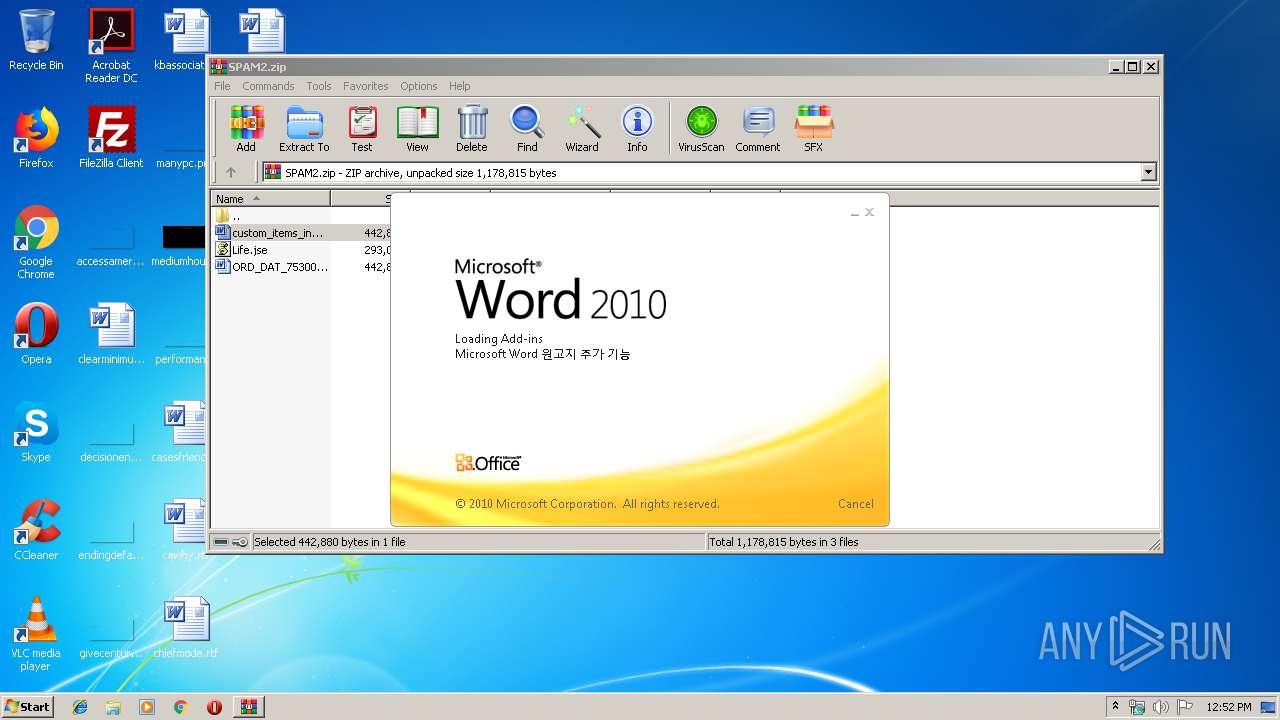
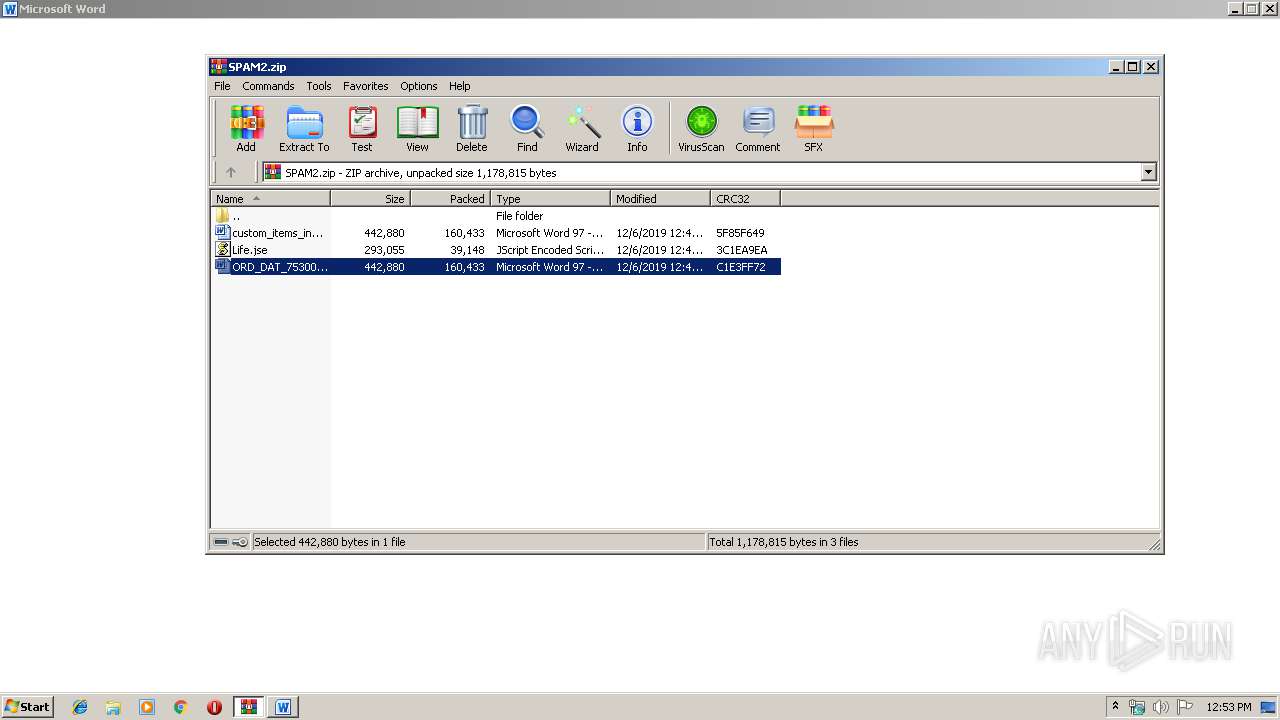
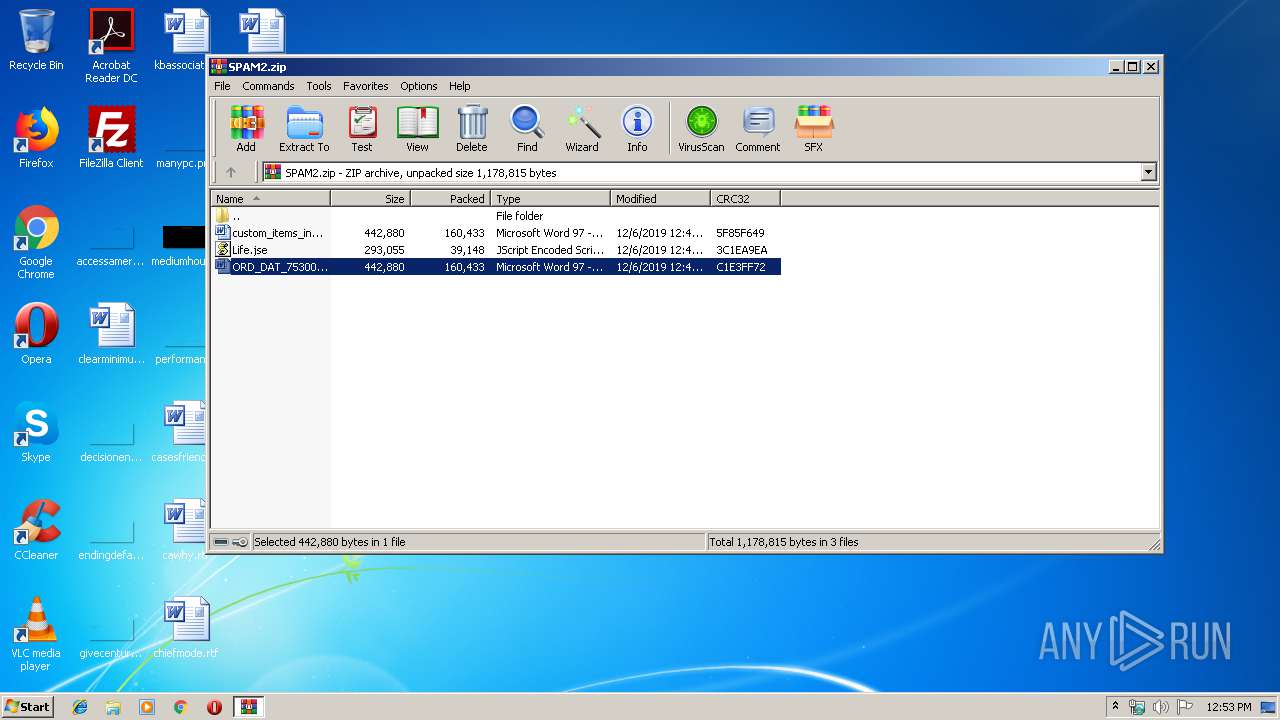
| File name: | SPAM2.zip |
| Full analysis: | https://app.any.run/tasks/b9288947-7441-4e05-8bd4-356da37a1955 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 12:52:20 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E514D180BC4AC2EACBE0566523E7334F |
| SHA1: | 608139A2C9FA6664B379193D06F103FC0565A01B |
| SHA256: | D60047CA9D086265A84B7C17211EE912CA5E24AE386AFE0965E9F790A076316A |
| SSDEEP: | 6144:qAz36yWdiksDRpeu1ls/qZ2Ei1ElHmFla3q/XJ4Az36yWdiksDRpeu1ls/qZ2Eiy:l2YxYu1lGRVmhqaa/X52YxYu1lGRVmhB |
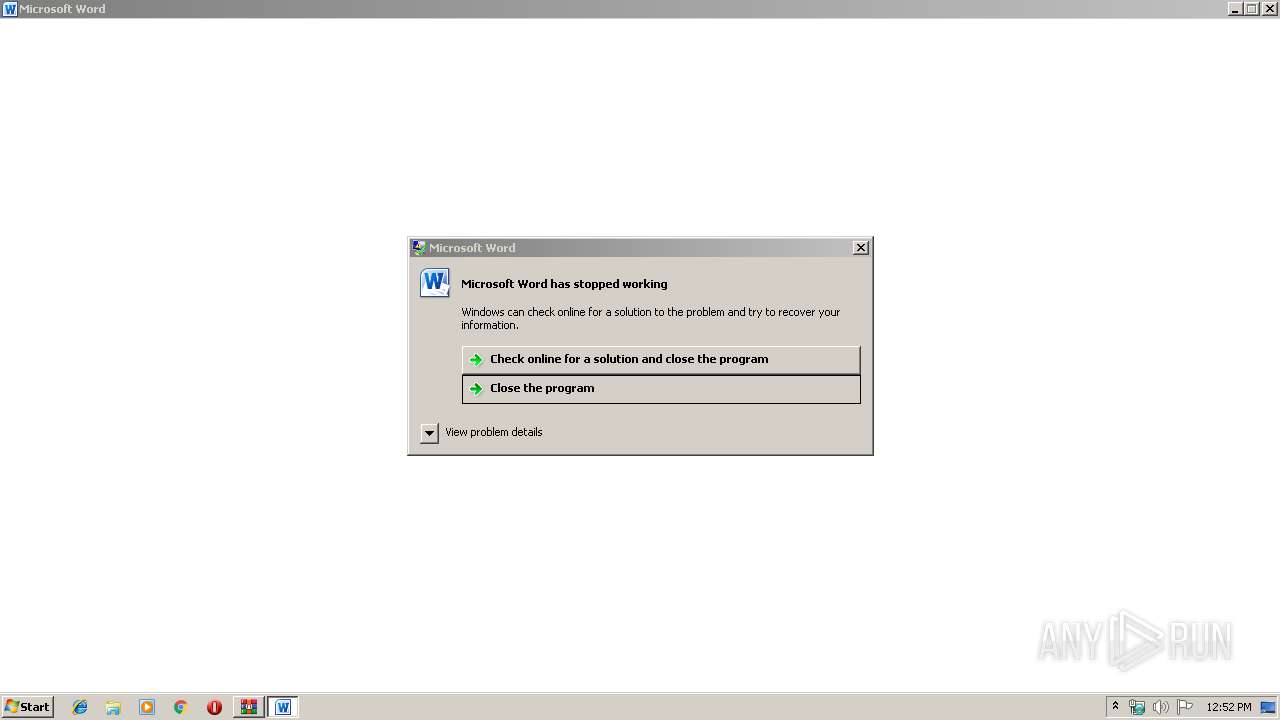
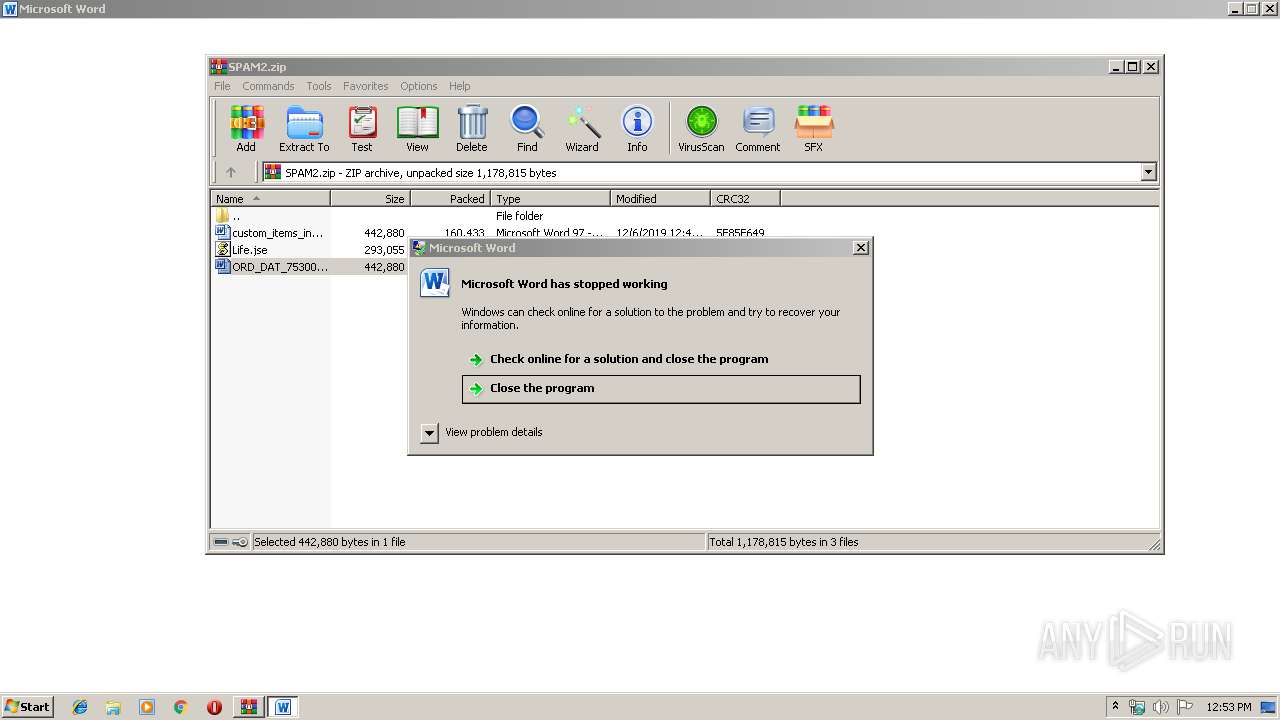
MALICIOUS
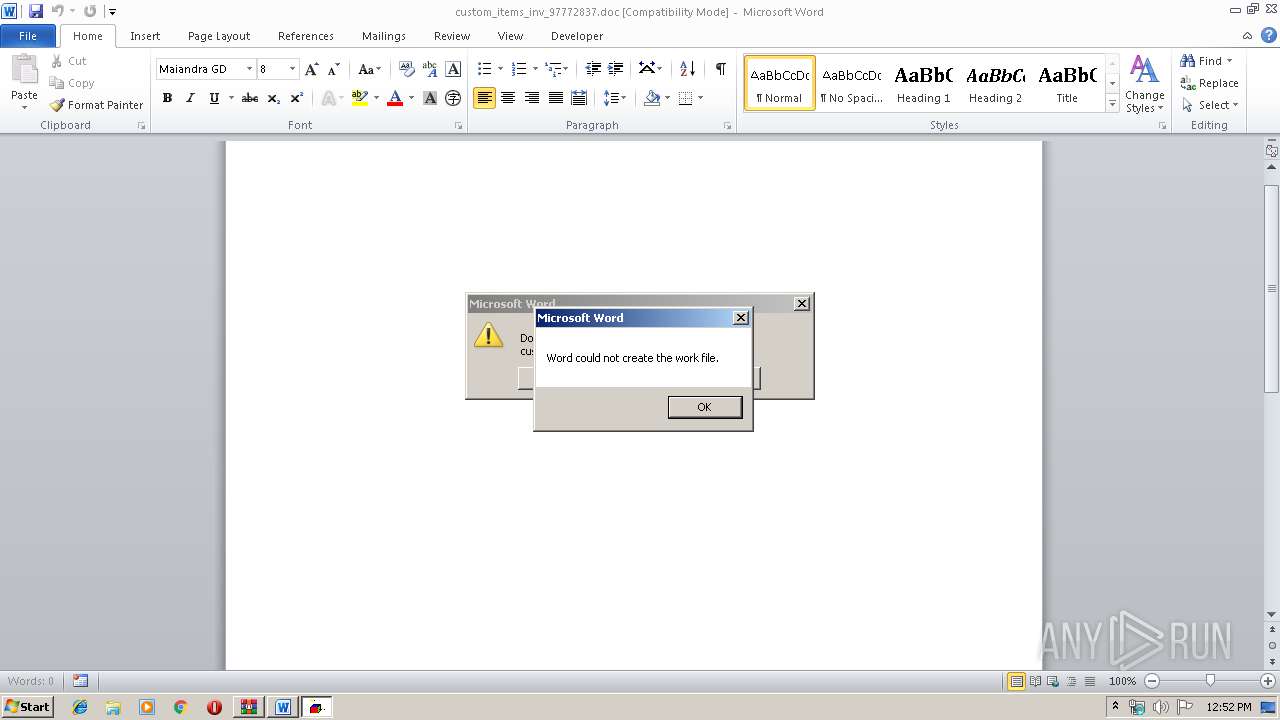
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1972)
- WINWORD.EXE (PID: 3272)
Executes scripts
- WINWORD.EXE (PID: 1972)
- WINWORD.EXE (PID: 3272)
SUSPICIOUS
Executes scripts
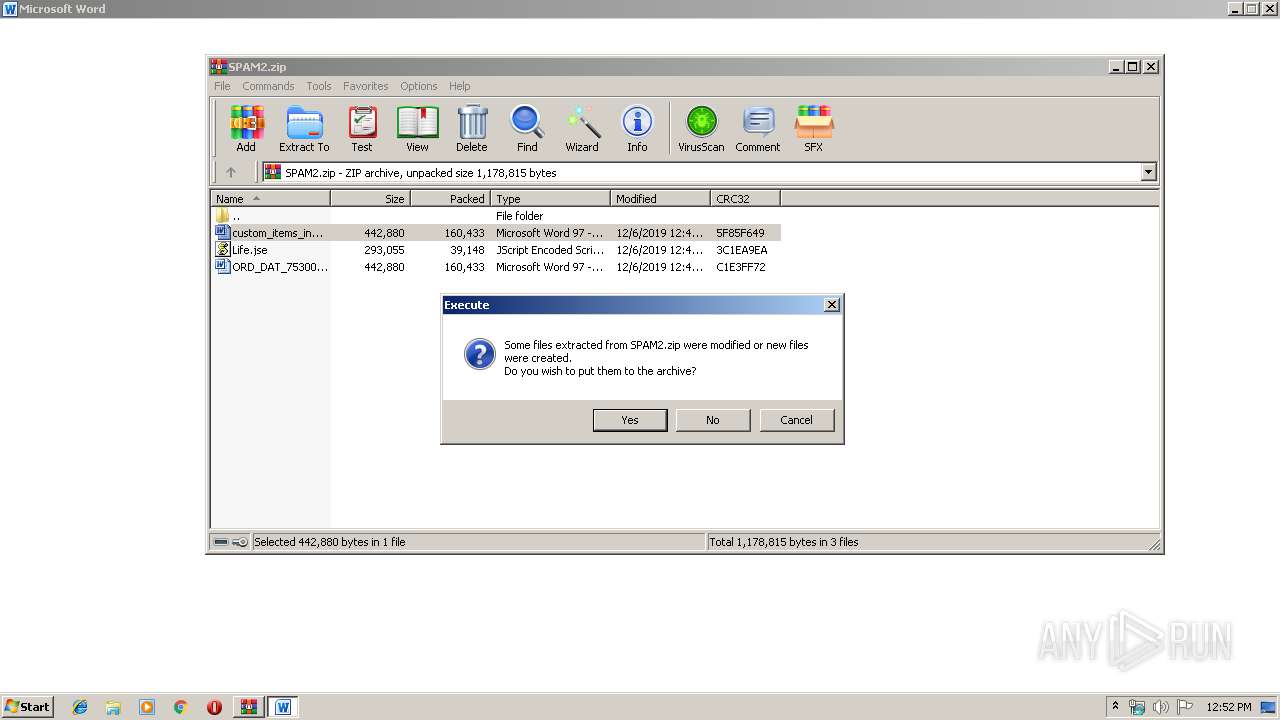
- WinRAR.exe (PID: 2428)
Starts Microsoft Office Application
- WinRAR.exe (PID: 2428)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1972)
- WINWORD.EXE (PID: 3272)
Creates files in the user directory
- WINWORD.EXE (PID: 1972)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:12:06 13:41:18 |
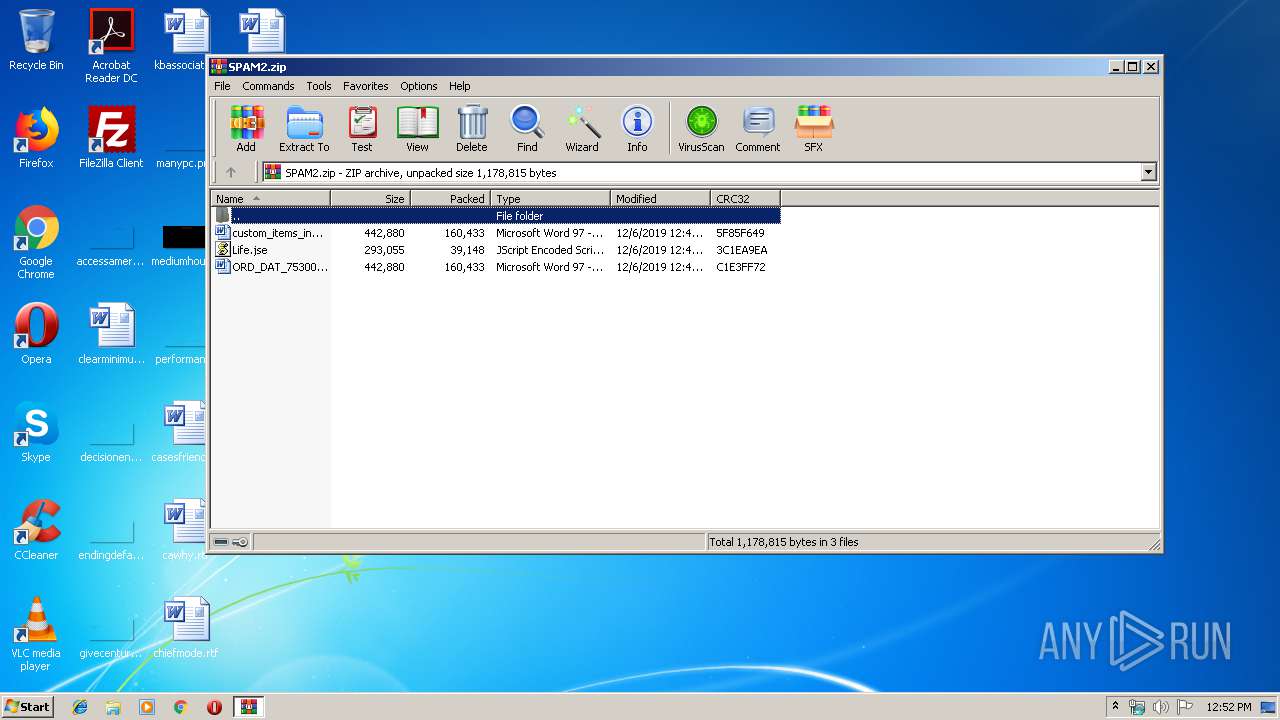
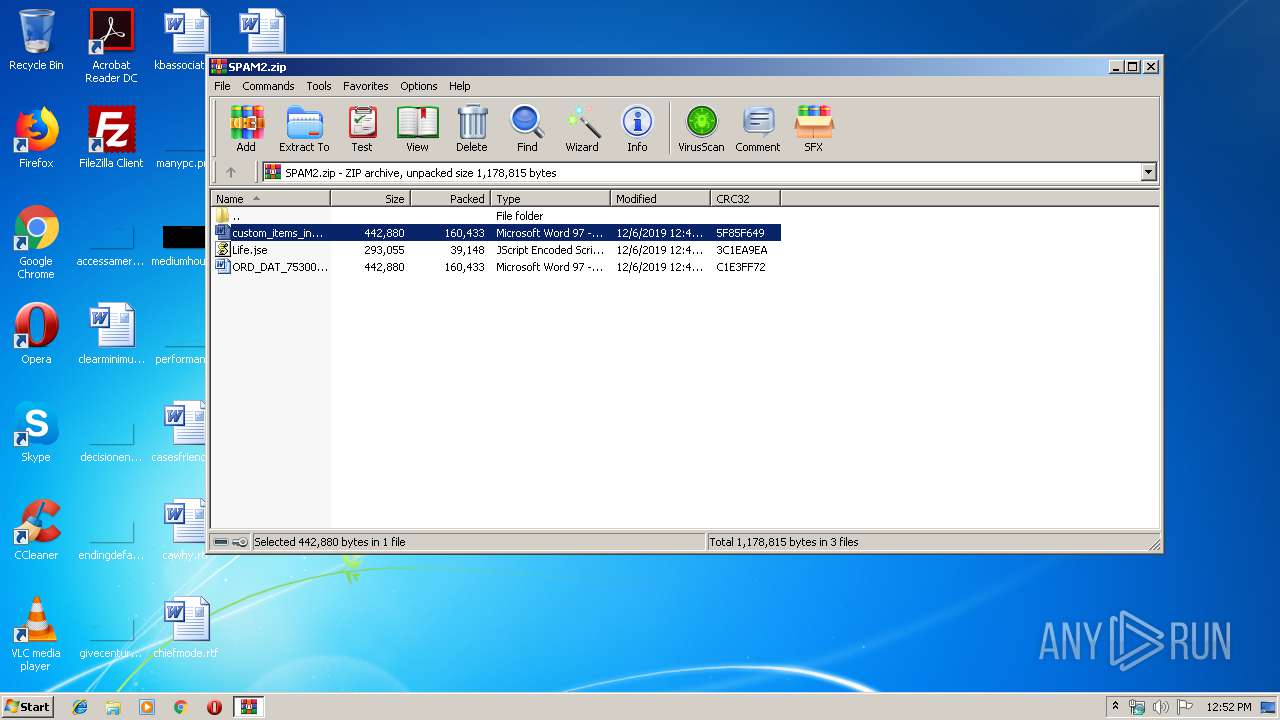
| ZipCRC: | 0x5f85f649 |
| ZipCompressedSize: | 160433 |
| ZipUncompressedSize: | 442880 |
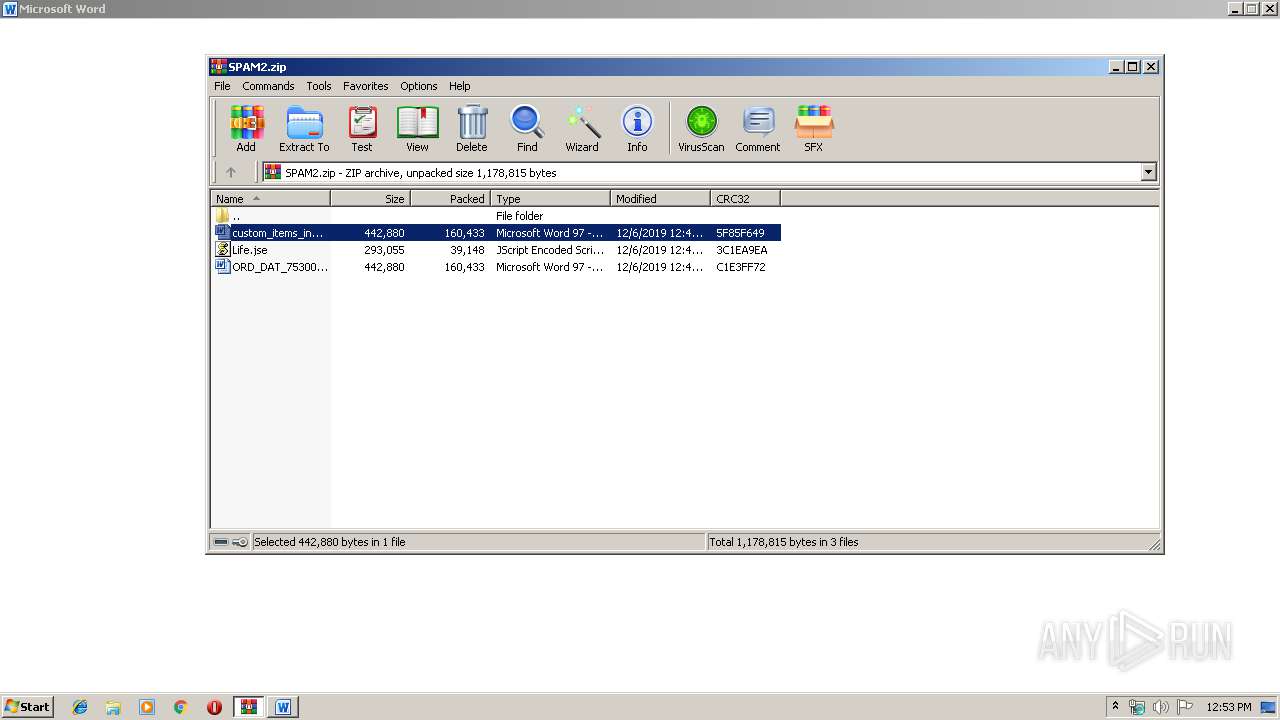
| ZipFileName: | custom_items_inv_97772837.doc |
Total processes
44
Monitored processes
10
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
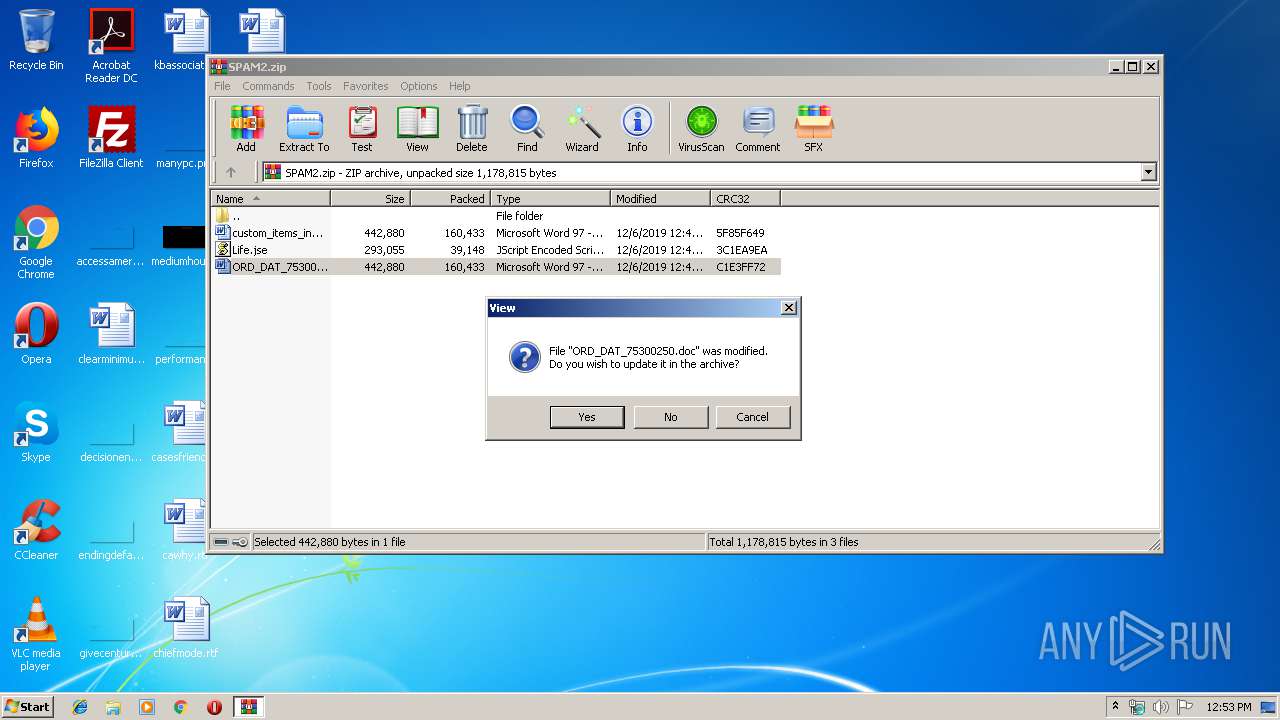
| 436 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\Microsoft\Word\Activ\Life.jse" 1 | C:\Windows\System32\WScript.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 932 | C:\Windows\system32\dwwin.exe -x -s 1060 | C:\Windows\system32\dwwin.exe | — | DW20.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1044 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Roaming\Microsoft\Word\Activ\Life.jse" 1 | C:\Windows\System32\WScript.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1792 | C:\Windows\system32\dwwin.exe -x -s 336 | C:\Windows\system32\dwwin.exe | — | DW20.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Watson Client Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1952 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa2428.30992\Life.jse" | C:\Windows\System32\WScript.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1972 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIa2428.26606\custom_items_inv_97772837.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\SPAM2.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2836 | "C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE" -x -s 336 | C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Application Error Reporting Exit code: 0 Version: 14.0.6015.1000 Modules
| |||||||||||||||
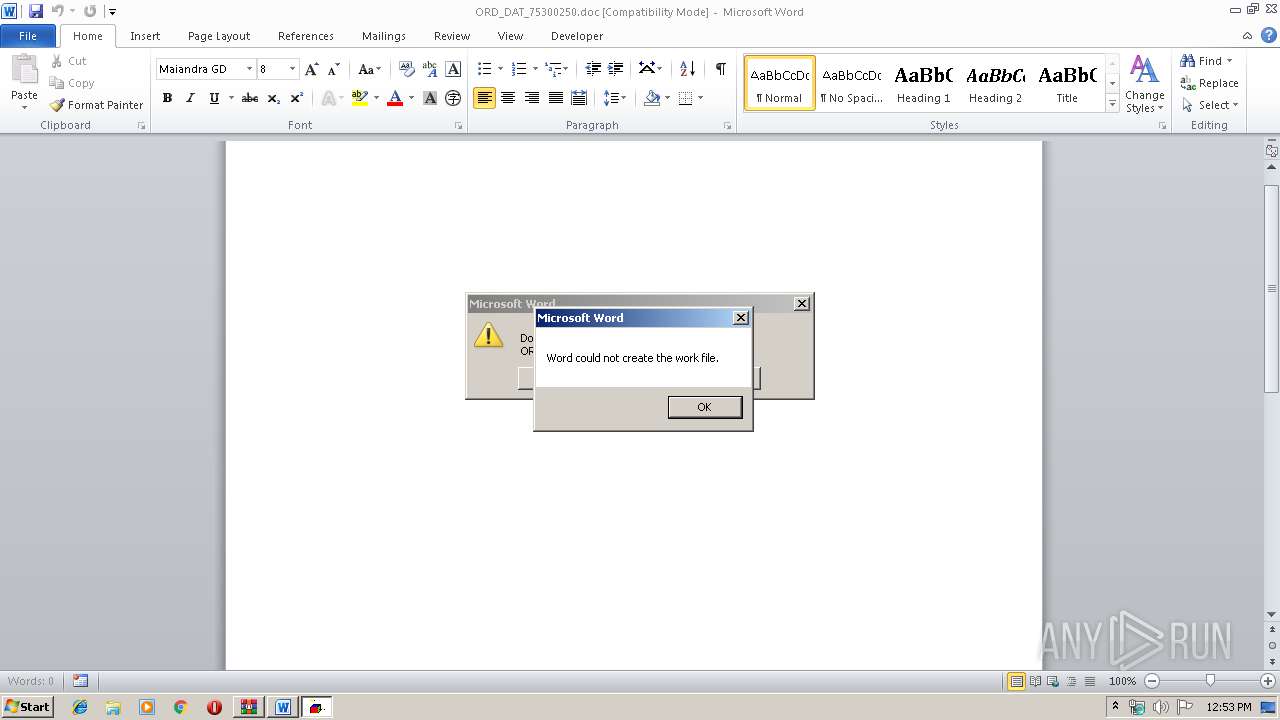
| 3272 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIa2428.28465\ORD_DAT_75300250.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3928 | "C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE" -x -s 1060 | C:\PROGRA~1\COMMON~1\MICROS~1\DW\DW20.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Application Error Reporting Exit code: 0 Version: 14.0.6015.1000 Modules
| |||||||||||||||
Total events
3 091
Read events
2 406
Write events
404
Delete events
281
Modification events
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\SPAM2.zip | |||
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2428) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\wshext.dll,-4805 |
Value: JScript Encoded Script File | |||
| (PID) Process: | (1972) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | -pa |
Value: 2D706100B4070000010000000000000000000000 | |||
Executable files
0
Suspicious files
11
Text files
0
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1972 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC80D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1972 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\E944A22D.wmf | — | |
MD5:— | SHA256:— | |||
| 1972 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\2D88A1C3.wmf | — | |
MD5:— | SHA256:— | |||
| 1972 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF75F53A976077DCAF.TMP | — | |
MD5:— | SHA256:— | |||
| 1972 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{B4123668-6ABE-478E-8A98-867ADBE4F63A}.tmp | — | |
MD5:— | SHA256:— | |||
| 3272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRFB5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\42EF14BE.wmf | — | |
MD5:— | SHA256:— | |||
| 3272 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B6F25F7C.wmf | — | |
MD5:— | SHA256:— | |||
| 1972 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{C2BD5854-FA12-40BF-BBC2-79773DD407C0}.tmp | — | |
MD5:— | SHA256:— | |||
| 1972 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{410E45A2-3E33-4C2C-8658-65C7174D6815}.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report