| download: | crack-adobe-acrobat-pro-dc |
| Full analysis: | https://app.any.run/tasks/28dc860f-1b7d-4a39-a37c-41c9ffbb7f28 |
| Verdict: | No threats detected |
| Analysis date: | July 30, 2018, 23:57:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines, with CRLF, LF line terminators |
| MD5: | C27FAB51858ED698EEAE7E98AB93E4BB |
| SHA1: | 12D98E27D5448CC8D420A84F303BA6621A9B4DED |
| SHA256: | D5FFF6D16B483521A1CDAD3DB234AC7847EEEACA5F989C77D800A231A7415FE5 |
| SSDEEP: | 192:/wrrRoQfgTEWiR5ULqg27YKlHDOTKeH+VJhw4sjCxLqHRMTMEs9N:orrRoQrWWULqg27Y6DOTKeH+9w5O62AN |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Changes internet zones settings
- iexplore.exe (PID: 2172)
Reads internet explorer settings
- iexplore.exe (PID: 2212)
Creates files in the user directory
- iexplore.exe (PID: 2212)
Application launched itself
- iexplore.exe (PID: 2172)
Reads Internet Cache Settings
- iexplore.exe (PID: 2212)
Dropped object may contain URL's
- iexplore.exe (PID: 2212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| viewport: | width=device-width, initial-scale=1.0 |
|---|---|
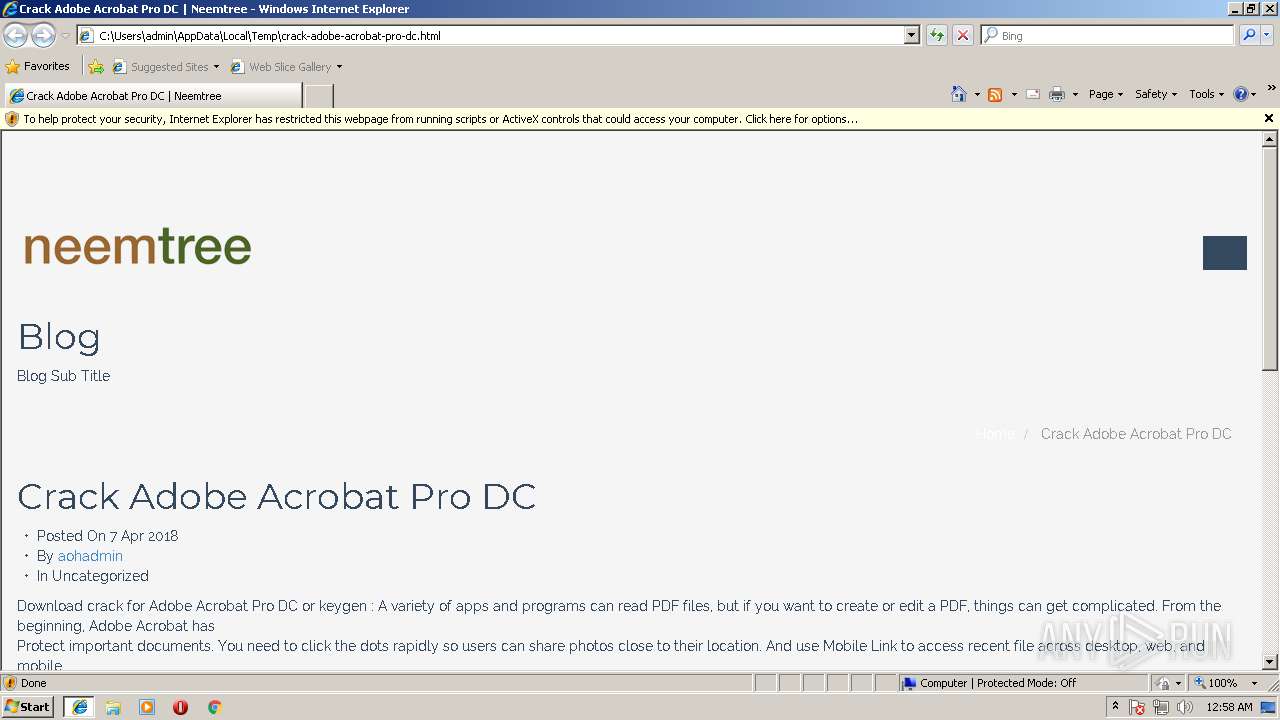
| Title: | Crack Adobe Acrobat Pro DC | Neemtree |
| Generator: | WordPress 4.0.2 |
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2172 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\crack-adobe-acrobat-pro-dc.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2172 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
382
Read events
311
Write events
70
Delete events
1
Modification events
| (PID) Process: | (2172) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2172) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2172) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2172) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2172) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2172) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000048000000010000000000000000000000000000000000000000000000B096B68868EBD301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000D8BFD602040000000000000000000000000000000000000000000000F4BFD602040000000000000000000000000000000000000000000000D8372A0000000000FFFFFFFF000000000000000000000000010000002E00000000000000000000000000000002000000C0A801640000000000000000D84ED505AC02000005000000010000000000000000000000010000000000000000000000BF060000000000000000000000000000000000001000000088C0D60204000000000000000000000000000000000000000000000000000000C8E40C00000000000C0000000000000000000000 | |||
| (PID) Process: | (2172) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {62A707BF-9454-11E8-ACE5-5254004AAD11} |
Value: 0 | |||
| (PID) Process: | (2172) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2172) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 10 | |||
| (PID) Process: | (2172) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E207070001001E0017003A0000005900 | |||
Executable files
0
Suspicious files
0
Text files
12
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2172 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2172 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2212 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 2212 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GUFVP8I9\style[1].css | text | |
MD5:— | SHA256:— | |||
| 2212 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\XB3OCR2W\bootstrap.min[1].css | text | |
MD5:— | SHA256:— | |||
| 2212 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GUFVP8I9\css[1].txt | text | |
MD5:— | SHA256:— | |||
| 2212 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\NBLQPZGH\font-awesome.min[1].css | text | |
MD5:5034FB120B167841D865CFB74DB35AFB | SHA256:7D29C411740F64C962548166E1C9AE5CECC6A878E62910956309BDA5DB585232 | |||
| 2212 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\NBLQPZGH\html5shiv[1].js | html | |
MD5:262BB88879EFAAF75C74154FE0308952 | SHA256:B3AA003ABF3B6AAF1654FE8669472E3C01DBA7BB73BE4A8B73A3423CFEEB0E39 | |||
| 2212 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\HHUAAB7W\animate[1].css | text | |
MD5:6F60887BBB701EE7B18987F47FD1D810 | SHA256:18518744197A63F783E6B6F310CB6B835867939028AFFD5DEAA3DD980F3E6EA7 | |||
| 2212 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\GUFVP8I9\prettyPhoto[1].css | text | |
MD5:E8D324D0A1C308CC2C9FDDDB263223D5 | SHA256:C63BE02717683D2EFDC8C887D77D289092A50B7D51210E87033045EA2B7C9EED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
14
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2212 | iexplore.exe | GET | — | 182.50.148.128:80 | http://www.neemtree.in/wp-content/themes/flat-theme/assets/js/jquery.prettyPhoto.js?ver=4.0.2 | SG | — | — | unknown |
2212 | iexplore.exe | GET | — | 182.50.148.128:80 | http://www.neemtree.in/wp-content/themes/flat-theme/assets/js/bootstrap.min.js?ver=4.0.2 | SG | — | — | unknown |
2212 | iexplore.exe | GET | — | 182.50.148.128:80 | http://www.neemtree.in/wp-content/themes/flat-theme/assets/js/jquery.isotope.min.js?ver=4.0.2 | SG | — | — | unknown |
2212 | iexplore.exe | GET | 200 | 182.50.148.128:80 | http://www.neemtree.in/wp-content/themes/flat-theme/assets/css/bootstrap.min.css?ver=4.0.2 | SG | text | 15.7 Kb | unknown |
2212 | iexplore.exe | GET | 200 | 216.58.215.234:80 | http://fonts.googleapis.com/css?family=Raleway:400,100,100italic,300,300italic,400italic,500,500italic,700,700italic,900,900italic | US | text | 162 b | whitelisted |
2212 | iexplore.exe | GET | 200 | 182.50.148.128:80 | http://www.neemtree.in/wp-content/uploads/2018/02/NT-Logo-trans2.png | SG | image | 8.37 Kb | unknown |
2212 | iexplore.exe | GET | 200 | 182.50.148.128:80 | http://www.neemtree.in/wp-content/themes/flat-theme/assets/js/html5shiv.js | SG | html | 1.19 Kb | unknown |
2212 | iexplore.exe | GET | 200 | 182.50.148.128:80 | http://www.neemtree.in/wp-content/themes/flat-theme/assets/css/prettyPhoto.css?ver=4.0.2 | SG | text | 2.70 Kb | unknown |
2212 | iexplore.exe | GET | 200 | 182.50.148.128:80 | http://www.neemtree.in/wp-content/themes/flat-theme/assets/js/respond.min.js | SG | html | 2.00 Kb | unknown |
2212 | iexplore.exe | GET | — | 182.50.148.128:80 | http://www.neemtree.in/wp-includes/js/jquery/jquery-migrate.min.js?ver=1.2.1 | SG | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.229.133.150:445 | platform.linkedin.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
4 | System | 192.229.133.150:139 | platform.linkedin.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2172 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2212 | iexplore.exe | 182.50.148.128:80 | www.neemtree.in | GoDaddy.com, LLC | SG | unknown |
2212 | iexplore.exe | 216.58.215.234:80 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2212 | iexplore.exe | 216.58.215.227:80 | fonts.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
platform.linkedin.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.neemtree.in |
| unknown |
www.bing.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |