| File name: | m443_new.exe |
| Full analysis: | https://app.any.run/tasks/e6e86f49-ab1d-48f3-a1a4-c84e52e4d70d |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 23:55:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 7 sections |
| MD5: | 2389FB97AD8DBE7E84CACB8EC10BC5A6 |
| SHA1: | A183E99440D4593791C4CC2C6186AA30699C53C6 |
| SHA256: | D5F0B84B1E0EB493FCAE70F5077639BC7677E36216067DD41868B9D40486E224 |
| SSDEEP: | 98304:u/NkRdEtqLdOvOSWHO2mSxzbOep2irTPn6:W+dl6 |
MALICIOUS
Executing a file with an untrusted certificate
- m443_new.exe (PID: 6892)
- m443_new.exe (PID: 7056)
- RuntimeBroker.exe (PID: 1944)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 5008)
SUSPICIOUS
Uses WMIC.EXE to obtain operating system information
- m443_new.exe (PID: 6892)
- RuntimeBroker.exe (PID: 1944)
There is functionality for taking screenshot (YARA)
- m443_new.exe (PID: 6892)
- RuntimeBroker.exe (PID: 1944)
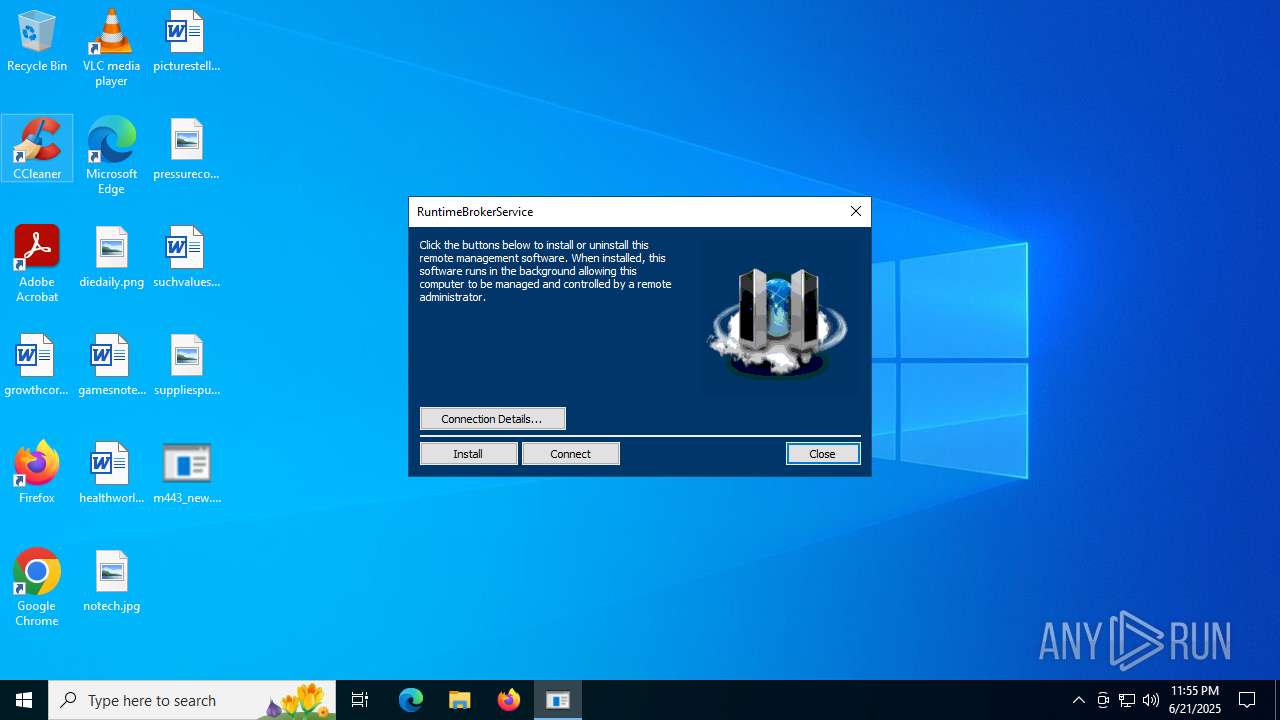
MeshAgent potential remote access (YARA)
- m443_new.exe (PID: 6892)
- RuntimeBroker.exe (PID: 1944)
Reads security settings of Internet Explorer
- m443_new.exe (PID: 6892)
- RuntimeBroker.exe (PID: 1944)
Reads the date of Windows installation
- m443_new.exe (PID: 6892)
Application launched itself
- m443_new.exe (PID: 6892)
The process verifies whether the antivirus software is installed
- m443_new.exe (PID: 7056)
- WMIC.exe (PID: 1688)
- conhost.exe (PID: 2808)
- WMIC.exe (PID: 4520)
- conhost.exe (PID: 4168)
- conhost.exe (PID: 5496)
- WMIC.exe (PID: 6896)
- WMIC.exe (PID: 6828)
- conhost.exe (PID: 2148)
- powershell.exe (PID: 3932)
- conhost.exe (PID: 6404)
- RuntimeBroker.exe (PID: 1944)
- conhost.exe (PID: 4100)
- powershell.exe (PID: 5008)
- conhost.exe (PID: 3488)
- powershell.exe (PID: 3672)
- cmd.exe (PID: 2320)
- conhost.exe (PID: 2212)
- manage-bde.exe (PID: 2348)
Executable content was dropped or overwritten
- m443_new.exe (PID: 7056)
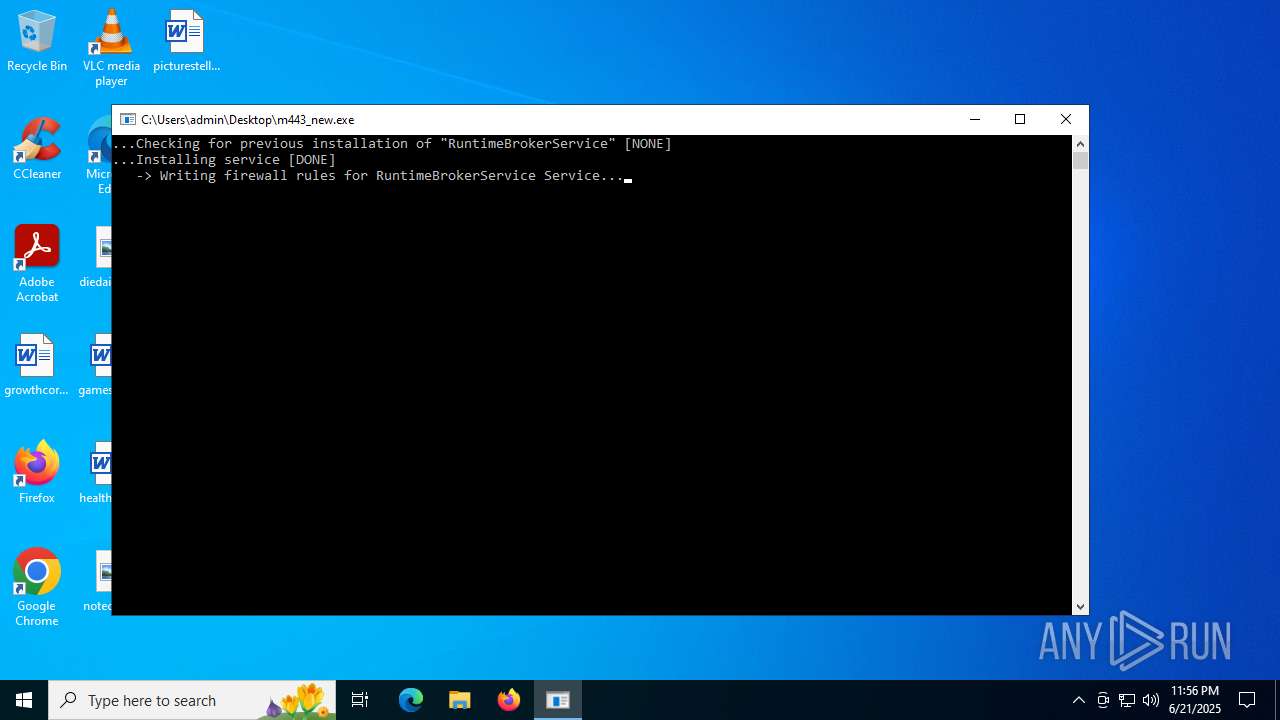
Creates or modifies Windows services
- m443_new.exe (PID: 7056)
Executes as Windows Service
- RuntimeBroker.exe (PID: 1944)
Creates a software uninstall entry
- m443_new.exe (PID: 7056)
- RuntimeBroker.exe (PID: 1944)
Uses WMIC.EXE to obtain system information
- RuntimeBroker.exe (PID: 1944)
Uses WMIC.EXE to obtain computer system information
- RuntimeBroker.exe (PID: 1944)
Starts POWERSHELL.EXE for commands execution
- RuntimeBroker.exe (PID: 1944)
The process hides Powershell's copyright startup banner
- RuntimeBroker.exe (PID: 1944)
The process bypasses the loading of PowerShell profile settings
- RuntimeBroker.exe (PID: 1944)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 5008)
Starts CMD.EXE for commands execution
- RuntimeBroker.exe (PID: 1944)
INFO
The sample compiled with english language support
- m443_new.exe (PID: 6892)
- m443_new.exe (PID: 7056)
Checks supported languages
- m443_new.exe (PID: 6892)
- m443_new.exe (PID: 7056)
- RuntimeBroker.exe (PID: 1944)
Reads the computer name
- m443_new.exe (PID: 6892)
- m443_new.exe (PID: 7056)
- RuntimeBroker.exe (PID: 1944)
Reads security settings of Internet Explorer
- WMIC.exe (PID: 4676)
- WMIC.exe (PID: 1688)
- WMIC.exe (PID: 4520)
- WMIC.exe (PID: 6828)
- WMIC.exe (PID: 6896)
Reads the machine GUID from the registry
- m443_new.exe (PID: 6892)
- RuntimeBroker.exe (PID: 1944)
Process checks computer location settings
- m443_new.exe (PID: 6892)
Creates files in the program directory
- m443_new.exe (PID: 7056)
- RuntimeBroker.exe (PID: 1944)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 3672)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2022:12:09 20:12:49+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14 |
| CodeSize: | 2122240 |
| InitializedDataSize: | 1294848 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d9d8c |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 3.0.0.1 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | RuntimeBrokerService |
| FileVersion: | 3.0.0.1 |
| LegalCopyright: | Apache 2.0 License |
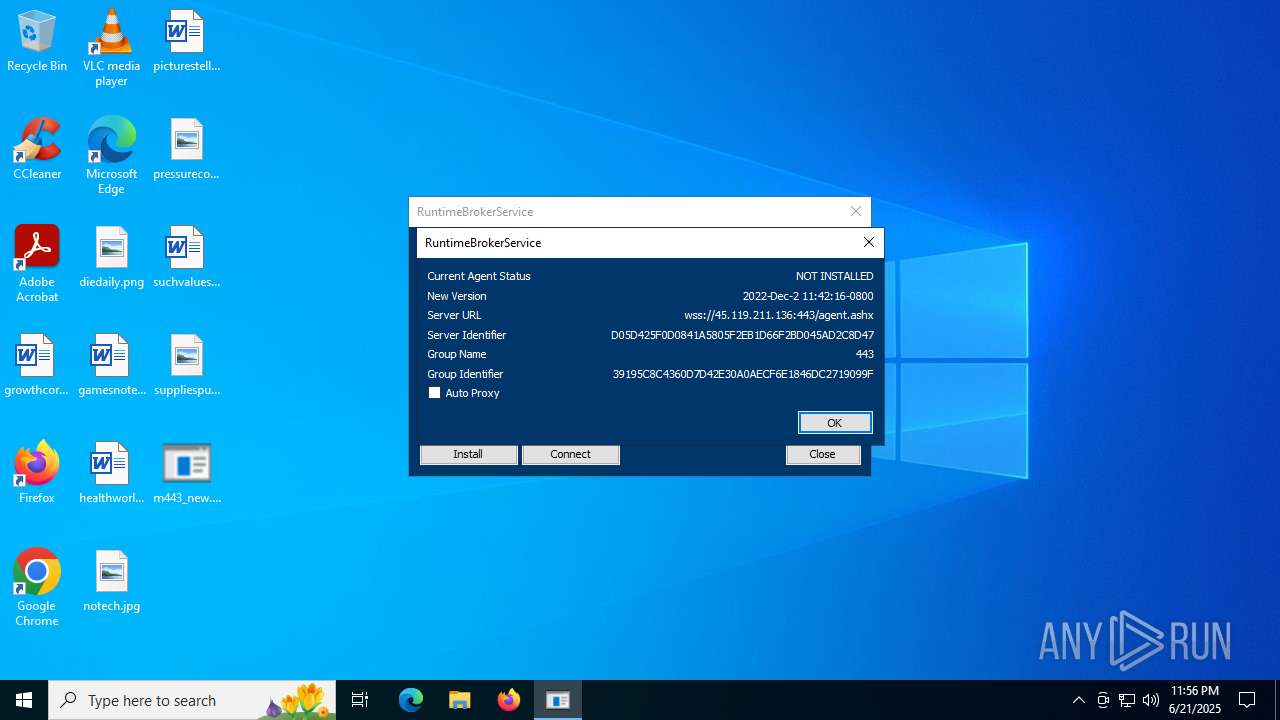
| ProductName: | MeshCentral Agent |
| ProductVersion: | Commit: 2022-Dec-2 11:42:16-0800 |
| OriginalFileName: | RuntimeBroker |
Total processes
164
Monitored processes
25
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1688 | wmic SystemEnclosure get ChassisTypes | C:\Windows\System32\wbem\WMIC.exe | — | RuntimeBroker.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1944 | "C:\Program Files\AVGCompany\RuntimeBrokerService\RuntimeBroker.exe" --meshServiceName="RuntimeBrokerService" --installedByUser="S-1-5-21-1693682860-607145093-2874071422-1001" | C:\Program Files\AVGCompany\RuntimeBrokerService\RuntimeBroker.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Description: RuntimeBrokerService Version: 3.0.0.1 Modules
| |||||||||||||||
| 2040 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | m443_new.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2212 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2320 | /c manage-bde -protectors -get C: -Type recoverypassword | C:\Windows\System32\cmd.exe | — | RuntimeBroker.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 4294967295 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2348 | manage-bde -protectors -get C: -Type recoverypassword | C:\Windows\System32\manage-bde.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: BitLocker Drive Encryption: Configuration Tool Exit code: 4294967295 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2808 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | WMIC.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3488 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 051
Read events
18 031
Write events
20
Delete events
0
Modification events
| (PID) Process: | (7056) m443_new.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\RuntimeBrokerService |
| Operation: | write | Name: | ImagePath |
Value: "C:\Program Files\AVGCompany\RuntimeBrokerService\RuntimeBroker.exe" --meshServiceName="RuntimeBrokerService" --installedByUser="S-1-5-21-1693682860-607145093-2874071422-1001" | |||
| (PID) Process: | (7056) m443_new.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\RuntimeBrokerService |
| Operation: | write | Name: | _InstalledBy |
Value: S-1-5-21-1693682860-607145093-2874071422-1001 | |||
| (PID) Process: | (7056) m443_new.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RuntimeBrokerService |
| Operation: | write | Name: | DisplayName |
Value: RuntimeBrokerService | |||
| (PID) Process: | (7056) m443_new.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RuntimeBrokerService |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\AVGCompany\RuntimeBrokerService\RuntimeBroker.exe | |||
| (PID) Process: | (7056) m443_new.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RuntimeBrokerService |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\AVGCompany\RuntimeBrokerService\ | |||
| (PID) Process: | (7056) m443_new.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RuntimeBrokerService |
| Operation: | write | Name: | EstimatedSize |
Value: 3378 | |||
| (PID) Process: | (7056) m443_new.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RuntimeBrokerService |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (7056) m443_new.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RuntimeBrokerService |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (7056) m443_new.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RuntimeBrokerService |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\AVGCompany\RuntimeBrokerService\RuntimeBroker.exe -funinstall --meshServiceName="RuntimeBrokerService" | |||
| (PID) Process: | (7056) m443_new.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\RuntimeBrokerService |
| Operation: | write | Name: | DisplayVersion |
Value: 2022-12-02 19:42:16.000+00:00 | |||
Executable files
1
Suspicious files
7
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7056 | m443_new.exe | C:\Program Files\AVGCompany\RuntimeBrokerService\RuntimeBroker.exe | executable | |
MD5:2389FB97AD8DBE7E84CACB8EC10BC5A6 | SHA256:D5F0B84B1E0EB493FCAE70F5077639BC7677E36216067DD41868B9D40486E224 | |||
| 1944 | RuntimeBroker.exe | C:\Windows\System32\config\systemprofile\AppData\Roaming\Microsoft\SystemCertificates\My\Keys\4D1B4D6B94AA38B684A776DAA0F4DFED321461A2 | binary | |
MD5:FC6266F6B41A1FCD28A6CEA0E6D30965 | SHA256:BE22E6F72C60E2E41250D3B1E2531FF93B1BC76E031013A524F53A3B4F29F789 | |||
| 1944 | RuntimeBroker.exe | C:\Windows\System32\config\systemprofile\AppData\Roaming\Microsoft\SystemCertificates\My\Certificates\72389FA734700409D72D053CE0C544DA48BAE0B2 | binary | |
MD5:8F1F1CF8AE17565A2E2BF55E6057875F | SHA256:230441254146F1B982A8E613F213A92F261FD6B511F7F1CB95E525DC5F098996 | |||
| 1944 | RuntimeBroker.exe | C:\Windows\System32\config\systemprofile\AppData\Roaming\Microsoft\SystemCertificates\My\Certificates\9DC9421EA7A8748E1A0B1E063785FAA62B05AE42 | binary | |
MD5:B8E46BC97C08E7985E3B5EA703EB1FE8 | SHA256:DC3354B90A0549099F6D78AC9E22FB9813F3F76C92238200BC0C2BD4C5BFF182 | |||
| 1944 | RuntimeBroker.exe | C:\Program Files\AVGCompany\RuntimeBrokerService\RuntimeBroker.msh | text | |
MD5:B3B85880ECFA8898F5F5E215359984A4 | SHA256:7D747081C7B6F018CF67443330D55A9784746E635E4D790C99D5FD7370F7B51A | |||
| 3932 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_wnol0zxl.ku5.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 1944 | RuntimeBroker.exe | C:\Program Files\AVGCompany\RuntimeBrokerService\RuntimeBroker.db | binary | |
MD5:62939654112735994A41395C8AB2223B | SHA256:0490B3DDD9D28E7F5796C5C980B7555566A87E7E955D670565B382FF5773EEEA | |||
| 1944 | RuntimeBroker.exe | C:\Windows\System32\config\systemprofile\AppData\Roaming\Microsoft\SystemCertificates\My\Keys\856486C2488D232F67985A97A449CA1A1BA3BC18 | binary | |
MD5:E4080575EC713DEFB5BFC1CE62A001FE | SHA256:371F6D758979761E38C18B1F89610092EFFAA49334297A150ACC0E0886F4B552 | |||
| 5008 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_wjvde44v.rs0.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3672 | powershell.exe | C:\Windows\Temp\__PSScriptPolicyTest_qwgs0hau.300.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
25
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5848 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2620 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2620 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5476 | RUXIMICS.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
5848 | svchost.exe | 20.190.159.23:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5848 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |