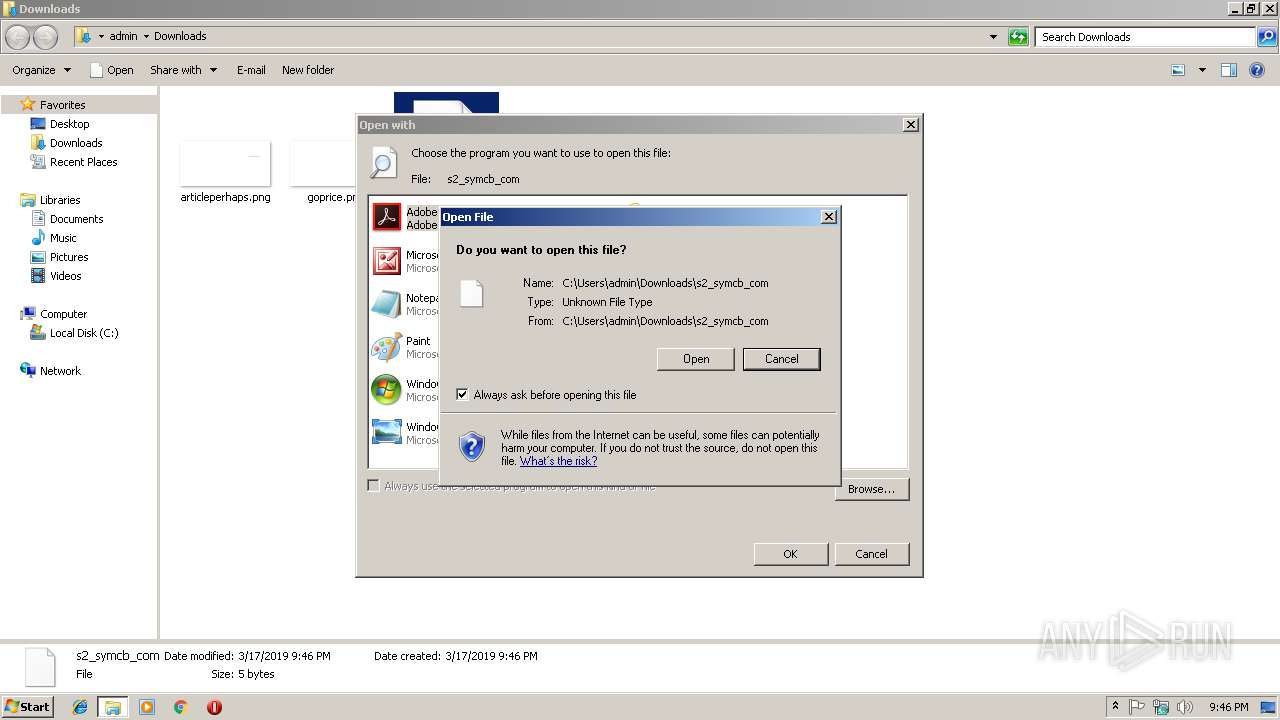
Uses RUNDLL32.EXE to load library
- chrome.exe (PID: 2168)
INFO
Application launched itself
- iexplore.exe (PID: 2916)
- AcroRd32.exe (PID: 3004)
- RdrCEF.exe (PID: 2564)
- chrome.exe (PID: 2168)
Changes internet zones settings
- iexplore.exe (PID: 2916)
Reads Internet Cache Settings
- iexplore.exe (PID: 2916)
- iexplore.exe (PID: 3208)
- chrome.exe (PID: 2168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
61
Monitored processes
27
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,724096389405454186,1677351058586871772,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=C0564C24EA4F09FE79E8BEEBC0E0F5FF --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C0564C24EA4F09FE79E8BEEBC0E0F5FF --renderer-client-id=15 --mojo-platform-channel-handle=1772 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\Reader_sl.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat SpeedLauncher Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,724096389405454186,1677351058586871772,131072 --enable-features=PasswordImport --service-pipe-token=61003CD4B112717643D399140E41ED5D --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=61003CD4B112717643D399140E41ED5D --renderer-client-id=5 --mojo-platform-channel-handle=1684 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2084 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,724096389405454186,1677351058586871772,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=97D0B7E113ABEEE72A81CEC450E5E93F --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=97D0B7E113ABEEE72A81CEC450E5E93F --renderer-client-id=9 --mojo-platform-channel-handle=4348 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,724096389405454186,1677351058586871772,131072 --enable-features=PasswordImport --service-pipe-token=2D63E35DA5949C0988995E7DCA20E926 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2D63E35DA5949C0988995E7DCA20E926 --renderer-client-id=3 --mojo-platform-channel-handle=2108 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2188 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2564 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,724096389405454186,1677351058586871772,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=40ED4D430649794E7674C1FDCFC0F47C --mojo-platform-channel-handle=4160 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
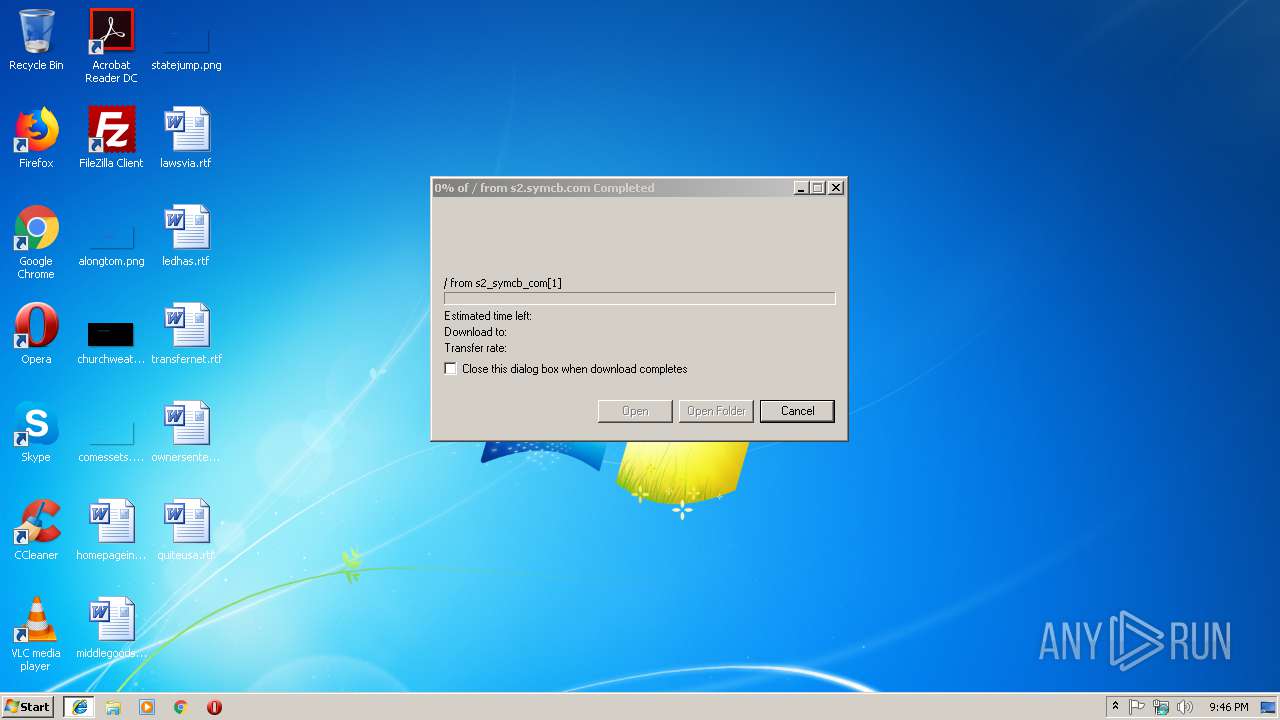
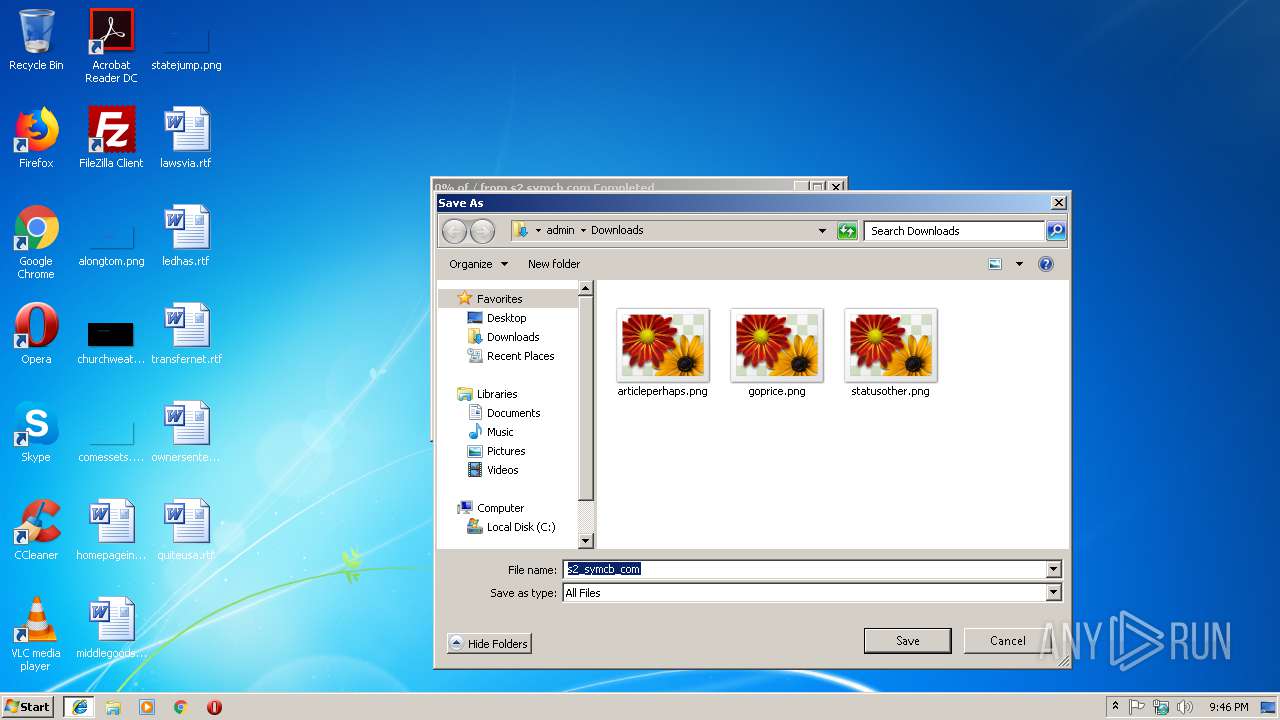
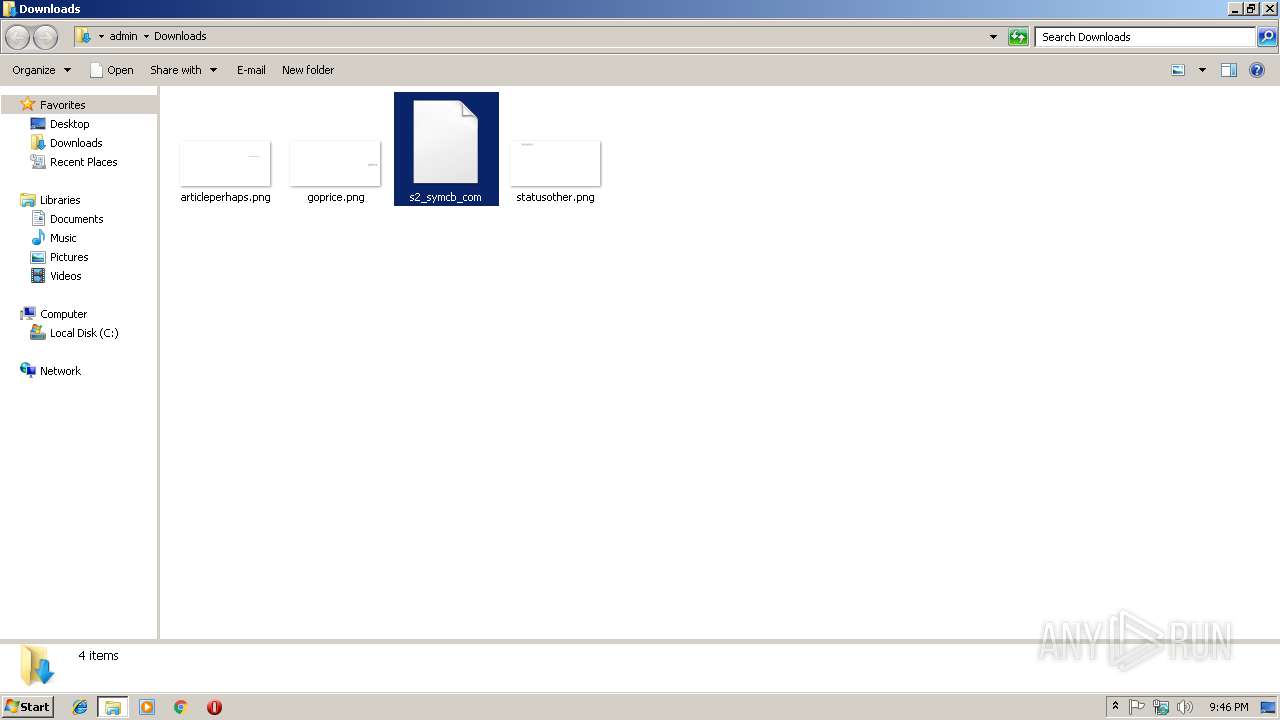
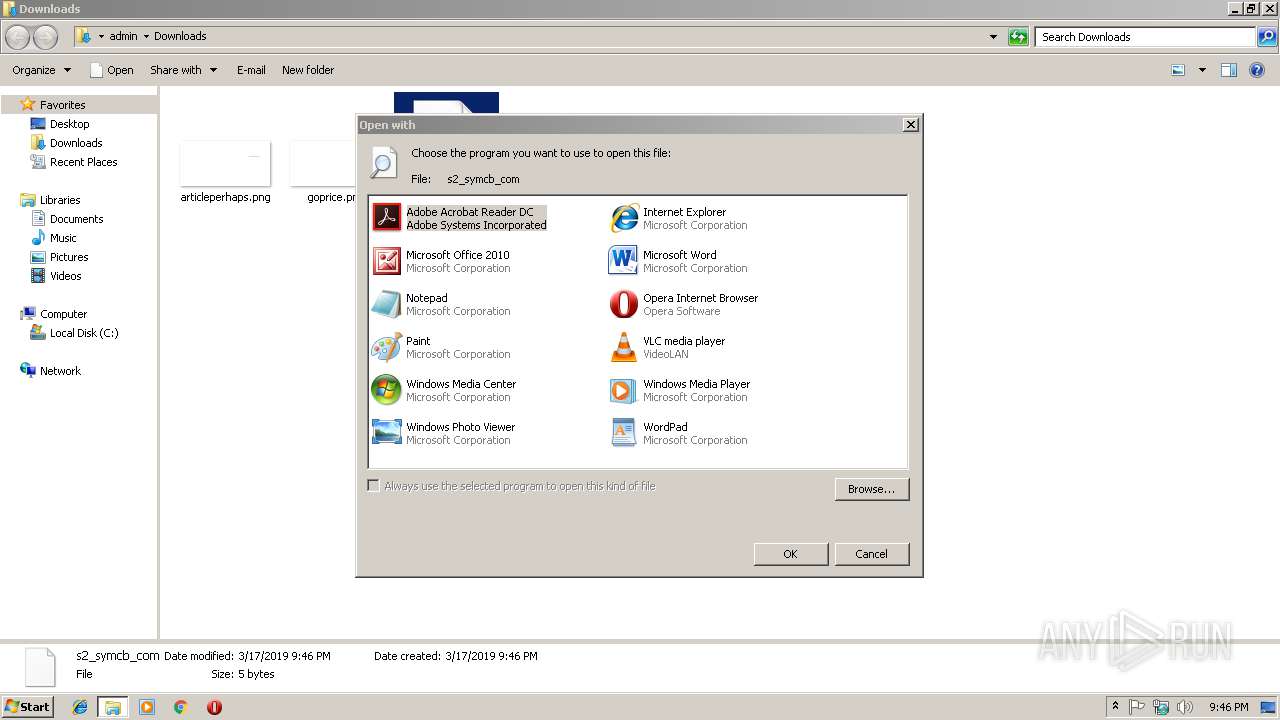
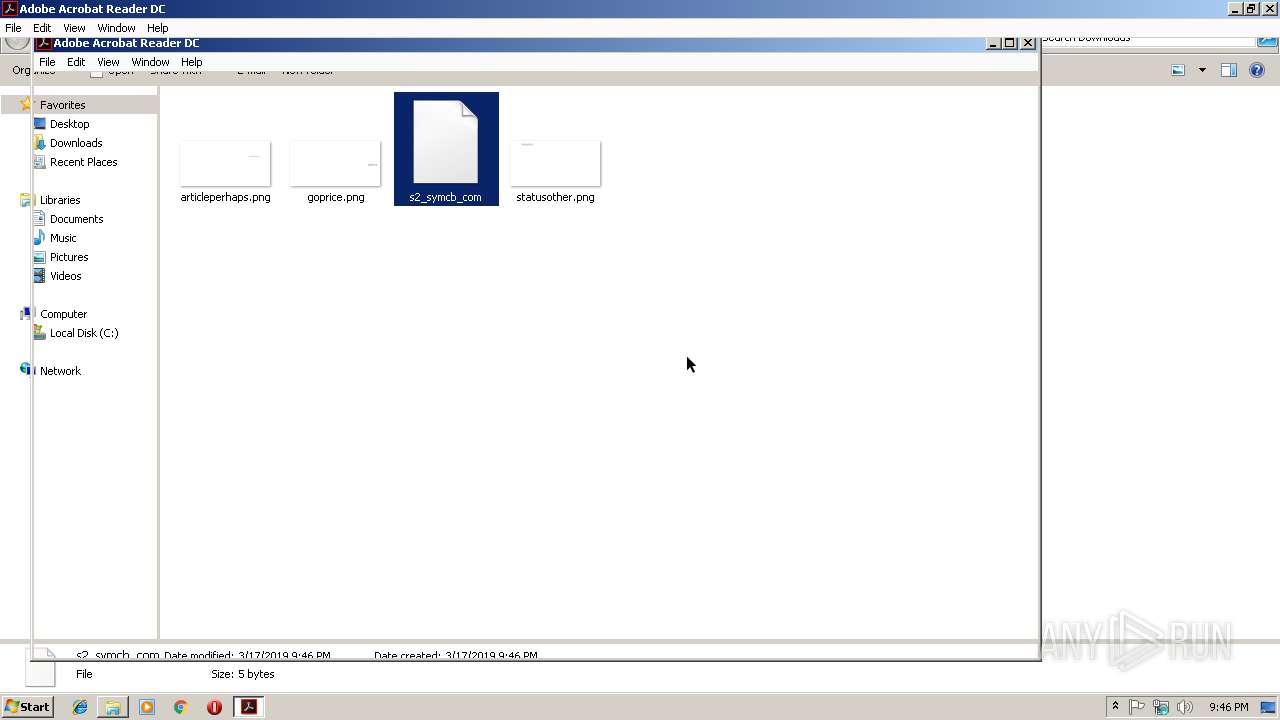
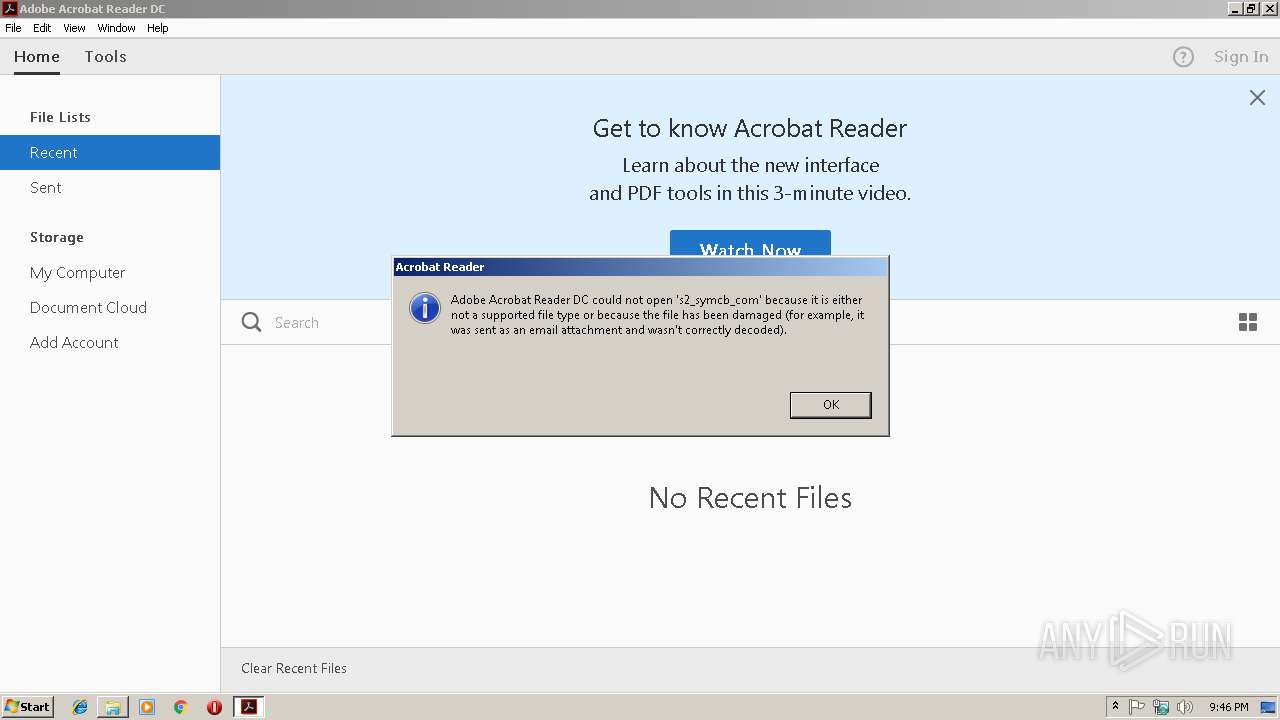
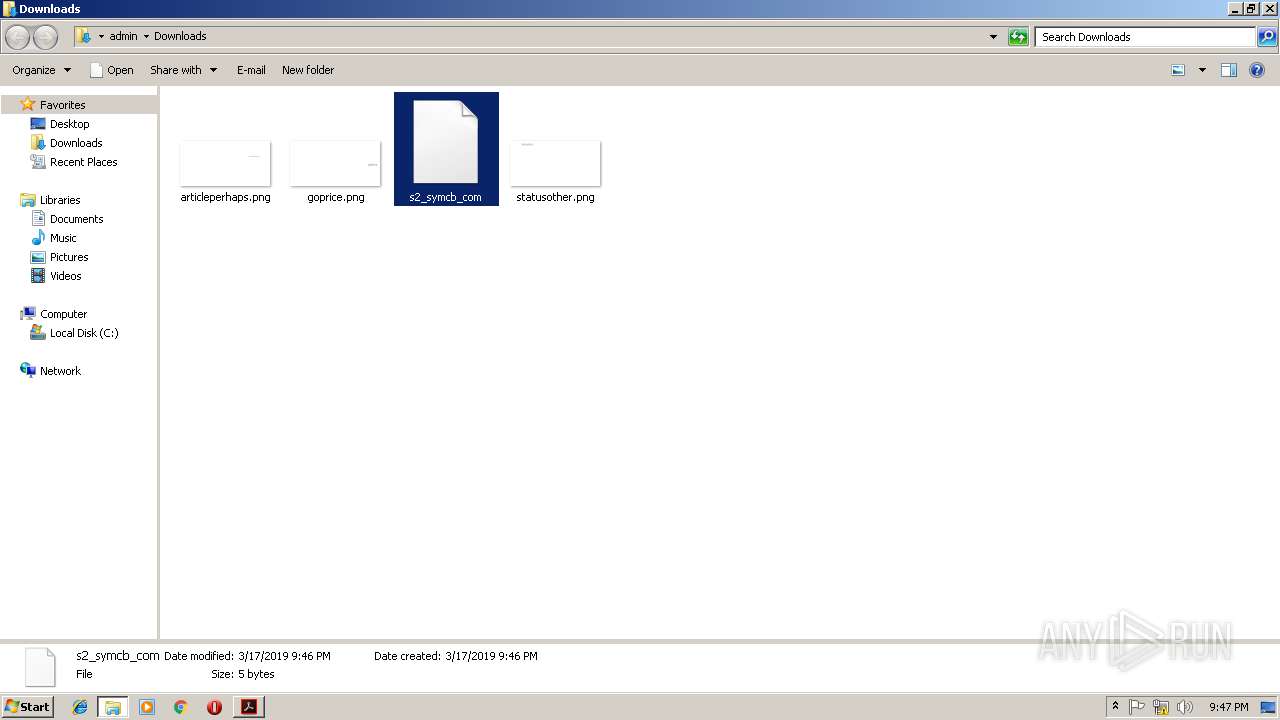
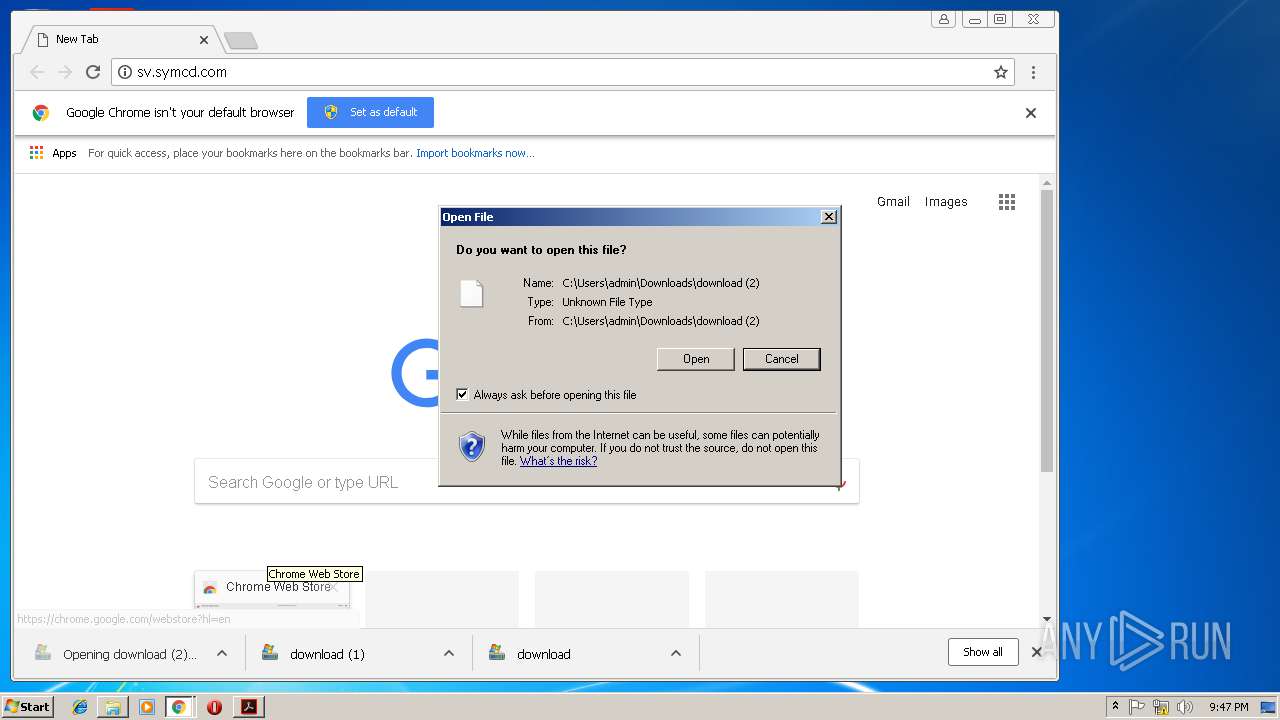
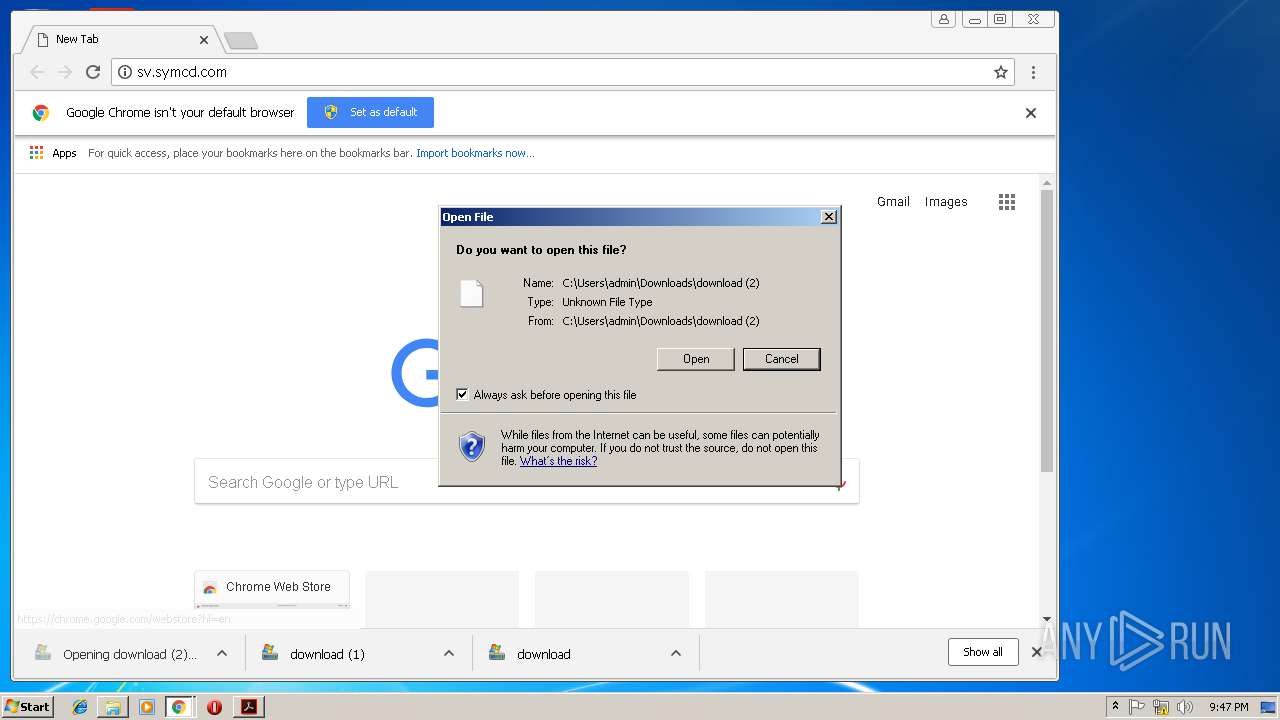
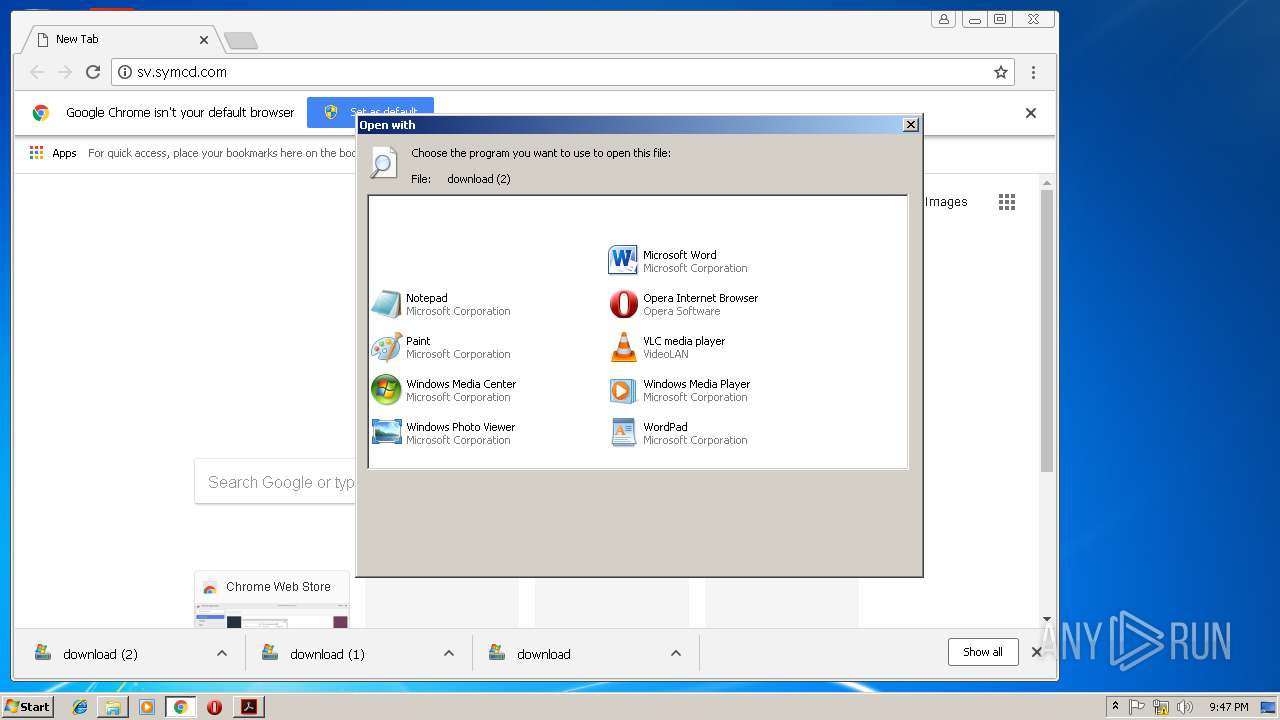
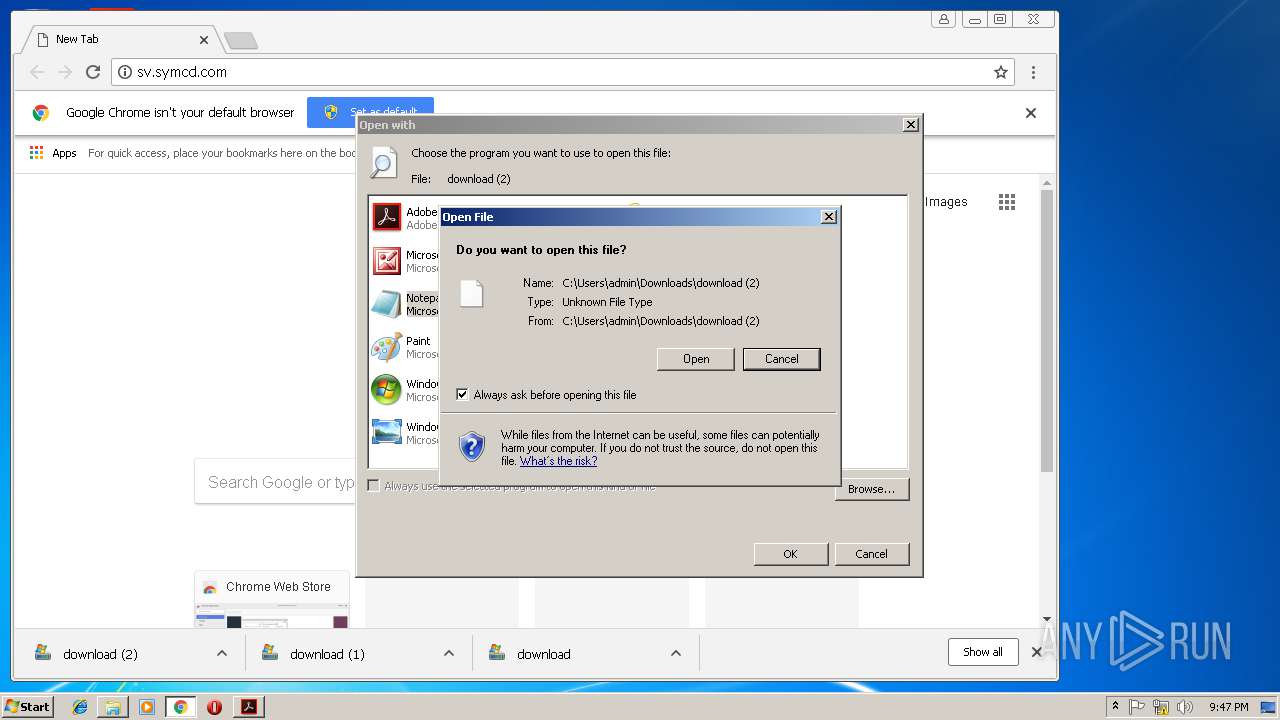
| 2628 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\s2_symcb_com | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 954
Read events
2 614
Write events
331
Delete events
9
Modification events
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {0F67C909-48FE-11E9-BAD8-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2916) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E30703000000110015002E000400FF01 | |||
Executable files
0
Suspicious files
64
Text files
110
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2916 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2916 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2916 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFBE1F73A5E69F57B8.TMP | — | |
MD5:— | SHA256:— | |||
| 2916 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF86F129DE570501C9.TMP | — | |
MD5:— | SHA256:— | |||
| 2916 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{0F67C909-48FE-11E9-BAD8-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2728 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 2728 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1dgo4fq_p9fffp_23s.tmp | — | |
MD5:— | SHA256:— | |||
| 2728 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rio5hdr_p9fffq_23s.tmp | — | |
MD5:— | SHA256:— | |||
| 2728 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rm3iu7_p9fffr_23s.tmp | — | |
MD5:— | SHA256:— | |||
| 2728 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R71caed_p9fffs_23s.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
37
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3004 | AcroRd32.exe | GET | 304 | 2.16.186.27:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/279_15_23_20070.zip | unknown | — | — | whitelisted |
3004 | AcroRd32.exe | GET | 304 | 2.16.186.27:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
3004 | AcroRd32.exe | GET | 304 | 2.16.186.27:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
3004 | AcroRd32.exe | GET | 304 | 2.16.186.27:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
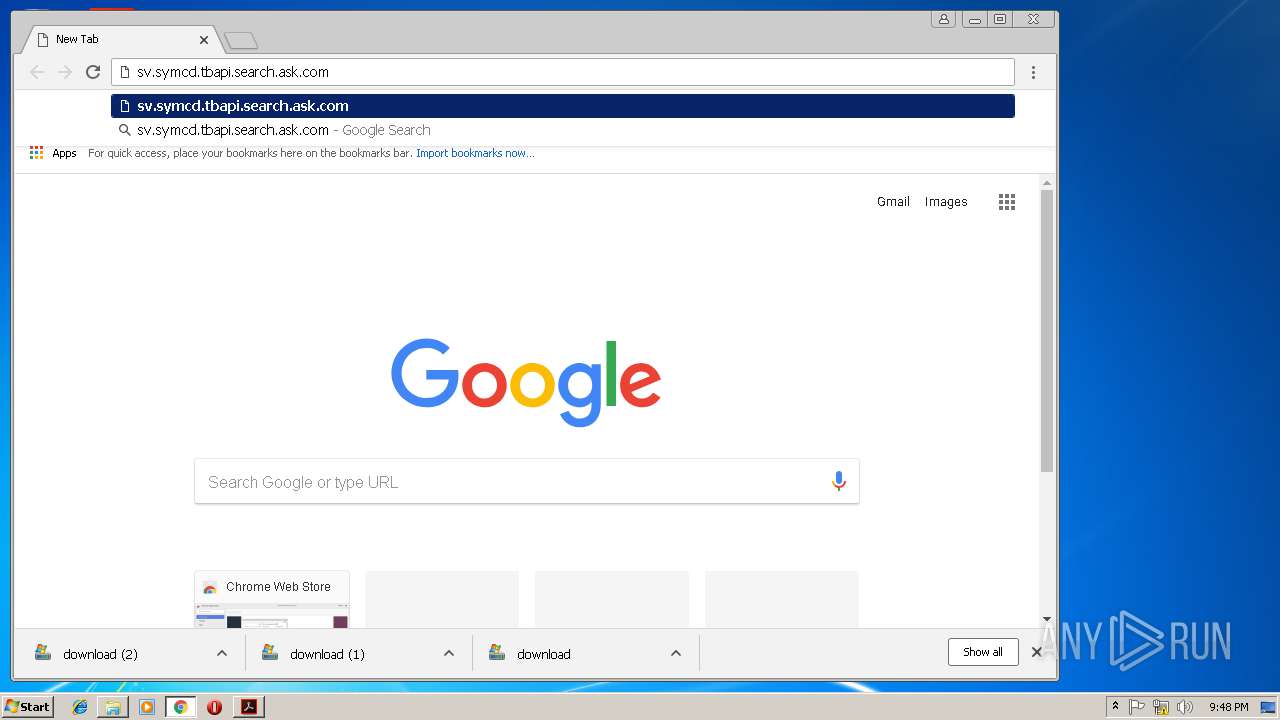
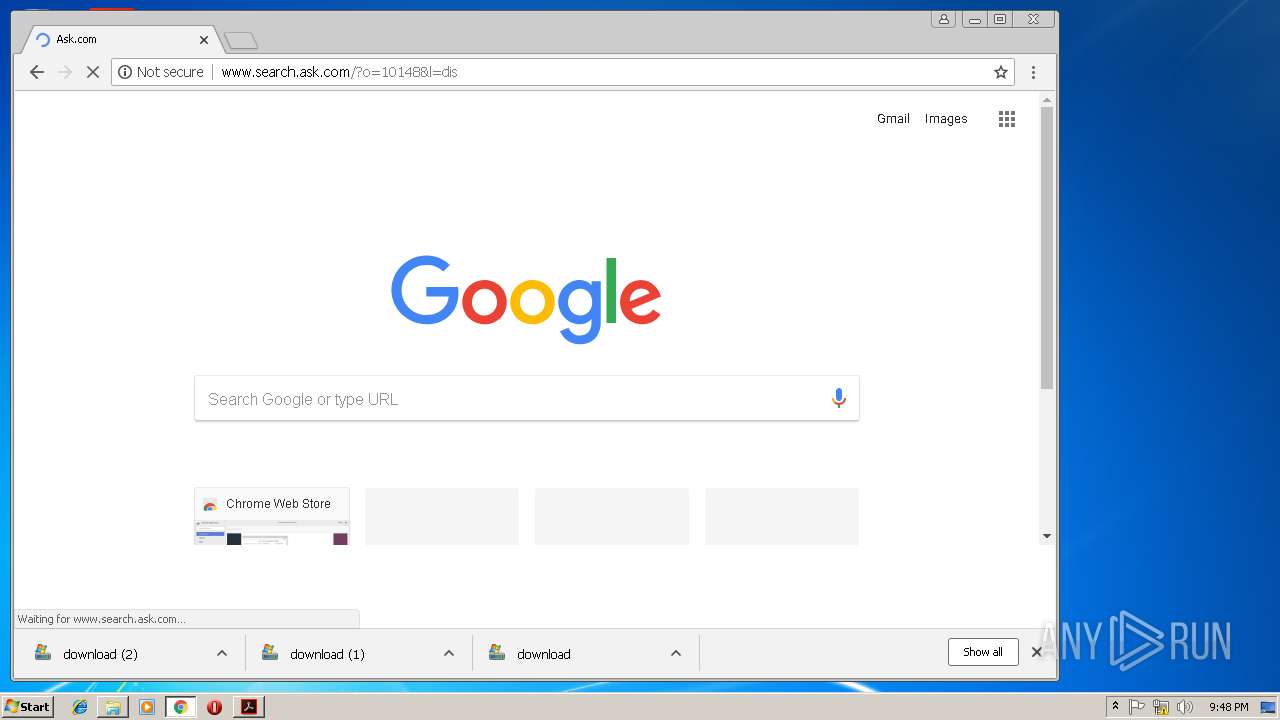
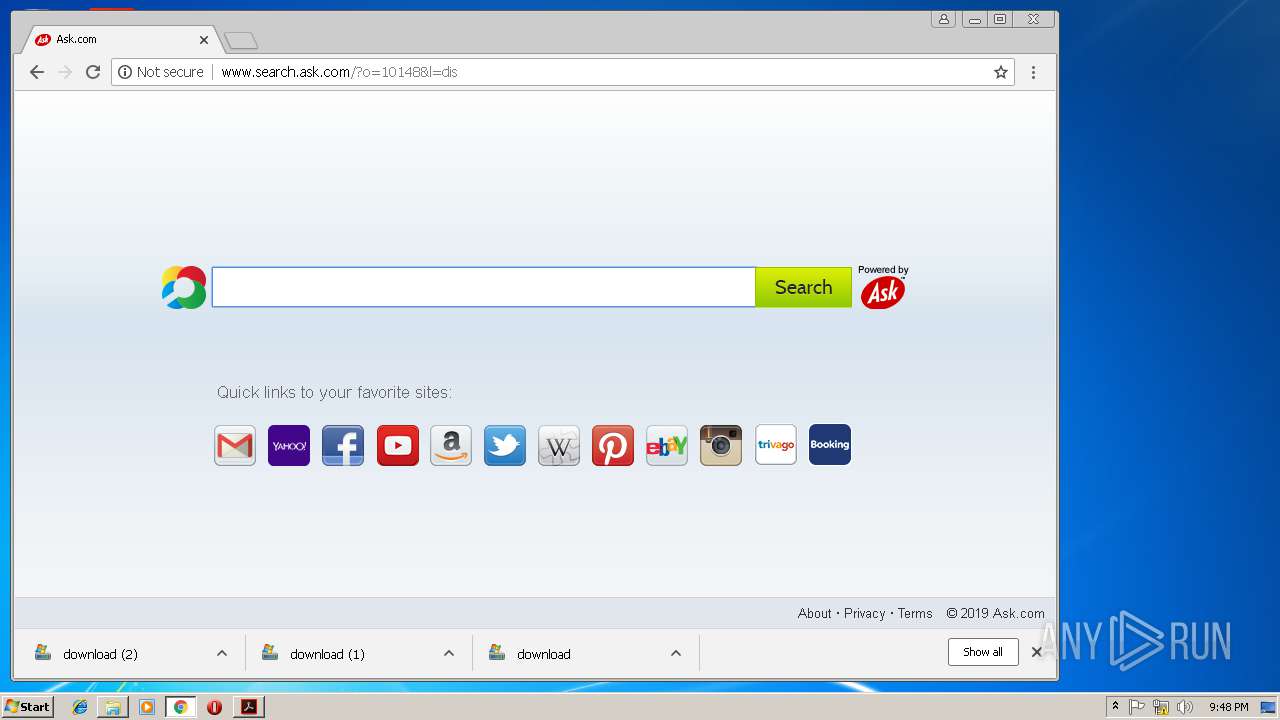
2168 | chrome.exe | GET | 204 | 104.109.80.67:80 | http://www.search.ask.com/ulpixel?anxuu=5352A4E3-96FB-4923-A273-BD170AD461AD&anxa=APNSearchOasis&anxv=0e2db84e81a69446cbfd439afe1677e0a9cff6b3&anxd=2019-03-13T00%3A00%3A00Z&anxsn=&anxu=http%3A%2F%2Fwww.search.ask.com%2F&anxl=en-US&anxlv=1552859293234&anxrd=none&anxrp=-&anxrk=-&anxrm=-&anxrb=-&anxrc=-&anxrs=-&anxsq=2&q=&tpr=&userip=185.212.170.83&acpt=homepage&acoc=10148&l=dis&acst=bar&anxi=a5fa5b4f-c482-4ab3-b830-599a440c9c7e&du=1&anxe=backFill&anxr=734268060 | NL | — | — | whitelisted |
2168 | chrome.exe | GET | 204 | 74.113.235.189:80 | http://anx.apnanalytics.com/ | IE | — | — | malicious |
2168 | chrome.exe | GET | — | 199.36.102.106:80 | http://tbapi.search.ask.com/ | US | — | — | whitelisted |
2168 | chrome.exe | GET | 200 | 104.109.80.67:80 | http://www.search.ask.com/assets/js/ask/ask-min-8b09a2d368f4139df2812d232dd90546.js | NL | text | 35.6 Kb | whitelisted |
2168 | chrome.exe | GET | 200 | 104.109.80.67:80 | http://www.search.ask.com/assets/common/ask_flower_03b_24bit_07_sprite.png | NL | image | 84.4 Kb | whitelisted |
2168 | chrome.exe | GET | 200 | 104.109.80.67:80 | http://www.search.ask.com/favicon.ico | NL | image | 1.12 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2168 | chrome.exe | 216.58.207.78:443 | apis.google.com | Google Inc. | US | whitelisted |
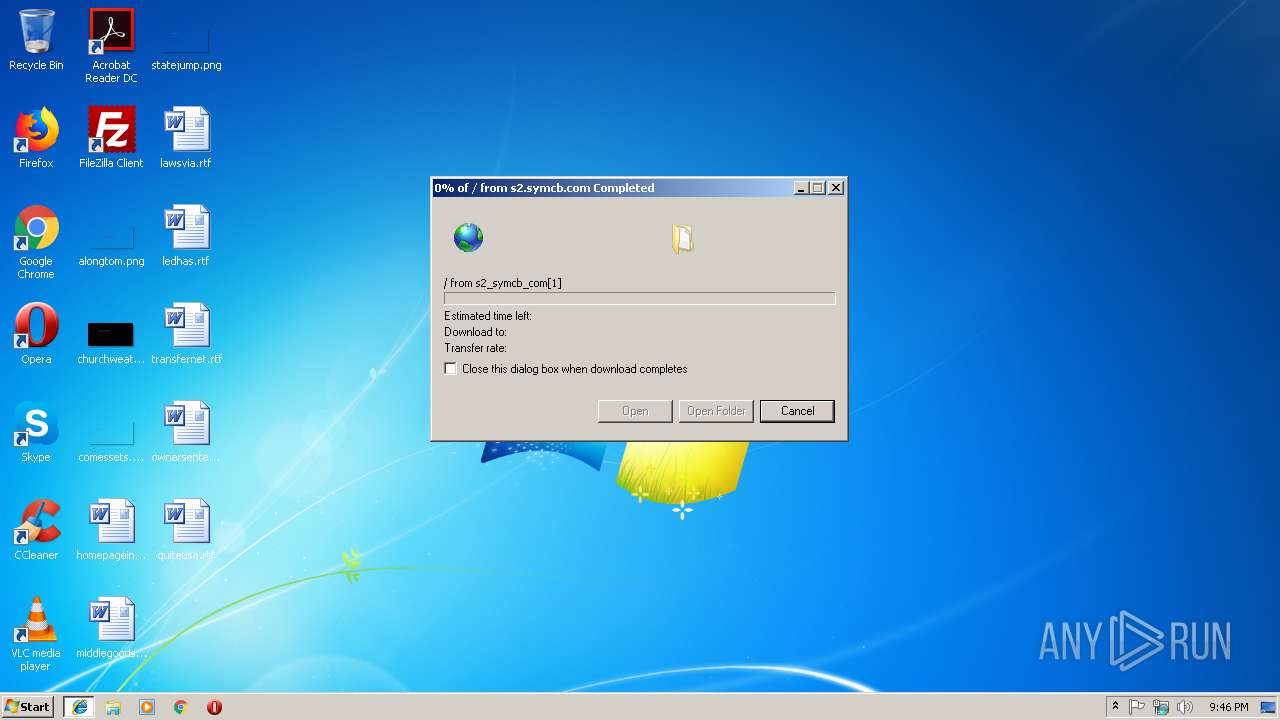
2168 | chrome.exe | 23.51.123.27:80 | s2.symcb.com | Akamai Technologies, Inc. | NL | whitelisted |
2168 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
2916 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3208 | iexplore.exe | 23.51.123.27:80 | s2.symcb.com | Akamai Technologies, Inc. | NL | whitelisted |
3004 | AcroRd32.exe | 2.16.186.27:80 | acroipm2.adobe.com | Akamai International B.V. | — | whitelisted |
3004 | AcroRd32.exe | 2.21.36.203:443 | armmf.adobe.com | GTT Communications Inc. | FR | suspicious |
2168 | chrome.exe | 172.217.16.163:443 | www.google.de | Google Inc. | US | whitelisted |
2168 | chrome.exe | 216.58.210.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2168 | chrome.exe | 172.217.16.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
s2.symcb.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |