| File name: | OfficeTimeline.exe |
| Full analysis: | https://app.any.run/tasks/f7edaf7e-7dac-4242-8bff-8dfc9430edfe |
| Verdict: | Suspicious activity |
| Analysis date: | March 07, 2018, 09:58:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 33291D0D79AADF3648E450096DBE5972 |
| SHA1: | DD3572DC13BE9B427F1F3C2B5AD3300053CB5215 |
| SHA256: | D5ED5ECD376B834D6520608888DF3E6EF0D291A2C72222DFE337BBB87E09EBAC |
| SSDEEP: | 393216:sm5u+UrlrWl26wR39+Elv1cVwOdWOvn2c6rWjNXIY:ng+Wras30uqVLdWOf/6rWjt1 |
MALICIOUS
Application was dropped or rewritten from another process
- Setup.exe (PID: 3332)
SUSPICIOUS
Creates files in the program directory
- OfficeTimeline.exe (PID: 2020)
INFO
Loads rich edit control libraries
- OfficeTimeline.exe (PID: 2020)
- Setup.exe (PID: 3332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:08:22 14:09:07+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 152064 |
| InitializedDataSize: | 175104 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d348 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.20.4.0 |
| ProductVersionNumber: | 3.20.4.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Office Timeline LLC |
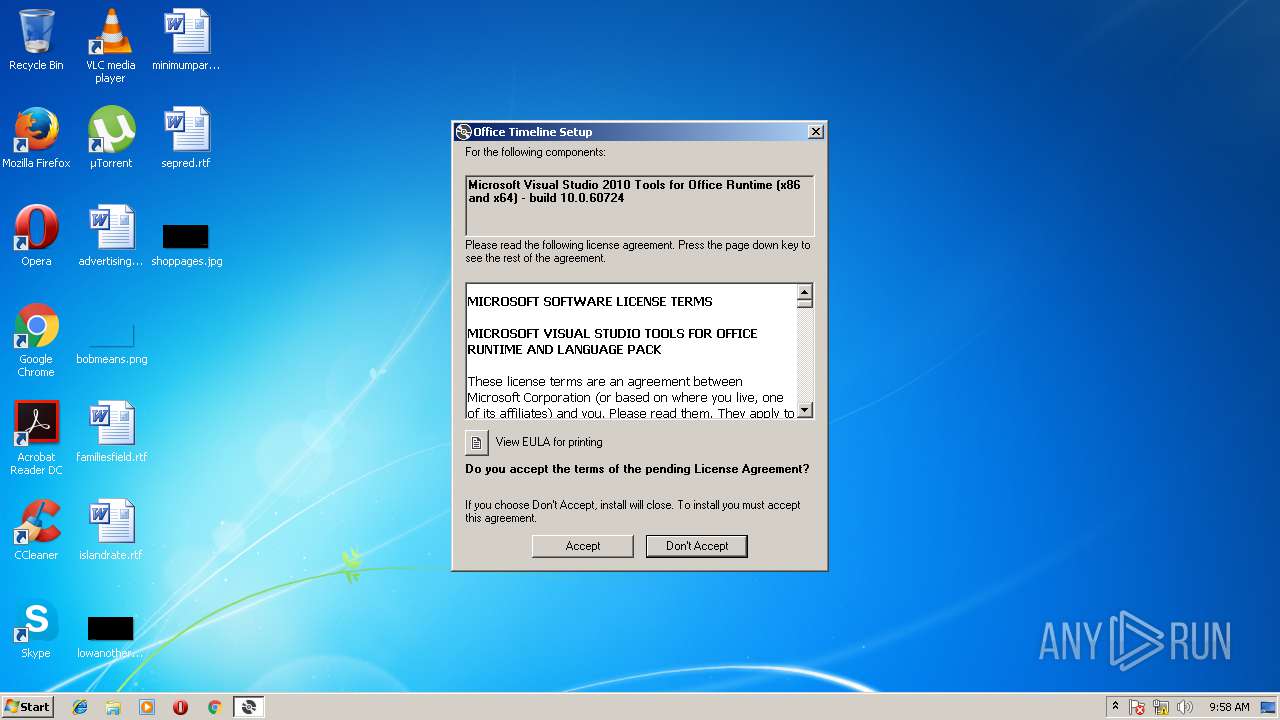
| FileDescription: | Office Timeline Setup |
| FileVersion: | 3.20.4.0 |
| InternalName: | OfficeTimeline.exe |
| LegalCopyright: | (c) OfficeTimeline LLC. All rights reserved. |
| OriginalFileName: | OfficeTimeline.exe |
| ProductName: | Office Timeline |
| ProductVersion: | 3.20.4.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Aug-2013 12:09:07 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Office Timeline LLC |
| FileDescription: | Office Timeline Setup |
| FileVersion: | 3.20.4.0 |
| InternalName: | OfficeTimeline.exe |
| LegalCopyright: | (c) OfficeTimeline LLC. All rights reserved. |
| OriginalFilename: | OfficeTimeline.exe |
| ProductName: | Office Timeline |
| ProductVersion: | 3.20.4.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 22-Aug-2013 12:09:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002517E | 0x00025200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70052 |
.rdata | 0x00027000 | 0x00004F43 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.32551 |
.data | 0x0002C000 | 0x000215E0 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.53948 |
.rsrc | 0x0004E000 | 0x00004581 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.8926 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.88858 | 377 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.36332 | 1128 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.18906 | 536 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
11 | 3.2036 | 1094 | UNKNOWN | English - United States | RT_STRING |
12 | 3.12889 | 358 | UNKNOWN | English - United States | RT_STRING |
13 | 2.95673 | 288 | UNKNOWN | English - United States | RT_STRING |
14 | 2.77928 | 186 | UNKNOWN | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
36
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1568 | "C:\Users\admin\AppData\Local\Temp\OfficeTimeline.exe" | C:\Users\admin\AppData\Local\Temp\OfficeTimeline.exe | — | explorer.exe | |||||||||||
User: admin Company: Office Timeline LLC Integrity Level: MEDIUM Description: Office Timeline Setup Exit code: 3221226540 Version: 3.20.4.0 Modules
| |||||||||||||||
| 2020 | "C:\Users\admin\AppData\Local\Temp\OfficeTimeline.exe" | C:\Users\admin\AppData\Local\Temp\OfficeTimeline.exe | explorer.exe | ||||||||||||
User: admin Company: Office Timeline LLC Integrity Level: HIGH Description: Office Timeline Setup Exit code: 0 Version: 3.20.4.0 Modules
| |||||||||||||||
| 3332 | "C:\Program Files\Office Timeline\Current\Setup Files\Setup.exe" | C:\Program Files\Office Timeline\Current\Setup Files\Setup.exe | OfficeTimeline.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup Exit code: 0 Version: 14.0.23107.0 built by: D14REL Modules
| |||||||||||||||
Total events
130
Read events
92
Write events
38
Delete events
0
Modification events
| (PID) Process: | (2020) OfficeTimeline.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2020) OfficeTimeline.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3332) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Setup_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3332) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Setup_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3332) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Setup_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3332) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Setup_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3332) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Setup_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3332) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Setup_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3332) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Setup_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3332) Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Setup_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2020 | OfficeTimeline.exe | C:\Program Files\Office Timeline\Current\Setup Files\OfficeTimeline.msi | — | |
MD5:— | SHA256:— | |||
| 3332 | Setup.exe | C:\Users\admin\AppData\Local\Temp\VSD4587.tmp\Setup.exe | executable | |
MD5:654B40ADE8677BB5C660D528749A3CBB | SHA256:1CDFDFDE5BE6257DE07F0CC53B71DFFCE58C1250938A2D9DFD024C6B645360AF | |||
| 2020 | OfficeTimeline.exe | C:\Program Files\Office Timeline\Current\Setup Files\Setup.exe | executable | |
MD5:654B40ADE8677BB5C660D528749A3CBB | SHA256:1CDFDFDE5BE6257DE07F0CC53B71DFFCE58C1250938A2D9DFD024C6B645360AF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
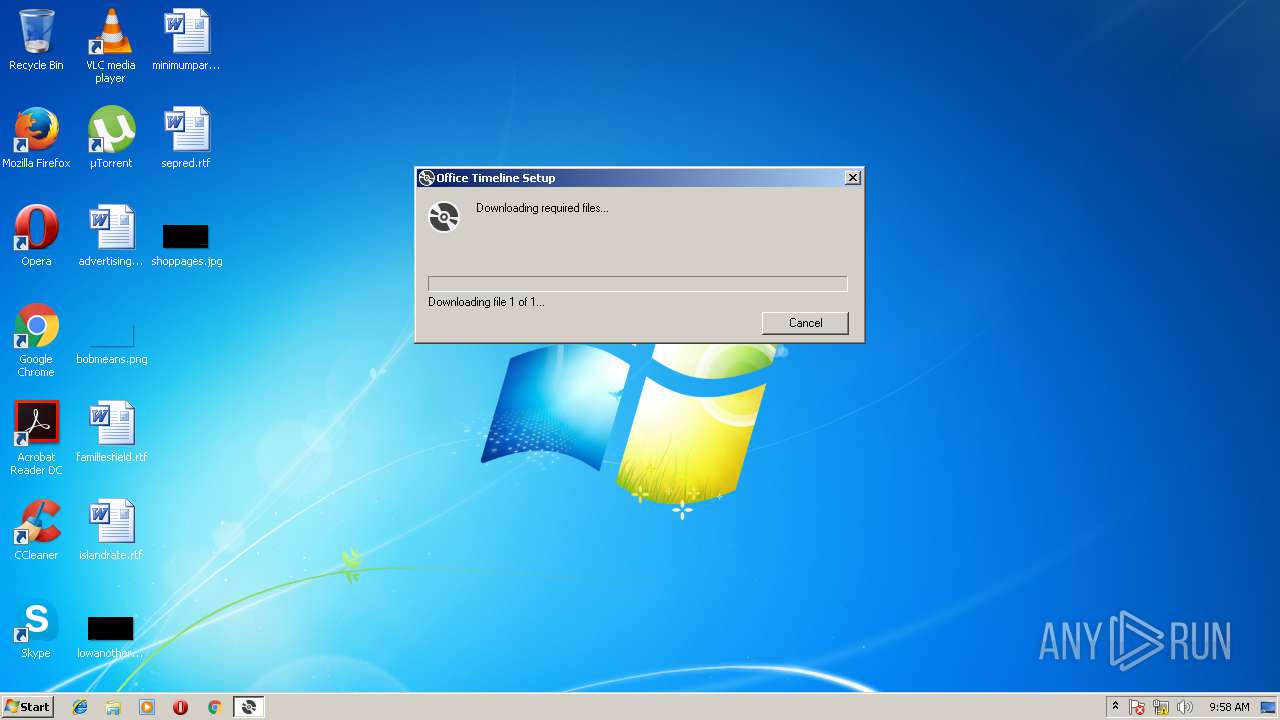
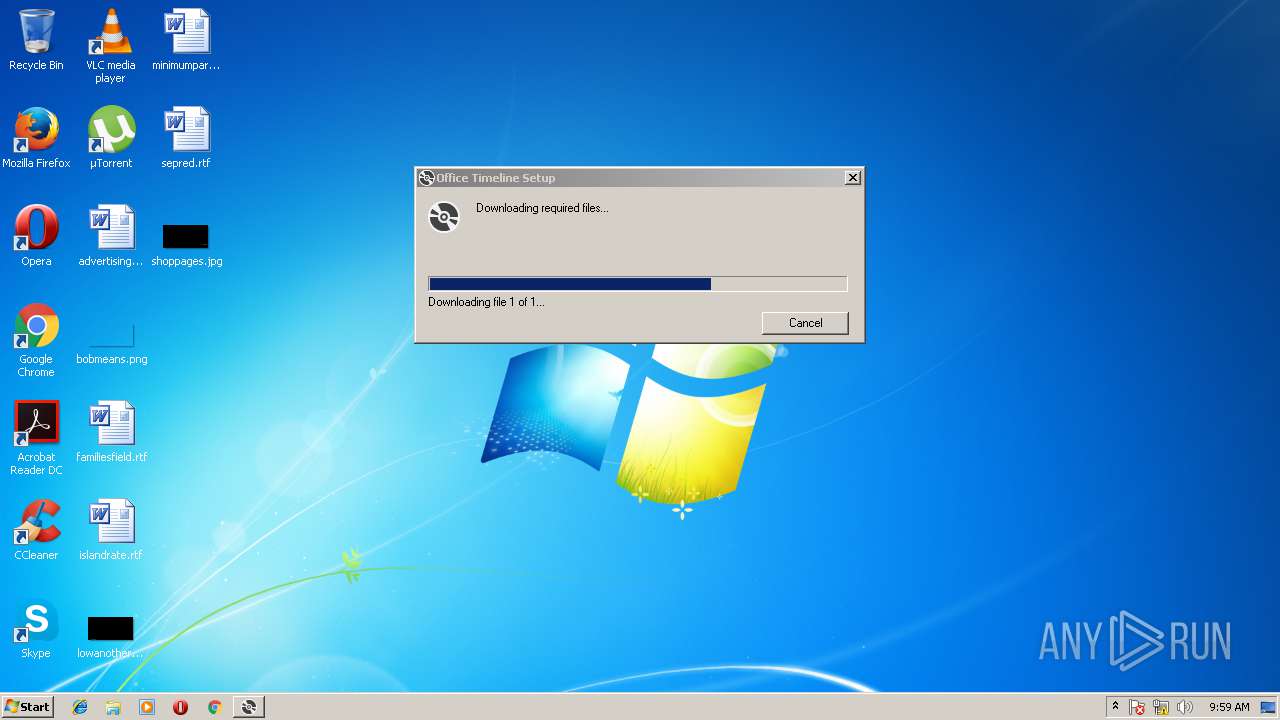
— | — | GET | — | 2.18.233.19:80 | http://download.microsoft.com/download/F/B/A/FBAB6866-71F8-4A3F-89A4-5BC6AB035C62/vstor_redist.exe | unknown | — | — | whitelisted |
— | — | GET | 302 | 104.111.246.179:80 | http://go.microsoft.com/fwlink/?LinkId=158918 | NL | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 104.111.246.179:80 | go.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.18.233.19:80 | download.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
download.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |