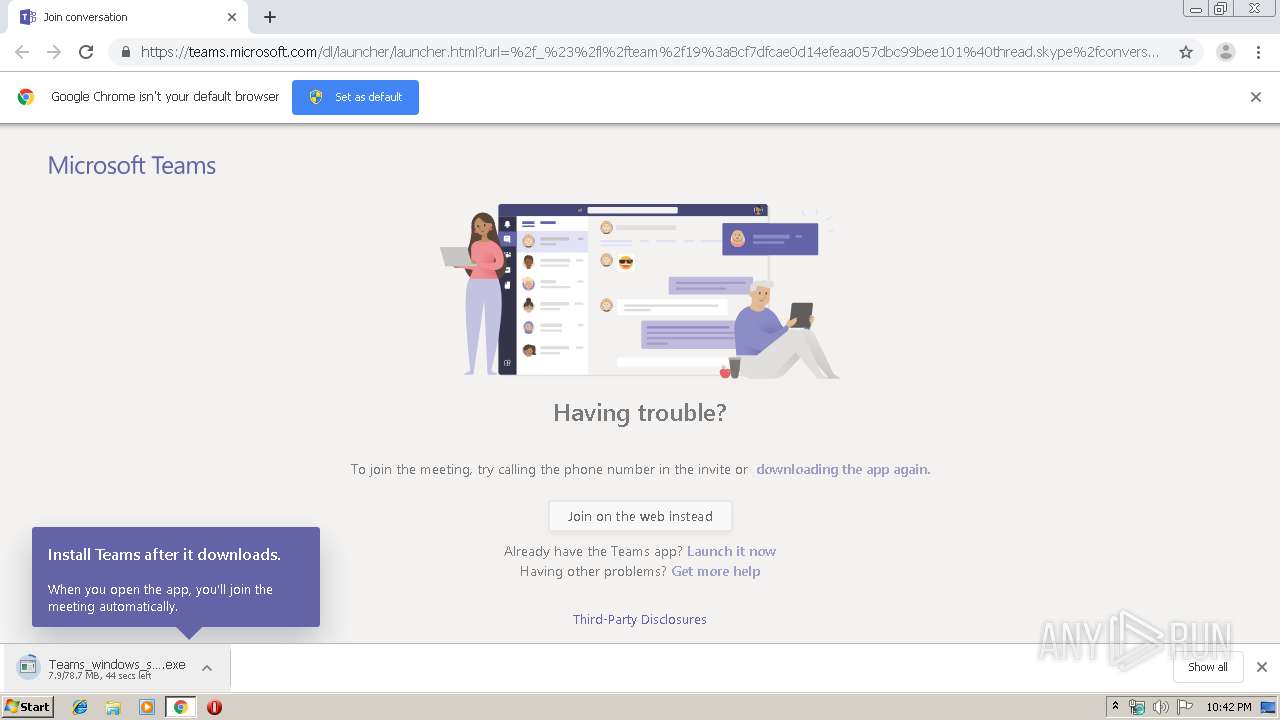
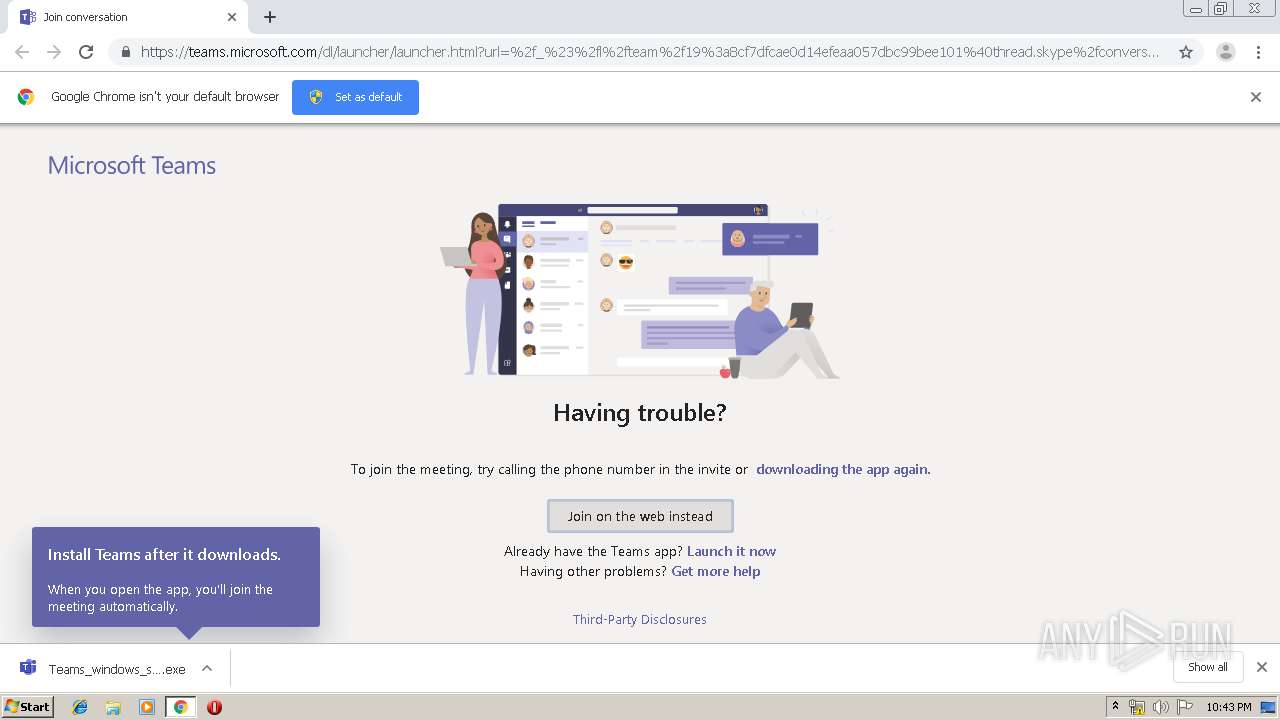
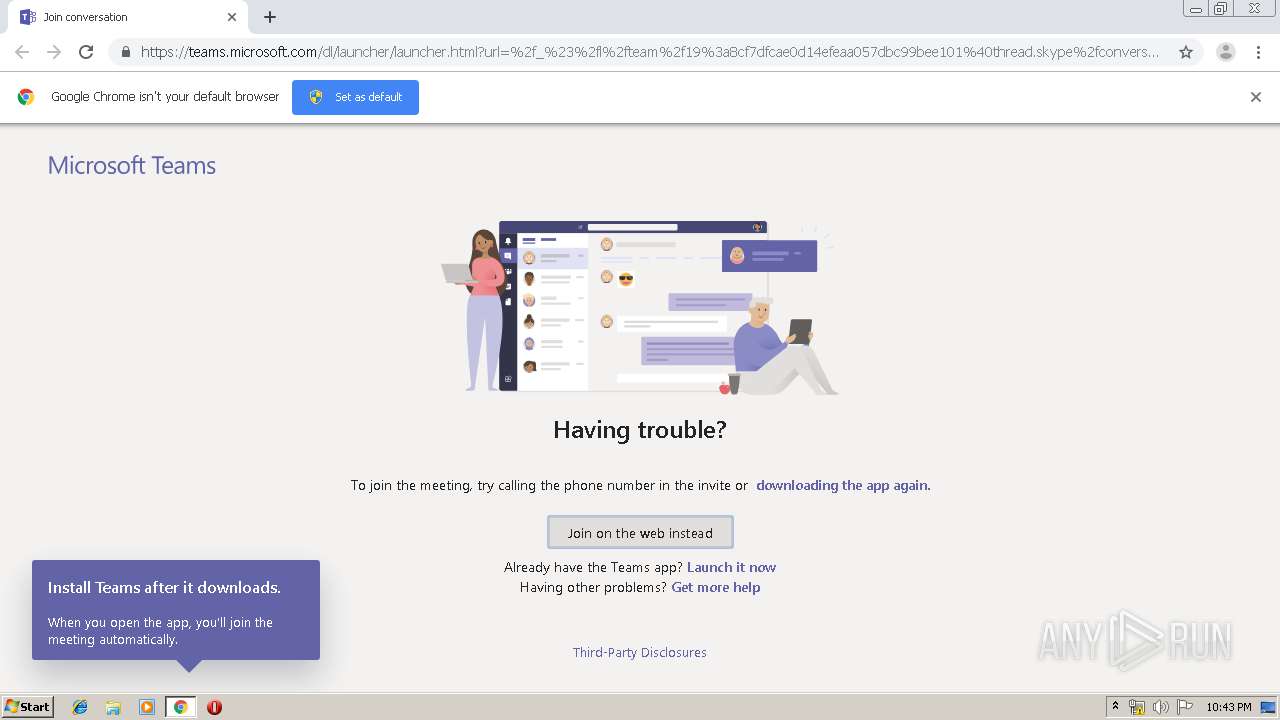
| URL: | https://teams.microsoft.com/dl/launcher/launcher.html?url=%2f_%23%2fl%2fteam%2f19%3a8cf7dfcae0d14efeaa057dbc99bee101%40thread.skype%2fconversations%3ftenantId%3d7087a6be-5e7d-49e8-9ee5-3c7ffd3f1e65&type=team&deeplinkId=ca329099-d6db-4a01-832c-2703c9453ae2&directDl=true&msLaunch=true&enableMobilePage=true&suppressPrompt=true |
| Full analysis: | https://app.any.run/tasks/18f231fd-f4a4-4c1a-b63f-41e3013b570b |
| Verdict: | Malicious activity |
| Analysis date: | September 10, 2019, 21:42:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 95231AF6639855AAF40E1830BD69ACC0 |
| SHA1: | 779D71D656ED3E505B583A723B1C9FA48550E352 |
| SHA256: | D5E73BCD9A49F0F6938785286C073CAE49B6A223F647FE08378657A22B5D6D1A |
| SSDEEP: | 6:2In+DIeG531EgCDy1DNQotzMSj6Rsxv/iPsEtnZdEbALLjd:2In+DIeY31xDNntURsN+ltZdEb8jd |
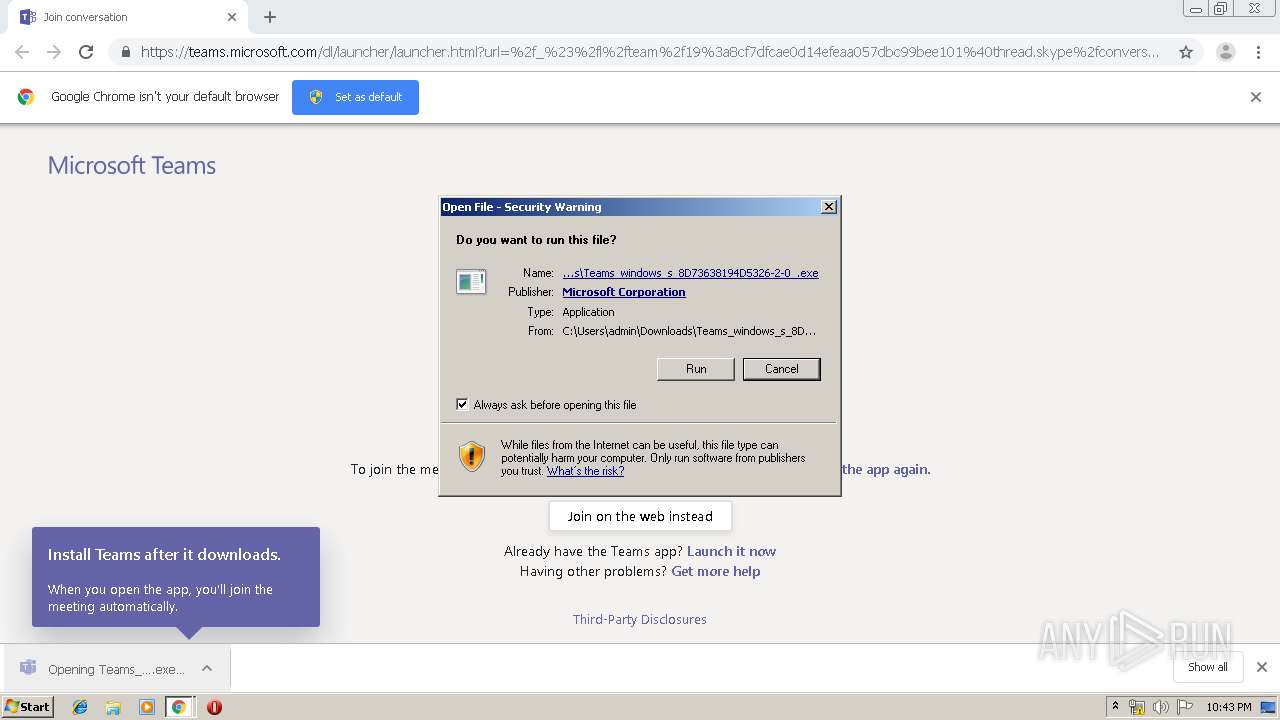
MALICIOUS
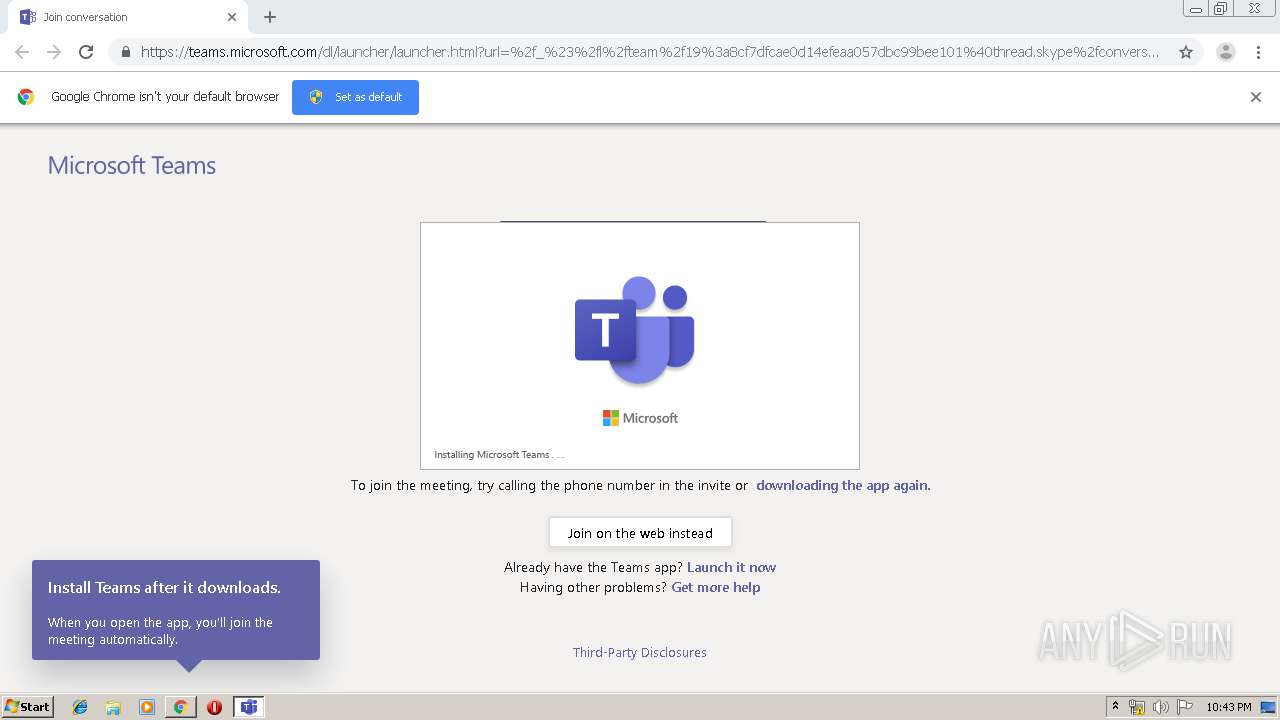
Application was dropped or rewritten from another process
- Teams_windows_s_8D73638194D5326-2-0_.exe (PID: 2932)
- update.exe (PID: 3800)
- Update.exe (PID: 3044)
- Squirrel.exe (PID: 2472)
Loads dropped or rewritten executable
- Teams.exe (PID: 1156)
- Teams.exe (PID: 1260)
- Teams.exe (PID: 3792)
- Teams.exe (PID: 2528)
- regsvr32.exe (PID: 528)
- Teams.exe (PID: 3596)
- Teams.exe (PID: 2360)
- Teams.exe (PID: 3148)
- Teams.exe (PID: 2588)
- Teams.exe (PID: 3568)
- Teams.exe (PID: 2244)
- Teams.exe (PID: 3644)
- Teams.exe (PID: 1360)
- Teams.exe (PID: 3564)
- Teams.exe (PID: 552)
- Teams.exe (PID: 3192)
- Teams.exe (PID: 4068)
- Teams.exe (PID: 2824)
- Teams.exe (PID: 3632)
- Teams.exe (PID: 2572)
- Teams.exe (PID: 1816)
- Teams.exe (PID: 3224)
- Teams.exe (PID: 3052)
- Teams.exe (PID: 3680)
- Teams.exe (PID: 1016)
Changes the autorun value in the registry
- Teams.exe (PID: 2528)
- Teams.exe (PID: 2244)
- Teams.exe (PID: 3632)
Registers / Runs the DLL via REGSVR32.EXE
- Update.exe (PID: 3044)
SUSPICIOUS
Executable content was dropped or overwritten
- Teams_windows_s_8D73638194D5326-2-0_.exe (PID: 2932)
- chrome.exe (PID: 2912)
- Squirrel.exe (PID: 2472)
- Update.exe (PID: 3044)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2912)
Creates files in the user directory
- Teams.exe (PID: 1156)
- update.exe (PID: 3800)
- Teams.exe (PID: 2528)
- Teams.exe (PID: 2244)
- Teams.exe (PID: 3632)
Application launched itself
- Teams.exe (PID: 1156)
- Teams.exe (PID: 2528)
- Teams.exe (PID: 2244)
- Teams.exe (PID: 3632)
Reads CPU info
- Teams.exe (PID: 1156)
- Teams.exe (PID: 2528)
- Teams.exe (PID: 2244)
- Teams.exe (PID: 3632)
Creates COM task schedule object
- regsvr32.exe (PID: 528)
Creates a software uninstall entry
- Update.exe (PID: 3044)
Modifies the open verb of a shell class
- Teams.exe (PID: 2528)
- Teams.exe (PID: 2244)
- Teams.exe (PID: 3632)
Reads Environment values
- Update.exe (PID: 3044)
Reads Internet Cache Settings
- Teams.exe (PID: 2244)
Reads internet explorer settings
- Teams.exe (PID: 2244)
INFO
Reads Internet Cache Settings
- chrome.exe (PID: 2912)
Application launched itself
- chrome.exe (PID: 2912)
Reads the hosts file
- chrome.exe (PID: 2392)
- chrome.exe (PID: 2912)
- Teams.exe (PID: 1156)
- Teams.exe (PID: 2528)
- Teams.exe (PID: 2244)
- Teams.exe (PID: 3632)
Reads settings of System Certificates
- chrome.exe (PID: 2392)
- Update.exe (PID: 3044)
- Teams.exe (PID: 2528)
- Teams.exe (PID: 2244)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
84
Monitored processes
50
Malicious processes
28
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 528 | "C:\Windows\system32\regsvr32.exe" /s /n /i:user "C:\Users\admin\AppData\Local\Microsoft\TeamsMeetingAddin\1.0.19178.2\x86\Microsoft.Teams.AddinLoader.dll" | C:\Windows\system32\regsvr32.exe | — | Update.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 552 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=renderer --autoplay-policy=no-user-gesture-required --enable-features=FixAltGraph --service-pipe-token=0F017A53887CE7CF58B37DA1B11DF677 --lang=en-US --app-user-model-id=com.squirrel.Teams.Teams --app-path="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar" --node-integration=false --webview-tag=false --no-sandbox --preload="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar\lib\renderer\notifications\preload_notifications.js" --background-color=#fff --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --enable-compositor-image-animations --service-request-channel-token=0F017A53887CE7CF58B37DA1B11DF677 --renderer-client-id=9 --mojo-platform-channel-handle=2008 /prefetch:1 --msteams-process-type=notificationsManager | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.2.00.22654 Modules
| |||||||||||||||
| 1016 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=renderer --autoplay-policy=no-user-gesture-required --enable-features=FixAltGraph --service-pipe-token=D656954A742913B59728A16078E6CB86 --lang=en-US --app-user-model-id=com.squirrel.Teams.Teams --app-path="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar" --node-integration=false --webview-tag=false --enable-sandbox --preload="C:\Users\admin\AppData\Local\Microsoft\Teams\current\resources\app.asar\lib\renderer\preload_default_sandbox.js" --background-color=#fff --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --enable-compositor-image-animations --service-request-channel-token=D656954A742913B59728A16078E6CB86 --renderer-client-id=11 --mojo-platform-channel-handle=1452 /prefetch:1 --msteams-process-type=upnWindow | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Teams Exit code: 0 Version: 1.2.00.22654 Modules
| |||||||||||||||
| 1156 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --squirrel-install 1.2.00.22654 | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | Update.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.2.00.22654 Modules
| |||||||||||||||
| 1216 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,15063037570338234419,11209023755964087141,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=1530379318811630506 --mojo-platform-channel-handle=3176 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1260 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=gpu-process --enable-features=FixAltGraph --no-sandbox --gpu-preferences=KAAAAAAAAACAAwCAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=780C2F5384A9E7576E9473CF8898D5E0 --mojo-platform-channel-handle=1240 /prefetch:2 | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 4 Version: 1.2.00.22654 Modules
| |||||||||||||||
| 1360 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=gpu-process --enable-features=FixAltGraph --gpu-preferences=KAAAAAAAAACAAwCAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=B2E5091204B079F0D6283C90FE9D023C --mojo-platform-channel-handle=1240 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Teams Exit code: 4 Version: 1.2.00.22654 Modules
| |||||||||||||||
| 1816 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" --type=gpu-process --enable-features=FixAltGraph --gpu-preferences=KAAAAAAAAACAAwCAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=88FEF2478BBB18802E2504BAE57AB471 --mojo-platform-channel-handle=1240 --ignored=" --type=renderer " /prefetch:2 | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | — | Teams.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Teams Exit code: 4 Version: 1.2.00.22654 Modules
| |||||||||||||||
| 2192 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,15063037570338234419,11209023755964087141,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3960847473709533248 --mojo-platform-channel-handle=3412 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2244 | "C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe" | C:\Users\admin\AppData\Local\Microsoft\Teams\current\Teams.exe | Teams.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Teams Exit code: 0 Version: 1.2.00.22654 Modules
| |||||||||||||||
Total events
3 485
Read events
3 257
Write events
223
Delete events
5
Modification events
| (PID) Process: | (2800) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2912-13212625335751375 |
Value: 259 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2912) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
365
Suspicious files
51
Text files
410
Unknown types
69
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\9530801e-9390-44f2-ba8c-3fc9a7df4cdb.tmp | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF168ed7.TMP | text | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2912 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
54
DNS requests
33
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2392 | chrome.exe | GET | 302 | 172.217.22.78:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
2392 | chrome.exe | GET | 200 | 172.217.132.102:80 | http://r1---sn-5hne6nsy.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.104.186.93&mm=28&mn=sn-5hne6nsy&ms=nvh&mt=1568151682&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2392 | chrome.exe | 104.109.67.58:443 | secure.skypeassets.com | Akamai International B.V. | NL | whitelisted |
2392 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2392 | chrome.exe | 152.199.19.160:443 | az725175.vo.msecnd.net | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2392 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2392 | chrome.exe | 52.114.158.91:443 | browser.pipe.aria.microsoft.com | Microsoft Corporation | US | unknown |
2392 | chrome.exe | 52.113.194.131:443 | teams.microsoft.com | Microsoft Corporation | US | whitelisted |
2392 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
2392 | chrome.exe | 40.77.226.250:443 | web.vortex.data.microsoft.com | Microsoft Corporation | IE | whitelisted |
2392 | chrome.exe | 52.142.114.2:443 | c1.microsoft.com | Microsoft Corporation | IE | whitelisted |
2392 | chrome.exe | 204.79.197.200:443 | c.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
teams.microsoft.com |
| whitelisted |
accounts.google.com |
| shared |
statics.teams.microsoft.com |
| whitelisted |
secure.skypeassets.com |
| whitelisted |
az725175.vo.msecnd.net |
| whitelisted |
browser.pipe.aria.microsoft.com |
| whitelisted |
web.vortex.data.microsoft.com |
| whitelisted |
c1.microsoft.com |
| whitelisted |
c.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
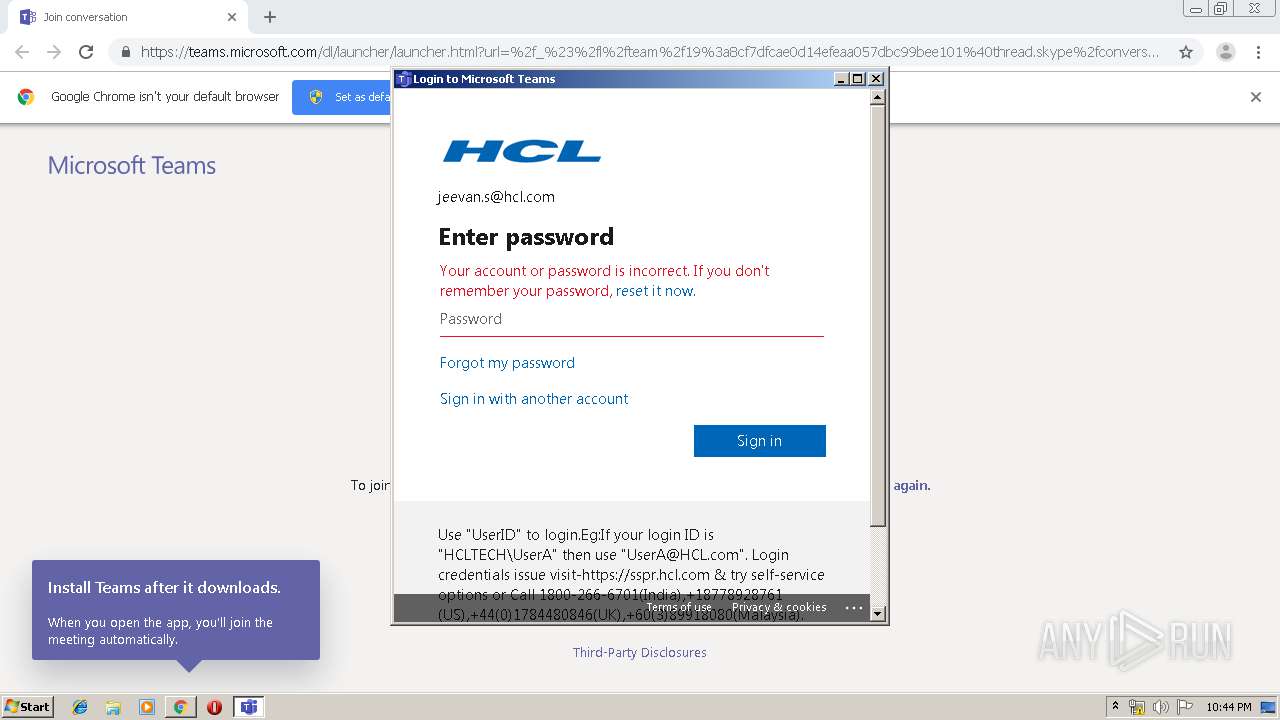
Teams.exe | [native-utils/CrashHandler] starting with UseWERFlagAndErrorMode
|
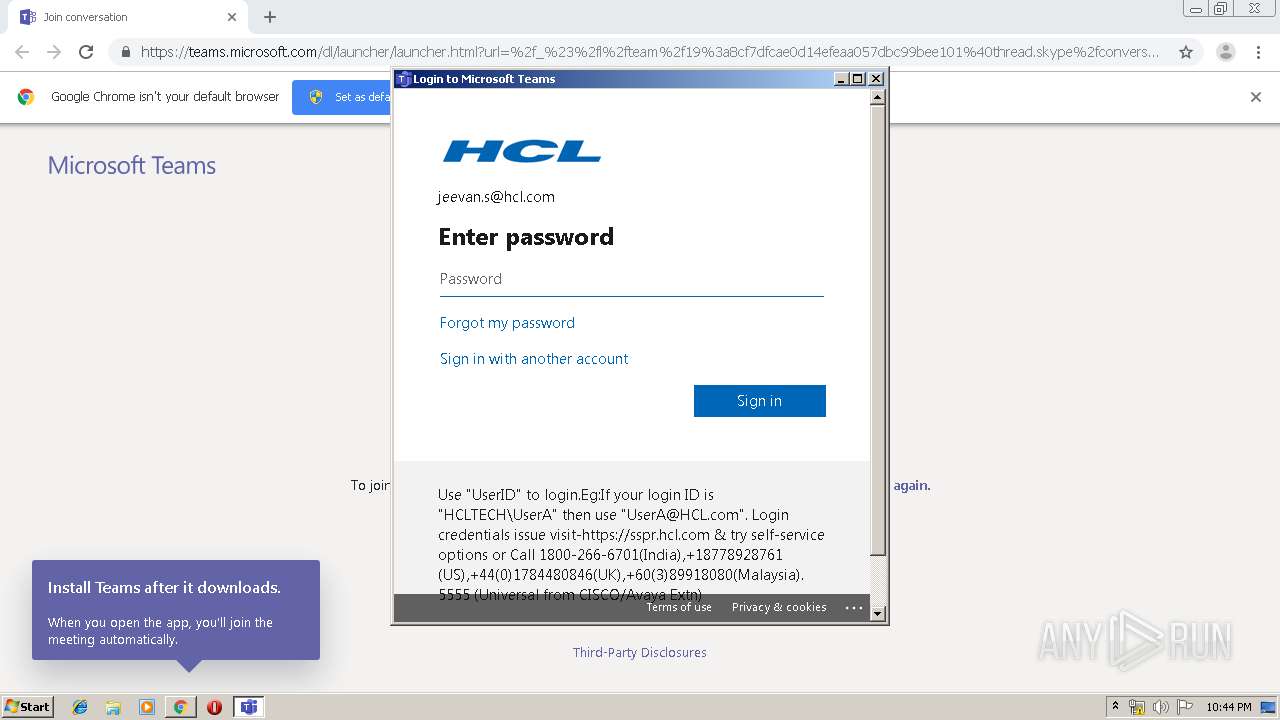
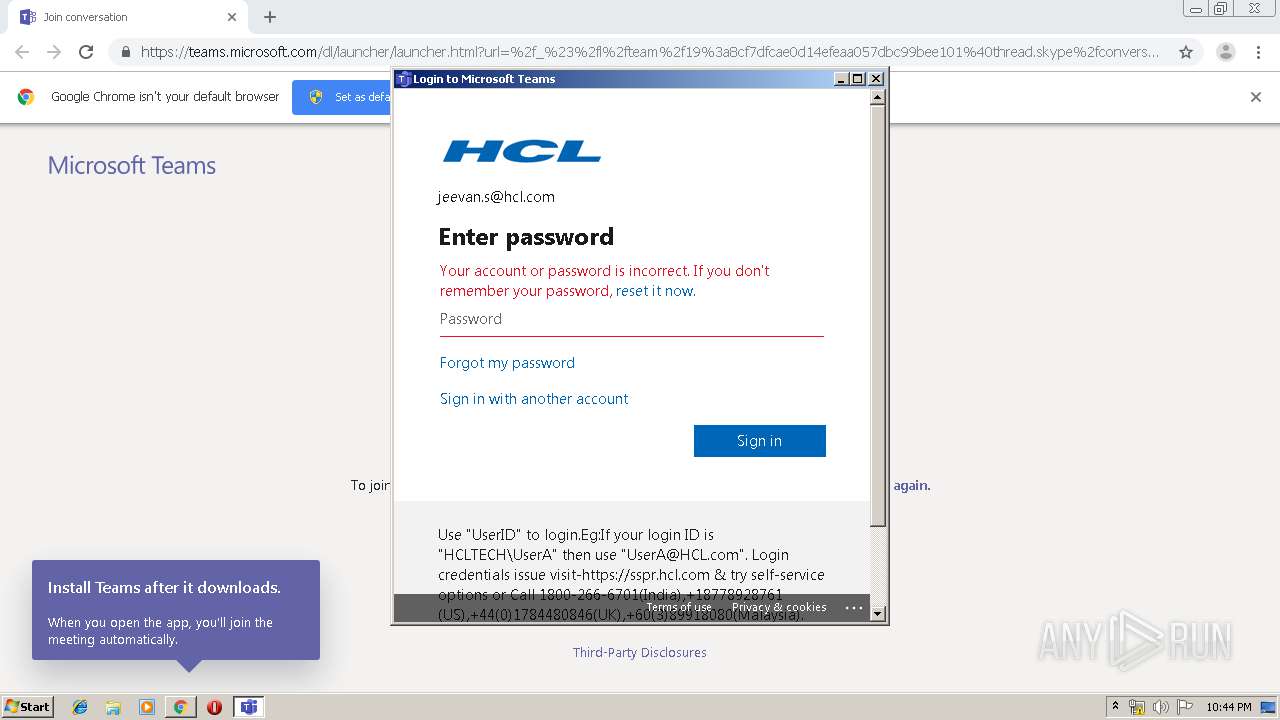
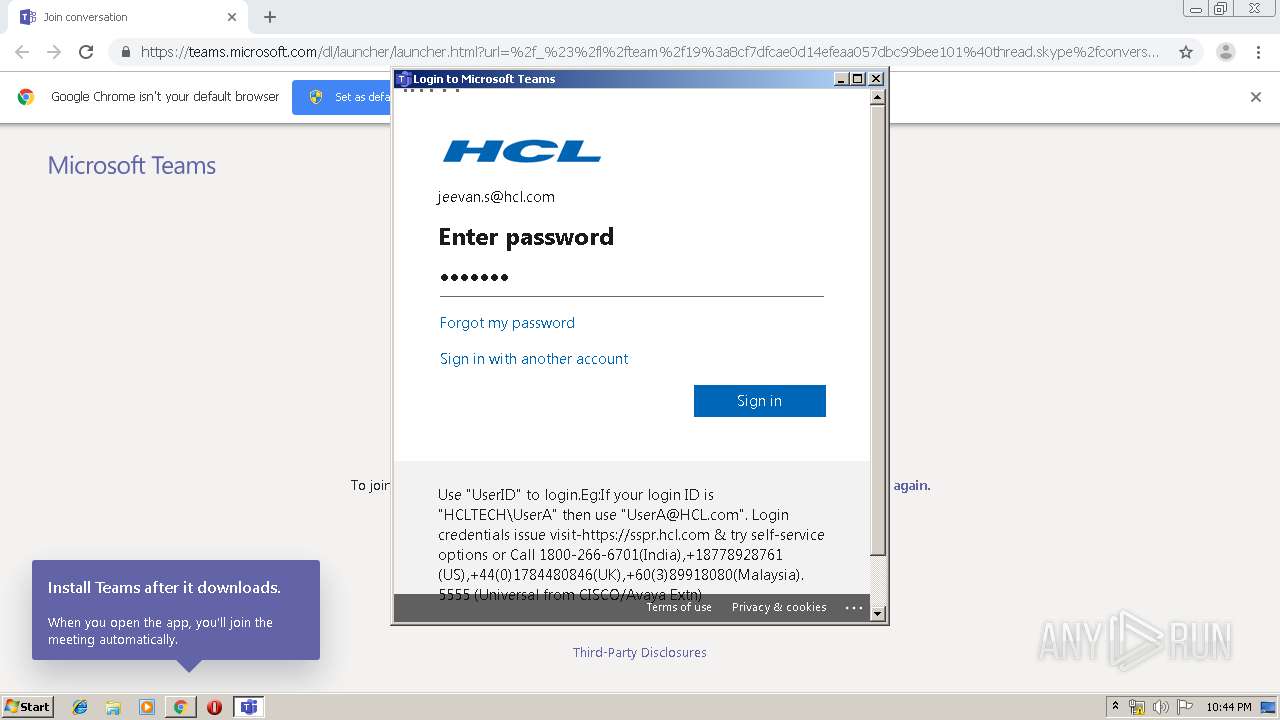
Teams.exe | AuthenticationContext created |
Teams.exe | AuthenticationRequest created |
Teams.exe | AuthenticationRequest created |
Teams.exe | AuthenticationRequest created |
Teams.exe | AuthenticationRequest destroyed |
Teams.exe | [native-utils/CrashHandler] starting with UseWERFlagAndErrorMode
|