| File name: | main.exe |
| Full analysis: | https://app.any.run/tasks/6d390634-be12-4768-ab17-985d06346121 |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 00:42:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 708A6BE79EB60B18782349F7C1E15E78 |
| SHA1: | A159824DF5EE8F99A88CB303D6A0F9F481BBAE8A |
| SHA256: | D5D229B8D48376274D856A905181E2BEAACCB4D3D394BF91760AD31B769BE5F4 |
| SSDEEP: | 196608:p5ooP1HSsimvlG2etbYPvbJQlHJCrFTvN8CNy1q:7P1pimtokJQlp4FTnb |
MALICIOUS
Drops executable file immediately after starts
- main.exe (PID: 3148)
Loads dropped or rewritten executable
- main.exe (PID: 1068)
SUSPICIOUS
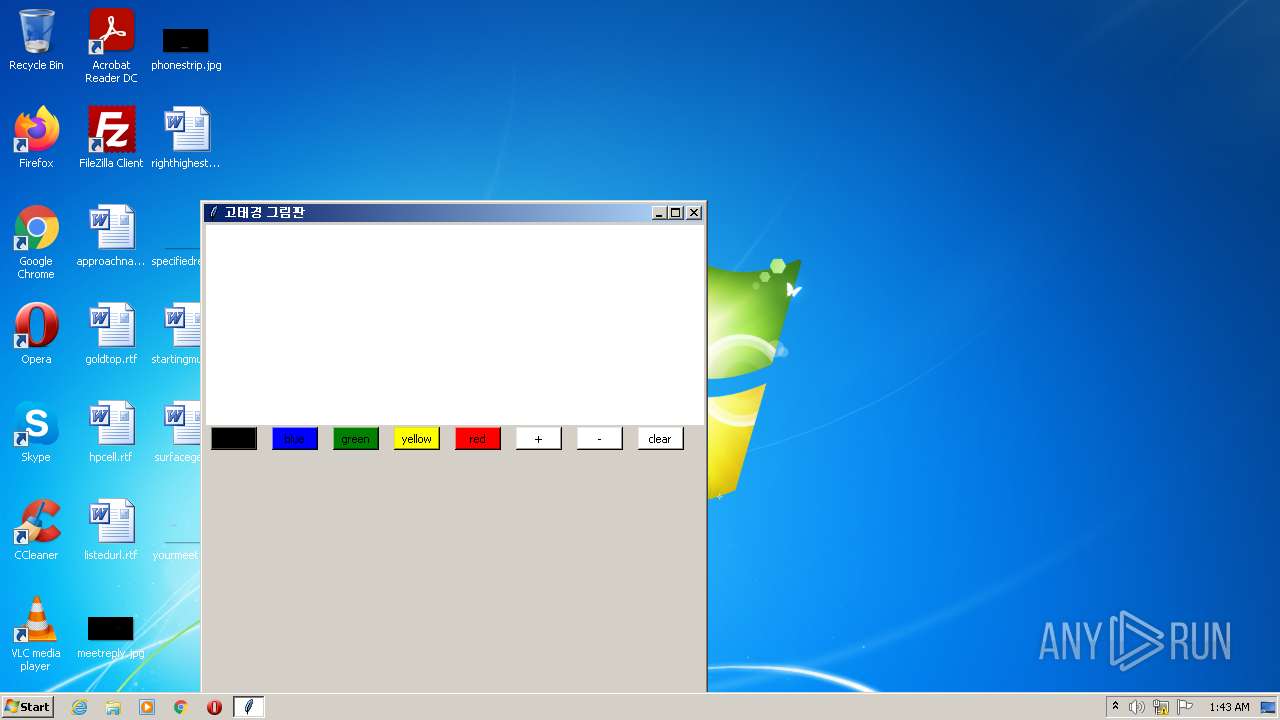
Checks supported languages
- main.exe (PID: 3148)
- main.exe (PID: 1068)
Reads the computer name
- main.exe (PID: 3148)
Application launched itself
- main.exe (PID: 3148)
Drops a file with a compile date too recent
- main.exe (PID: 3148)
Executable content was dropped or overwritten
- main.exe (PID: 3148)
Loads Python modules
- main.exe (PID: 1068)
INFO
Dropped object may contain Bitcoin addresses
- main.exe (PID: 3148)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0xa260 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 128000 |
| CodeSize: | 151040 |
| LinkerVersion: | 14.29 |
| PEType: | PE32 |
| TimeStamp: | 2022:05:07 04:06:39+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-May-2022 02:06:39 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 07-May-2022 02:06:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00024CD5 | 0x00024E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.65252 |
.rdata | 0x00026000 | 0x0000D134 | 0x0000D200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.01457 |
.data | 0x00034000 | 0x0000F8DC | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.89567 |
.rsrc | 0x00044000 | 0x0000F494 | 0x0000F600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.55554 |
.reloc | 0x00054000 | 0x00001E0C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.50108 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
0 | 2.71858 | 104 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
1 | 5.28693 | 1415 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 6.44895 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 5.77742 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 7.95095 | 38188 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 6.0521 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 6.15081 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 6.39466 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
34
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1068 | "C:\Users\admin\AppData\Local\Temp\main.exe" | C:\Users\admin\AppData\Local\Temp\main.exe | — | main.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3148 | "C:\Users\admin\AppData\Local\Temp\main.exe" | C:\Users\admin\AppData\Local\Temp\main.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
160
Read events
160
Write events
0
Delete events
0
Modification events
Executable files
22
Suspicious files
1
Text files
915
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3148 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI31482\VCRUNTIME140.dll | executable | |
MD5:2EBF45DA71BD8EF910A7ECE7E4647173 | SHA256:CF39E1E81F57F42F4D60ABC1D30ECF7D773E576157AA88BBC1D672BF5AD9BB8B | |||
| 3148 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI31482\_lzma.pyd | executable | |
MD5:38C434AFB2A885A95999903977DC3624 | SHA256:BFE6E288B2D93905F5CBB6D74E9C0FC37145B9225DB6D1F00C0F69EB45AFD051 | |||
| 3148 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI31482\_asyncio.pyd | executable | |
MD5:A2FFF5C11F404D795E7D2B4907ED4485 | SHA256:ED7830D504D726CE42B3B7A1321F39C8E29D1EBAD7B64632E45B712F0C47E189 | |||
| 3148 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI31482\_overlapped.pyd | executable | |
MD5:09716BCE87ED2BF7E5A1F19952305E5C | SHA256:F4A27F4E242D788FCB1F5DD873608C72CDFC0799358364420ECEA1A7E52CC2B0 | |||
| 3148 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI31482\_ctypes.pyd | executable | |
MD5:C827A20FC5F1F4E0EF9431F29EBF03B4 | SHA256:D500CFF28678ECED1FC4B3AEABECC0F3B30DE735FDEFE90855536BC29FC2CB4D | |||
| 3148 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI31482\_hashlib.pyd | executable | |
MD5:F9799B167C3E4FFEE4629B4A4E2606F2 | SHA256:02DD924D4EBFBB8B5B0B66B6E6BB2388FCCDAD64D0493854A5443018AD5D1543 | |||
| 3148 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI31482\_socket.pyd | executable | |
MD5:6B59705D8AC80437DD81260443912532 | SHA256:62ED631A6AD09E96B4B6F4566C2AFC710B3493795EDEE4CC14A9C9DE88230648 | |||
| 3148 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI31482\pyexpat.pyd | executable | |
MD5:D2A2D11003EC60899823733BC3A4A0B1 | SHA256:91E096B1ECE79CB4FCD76F0F430A810712235CA9603443B378CA6BE03218500D | |||
| 3148 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI31482\_multiprocessing.pyd | executable | |
MD5:7D3306BA4645463CB0D4C34C77B2BDF2 | SHA256:3A183E0F6A31507C3B0ACBCAE5D6C3D843C590BB370DE5382E2DF9CFC2CB156E | |||
| 3148 | main.exe | C:\Users\admin\AppData\Local\Temp\_MEI31482\libffi-7.dll | executable | |
MD5:BC20614744EBF4C2B8ACD28D1FE54174 | SHA256:0C7EC6DE19C246A23756B8550E6178AC2394B1093E96D0F43789124149486F57 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report