| File name: | 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn |
| Full analysis: | https://app.any.run/tasks/70c337c1-7a45-438c-93f9-27d5239467f8 |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 10:58:40 |
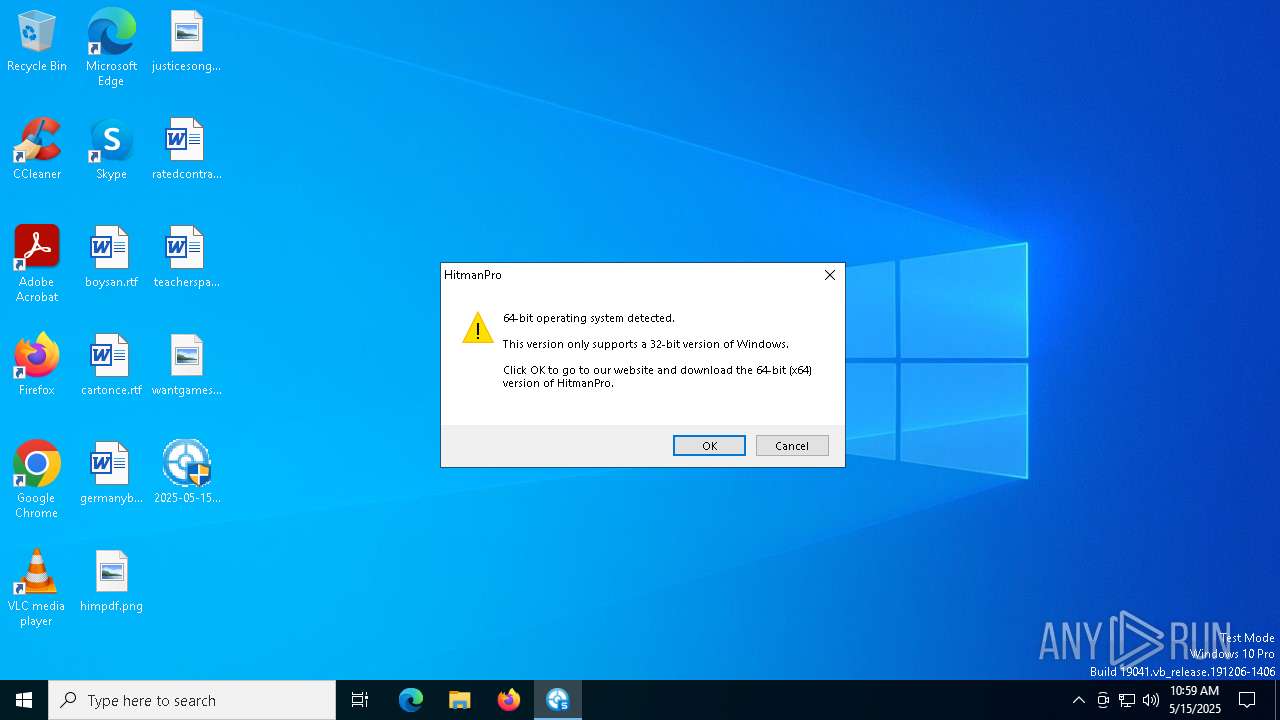
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 3 sections |
| MD5: | F770262572E19F890947C28883CCAB5B |
| SHA1: | C3783E304264568562947ECC5BEFEAE96688FF9C |
| SHA256: | D59CD6A9E85A861138FFA3EACED7DA8E435027FBAE516393801648D63EA35E51 |
| SSDEEP: | 98304:5cSfEygSPZB90KTnbc7qgJXozqXIZLFgBrVJ+5RhNX5nsBDYsB1pHTdhQBLCOyAb:YRSq/0epjMWR8 |
MALICIOUS
JEEFO has been detected
- 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe (PID: 7396)
- icsys.icn.exe (PID: 7732)
- svchost.exe (PID: 7828)
- explorer.exe (PID: 7776)
Changes the autorun value in the registry
- explorer.exe (PID: 7776)
- svchost.exe (PID: 7828)
SUSPICIOUS
Executable content was dropped or overwritten
- 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe (PID: 7396)
- icsys.icn.exe (PID: 7732)
- explorer.exe (PID: 7776)
- spoolsv.exe (PID: 7796)
Starts application with an unusual extension
- 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe (PID: 7396)
Starts itself from another location
- 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe (PID: 7396)
- icsys.icn.exe (PID: 7732)
- explorer.exe (PID: 7776)
- spoolsv.exe (PID: 7796)
- svchost.exe (PID: 7828)
The process creates files with name similar to system file names
- icsys.icn.exe (PID: 7732)
- spoolsv.exe (PID: 7796)
Creates or modifies Windows services
- svchost.exe (PID: 7828)
INFO
Reads the computer name
- 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe (PID: 7592)
- svchost.exe (PID: 7828)
Checks supported languages
- 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe (PID: 7396)
- 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe (PID: 7592)
- icsys.icn.exe (PID: 7732)
- explorer.exe (PID: 7776)
- spoolsv.exe (PID: 7796)
- svchost.exe (PID: 7828)
- spoolsv.exe (PID: 7888)
Create files in a temporary directory
- 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe (PID: 7396)
- icsys.icn.exe (PID: 7732)
- explorer.exe (PID: 7776)
- svchost.exe (PID: 7828)
- spoolsv.exe (PID: 7888)
- spoolsv.exe (PID: 7796)
Creates files in the program directory
- 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe (PID: 7592)
Auto-launch of the file from Registry key
- explorer.exe (PID: 7776)
- svchost.exe (PID: 7828)
Manual execution by a user
- explorer.exe (PID: 7208)
- svchost.exe (PID: 7268)
Checks proxy server information
- slui.exe (PID: 8180)
Reads the software policy settings
- slui.exe (PID: 8180)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:04:01 07:08:22+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 106496 |
| InitializedDataSize: | 12288 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x290c |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| ProductName: | Project1 |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | TJprojMain |
| OriginalFileName: | TJprojMain.exe |
Total processes
138
Monitored processes
11
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7208 | c:\windows\resources\themes\explorer.exe RO | C:\Windows\Resources\Themes\explorer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.00 Modules
| |||||||||||||||
| 7268 | c:\windows\resources\svchost.exe RO | C:\Windows\Resources\svchost.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.00 Modules
| |||||||||||||||
| 7332 | "C:\Users\admin\Desktop\2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe" | C:\Users\admin\Desktop\2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.00 Modules
| |||||||||||||||
| 7396 | "C:\Users\admin\Desktop\2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe" | C:\Users\admin\Desktop\2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 7592 | c:\users\admin\desktop\2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\Desktop\2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe | — | 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe | |||||||||||
User: admin Company: Sophos B.V. Integrity Level: HIGH Description: HitmanPro 3.8 Version: 3, 8, 44, 340 Modules
| |||||||||||||||
| 7732 | C:\Windows\Resources\Themes\icsys.icn.exe | C:\Windows\Resources\Themes\icsys.icn.exe | 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 7776 | c:\windows\resources\themes\explorer.exe | C:\Windows\Resources\Themes\explorer.exe | icsys.icn.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.00 Modules
| |||||||||||||||
| 7796 | c:\windows\resources\spoolsv.exe SE | C:\Windows\Resources\spoolsv.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 7828 | c:\windows\resources\svchost.exe | C:\Windows\Resources\svchost.exe | spoolsv.exe | ||||||||||||
User: admin Integrity Level: HIGH Version: 1.00 Modules
| |||||||||||||||
| 7888 | c:\windows\resources\spoolsv.exe PR | C:\Windows\Resources\spoolsv.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
Total events
3 907
Read events
3 887
Write events
16
Delete events
4
Modification events
| (PID) Process: | (7396) 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (7592) 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\HitmanPro |
| Operation: | write | Name: | UID |
Value: {DEC2849E-3622-41F5-930C-49AB28C51302} | |||
| (PID) Process: | (7732) icsys.icn.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\VB and VBA Program Settings\Explorer\Process |
| Operation: | write | Name: | LO |
Value: 1 | |||
| (PID) Process: | (7776) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (7776) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (7776) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
| (PID) Process: | (7776) explorer.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Svchost |
Value: | |||
| (PID) Process: | (7828) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Explorer |
Value: c:\windows\resources\themes\explorer.exe RO | |||
| (PID) Process: | (7828) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\RunOnce |
| Operation: | write | Name: | Svchost |
Value: c:\windows\resources\svchost.exe RO | |||
| (PID) Process: | (7828) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete value | Name: | Explorer |
Value: | |||
Executable files
5
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7732 | icsys.icn.exe | C:\Windows\Resources\Themes\explorer.exe | executable | |
MD5:65513A98D66FC91A20FF957ED471EF66 | SHA256:A7A070FCC2D01BE2DB7298B80A184272AEAA6827A0E6B00E4B8FAB9292534A80 | |||
| 7776 | explorer.exe | C:\Windows\Resources\spoolsv.exe | executable | |
MD5:22400268A9F68126F30AB1DD1677D023 | SHA256:07D42BD0B784D4C993882BE66822BD5AD9F0A1DB2C92C5450E1CE468CAE82DD0 | |||
| 7888 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DF2159FE567F52C3C2.TMP | binary | |
MD5:8FA20D0234F7FFB23D463D7158FE0F4A | SHA256:6594C735D6FCC41E57276E078155111868DFDBD8CB2FF8052AEC3636B012A484 | |||
| 7732 | icsys.icn.exe | C:\Users\admin\AppData\Local\Temp\~DF84714123E2BA72AB.TMP | binary | |
MD5:658EAC99B10FBBEFF605D70F2F78EE2C | SHA256:DF797579B92803270EC85C720B0AA7F087E811DFC339D09BFCF192DA2D175814 | |||
| 7796 | spoolsv.exe | C:\Users\admin\AppData\Local\Temp\~DF2E1F2F13CB46832E.TMP | binary | |
MD5:598A491BCC77DE8EBE9B454AD5C651EC | SHA256:909FF2EF308DB5D911E28D8B60912A616D2DB94FDC6EDE85F3B31A813A0928EB | |||
| 7396 | 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe | C:\Windows\Resources\Themes\icsys.icn.exe | executable | |
MD5:9C00C1121E21CFE5A8A2FE55621C9174 | SHA256:CAF0991A6276819AD265E63264A7C3D36401B061B97D125607F4A592283A1818 | |||
| 7796 | spoolsv.exe | C:\Windows\Resources\svchost.exe | executable | |
MD5:1A0ADF970E31E56F2727885C96CDBDDF | SHA256:1117F441A8E0AA4A44F35BD57354BB27C2BEA3D771492875BC99CB49CB048DF0 | |||
| 7396 | 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\AppData\Local\Temp\~DF8C87861102B0565C.TMP | binary | |
MD5:5053FD779EB59FAA469F90602923FFE8 | SHA256:EEE3C5FFBC37520692765F00D40A02ED085F2469EA1273382A4B399A41C33FBF | |||
| 7396 | 2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe | C:\Users\admin\Desktop\2025-05-15_f770262572e19f890947c28883ccab5b_amadey_darkgate_elex_hijackloader_ngrbot_remcos_rhadamanthys_smoke-loader_swisyn.exe | executable | |
MD5:F9F2EFB59CF9214DF74CAC643C5EBAA6 | SHA256:7E337FFFC1540C5902A93C36D2C313CECCA0B6D88A5EDCCF31177F724B21C29D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
62
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7836 | SIHClient.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
7836 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7836 | SIHClient.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
7836 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
7836 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7836 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
7836 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
— | — | 20.190.160.22:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.19.11.105:80 | crl.microsoft.com | Elisa Oyj | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |