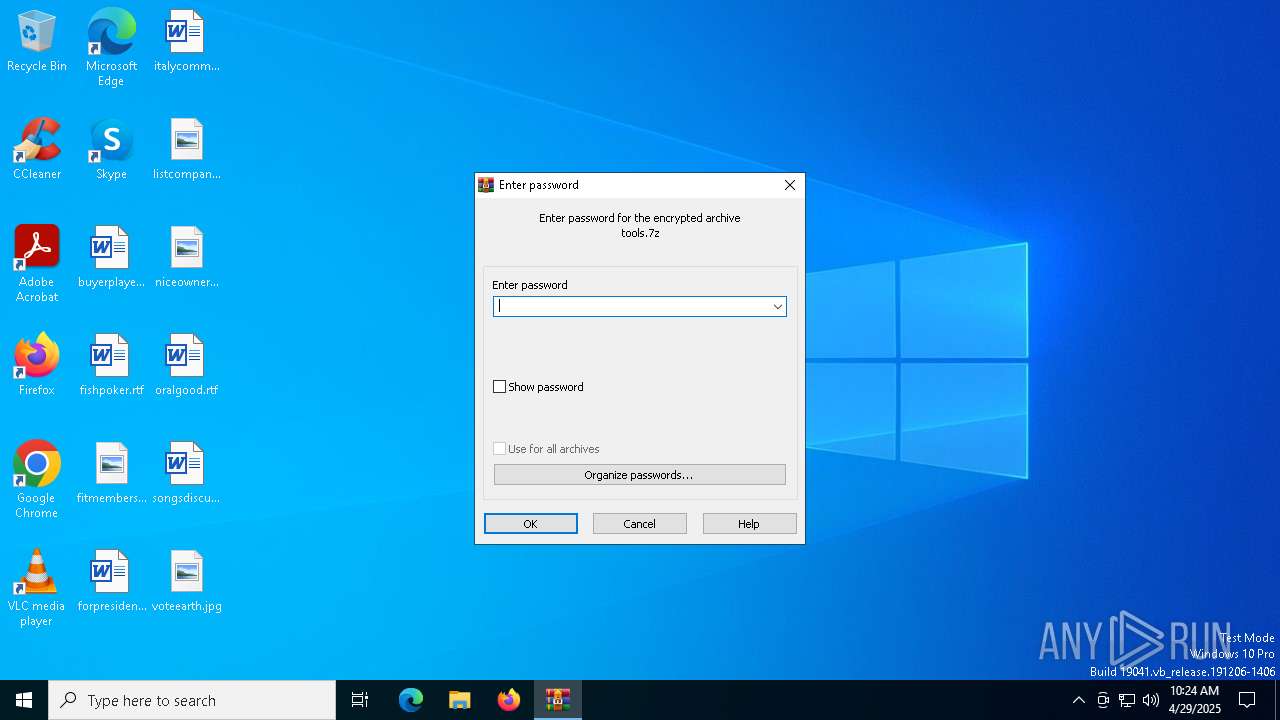
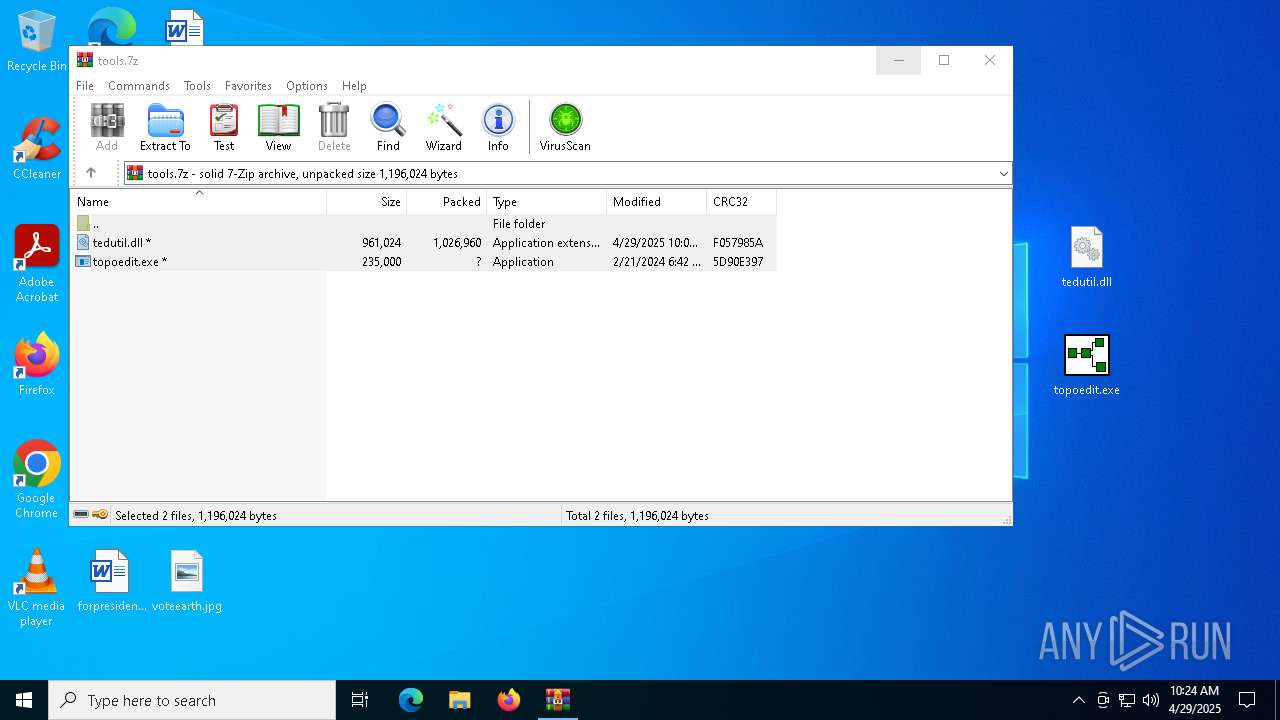
| File name: | tools.7z |
| Full analysis: | https://app.any.run/tasks/3fb17f25-09d3-488c-80e3-d74549d99876 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 10:24:22 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 125F7FB77CC91161F30732AA1095BCAB |
| SHA1: | C732E10586E0208B6CA4069F49D24F24BF614AE3 |
| SHA256: | D5A3AA0400E1FC9555BF85A1E1FA6BB996DA24E31AD9A67654D394FB8B404911 |
| SSDEEP: | 49152:SF9LDZThzBD1jTsuWAaXIQ0i8BustS8yUdRqqLeB9fRHae7v10KNpfBt871MPtPC:SF9LDZTh1D1jIuBa4g8Iky0w9R7xpNd+ |
MALICIOUS
Bypass User Account Control (Modify registry)
- topoedit.exe (PID: 6388)
Bypass User Account Control (fodhelper)
- fodhelper.exe (PID: 5072)
SUSPICIOUS
Changes default file association
- topoedit.exe (PID: 6388)
Reads security settings of Internet Explorer
- topoedit.exe (PID: 6388)
Reads the date of Windows installation
- topoedit.exe (PID: 6388)
Executes application which crashes
- topoedit.exe (PID: 6388)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5212)
Manual execution by a user
- topoedit.exe (PID: 6388)
Checks supported languages
- topoedit.exe (PID: 6388)
Reads the computer name
- topoedit.exe (PID: 6388)
Process checks computer location settings
- topoedit.exe (PID: 6388)
Creates files or folders in the user directory
- WerFault.exe (PID: 2420)
- WerFault.exe (PID: 2340)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|
Total processes
139
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2340 | C:\WINDOWS\system32\WerFault.exe -u -p 6388 -s 1284 | C:\Windows\System32\WerFault.exe | — | topoedit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2420 | C:\WINDOWS\system32\WerFault.exe -u -p 6388 -s 1560 | C:\Windows\System32\WerFault.exe | — | topoedit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4688 | "C:\Windows\System32\fodhelper.exe" | C:\Windows\System32\fodhelper.exe | — | topoedit.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Features On Demand Helper Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4868 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5072 | "C:\Windows\System32\fodhelper.exe" | C:\Windows\System32\fodhelper.exe | topoedit.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Features On Demand Helper Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
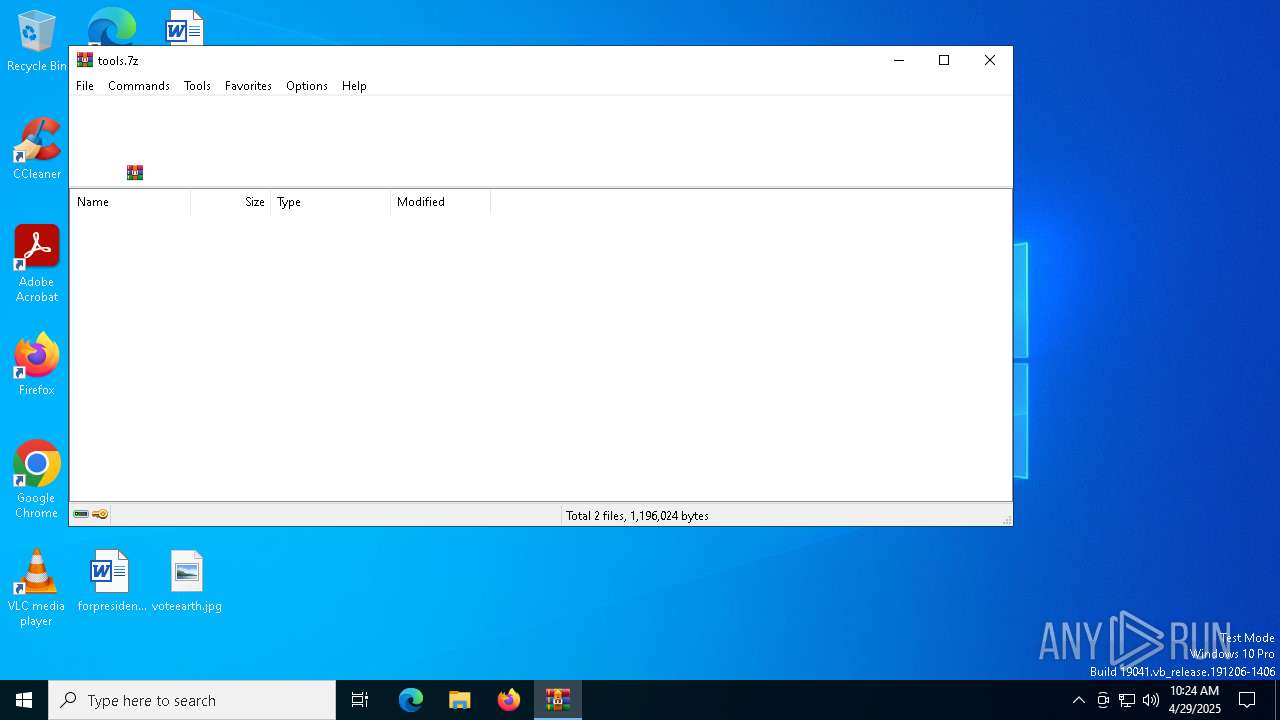
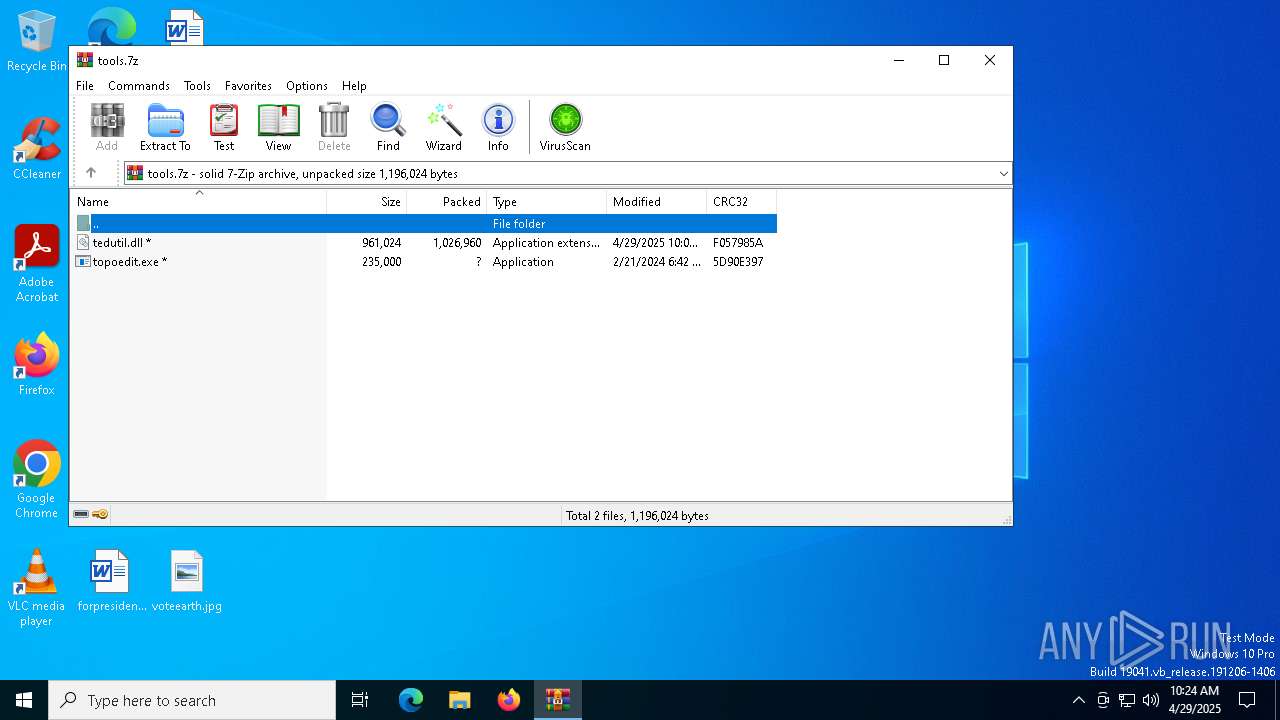
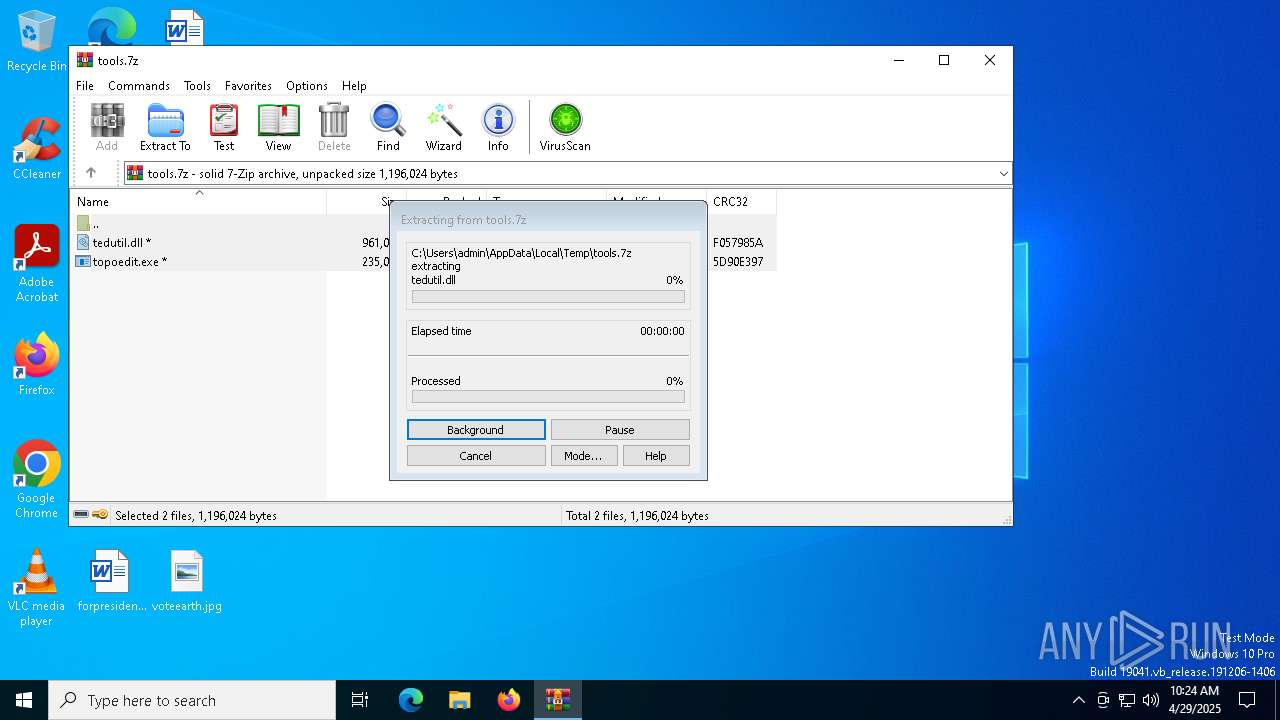
| 5212 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\tools.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5280 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6388 | "C:\Users\admin\Desktop\topoedit.exe" | C:\Users\admin\Desktop\topoedit.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Topology Editor Exit code: 3221226525 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
5 479
Read events
5 469
Write events
10
Delete events
0
Modification events
| (PID) Process: | (5212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (5212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\tools.7z | |||
| (PID) Process: | (5212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5212) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6388) topoedit.exe | Key: | HKEY_CLASSES_ROOT\ms-settings\Shell\Open\command |
| Operation: | write | Name: | DelegateExecute |
Value: | |||
Executable files
2
Suspicious files
6
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2340 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_topoedit.exe_cf43ef18ae83d5e647cc3ac715183af22b970_f28f68ee_95106003-b6aa-4dc4-a782-7f3d8a84ea28\Report.wer | — | |
MD5:— | SHA256:— | |||
| 2420 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_topoedit.exe_c2731fba9c8217f12fb6240f9895ed85fb429_f28f68ee_60e72846-bf55-4b38-aa5a-c5e3a321b3cd\Report.wer | — | |
MD5:— | SHA256:— | |||
| 5212 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb5212.9017\tedutil.dll | executable | |
MD5:2E33D314EBAA391430EB3AA6C667A5AE | SHA256:493D950842B358E00CA16649A85213CC80EE36A63A3169784C1996B837318960 | |||
| 2340 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\topoedit.exe.6388.dmp | binary | |
MD5:9269E6C279748AC4620D9D98910D8BBD | SHA256:F98AC636C8FD7070CC4BD393A6792E6D4CFD1AE34B250498DF20C0AD395118B7 | |||
| 2340 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER7DD.tmp.dmp | binary | |
MD5:5C4404D12C5983A6B043AFA589643191 | SHA256:74F402193FC39C40A77653628E9C24D294F1B2F5E95F2A50E9D8EC47FF1D9C2F | |||
| 2340 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERAFA.tmp.WERInternalMetadata.xml | binary | |
MD5:1FA8E1F575FE297FD72BABB24305AE6C | SHA256:EB2A77EF153EF59AAD3877B3018355729E8A2988E2DDCAD9F64EE514B174C0BD | |||
| 2340 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERB4A.tmp.xml | xml | |
MD5:97EA523D1E377C873223FBBA51A47352 | SHA256:B6CE20DABD6845FAB7A87A811533C3CB3C9F88AB1311E1E96D1237BBB557F0D1 | |||
| 2420 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER1125.tmp.WERInternalMetadata.xml | binary | |
MD5:C7DAB200D84B4048834E76C49336E91D | SHA256:27E833BED8651FC625B78F7E064626CB908BDDEBD938750B5834A1439316C591 | |||
| 5212 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb5212.9017\topoedit.exe | executable | |
MD5:CB9954E893674AAFA74BECCBA996F754 | SHA256:7AC3CAC9C07328AC49D0956E4C3B4ACF2A3D31568CBF99ACCE172E0637AE11A4 | |||
| 2420 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WER1164.tmp.xml | xml | |
MD5:A2AD36D258455CE1315B305DF25B1A14 | SHA256:4F8A01A99942D21ABCCA409BF34F98DBFC320CD7363FDF83CF95379D78044C7D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
19
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.32.238.107:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.51.98.7:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5228 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5228 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.32.238.107:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 23.51.98.7:80 | ocsp.digicert.com | Akamai International B.V. | US | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5228 | SIHClient.exe | 20.12.23.50:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |