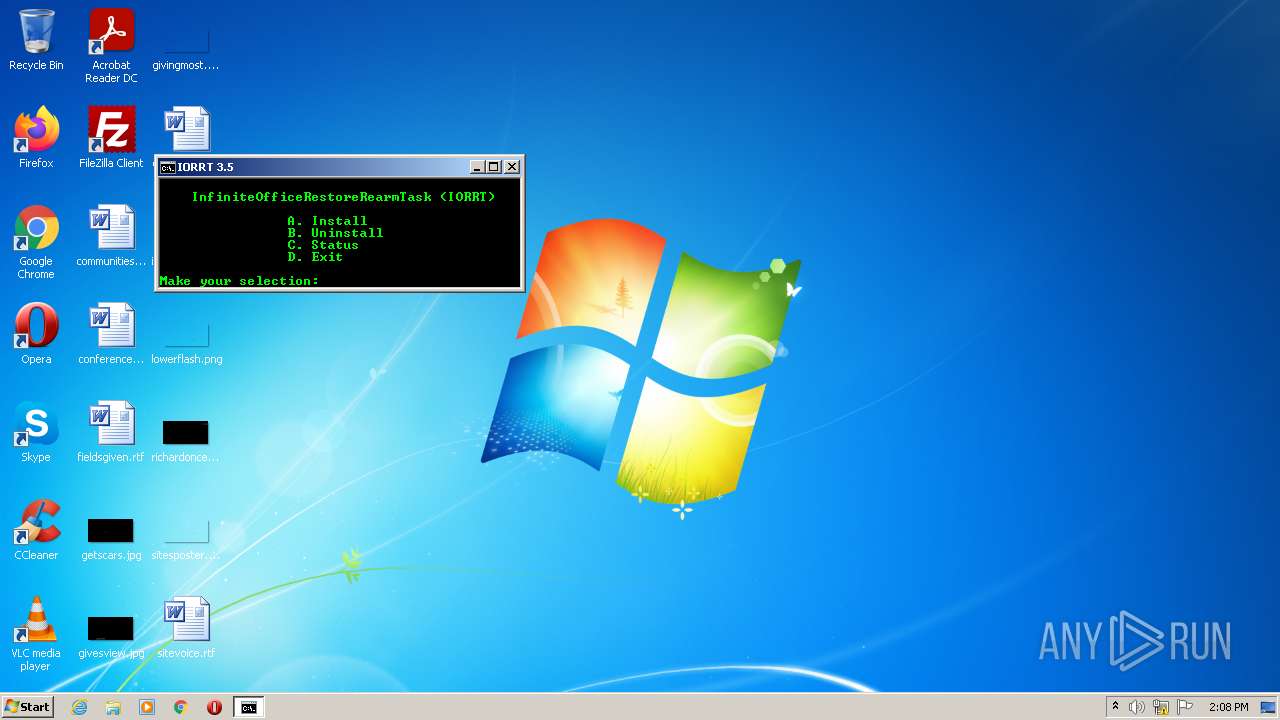
| File name: | IORRT 3.5.cmd |
| Full analysis: | https://app.any.run/tasks/3908b65c-d6aa-40d9-89a1-5a1009953401 |
| Verdict: | Malicious activity |
| Analysis date: | March 17, 2022, 14:08:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | D9F7C8A28105BAFA9308FF6C76F77D14 |
| SHA1: | D32BFC9AB7FF9FAEEAE79BC4A745706B03AB2986 |
| SHA256: | D611ACB095B1577CC1245E44BA3DEC52B3C60EB84768A9BA529B1539DE0CEC8A |
| SSDEEP: | 96:zGhF5FfwULDrpvs3s0ef7vlblHr9x3K+2eZo8zXOT2b2eZo8zXU6QlvirQCAQ2ag:sUi9y+pFbp4ELdxOdA0b |
MALICIOUS
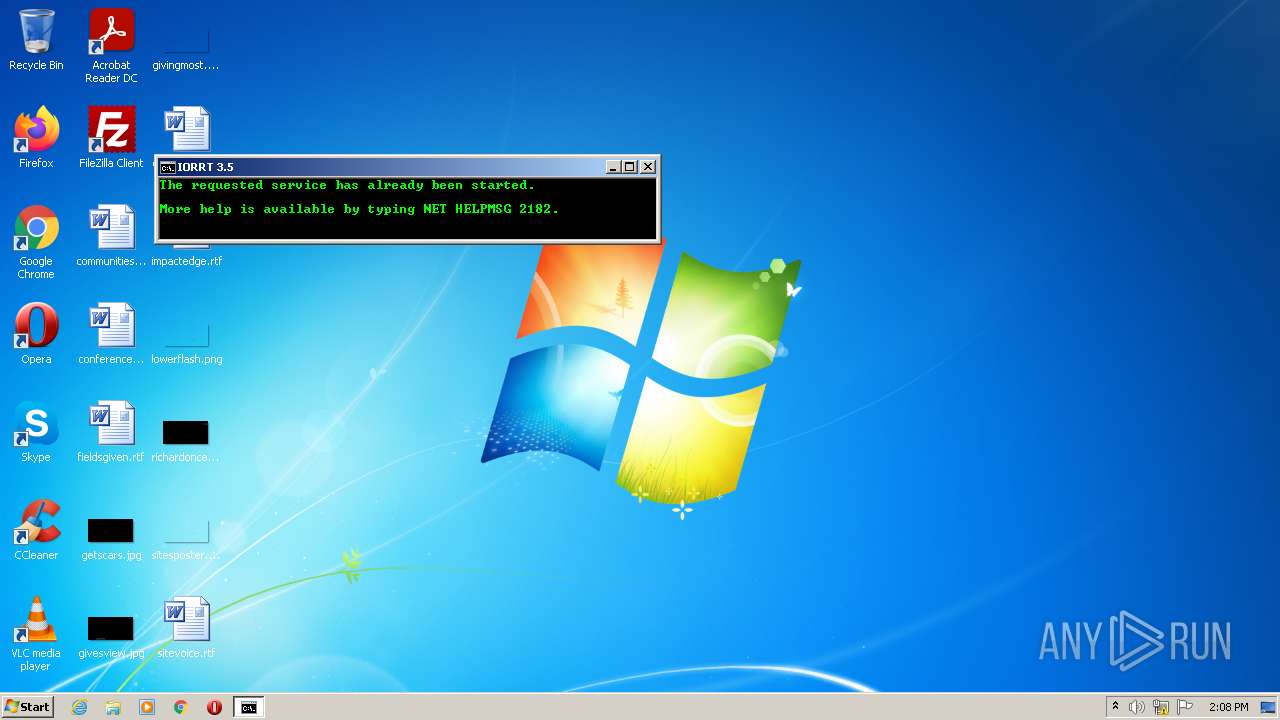
Starts NET.EXE for service management
- cmd.exe (PID: 3924)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3924)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 904)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 3924)
SUSPICIOUS
Checks supported languages
- cmd.exe (PID: 3924)
- cmd.exe (PID: 3152)
- mode.com (PID: 3944)
- mode.com (PID: 2608)
- OSPPREARM.EXE (PID: 3756)
- cscript.exe (PID: 2756)
- WScript.exe (PID: 1956)
- mode.com (PID: 532)
- cscript.exe (PID: 3028)
- mode.com (PID: 3244)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3152)
- cmd.exe (PID: 3924)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 3924)
Application launched itself
- cmd.exe (PID: 3924)
Reads the computer name
- OSPPREARM.EXE (PID: 3756)
- cscript.exe (PID: 2756)
- cscript.exe (PID: 3028)
- WScript.exe (PID: 1956)
- cmd.exe (PID: 3924)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 3924)
Executes scripts
- cmd.exe (PID: 3924)
Creates files in the user directory
- WScript.exe (PID: 1956)
INFO
Checks supported languages
- reg.exe (PID: 3364)
- net.exe (PID: 3588)
- net1.exe (PID: 3692)
- schtasks.exe (PID: 904)
- findstr.exe (PID: 1036)
- net1.exe (PID: 3260)
- net.exe (PID: 3308)
- xcopy.exe (PID: 1760)
- reg.exe (PID: 1236)
- net1.exe (PID: 1456)
- net.exe (PID: 1104)
- net.exe (PID: 3004)
- net1.exe (PID: 2052)
- reg.exe (PID: 996)
- net.exe (PID: 3840)
- net1.exe (PID: 404)
- attrib.exe (PID: 2788)
- findstr.exe (PID: 928)
- findstr.exe (PID: 3272)
- xcopy.exe (PID: 2332)
- reg.exe (PID: 2488)
- reg.exe (PID: 1684)
- PING.EXE (PID: 2768)
Reads Microsoft Office registry keys
- reg.exe (PID: 3364)
Reads the computer name
- net1.exe (PID: 3692)
- net1.exe (PID: 3260)
- reg.exe (PID: 1236)
- net1.exe (PID: 2052)
- net1.exe (PID: 1456)
- net1.exe (PID: 404)
- PING.EXE (PID: 2768)
- schtasks.exe (PID: 904)
Checks Windows Trust Settings
- cscript.exe (PID: 2756)
- WScript.exe (PID: 1956)
- cscript.exe (PID: 3028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
33
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 404 | C:\Windows\system32\net1 start osppsvc | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 532 | mode con: cols=45 lines=9 | C:\Windows\system32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 904 | schtasks /query | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 928 | FINDSTR /i "Status" | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 996 | reg restore "HKLM\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform" C:\Check\Backup\Registry\OfficeSPPInfo.hiv | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1036 | FINDSTR /I "IORRT" | C:\Windows\system32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1104 | net stop osppsvc | C:\Windows\system32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1236 | reg save "HKLM\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform" C:\Check\Backup\Registry\OfficeSPPInfo.hiv | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1456 | C:\Windows\system32\net1 stop osppsvc | C:\Windows\system32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1684 | REG ADD HKLM\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 622
Read events
1 584
Write events
38
Delete events
0
Modification events
| (PID) Process: | (3924) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3924) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3924) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3924) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1956) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\CurrentUserLexicon |
| Operation: | write | Name: | CLSID |
Value: {C9E37C15-DF92-4727-85D6-72E5EEB6995A} | |||
| (PID) Process: | (1956) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\CurrentUserLexicon |
| Operation: | write | Name: | (default) |
Value: Current User Lexicon | |||
| (PID) Process: | (1956) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\CurrentUserLexicon\{C9E37C15-DF92-4727-85D6-72E5EEB6995A}\Files |
| Operation: | write | Name: | Datafile |
Value: %1a%\Microsoft\Speech\Files\UserLexicons\SP_65DC5DCEBCEF41B6A20B1684386E10FD.dat | |||
| (PID) Process: | (1956) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\CurrentUserLexicon |
| Operation: | write | Name: | Generation |
Value: 0 | |||
| (PID) Process: | (1956) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\PhoneConverters |
| Operation: | write | Name: | DefaultTokenId |
Value: HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Speech\PhoneConverters\Tokens\English | |||
| (PID) Process: | (1956) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Speech\AudioOutput\TokenEnums\MMAudioOut\{0.0.0.00000000}.{e602c5a2-9378-42f9-9806-a74c065977f6} |
| Operation: | write | Name: | (default) |
Value: Speakers (Realtek AC'97 Audio) | |||
Executable files
0
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1760 | xcopy.exe | C:\Check\Backup\Files\Tokens\tokens.dat | — | |
MD5:— | SHA256:— | |||
| 1956 | WScript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Speech\Files\UserLexicons\SP_65DC5DCEBCEF41B6A20B1684386E10FD.dat | binary | |
MD5:— | SHA256:— | |||
| 1760 | xcopy.exe | C:\Check\Backup\Files\Tokens\Cache\cache.dat | binary | |
MD5:— | SHA256:— | |||
| 3924 | cmd.exe | C:\Users\admin\AppData\Local\Temp\vc.vbs | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report