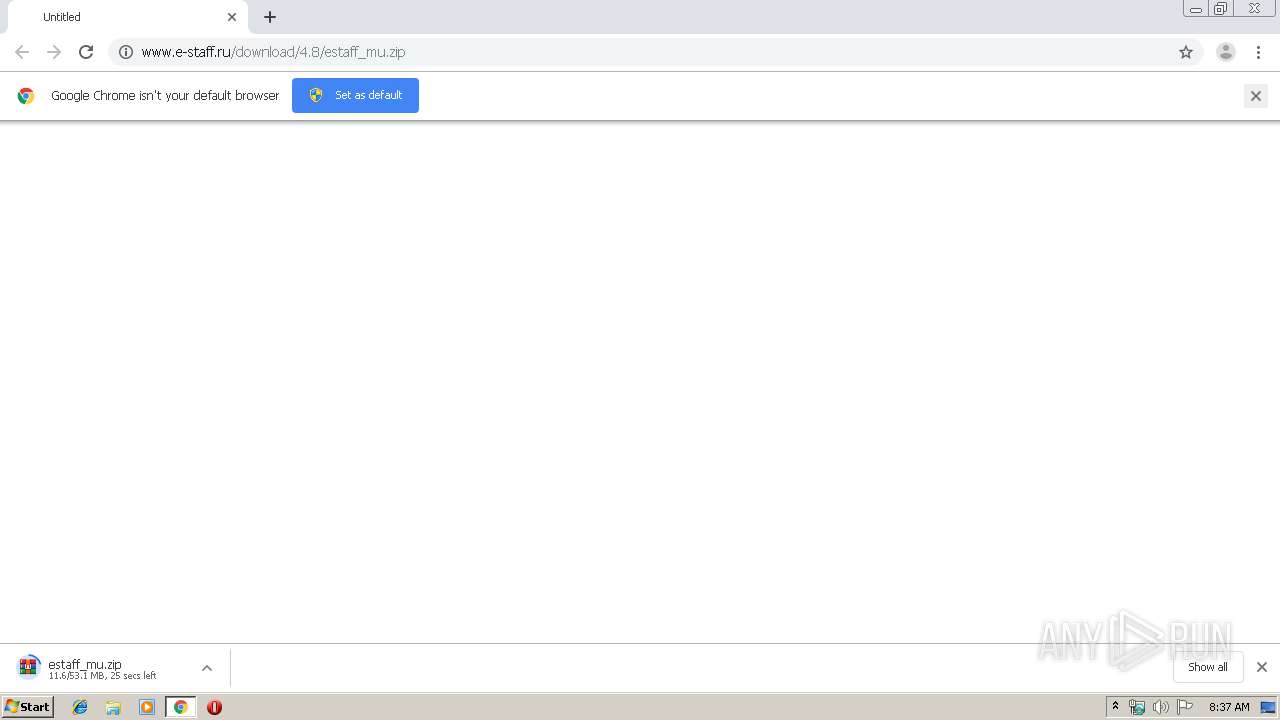
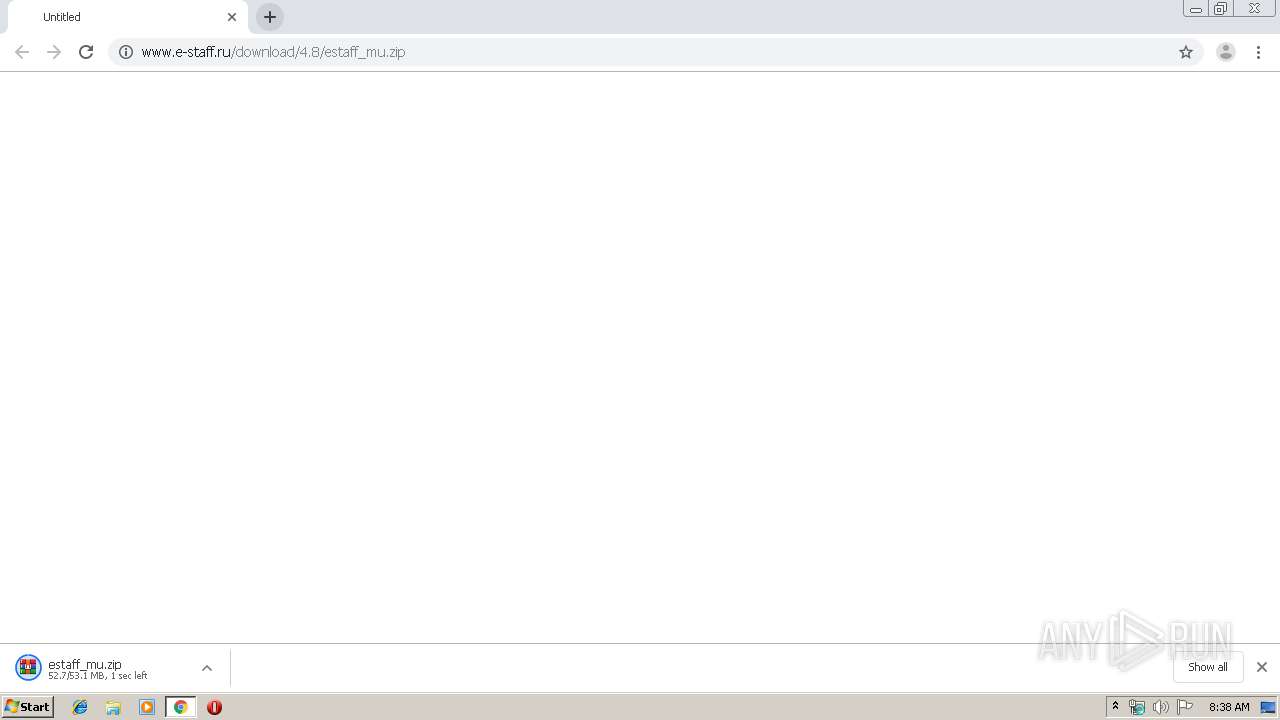
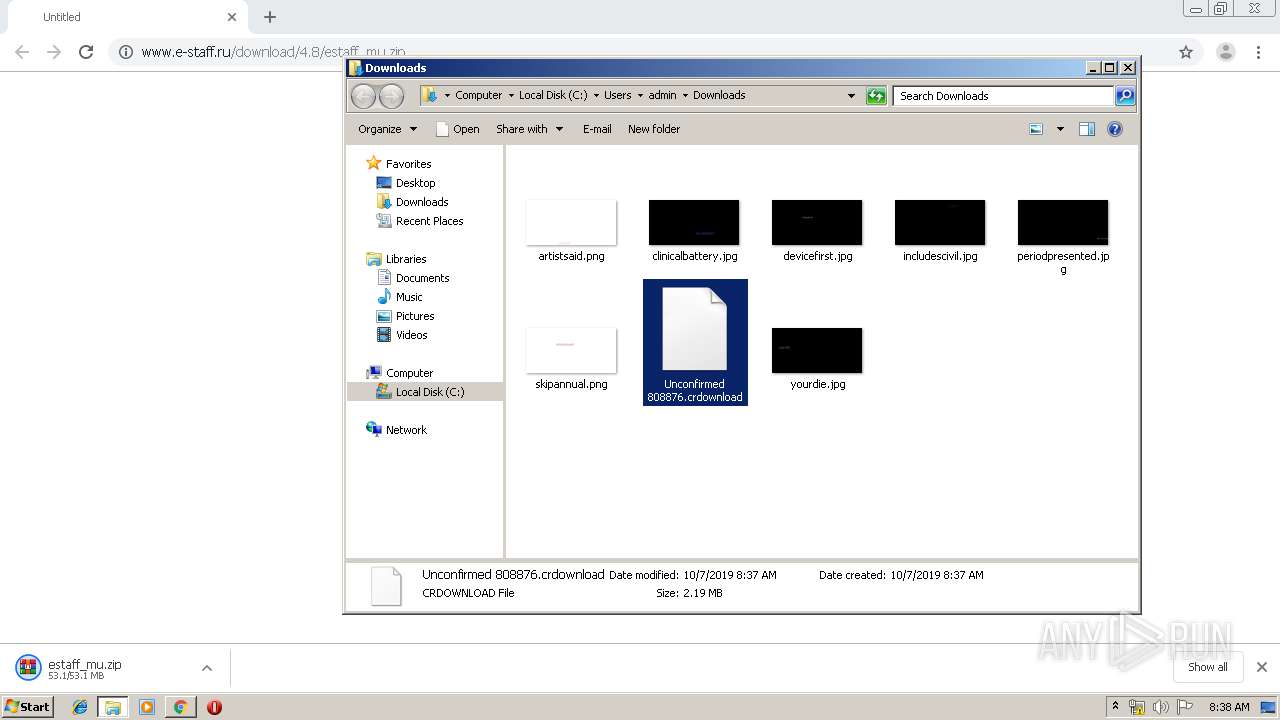
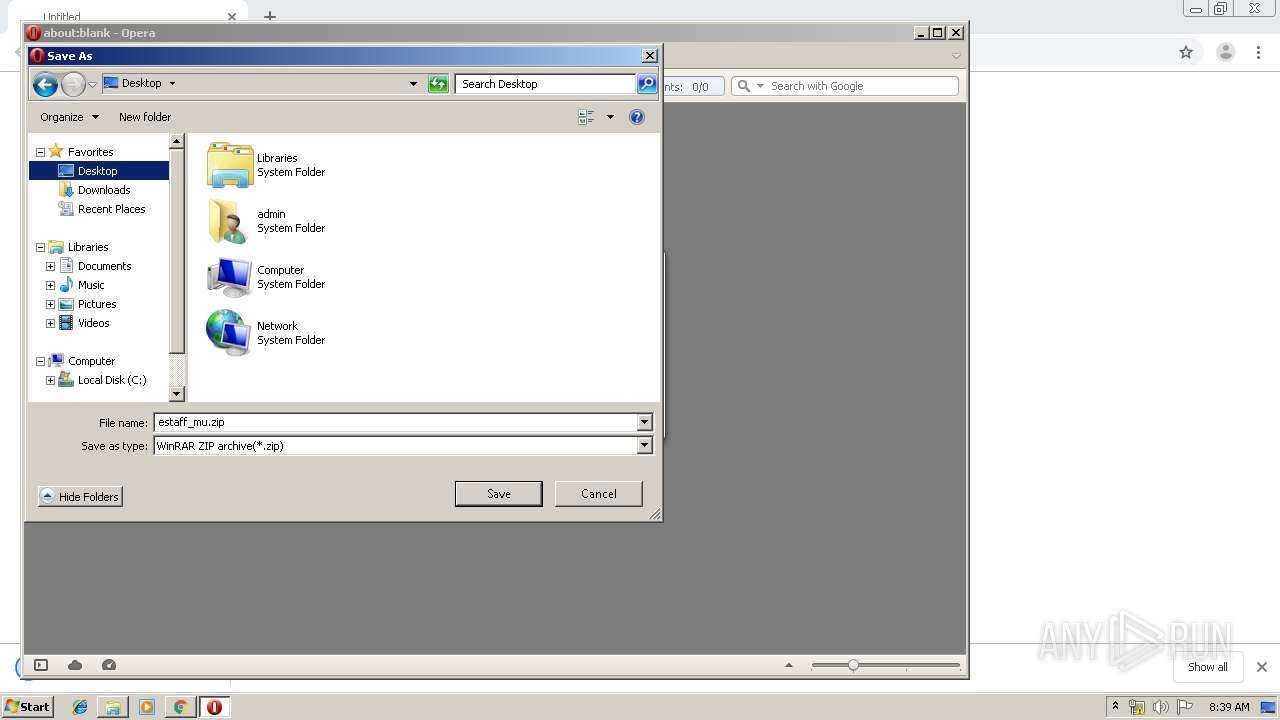
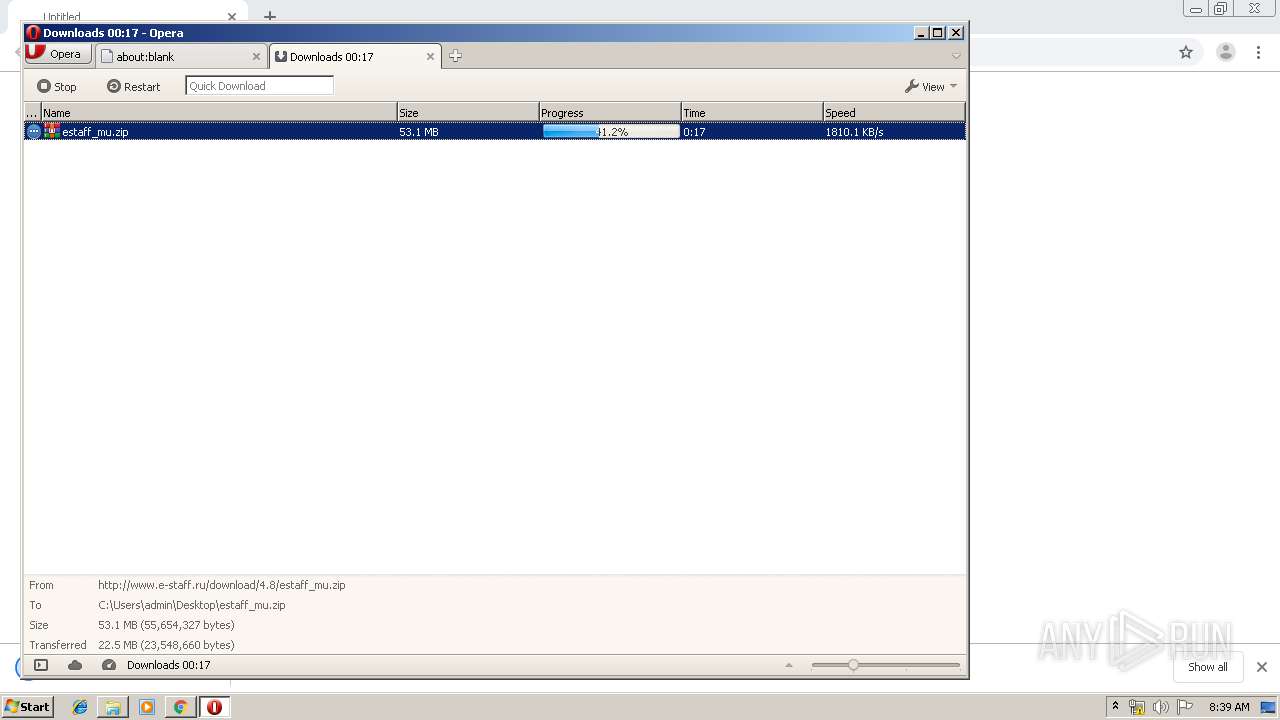
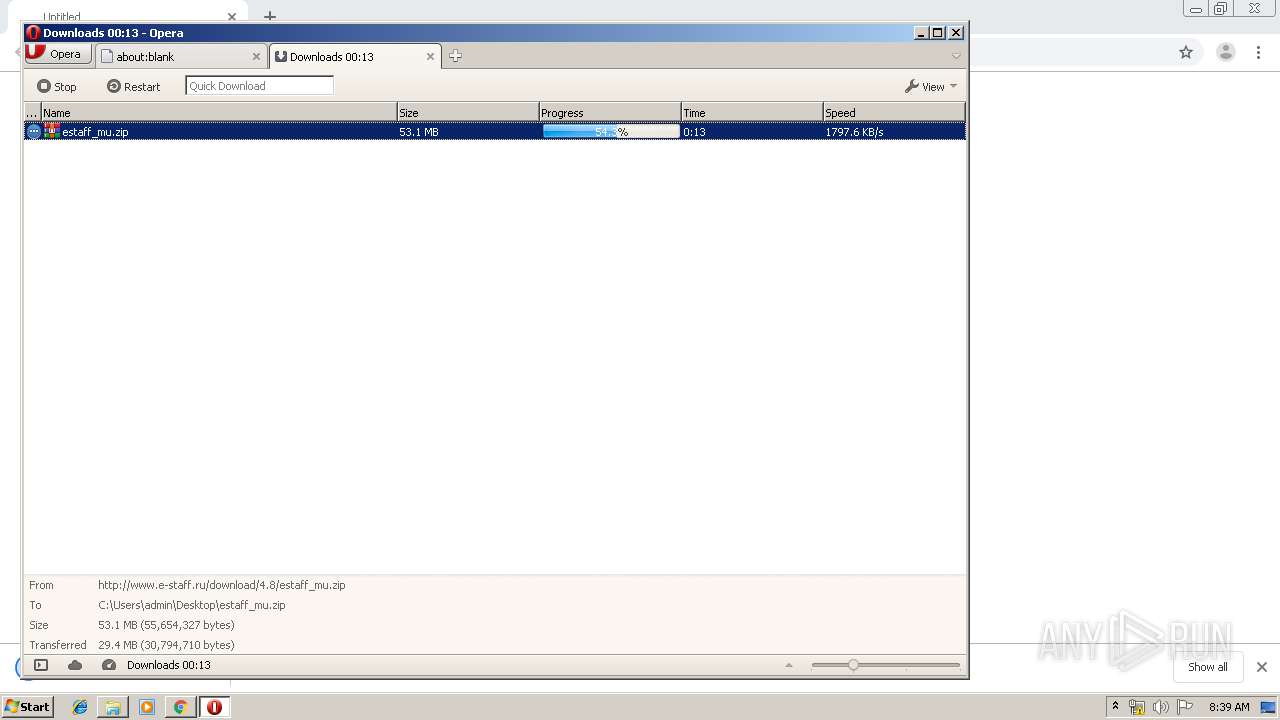
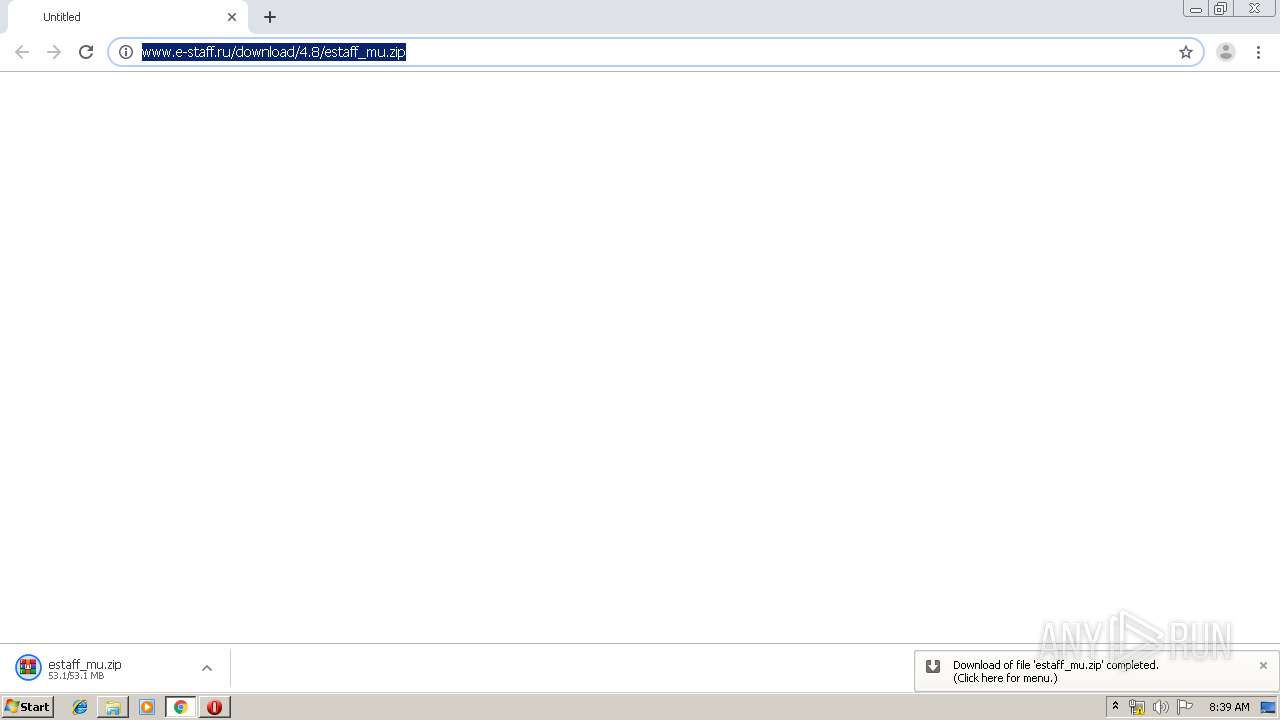
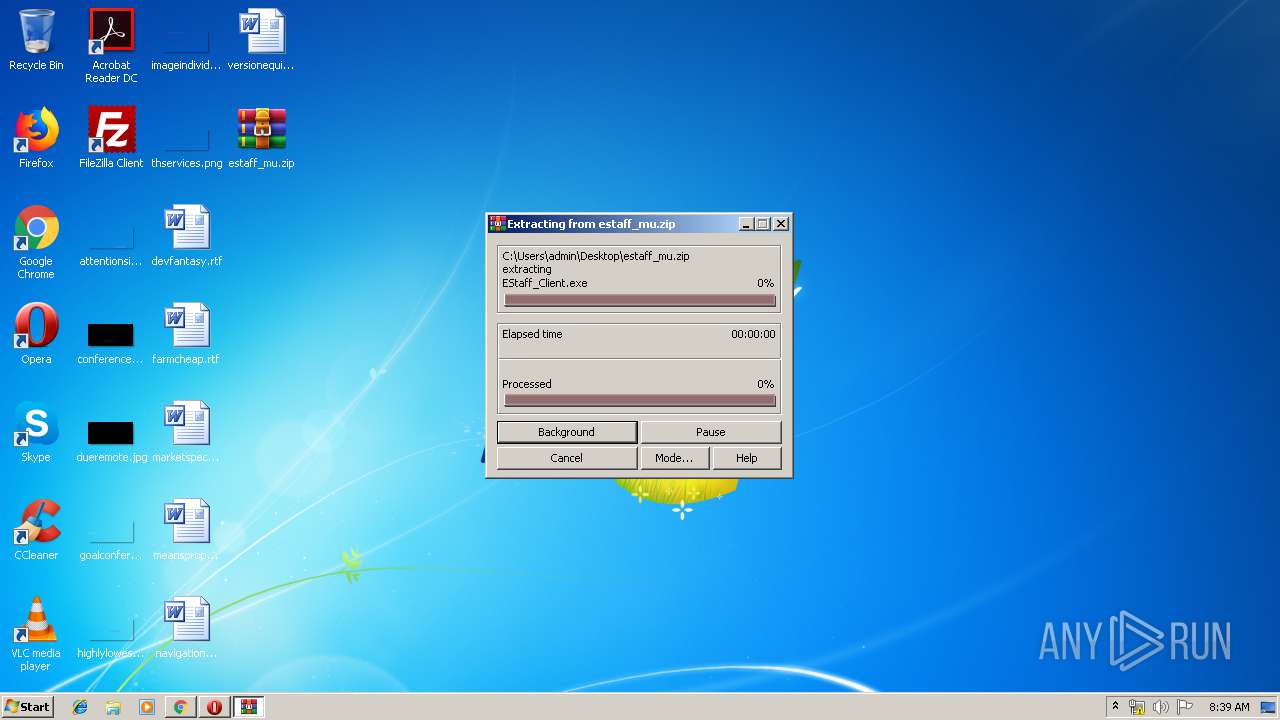
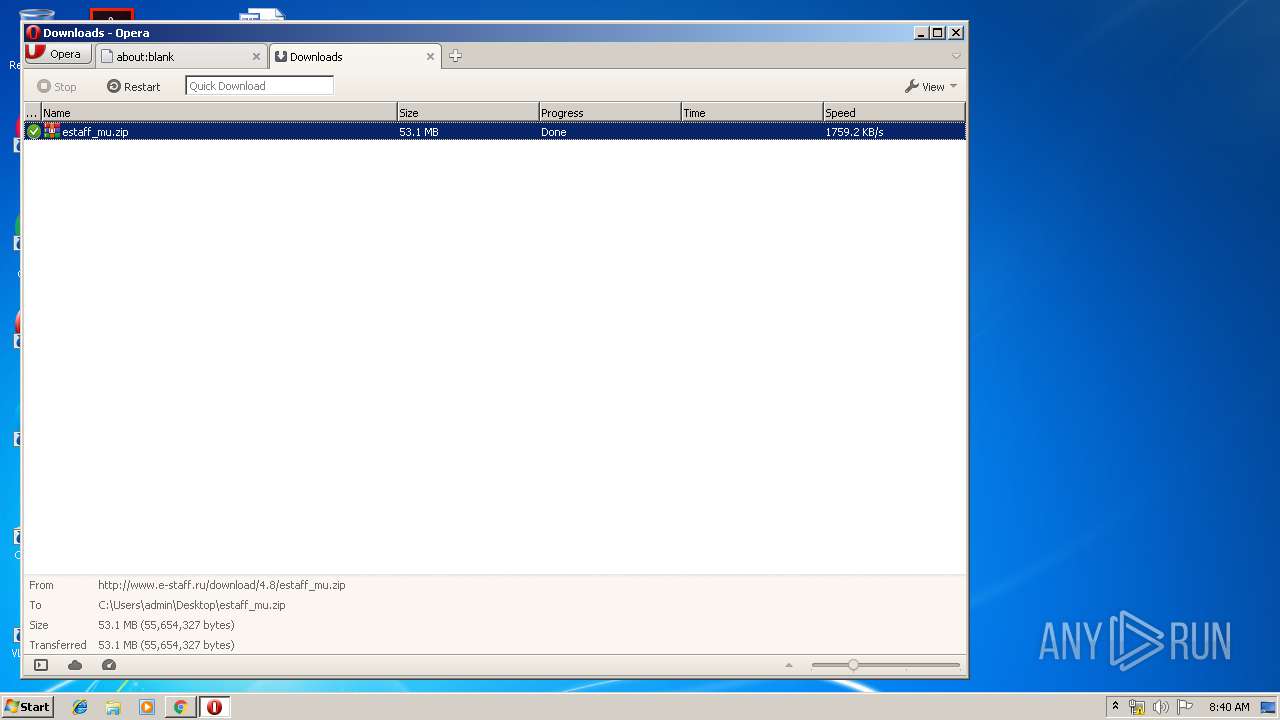
| URL: | http://www.e-staff.ru/download/4.8/estaff_mu.zip |
| Full analysis: | https://app.any.run/tasks/c949243e-e5a0-4b44-ad8c-fac50f090c2c |
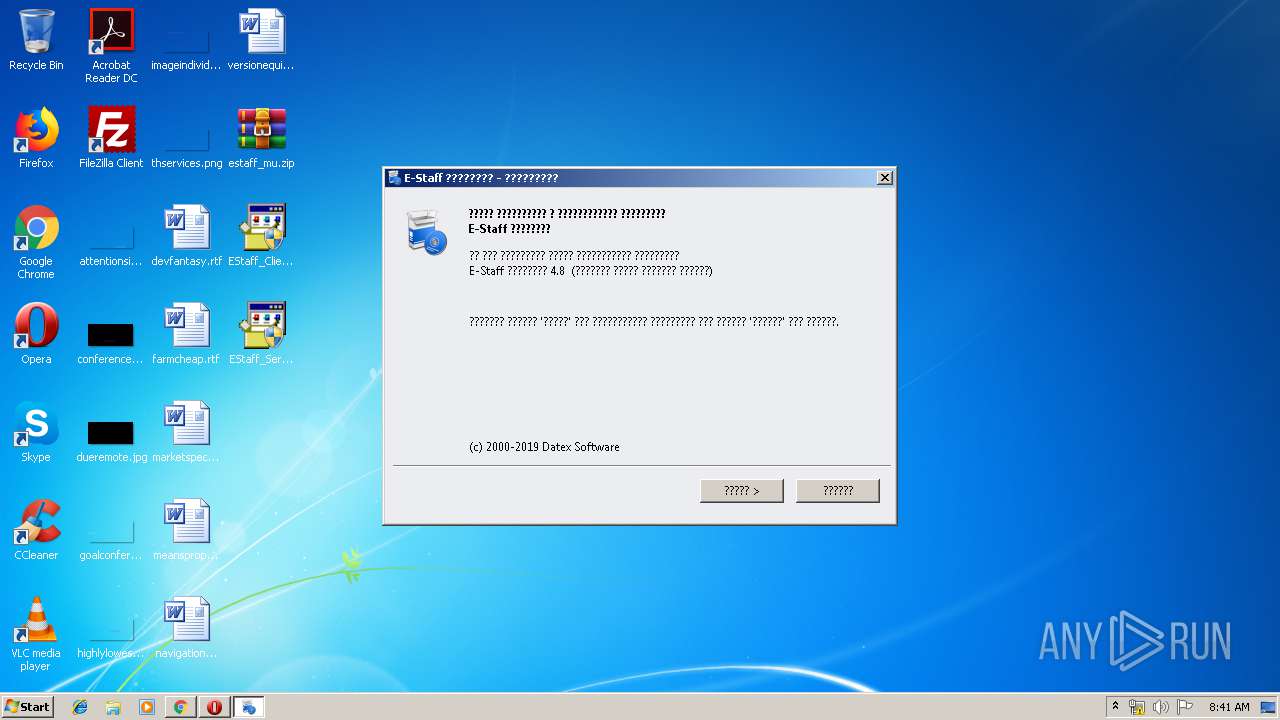
| Verdict: | Malicious activity |
| Analysis date: | October 07, 2019, 07:37:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 5DEB1D5DCC421D07DB4C56E783F3839C |
| SHA1: | 6DBA7D38FC108A9DAE134EF4D639E8B3396E191F |
| SHA256: | D5868D70E5E0E366825C23377CD14209C7C82875E626464C4CBD4971692A9423 |
| SSDEEP: | 3:N1KJS4kmQK8SLJkRpHfkMVn:Cc4kkykMV |
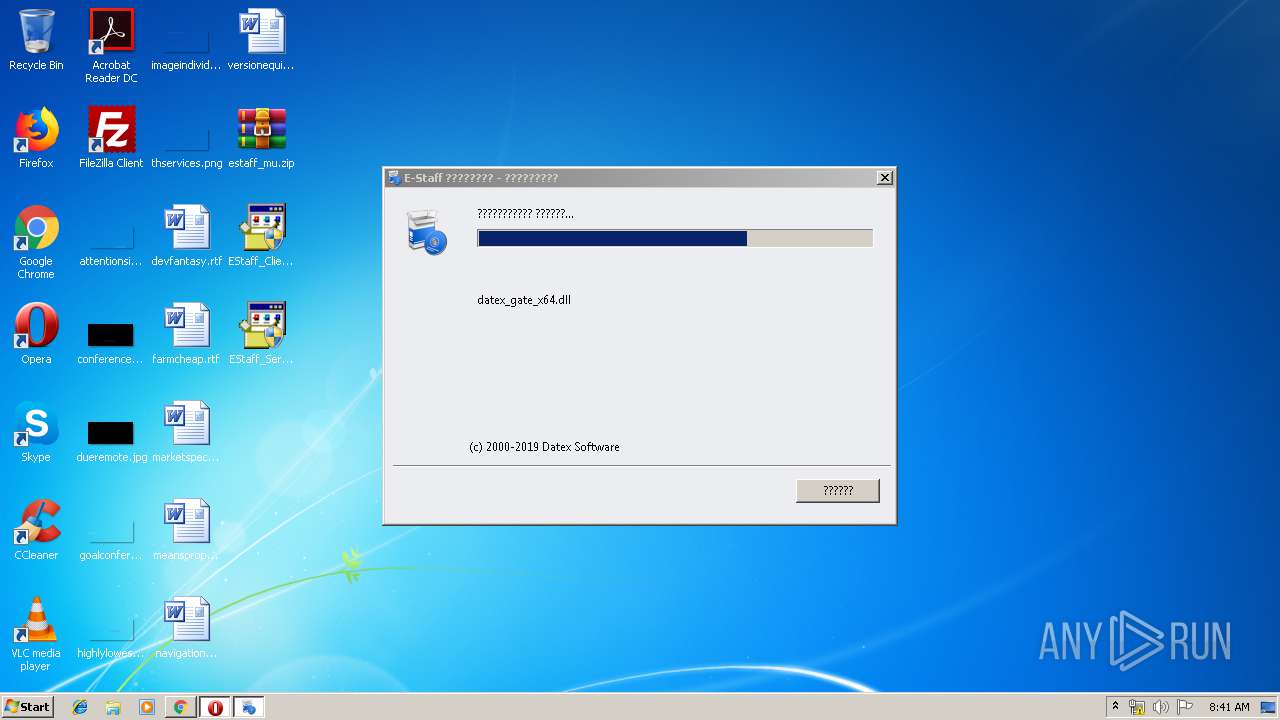
MALICIOUS
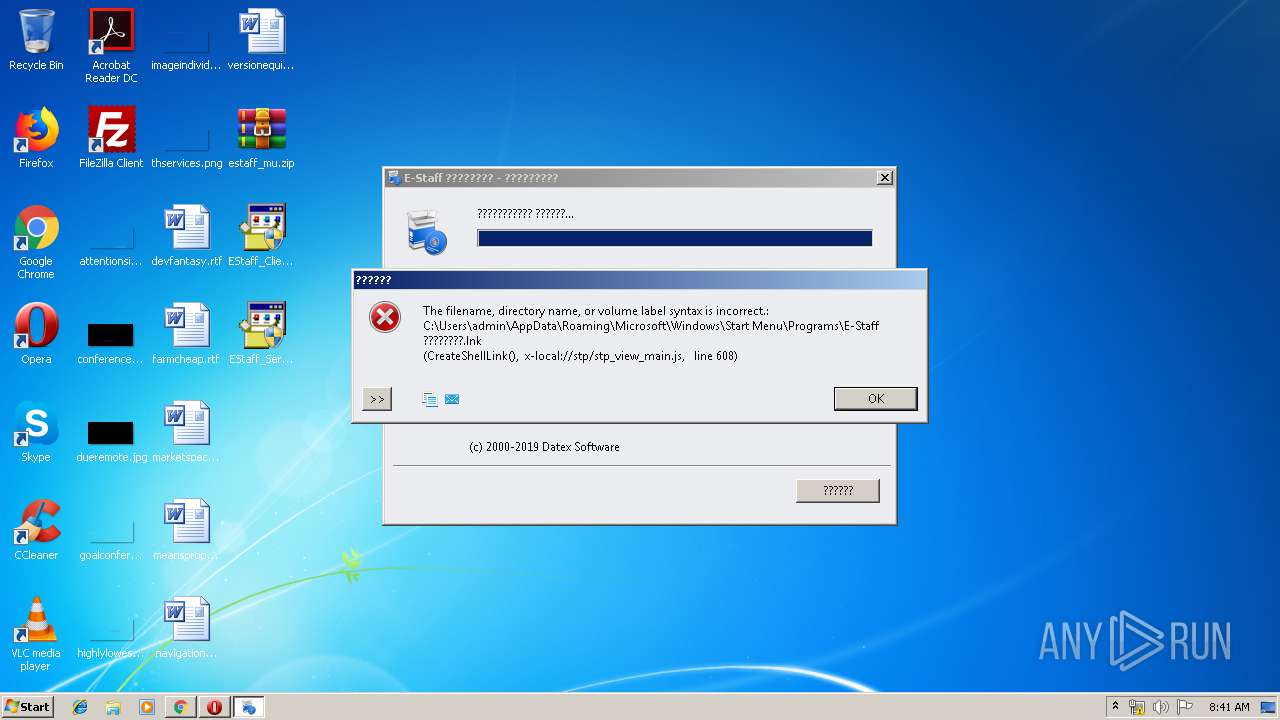
Application was dropped or rewritten from another process
- EStaff_Client.exe (PID: 1444)
- SpXml.exe (PID: 2388)
- EStaff_Client.exe (PID: 632)
- SpXml.exe (PID: 2272)
Loads dropped or rewritten executable
- SpXml.exe (PID: 2388)
- SpXml.exe (PID: 2272)
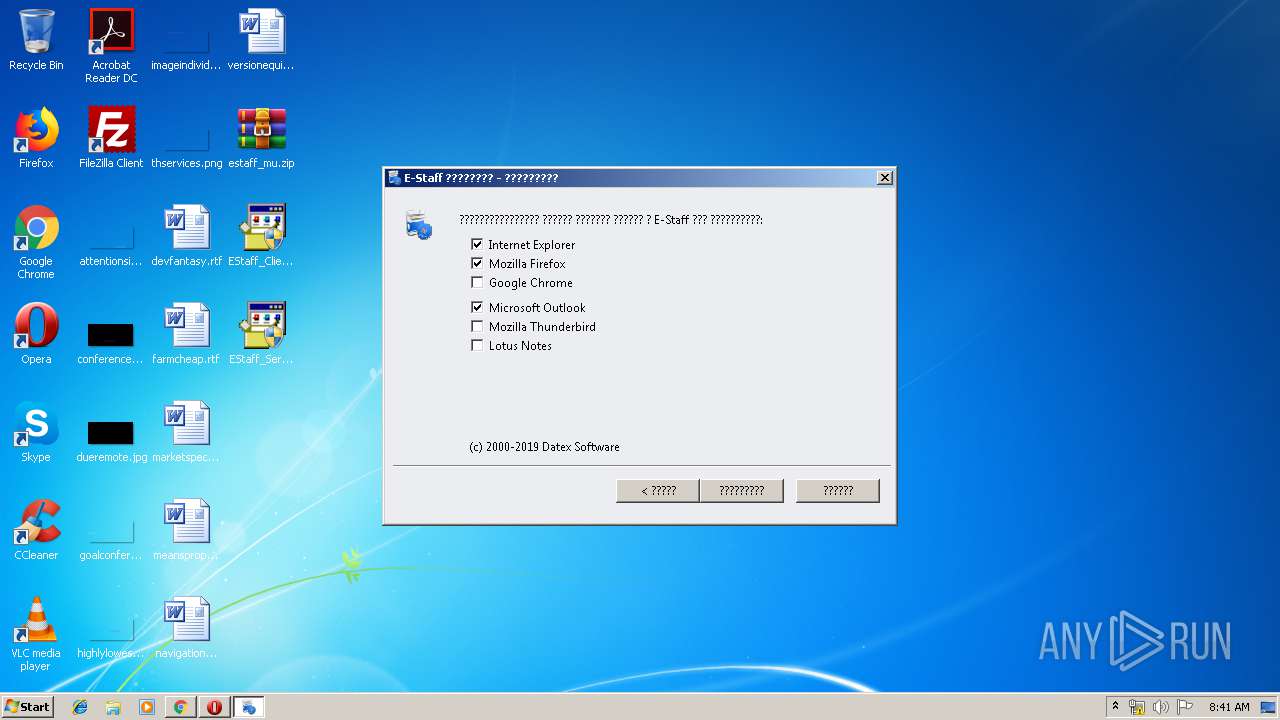
Actions looks like stealing of personal data
- EStaff_Client.exe (PID: 632)
- SpXml.exe (PID: 2388)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2968)
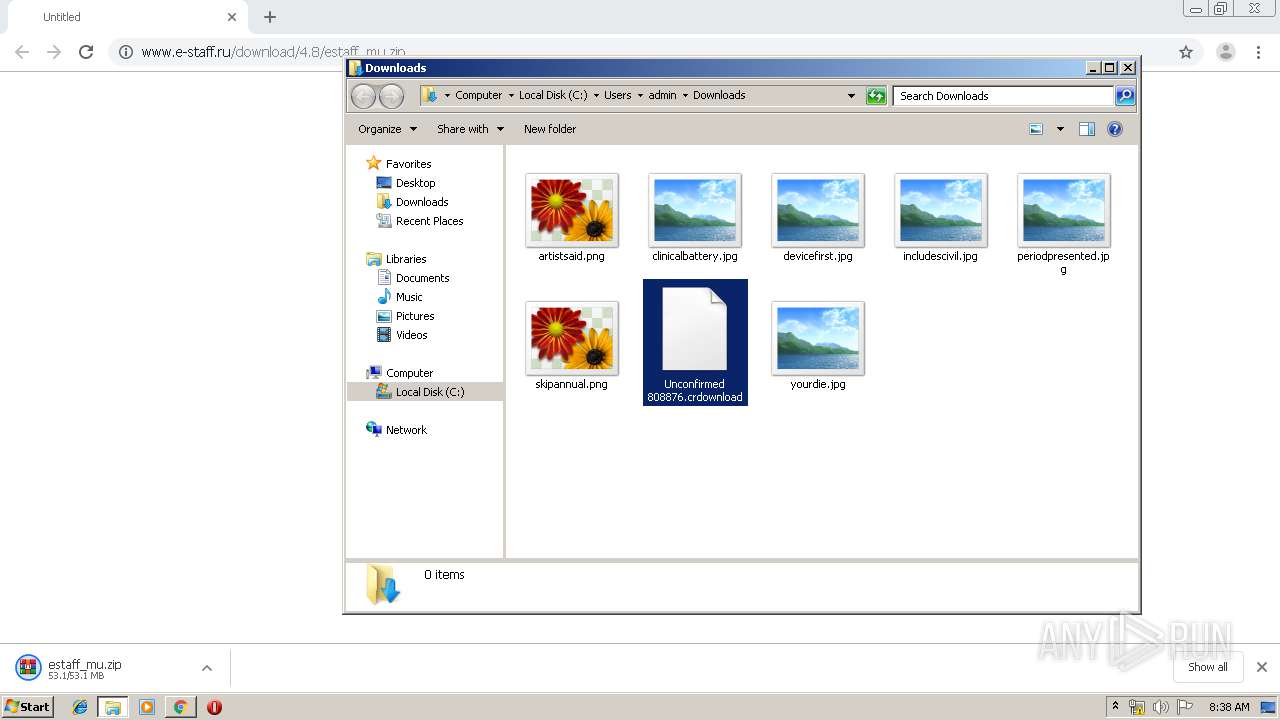
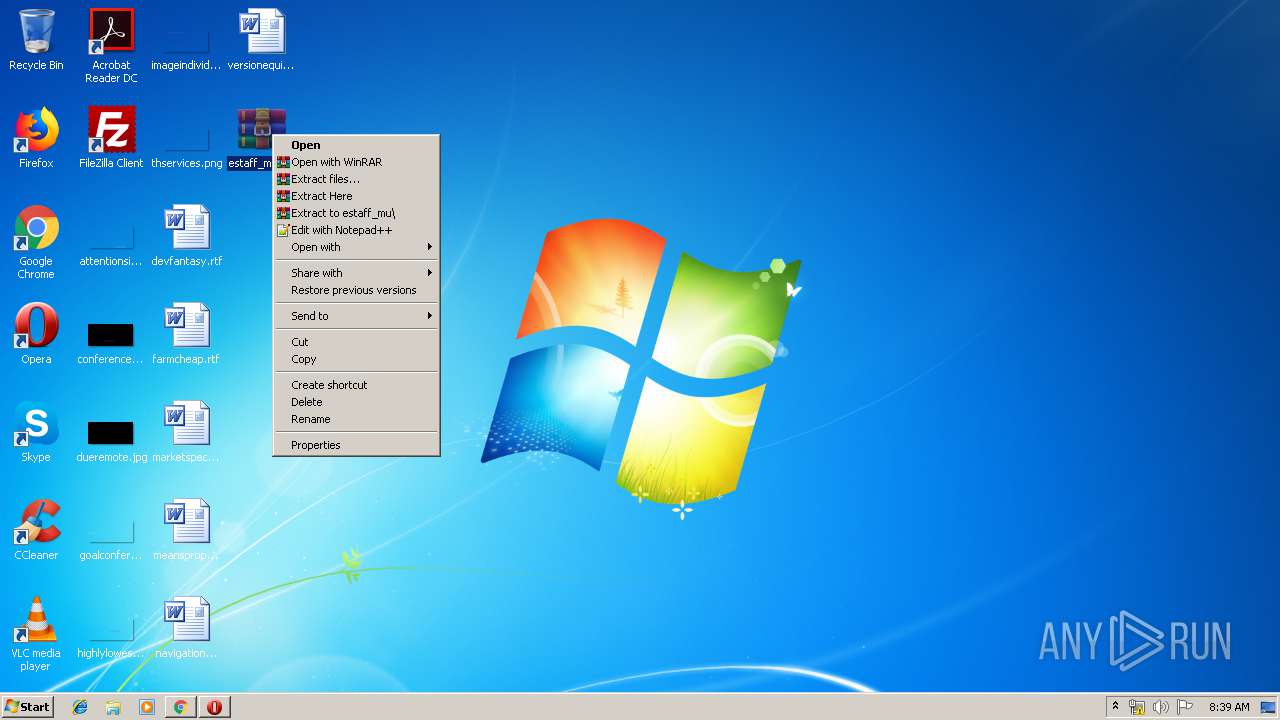
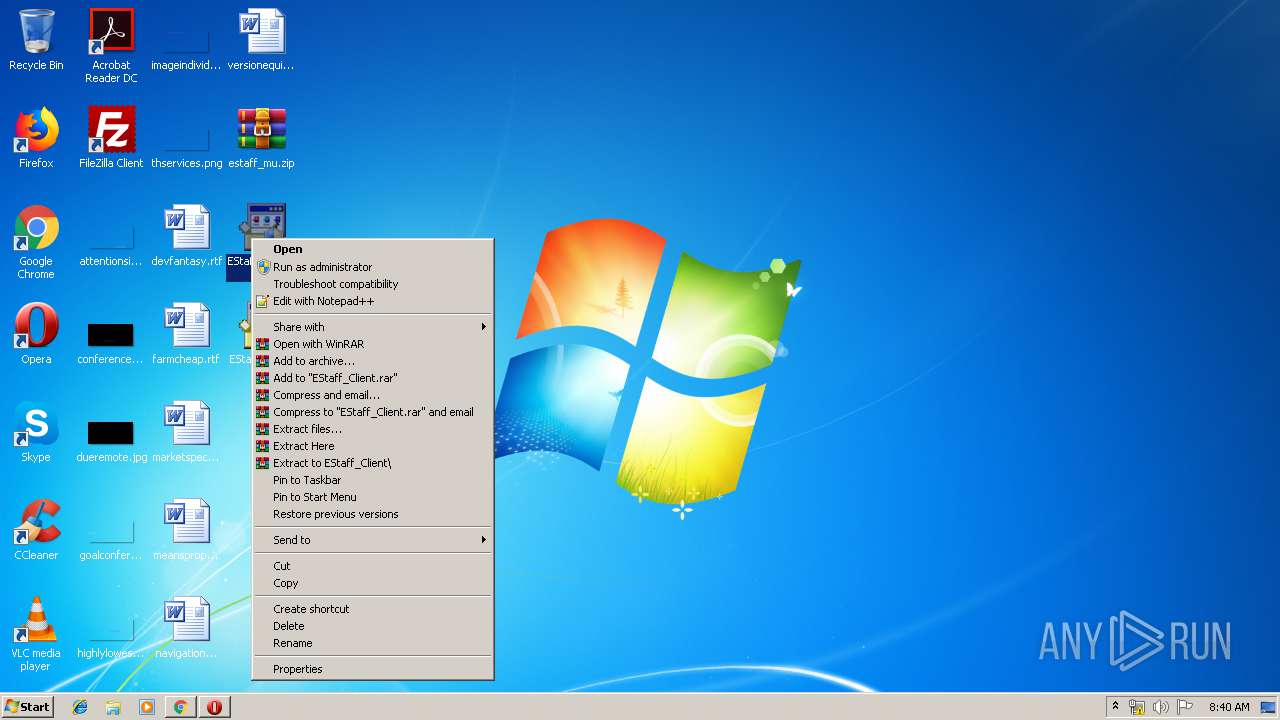
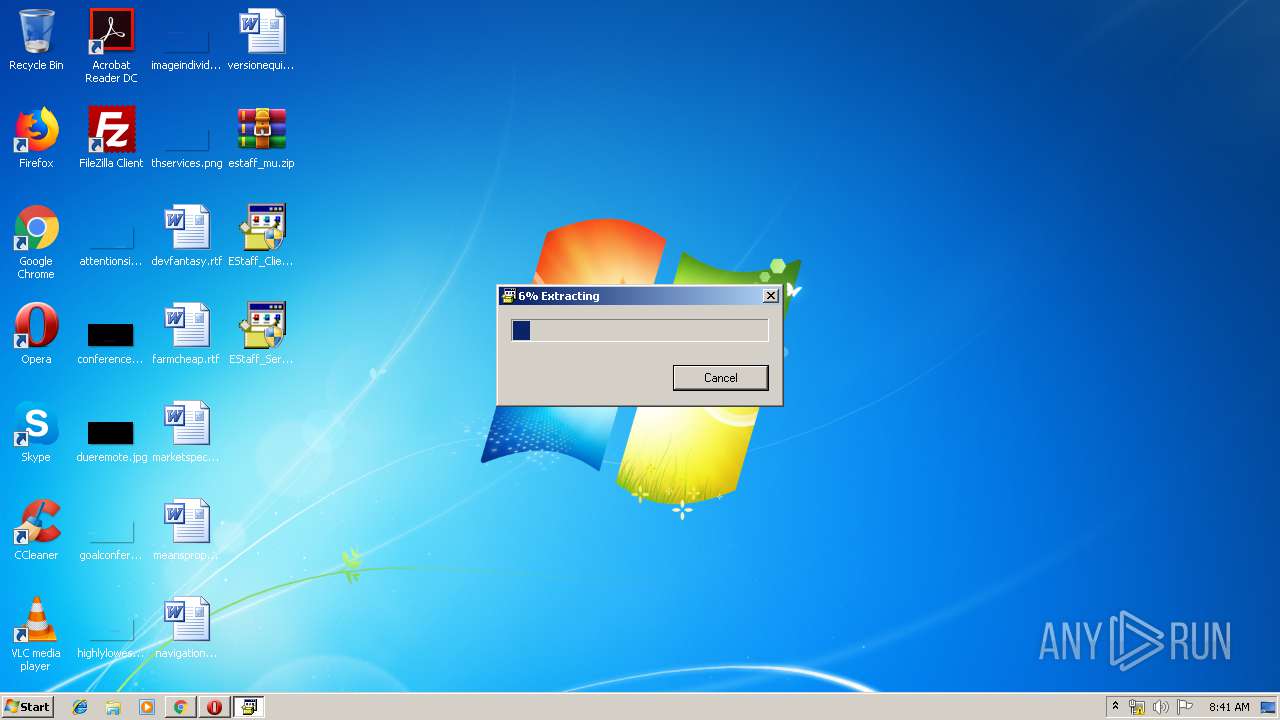
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2400)
- EStaff_Client.exe (PID: 632)
- SpXml.exe (PID: 2388)
Creates files in the program directory
- SpXml.exe (PID: 2388)
INFO
Application launched itself
- chrome.exe (PID: 2968)
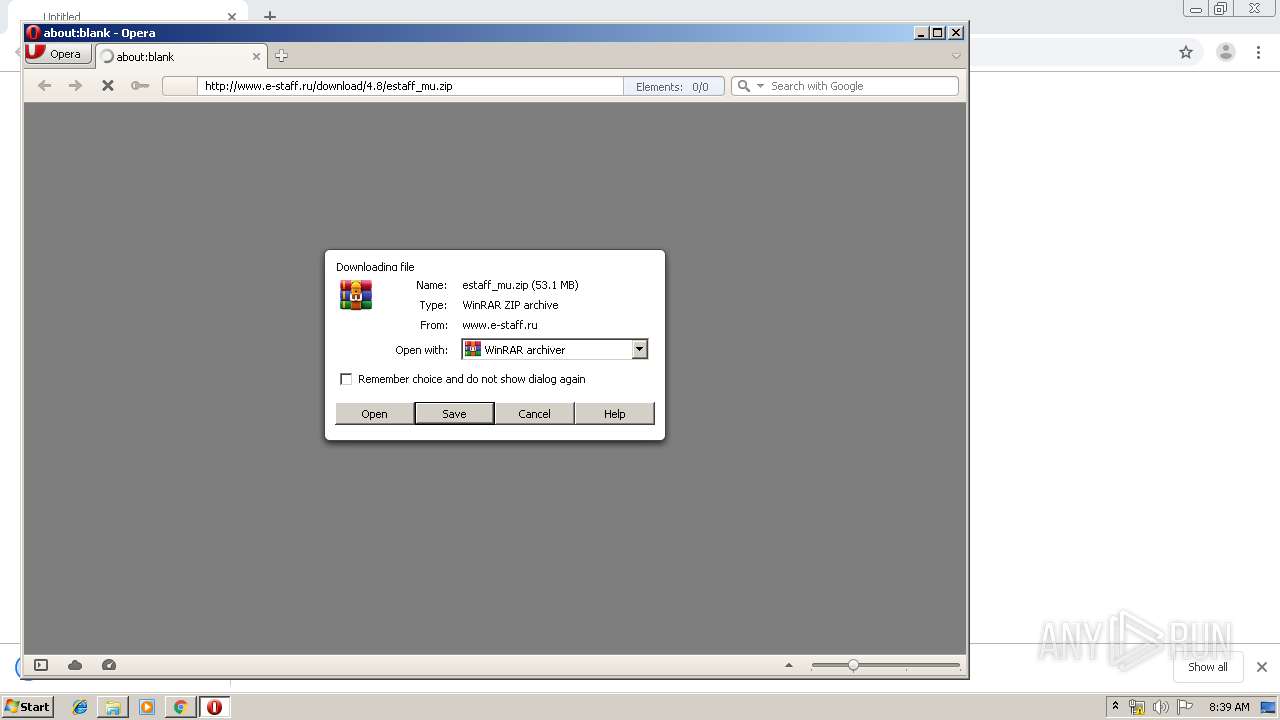
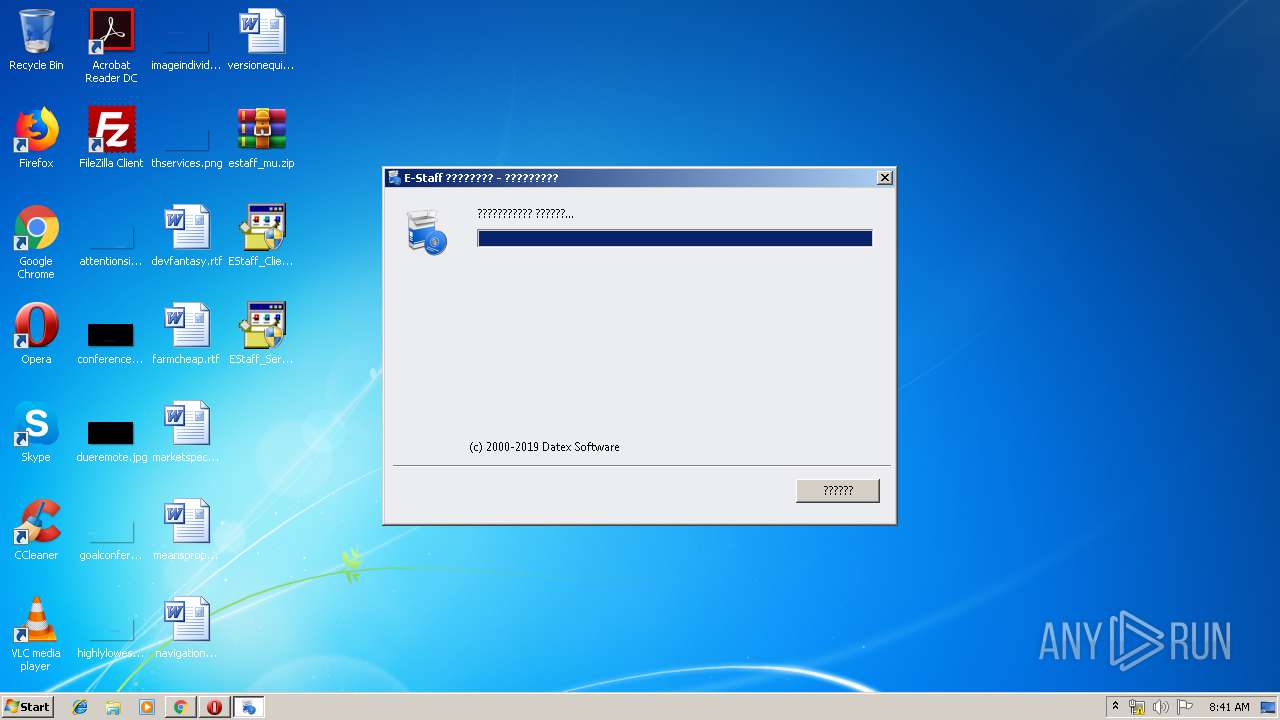
Manual execution by user
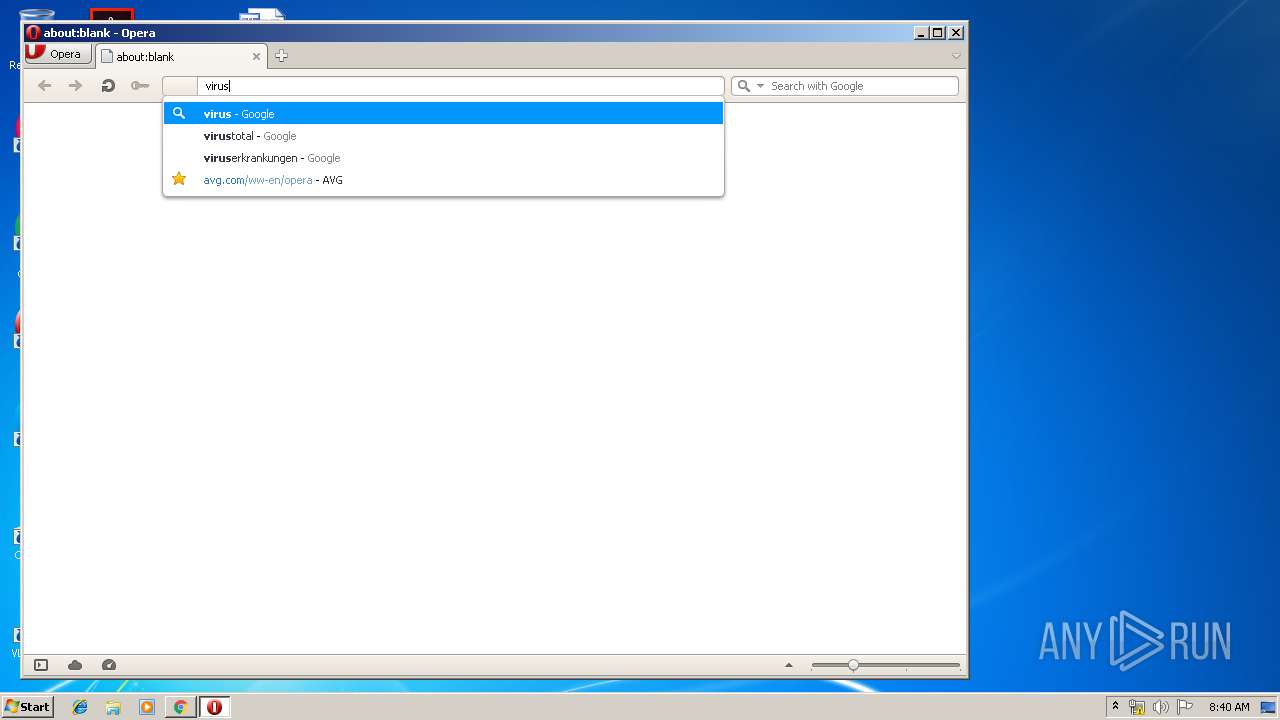
- opera.exe (PID: 3416)
- WinRAR.exe (PID: 2400)
- EStaff_Client.exe (PID: 1444)
- EStaff_Client.exe (PID: 632)
- EStaff_Server.exe (PID: 1576)
- EStaff_Server.exe (PID: 3852)
Reads the hosts file
- chrome.exe (PID: 2968)
- chrome.exe (PID: 1440)
Reads Internet Cache Settings
- opera.exe (PID: 3416)
- chrome.exe (PID: 2968)
Creates files in the user directory
- chrome.exe (PID: 2968)
- opera.exe (PID: 3416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
83
Monitored processes
35
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,12156623259375412854,14272541740186981852,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12497042578637431442 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4100 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
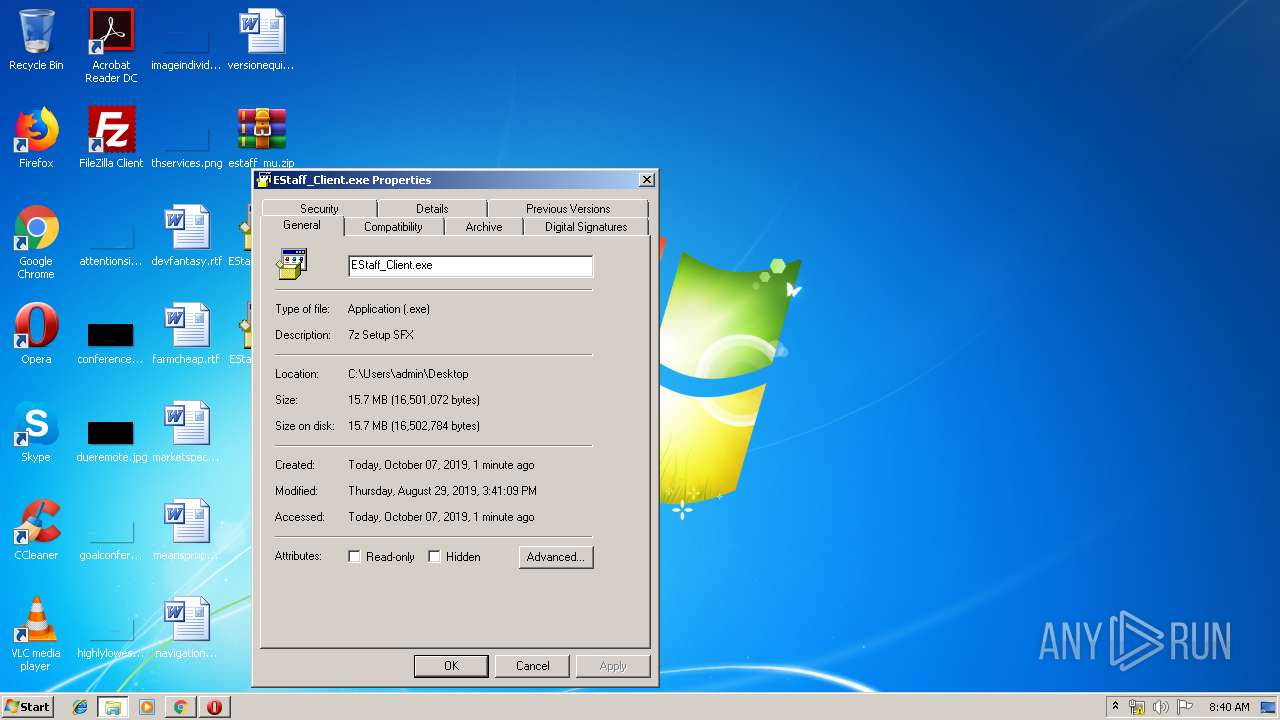
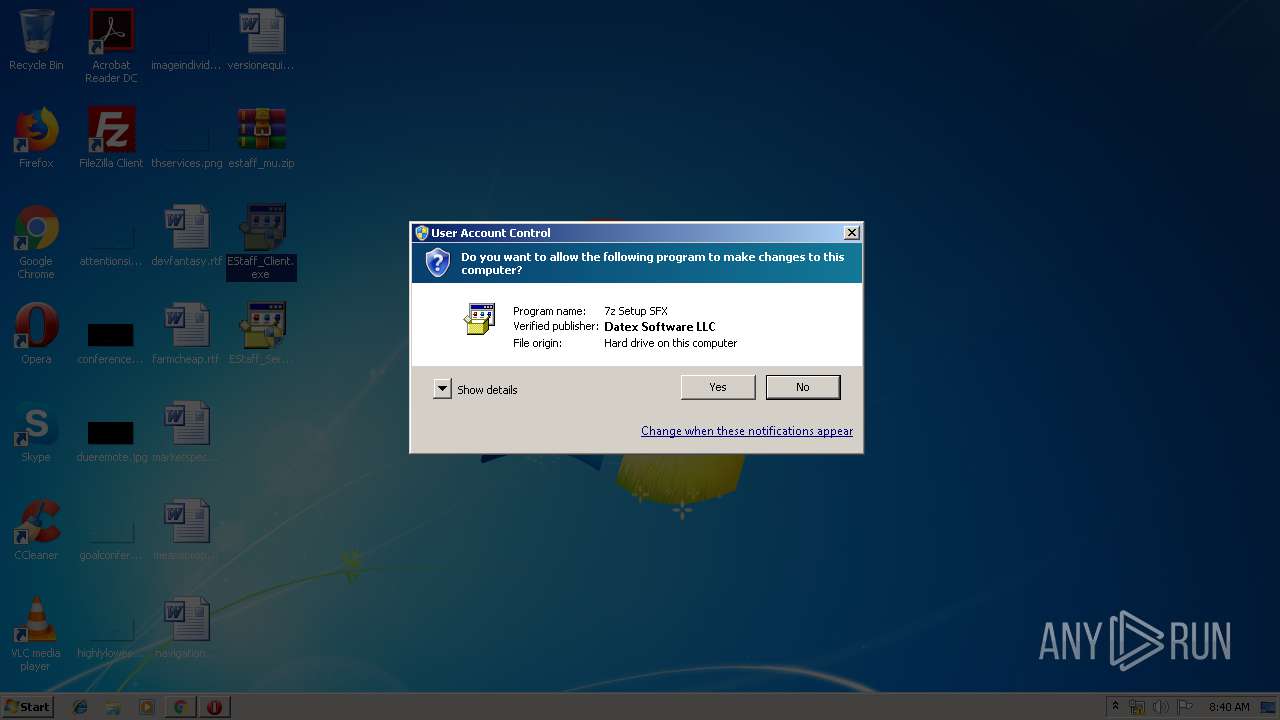
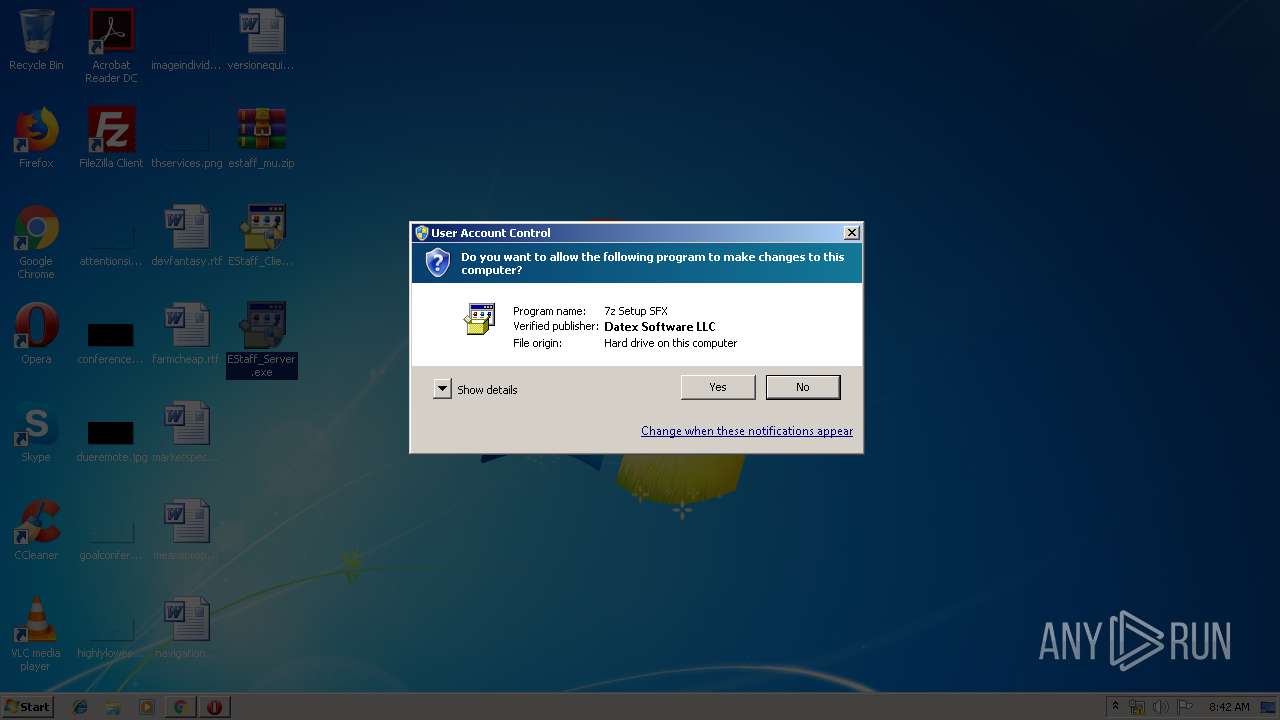
| 632 | "C:\Users\admin\Desktop\EStaff_Client.exe" | C:\Users\admin\Desktop\EStaff_Client.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7z Setup SFX Exit code: 0 Version: 9.20 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,12156623259375412854,14272541740186981852,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6771794850560678651 --mojo-platform-channel-handle=3708 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,12156623259375412854,14272541740186981852,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=3049465100696955218 --mojo-platform-channel-handle=1496 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1444 | "C:\Users\admin\Desktop\EStaff_Client.exe" | C:\Users\admin\Desktop\EStaff_Client.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7z Setup SFX Exit code: 3221226540 Version: 9.20 Modules
| |||||||||||||||
| 1524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,12156623259375412854,14272541740186981852,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10040183172459276023 --mojo-platform-channel-handle=4704 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1576 | "C:\Users\admin\Desktop\EStaff_Server.exe" | C:\Users\admin\Desktop\EStaff_Server.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7z Setup SFX Exit code: 3221226540 Version: 9.20 Modules
| |||||||||||||||
| 2272 | .\SpXml.exe | C:\Users\admin\AppData\Local\Temp\7zS7D61.tmp\SpXml.exe | — | EStaff_Server.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=984,12156623259375412854,14272541740186981852,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3626419582790793618 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3728 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2388 | .\SpXml.exe | C:\Users\admin\AppData\Local\Temp\7zS6682.tmp\SpXml.exe | EStaff_Client.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
1 686
Read events
1 461
Write events
218
Delete events
7
Modification events
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2744) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2968-13214907442609000 |
Value: 259 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2968) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
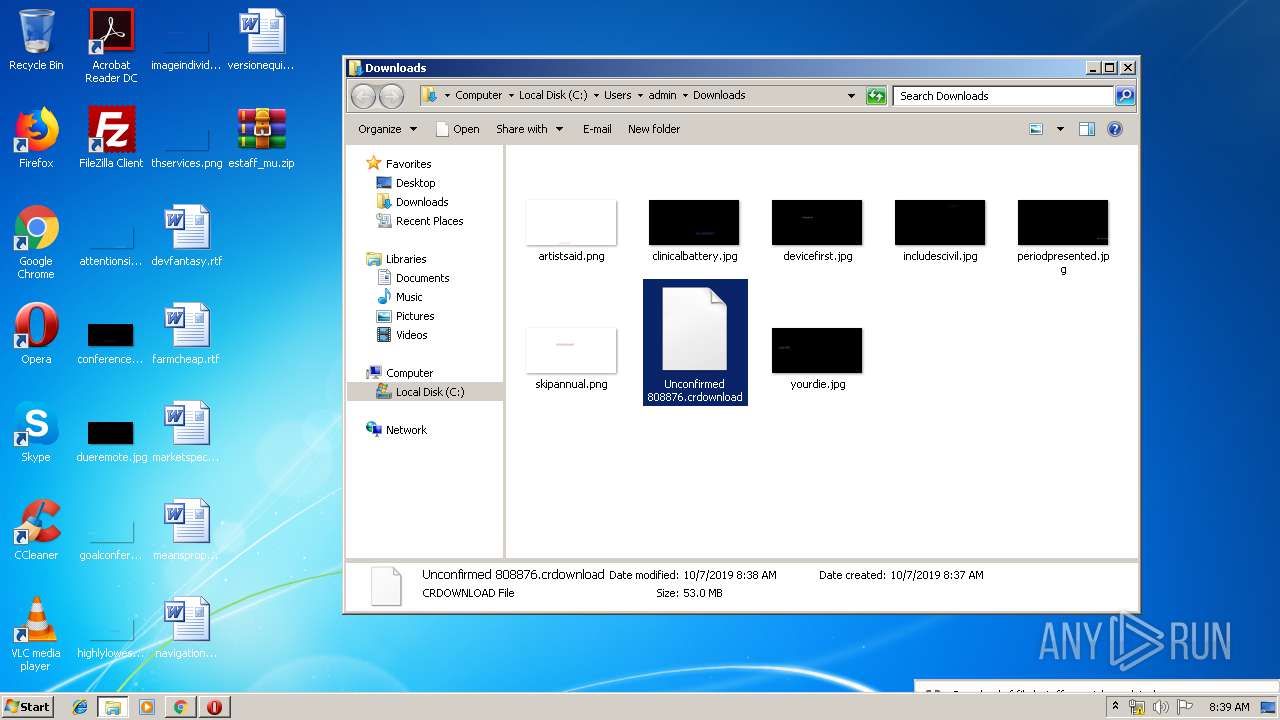
Executable files
35
Suspicious files
144
Text files
3 641
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e423f888-4361-4775-8486-1b1de2b159c3.tmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2968 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFf169c.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
44
DNS requests
31
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3416 | opera.exe | GET | 302 | 216.239.36.21:80 | http://virustotal.com/ | US | — | — | whitelisted |
3416 | opera.exe | GET | 200 | 172.217.22.14:80 | http://clients1.google.com/complete/search?q=vir&client=opera-suggest-omnibox&hl=de | US | text | 142 b | whitelisted |
3416 | opera.exe | GET | 200 | 93.184.220.29:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 528 b | whitelisted |
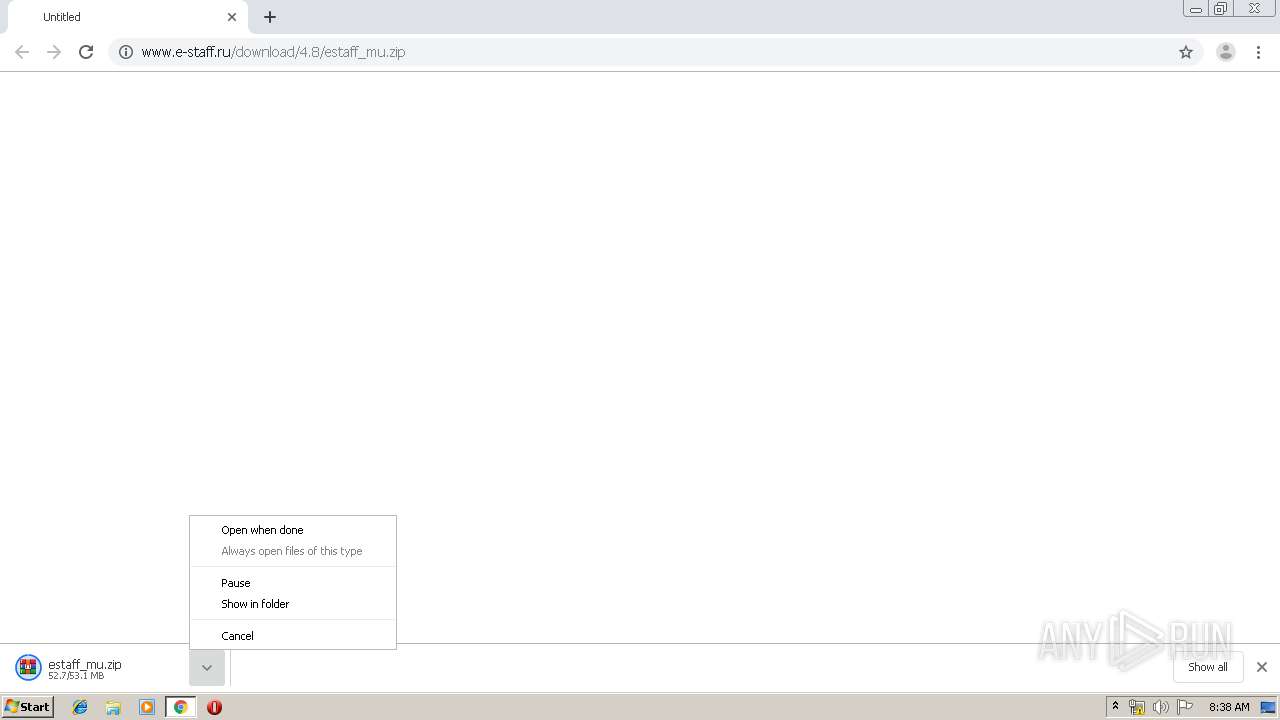
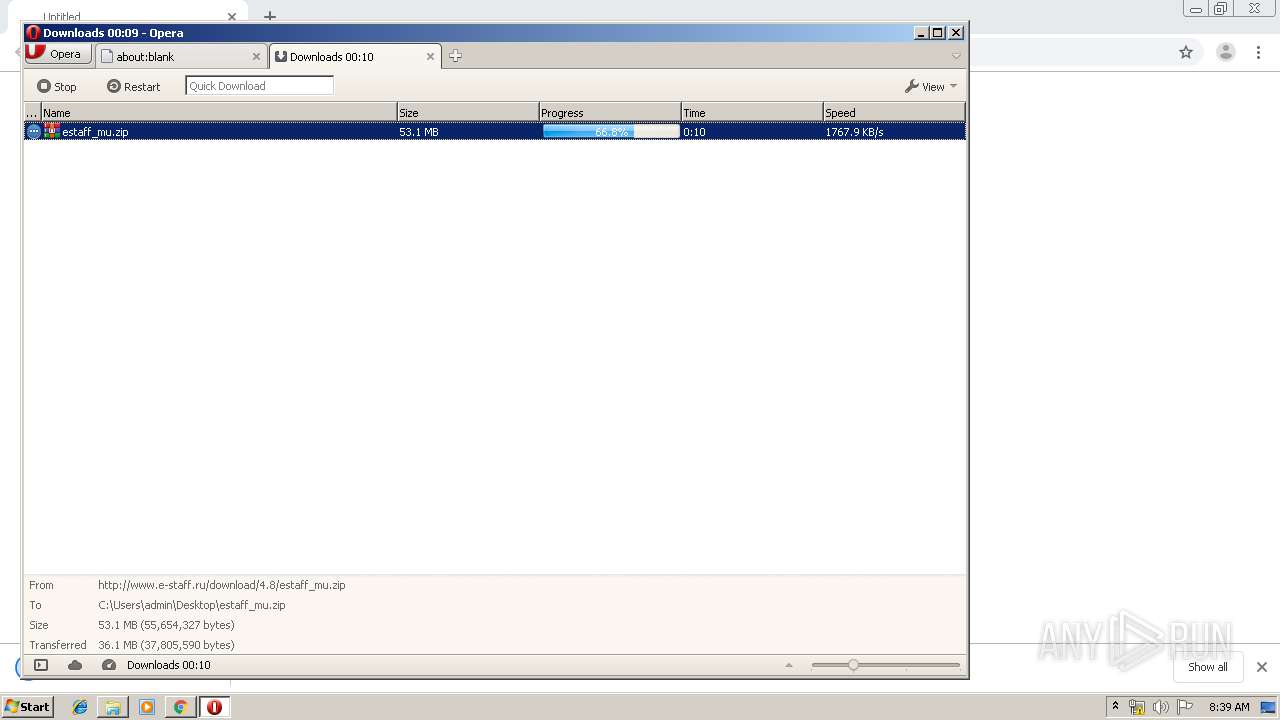
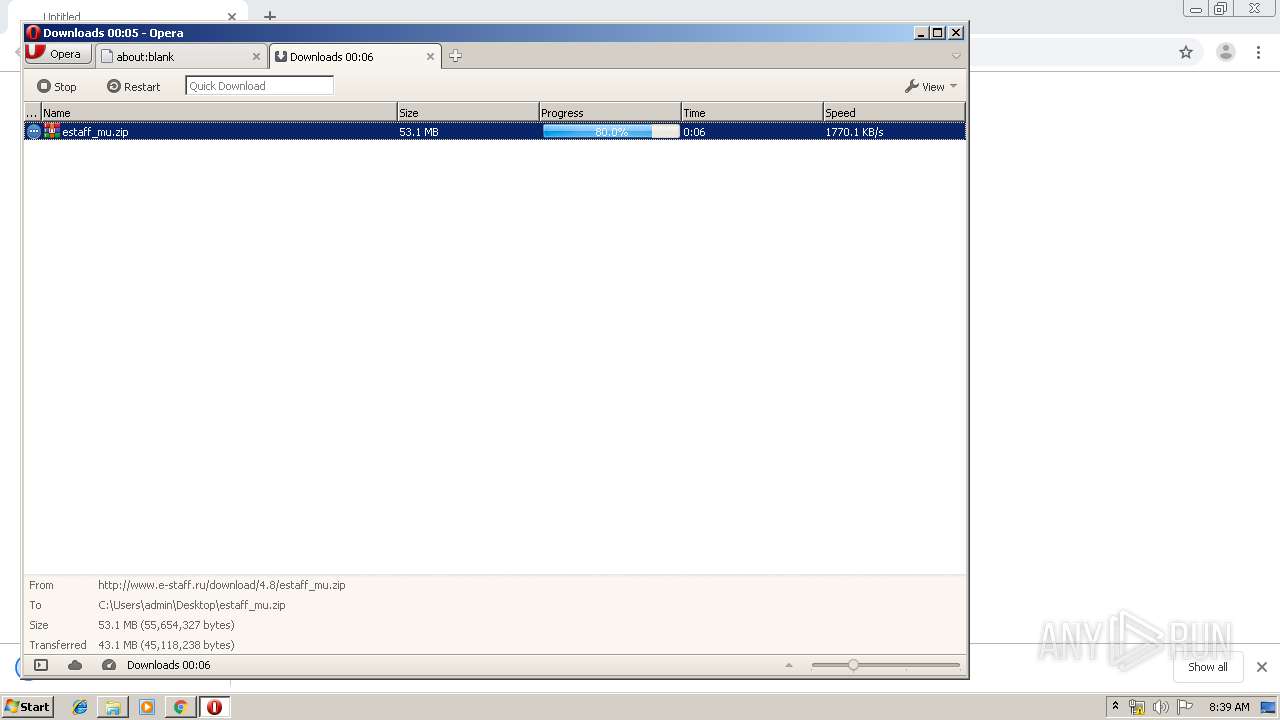
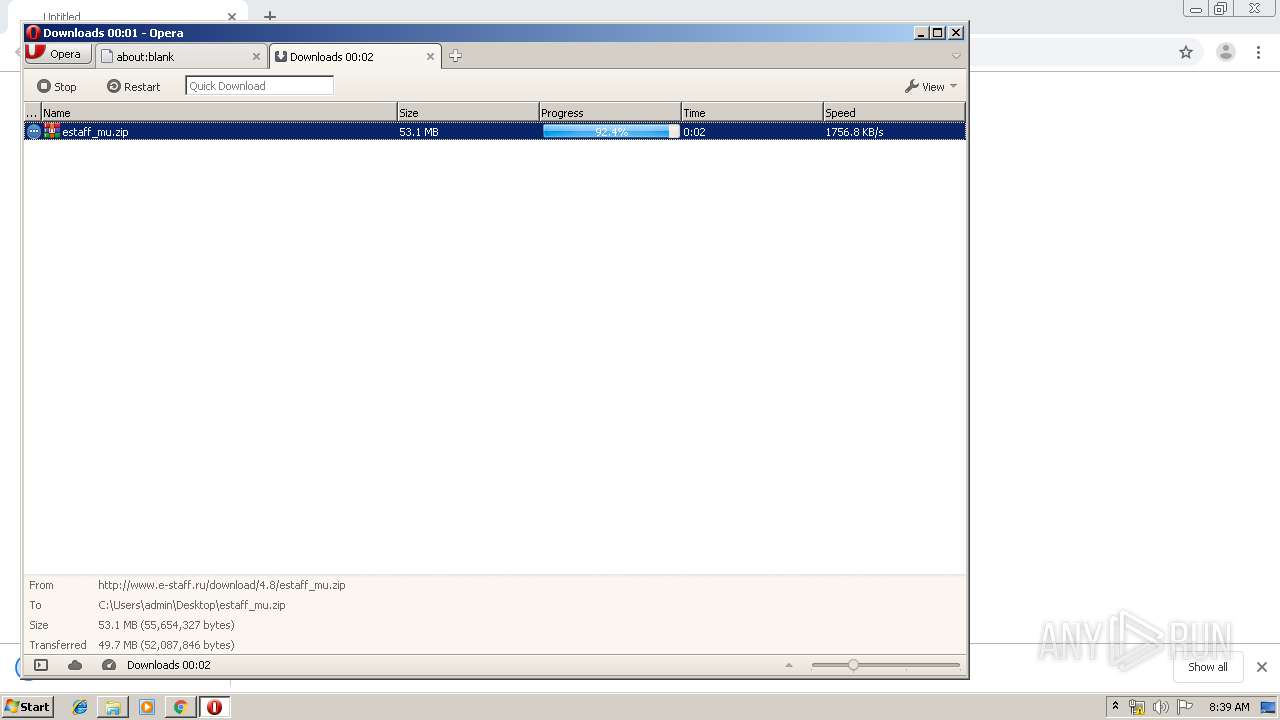
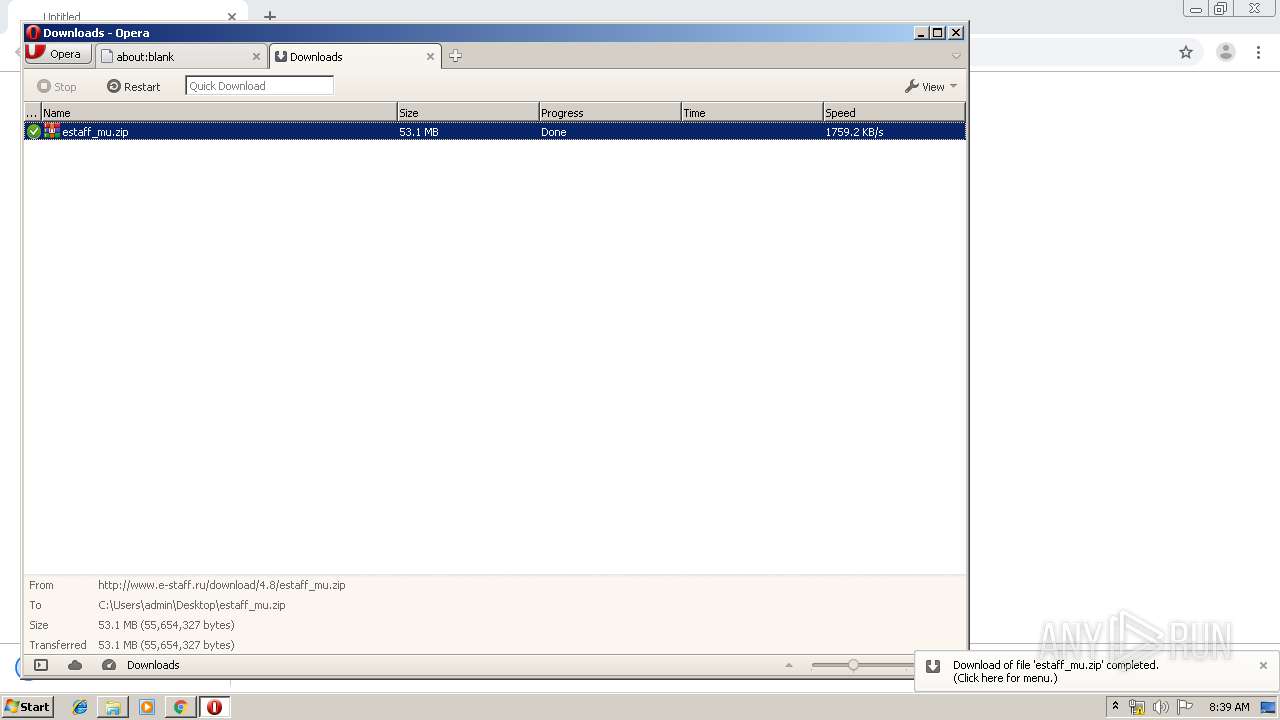
1440 | chrome.exe | GET | 200 | 89.104.91.207:80 | http://www.e-staff.ru/download/4.8/estaff_mu.zip | RU | compressed | 53.0 Mb | suspicious |
3416 | opera.exe | GET | 200 | 89.104.91.207:80 | http://www.e-staff.ru/download/4.8/estaff_mu.zip | RU | compressed | 53.0 Mb | suspicious |
3416 | opera.exe | GET | 200 | 172.217.22.14:80 | http://clients1.google.com/complete/search?q=virust&client=opera-suggest-omnibox&hl=de | US | text | 108 b | whitelisted |
3416 | opera.exe | GET | 200 | 172.217.22.14:80 | http://clients1.google.com/complete/search?q=virus&client=opera-suggest-omnibox&hl=de | US | text | 111 b | whitelisted |
3416 | opera.exe | GET | 200 | 172.217.22.14:80 | http://clients1.google.com/complete/search?q=viru&client=opera-suggest-omnibox&hl=de | US | text | 109 b | whitelisted |
3416 | opera.exe | GET | 200 | 172.217.22.14:80 | http://clients1.google.com/complete/search?q=virustot&client=opera-suggest-omnibox&hl=de | US | text | 107 b | whitelisted |
1440 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1440 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1440 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
1440 | chrome.exe | 216.58.205.228:443 | www.google.com | Google Inc. | US | whitelisted |
1440 | chrome.exe | 89.104.91.207:80 | www.e-staff.ru | Jsc ru-center | RU | suspicious |
1440 | chrome.exe | 172.217.16.206:443 | clients4.google.com | Google Inc. | US | whitelisted |
1440 | chrome.exe | 172.217.22.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1440 | chrome.exe | 172.217.23.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1440 | chrome.exe | 172.217.22.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
1440 | chrome.exe | 172.217.18.163:443 | www.google.fr | Google Inc. | US | whitelisted |
1440 | chrome.exe | 172.217.22.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.e-staff.ru |
| suspicious |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
clients4.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
www.google.fr |
| whitelisted |
clients1.google.com |
| whitelisted |