| File name: | mysetup.exe |
| Full analysis: | https://app.any.run/tasks/de5dd6ef-320e-46cb-891d-a1203aac7190 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2024, 13:15:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 54D8FF627DBD1FF4B59ACD19D43BCA29 |
| SHA1: | 0AF4C9D01E5EFA045E5F5E317408F58E5B4C440D |
| SHA256: | D58916B8B9B77784013075798E88AB7C344AE69CD9ABED0C430995D4187D0671 |
| SSDEEP: | 49152:u7HecD4dnbibBlK6bjsbmLApne0Fop4R2uXB3iyLT/ex4XrL7P42DpJXWZn80cwi:2+cD4dnYbIkWnXFopLQ3iUrex4vkY7ma |
MALICIOUS
Drops the executable file immediately after the start
- mysetup.exe (PID: 324)
- mysetup.tmp (PID: 2740)
- mysetup.exe (PID: 2268)
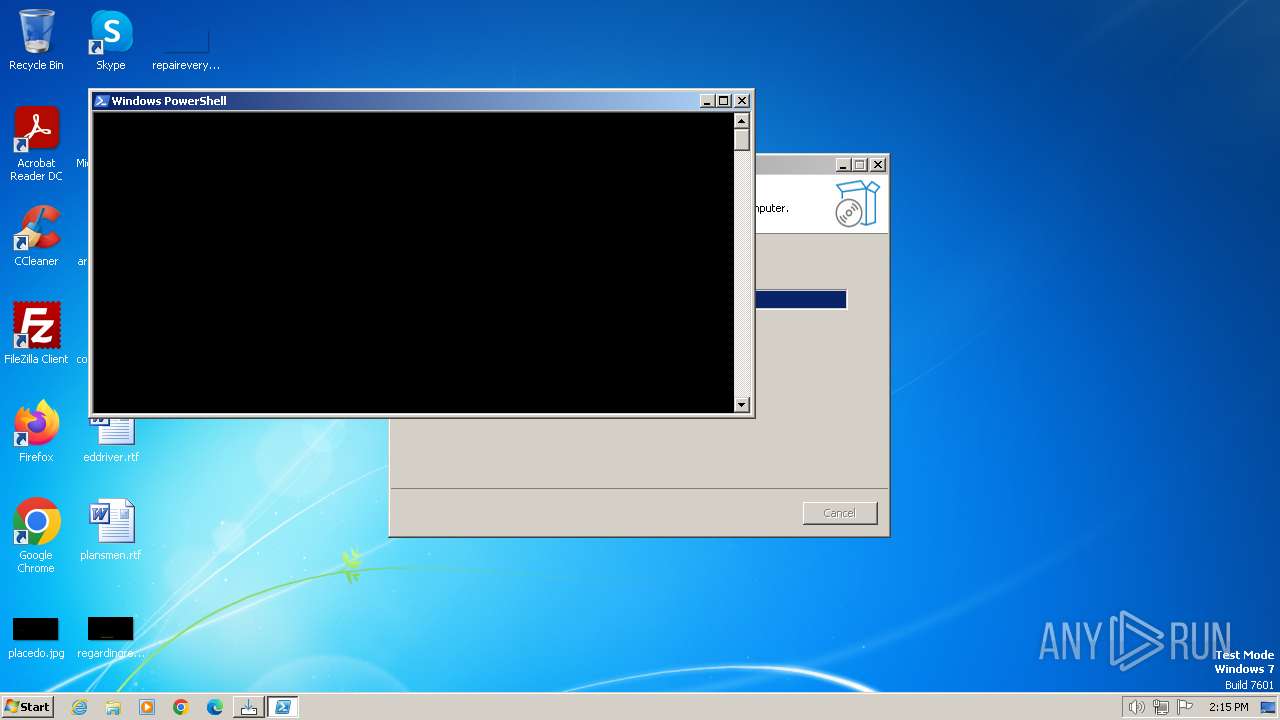
Bypass execution policy to execute commands
- powershell.exe (PID: 3244)
Changes powershell execution policy (Bypass)
- mysetup.tmp (PID: 2740)
SUSPICIOUS
Executable content was dropped or overwritten
- mysetup.exe (PID: 324)
- mysetup.exe (PID: 2268)
- mysetup.tmp (PID: 2740)
Starts POWERSHELL.EXE for commands execution
- mysetup.tmp (PID: 2740)
Non-standard symbols in registry
- mysetup.tmp (PID: 2740)
- WINWORD.EXE (PID: 2336)
Reads the Windows owner or organization settings
- mysetup.tmp (PID: 2740)
INFO
Checks supported languages
- mysetup.exe (PID: 324)
- mysetup.tmp (PID: 1072)
- mysetup.exe (PID: 2268)
- mysetup.tmp (PID: 2740)
Reads the computer name
- mysetup.tmp (PID: 1072)
- mysetup.tmp (PID: 2740)
Create files in a temporary directory
- mysetup.exe (PID: 324)
- mysetup.exe (PID: 2268)
Manual execution by a user
- WINWORD.EXE (PID: 2336)
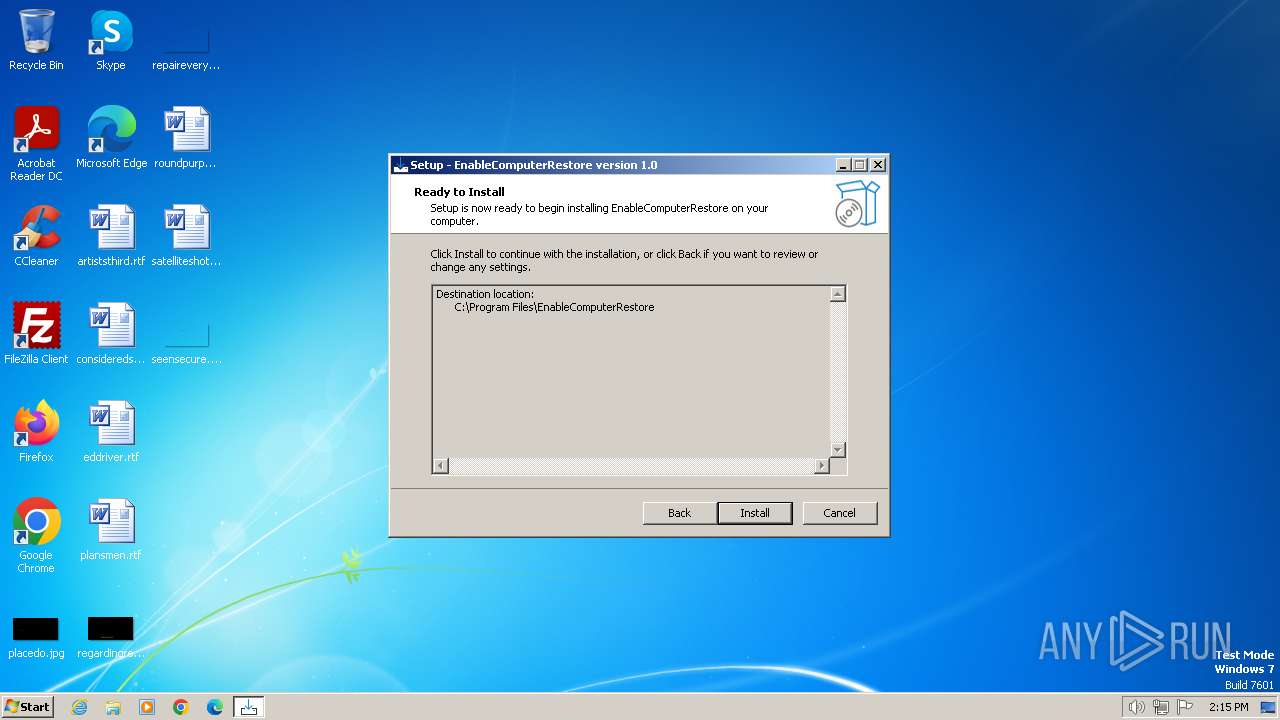
Creates a software uninstall entry
- mysetup.tmp (PID: 2740)
Creates files in the program directory
- mysetup.tmp (PID: 2740)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (53.5) |
|---|---|---|
| .exe | | | InstallShield setup (21) |
| .exe | | | Win32 EXE PECompact compressed (generic) (20.2) |
| .exe | | | Win32 Executable (generic) (2.1) |
| .exe | | | Win16/32 Executable Delphi generic (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:02:15 14:54:16+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741888 |
| InitializedDataSize: | 89600 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
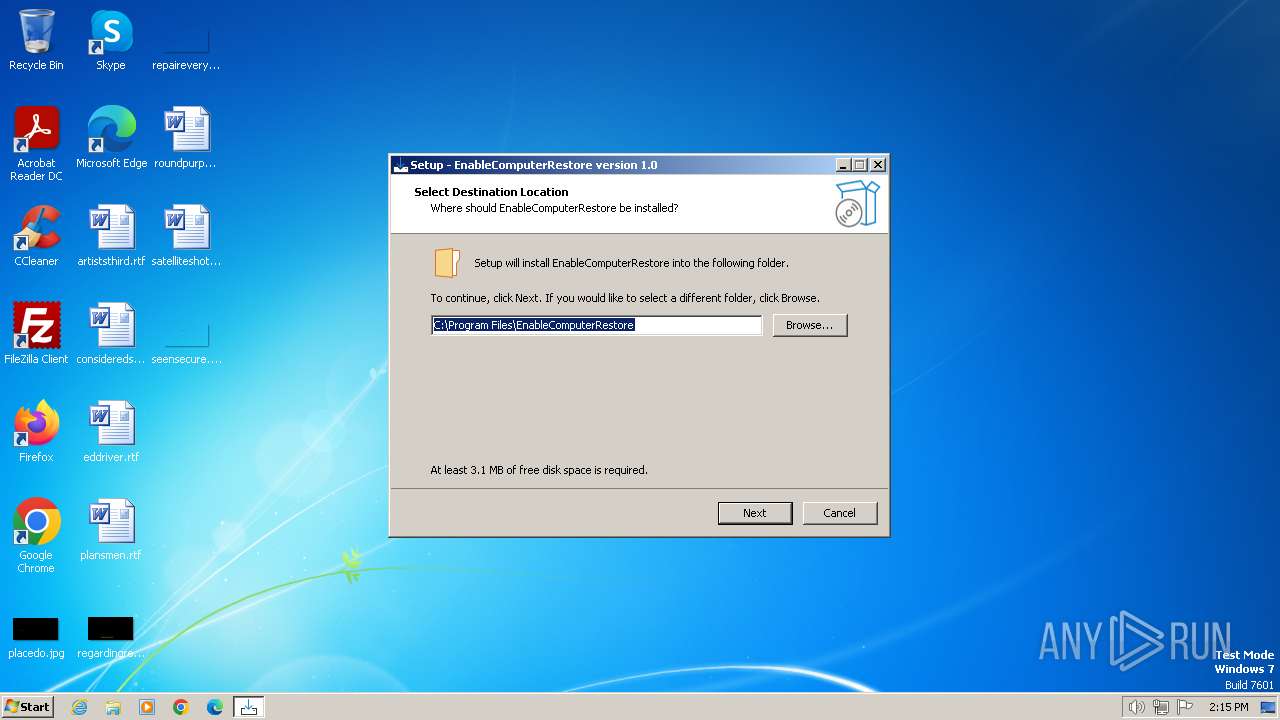
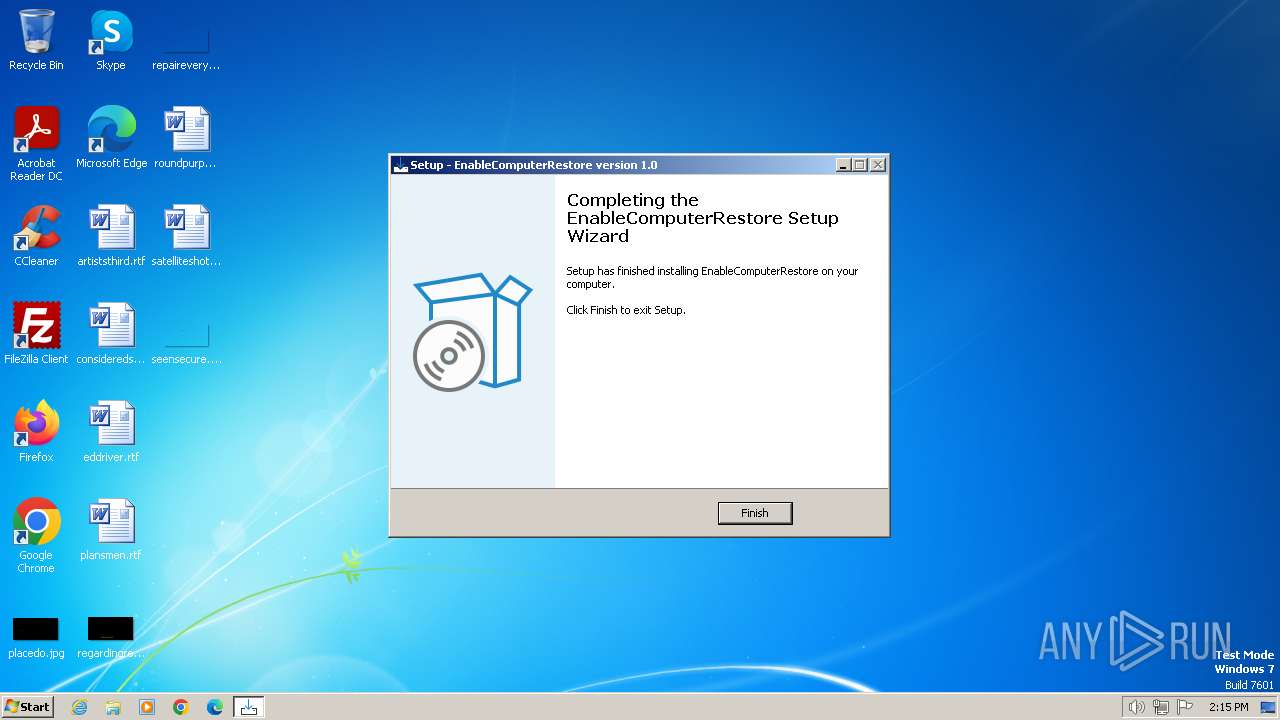
| FileDescription: | EnableComputerRestore Setup |
| FileVersion: | |
| LegalCopyright: | |
| OriginalFileName: | |
| ProductName: | EnableComputerRestore |
| ProductVersion: | 1.0 |
Total processes
47
Monitored processes
7
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 324 | "C:\Users\admin\AppData\Local\Temp\mysetup.exe" | C:\Users\admin\AppData\Local\Temp\mysetup.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: EnableComputerRestore Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1072 | "C:\Users\admin\AppData\Local\Temp\is-8OLAR.tmp\mysetup.tmp" /SL5="$22016A,832512,832512,C:\Users\admin\AppData\Local\Temp\mysetup.exe" | C:\Users\admin\AppData\Local\Temp\is-8OLAR.tmp\mysetup.tmp | — | mysetup.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2156 | C:\Windows\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2268 | "C:\Users\admin\AppData\Local\Temp\mysetup.exe" /SPAWNWND=$190140 /NOTIFYWND=$22016A | C:\Users\admin\AppData\Local\Temp\mysetup.exe | mysetup.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: EnableComputerRestore Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2336 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\roundpurposes.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2740 | "C:\Users\admin\AppData\Local\Temp\is-975PT.tmp\mysetup.tmp" /SL5="$1C0194,832512,832512,C:\Users\admin\AppData\Local\Temp\mysetup.exe" /SPAWNWND=$190140 /NOTIFYWND=$22016A | C:\Users\admin\AppData\Local\Temp\is-975PT.tmp\mysetup.tmp | mysetup.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3244 | "C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe" -ExecutionPolicy Bypass -Command "Enable-ComputerRestore -Drive 'C:'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | mysetup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
12 441
Read events
11 491
Write events
630
Delete events
320
Modification events
| (PID) Process: | (2740) mysetup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: B40A0000C8DED3A41297DA01 | |||
| (PID) Process: | (2740) mysetup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: AB835AF3A75C8E41C06215D7A1BCE6C4E4DF8FDC4A5670D1F47494B5AEC31A8B | |||
| (PID) Process: | (2740) mysetup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2740) mysetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EnableComputerRestore_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.2.2 | |||
| (PID) Process: | (2740) mysetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EnableComputerRestore_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\EnableComputerRestore | |||
| (PID) Process: | (2740) mysetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EnableComputerRestore_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\EnableComputerRestore\ | |||
| (PID) Process: | (2740) mysetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EnableComputerRestore_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: (Default) | |||
| (PID) Process: | (2740) mysetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EnableComputerRestore_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
| (PID) Process: | (2740) mysetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EnableComputerRestore_is1 |
| Operation: | write | Name: | Inno Setup: Language |
Value: default | |||
| (PID) Process: | (2740) mysetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\EnableComputerRestore_is1 |
| Operation: | write | Name: | DisplayName |
Value: EnableComputerRestore version 1.0 | |||
Executable files
5
Suspicious files
8
Text files
0
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8506.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2268 | mysetup.exe | C:\Users\admin\AppData\Local\Temp\is-975PT.tmp\mysetup.tmp | executable | |
MD5:AD8934B75793A3D9E62798825516276E | SHA256:0BD4C18DC4C86BA337D79D6990407C39B6BD4F7BFDA08737E8E681D2C37BC0C1 | |||
| 324 | mysetup.exe | C:\Users\admin\AppData\Local\Temp\is-8OLAR.tmp\mysetup.tmp | executable | |
MD5:AD8934B75793A3D9E62798825516276E | SHA256:0BD4C18DC4C86BA337D79D6990407C39B6BD4F7BFDA08737E8E681D2C37BC0C1 | |||
| 3244 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1bff3c.TMP | binary | |
MD5:0268C3470C936E6FBAC2945B9E1C2099 | SHA256:DF2AF58E8879B48826D8A418ED3B02CC8D484BCFC231C5B7A11BD153ED3998E9 | |||
| 2740 | mysetup.tmp | C:\Program Files\EnableComputerRestore\is-VO7OO.tmp | executable | |
MD5:95D8E4D0F94A062F8AD4570E6BE4BD17 | SHA256:56FCF6BF51870E9ED32A2BD6F018CE57F5DD277BDD1B35CBCCF0C4541A519B5C | |||
| 3244 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\IQR3B1KCYM617H2J5CQS.temp | binary | |
MD5:42E3956892291F5EE35E1B989213EF05 | SHA256:D4E6947871B5FD00AD32F8707479DD6EC92AB65D8C6D157B1C0C3D99D575E468 | |||
| 2740 | mysetup.tmp | C:\Program Files\EnableComputerRestore\unins000.exe | executable | |
MD5:95D8E4D0F94A062F8AD4570E6BE4BD17 | SHA256:56FCF6BF51870E9ED32A2BD6F018CE57F5DD277BDD1B35CBCCF0C4541A519B5C | |||
| 2740 | mysetup.tmp | C:\Program Files\EnableComputerRestore\unins000.dat | binary | |
MD5:B46D4582DE876204142E2C8086C186B1 | SHA256:13577AF87D7BE54E54CCD30A3F58B072E40A2D026DBEBCC675E27EAFCA2B299B | |||
| 3244 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | dbf | |
MD5:446DD1CF97EABA21CF14D03AEBC79F27 | SHA256:A7DE5177C68A64BD48B36D49E2853799F4EBCFA8E4761F7CC472F333DC5F65CF | |||
| 3244 | powershell.exe | C:\Users\admin\AppData\Local\Temp\2xsr5tev.axp.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | unknown |