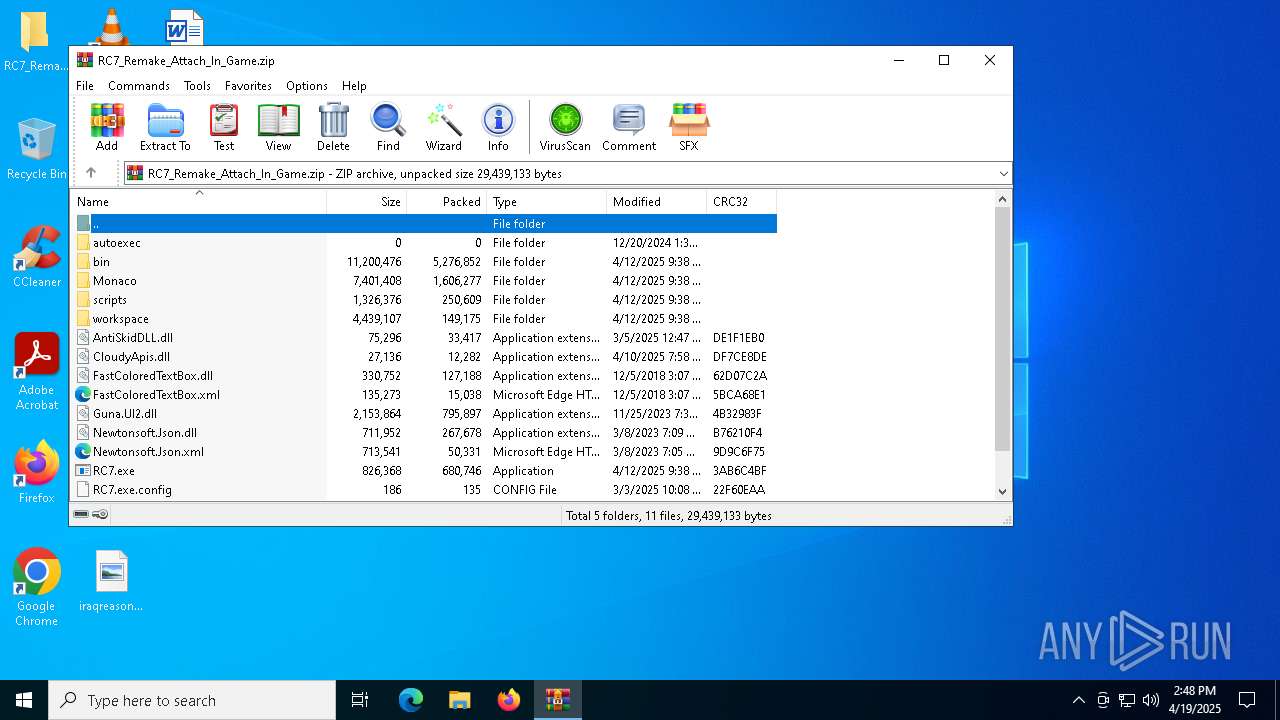
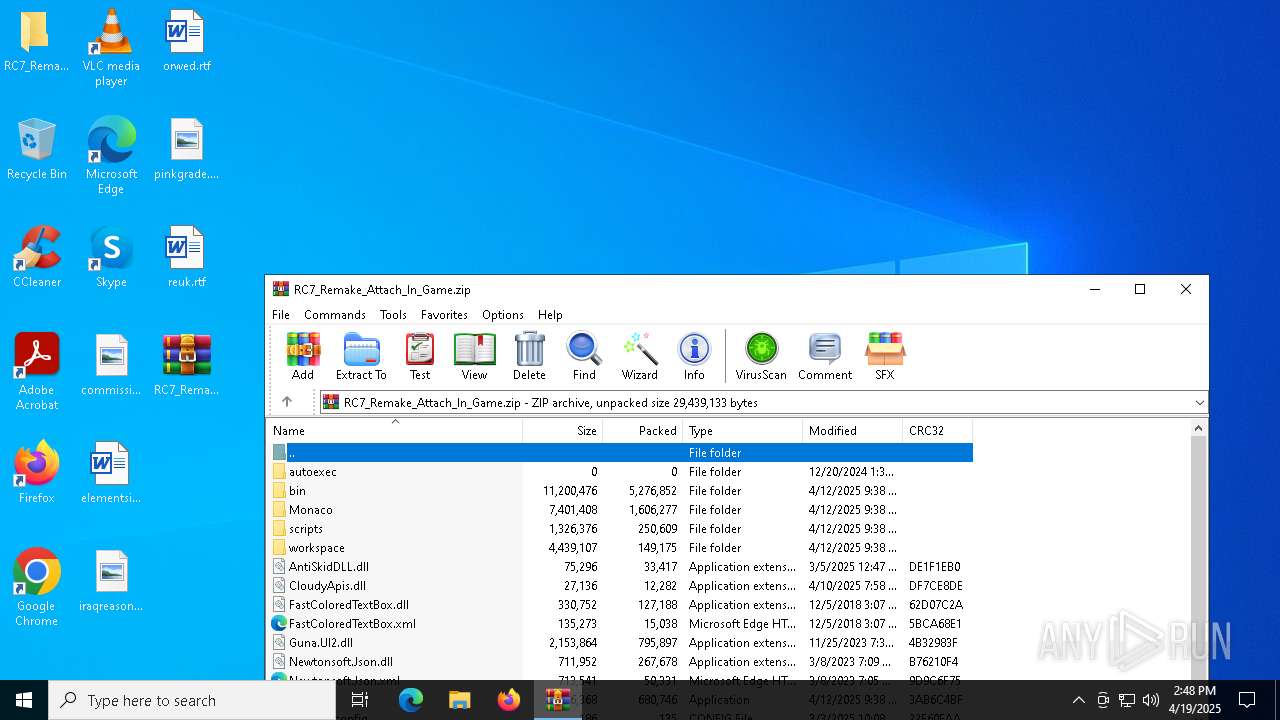
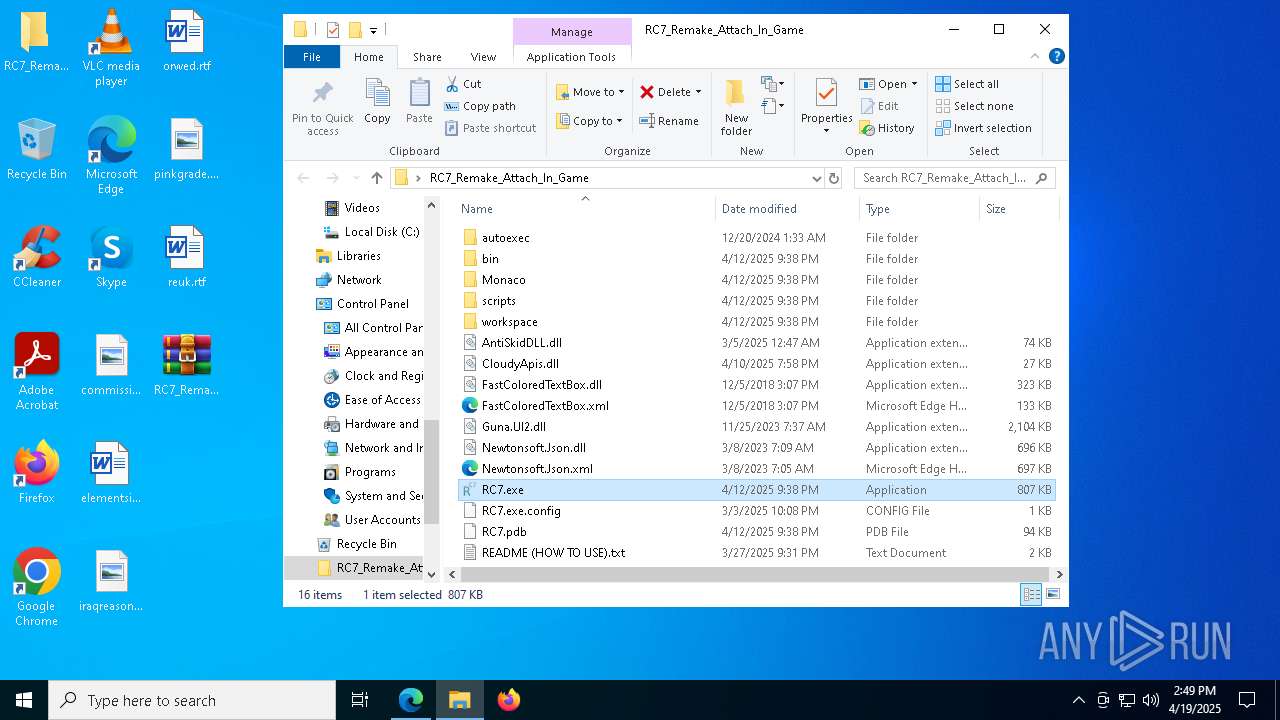
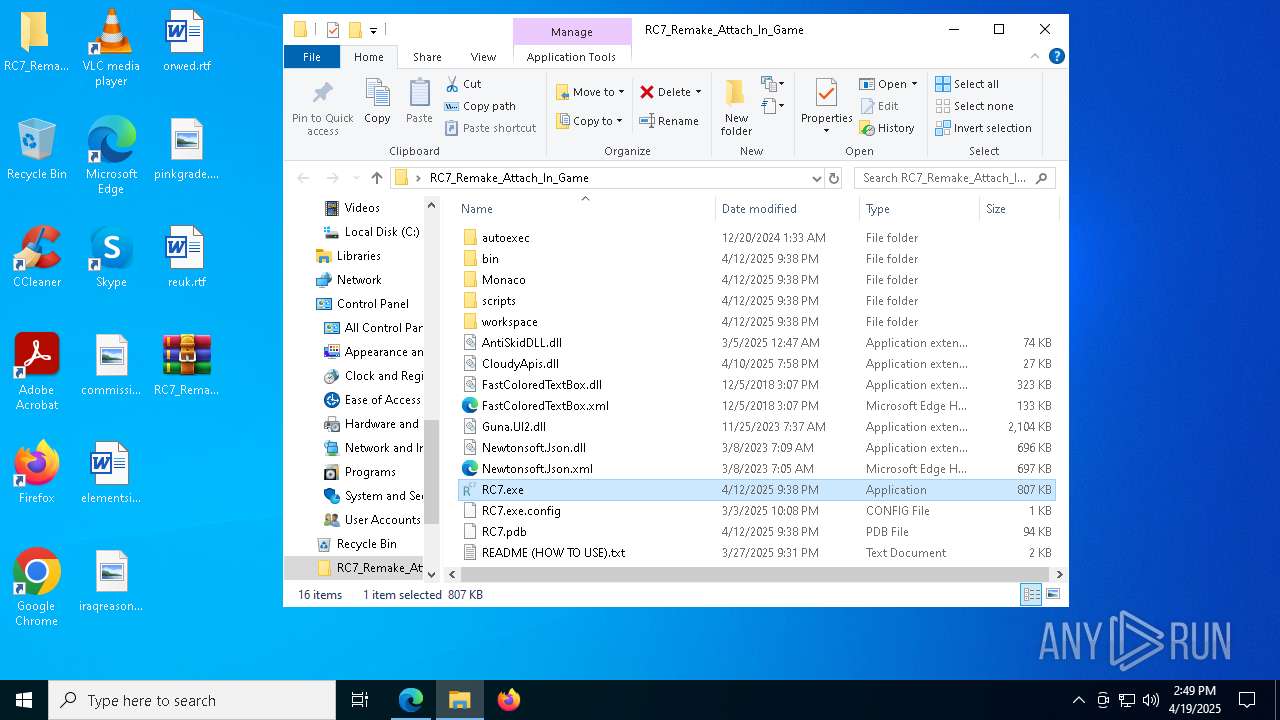
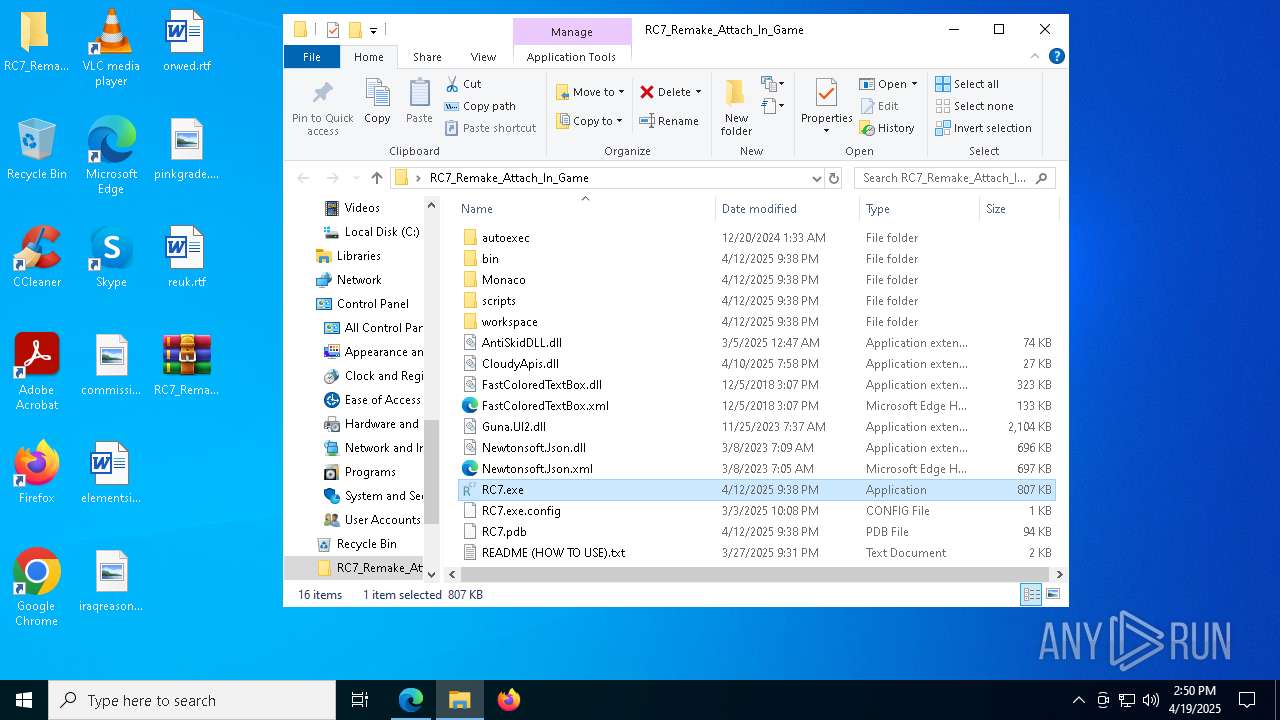
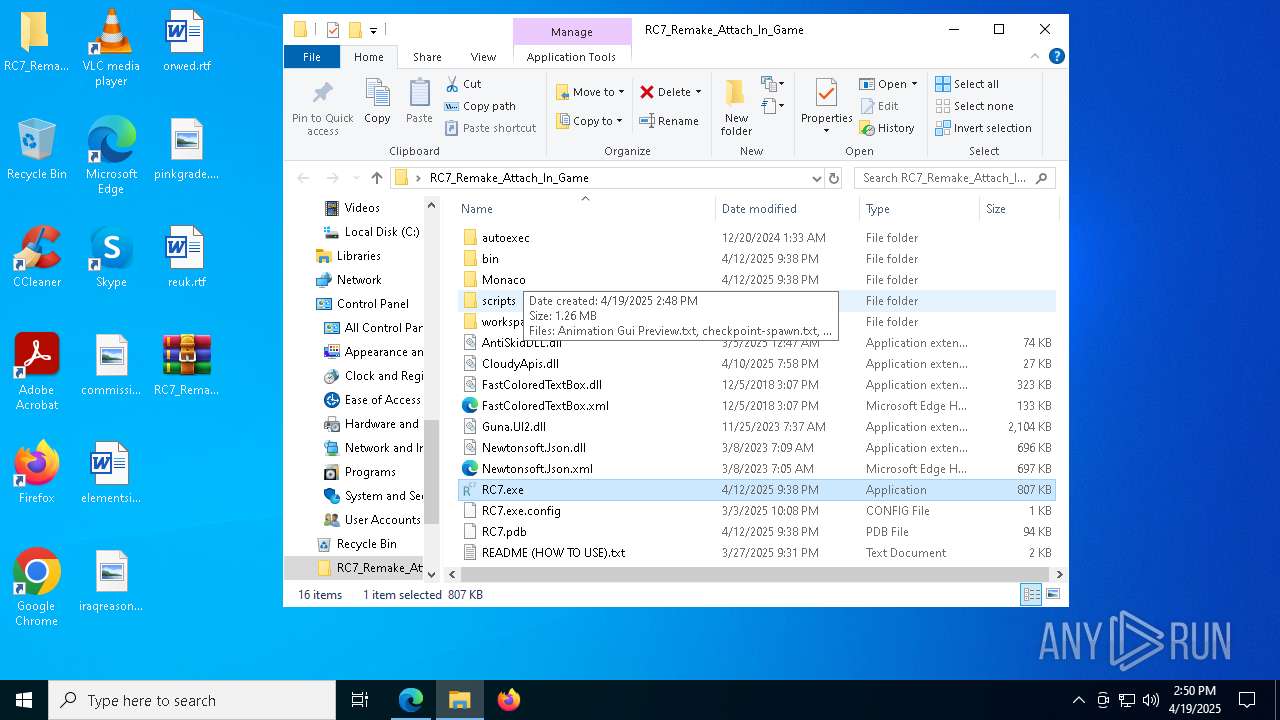
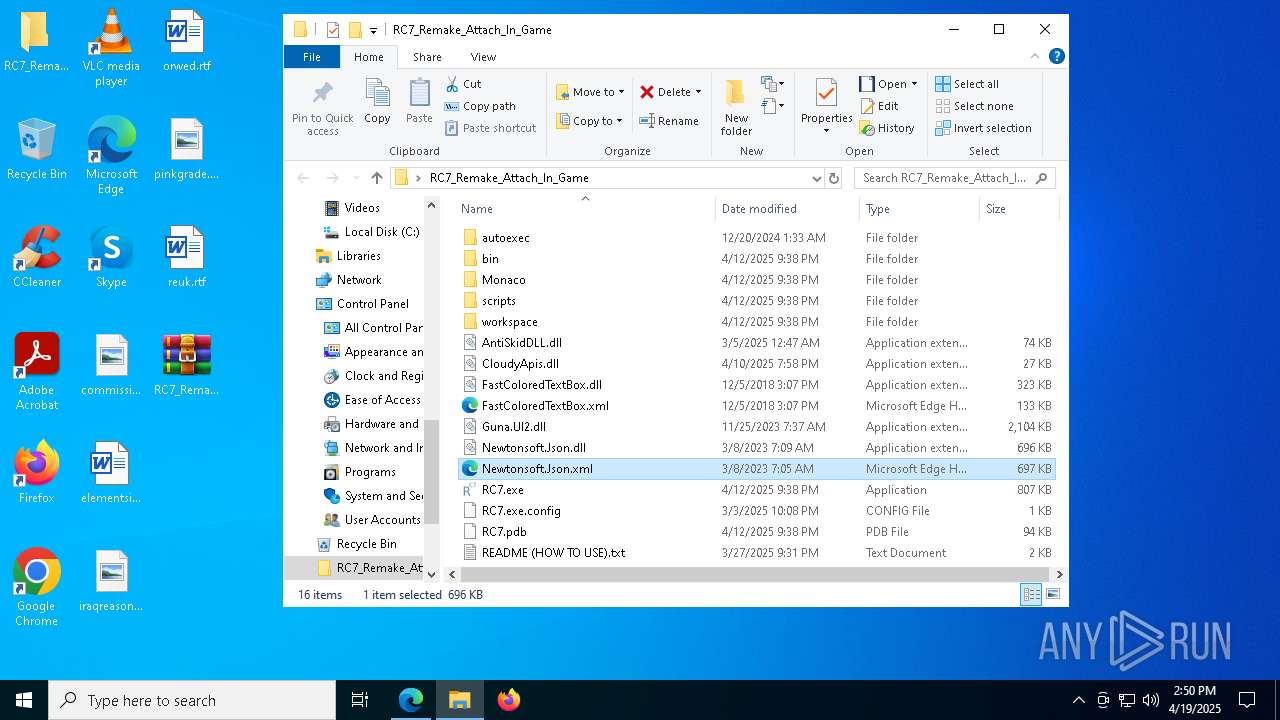
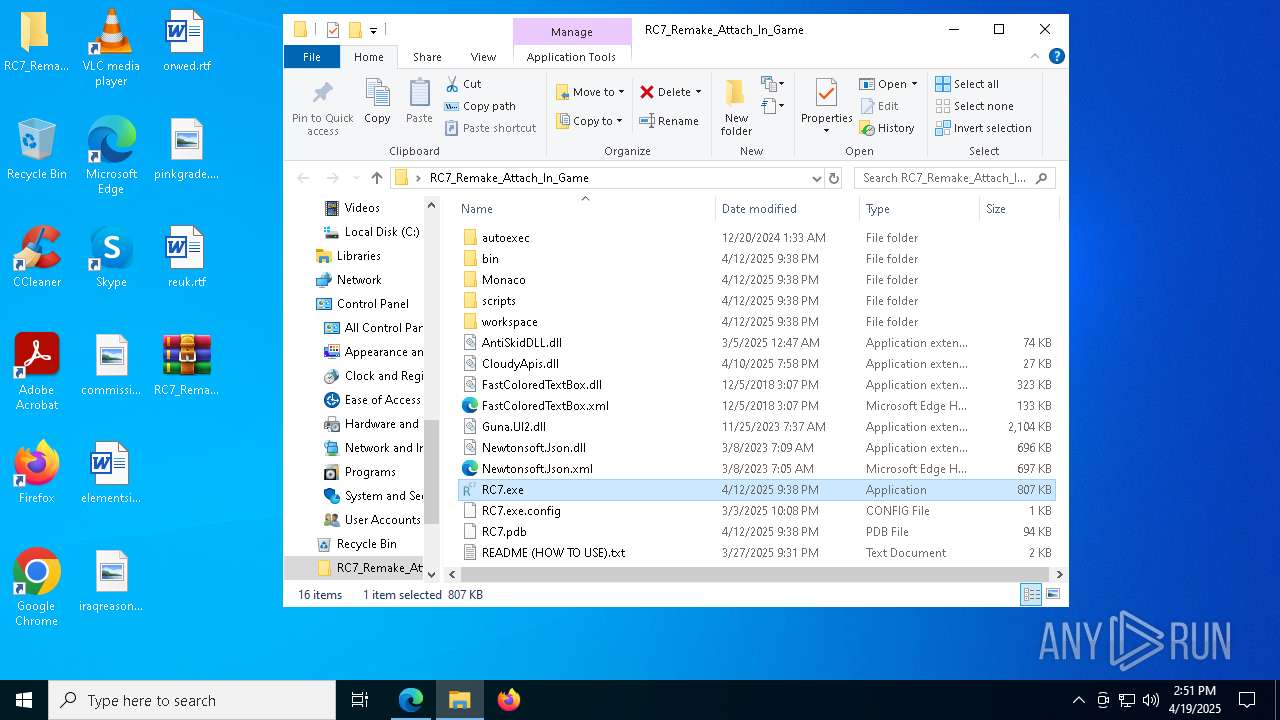
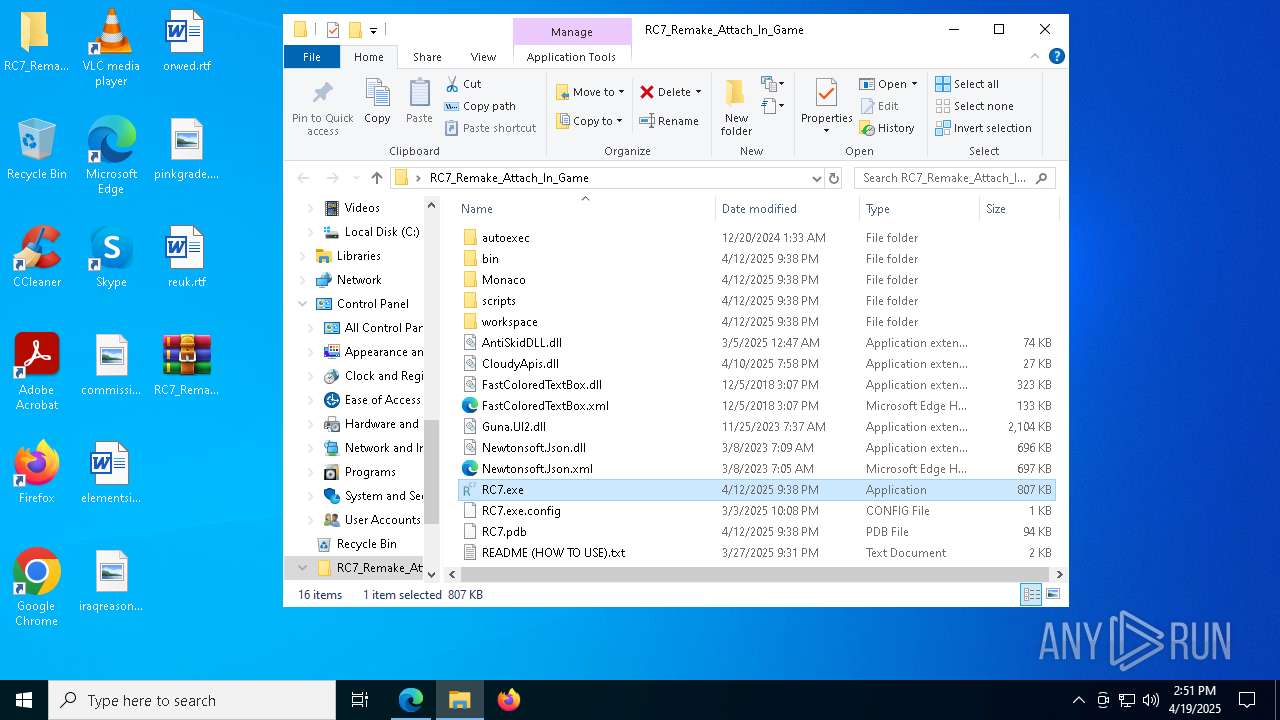
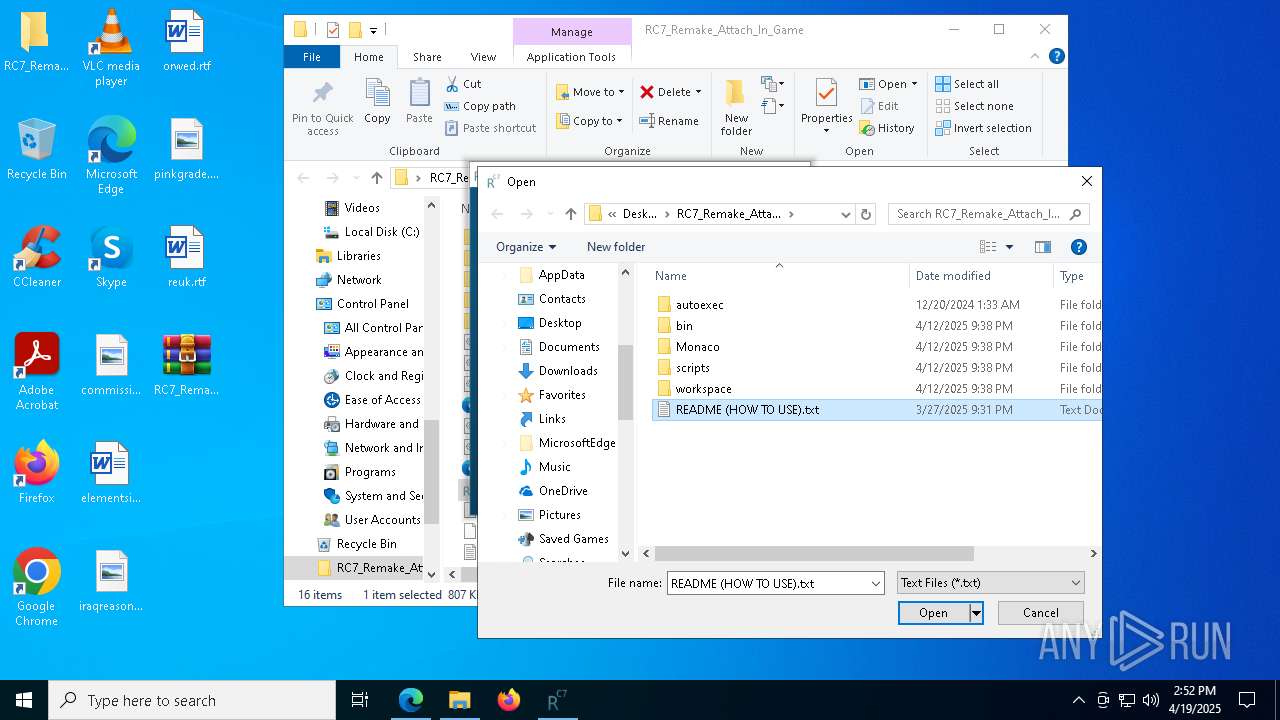
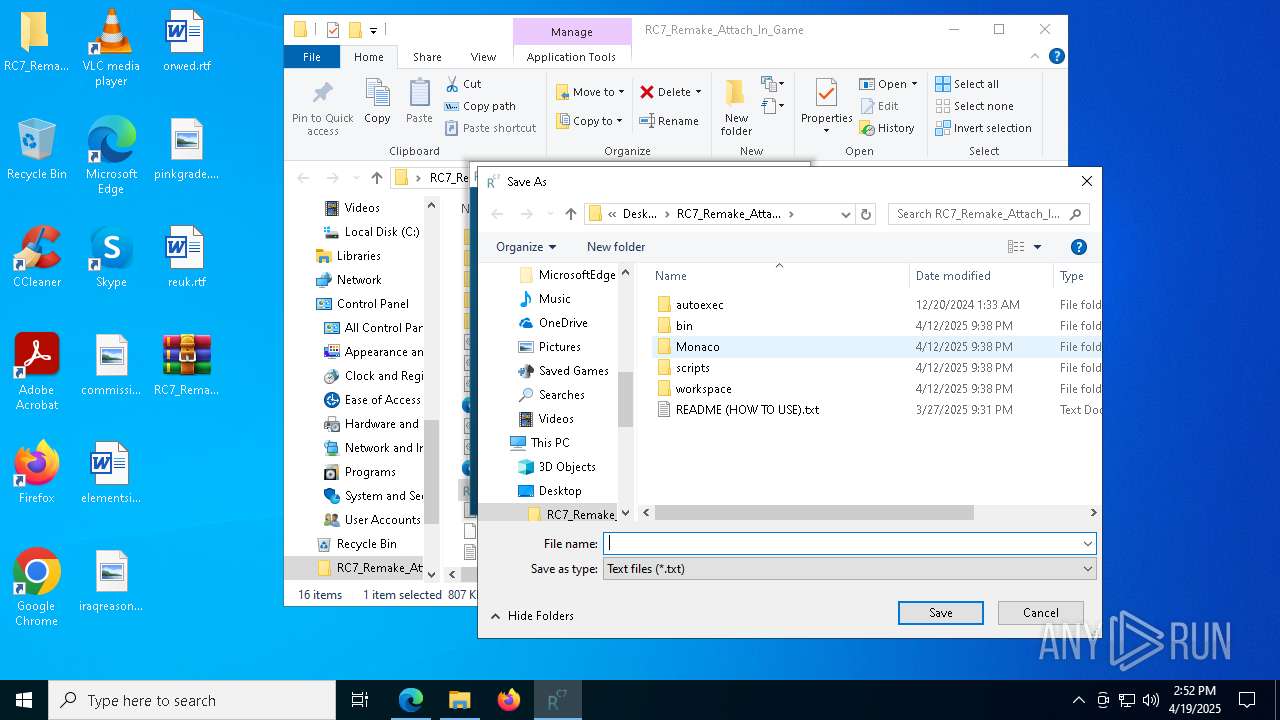
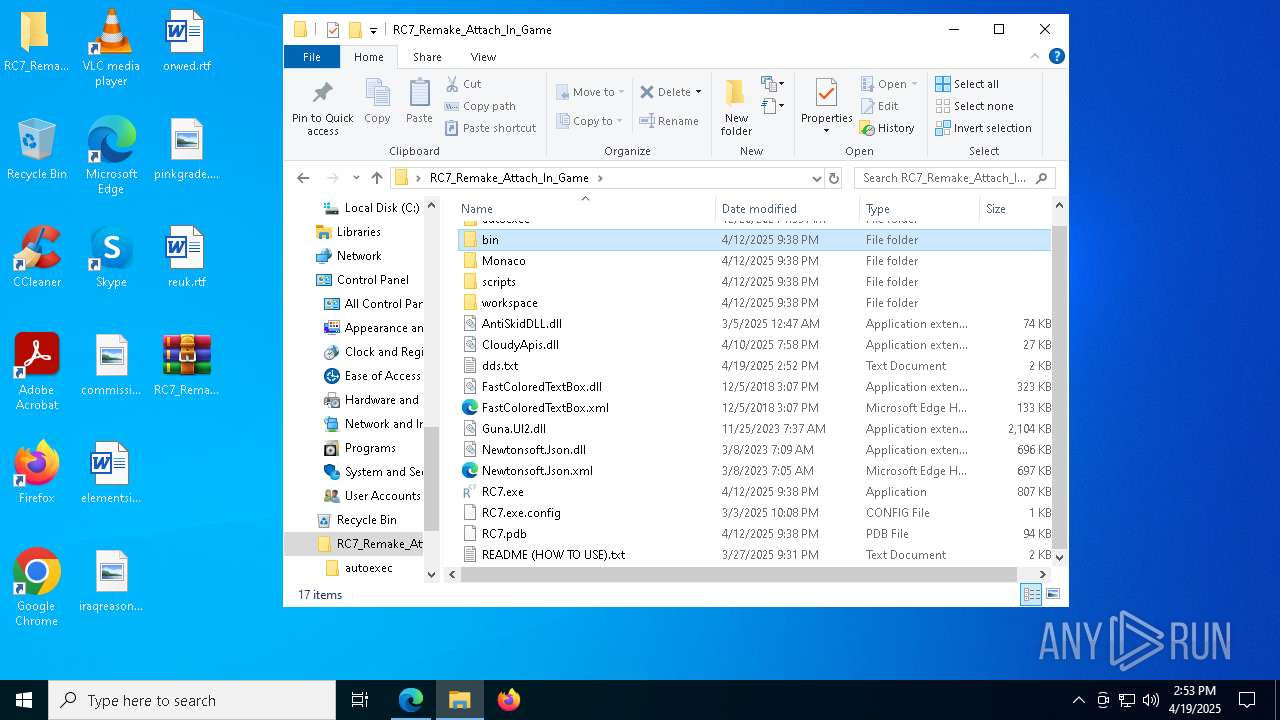
| download: | /attachments/1356708260408983602/1363160949498056774/RC7_Remake_Attach_In_Game.zip |
| Full analysis: | https://app.any.run/tasks/6a483f77-8968-4837-8119-c2f8283f3c65 |
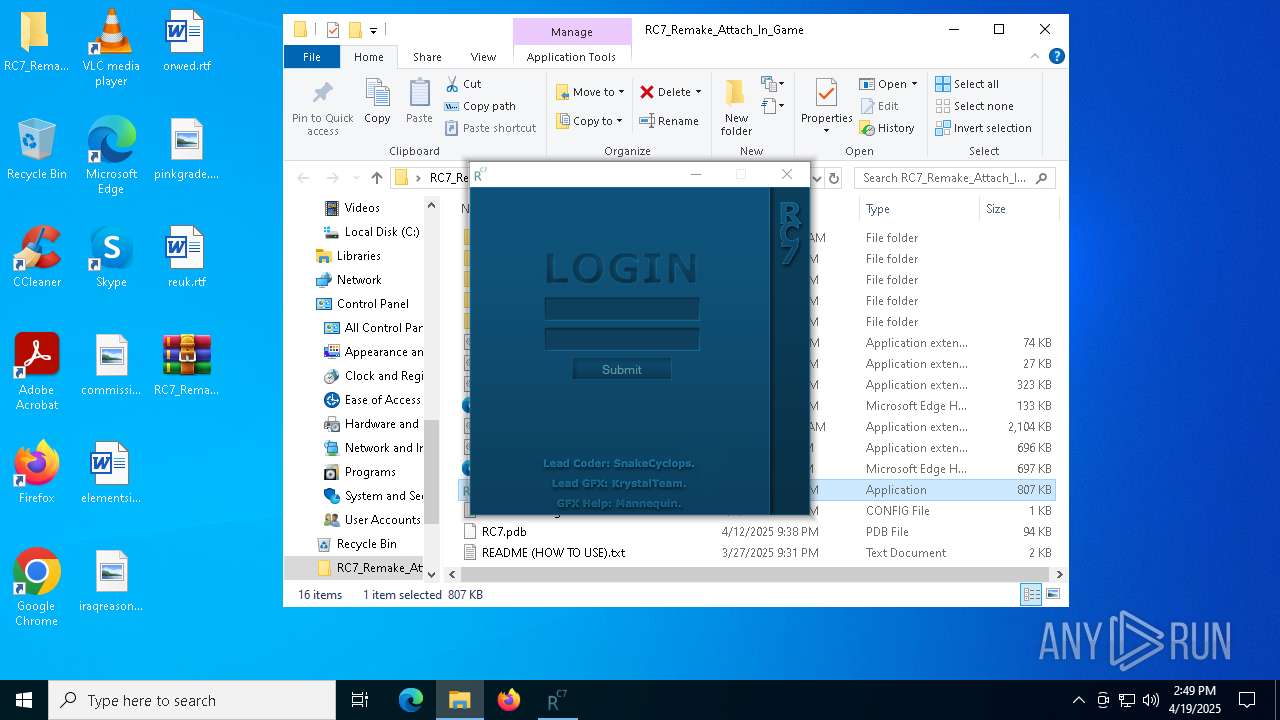
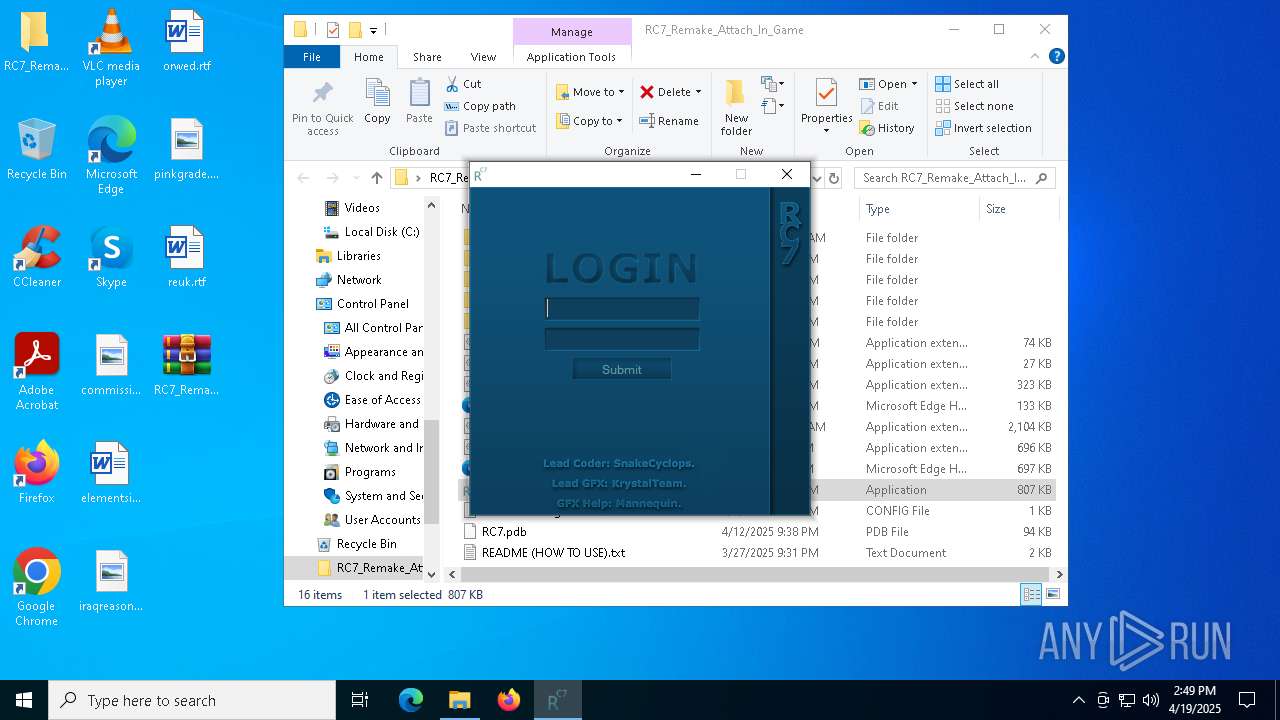
| Verdict: | Malicious activity |
| Analysis date: | April 19, 2025, 14:48:08 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
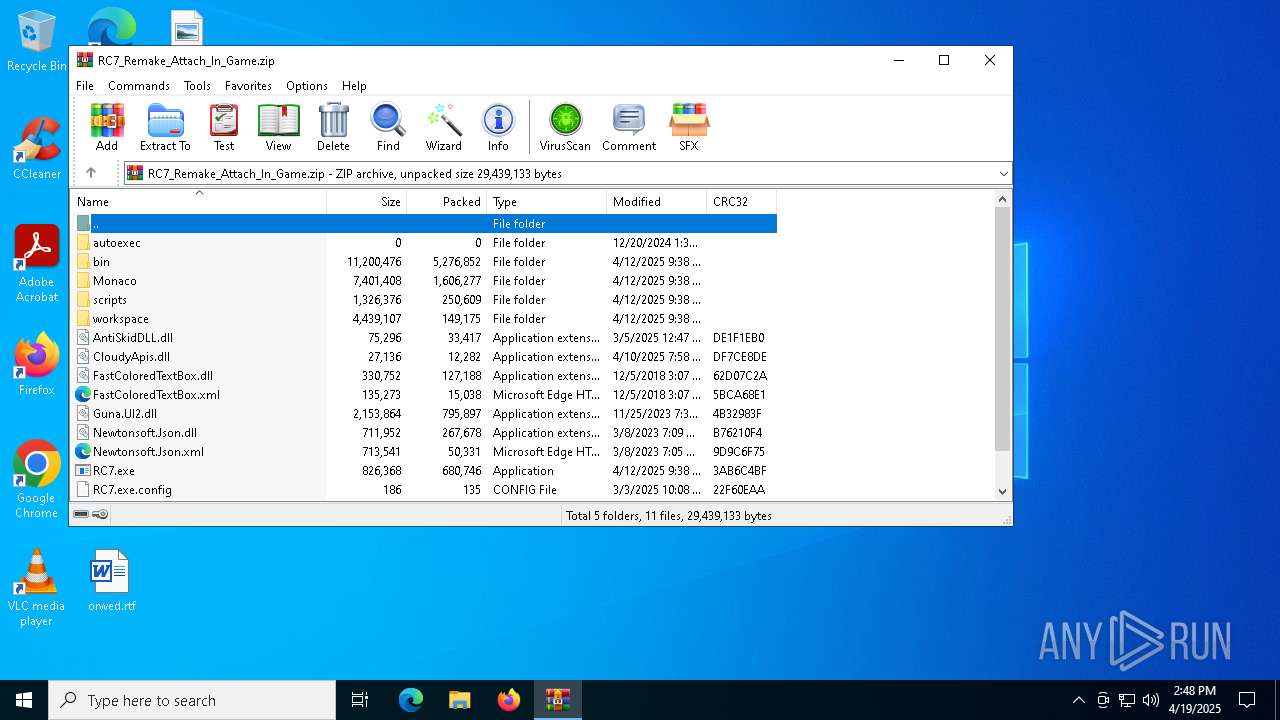
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 45B73A9D1DEA14040B68AC29B7F4B8D7 |
| SHA1: | BF293D2ACBAAF2B4EB1CC0F82AED46C5ABE4EACB |
| SHA256: | D5CD9031DFF206FFD38A6294C84477F598AADEBC592E98FF34AEEFBE31B6C210 |
| SSDEEP: | 98304:9JQdOK+2wMRzQfBuG9gFeWCewAdqiRBlv9gaGeZMJpGWbOKoRfdLhwZ97Diu9TXD:YSc3OSeBfEtVjMK+HVCPtX6x |
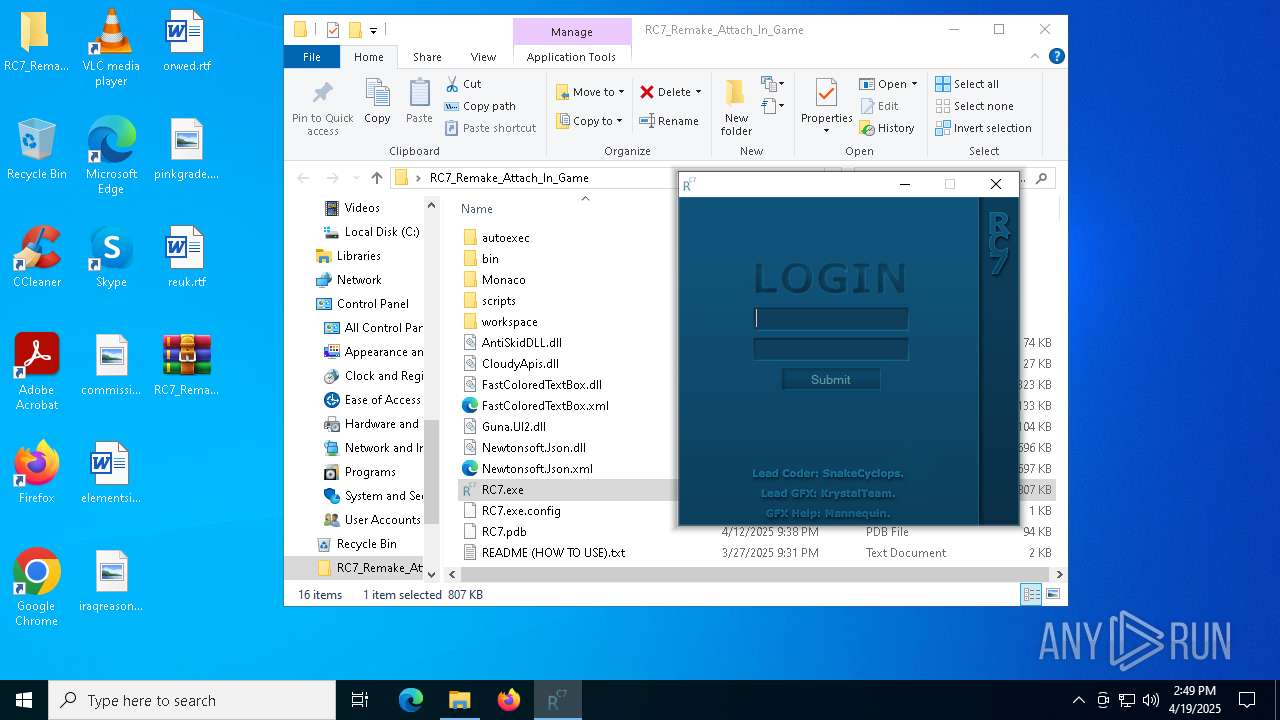
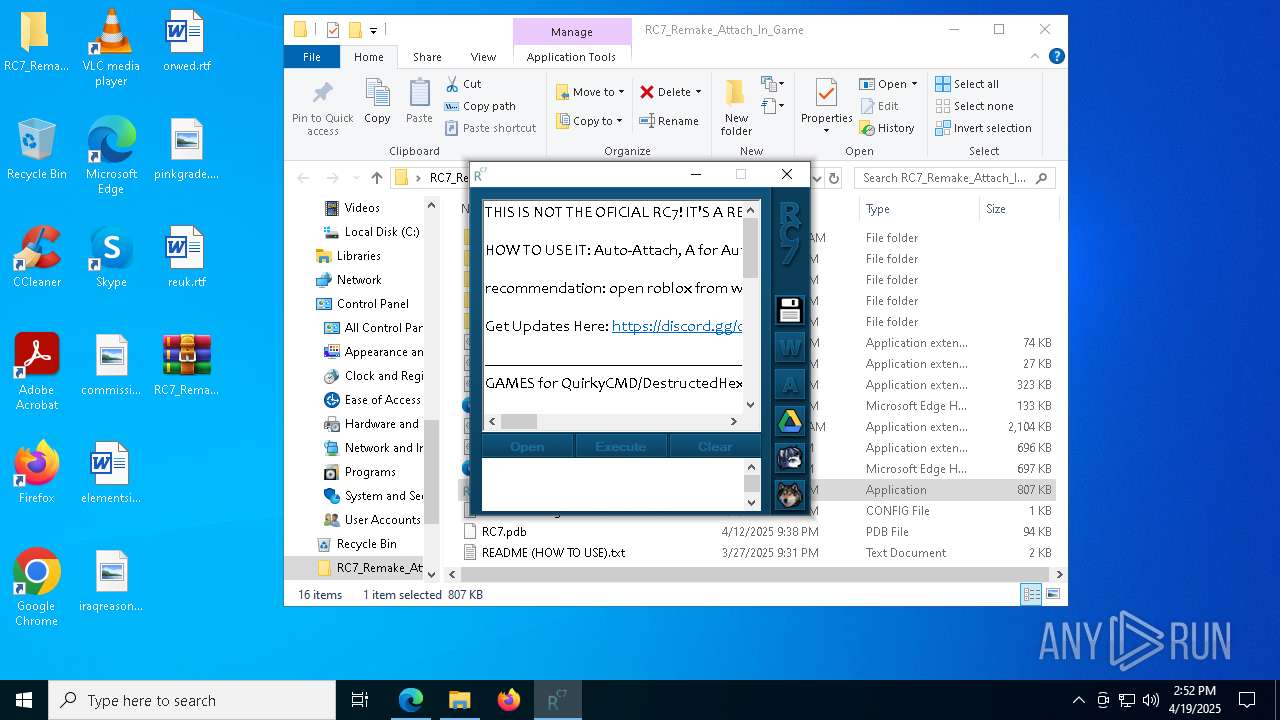
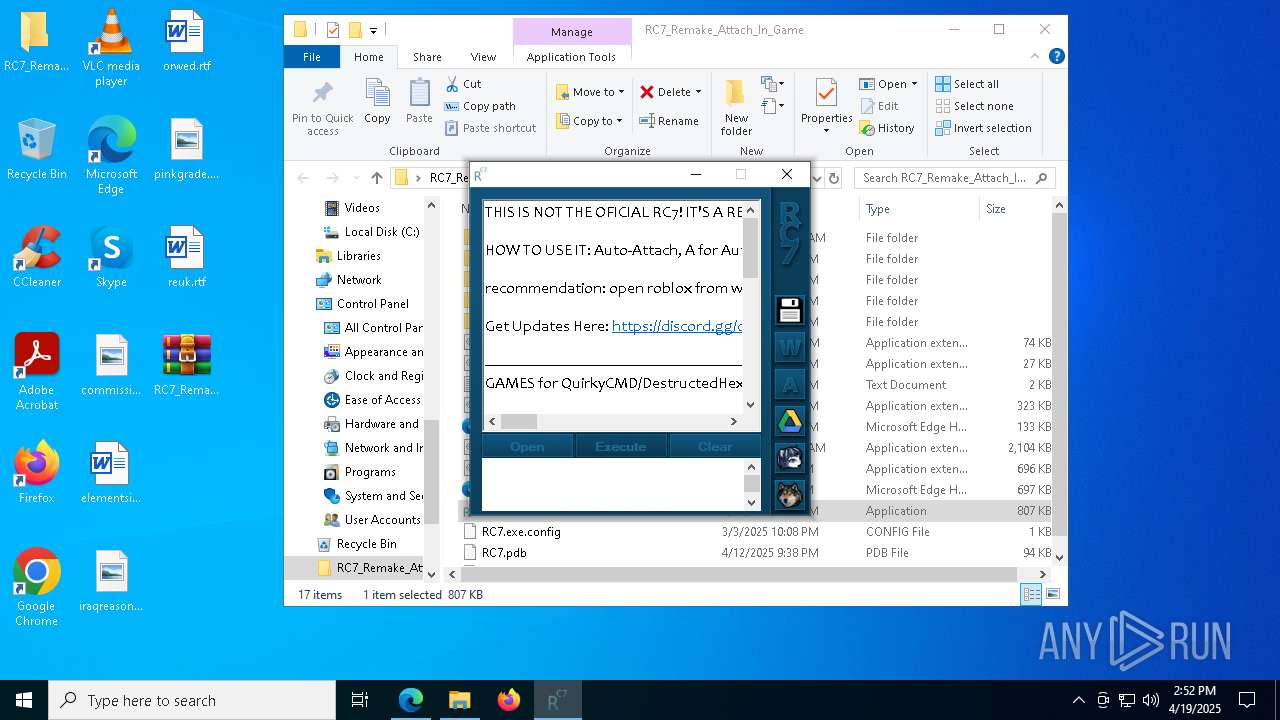
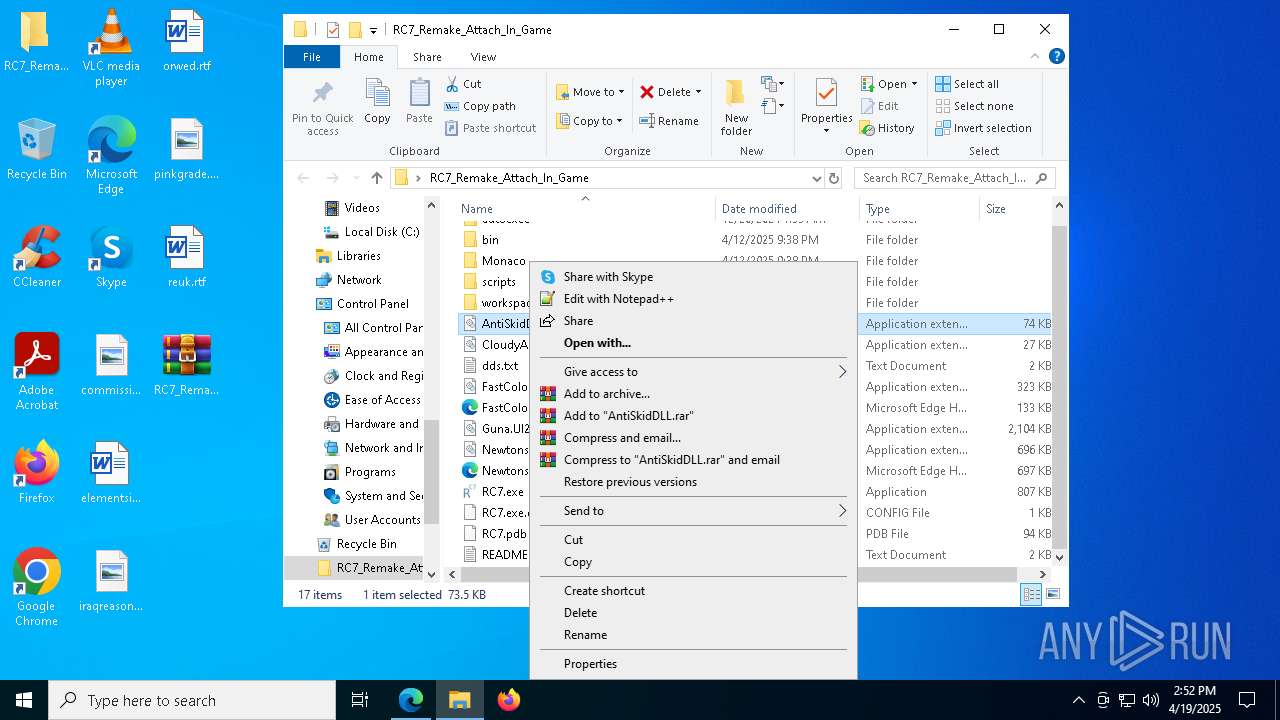
MALICIOUS
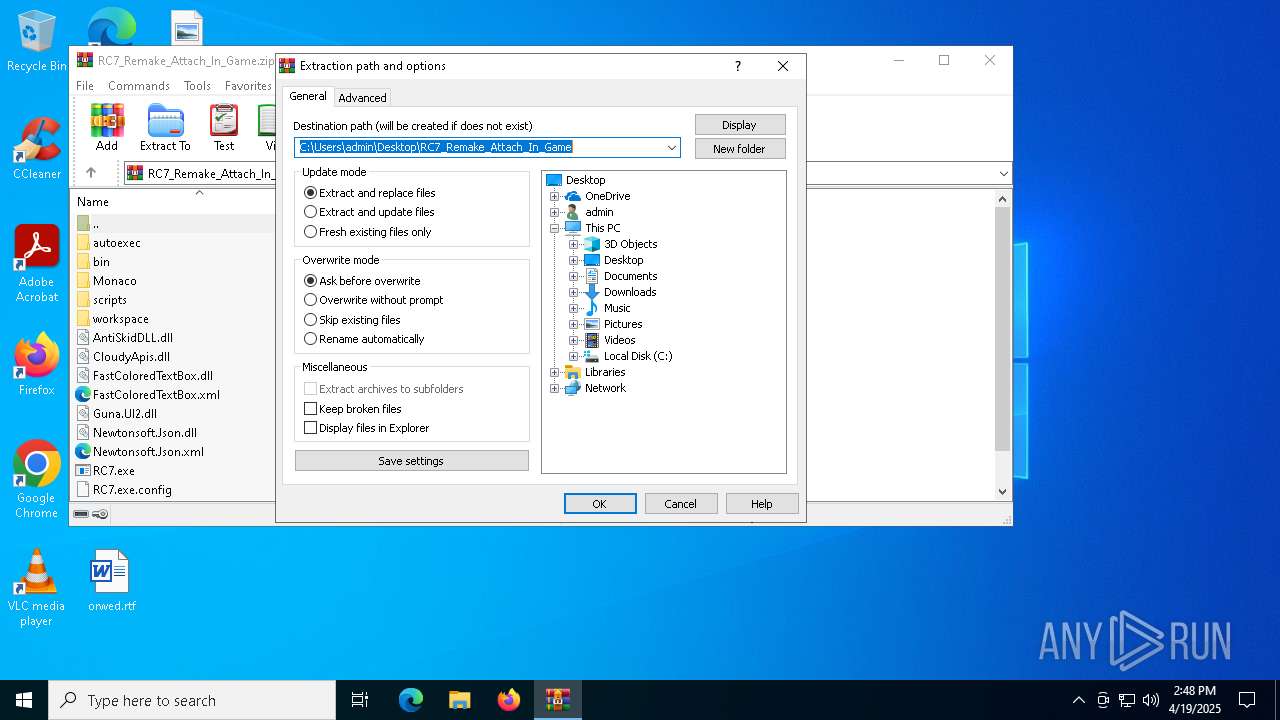
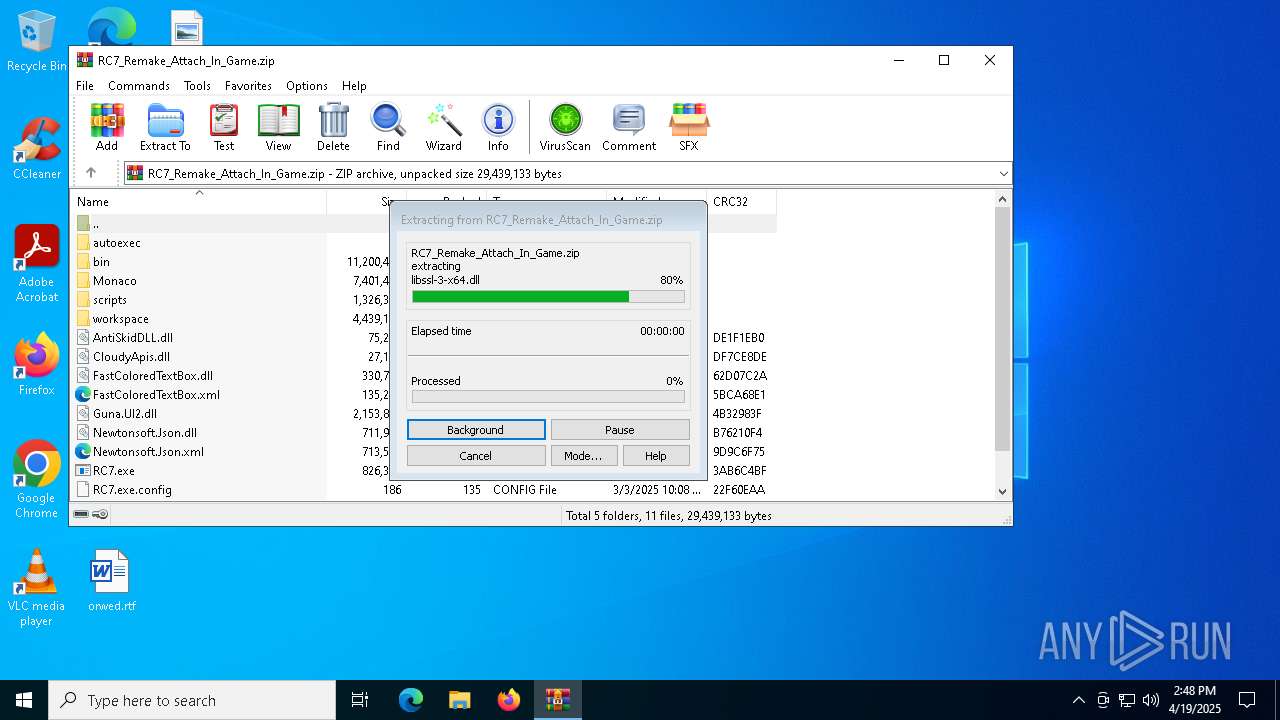
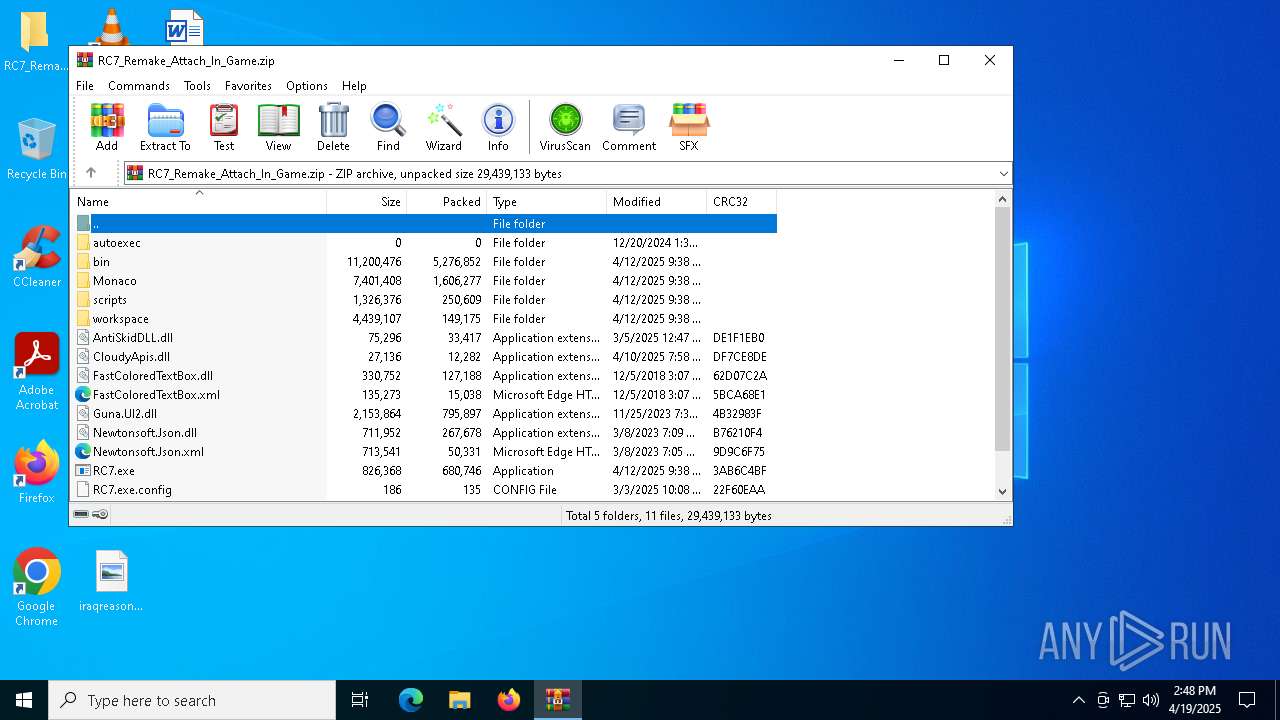
Generic archive extractor
- WinRAR.exe (PID: 6436)
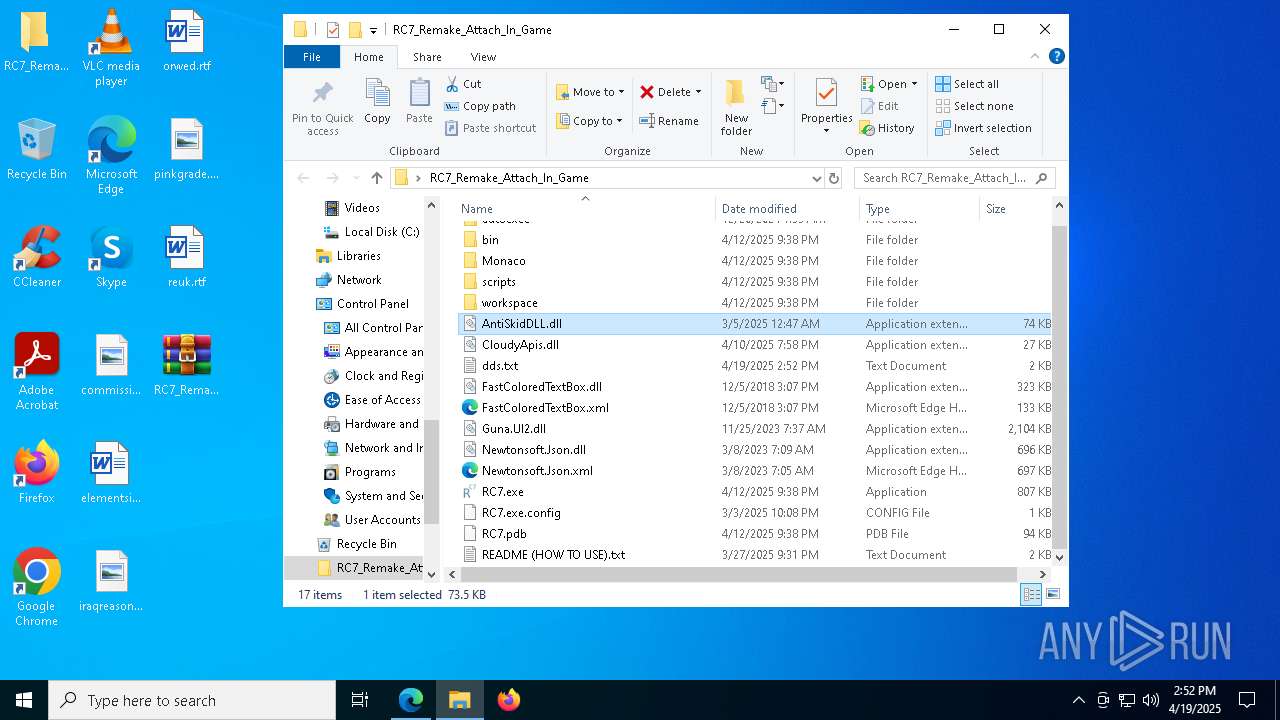
SUSPICIOUS
Reads the BIOS version
- RC7.exe (PID: 4200)
- RC7.exe (PID: 7744)
- RC7.exe (PID: 7584)
- RC7.exe (PID: 2504)
- RC7.exe (PID: 7724)
Read disk information to detect sandboxing environments
- RC7.exe (PID: 4200)
- RC7.exe (PID: 7744)
- RC7.exe (PID: 7584)
- RC7.exe (PID: 2504)
- RC7.exe (PID: 7724)
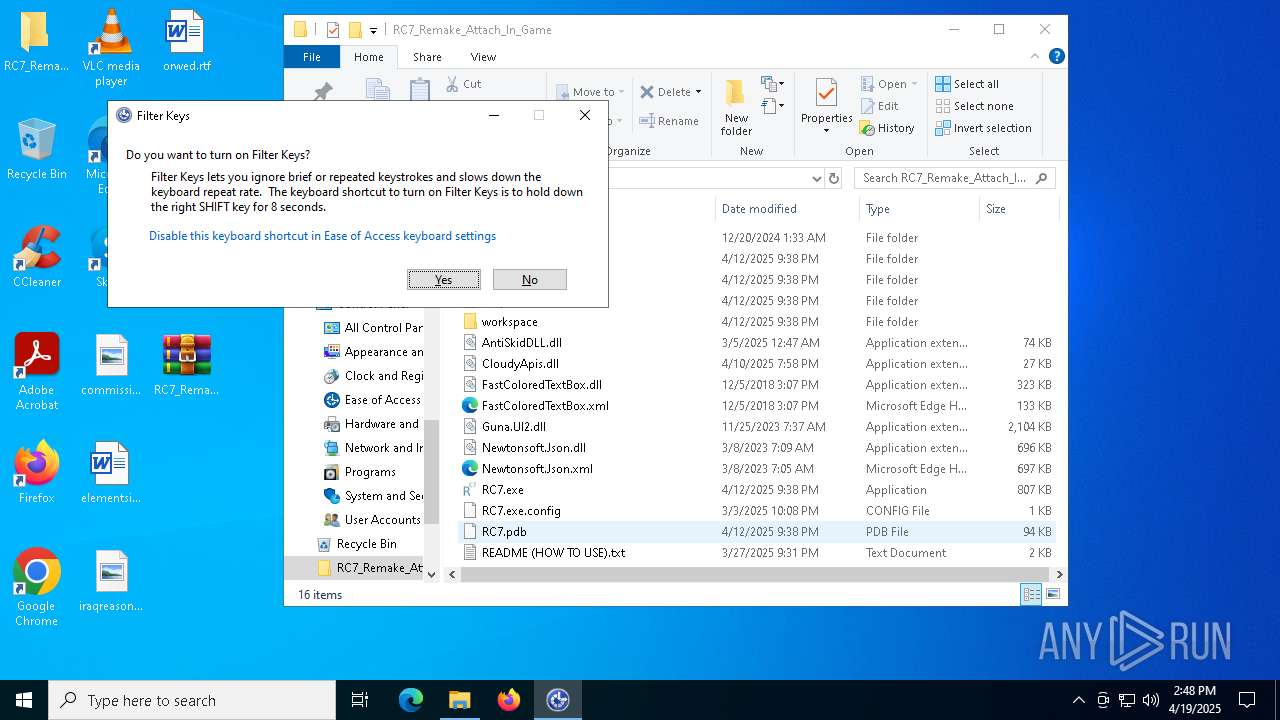
The process checks if it is being run in the virtual environment
- RC7.exe (PID: 4200)
- RC7.exe (PID: 7744)
- RC7.exe (PID: 7584)
- RC7.exe (PID: 2504)
- RC7.exe (PID: 7724)
Reads security settings of Internet Explorer
- RC7.exe (PID: 4200)
- RC7.exe (PID: 7724)
Executes application which crashes
- RC7.exe (PID: 4200)
- RC7.exe (PID: 7584)
- RC7.exe (PID: 7744)
- RC7.exe (PID: 7724)
- RC7.exe (PID: 2504)
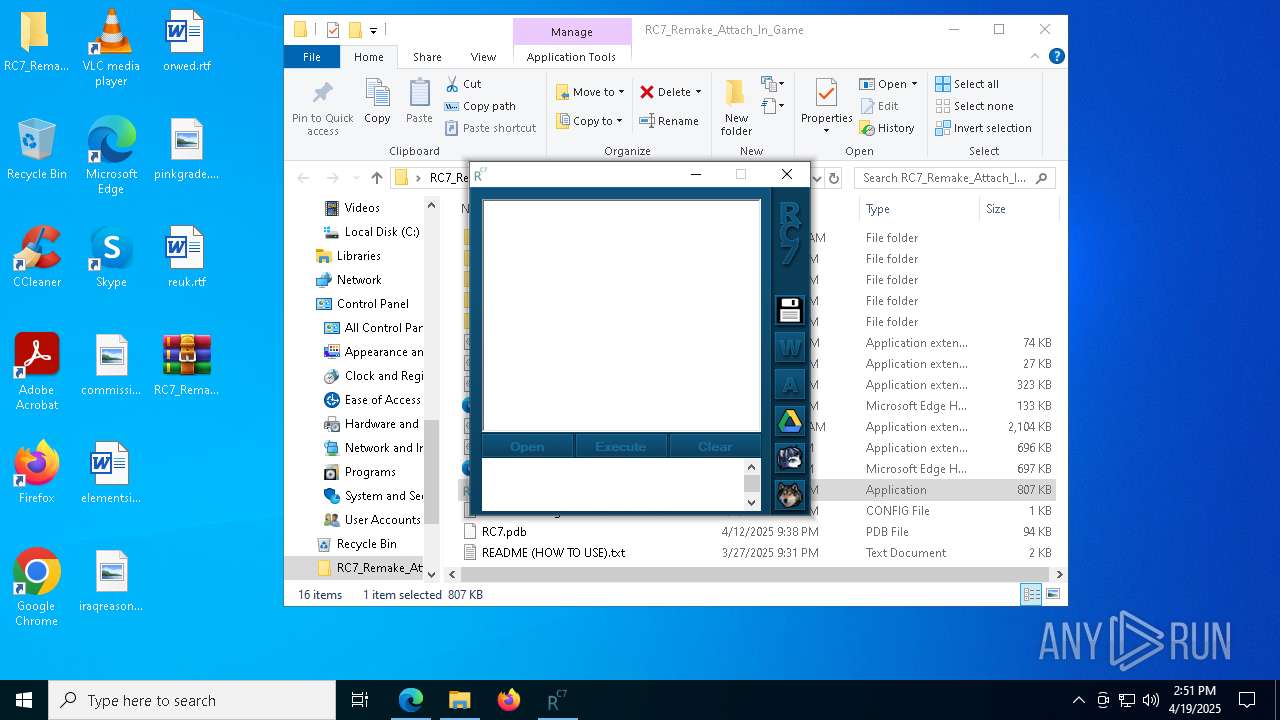
There is functionality for taking screenshot (YARA)
- RC7.exe (PID: 4200)
- RC7.exe (PID: 7744)
INFO
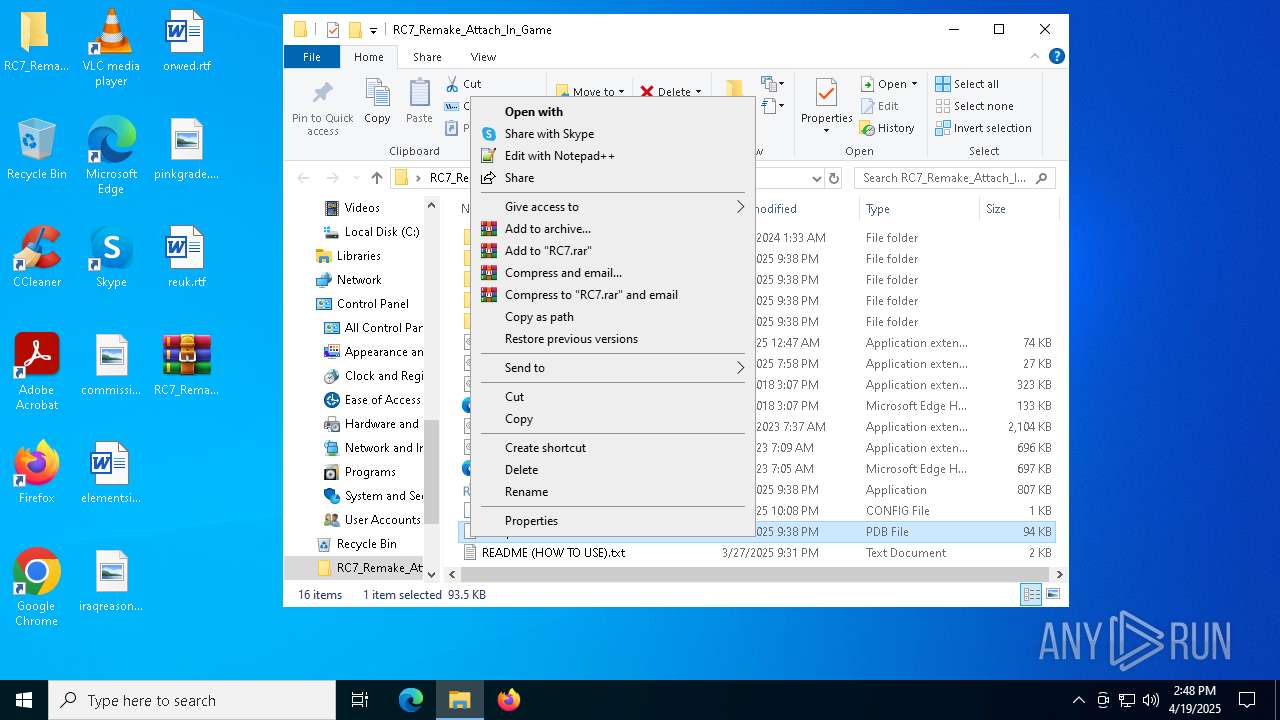
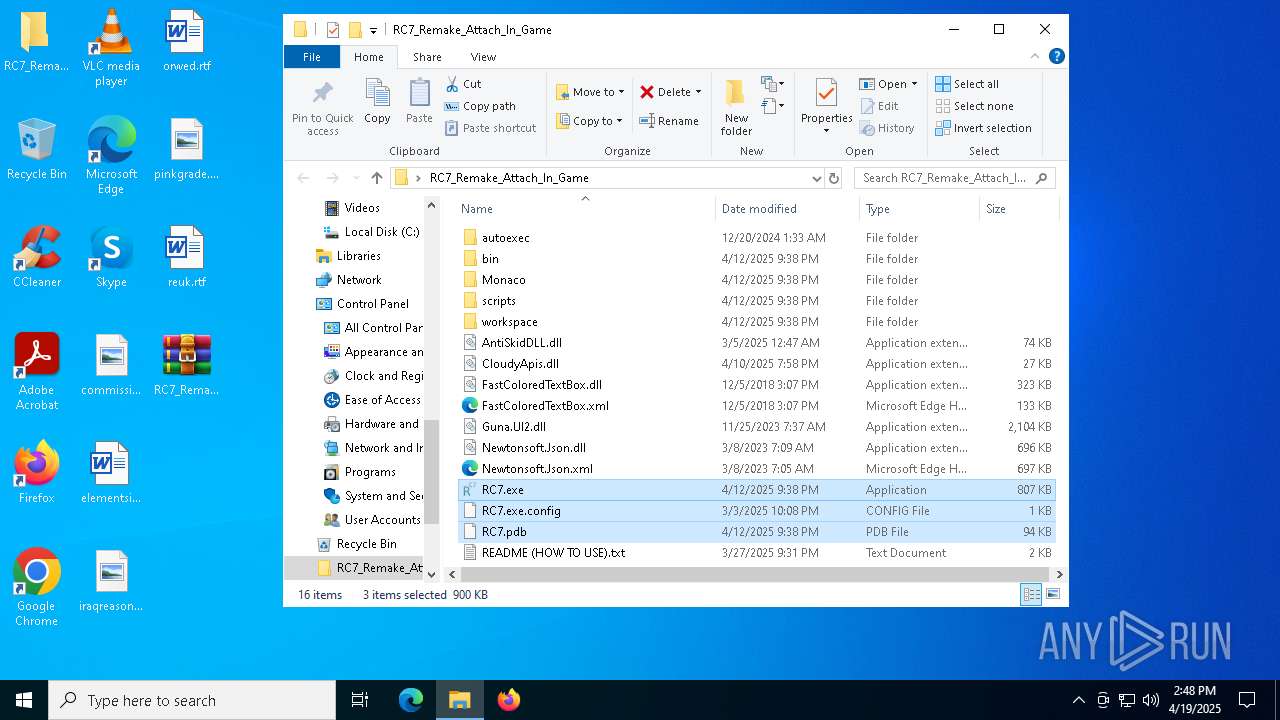
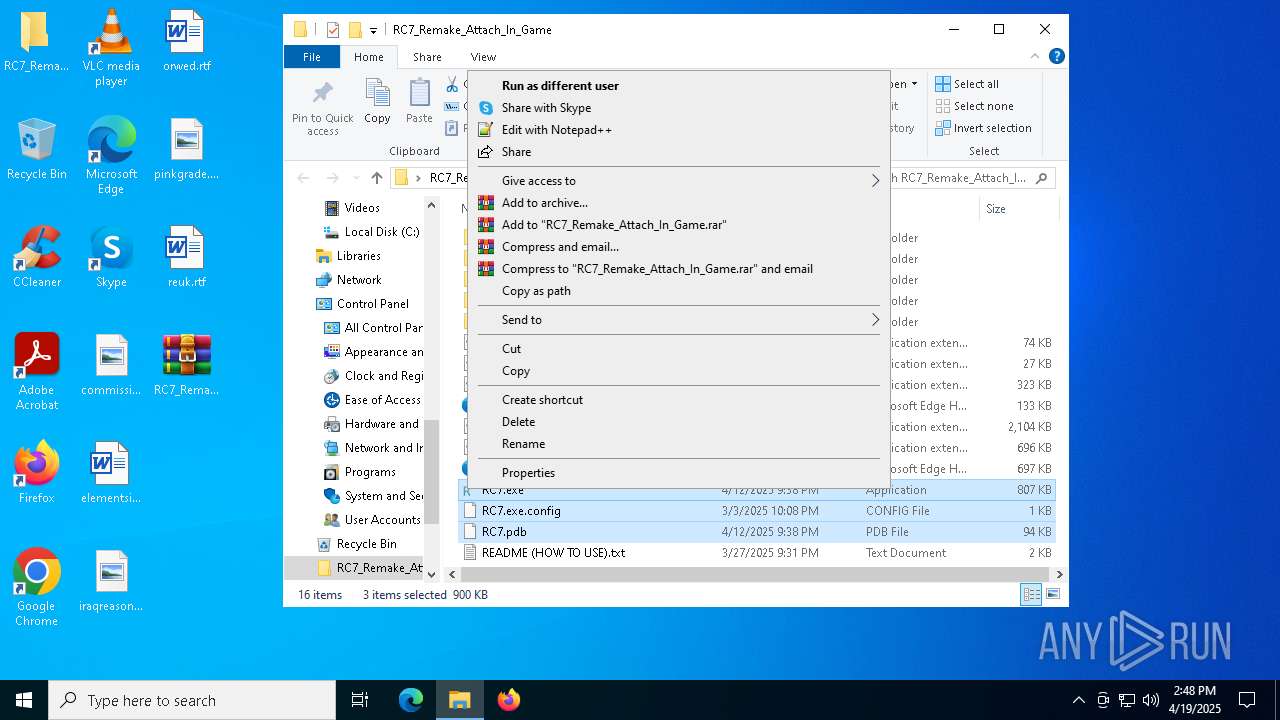
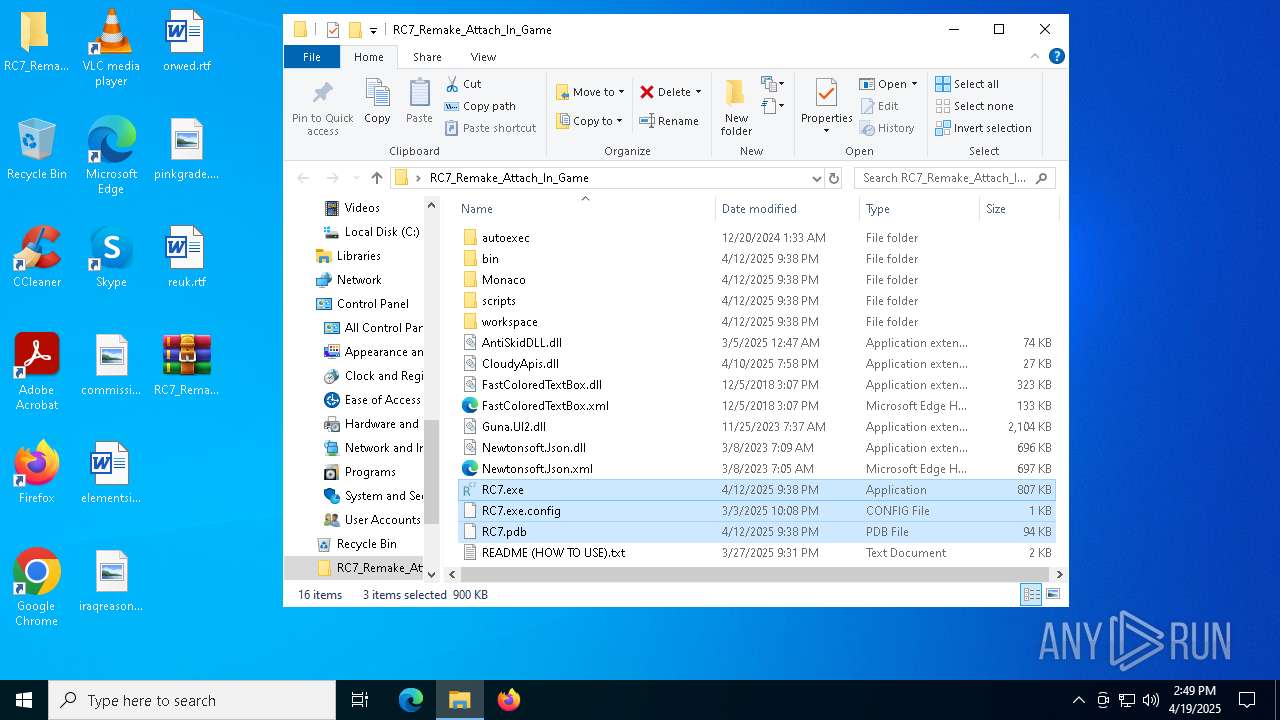
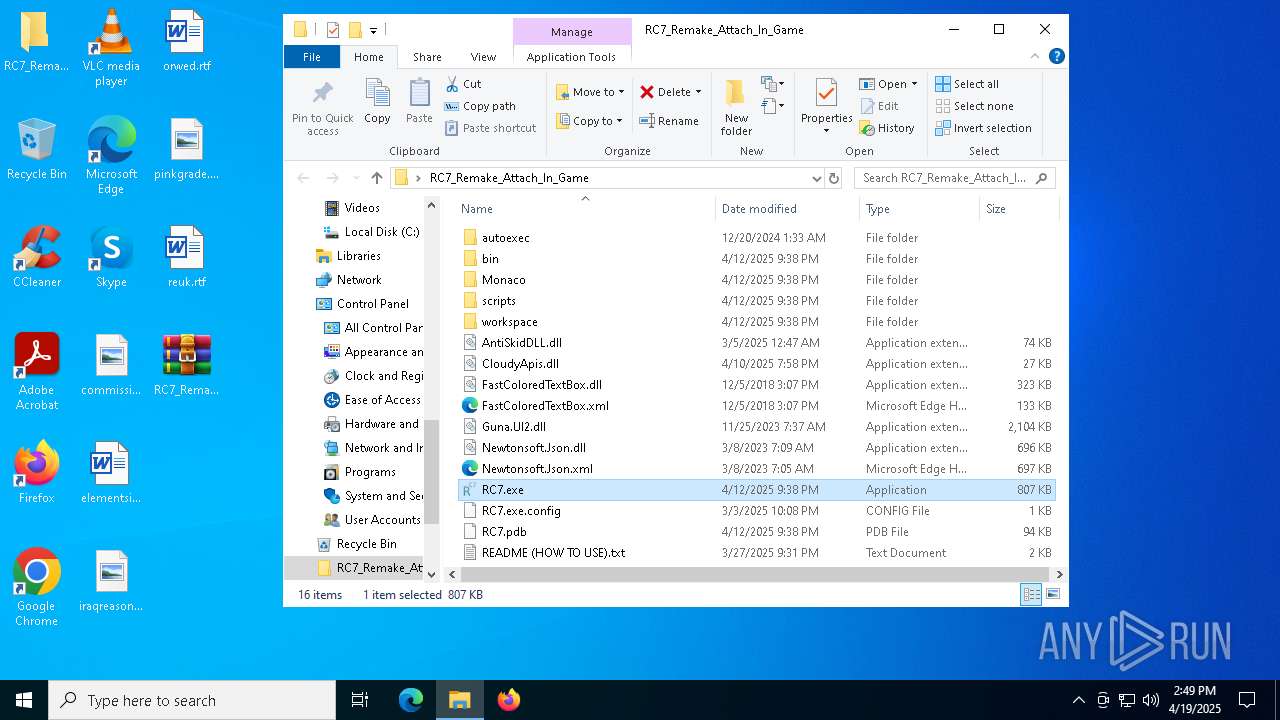
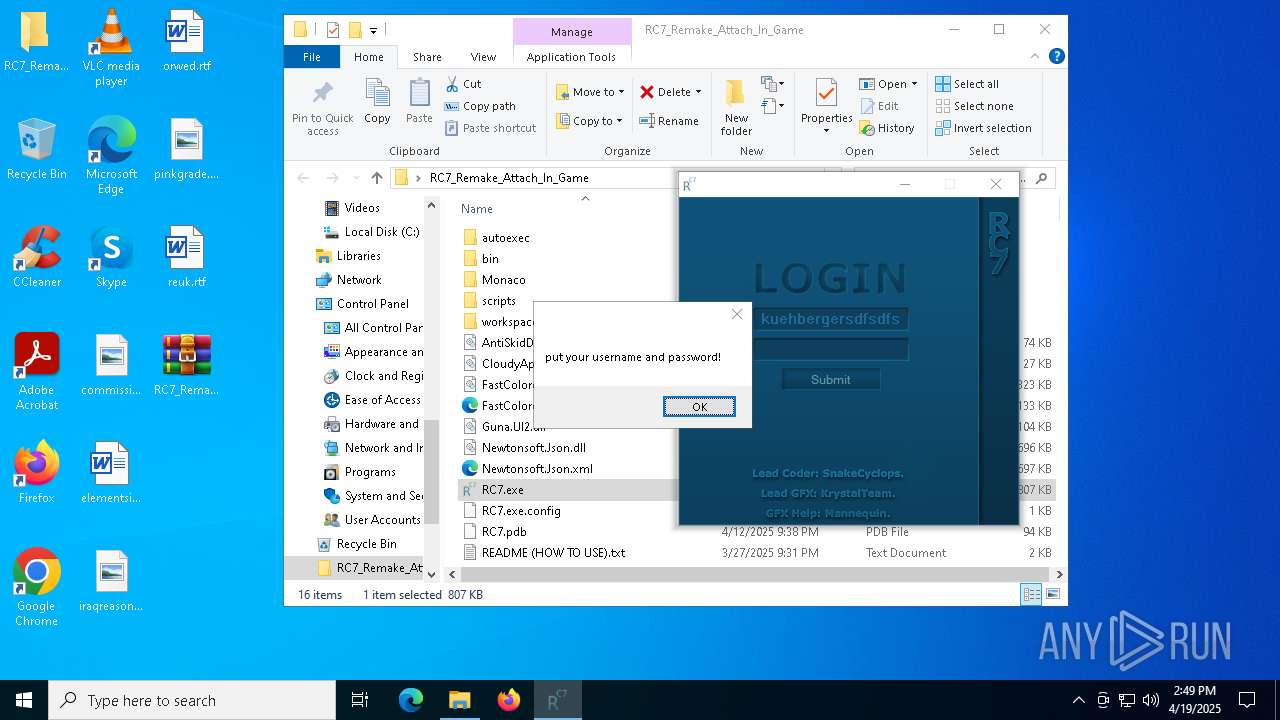
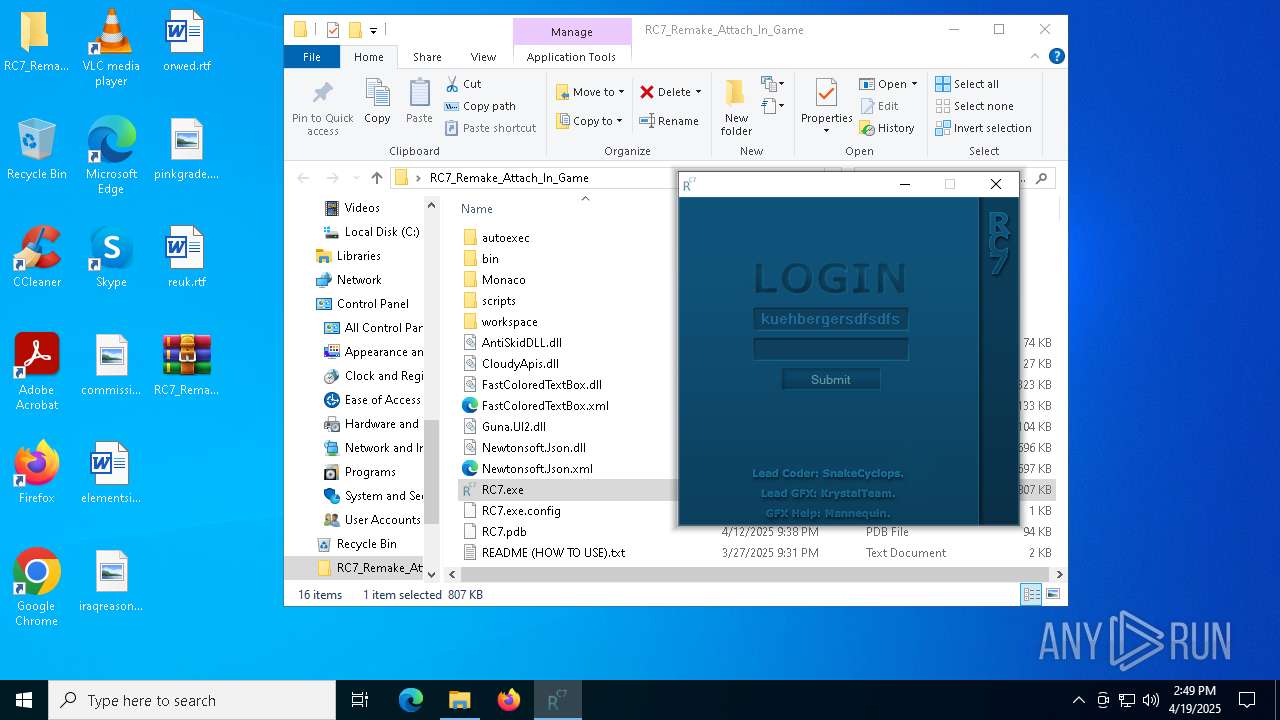
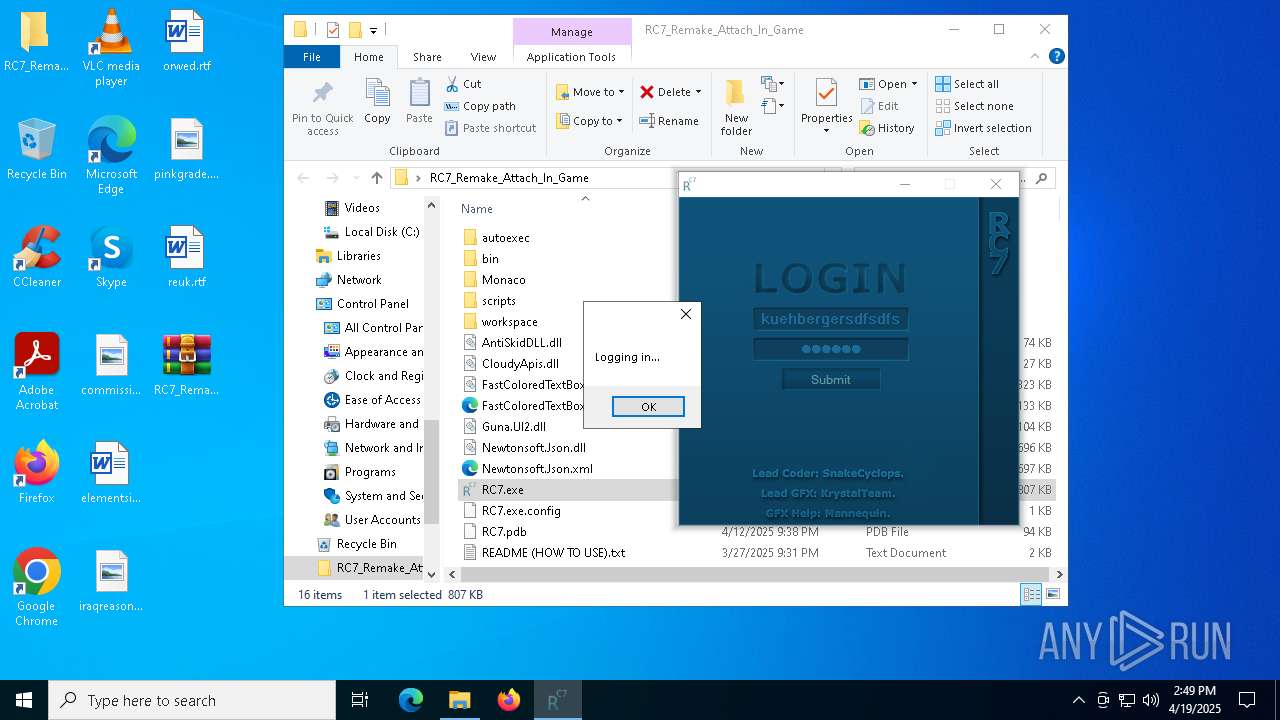
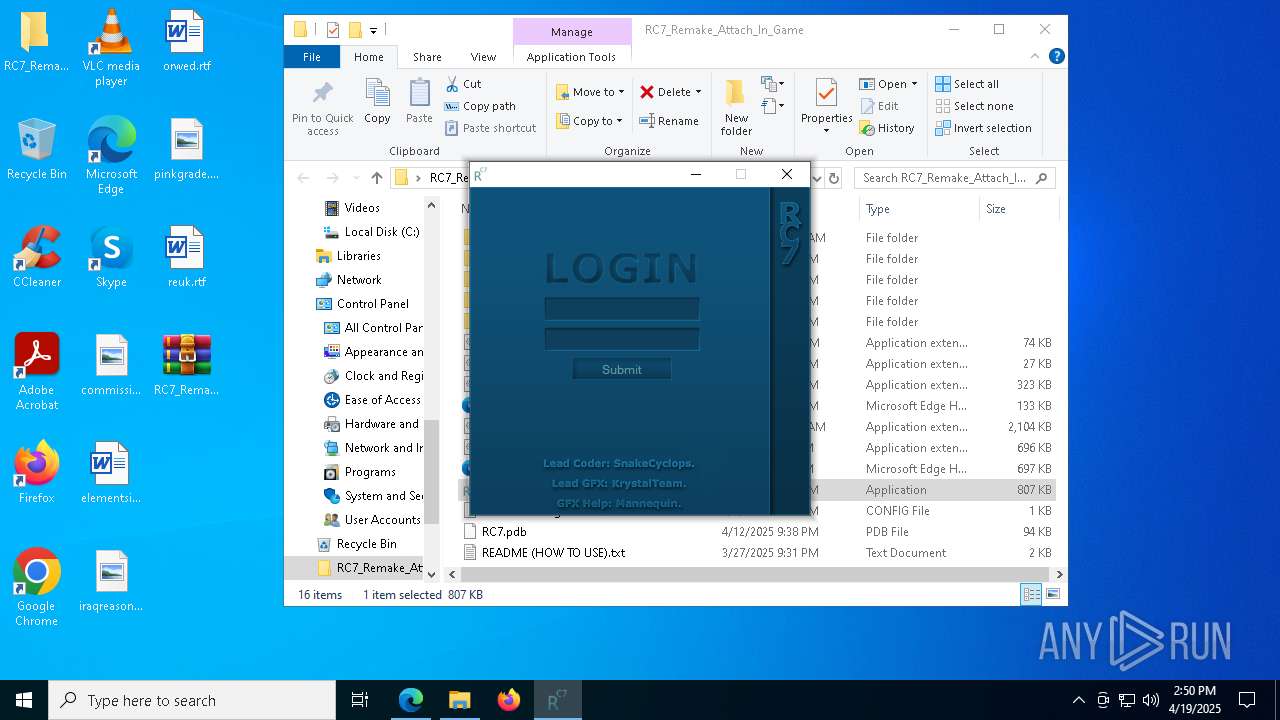
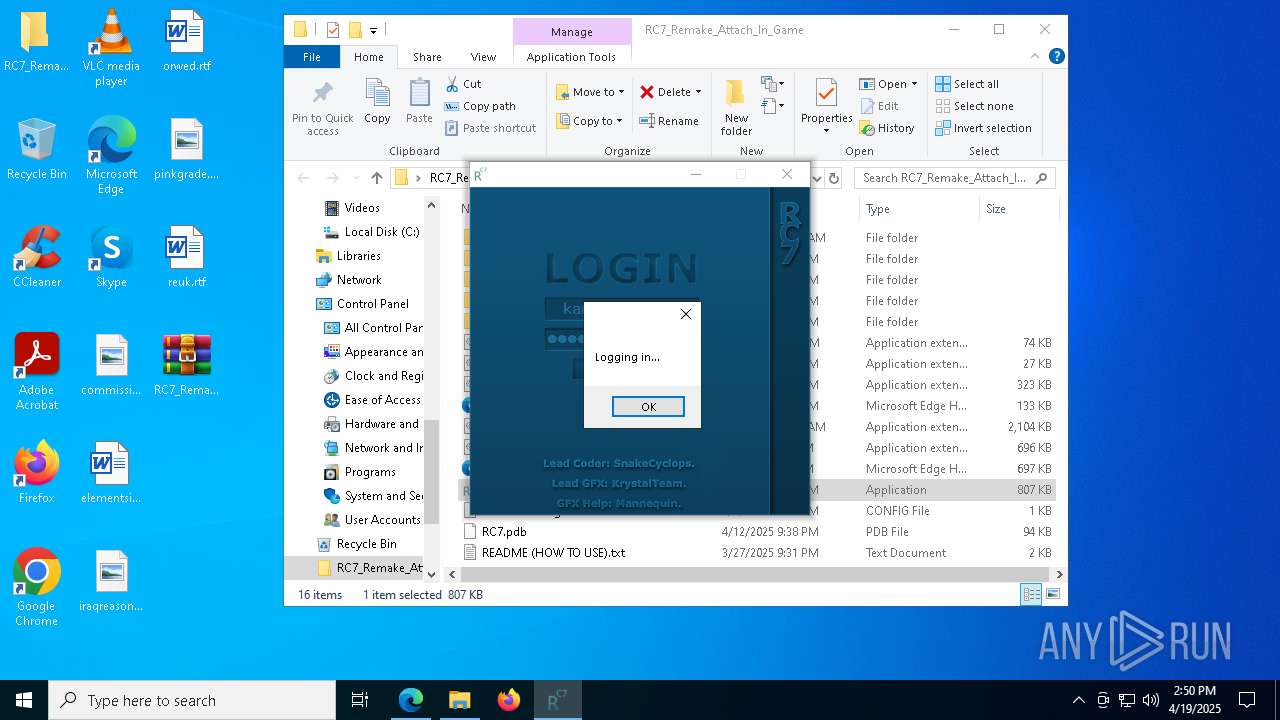
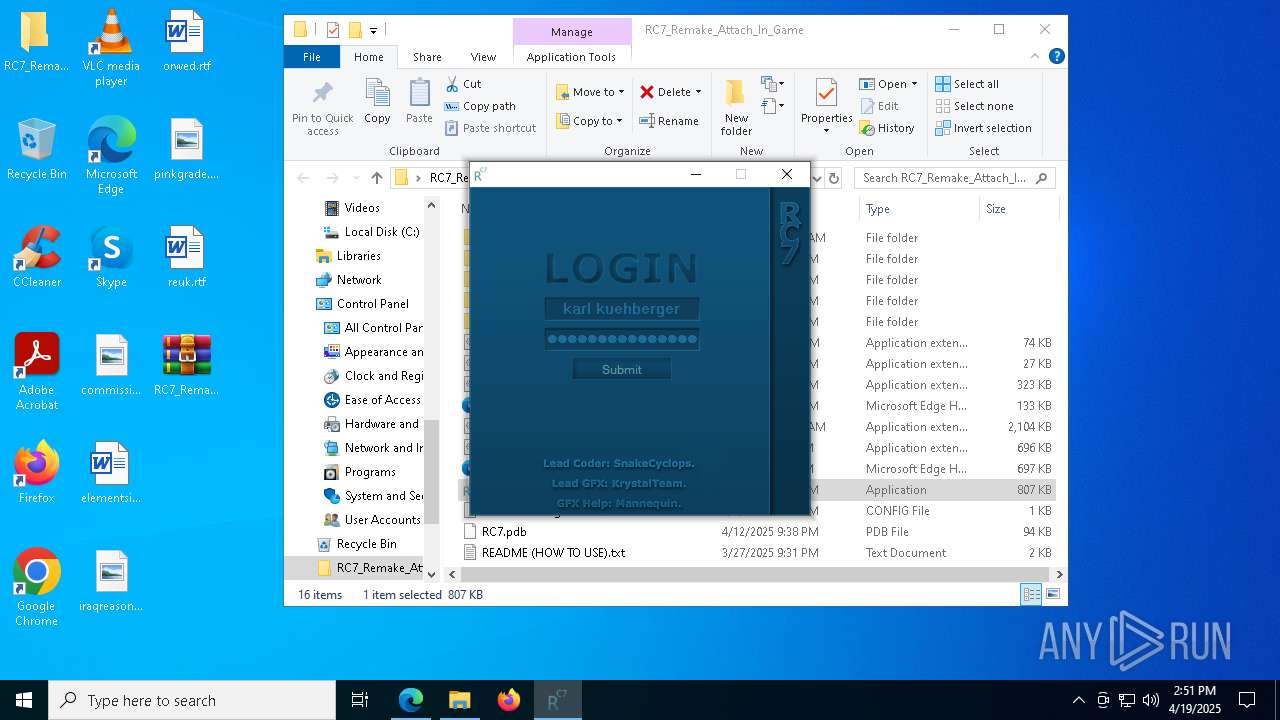
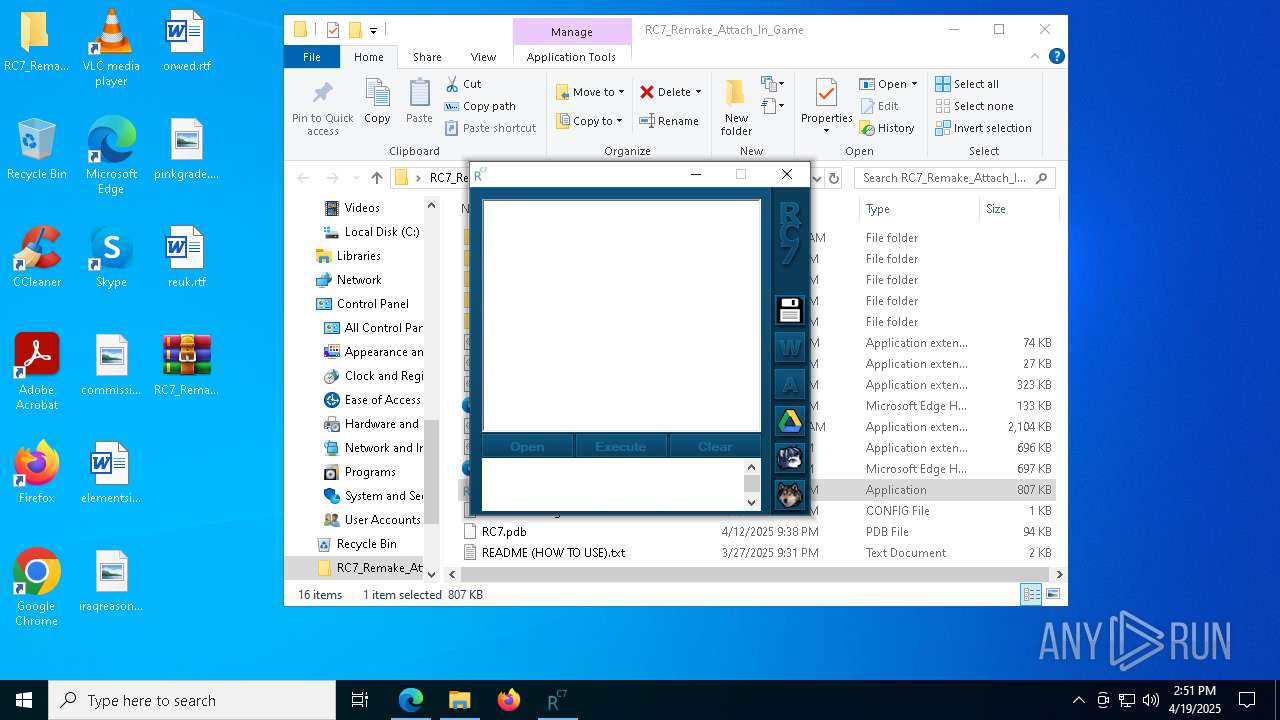
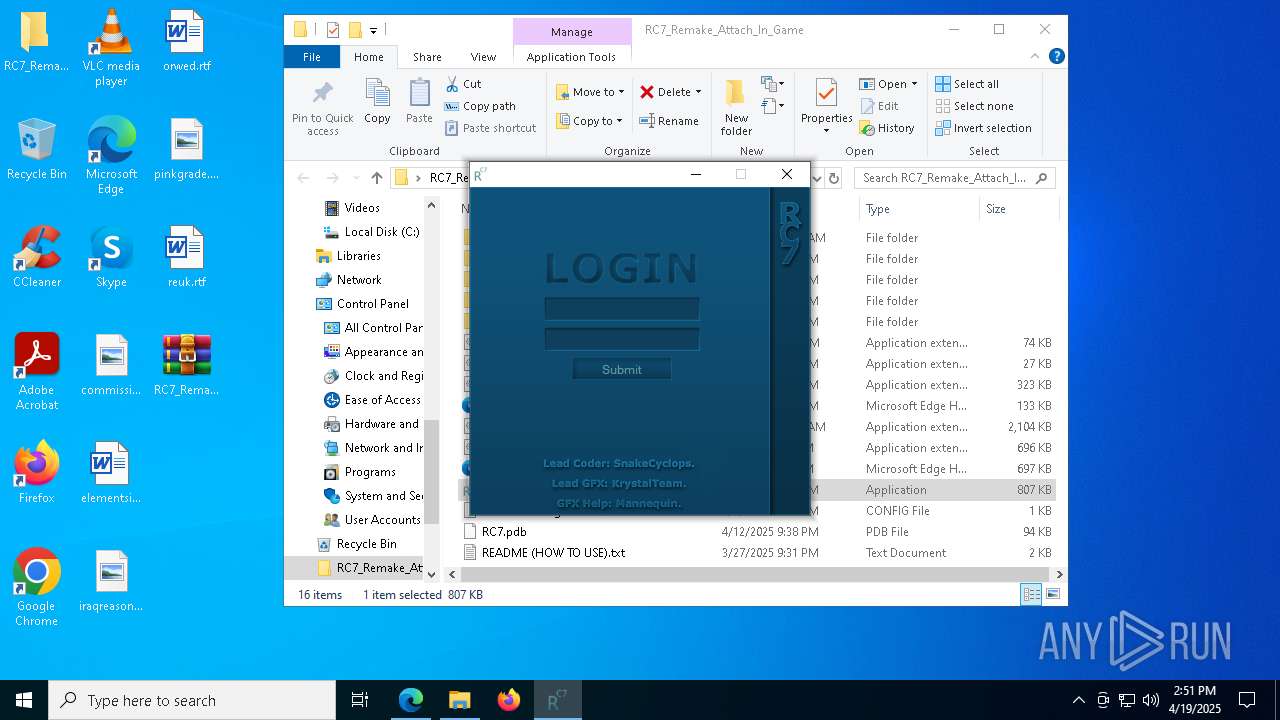
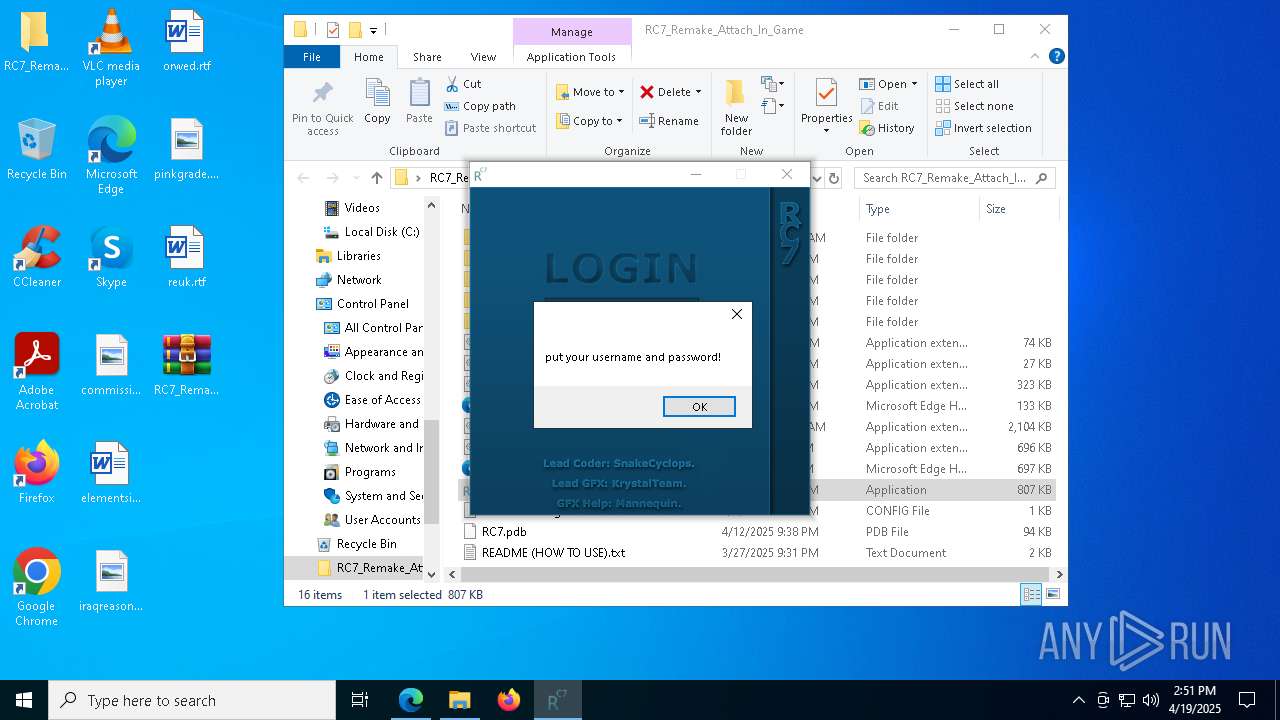
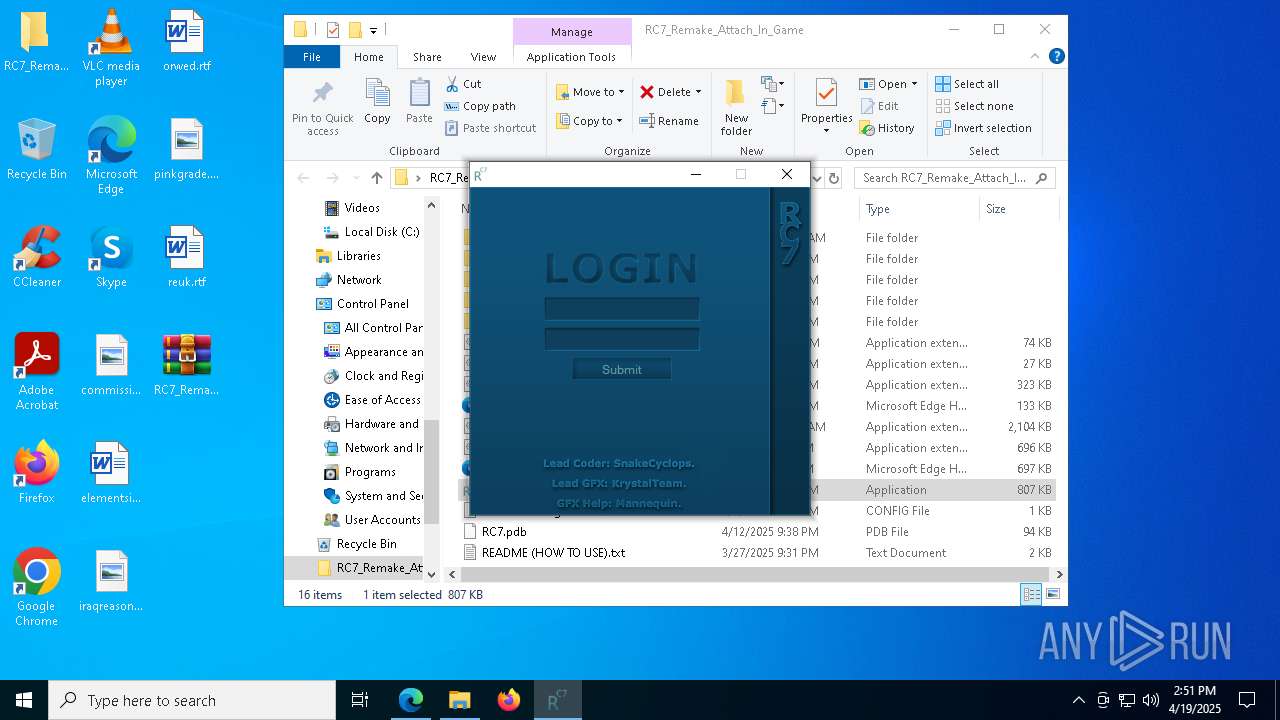
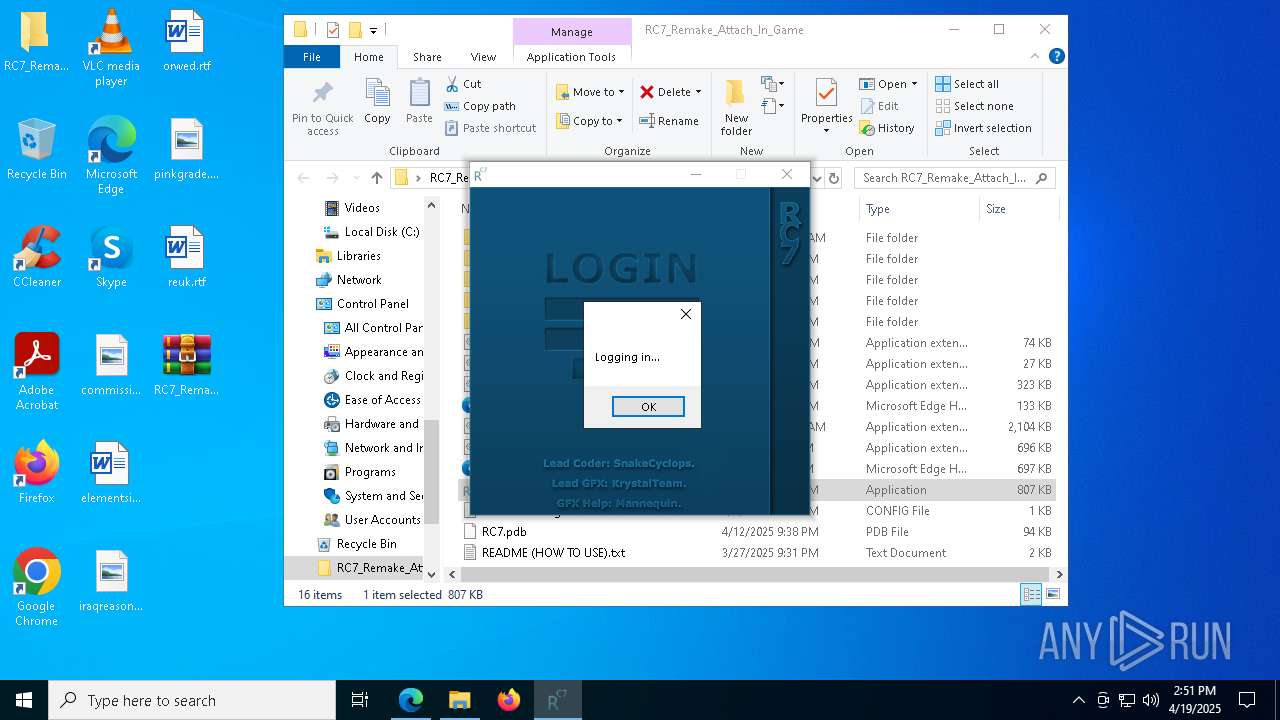
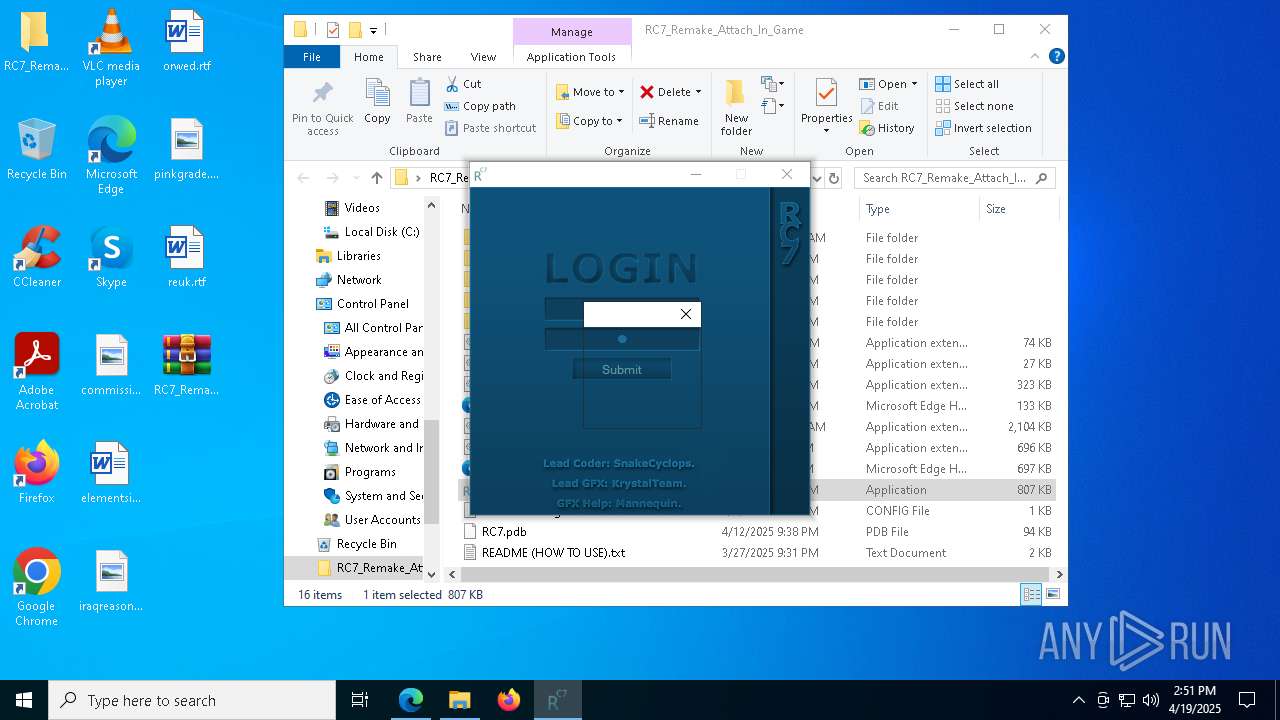
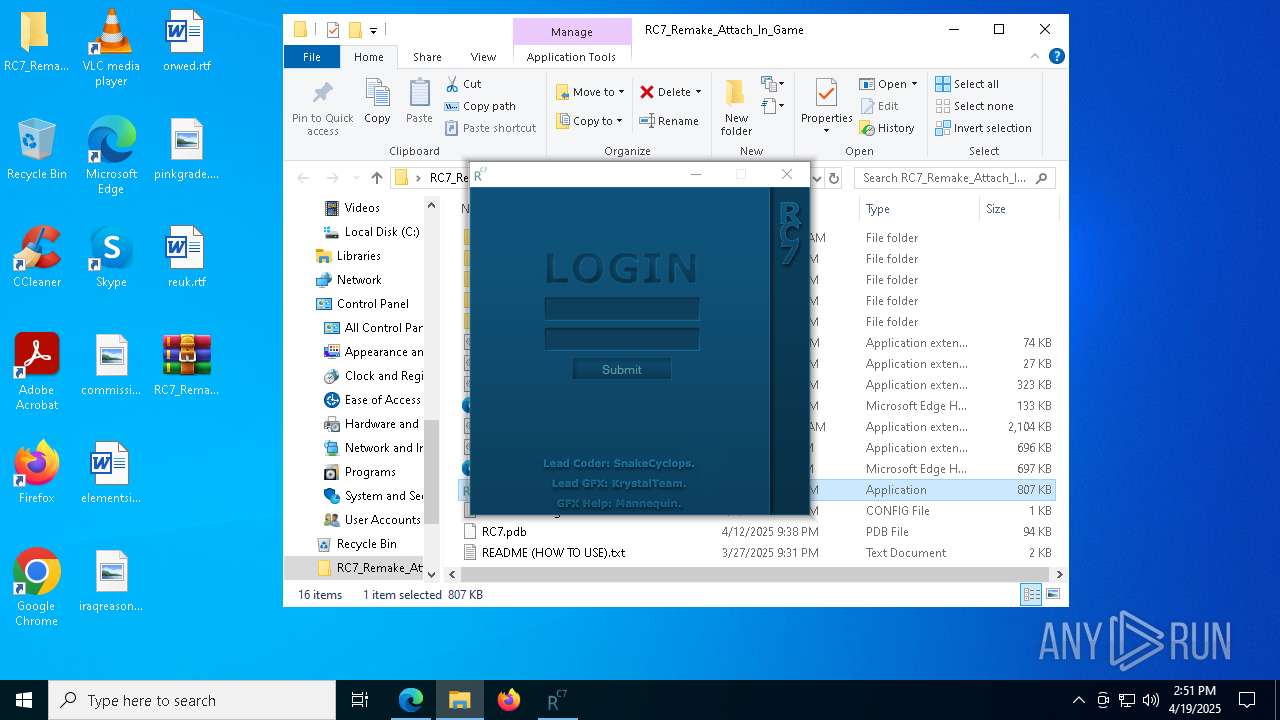
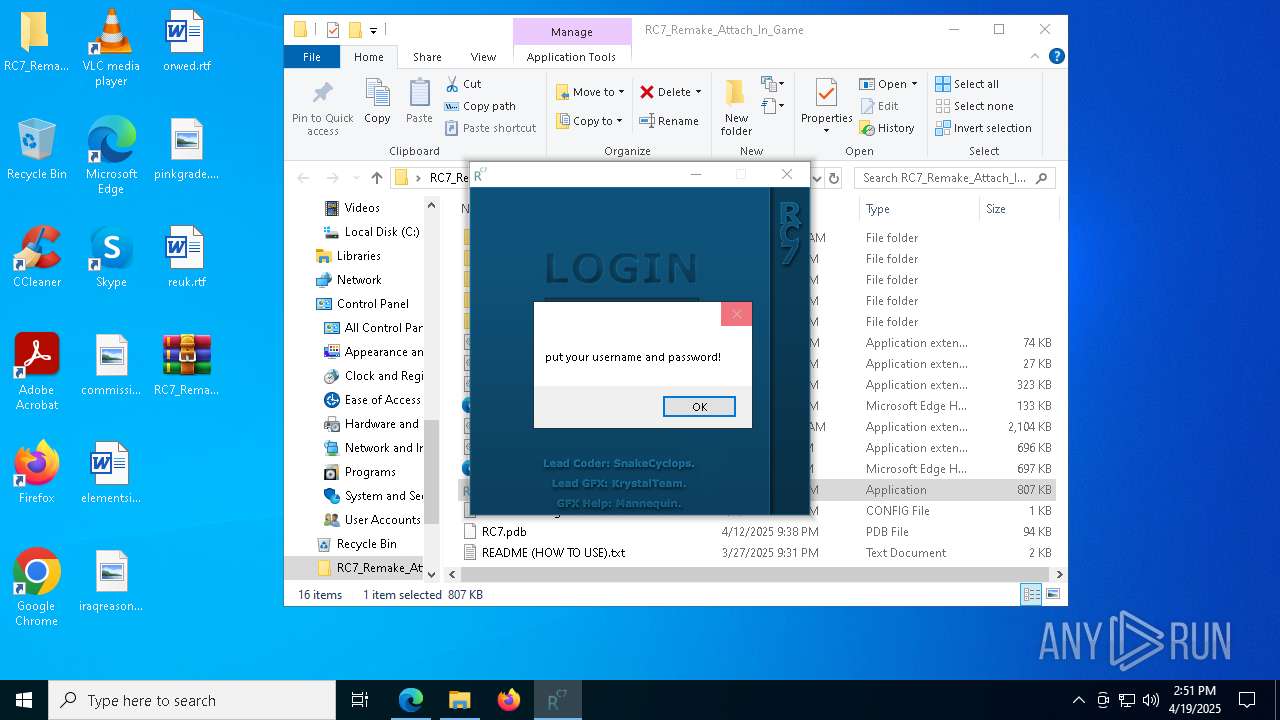
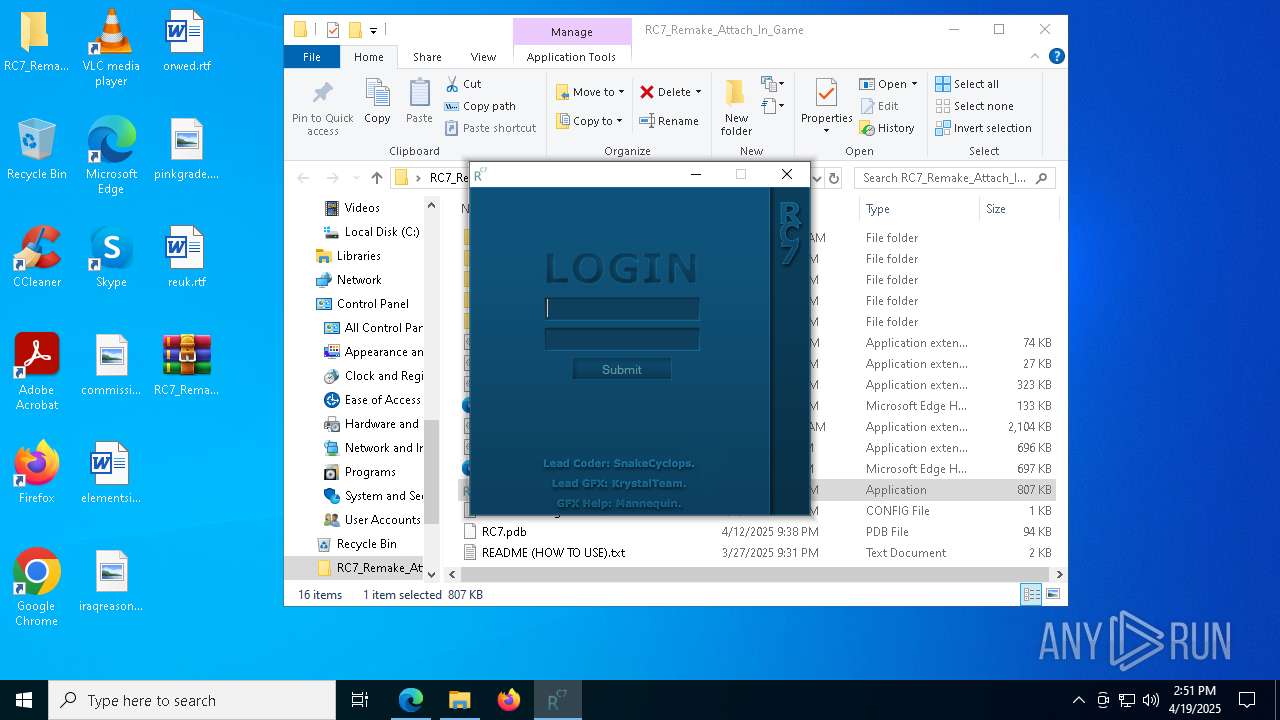
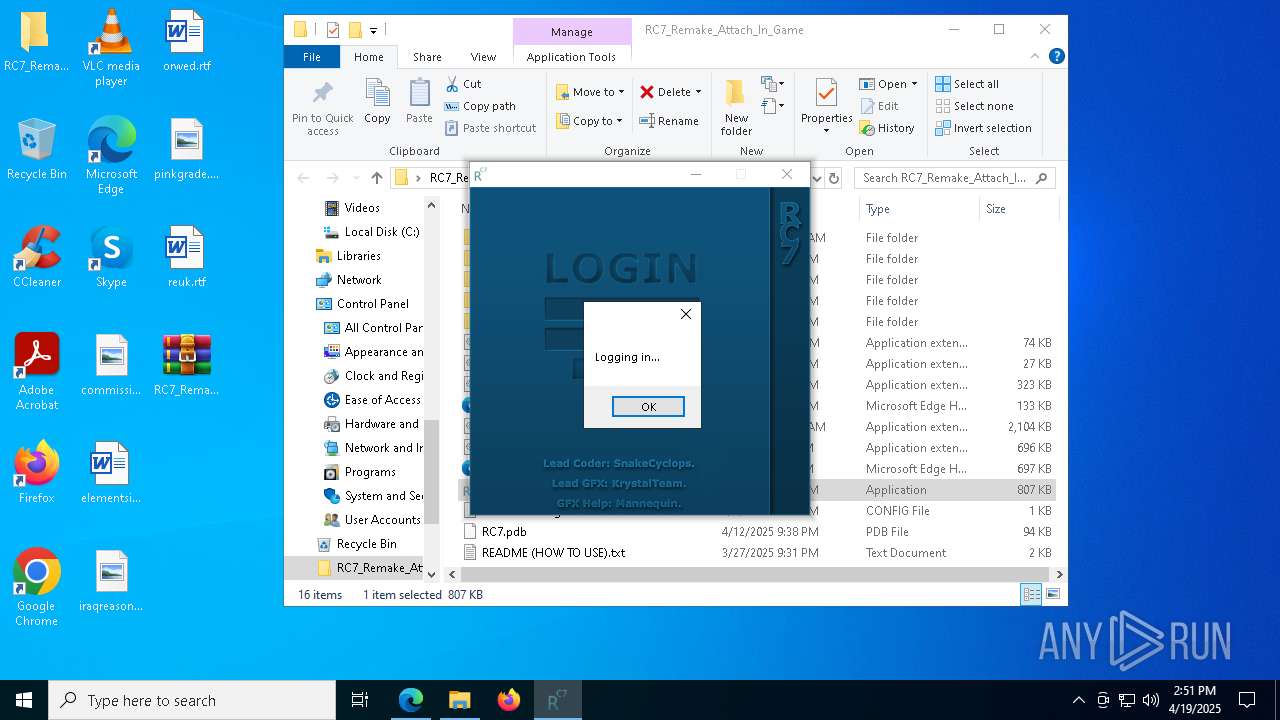
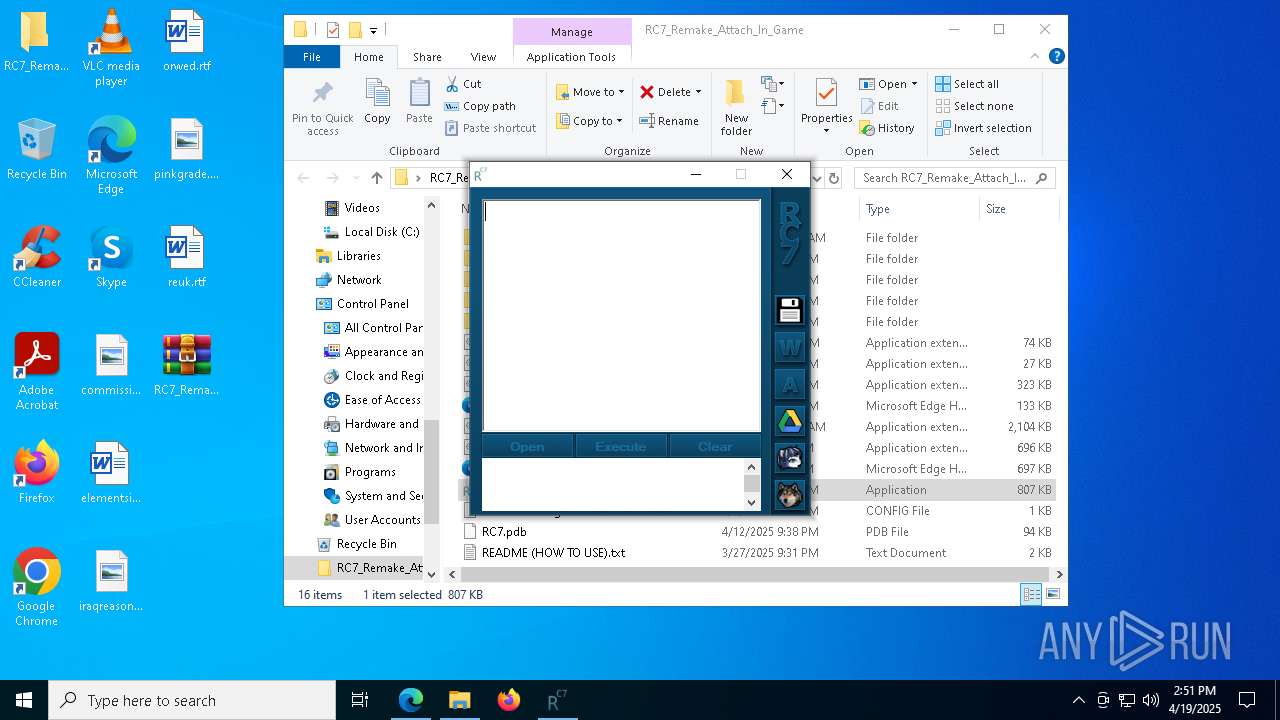
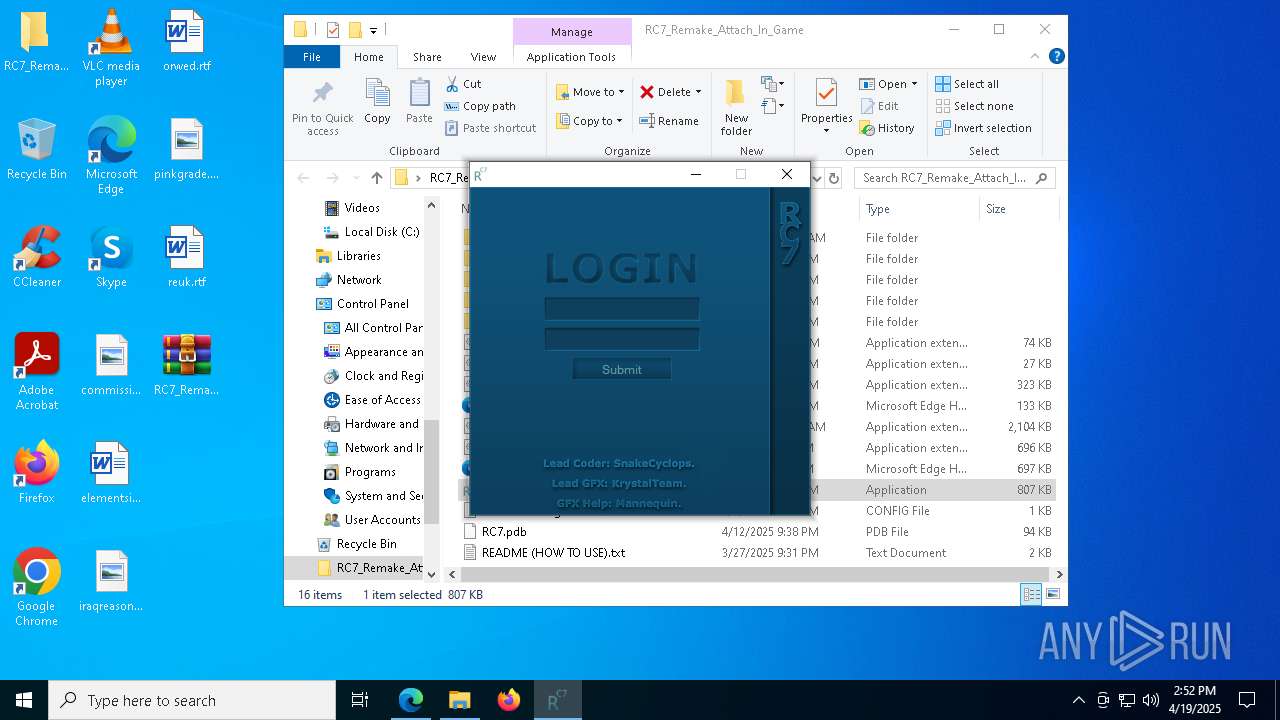
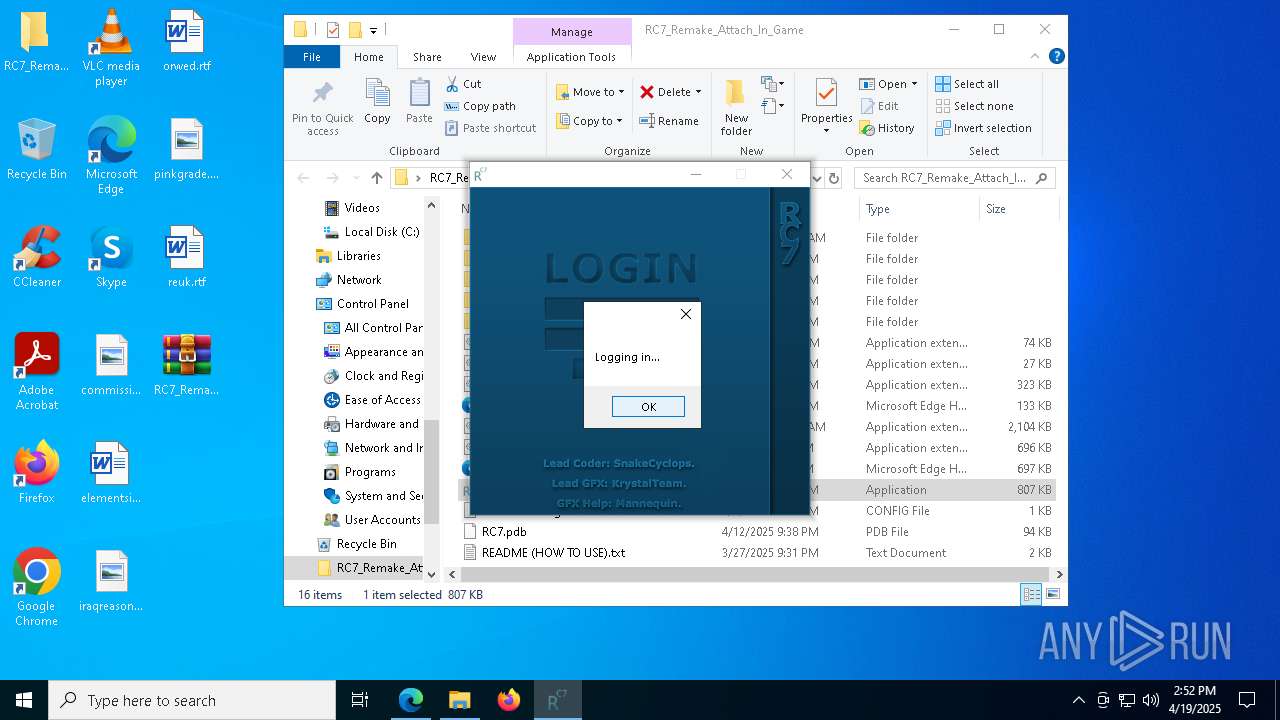
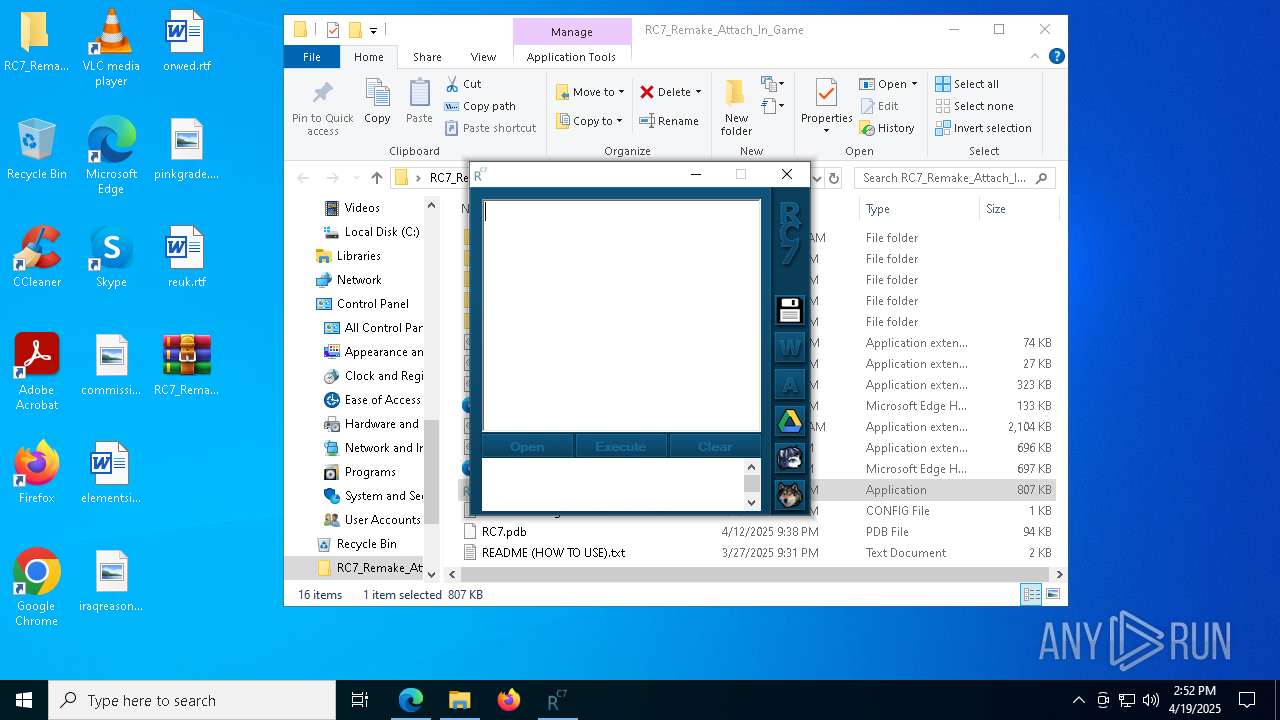
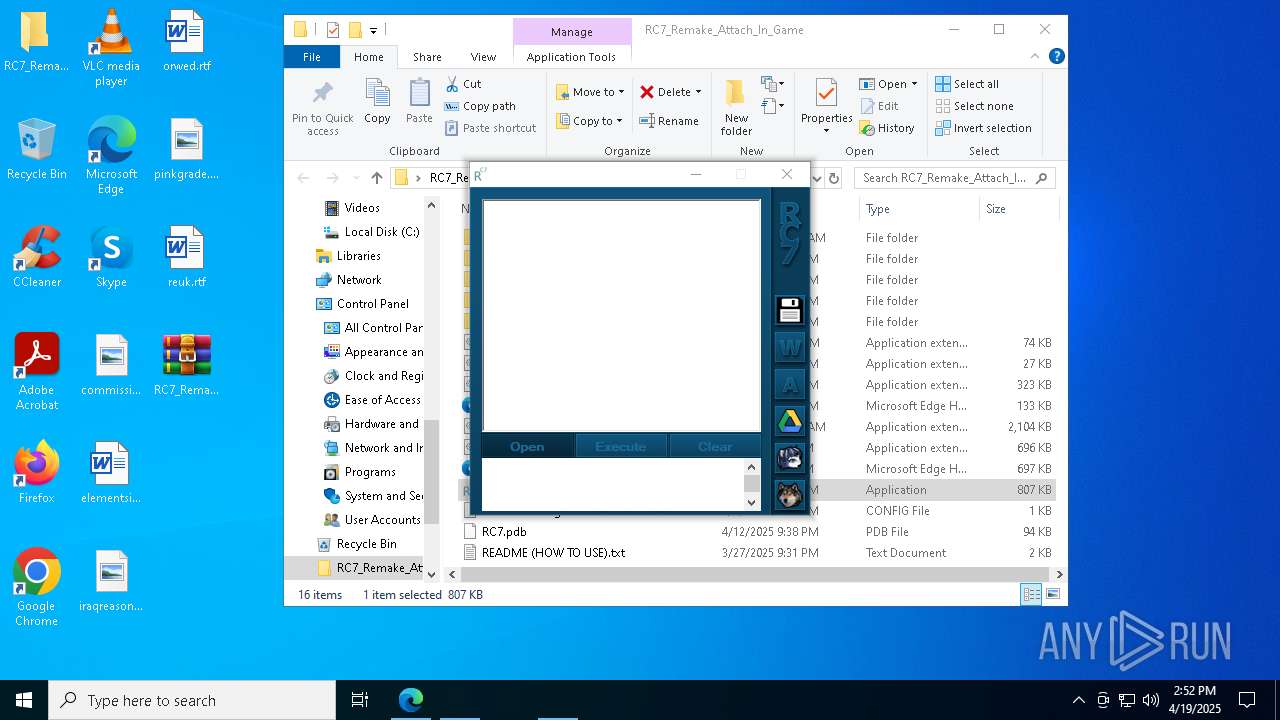
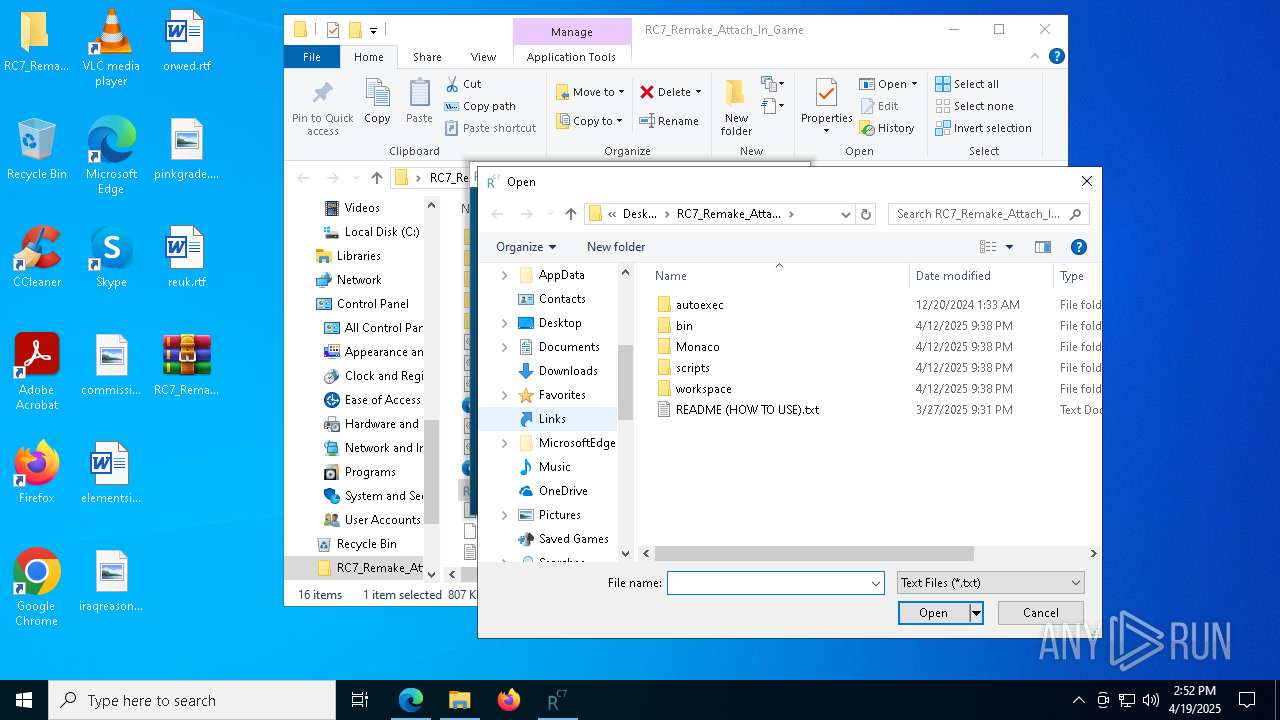
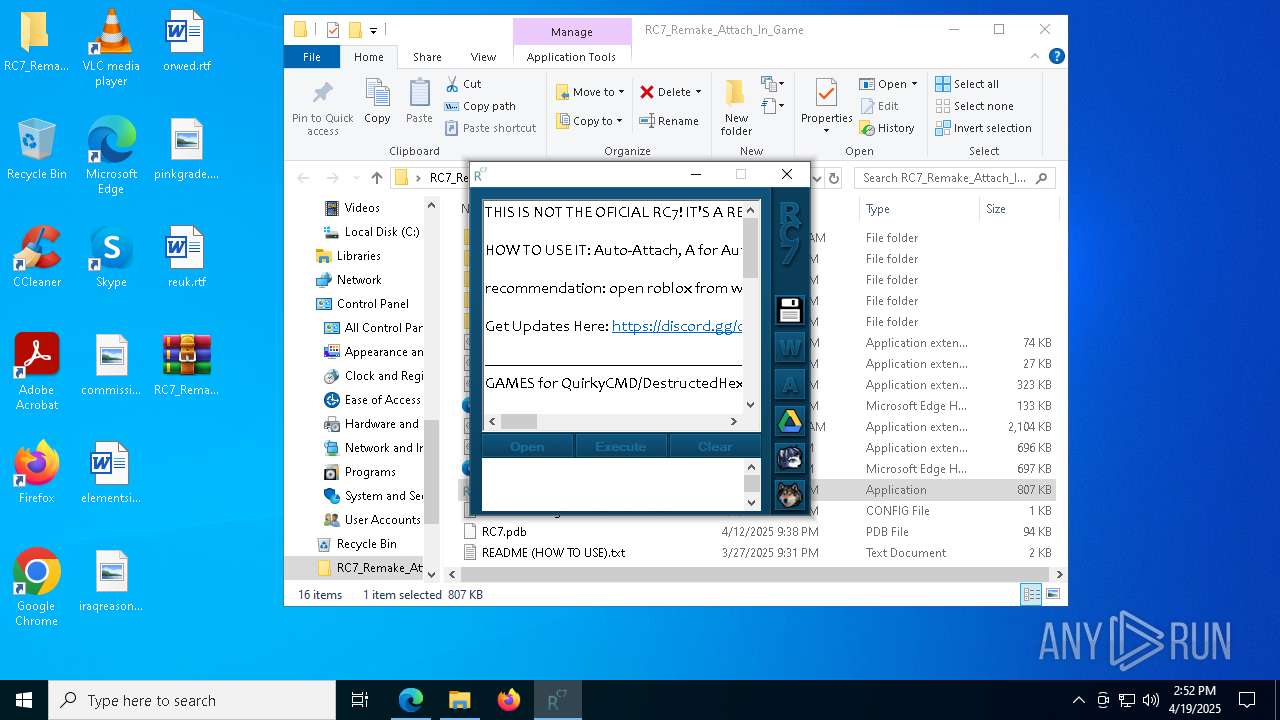
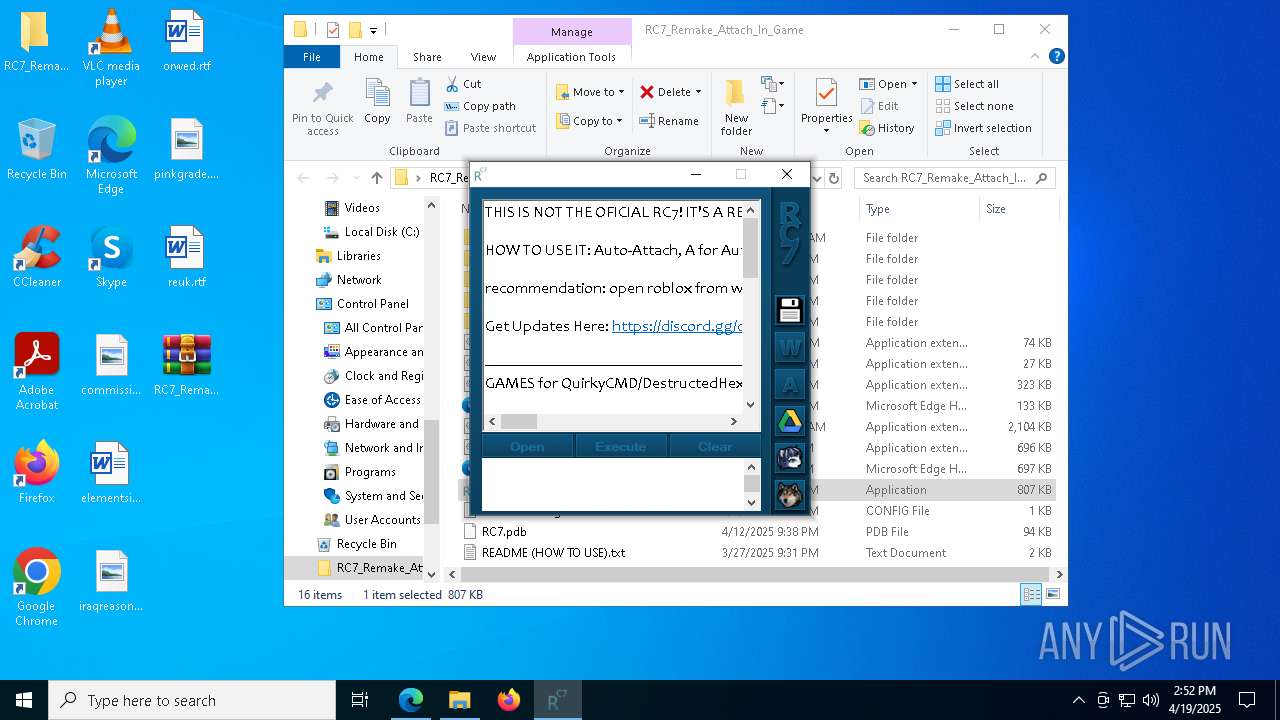
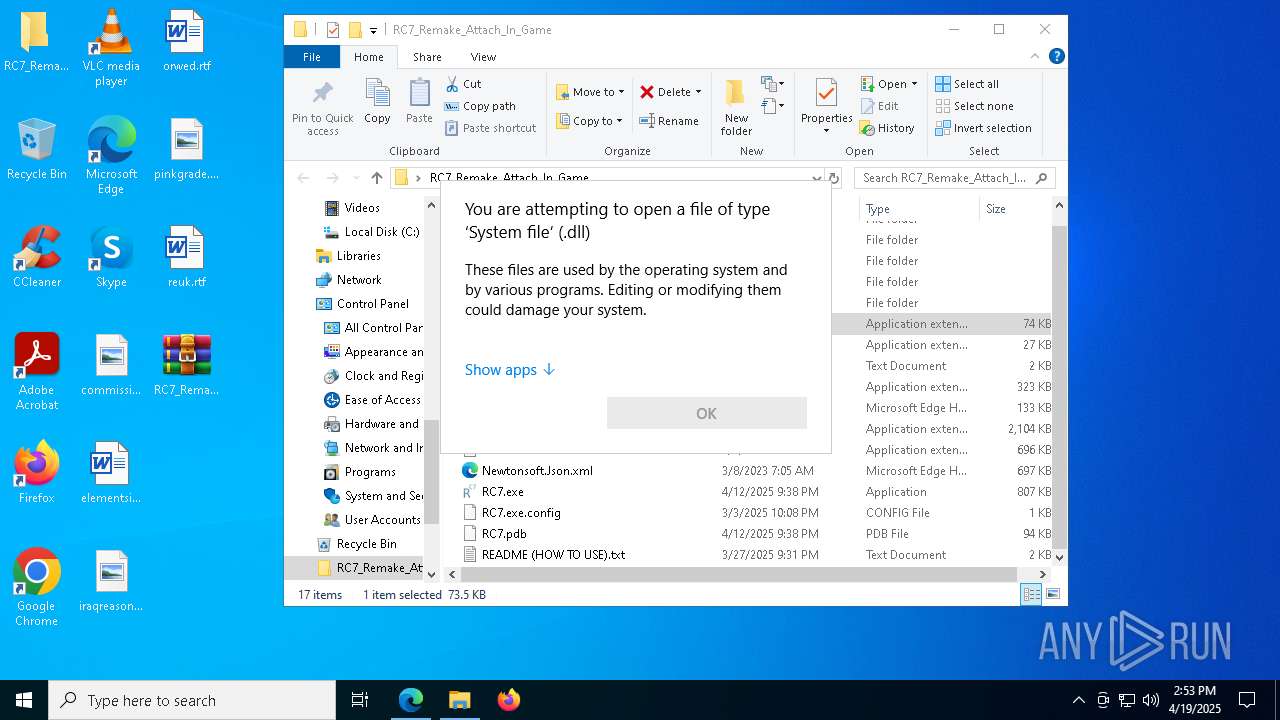
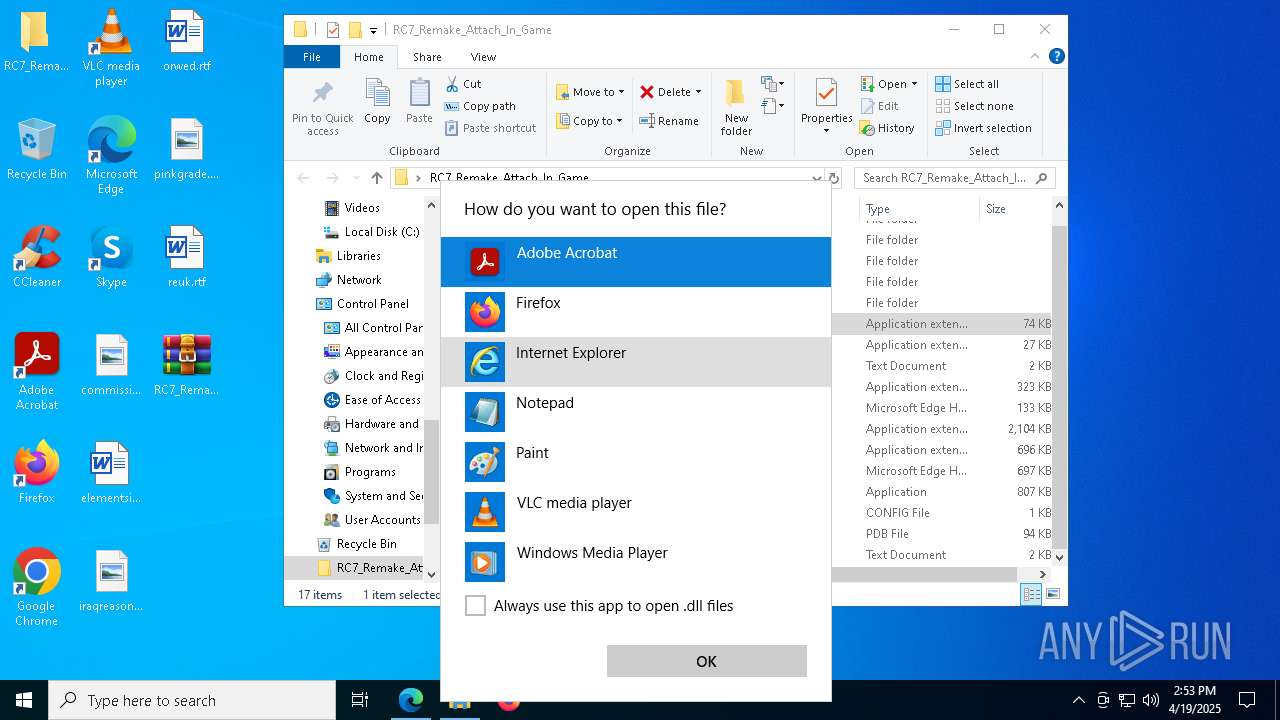
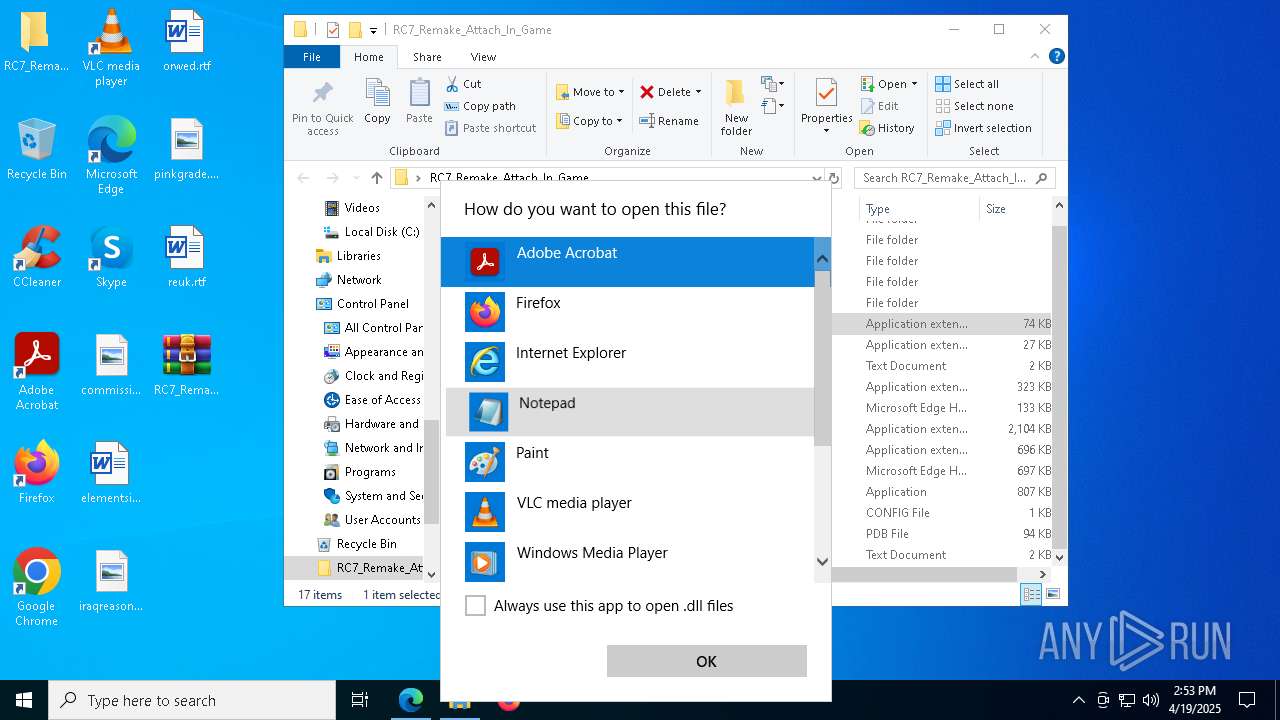
Manual execution by a user
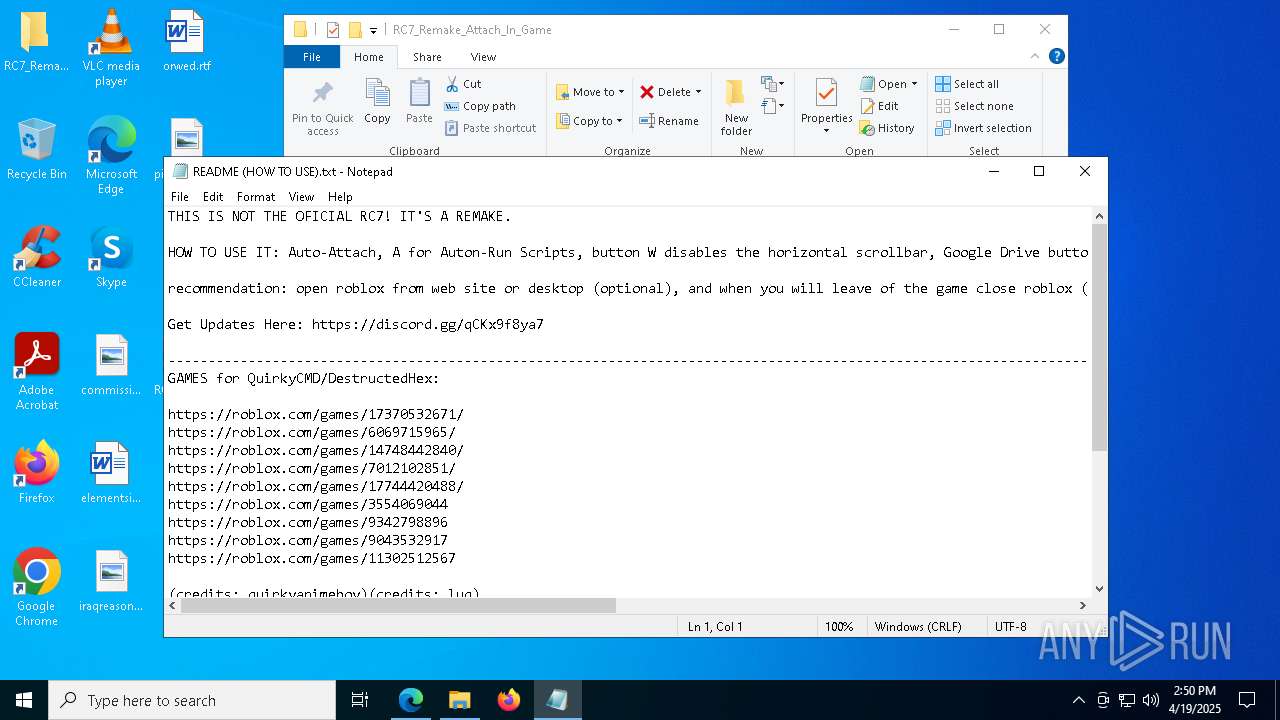
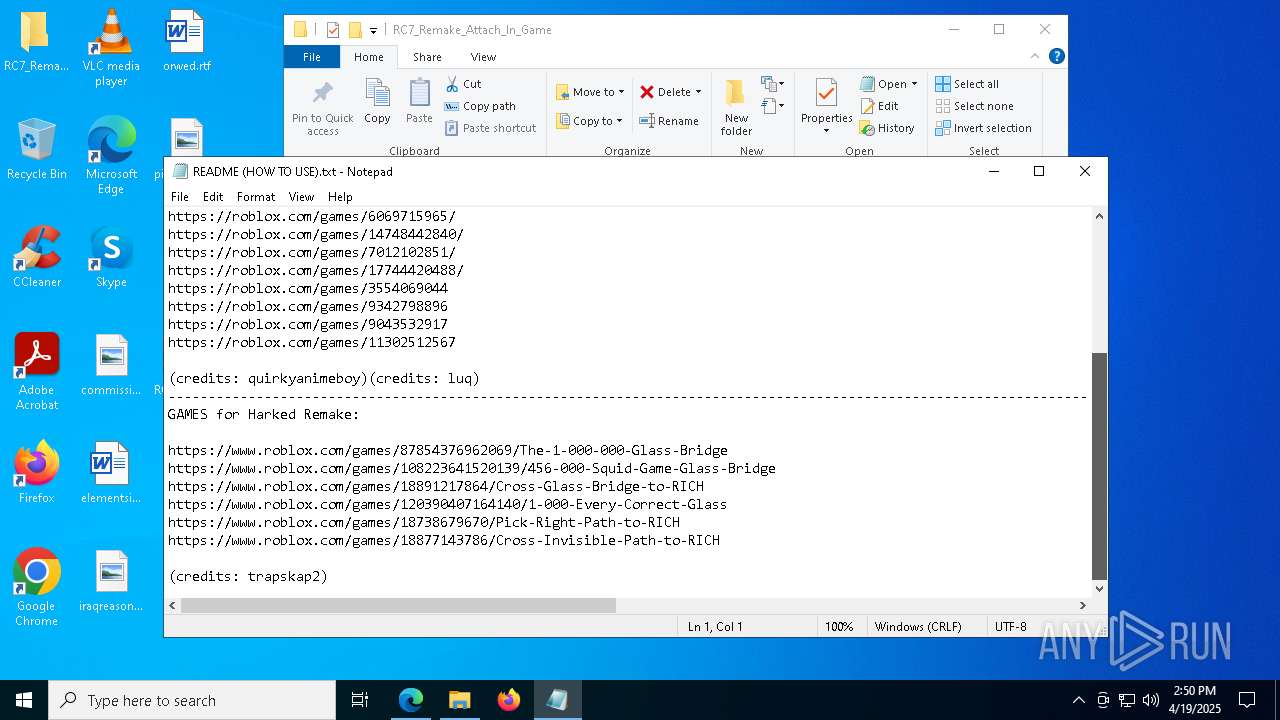
- RC7.exe (PID: 4200)
- notepad.exe (PID: 8068)
- RC7.exe (PID: 7744)
- msedge.exe (PID: 7484)
- RC7.exe (PID: 7584)
- RC7.exe (PID: 2504)
- RC7.exe (PID: 7724)
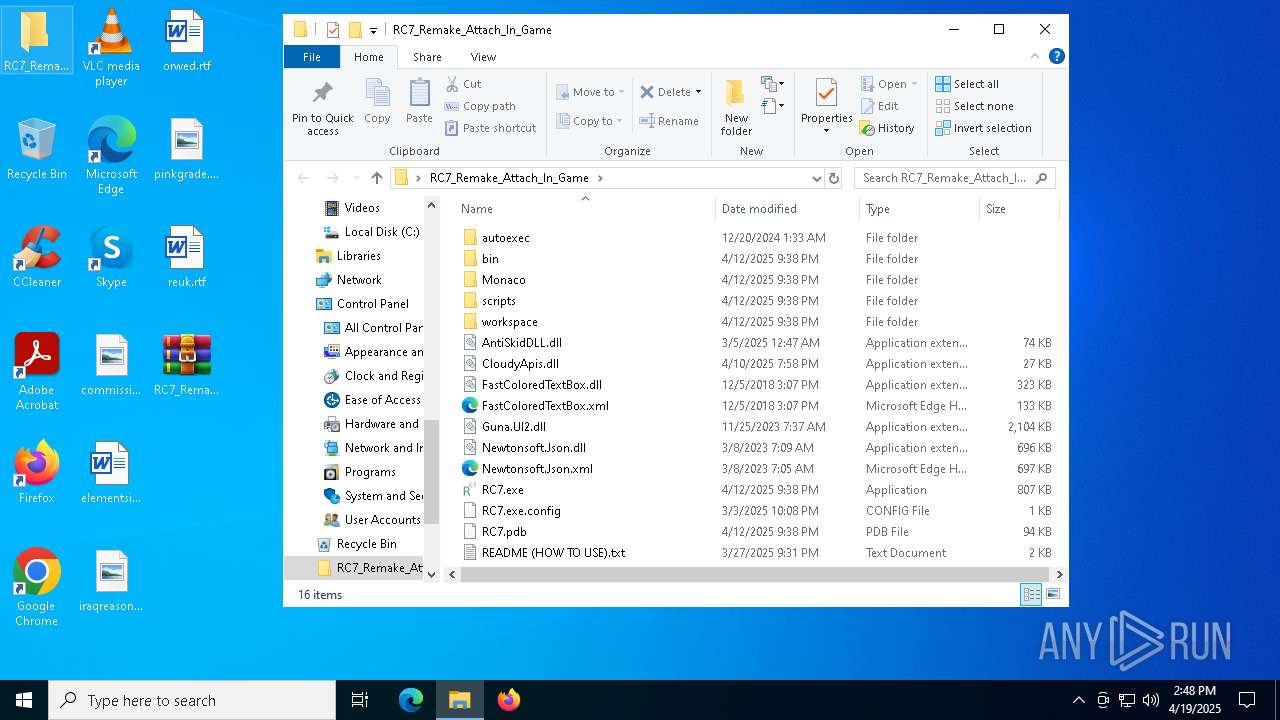
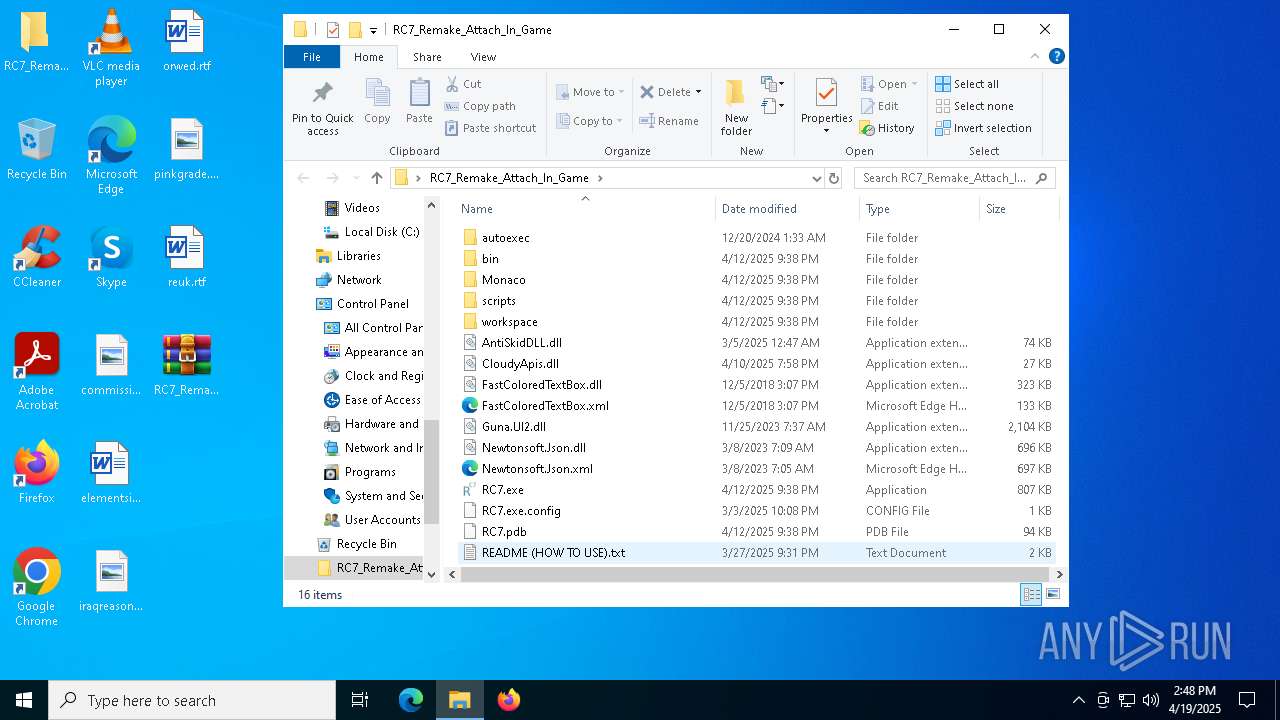
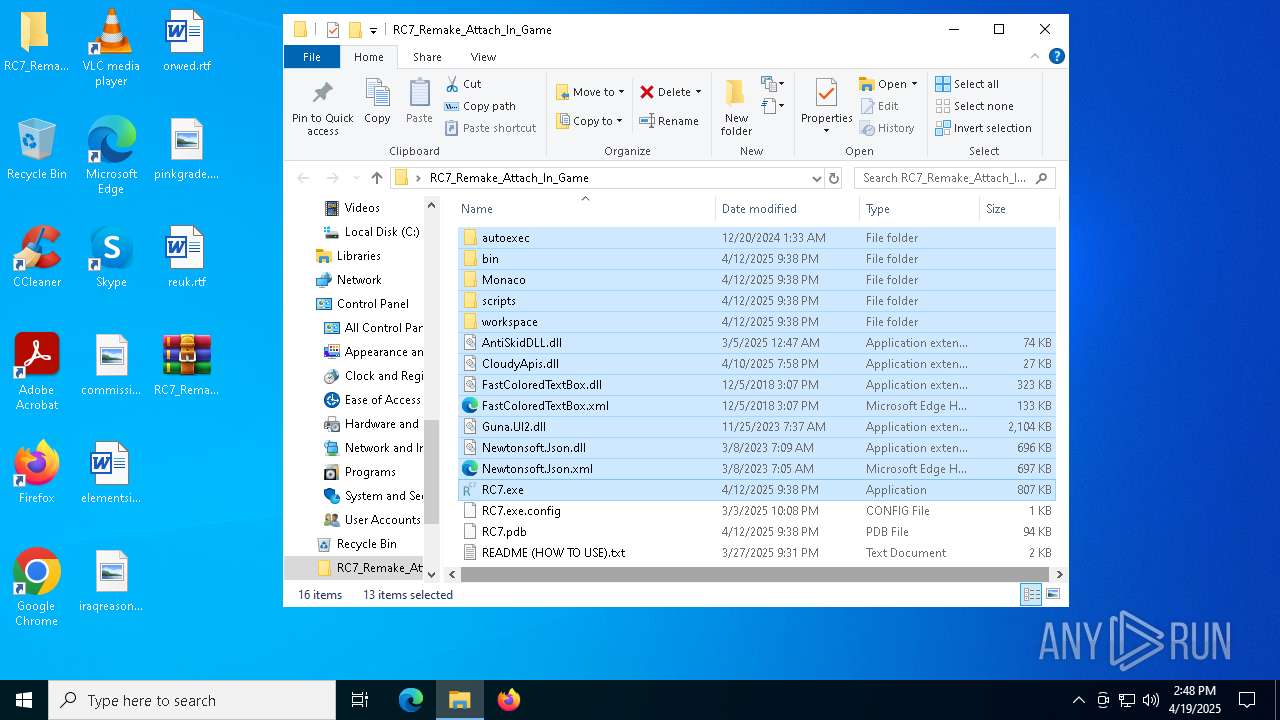
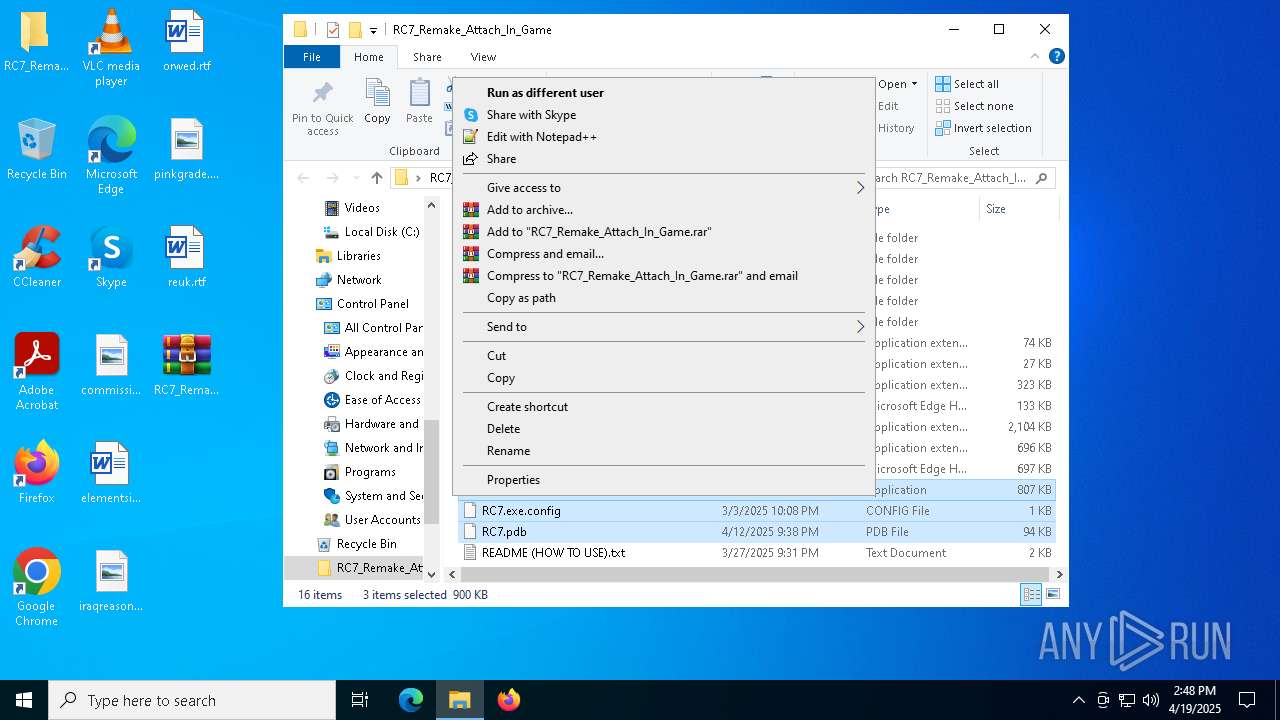
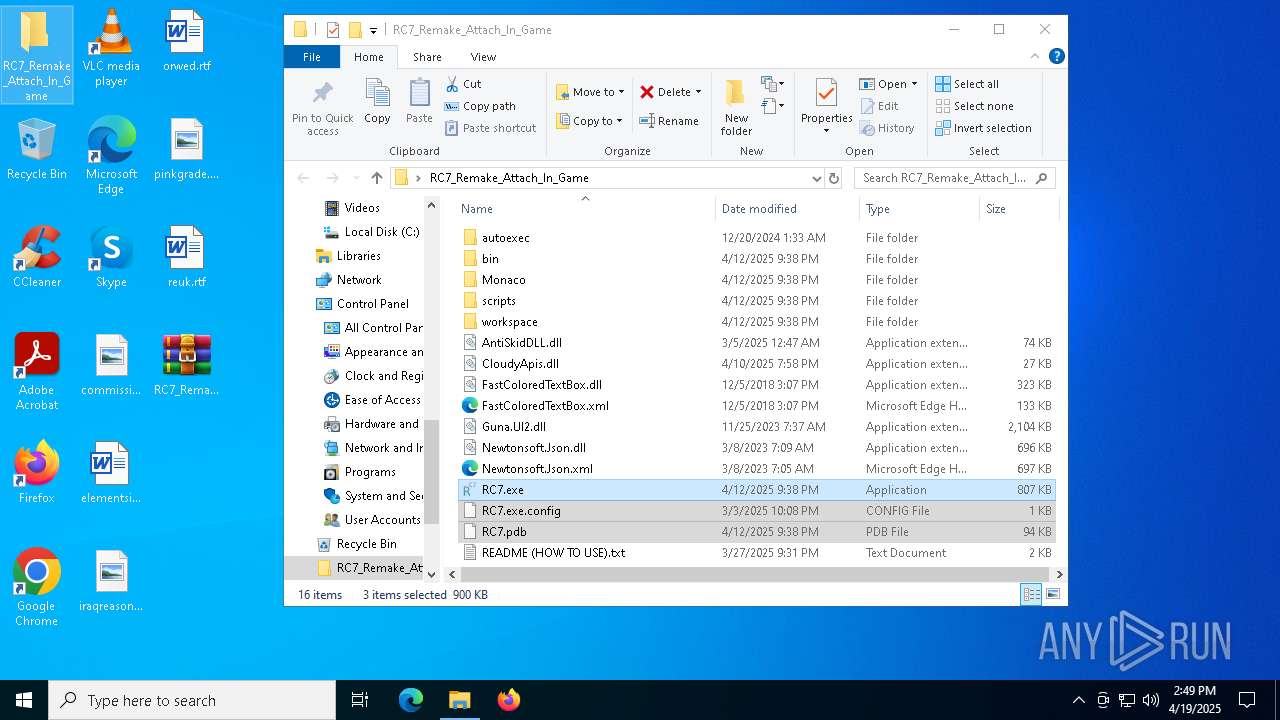
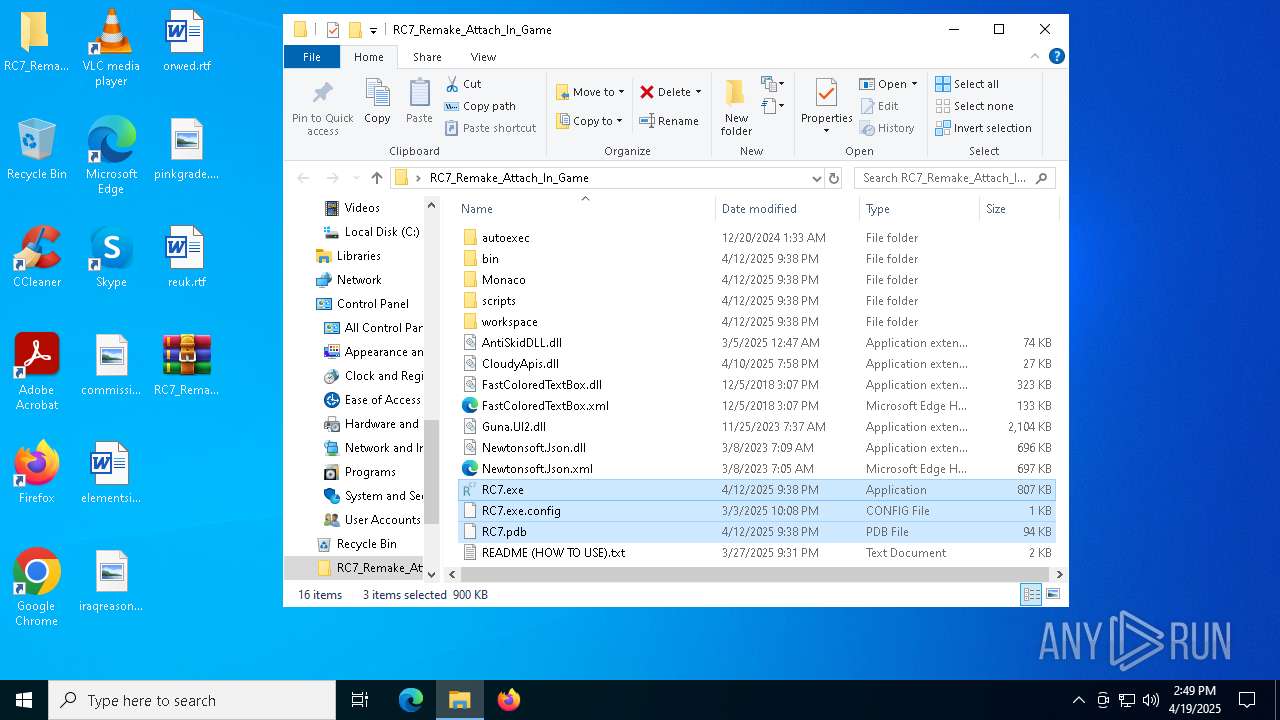
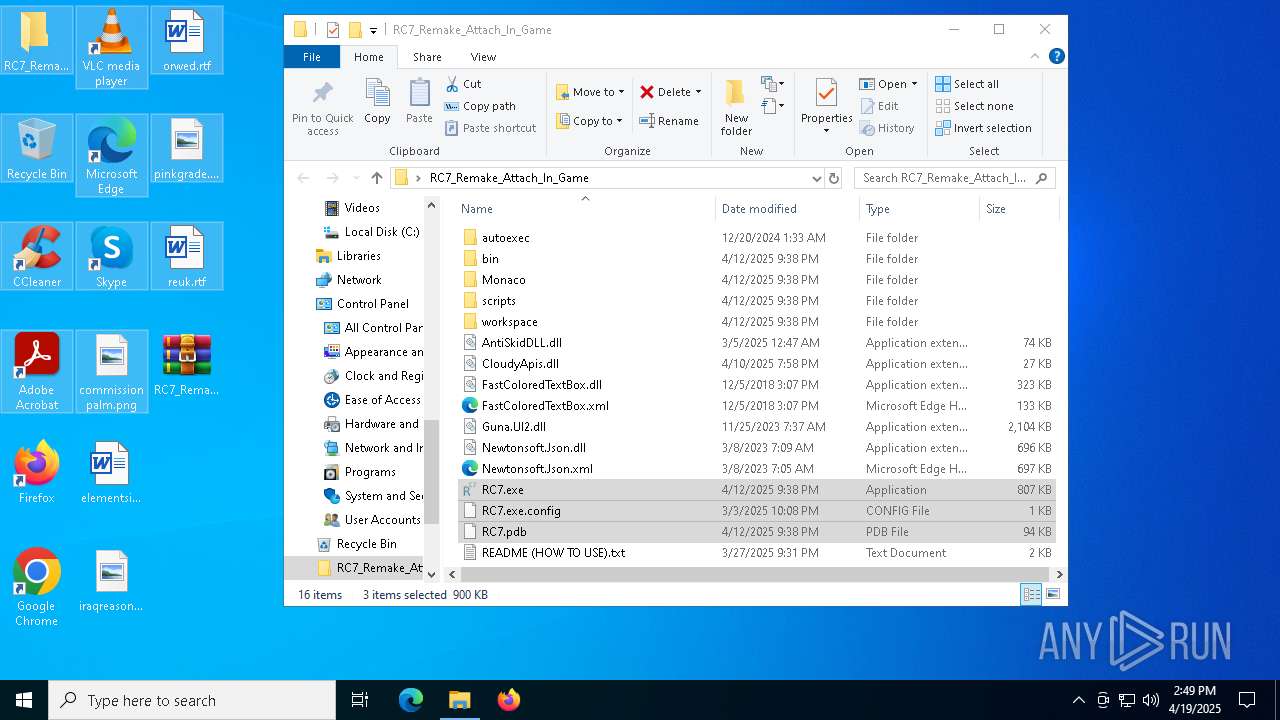
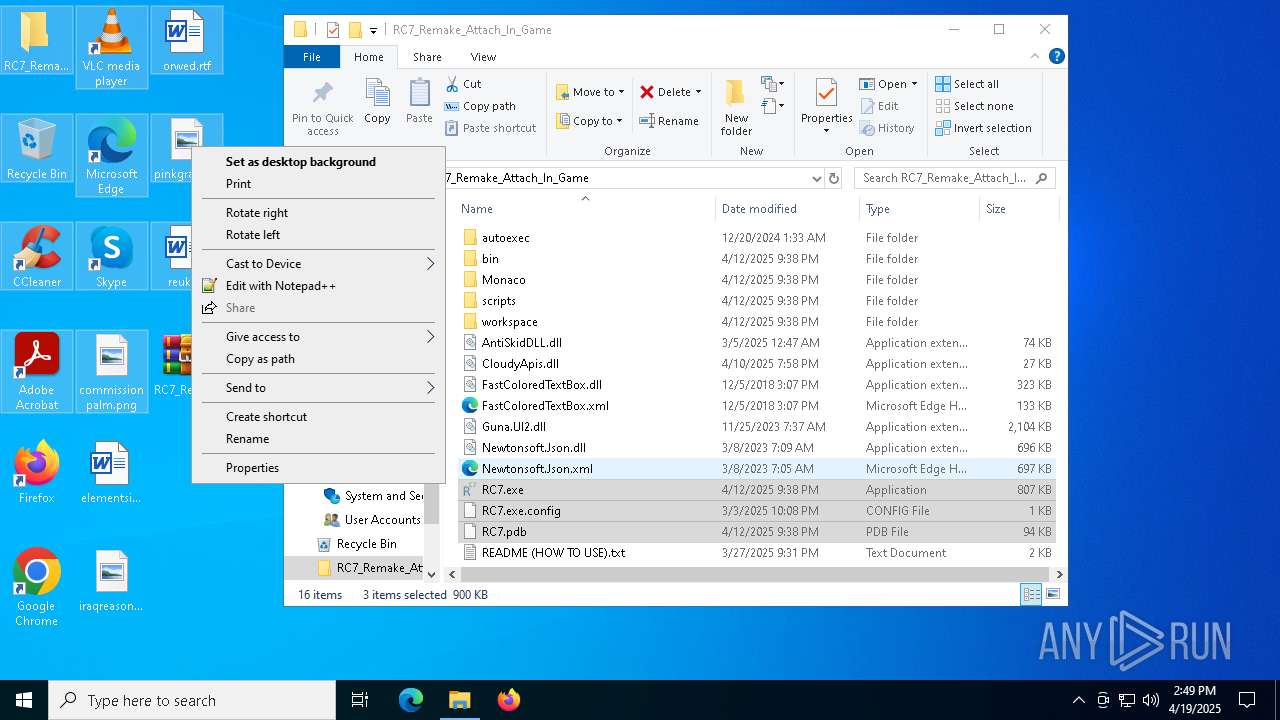
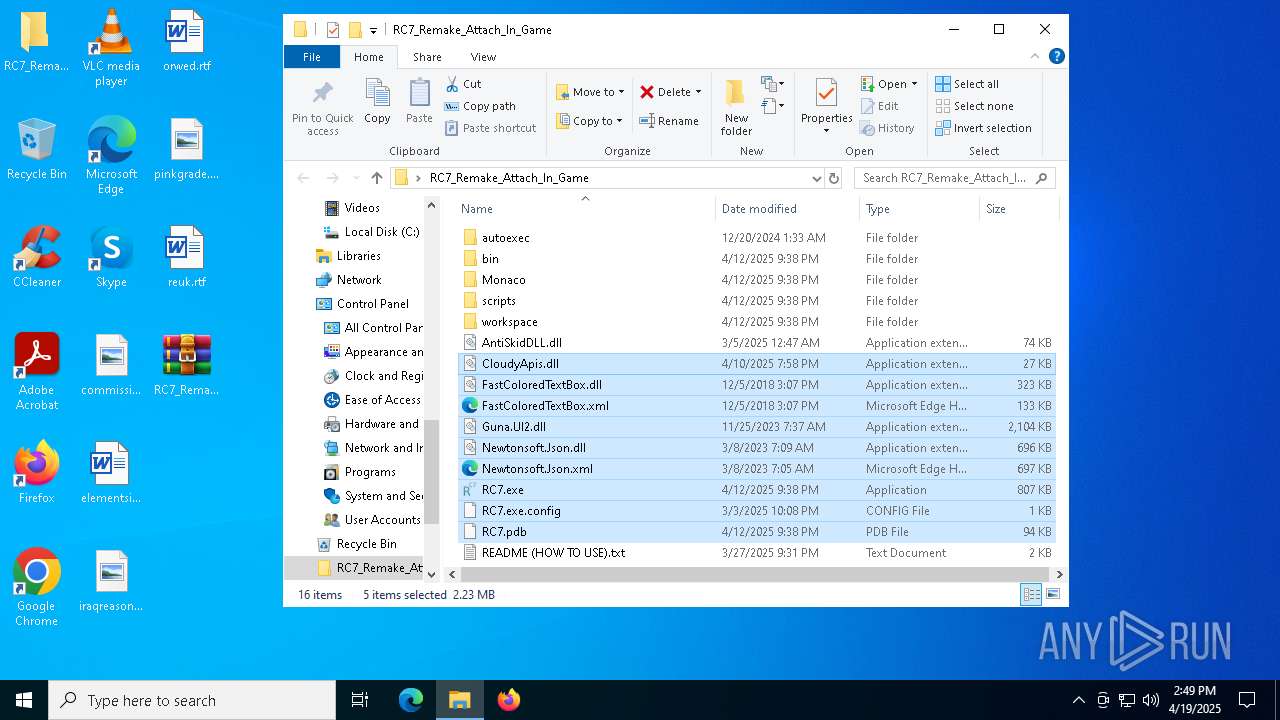
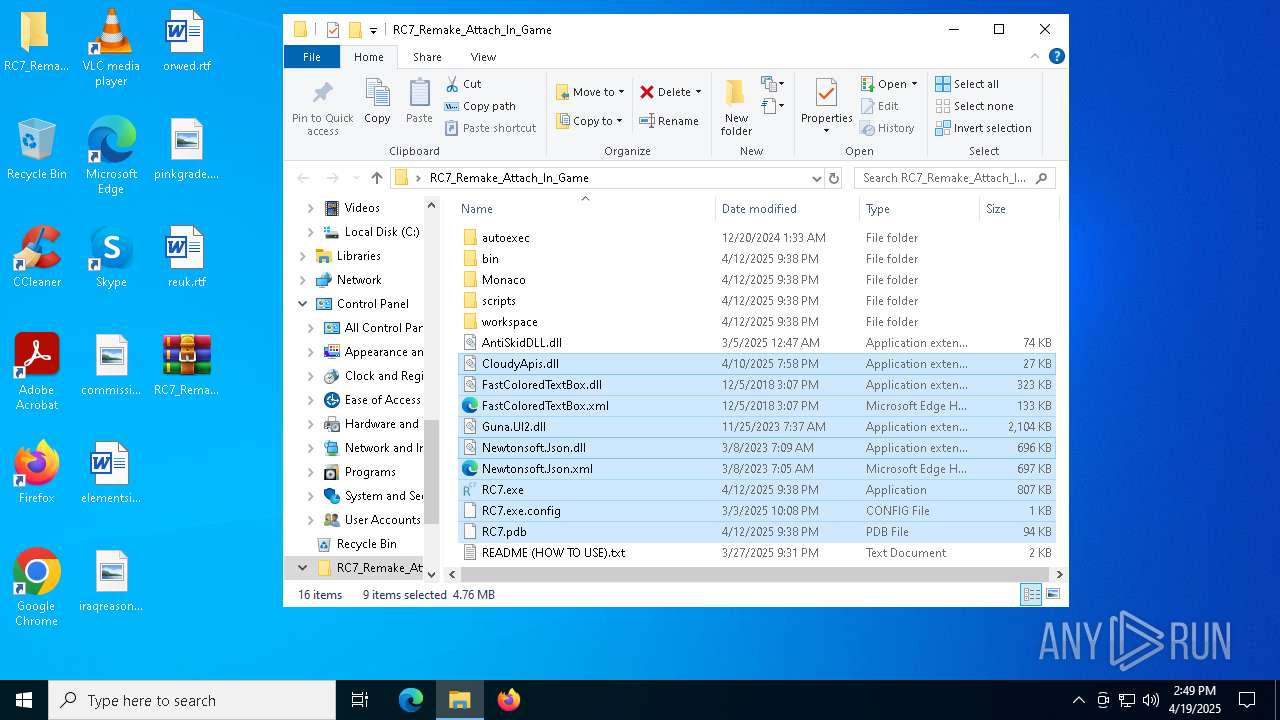
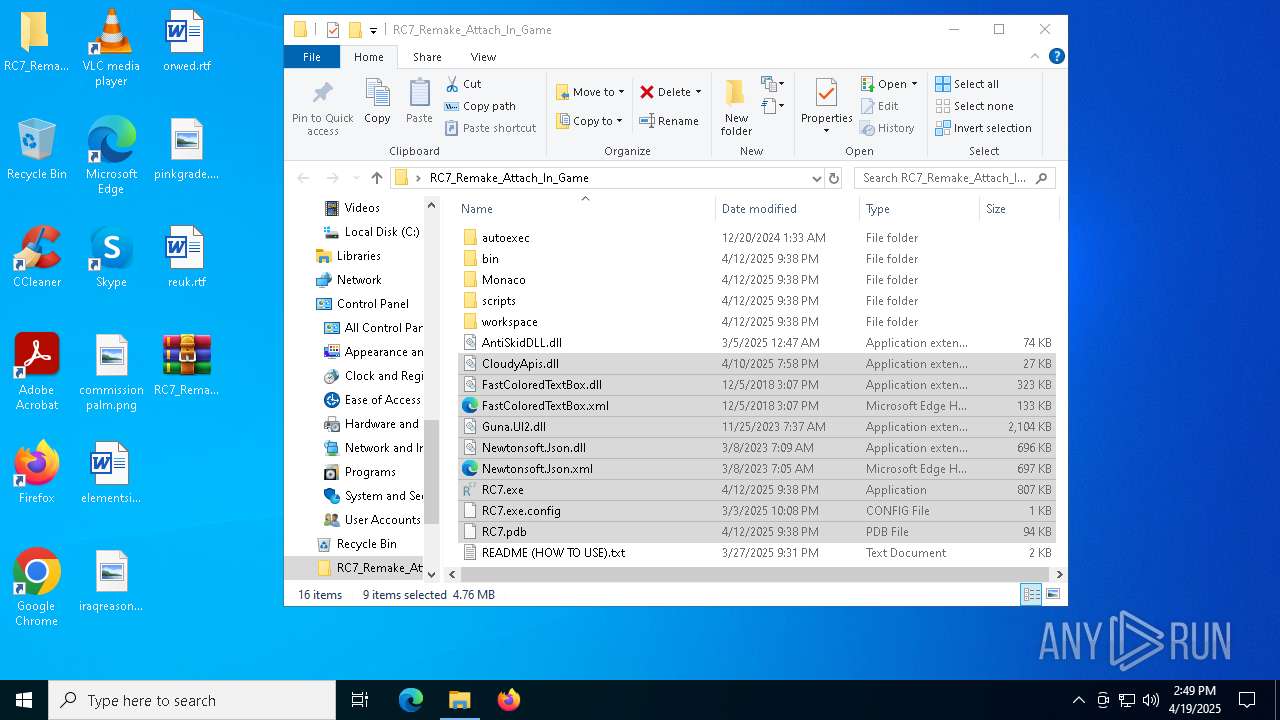
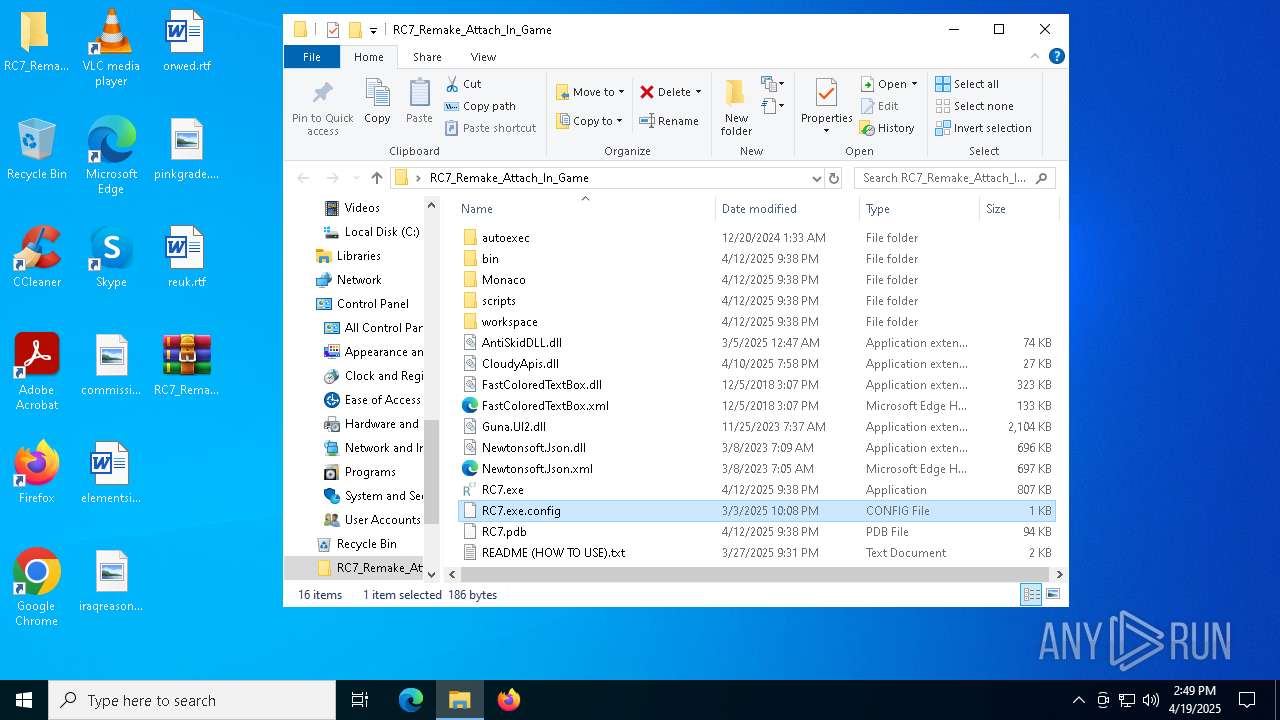
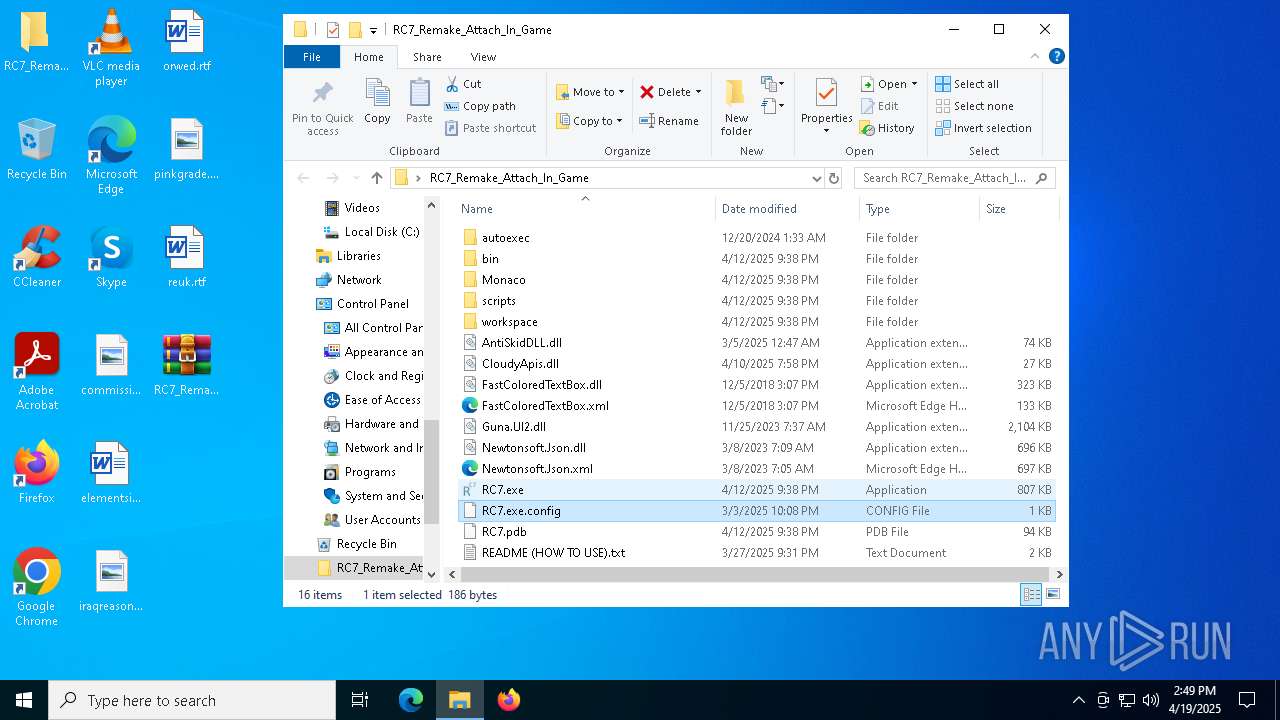
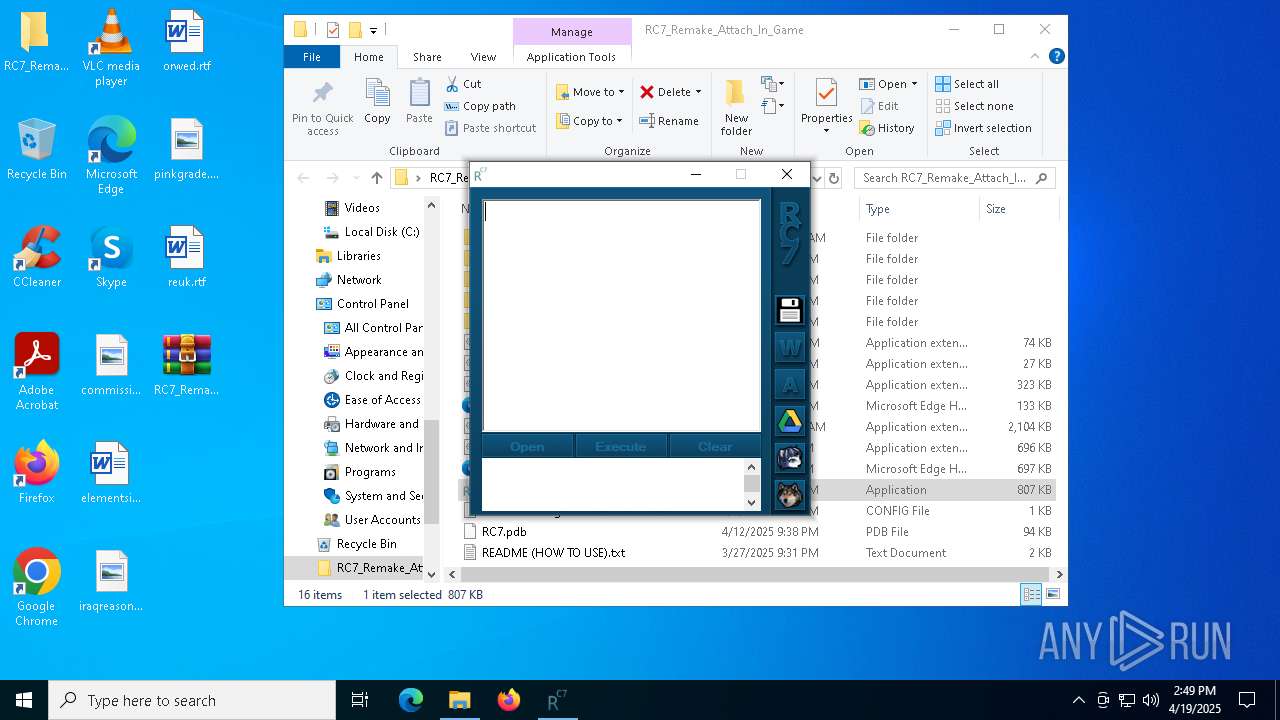
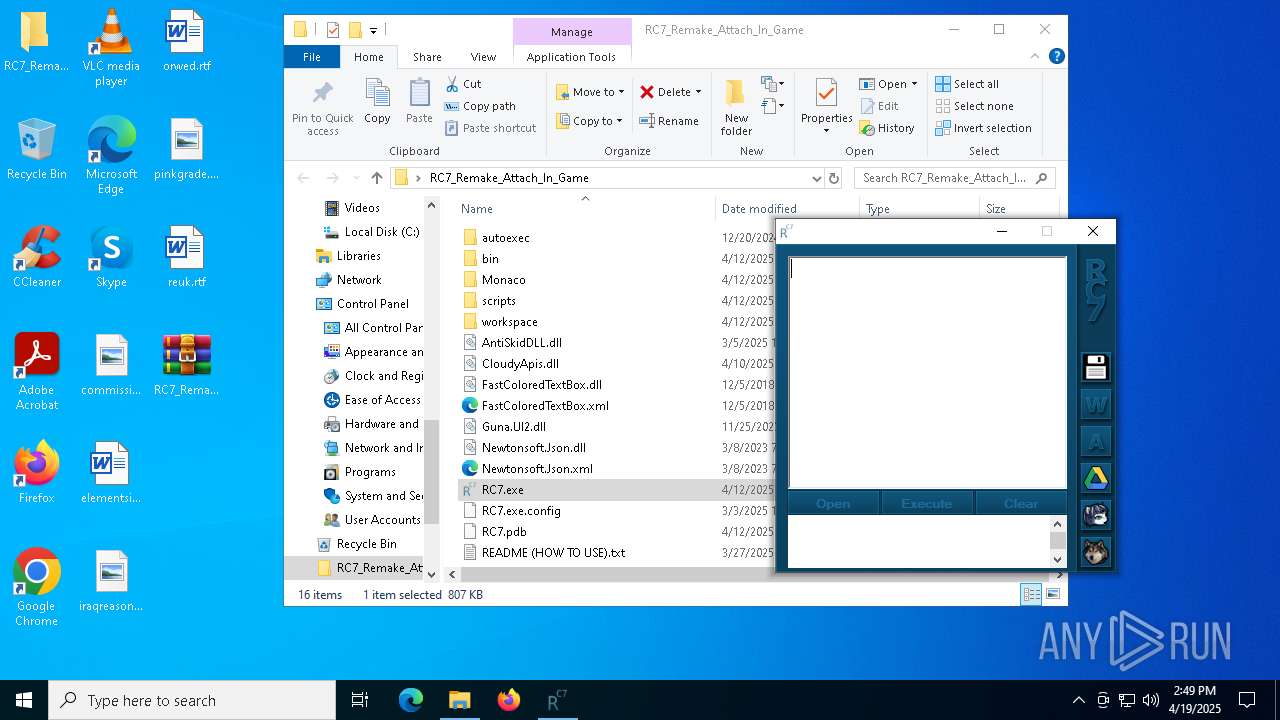
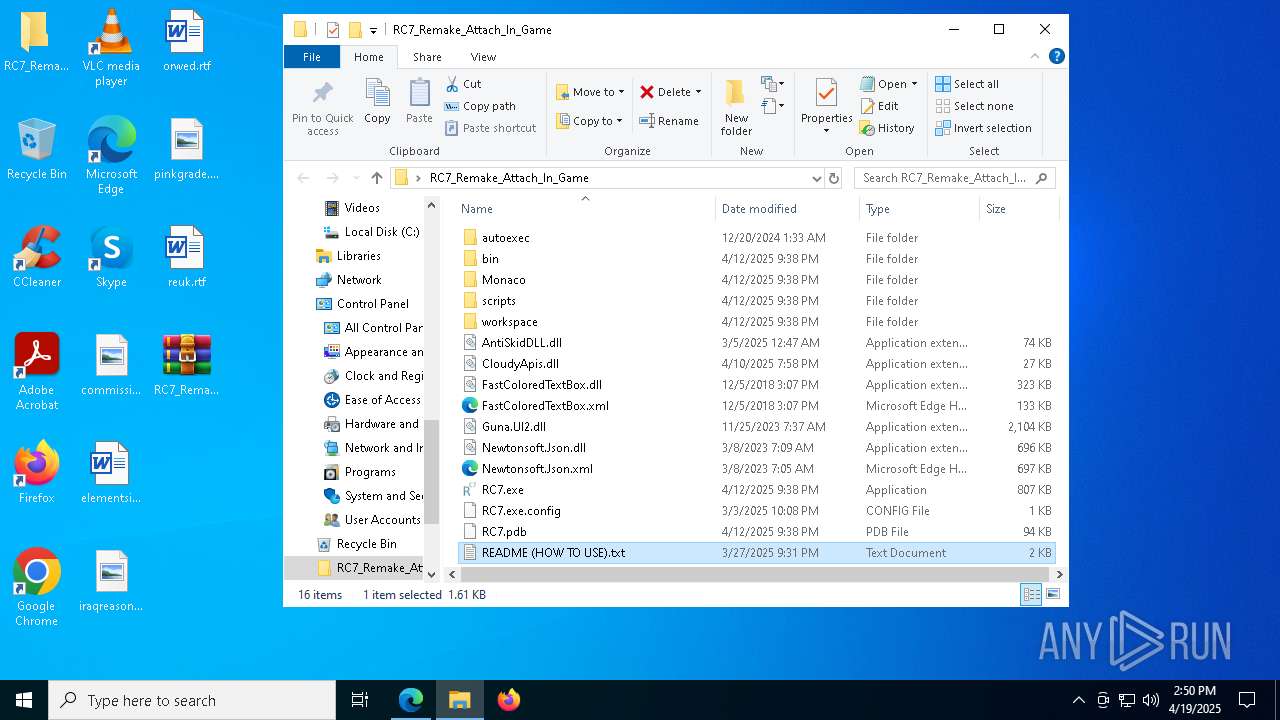
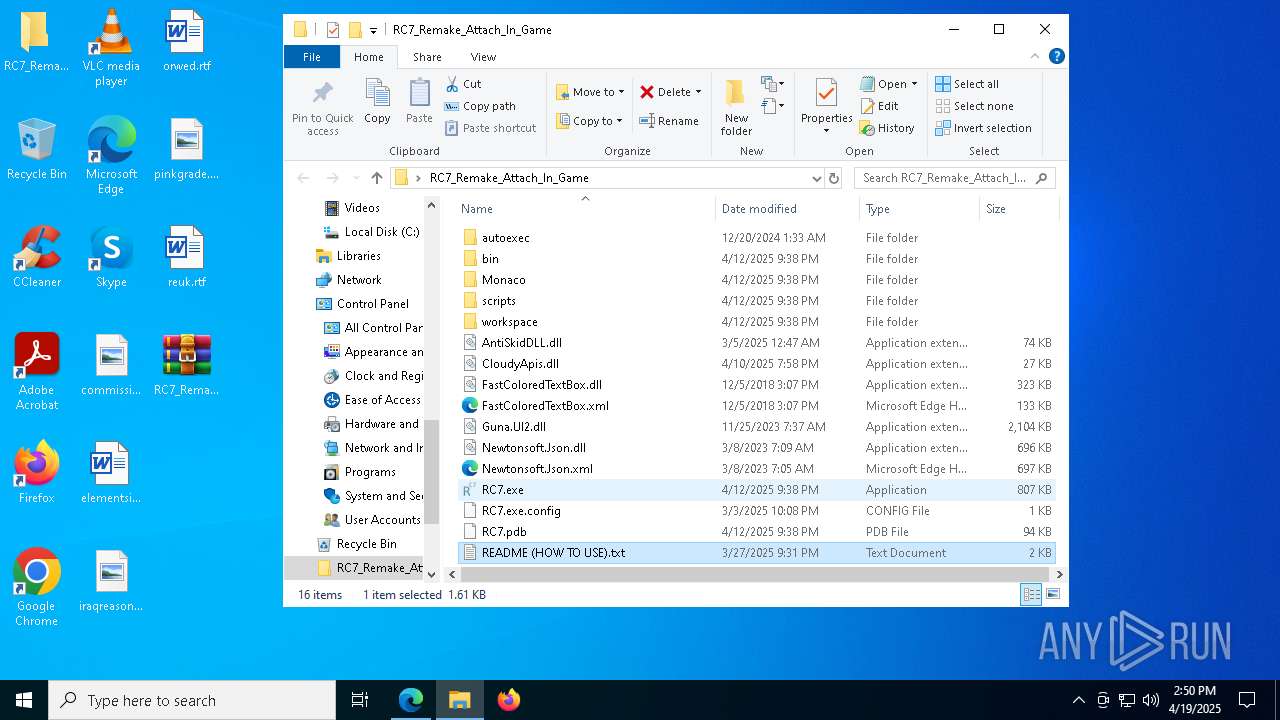
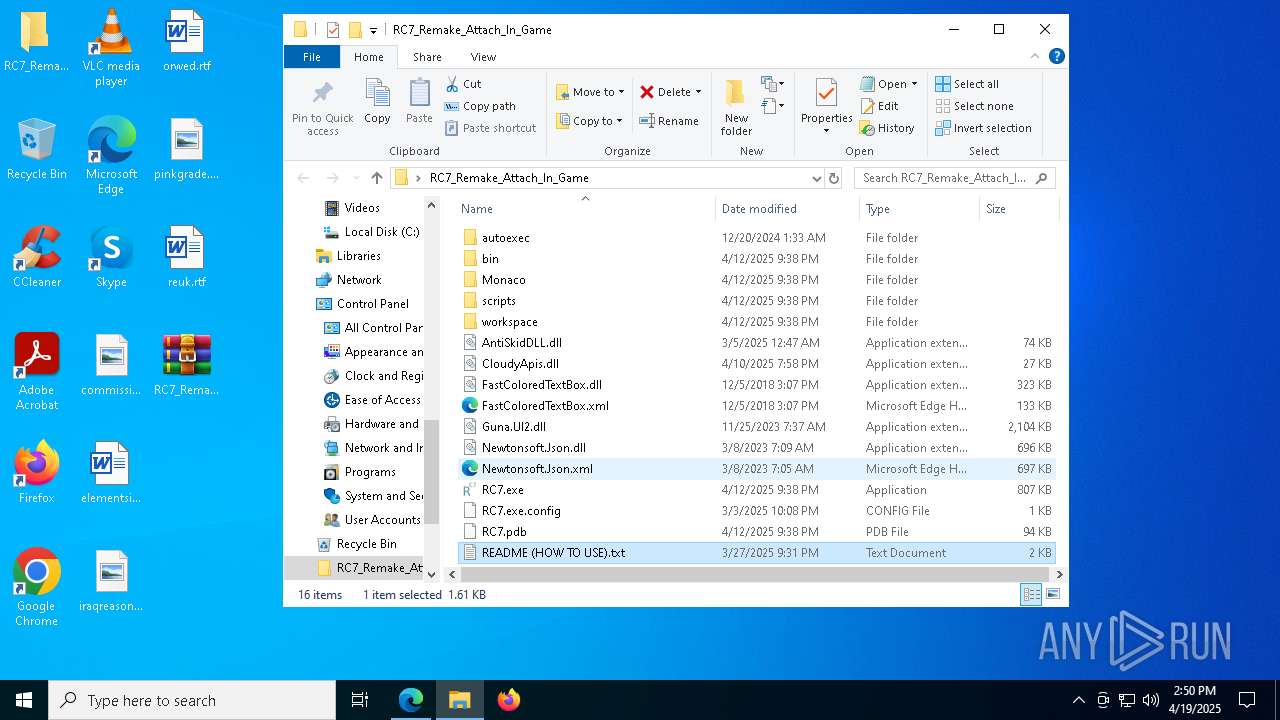
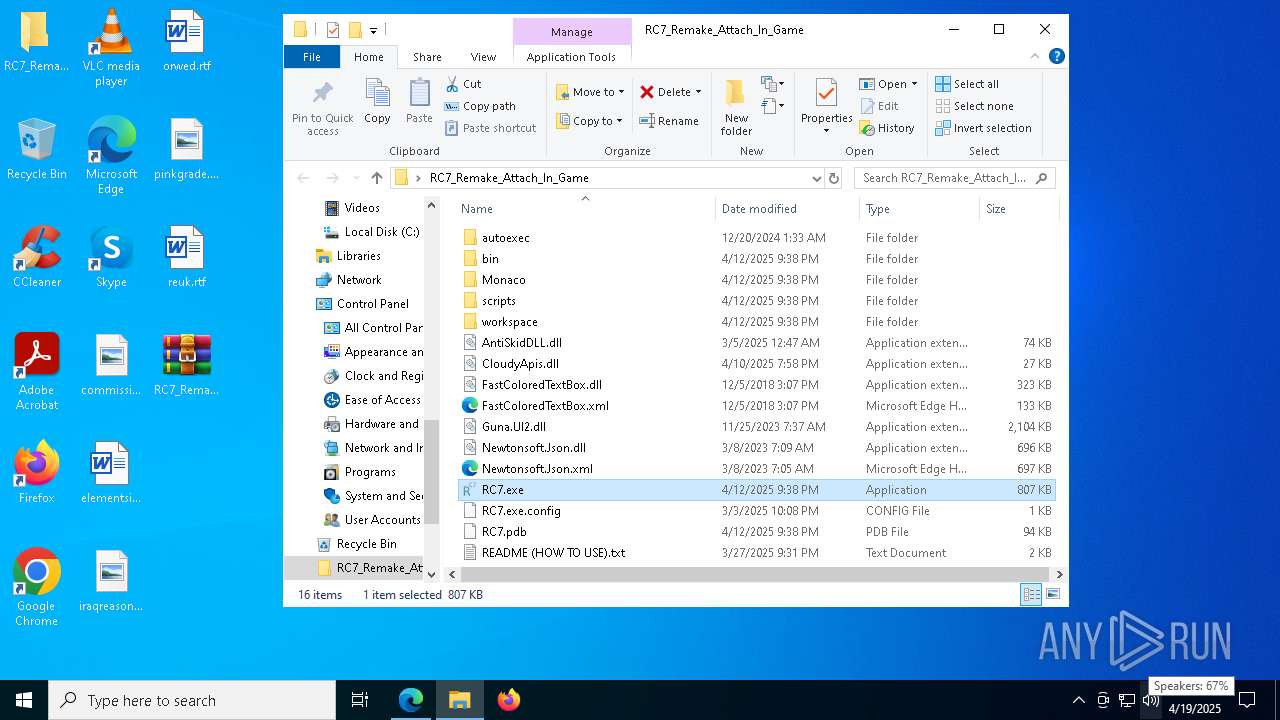
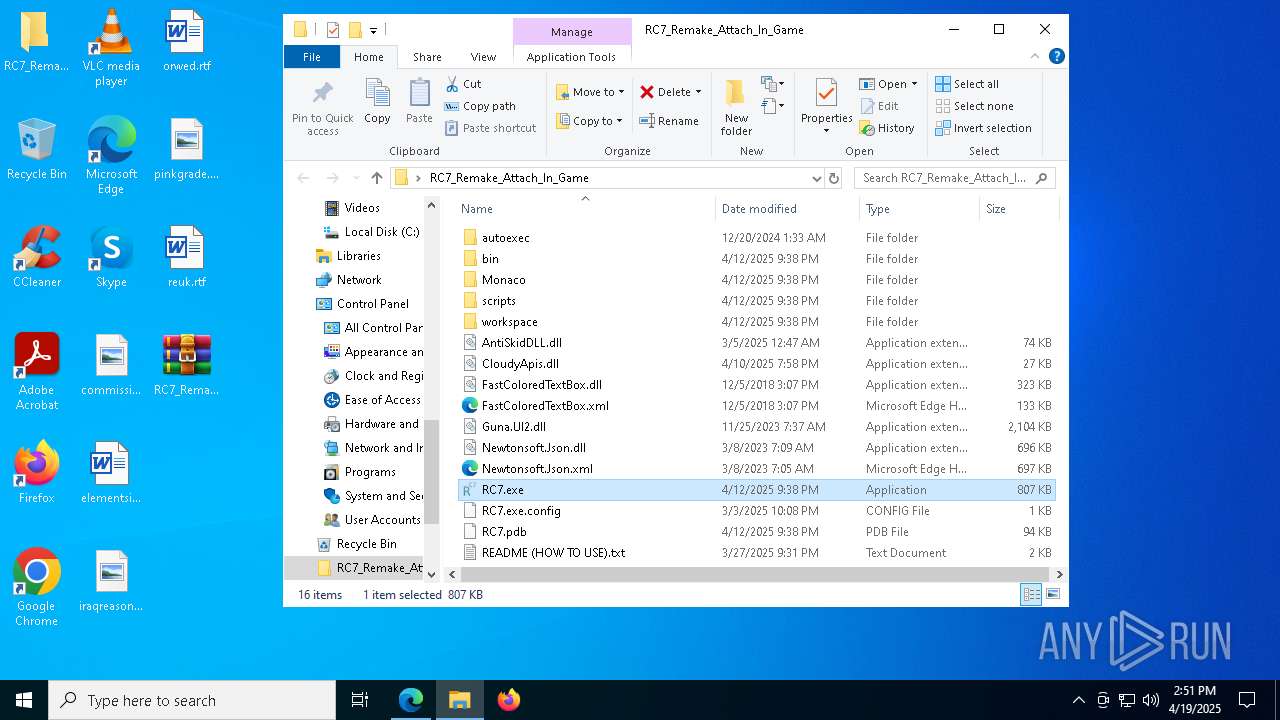
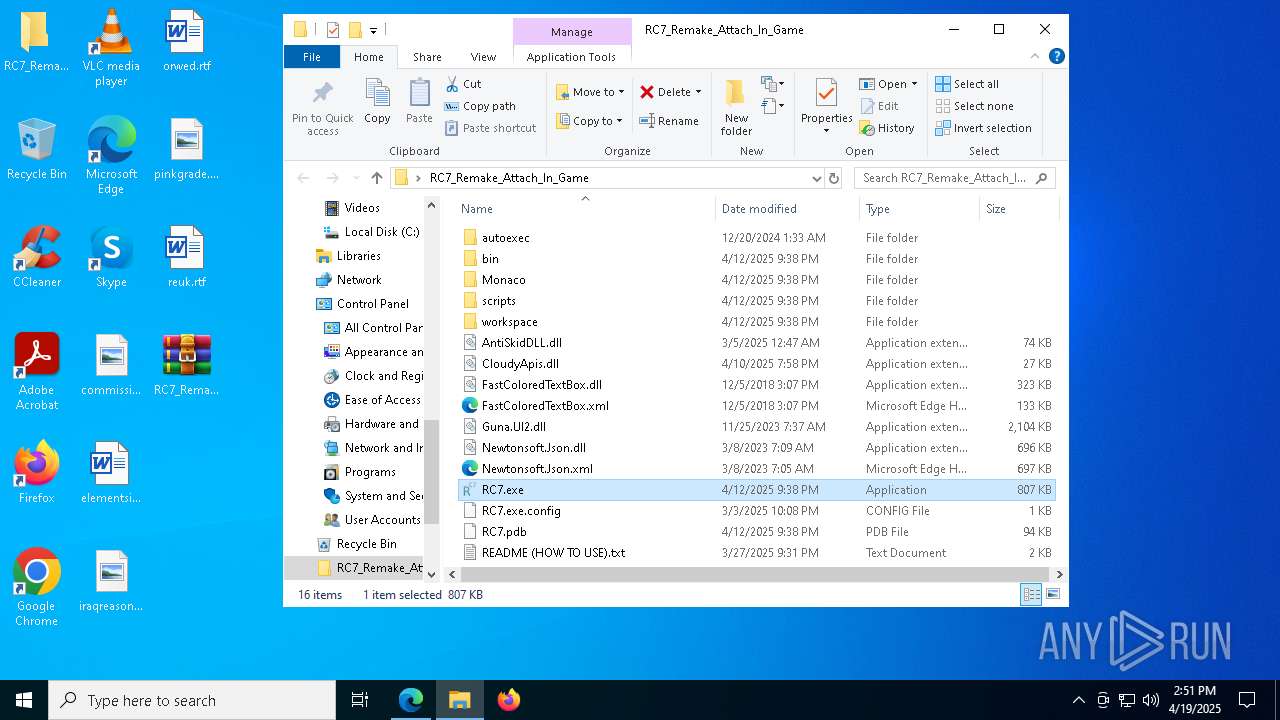
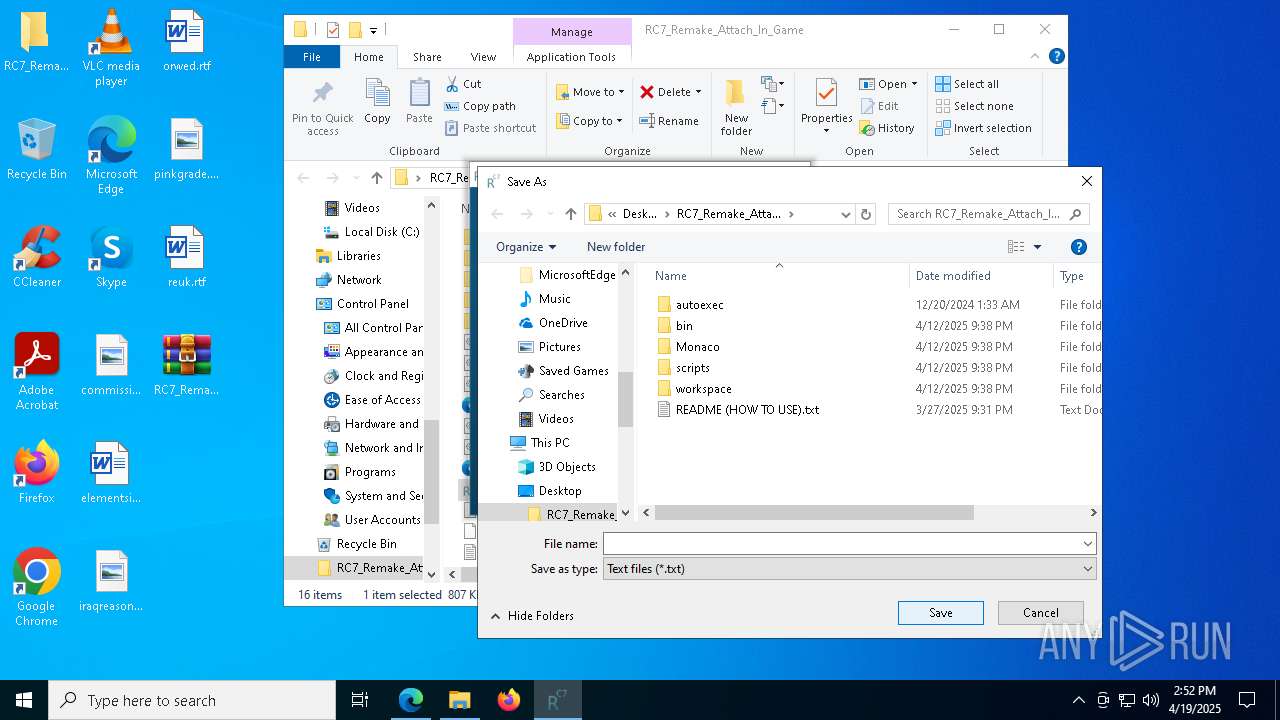
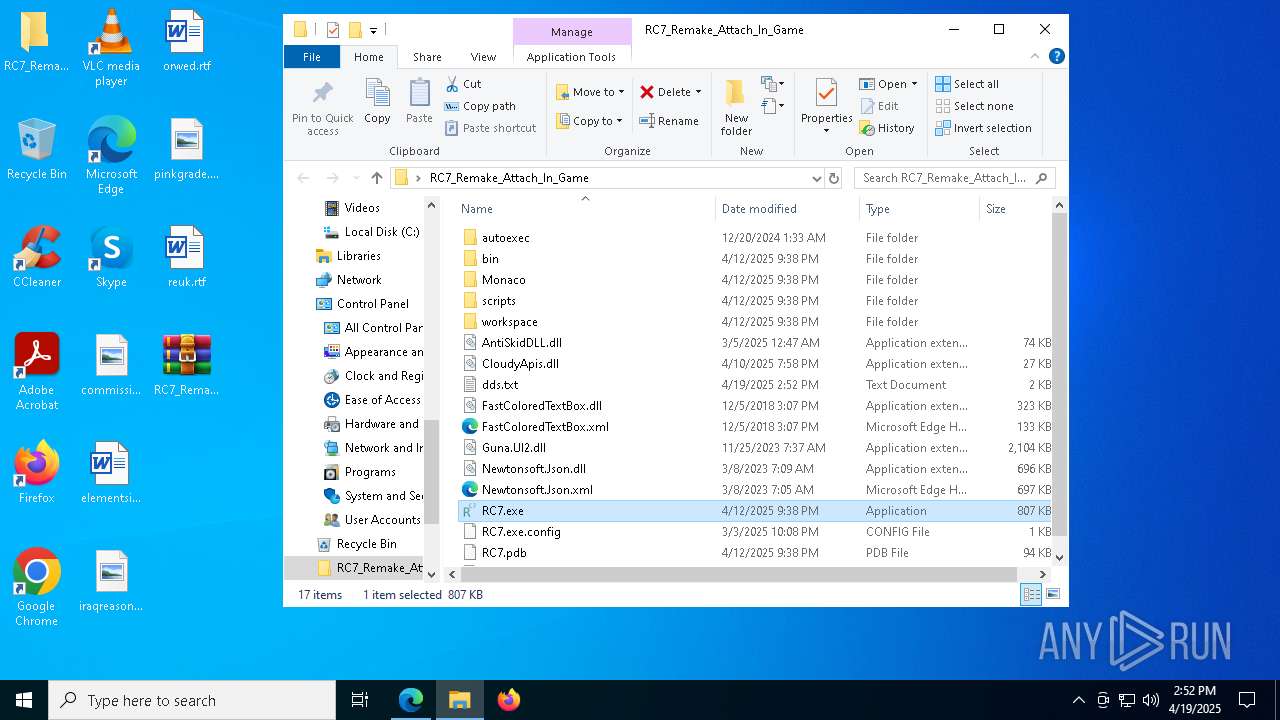
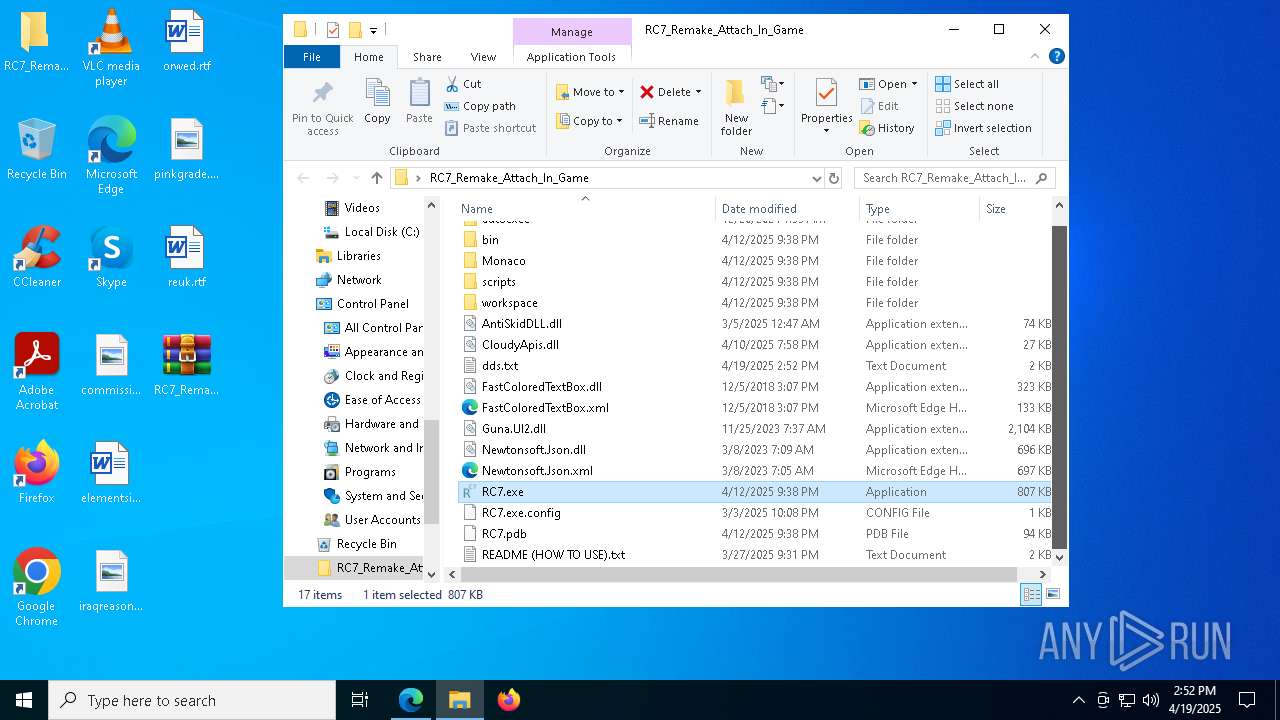
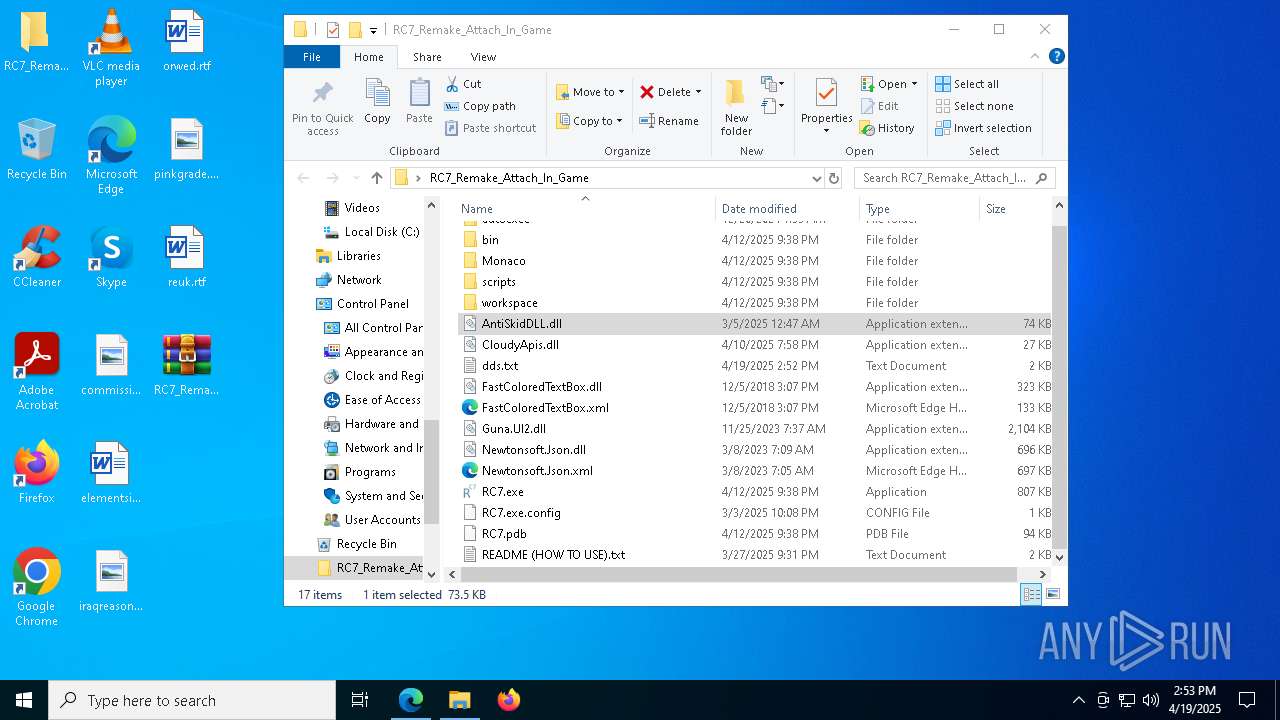
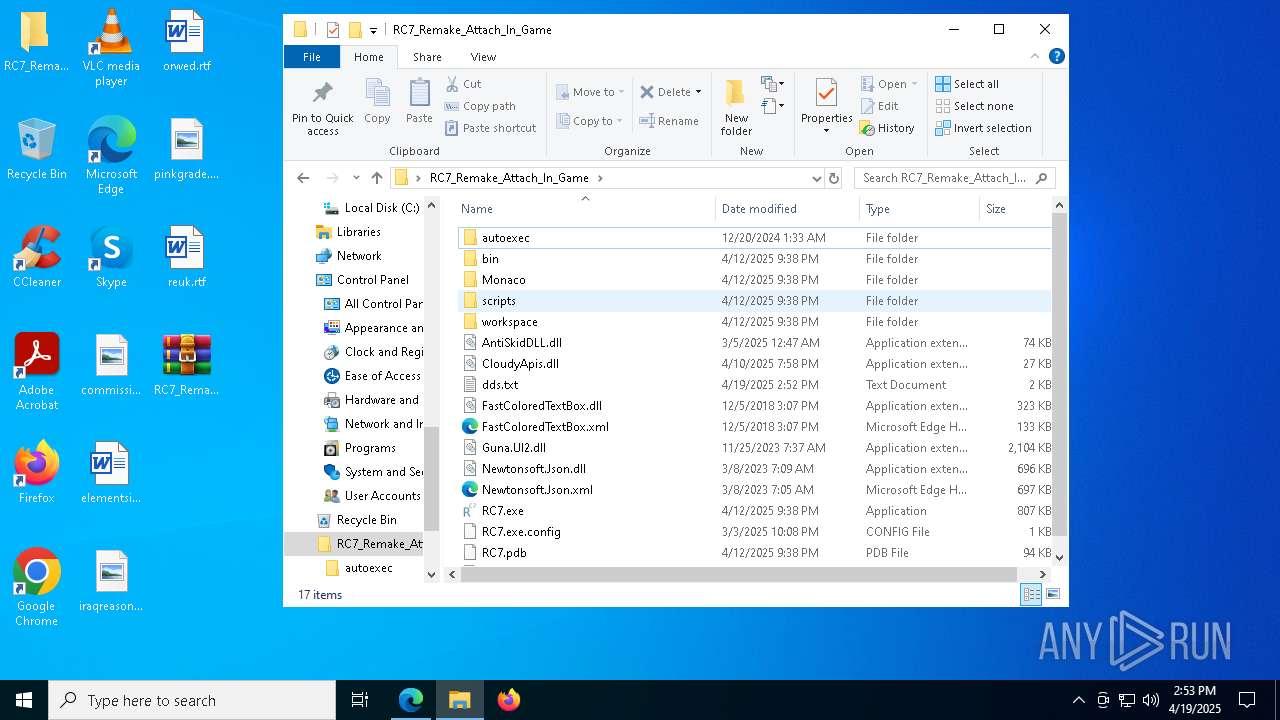
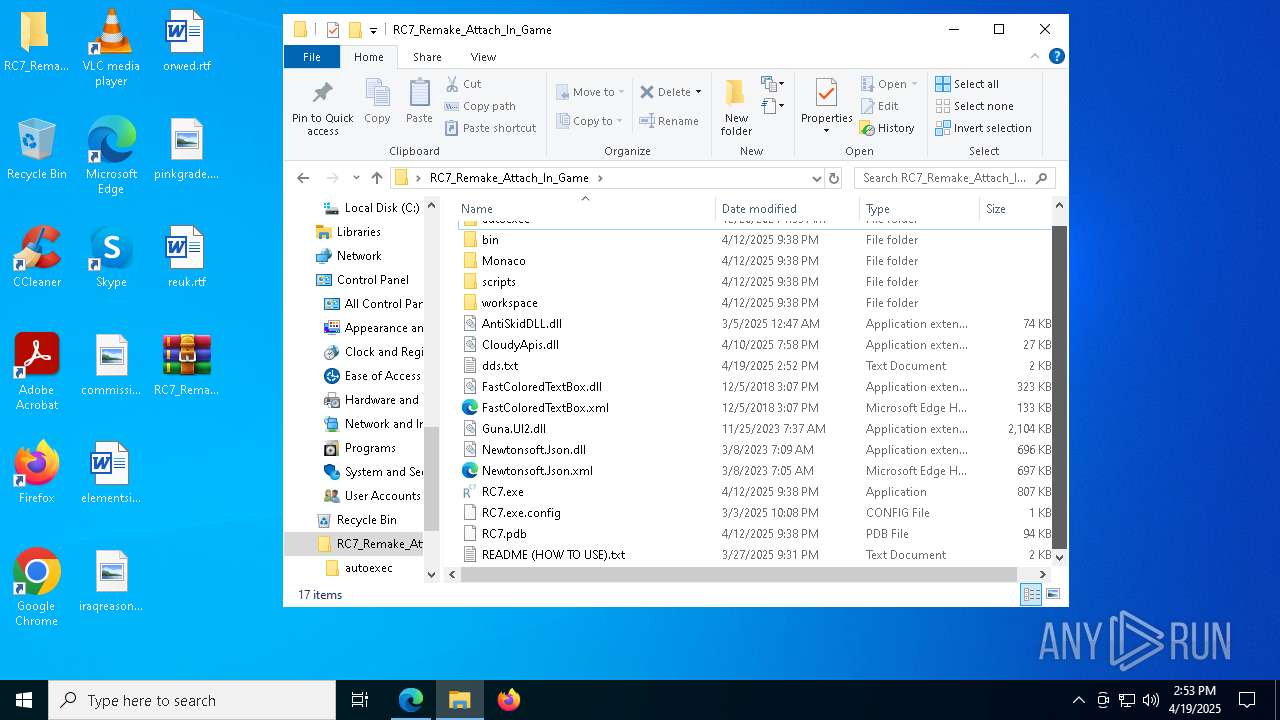
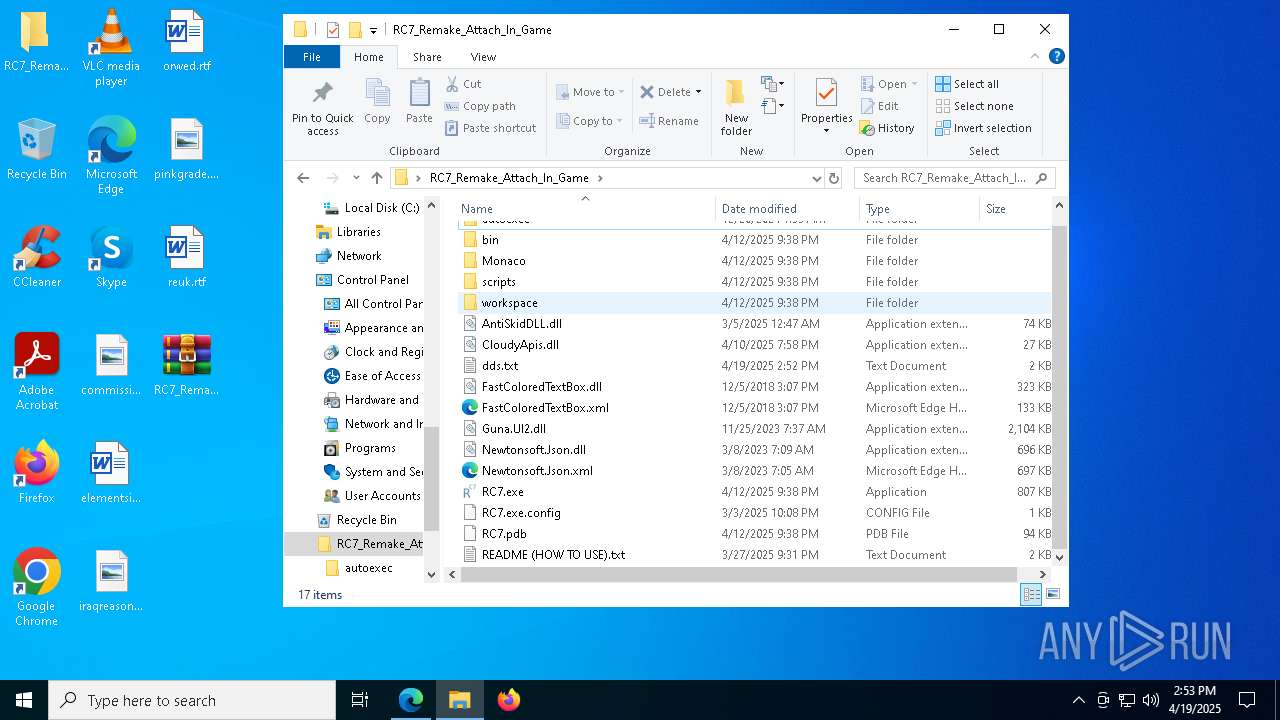
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6436)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 496)
- OpenWith.exe (PID: 5600)
Reads the computer name
- RC7.exe (PID: 4200)
- RC7.exe (PID: 7744)
- identity_helper.exe (PID: 7672)
- RC7.exe (PID: 2504)
- RC7.exe (PID: 7584)
- RC7.exe (PID: 7724)
The sample compiled with english language support
- WinRAR.exe (PID: 6436)
Reads the machine GUID from the registry
- RC7.exe (PID: 4200)
- RC7.exe (PID: 7744)
- RC7.exe (PID: 7584)
- RC7.exe (PID: 2504)
- RC7.exe (PID: 7724)
Checks supported languages
- RC7.exe (PID: 4200)
- identity_helper.exe (PID: 7672)
- RC7.exe (PID: 7744)
- RC7.exe (PID: 2504)
- RC7.exe (PID: 7584)
- RC7.exe (PID: 7724)
Reads Environment values
- RC7.exe (PID: 4200)
- identity_helper.exe (PID: 7672)
- RC7.exe (PID: 7744)
- RC7.exe (PID: 7584)
- RC7.exe (PID: 7724)
- RC7.exe (PID: 2504)
Reads the software policy settings
- slui.exe (PID: 5868)
- slui.exe (PID: 6004)
Confuser has been detected (YARA)
- RC7.exe (PID: 4200)
- RC7.exe (PID: 7744)
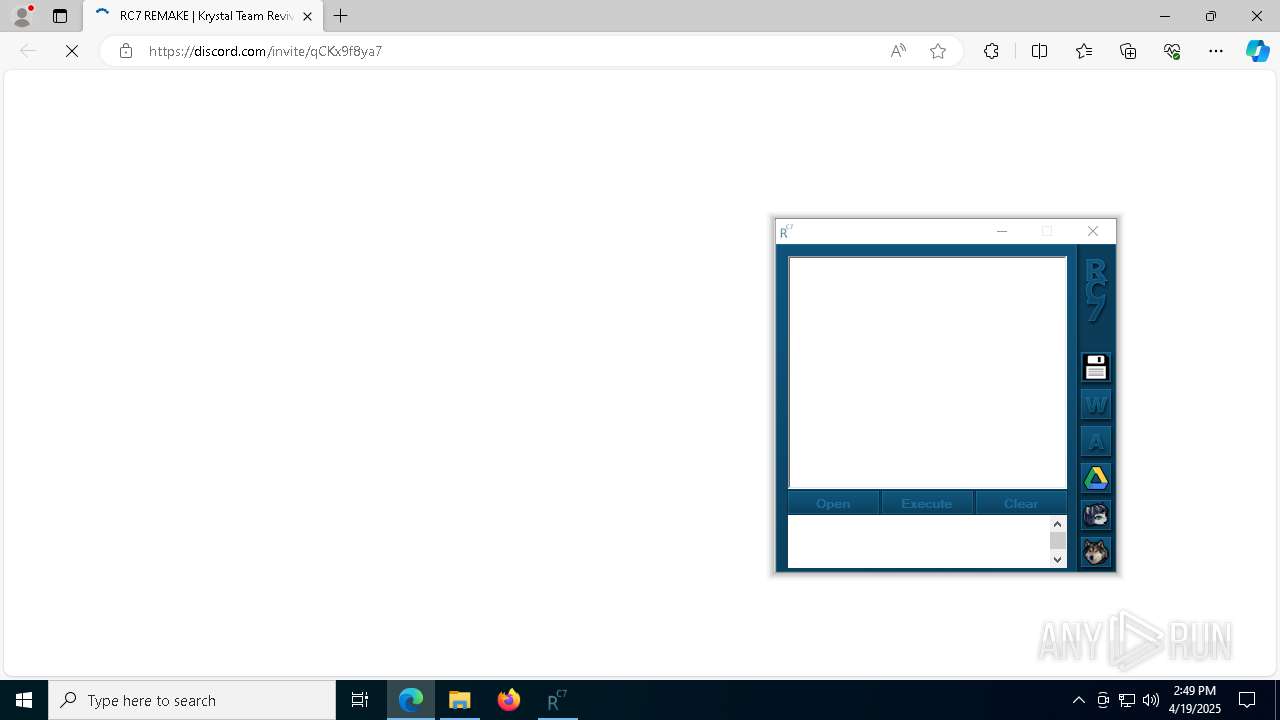
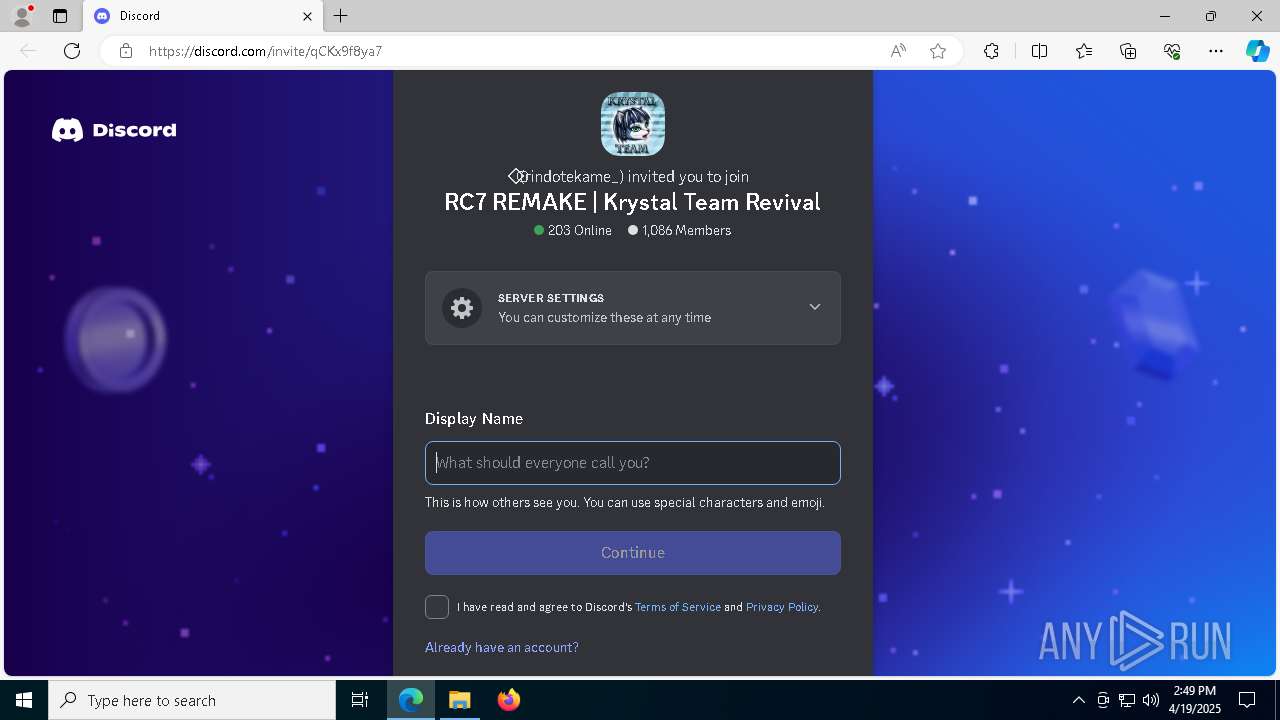
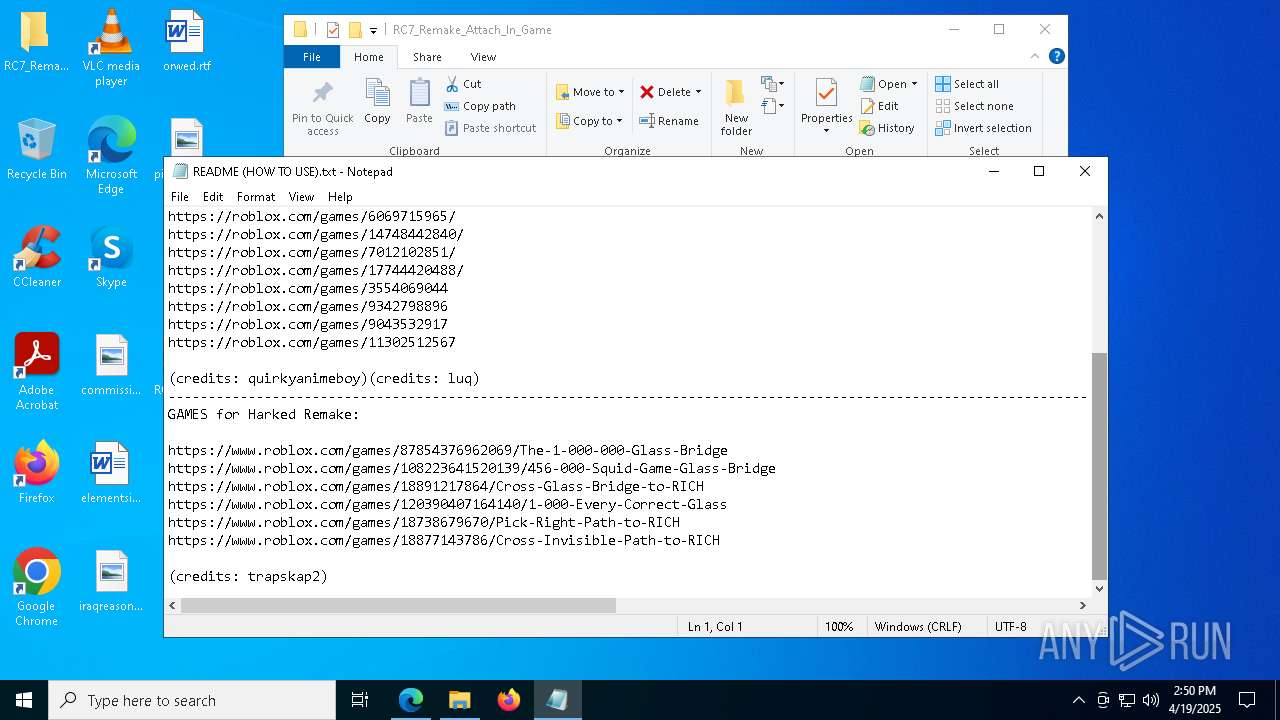
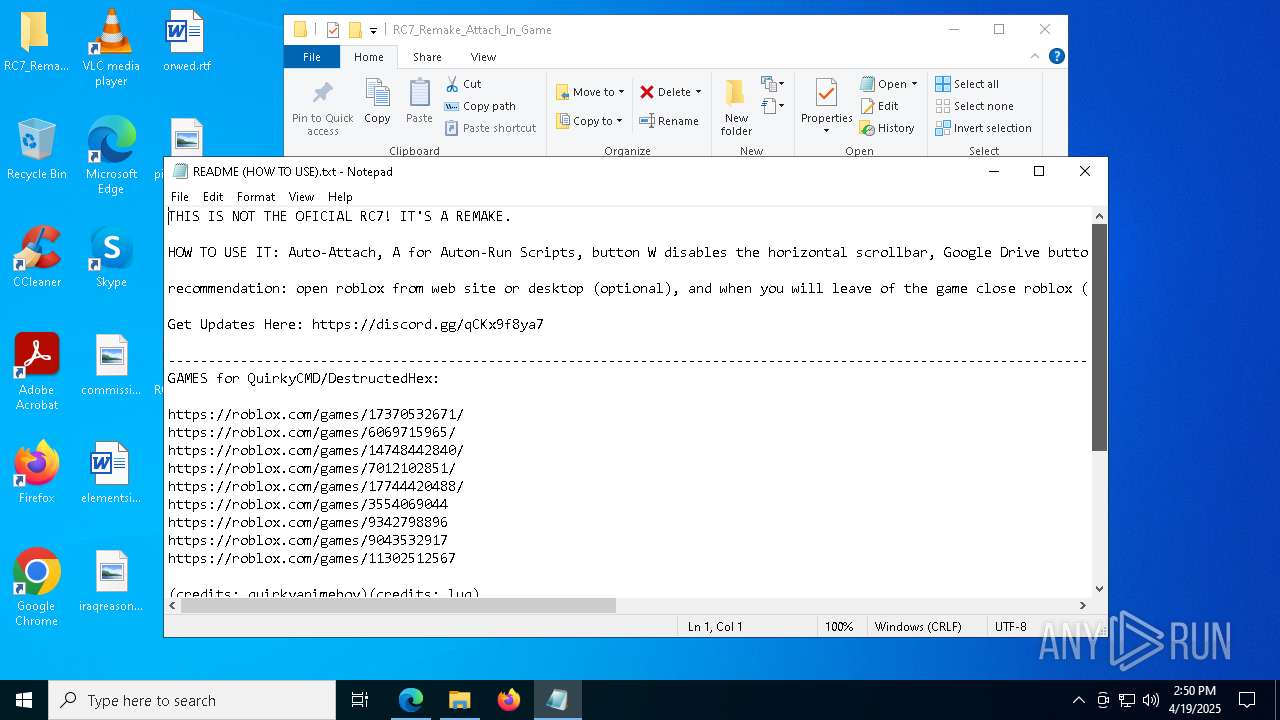
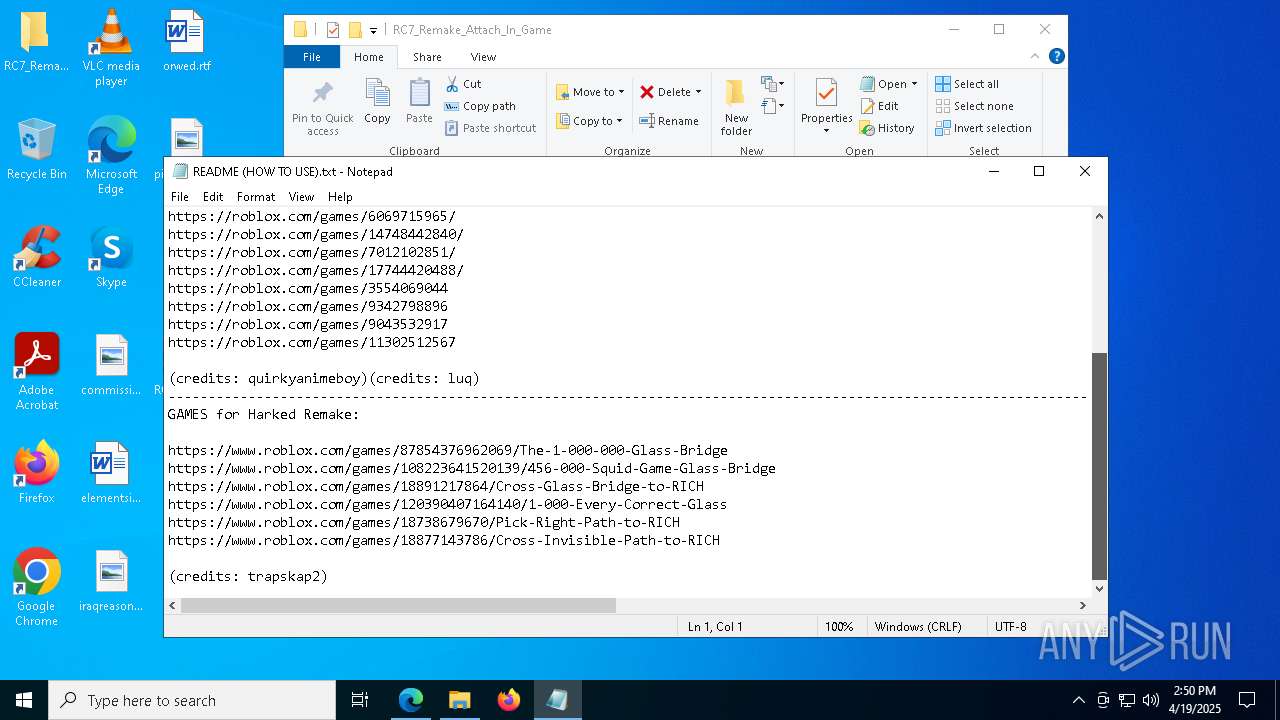
Attempting to use instant messaging service
- msedge.exe (PID: 6244)
Creates files or folders in the user directory
- WerFault.exe (PID: 7188)
- WerFault.exe (PID: 7480)
- WerFault.exe (PID: 444)
- WerFault.exe (PID: 7792)
- WerFault.exe (PID: 7480)
Application launched itself
- msedge.exe (PID: 6660)
Reads security settings of Internet Explorer
- notepad.exe (PID: 8068)
- OpenWith.exe (PID: 5600)
- notepad.exe (PID: 5332)
Checks proxy server information
- slui.exe (PID: 6004)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (36.3) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2024:12:19 22:33:20 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | autoexec/ |
Total processes
223
Monitored processes
78
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 444 | C:\WINDOWS\system32\WerFault.exe -u -p 7744 -s 2328 | C:\Windows\System32\WerFault.exe | — | RC7.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
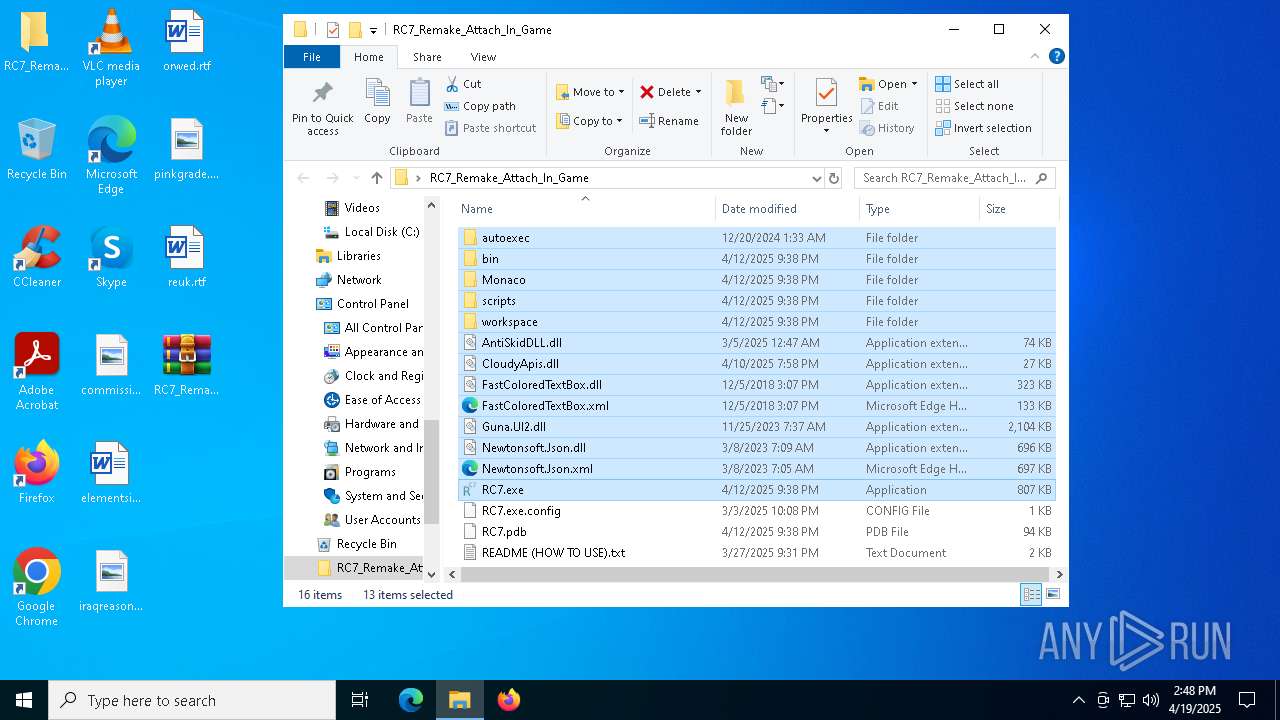
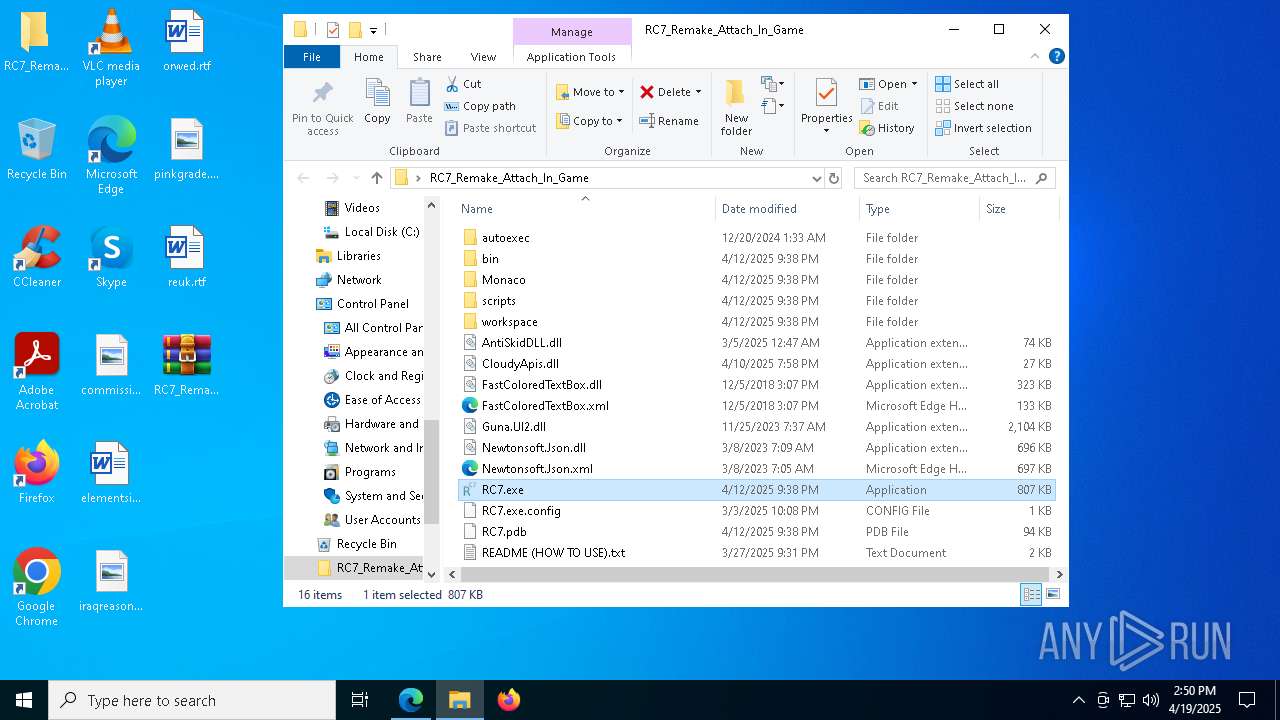
| 2504 | "C:\Users\admin\Desktop\RC7_Remake_Attach_In_Game\RC7.exe" | C:\Users\admin\Desktop\RC7_Remake_Attach_In_Game\RC7.exe | explorer.exe | ||||||||||||
User: admin Company: Krystal Team Revival Integrity Level: MEDIUM Description: RC7 Remake Exit code: 3762504530 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3272 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=5228 --field-trial-handle=2344,i,14670612182515780039,1611961197677393982,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3396 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=3196 --field-trial-handle=2344,i,14670612182515780039,1611961197677393982,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3884 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=4148 --field-trial-handle=2344,i,14670612182515780039,1611961197677393982,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3976 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=audio.mojom.AudioService --lang=en-US --service-sandbox-type=audio --no-appcompat-clear --mojo-platform-channel-handle=3864 --field-trial-handle=2344,i,14670612182515780039,1611961197677393982,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 3992 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3816 --field-trial-handle=2344,i,14670612182515780039,1611961197677393982,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4016 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=8044 --field-trial-handle=2344,i,14670612182515780039,1611961197677393982,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
31 001
Read events
30 864
Write events
120
Delete events
17
Modification events
| (PID) Process: | (6436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\RC7_Remake_Attach_In_Game.zip | |||
| (PID) Process: | (6436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 15 |
Value: | |||
| (PID) Process: | (6436) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | delete value | Name: | 14 |
Value: | |||
Executable files
25
Suspicious files
568
Text files
121
Unknown types
0
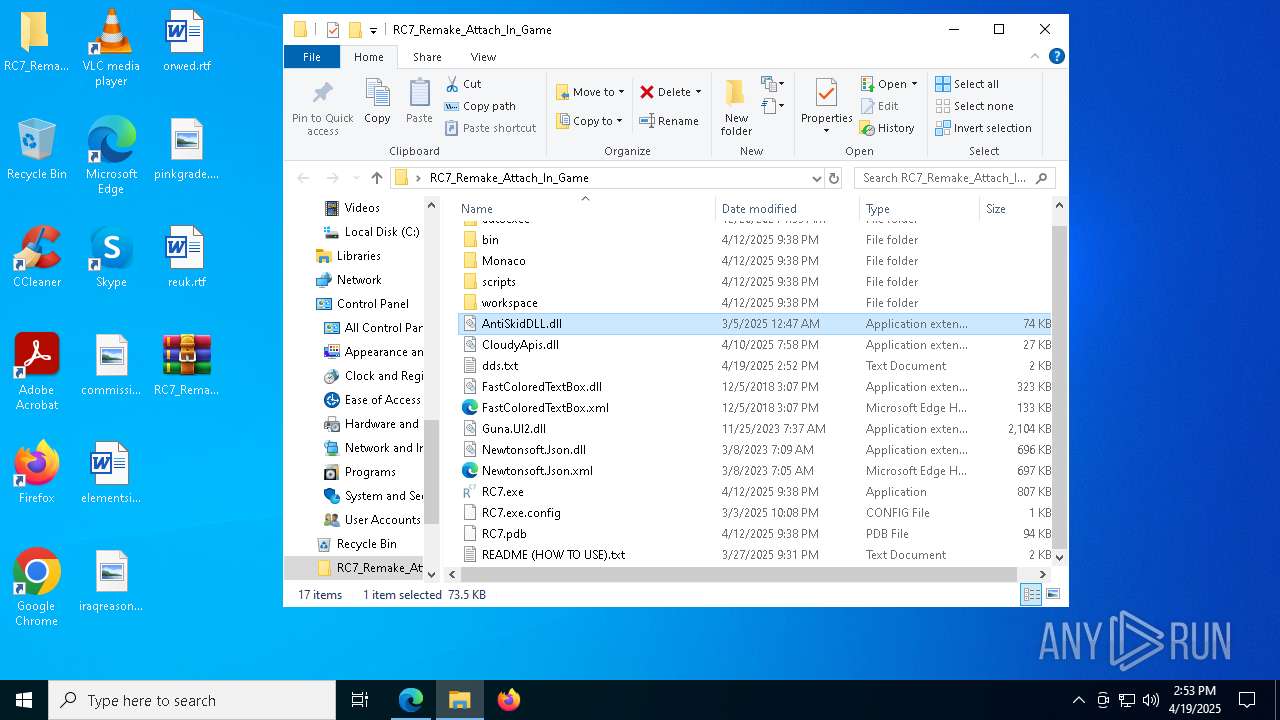
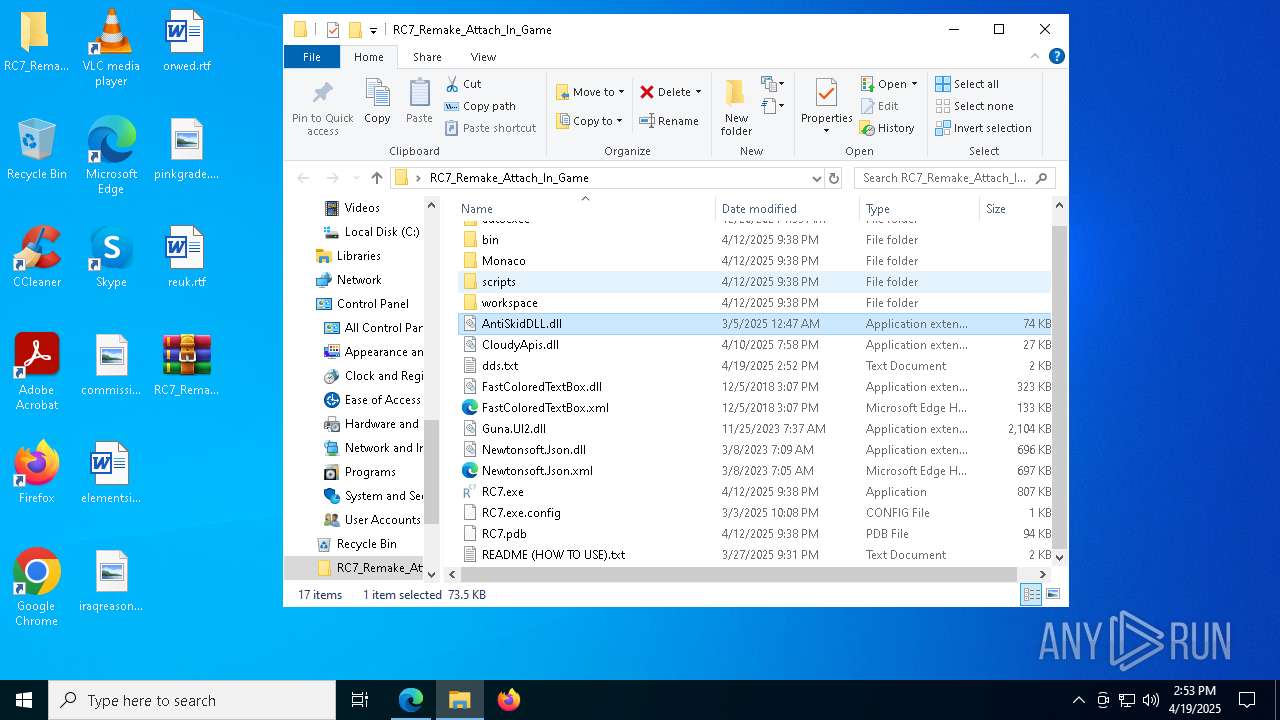
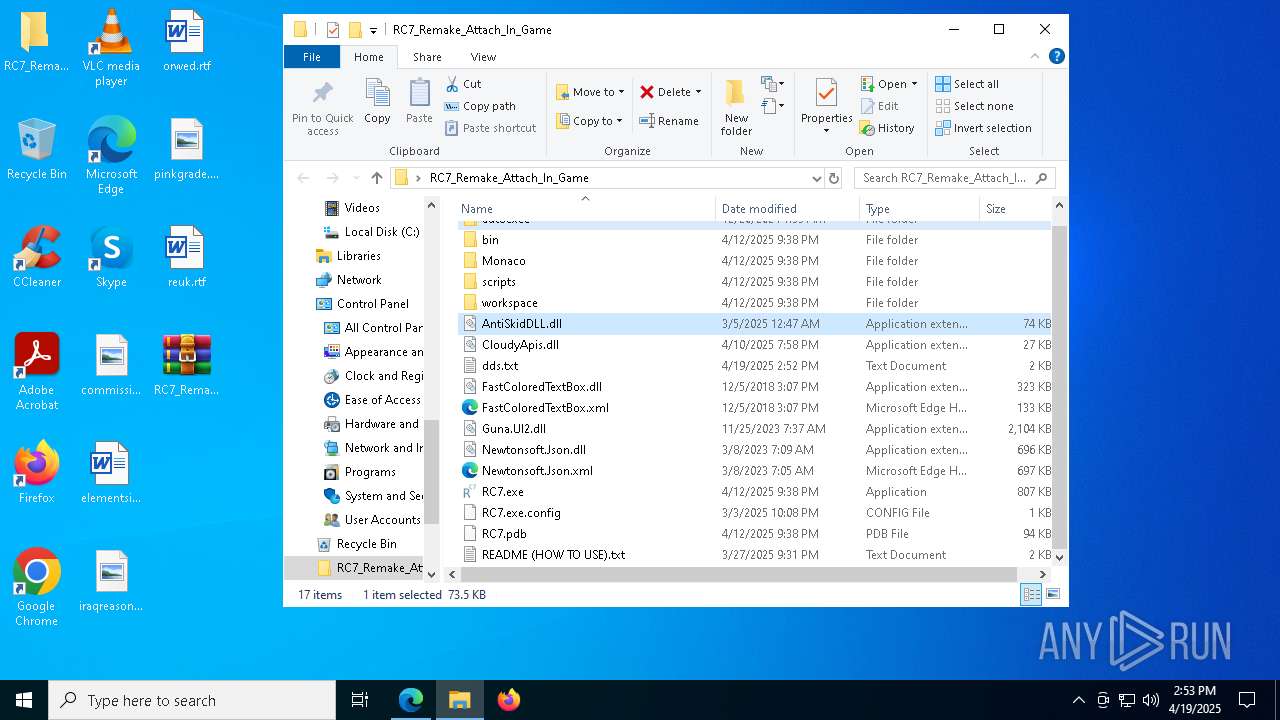
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6436 | WinRAR.exe | C:\Users\admin\Desktop\RC7_Remake_Attach_In_Game\bin\zstd.dll | executable | |
MD5:5B96FB0D4E6453680DA278F5B7E51A29 | SHA256:1374391DAFD6262795243A58F9FB234BE859D940683FE756C64692CA807F0478 | |||
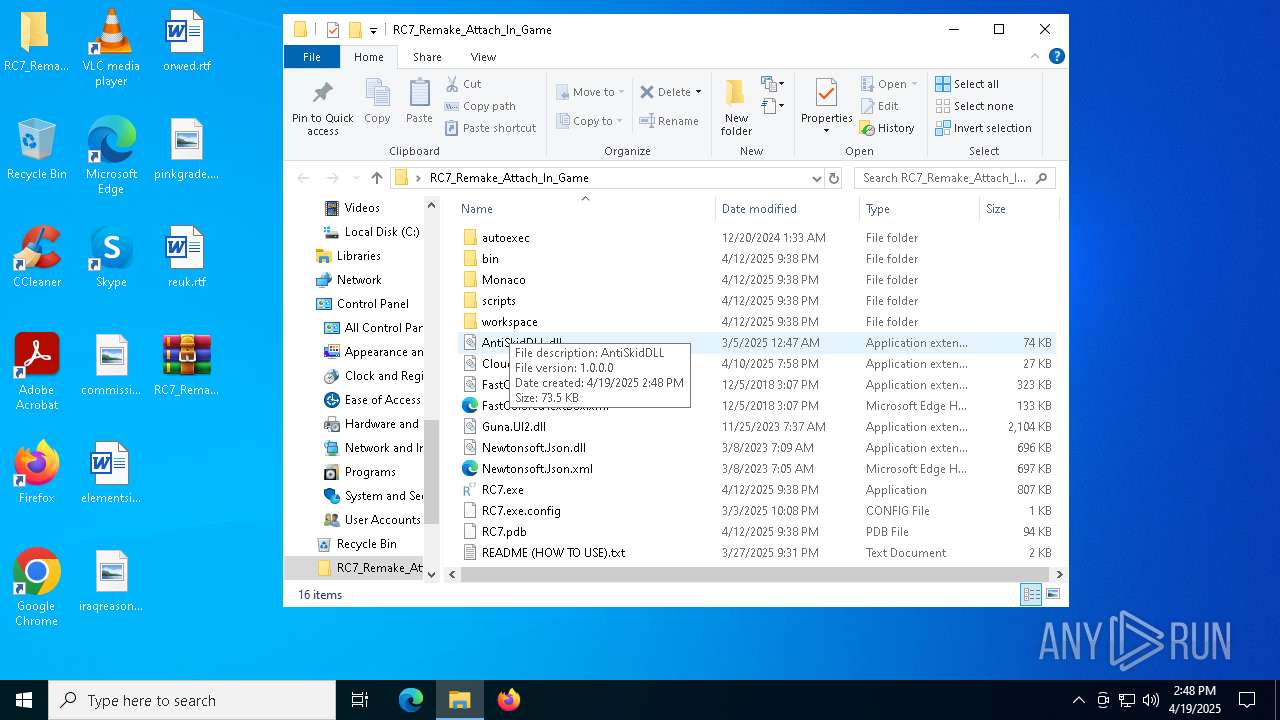
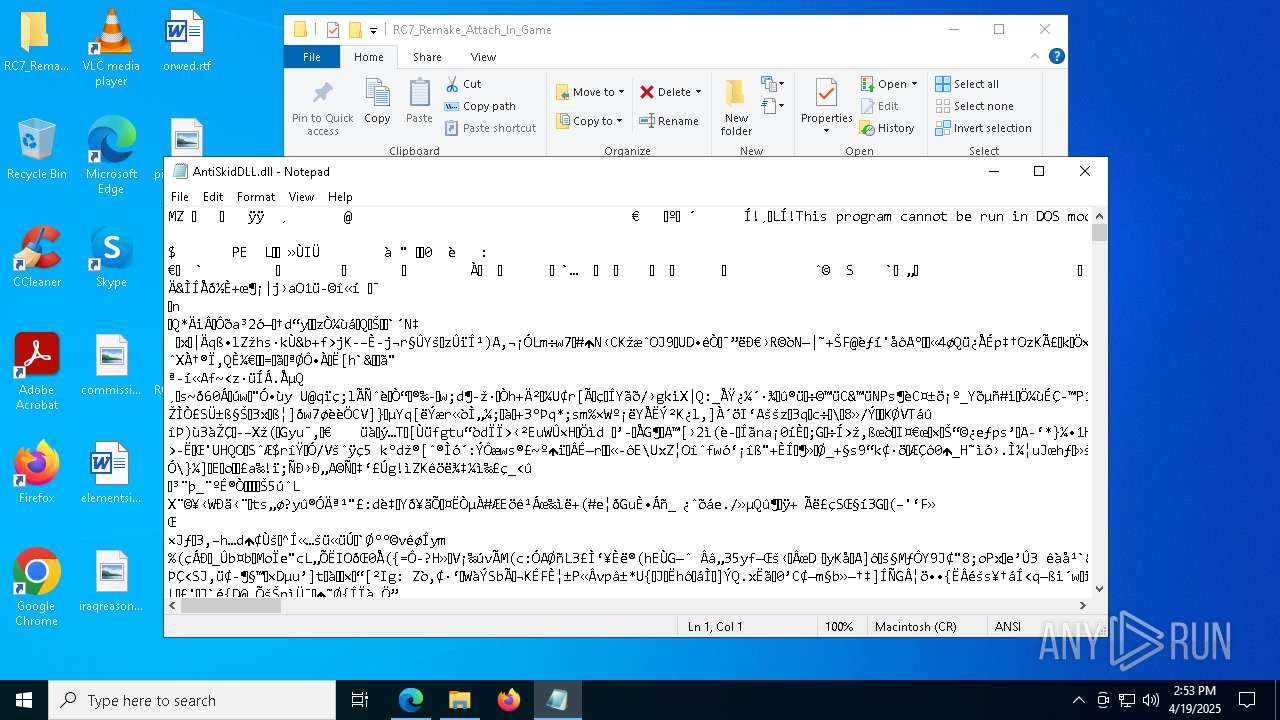
| 6436 | WinRAR.exe | C:\Users\admin\Desktop\RC7_Remake_Attach_In_Game\bin\AntiSkidDLL.dll | executable | |
MD5:87294AA0912182EC94F9341FBFA73A6C | SHA256:69E962D9EA9A55F629D1D2F050D5C70889ECB86C79988AAFBE976903F4E96ED7 | |||
| 6436 | WinRAR.exe | C:\Users\admin\Desktop\RC7_Remake_Attach_In_Game\bin\RobloxPlayerLauncher.exe | executable | |
MD5:2C852B9D329284E85FCA0E1CCA876ACA | SHA256:3A8EDC56B985CB0E13DF87EC94D04C69E164498C7342BE7348EE7681C9ABDDD3 | |||
| 6436 | WinRAR.exe | C:\Users\admin\Desktop\RC7_Remake_Attach_In_Game\bin\libcrypto-3-x64.dll | executable | |
MD5:BE0F6D1D60E149CEDACA33A04963E05F | SHA256:81A5FE6CD0EF5B083E5C4BDB6A40A30BFB1B0DE15A9DFAD459DE2D6A36D94F86 | |||
| 6436 | WinRAR.exe | C:\Users\admin\Desktop\RC7_Remake_Attach_In_Game\Monaco\vs\basic-languages\bat\bat.js | binary | |
MD5:4CB475399C4490EEA41982DCD6D9653E | SHA256:9BCA42394FE8922FEC24B768EEB8CE04692DE6FAD82F9052D5B7E70F5C6B0F40 | |||
| 6436 | WinRAR.exe | C:\Users\admin\Desktop\RC7_Remake_Attach_In_Game\bin\Multiple_ROBLOX.exe | executable | |
MD5:AED655395747A6602479F6032D3C099F | SHA256:3D6123DC6FFBD1A11D73229988203052809BD17617B24A034C1122C8F4983DB4 | |||
| 6436 | WinRAR.exe | C:\Users\admin\Desktop\RC7_Remake_Attach_In_Game\bin\libssl-3-x64.dll | executable | |
MD5:733E3B58EE1760A442FEC4712848C3AD | SHA256:159198CB8E740F9AD5918B51503121FD1B7E70460F6A4F6A6AA27576BBFA31C7 | |||
| 6436 | WinRAR.exe | C:\Users\admin\Desktop\RC7_Remake_Attach_In_Game\bin\xxhash.dll | executable | |
MD5:70C514826D9428F184D27F0C8F397404 | SHA256:AFF59E91D222B75B3E3AC789BABA9E24EFF99796261AE5E887EF9E3C28BB3D64 | |||
| 6436 | WinRAR.exe | C:\Users\admin\Desktop\RC7_Remake_Attach_In_Game\Monaco\vs\base\worker\workerMain.js | binary | |
MD5:27EAD90C7702154755785E0E53398755 | SHA256:BDF9433692A08851E13DD58504EEF19F51BD2EC7241923A68EDF5772E0E53AF5 | |||
| 6436 | WinRAR.exe | C:\Users\admin\Desktop\RC7_Remake_Attach_In_Game\Monaco\vs\basic-languages\cpp\cpp.js | binary | |
MD5:0A16509E6CD0155FB622E785CFE976C7 | SHA256:A7C2BEA7CA3D9E203A3A286735945FE010C8F4F8D46620386EE8BEFC6A78B32B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
60
DNS requests
71
Threats
23
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5728 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5728 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7848 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1745626154&P2=404&P3=2&P4=QgLnWocjS%2fJ%2b%2bgRAE7kh2ub1%2fk%2fVFxNC3cuxyj3GwDvJuHRbfllUEKz8ZWmwF%2f%2bTKCaDtDSR5TEcG%2fXfTKxZdQ%3d%3d | unknown | — | — | whitelisted |
7848 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1745626154&P2=404&P3=2&P4=QgLnWocjS%2fJ%2b%2bgRAE7kh2ub1%2fk%2fVFxNC3cuxyj3GwDvJuHRbfllUEKz8ZWmwF%2f%2bTKCaDtDSR5TEcG%2fXfTKxZdQ%3d%3d | unknown | — | — | whitelisted |
7848 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1745626154&P2=404&P3=2&P4=QqxJgMw1QhhyHq8WSFu06ir3K24wsAacn6mARImf%2b9MNfZ%2bgSUeicHQiXU1cDlcDC%2f9GepPDOyzW1KIm8Dpe7g%3d%3d | unknown | — | — | whitelisted |
7848 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1745626154&P2=404&P3=2&P4=QgLnWocjS%2fJ%2b%2bgRAE7kh2ub1%2fk%2fVFxNC3cuxyj3GwDvJuHRbfllUEKz8ZWmwF%2f%2bTKCaDtDSR5TEcG%2fXfTKxZdQ%3d%3d | unknown | — | — | whitelisted |
7848 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1745626154&P2=404&P3=2&P4=QqxJgMw1QhhyHq8WSFu06ir3K24wsAacn6mARImf%2b9MNfZ%2bgSUeicHQiXU1cDlcDC%2f9GepPDOyzW1KIm8Dpe7g%3d%3d | unknown | — | — | whitelisted |
7848 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1745626154&P2=404&P3=2&P4=QqxJgMw1QhhyHq8WSFu06ir3K24wsAacn6mARImf%2b9MNfZ%2bgSUeicHQiXU1cDlcDC%2f9GepPDOyzW1KIm8Dpe7g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.5:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
keyauth.win |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Potentially Bad Traffic | ET INFO KeyAuth Open-source Authentication System Domain in DNS Lookup (keyauth .win) |
6244 | msedge.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
6244 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6244 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6244 | msedge.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |
6244 | msedge.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
6244 | msedge.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
6244 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
6244 | msedge.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
6244 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |