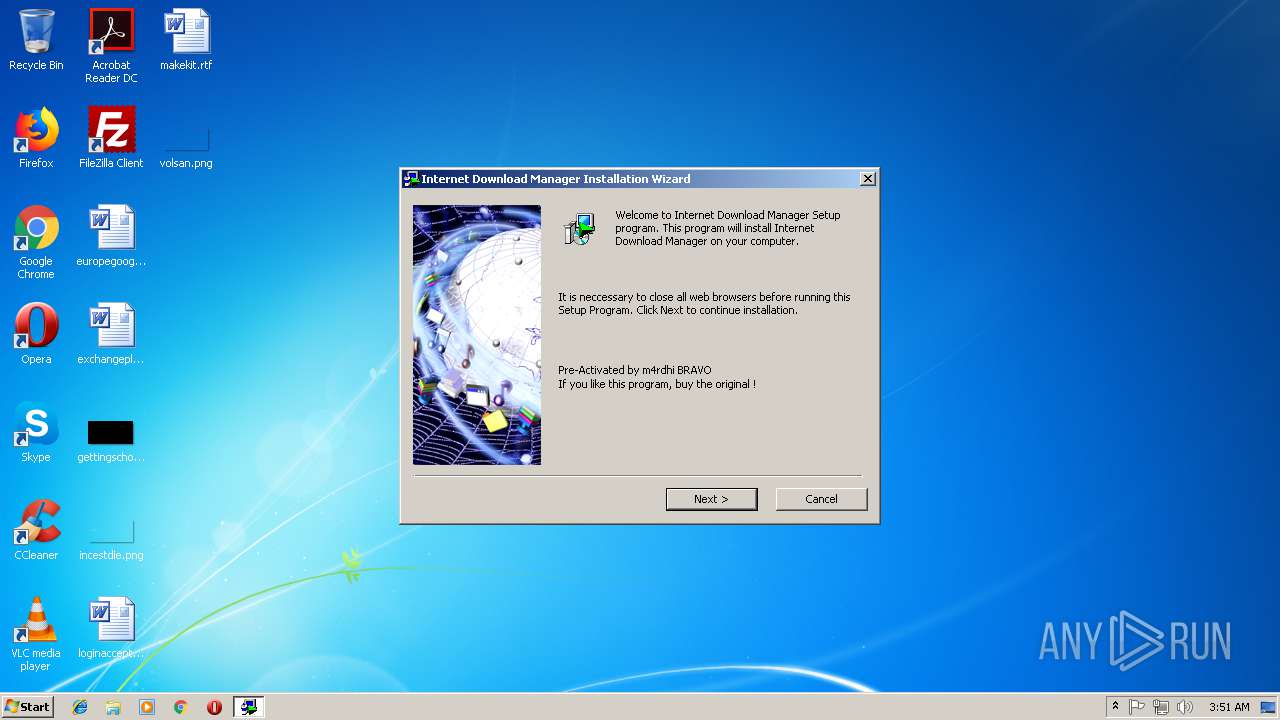
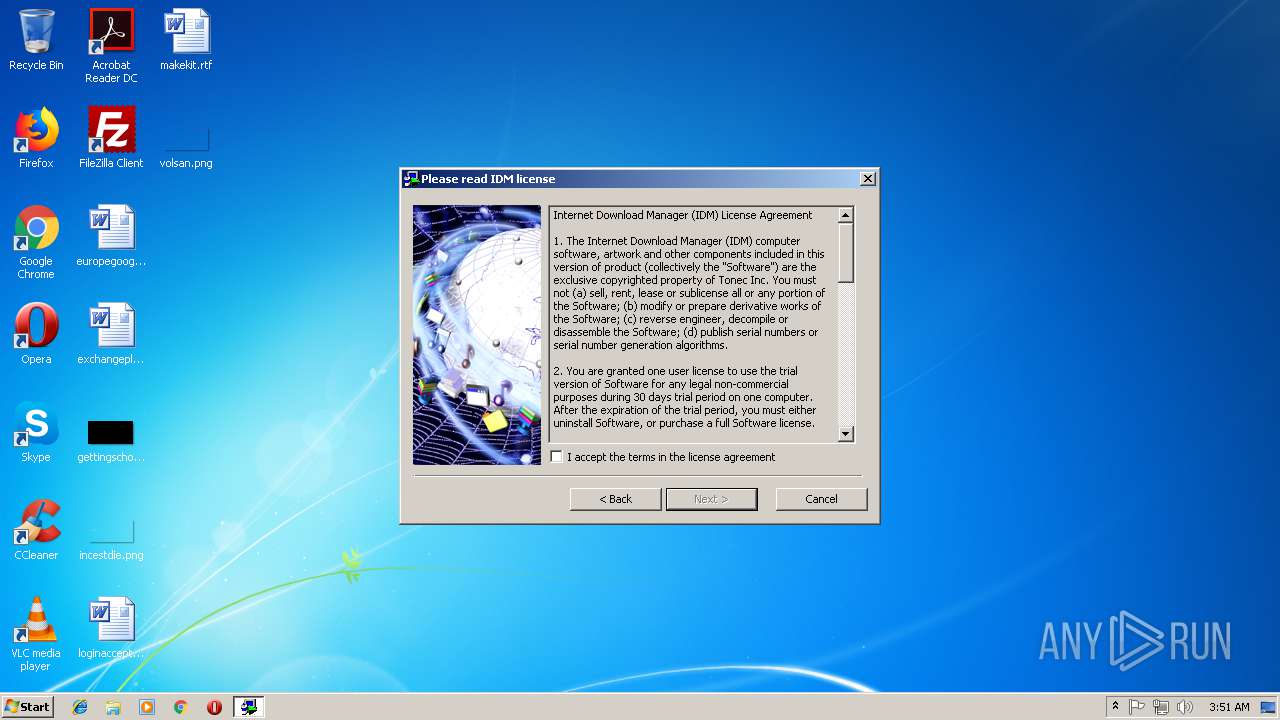
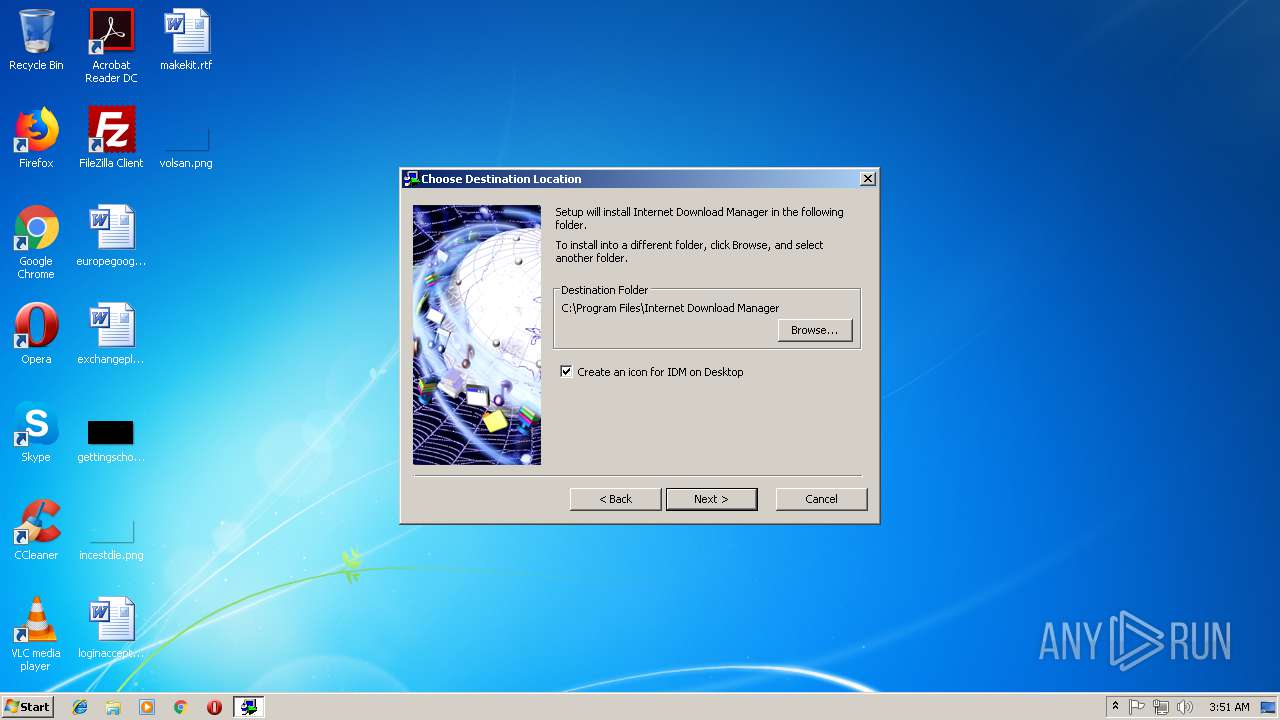
| File name: | Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe |
| Full analysis: | https://app.any.run/tasks/7af872bc-7156-49f5-b8c8-da8dba1cd61e |
| Verdict: | Malicious activity |
| Analysis date: | September 29, 2018, 02:50:50 |
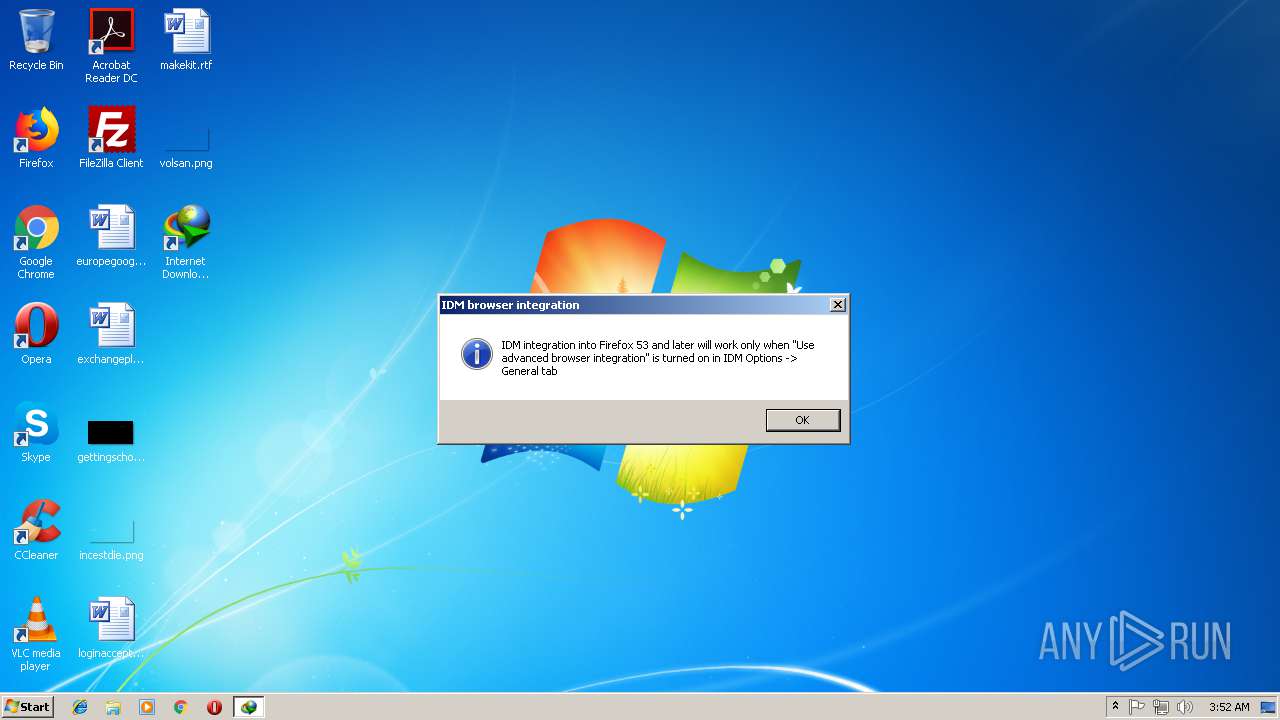
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 2AE11933B5FA4DA647BCCD62E6F4FBC9 |
| SHA1: | A16E51CAA732C97297356A1D6F72D975F0B3A72B |
| SHA256: | D618ADF897D2B3E2A5AEFEBD0993662A28FF2BCADABB2753A8CCA5E57E5E1403 |
| SSDEEP: | 98304:Ei9K++HrihKvdcq4OSLOUQZwI7W7HYbm2UCcOosE9m0BP:EAeHrl1cVQwF74s/M0F |
MALICIOUS
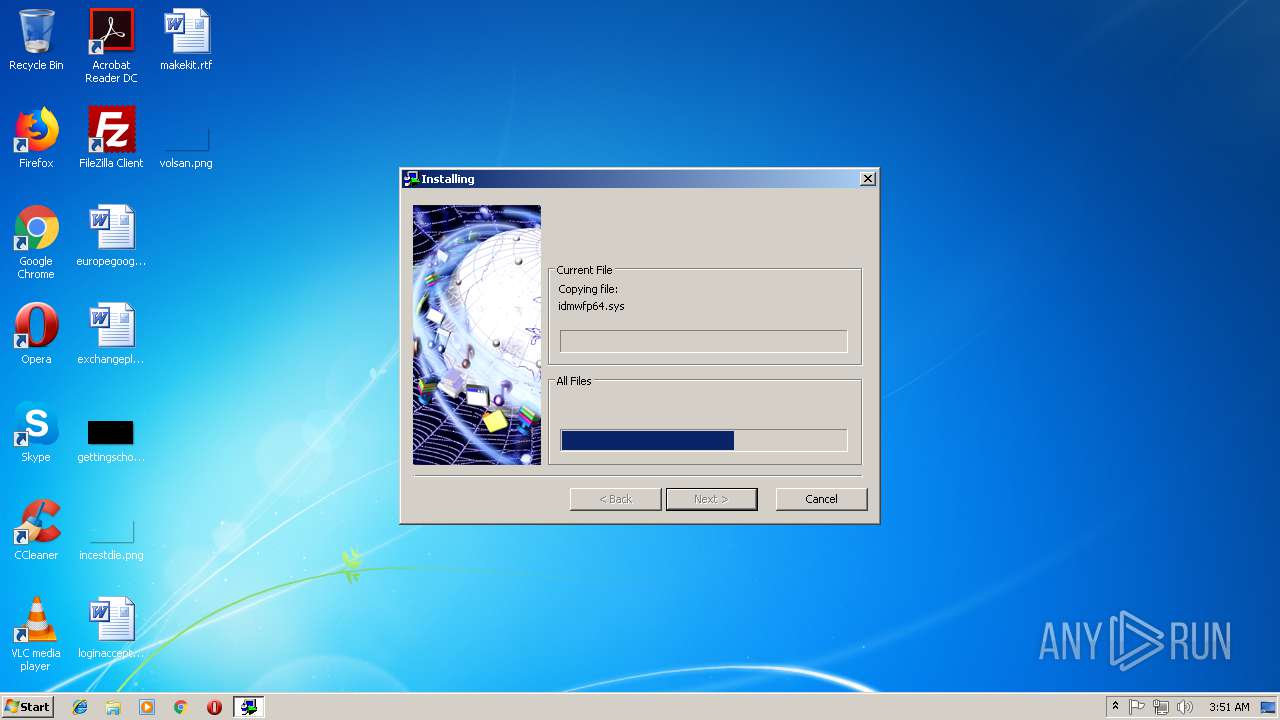
Loads dropped or rewritten executable
- Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe (PID: 3584)
- IDMan.exe (PID: 3428)
- IDM1.tmp (PID: 2584)
- Uninstall.exe (PID: 884)
- explorer.exe (PID: 1604)
- svchost.exe (PID: 852)
- IEMonitor.exe (PID: 3972)
- chrome.exe (PID: 3076)
- IDMan.exe (PID: 2432)
Application was dropped or rewritten from another process
- IDM1.tmp (PID: 2584)
- IDMan.exe (PID: 3428)
- idmBroker.exe (PID: 3132)
- Uninstall.exe (PID: 884)
- MediumILStart.exe (PID: 892)
- IDMan.exe (PID: 2432)
- IEMonitor.exe (PID: 3972)
Changes the autorun value in the registry
- rundll32.exe (PID: 2692)
- IDMan.exe (PID: 3428)
Starts NET.EXE for service management
- Uninstall.exe (PID: 884)
Changes settings of System certificates
- svchost.exe (PID: 852)
SUSPICIOUS
Executable content was dropped or overwritten
- Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe (PID: 3584)
- rundll32.exe (PID: 2692)
- IDMan.exe (PID: 3428)
Starts application with an unusual extension
- Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe (PID: 3584)
Creates files in the user directory
- IDM1.tmp (PID: 2584)
- IDMan.exe (PID: 3428)
- IDMan.exe (PID: 2432)
Creates COM task schedule object
- IDM1.tmp (PID: 2584)
- IDMan.exe (PID: 3428)
- Uninstall.exe (PID: 884)
Creates a software uninstall entry
- IDM1.tmp (PID: 2584)
Creates files in the program directory
- IDMan.exe (PID: 3428)
- IDM1.tmp (PID: 2584)
Creates files in the Windows directory
- rundll32.exe (PID: 2692)
Removes files from Windows directory
- rundll32.exe (PID: 2692)
Creates or modifies windows services
- Uninstall.exe (PID: 884)
Creates files in the driver directory
- rundll32.exe (PID: 2692)
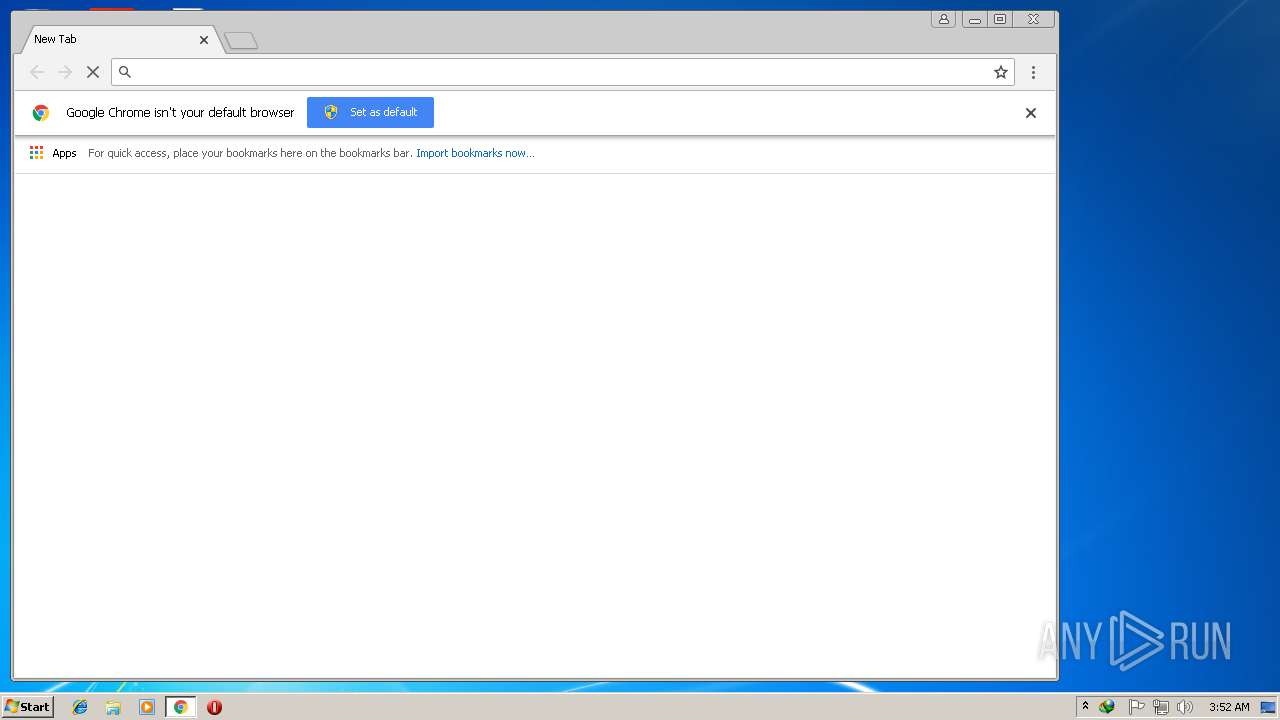
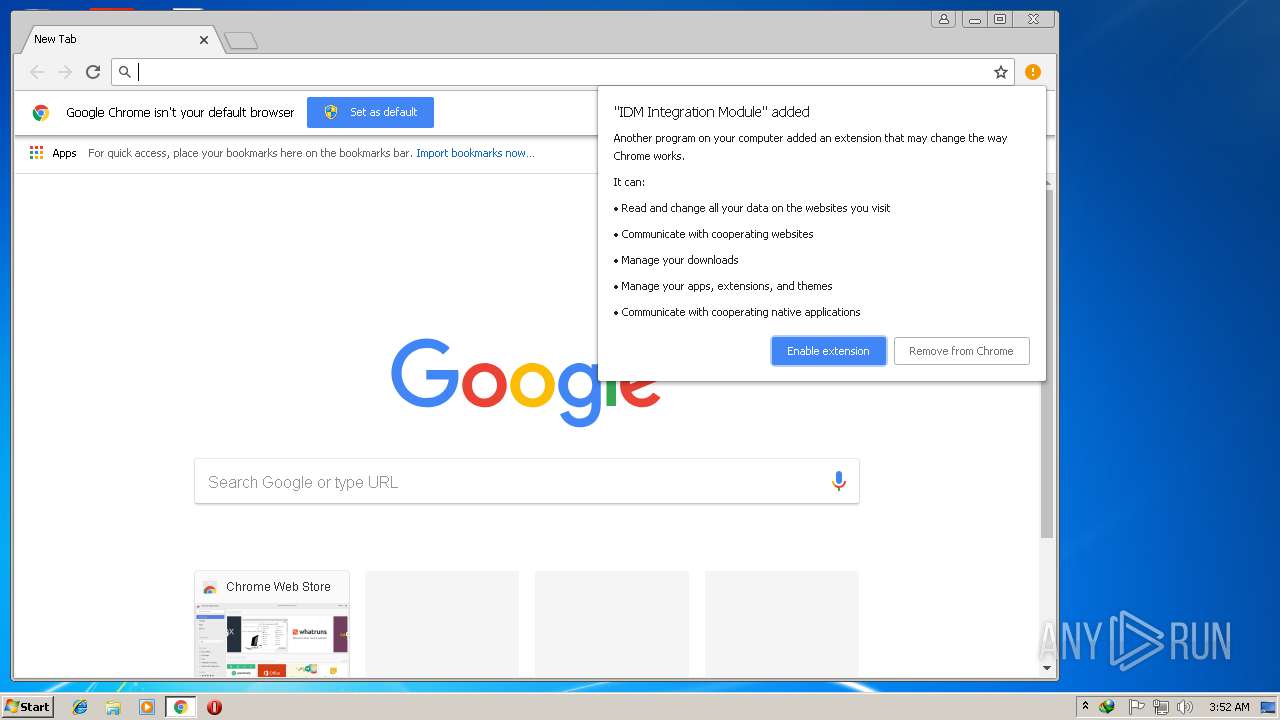
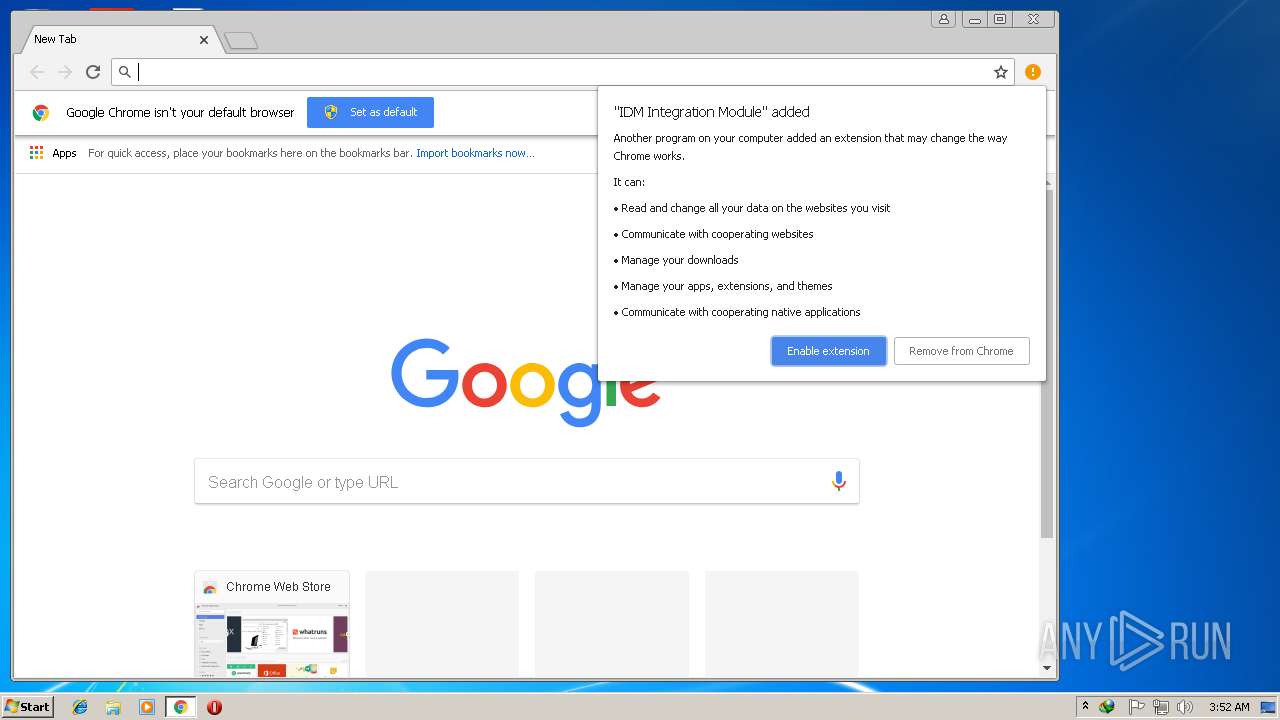
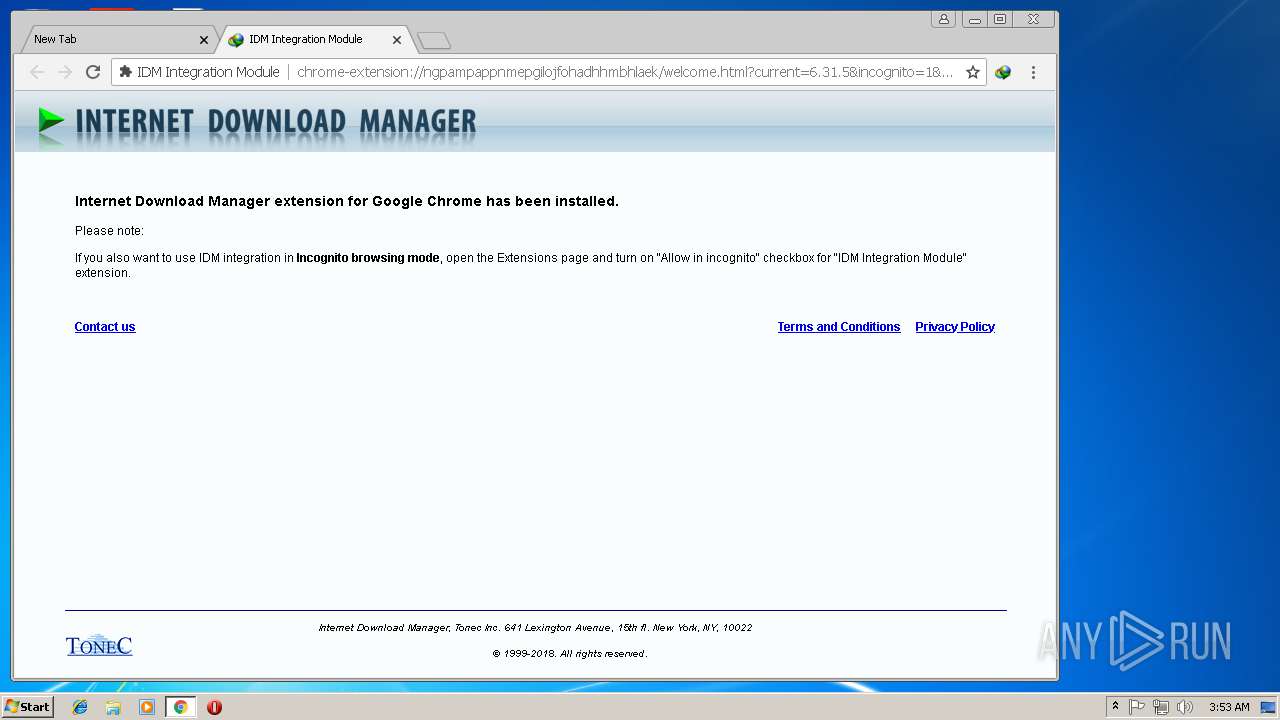
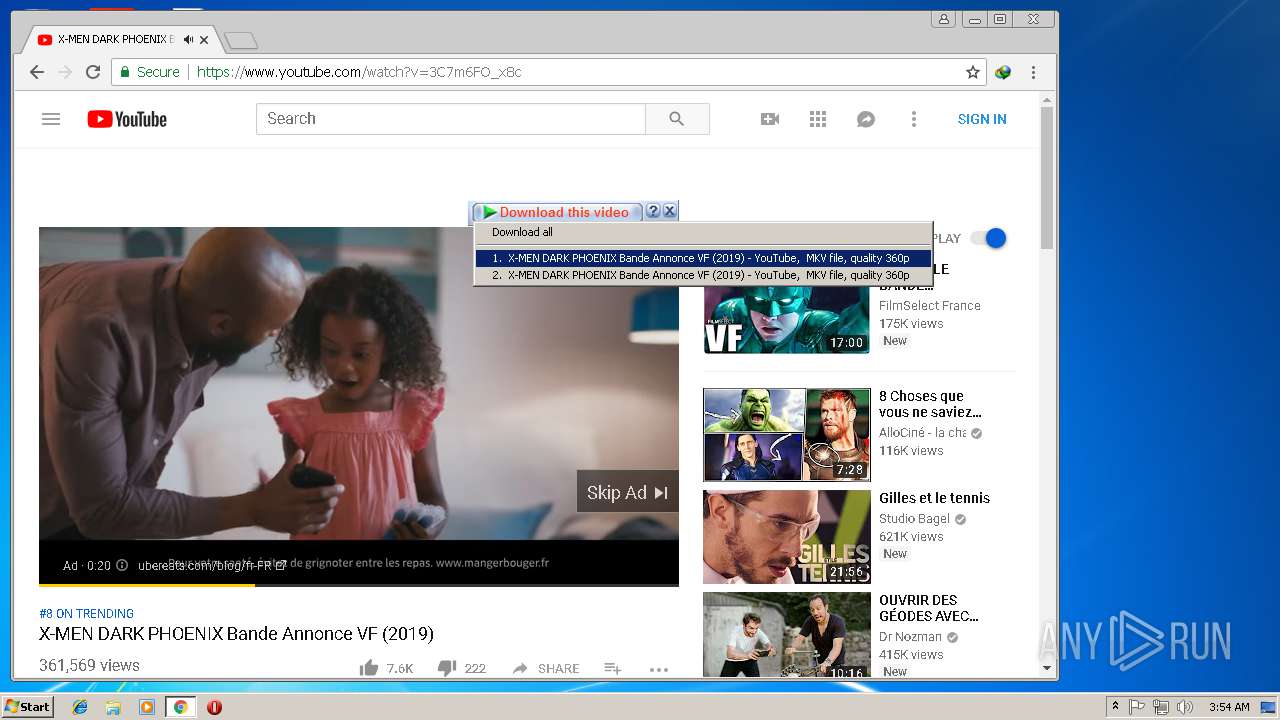
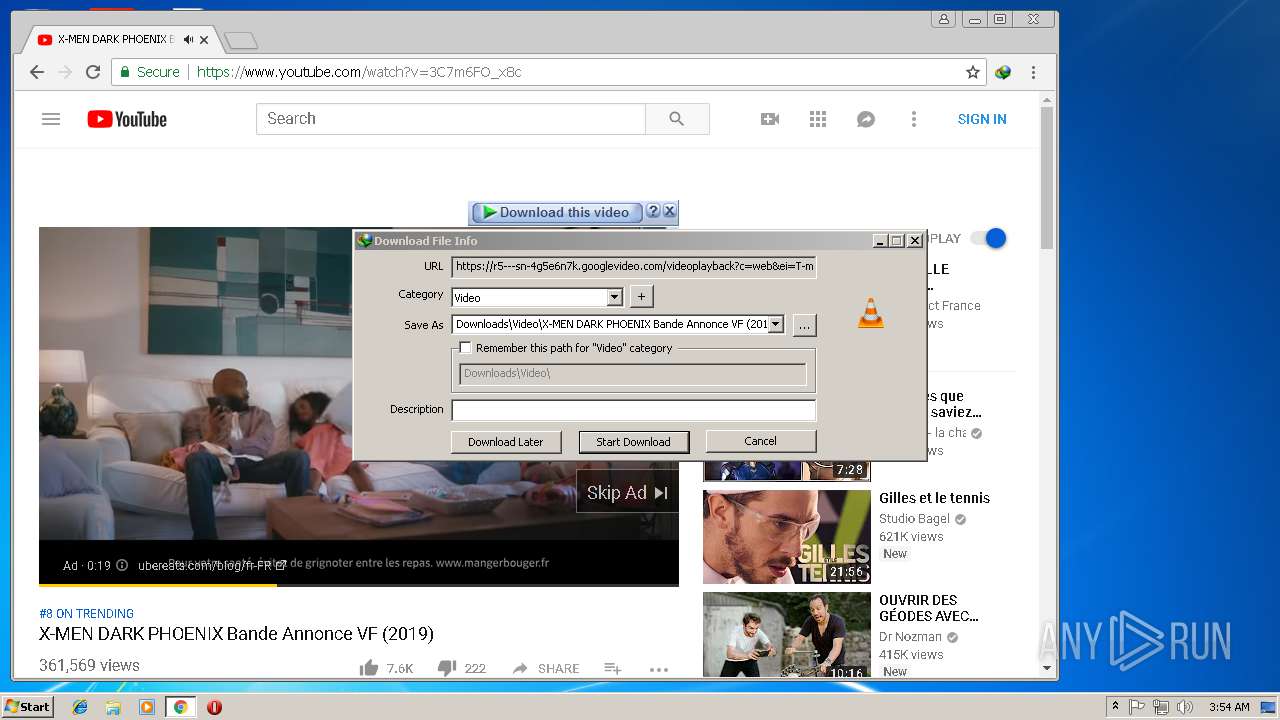
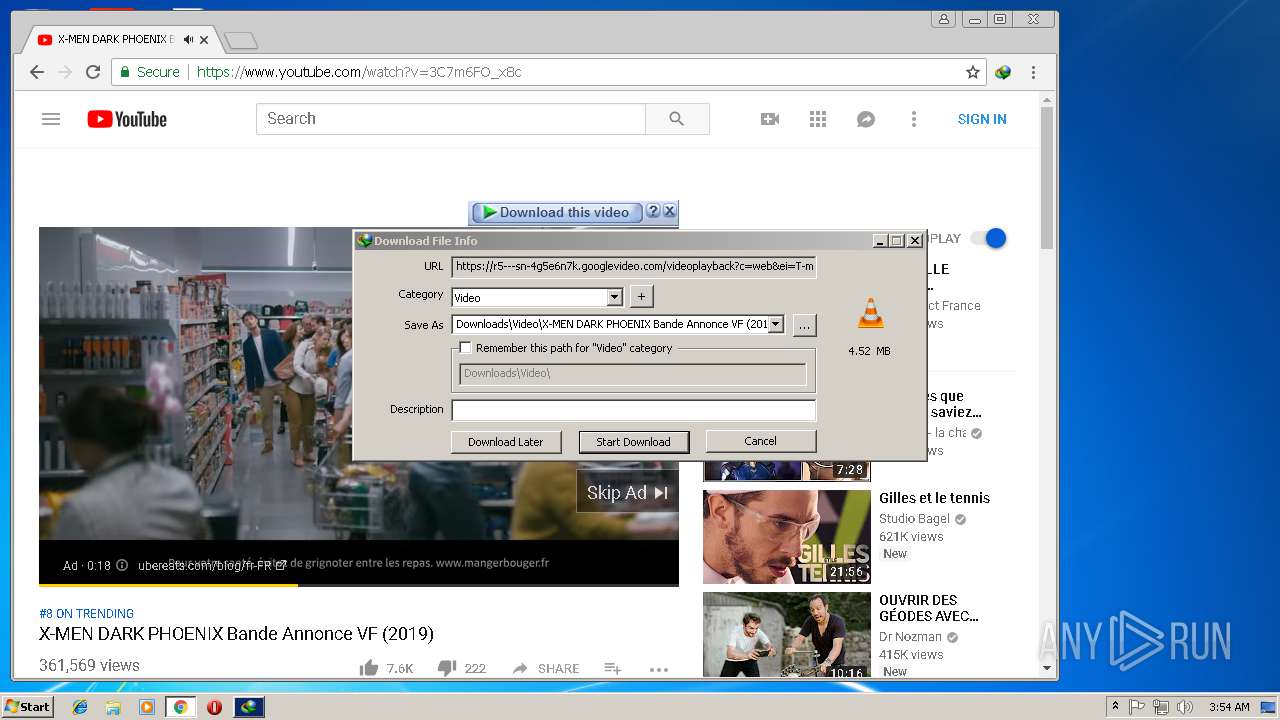
Modifies files in Chrome extension folder
- chrome.exe (PID: 3076)
INFO
Dropped object may contain Bitcoin addresses
- IDMan.exe (PID: 3428)
Reads settings of System Certificates
- chrome.exe (PID: 3076)
Application launched itself
- chrome.exe (PID: 3076)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 20:19:59+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28672 |
| InitializedDataSize: | 445952 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x39e3 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.31.7.1 |
| ProductVersionNumber: | 6.31.7.1 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | Please visit http://www.internetdownloadmanager.com |
| CompanyName: | Tonec Inc. |
| FileDescription: | Internet Download Manager installer |
| FileVersion: | 6, 31, 7, 1 |
| InternalName: | installer |
| LegalCopyright: | © 1999-2018. Tonec, Inc. All rights reserved. |
| LegalTrademarks: | Internet Download Manager (IDM) |
| OriginalFileName: | installer.exe |
| PrivateBuild: | - |
| ProductName: | Internet Download Manager installer |
| ProductVersion: | 6, 31, 7, 1 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:19:59 |
| Detected languages: |
|
| Comments: | Please visit http://www.internetdownloadmanager.com |
| CompanyName: | Tonec Inc. |
| FileDescription: | Internet Download Manager installer |
| FileVersion: | 6, 31, 7, 1 |
| InternalName: | installer |
| LegalCopyright: | © 1999-2018. Tonec, Inc. All rights reserved. |
| LegalTrademarks: | Internet Download Manager (IDM) |
| OriginalFilename: | installer.exe |
| PrivateBuild: | - |
| ProductName: | Internet Download Manager installer |
| ProductVersion: | 6, 31, 7, 1 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:19:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006F10 | 0x00007000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.49788 |
.rdata | 0x00008000 | 0x00002A92 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39389 |
.data | 0x0000B000 | 0x00067EBC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.47278 |
.ndata | 0x00073000 | 0x00085000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x000F8000 | 0x000016D0 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.57155 |
.reloc | 0x000FA000 | 0x00000F8A | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.4027 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21712 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.52824 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.38595 | 34 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
81
Monitored processes
40
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Windows\System32\net.exe" start IDMWFP | C:\Windows\System32\net.exe | — | Uninstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=872,14354862982677295289,4070434856547164203,131072 --enable-features=PasswordImport --disable-gpu-sandbox --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=0A483015FB061883F764ABF78D573A83 --mojo-platform-channel-handle=4372 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=872,14354862982677295289,4070434856547164203,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7783440540E09935440F01854CBEFA22 --mojo-platform-channel-handle=2468 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 852 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 884 | "C:\Program Files\Internet Download Manager\Uninstall.exe" -instdriv | C:\Program Files\Internet Download Manager\Uninstall.exe | — | IDMan.exe | |||||||||||
User: admin Company: Tonec Inc. Integrity Level: HIGH Description: Internet Download Manager installer Exit code: 1 Version: 6, 31, 5, 1 Modules
| |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=872,14354862982677295289,4070434856547164203,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=EFA10FCFDE42135BFFCA53F7CD5E5C30 --mojo-platform-channel-handle=904 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 892 | "C:\Program Files\Internet Download Manager\MediumILStart.exe" | C:\Program Files\Internet Download Manager\MediumILStart.exe | — | IDMan.exe | |||||||||||
User: admin Company: Internet Download Manager, Tonec Inc. Integrity Level: MEDIUM Description: IDM module Exit code: 0 Version: 6, 22, 1, 1 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=872,14354862982677295289,4070434856547164203,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=B53AB89E994E451646E528D934FC0289 --mojo-platform-channel-handle=2500 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1320 | "C:\Windows\system32\runonce.exe" -r | C:\Windows\system32\runonce.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Run Once Wrapper Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1604 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 918
Read events
2 508
Write events
1 296
Delete events
114
Modification events
| (PID) Process: | (1604) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\Vagrearg Qbjaybnq Znantre 6.31 Ohvyq 7 Cer-Npgvingrq ol fwgf perjf.rkr |
Value: 000000000000000000000000172B0000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (1604) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000001B000000260000007CDB0C000400000001000000E38300007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C004F0070006500720061005C006F0070006500720061002E0065007800650000002802FFFFFFFF82BA7975B0487D750200000001000000A0487D7501000000ECE62802C5B87975A8487D7501000000A81032000000000014E728026BB9797500000000350100C00100000034E72802973C47779C3C47770583677501000000350100C0000000000CE72802FFFFFFFF7CE72802EDE0437731780800FEFFFFFF44E728020D6B797524EC280210ED2802000000007CE72802973C47779C3C47774D8367750000000010ED280224EC280254E7280201000000F4EB2802EDE0437731780800FEFFFFFF8CE728020D6B79757E00000010ED280204EC2802F36B7975E18679757DE1E97A10ED280210000000F5021C004000420010ED280224EC280200000000000000000000000000000802E0E9280200000802D8E72802350100C00000000000000802E8E72802350100C00000000068005C0011000000F0443500E844350069006E006E00650064005C0074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802000000000B00000000F203007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E0065007800650000000000B8E9280284E82802A532EB76C4E828029CE9280200000000B432EB76FCE928020145EB766A00E3028C00E302B8ACE30280E728020001000101000000000100000000000028FCC102D0E92802E0E2D802ACE92802CAFED802A8E72802DCE928026000E3022B0000006A00E30228FCC102000000008C00E30264E928020A00E3020000000005000500A82355026601E3022B0000000F000000FCE92802C4E9280228FCC1021000000074FFC102050017004E1E5502C4E828021600000002000000B8ACE3020400280228FCC102030000000000000009090900090909090009111100000000000000000000000011000000F0443500E84435000000000000000000000000000000000024E800006751EA7AD8E728028291917524E828028CD800007351EA7AECE72802B69C917590D8D4034C06000004E8280200D4D40311000000F0443500E844350040B0C37504E8280220D4D40374E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802000000000B00000000F203007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E0065007800650000000000B8E9280284E82802A532EB76C4E828029CE9280200000000B432EB76FCE928020145EB766A00E3028C00E302B8ACE30280E728020001000101000000000100000000000028FCC102D0E92802E0E2D802ACE92802CAFED802A8E72802DCE928026000E3022B0000006A00E30228FCC102000000008C00E30264E928020A00E3020000000005000500A82355026601E3022B0000000F000000FCE92802C4E9280228FCC1021000000074FFC102050017004E1E5502C4E828021600000002000000B8ACE3020400280228FCC102030000000000000009090900090909090009111100000000000000000000000011000000F0443500E84435000000000000000000000000000000000024E800006751EA7AD8E728028291917524E828028CD800007351EA7AECE72802B69C917590D8D4034C06000004E8280200D4D40311000000F0443500E844350040B0C37504E8280220D4D40374E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802 | |||
| (PID) Process: | (3584) Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Internet Download Manager |
| Operation: | write | Name: | FName |
Value: | |||
| (PID) Process: | (3584) Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Internet Download Manager |
| Operation: | write | Name: | LName |
Value: | |||
| (PID) Process: | (3584) Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Internet Download Manager |
| Operation: | write | Name: | |
Value: m4rdhi@bravo.com | |||
| (PID) Process: | (3584) Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Internet Download Manager |
| Operation: | write | Name: | Serial |
Value: NC8TN-UIX5N-QAFEK-VCFXZ | |||
| (PID) Process: | (3584) Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Internet Download Manager |
| Operation: | write | Name: | FName |
Value: wea | |||
| (PID) Process: | (1604) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | P:\Hfref\nqzva\NccQngn\Ybpny\Grzc\Vagrearg Qbjaybnq Znantre 6.31 Ohvyq 7 Cer-Npgvingrq ol fwgf perjf.rkr |
Value: 0000000000000000000000004B3F0000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF000000000000000000000000 | |||
| (PID) Process: | (1604) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000001B00000026000000B0EF0C000400000001000000E38300007B00370043003500410034003000450046002D0041003000460042002D0034004200460043002D0038003700340041002D004300300046003200450030004200390046004100380045007D005C004F0070006500720061005C006F0070006500720061002E0065007800650000002802FFFFFFFF82BA7975B0487D750200000001000000A0487D7501000000ECE62802C5B87975A8487D7501000000A81032000000000014E728026BB9797500000000350100C00100000034E72802973C47779C3C47770583677501000000350100C0000000000CE72802FFFFFFFF7CE72802EDE0437731780800FEFFFFFF44E728020D6B797524EC280210ED2802000000007CE72802973C47779C3C47774D8367750000000010ED280224EC280254E7280201000000F4EB2802EDE0437731780800FEFFFFFF8CE728020D6B79757E00000010ED280204EC2802F36B7975E18679757DE1E97A10ED280210000000F5021C004000420010ED280224EC280200000000000000000000000000000802E0E9280200000802D8E72802350100C00000000000000802E8E72802350100C00000000068005C0011000000F0443500E844350069006E006E00650064005C0074E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802000000000B00000000F203007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E0065007800650000000000B8E9280284E82802A532EB76C4E828029CE9280200000000B432EB76FCE928020145EB766A00E3028C00E302B8ACE30280E728020001000101000000000100000000000028FCC102D0E92802E0E2D802ACE92802CAFED802A8E72802DCE928026000E3022B0000006A00E30228FCC102000000008C00E30264E928020A00E3020000000005000500A82355026601E3022B0000000F000000FCE92802C4E9280228FCC1021000000074FFC102050017004E1E5502C4E828021600000002000000B8ACE3020400280228FCC102030000000000000009090900090909090009111100000000000000000000000011000000F0443500E84435000000000000000000000000000000000024E800006751EA7AD8E728028291917524E828028CD800007351EA7AECE72802B69C917590D8D4034C06000004E8280200D4D40311000000F0443500E844350040B0C37504E8280220D4D40374E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802000000000B00000000F203007B00440036003500320033003100420030002D0042003200460031002D0034003800350037002D0041003400430045002D004100380045003700430036004500410037004400320037007D005C007400610073006B006D00670072002E0065007800650000000000B8E9280284E82802A532EB76C4E828029CE9280200000000B432EB76FCE928020145EB766A00E3028C00E302B8ACE30280E728020001000101000000000100000000000028FCC102D0E92802E0E2D802ACE92802CAFED802A8E72802DCE928026000E3022B0000006A00E30228FCC102000000008C00E30264E928020A00E3020000000005000500A82355026601E3022B0000000F000000FCE92802C4E9280228FCC1021000000074FFC102050017004E1E5502C4E828021600000002000000B8ACE3020400280228FCC102030000000000000009090900090909090009111100000000000000000000000011000000F0443500E84435000000000000000000000000000000000024E800006751EA7AD8E728028291917524E828028CD800007351EA7AECE72802B69C917590D8D4034C06000004E8280200D4D40311000000F0443500E844350040B0C37504E8280220D4D40374E80000AB5EEA7A24E828028291917574E8280228E8280227959175000000008CD8D40350E82802CD9491758CD8D403FCE8280200D4D403E19491750000000000D4D403FCE8280258E82802 | |||
| (PID) Process: | (3584) Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Internet Download Manager |
| Operation: | write | Name: | LName |
Value: ewa | |||
Executable files
48
Suspicious files
244
Text files
257
Unknown types
62
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 852 | svchost.exe | C:\Windows\appcompat\programs\RecentFileCache.bcf | txt | |
MD5:9A24B65FCBC1386B75BEF6D800F00467 | SHA256:CA84D551051C7FEEEB2E618C1ED21EF3A5511C3F4937EB969629F58AEADF58E6 | |||
| 3584 | Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe | C:\Users\admin\AppData\Local\Temp\IDM_Setup_Temp\IDM1.tmp | executable | |
MD5:338290C2074954B0D5C53B0E79D14844 | SHA256:FA735D1734B64ABEA9B85D94AD920019589A0D600BD21A7178A952DE237B24E6 | |||
| 3584 | Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe | C:\Users\admin\AppData\Local\Temp\IDM_Setup_Temp\IDM0.tmp | text | |
MD5:AD26C65E88F61AE85CA4B515D8AD31CA | SHA256:8A86039630E5C5A4267C9DBC4BB465C39748D7DF9A7B065B14A3370022A3BD50 | |||
| 3584 | Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe | C:\Users\admin\AppData\Local\Temp\nsu25E8.tmp\System.dll | executable | |
MD5:BF712F32249029466FA86756F5546950 | SHA256:7851CB12FA4131F1FEE5DE390D650EF65CAC561279F1CFE70AD16CC9780210AF | |||
| 3584 | Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe | C:\Users\admin\AppData\Local\Temp\nsu25E8.tmp\FindProcDLL.dll | executable | |
MD5:B4FAF654DE4284A89EAF7D073E4E1E63 | SHA256:C0948B2EC36A69F82C08935FAC4B212238B6792694F009B93B4BDB478C4F26E3 | |||
| 3584 | Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe | C:\Users\admin\AppData\Local\Temp\IDM_Setup_Temp\IDM102.tmp | text | |
MD5:A5F24E957E1C79AE5F0EDD0BB932A3D0 | SHA256:F02E6C6F71D07D992FF20F8E74A28AA5F89C8DEB6244B796DC897529BAE9EDF6 | |||
| 3584 | Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe | C:\Users\admin\AppData\Local\Temp\IDM_Setup_Temp\IDM103.tmp | text | |
MD5:851529E5C892D1A528DA10663FB5ABD3 | SHA256:8D2C3A765AF78A6F3DD7A5F6045277D1ADE6D20A7F09A2DFDD1DD18DC7AA94D7 | |||
| 3584 | Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe | C:\Users\admin\AppData\Local\Temp\IDM_Setup_Temp\IDM10.tmp | html | |
MD5:648E7B2602158D2FF9197D664F59B28B | SHA256:47937F8F34BA56718D4BD3B97BFD9E42468D6B7615C745B7841272A2E3D39E57 | |||
| 3584 | Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe | C:\Users\admin\AppData\Local\Temp\IDM_Setup_Temp\IDM100.tmp | executable | |
MD5:09959EE223C5D34C82F1EFB8BC8233CB | SHA256:1FDB0D5B31E080084C82E0B773DAFC7860FA860938B8BAEF6A4D7F5BDE659F73 | |||
| 3584 | Internet Download Manager 6.31 Build 7 Pre-Activated by sjts crews.exe | C:\Users\admin\AppData\Local\Temp\IDM_Setup_Temp\IDM101.tmp | text | |
MD5:90B3221AF6739E8BBA67187B99430683 | SHA256:AB4B7F533A2097938E48B49A377365DA5FA005D6E29D37552E1708B06A1CE8C1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
93
DNS requests
43
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3076 | chrome.exe | 172.217.23.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3076 | chrome.exe | 172.217.23.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3076 | chrome.exe | 172.217.23.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
3076 | chrome.exe | 172.217.22.3:443 | www.google.de | Google Inc. | US | whitelisted |
3076 | chrome.exe | 216.58.207.35:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3076 | chrome.exe | 216.58.208.42:443 | www.googleapis.com | Google Inc. | US | whitelisted |
3076 | chrome.exe | 172.217.23.174:443 | chrome.google.com | Google Inc. | US | whitelisted |
3076 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
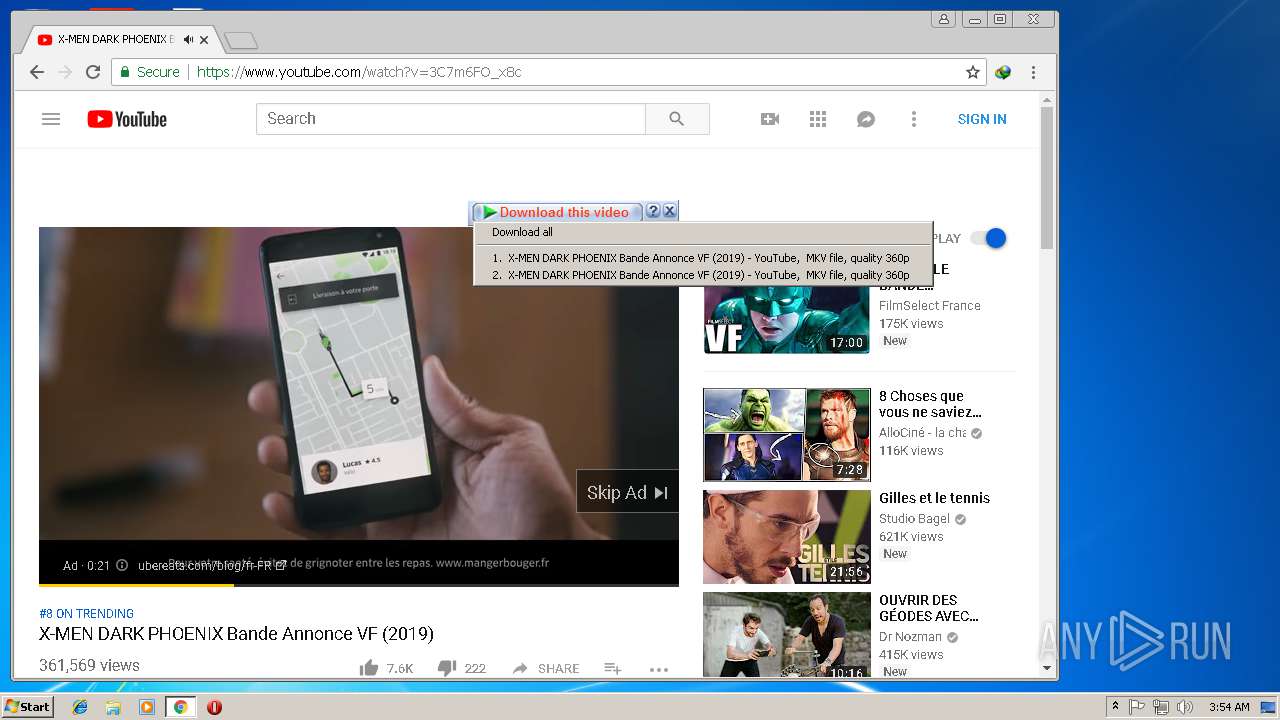
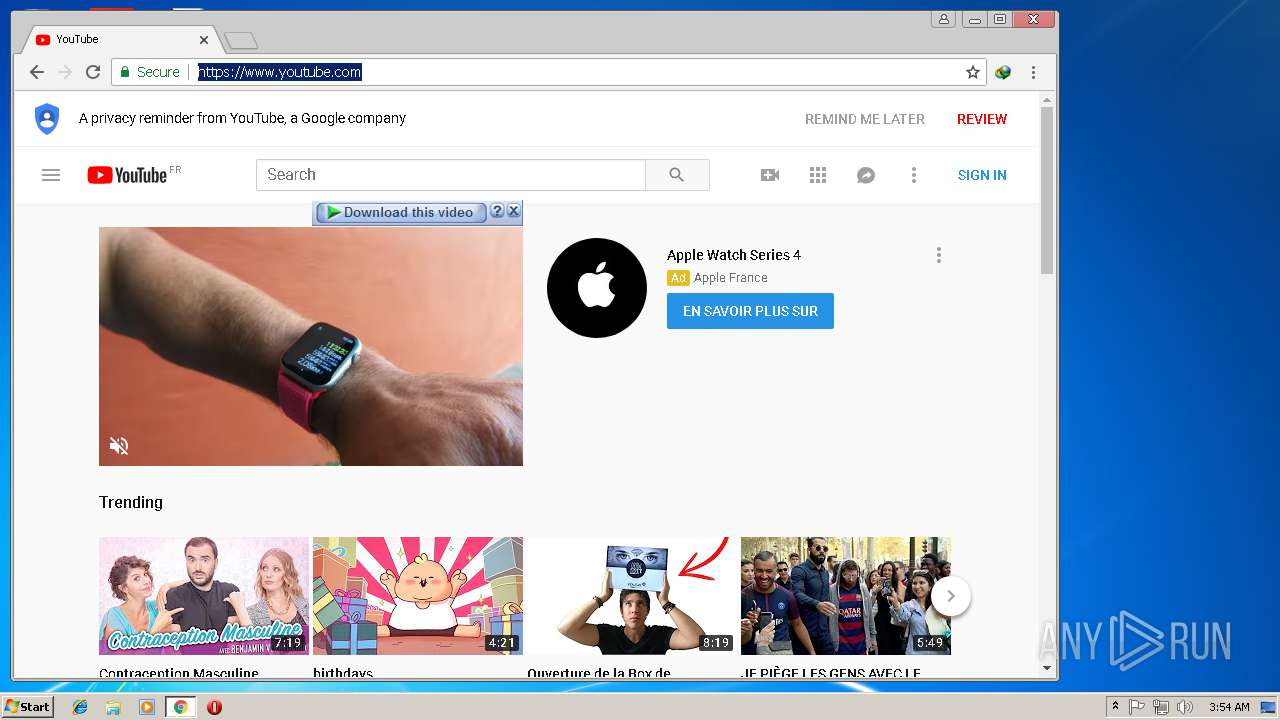
3076 | chrome.exe | 216.58.205.238:443 | www.youtube.com | Google Inc. | US | whitelisted |
3076 | chrome.exe | 172.217.22.1:443 | yt3.ggpht.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
test.internetdownloadmanager.com |
| whitelisted |
www.internetdownloadmanager.com |
| whitelisted |
secure.internetdownloadmanager.com |
| whitelisted |
mirror3.internetdownloadmanager.com |
| whitelisted |
registeridm.com |
| suspicious |
mirror5.internetdownloadmanager.com |
| whitelisted |