| File name: | HD-DisableHyperV_native_v2.exe |
| Full analysis: | https://app.any.run/tasks/a691331c-5baa-415e-b3e0-6702a37501be |
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2023, 19:07:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 4FE73F47423A35231F170ED7A678945B |
| SHA1: | 66932B36FDE3401EE92AA586D00E537E95F8F1F4 |
| SHA256: | D5FF2F248E53D56FCA298A403D780316C0C160867ECD79E8CEBDD3BBD02854AB |
| SSDEEP: | 6144:w95IzT4KtZYXQd0BG96mSVwt/+/+a+KxRFb+g3ZCdqOwnD+FcYFE3N:wivtCXQd0/mS6xfWRlZC89D+FcYFm |
MALICIOUS
Application was dropped or rewritten from another process
- HD-DisableHyperV.exe (PID: 1172)
- HD-DisableHyperV.exe (PID: 2940)
- dismhost.exe (PID: 3856)
- dismhost.exe (PID: 3392)
- dismhost.exe (PID: 3984)
Drops the executable file immediately after the start
- HD-DisableHyperV_native_v2.exe (PID: 1540)
Creates a writable file the system directory
- TrustedInstaller.exe (PID: 2844)
Loads dropped or rewritten executable
- Dism.exe (PID: 3852)
- Dism.exe (PID: 984)
- TrustedInstaller.exe (PID: 2844)
- Dism.exe (PID: 3280)
- dismhost.exe (PID: 3856)
- dismhost.exe (PID: 3984)
- dismhost.exe (PID: 3392)
SUSPICIOUS
Executable content was dropped or overwritten
- HD-DisableHyperV_native_v2.exe (PID: 1540)
- Dism.exe (PID: 3852)
- Dism.exe (PID: 984)
- Dism.exe (PID: 3280)
Reads the Internet Settings
- HD-DisableHyperV.exe (PID: 2940)
- HD-DisableHyperV_native_v2.exe (PID: 1540)
Uses REG/REGEDIT.EXE to modify register
- cmd.exe (PID: 452)
- cmd.exe (PID: 1240)
- cmd.exe (PID: 3024)
Starts CMD.EXE for commands execution
- HD-DisableHyperV.exe (PID: 2940)
Reads settings of System Certificates
- TrustedInstaller.exe (PID: 2844)
Drops a file with too old compile date
- Dism.exe (PID: 3852)
- Dism.exe (PID: 984)
- Dism.exe (PID: 3280)
Checks Windows Trust Settings
- TrustedInstaller.exe (PID: 2844)
INFO
Checks supported languages
- HD-DisableHyperV_native_v2.exe (PID: 1540)
- HD-DisableHyperV.exe (PID: 2940)
- dismhost.exe (PID: 3856)
- TrustedInstaller.exe (PID: 2844)
- dismhost.exe (PID: 3392)
- dismhost.exe (PID: 3984)
The process checks LSA protection
- HD-DisableHyperV.exe (PID: 2940)
- HD-DisableHyperV_native_v2.exe (PID: 1540)
- WISPTIS.EXE (PID: 184)
- Dism.exe (PID: 3852)
- dismhost.exe (PID: 3856)
- TrustedInstaller.exe (PID: 2844)
- Dism.exe (PID: 984)
- dismhost.exe (PID: 3392)
- Dism.exe (PID: 3280)
- dismhost.exe (PID: 3984)
Reads the computer name
- HD-DisableHyperV_native_v2.exe (PID: 1540)
- HD-DisableHyperV.exe (PID: 2940)
- dismhost.exe (PID: 3856)
- TrustedInstaller.exe (PID: 2844)
- dismhost.exe (PID: 3392)
- dismhost.exe (PID: 3984)
Reads the machine GUID from the registry
- HD-DisableHyperV.exe (PID: 2940)
- TrustedInstaller.exe (PID: 2844)
- dismhost.exe (PID: 3856)
- dismhost.exe (PID: 3392)
- dismhost.exe (PID: 3984)
Creates files or folders in the user directory
- HD-DisableHyperV.exe (PID: 2940)
Drops the executable file immediately after the start
- Dism.exe (PID: 3852)
- Dism.exe (PID: 984)
- Dism.exe (PID: 3280)
Drops a file that was compiled in debug mode
- Dism.exe (PID: 3852)
- Dism.exe (PID: 984)
- Dism.exe (PID: 3280)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2021-Jul-19 13:21:27 |
| Detected languages: |
|
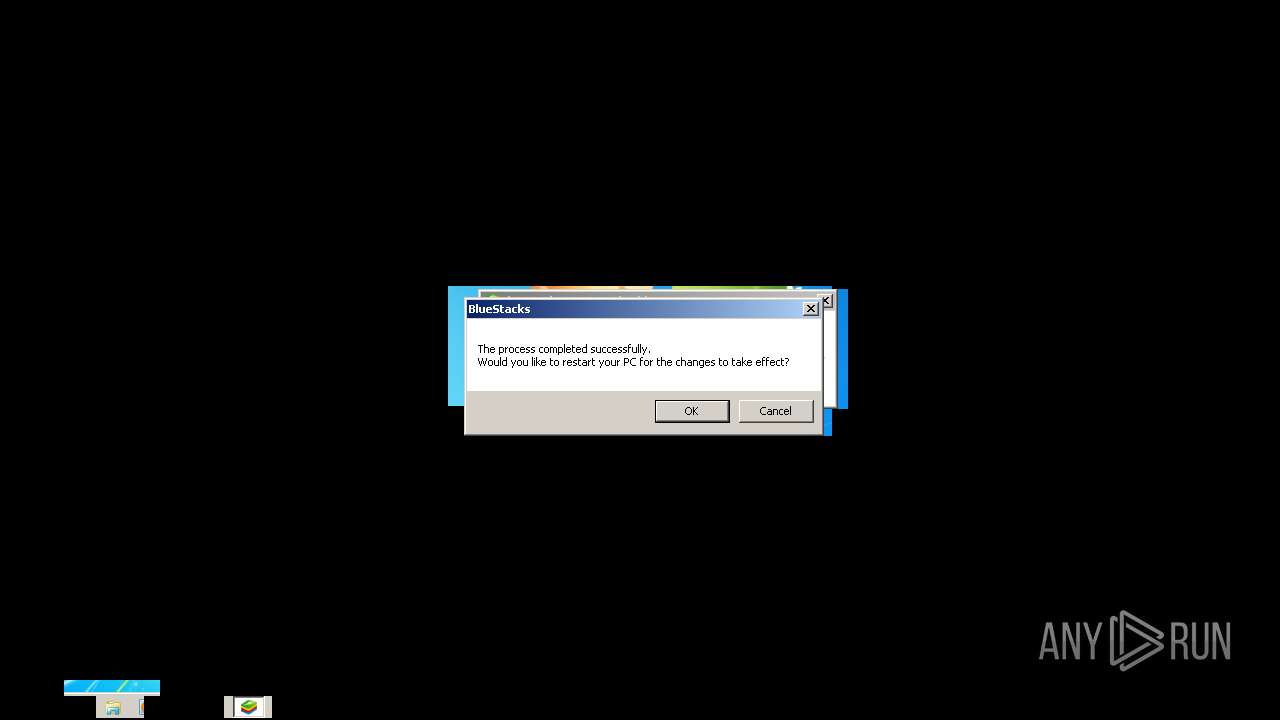
| CompanyName: | BlueStack Systems Inc. |
| FileDescription: | BlueStacks Setup |
| FileVersion: | 5.0 |
| InternalName: | BlueStacks Installer |
| LegalCopyright: | Copyright (c) 2010-2021 BlueStack Systems Inc. |
| OriginalFilename: | BlueStacksInstaller.exe |
| ProductName: | BlueStacks 5 |
| ProductVersion: | 5.0 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 240 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 4 |
| TimeDateStamp: | 2021-Jul-19 13:21:27 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 4096 | 133226 | 133632 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65255 |
.rdata | 139264 | 30512 | 30720 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.7182 |
.data | 172032 | 17988 | 6144 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.06813 |
.rsrc | 192512 | 122418 | 122880 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.62585 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 6.35216 | 1128 | UNKNOWN | English - United States | RT_ICON |
2 | 5.78375 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 5.3198 | 9640 | UNKNOWN | English - United States | RT_ICON |
4 | 5.11421 | 16936 | UNKNOWN | English - United States | RT_ICON |
5 | 4.72161 | 67624 | UNKNOWN | English - United States | RT_ICON |
6 | 7.958 | 20348 | UNKNOWN | English - United States | RT_ICON |
97 | 3.04857 | 184 | Latin 1 / Western European | English - United States | RT_DIALOG |
188 | 2.17822 | 84 | Latin 1 / Western European | English - United States | RT_STRING |
207 | 2.04373 | 76 | Latin 1 / Western European | English - United States | RT_STRING |
1 (#2) | 2.38262 | 96 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
Total processes
74
Monitored processes
24
Malicious processes
12
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 120 | bcdedit /set hypervisorlaunchtype off | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Boot Configuration Data Editor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 184 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | HD-DisableHyperV.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Pen and Touch Input Component Exit code: 24 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 452 | "cmd" /C reg add "HKLM\SYSTEM\CurrentControlSet\Control\DeviceGuard" /v "EnableVirtualizationBasedSecurity" /t REG_DWORD /d 0 /f | C:\Windows\system32\cmd.exe | — | HD-DisableHyperV.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 632 | reg add "HKLM\SYSTEM\CurrentControlSet\Control\DeviceGuard" /v "Locked" /t REG_DWORD /d 0 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 984 | dism.exe /Online /Disable-Feature:Containers-DisposableClientVM /NoRestart | C:\Windows\system32\Dism.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Image Servicing Utility Exit code: 2148468748 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1172 | "C:\Users\admin\AppData\Local\Temp\7zS406DA6F6\HD-DisableHyperV.exe" | C:\Users\admin\AppData\Local\Temp\7zS406DA6F6\HD-DisableHyperV.exe | — | HD-DisableHyperV_native_v2.exe | |||||||||||
User: admin Company: BlueStack Systems, Inc. Integrity Level: MEDIUM Description: BlueStacks 5 - Hyper-V Tool Exit code: 3221226540 Version: 5.3.80.1006 Modules
| |||||||||||||||
| 1240 | "cmd" /C reg add "HKLM\SYSTEM\CurrentControlSet\Control\DeviceGuard\Scenarios\HypervisorEnforcedCodeIntegrity" /v "Enabled" /t REG_DWORD /d 0 /f | C:\Windows\system32\cmd.exe | — | HD-DisableHyperV.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1396 | "cmd" /C dism.exe /Online /Disable-Feature:Containers-DisposableClientVM /NoRestart | C:\Windows\system32\cmd.exe | — | HD-DisableHyperV.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 2148468748 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1404 | reg add "HKLM\SYSTEM\CurrentControlSet\Control\DeviceGuard\Scenarios\HypervisorEnforcedCodeIntegrity" /v "Enabled" /t REG_DWORD /d 0 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1540 | "C:\Users\admin\AppData\Local\Temp\HD-DisableHyperV_native_v2.exe" | C:\Users\admin\AppData\Local\Temp\HD-DisableHyperV_native_v2.exe | Explorer.EXE | ||||||||||||
User: admin Company: BlueStack Systems Inc. Integrity Level: MEDIUM Description: BlueStacks Setup Exit code: 0 Version: 5.0 Modules
| |||||||||||||||
Total events
65 690
Read events
65 494
Write events
196
Delete events
0
Modification events
| (PID) Process: | (1540) HD-DisableHyperV_native_v2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1540) HD-DisableHyperV_native_v2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1540) HD-DisableHyperV_native_v2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1540) HD-DisableHyperV_native_v2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2940) HD-DisableHyperV.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: HD-DisableHyperV.exe | |||
| (PID) Process: | (2940) HD-DisableHyperV.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2940) HD-DisableHyperV.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2940) HD-DisableHyperV.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2940) HD-DisableHyperV.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (184) WISPTIS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: WISPTIS.EXE | |||
Executable files
126
Suspicious files
0
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3852 | Dism.exe | C:\Windows\Logs\DISM\dism.log | text | |
MD5:— | SHA256:— | |||
| 1540 | HD-DisableHyperV_native_v2.exe | C:\Users\admin\AppData\Local\Temp\7zS406DA6F6\HD-DisableHyperV.exe | executable | |
MD5:3AD5957A561427E93DB12C8911E41DA8 | SHA256:3AFCE2EBE39710ED6209F2640B7A11AFC8A66DD8293B2CB88A15861B7057ABFB | |||
| 3852 | Dism.exe | C:\Users\admin\AppData\Local\Temp\BC6F2BEC-EC44-4C45-A506-35E054B59B0C\DismCorePS.dll | executable | |
MD5:9733B1D4E0EFCC3E11A133238B55F10F | SHA256:E07766D4908BAA9790D0C843E7A6E5CEE45DD17A84860B2CF0477D276392C97B | |||
| 3852 | Dism.exe | C:\Users\admin\AppData\Local\Temp\BC6F2BEC-EC44-4C45-A506-35E054B59B0C\DismHost.exe | executable | |
MD5:5E2E337F6F942B63428DB19355D6742B | SHA256:F60406C5D01B22F95C7F7298498475F0930550CBBF6BB31EB01E1E565FA175AE | |||
| 1540 | HD-DisableHyperV_native_v2.exe | C:\Users\admin\AppData\Local\Temp\7zS406DA6F6\HD-DisableHyperV.exe.config | xml | |
MD5:1B456D88546E29F4F007CD0BF1025703 | SHA256:D6D316584B63BB0D670A42F88B8F84E0DE0DB4275F1A342084DC383EBEB278EB | |||
| 3852 | Dism.exe | C:\Users\admin\AppData\Local\Temp\BC6F2BEC-EC44-4C45-A506-35E054B59B0C\en-US\DismProv.dll.mui | executable | |
MD5:7B570BC665C907256E5C97F10521381C | SHA256:C5D1876E93346DB7457F1C05CB1AB17C372D9440F92093315D3321C2D6A26194 | |||
| 3852 | Dism.exe | C:\Users\admin\AppData\Local\Temp\BC6F2BEC-EC44-4C45-A506-35E054B59B0C\en-US\DismCore.dll.mui | executable | |
MD5:B065EAB0E07C62C698BD28AABC68411F | SHA256:9A2FC296980090295E214B25F37572820521C24439FED475F68C9E278DAAA3C9 | |||
| 3852 | Dism.exe | C:\Users\admin\AppData\Local\Temp\BC6F2BEC-EC44-4C45-A506-35E054B59B0C\en-US\FolderProvider.dll.mui | executable | |
MD5:0A1FFD32117198CA3F1056051635BC75 | SHA256:0C31CBB332B849236CE4159371C7C2488871E5420EFEC274E4B3F12BEE5FE480 | |||
| 3852 | Dism.exe | C:\Users\admin\AppData\Local\Temp\BC6F2BEC-EC44-4C45-A506-35E054B59B0C\DmiProvider.dll | executable | |
MD5:6128693331EA9946A186F2608330D5FB | SHA256:EFDA6FCDB7A9E94CA467DB23C00B04C42ADE536EE7D5B12D589EC913FB1B3536 | |||
| 3852 | Dism.exe | C:\Users\admin\AppData\Local\Temp\BC6F2BEC-EC44-4C45-A506-35E054B59B0C\en-US\CbsProvider.dll.mui | executable | |
MD5:3D3835F95630A5F46DEA1F7FD823E6A5 | SHA256:D32B28B184439673E3AC94070453FAF69434DF29A064558015D2A3FCE2956CA4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3180 | consent.exe | 8.248.139.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
dns.msftncsi.com |
| shared |
Threats
Process | Message |
|---|---|
Dism.exe | PID=3852 Attempting to initialize the logger from the Image Session. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=3852 Initializing a provider store for the LOCAL session type. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=3852 Instantiating the Provider Store. - CDISMImageSession::get_ProviderStore |
Dism.exe | PID=3852 Provider has not previously been encountered. Attempting to initialize the provider. - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=3852 Provider has not previously been encountered. Attempting to initialize the provider. - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=3852 Instantiating the Provider Store. - CDISMImageSession::get_ProviderStore |
Dism.exe | PID=3852 Initializing a provider store for the LOCAL session type. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=3852 Attempting to initialize the logger from the Image Session. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=3852 Loading Provider from location C:\Windows\System32\Dism\LogProvider.dll - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=3852 Loading Provider from location C:\Windows\System32\Dism\LogProvider.dll - CDISMProviderStore::Internal_GetProvider |